An improved lossless data hiding scheme based on
An improved lossless data hiding scheme based on image VQ-index residual value coding Zhe-Ming Lu, Jun-Xiang Wang, Bei-Bei Liu The Journal of Systems and Software Repoter : 王軍証 1
Outline 1. 2. 3. 4. 5. Introduction Related works Proposed algorithm Experimental results Conclusions 2
1. Introduction � We propose an improved algorithm based on the work of Yang et al. (2005). The capacity, one of the most important properties of data hiding schemes, is increased in the proposed scheme. 3
2. Related works � Vector quantization � Side-match VQ � MFCVQ-based reversible data hiding algorithm 4
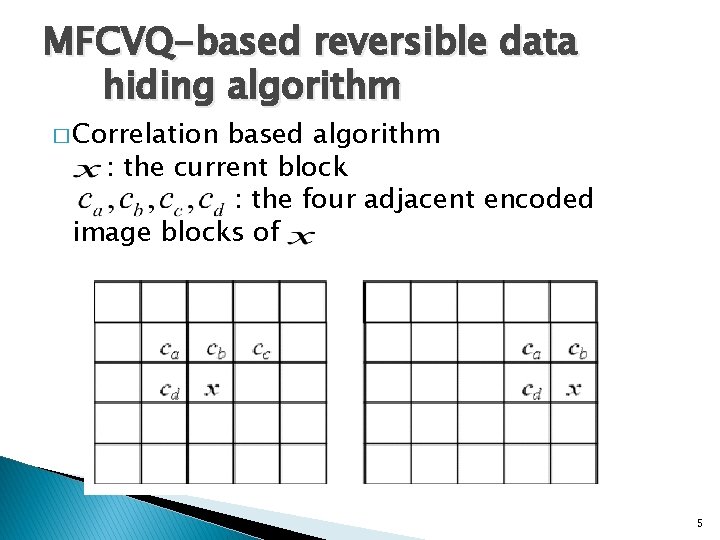
MFCVQ-based reversible data hiding algorithm � Correlation based algorithm : the current block : the four adjacent encoded image blocks of 5
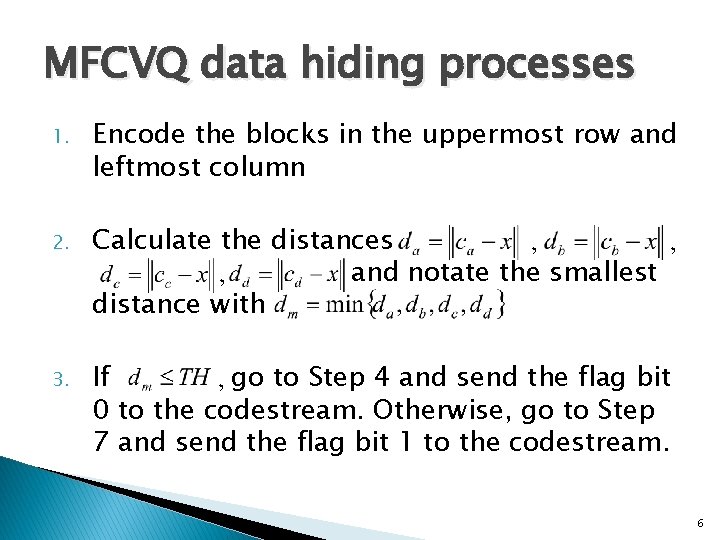
MFCVQ data hiding processes 1. Encode the blocks in the uppermost row and leftmost column 2. Calculate the distances , , , and notate the smallest distance with 3. If , go to Step 4 and send the flag bit 0 to the codestream. Otherwise, go to Step 7 and send the flag bit 1 to the codestream. 6
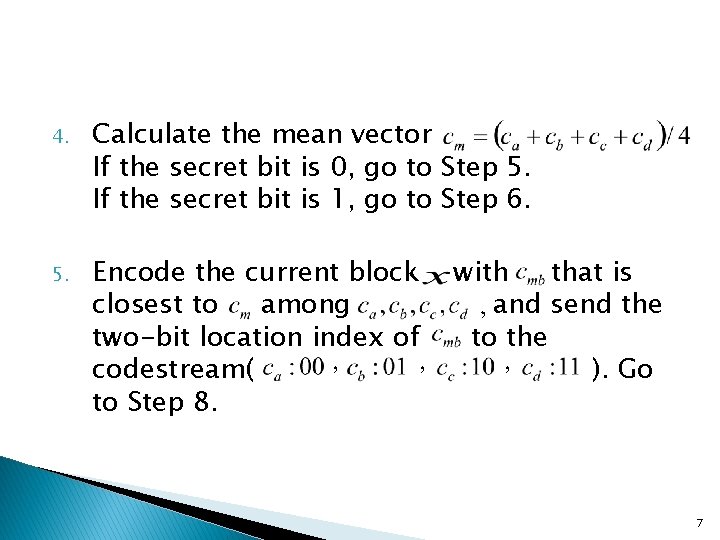
4. Calculate the mean vector If the secret bit is 0, go to Step 5. If the secret bit is 1, go to Step 6. 5. Encode the current block with that is closest to among , and send the two-bit location index of to the codestream( , , , ). Go to Step 8. 7
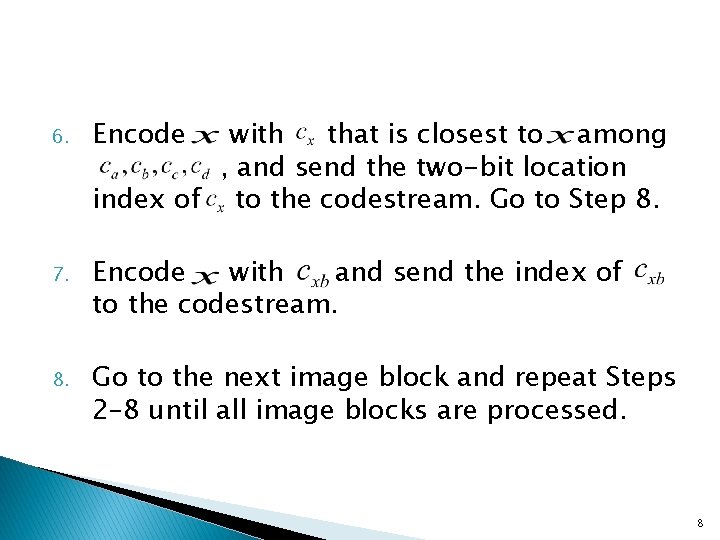
6. Encode with that is closest to among , and send the two-bit location index of to the codestream. Go to Step 8. 7. Encode with and send the index of to the codestream. 8. Go to the next image block and repeat Steps 2– 8 until all image blocks are processed. 8
� Note that if , the next best-matched code vector is selected to encode the current block. 9
MFCVQ data extraction � For the block encoded(flag bit 0) , if the transmitted index is for , then the secret bit 0 can be extracted. Otherwise, the secret bit 1 can be extracted. � To restore the original indices, just replace all the indices for nonwith the indices for. 10
3. Proposed algorithm ① ② ③ The preprocessing phase The data hiding phase The decoding and extracting phase 11
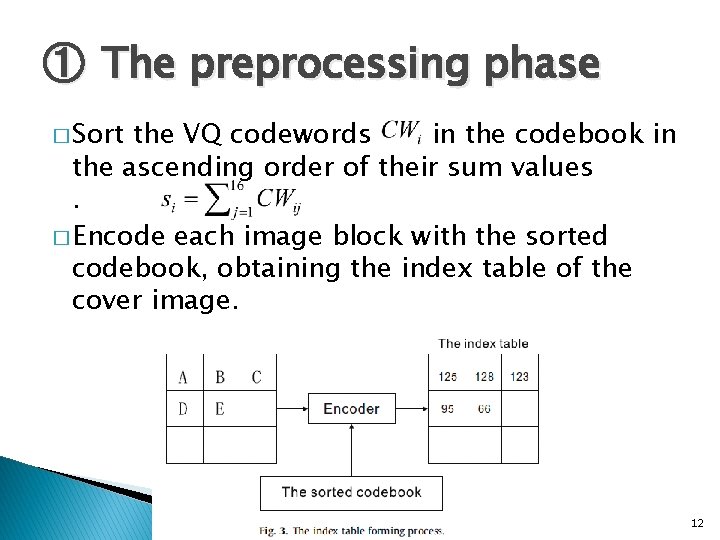
① The preprocessing phase � Sort the VQ codewords in the codebook in the ascending order of their sum values. � Encode each image block with the sorted codebook, obtaining the index table of the cover image. 12
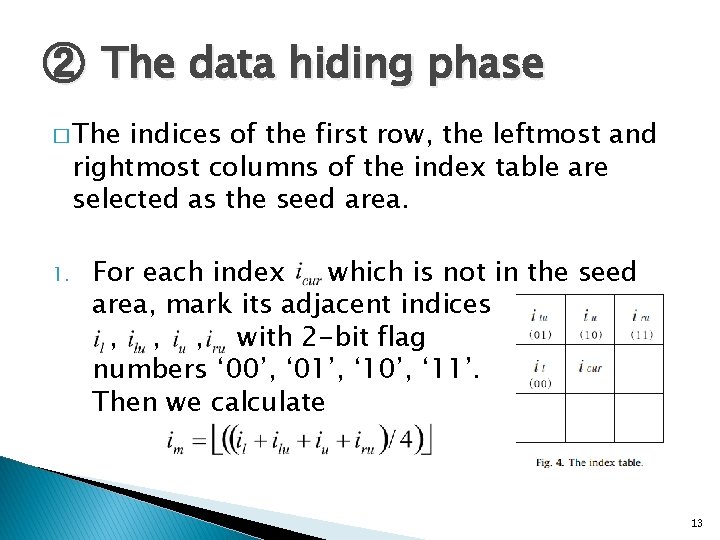
② The data hiding phase � The indices of the first row, the leftmost and rightmost columns of the index table are selected as the seed area. 1. For each index which is not in the seed area, mark its adjacent indices , , , with 2 -bit flag numbers ‘ 00’, ‘ 01’, ‘ 10’, ‘ 11’. Then we calculate 13
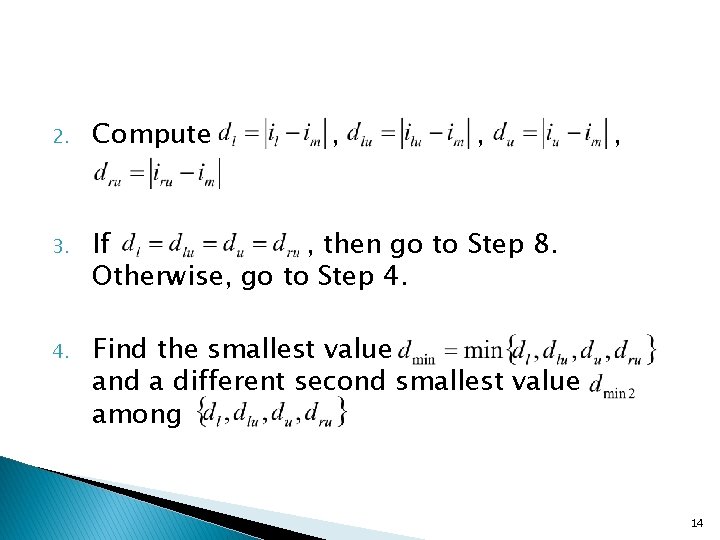
2. Compute , , 3. If , then go to Step 8. Otherwise, go to Step 4. Find the smallest value and a different second smallest value among , 14
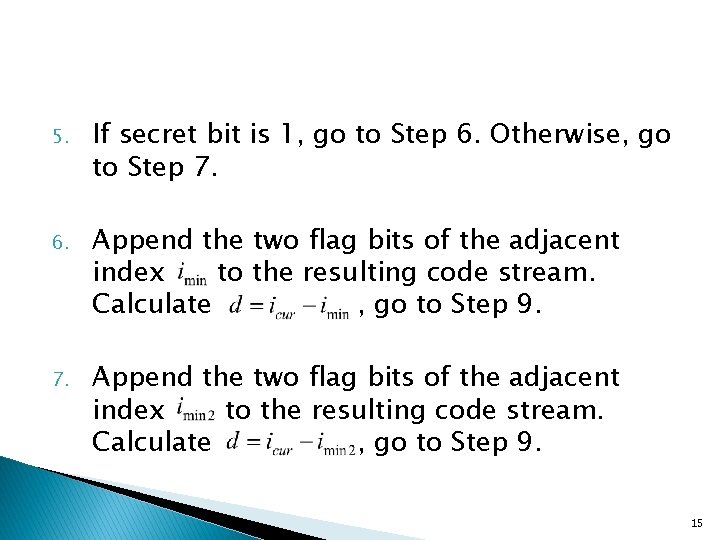
5. If secret bit is 1, go to Step 6. Otherwise, go to Step 7. 6. Append the two flag bits of the adjacent index to the resulting code stream. Calculate , go to Step 9. 7. Append the two flag bits of the adjacent index to the resulting code stream. Calculate , go to Step 9. 15
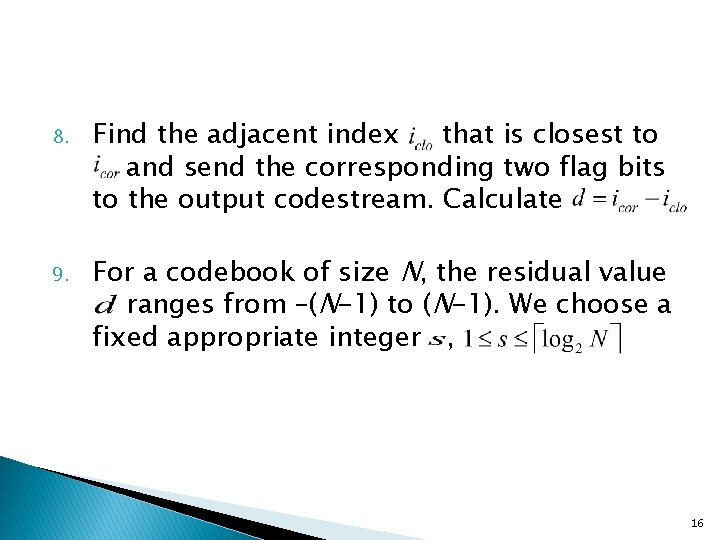
8. 9. Find the adjacent index that is closest to and send the corresponding two flag bits to the output codestream. Calculate For a codebook of size N, the residual value ranges from –(N-1) to (N-1). We choose a fixed appropriate integer , 16
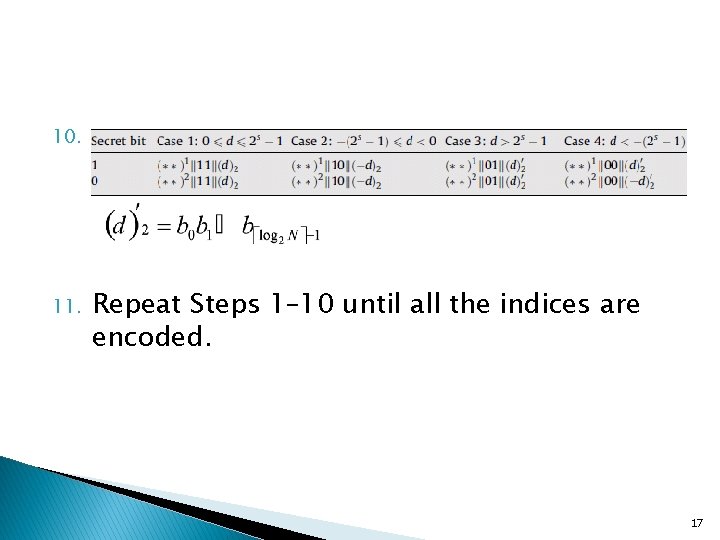
10. 11. Repeat Steps 1– 10 until all the indices are encoded. 17
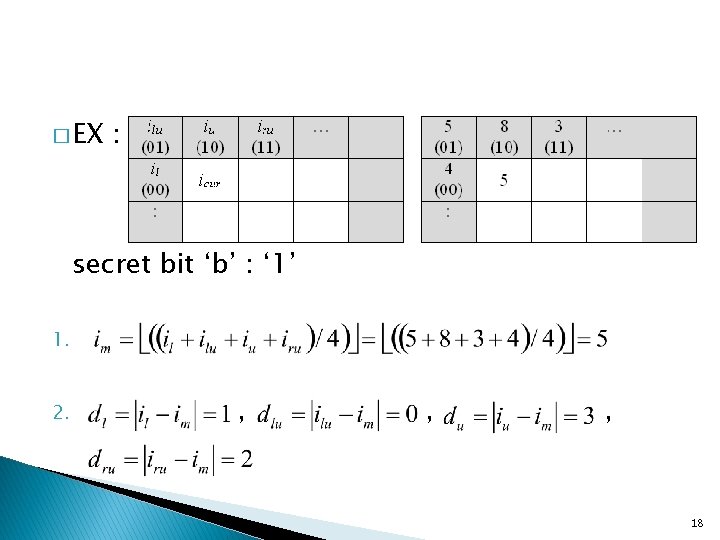
� EX : secret bit ‘b’ : ‘ 1’ 1. 2. , , , 18
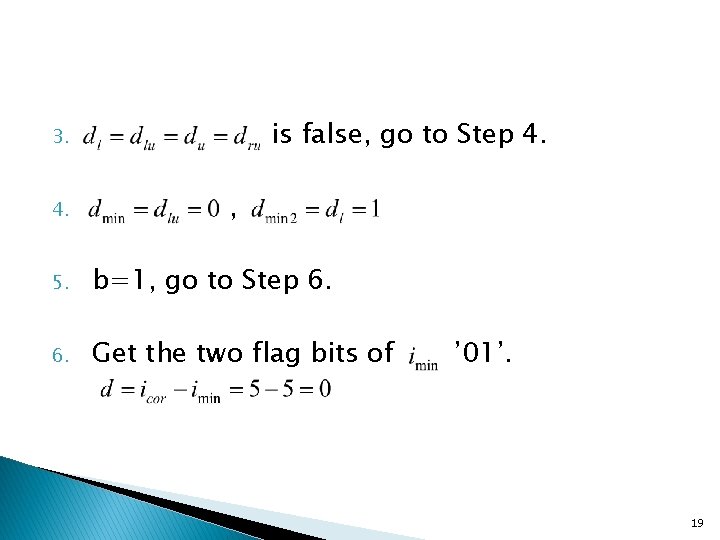
is false, go to Step 4. 3. 4. , 5. b=1, go to Step 6. Get the two flag bits of ’ 01’. 19
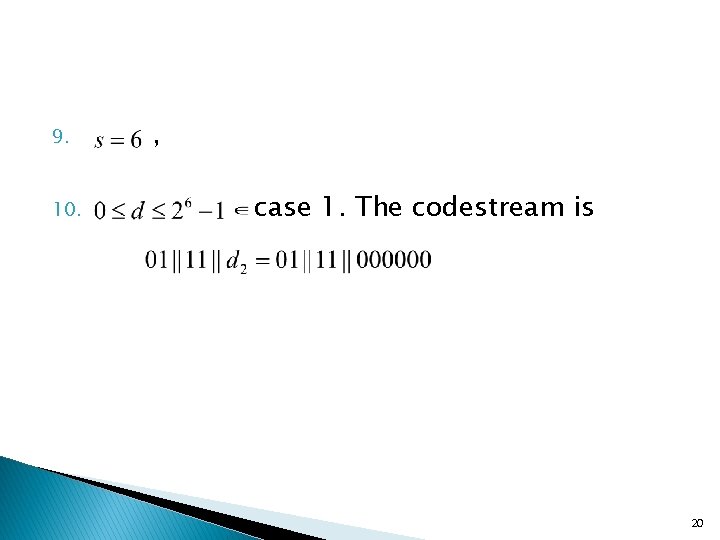
9. 10. , case 1. The codestream is 20
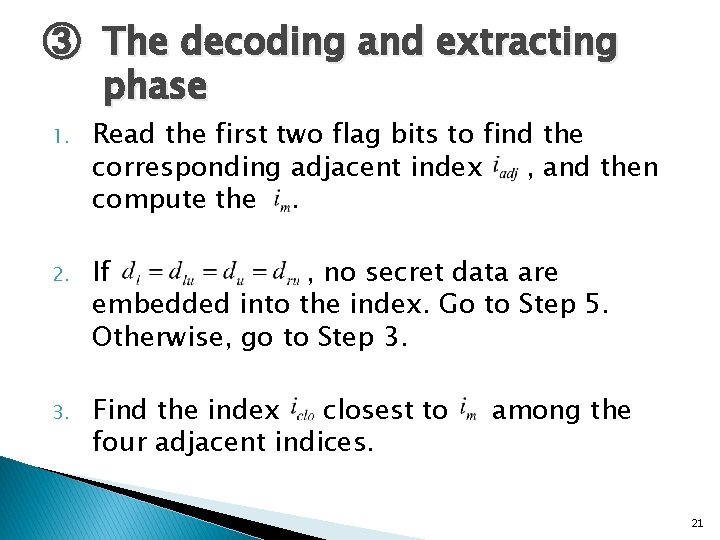
③ The decoding and extracting phase 1. Read the first two flag bits to find the corresponding adjacent index , and then compute the. 2. If , no secret data are embedded into the index. Go to Step 5. Otherwise, go to Step 3. Find the index closest to four adjacent indices. among the 21
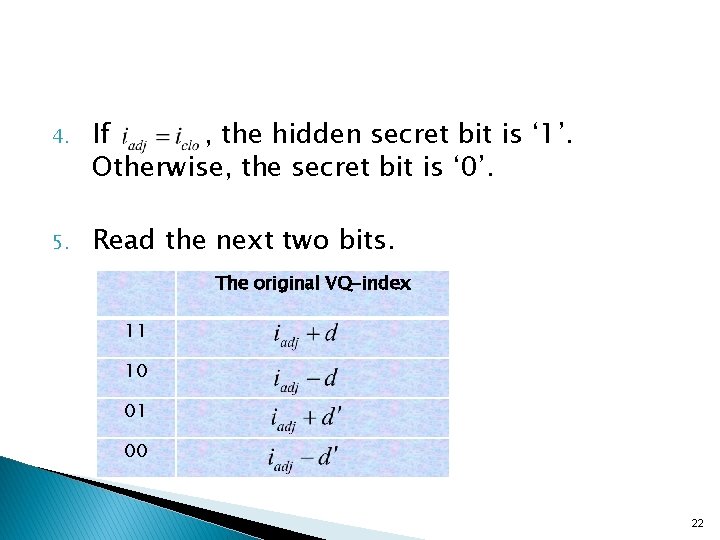
4. If , the hidden secret bit is ‘ 1’. Otherwise, the secret bit is ‘ 0’. 5. Read the next two bits. The original VQ-index 11 10 01 00 22
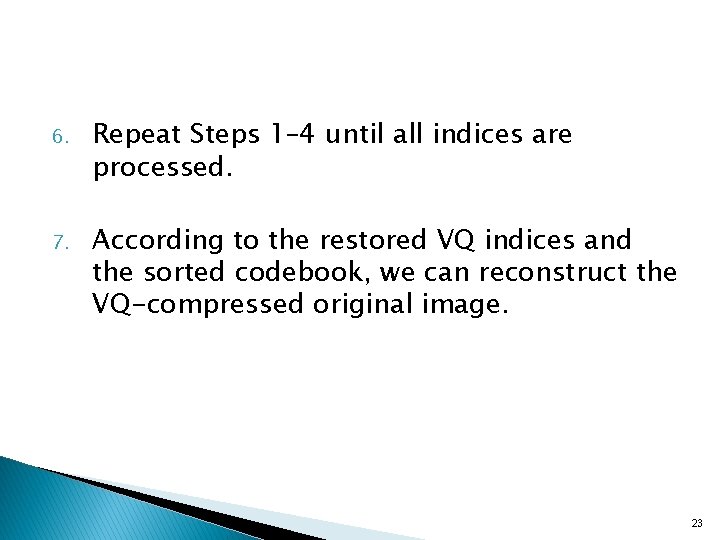
6. Repeat Steps 1– 4 until all indices are processed. 7. According to the restored VQ indices and the sorted codebook, we can reconstruct the VQ-compressed original image. 23
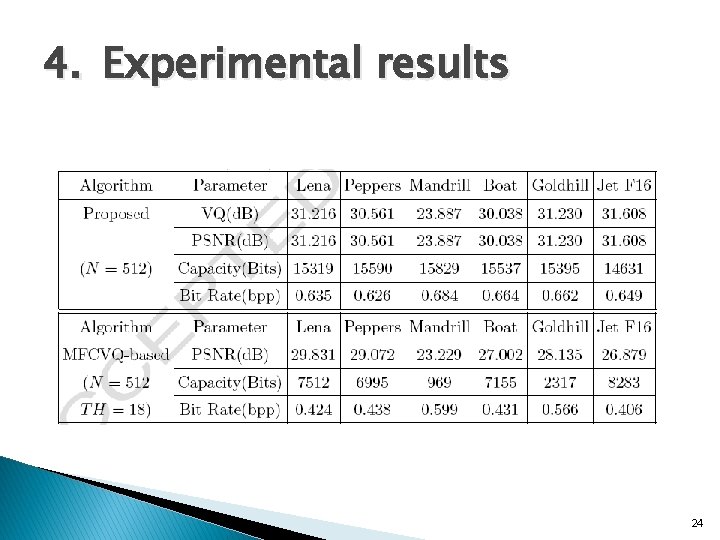
4. Experimental results 24
5. Conclusions � The main advantages of the scheme are as follows: (1) The proposed algorithm achieves higher PSNR and higher data hiding capacity. (2) According to Section 3, our proposed scheme can be separated into the VQ encoding process for generating the VQindex table and the data hiding process to embed secret data into the codestream. 25
- Slides: 25