SESSION CODE WEB 301 Pete Le Page Senior
SESSION CODE: WEB 301 Pete Le. Page Senior Product Manager Microsoft Corporation
A Little History Securing Your Infrastructure Trust User Input At Your Own Peril SQL Injection Attacks Cross Site Scripting Attacks Click. Jacking Attacks Native JSON Building Mash-Ups



Making The Correct Tradeoffs is Hard

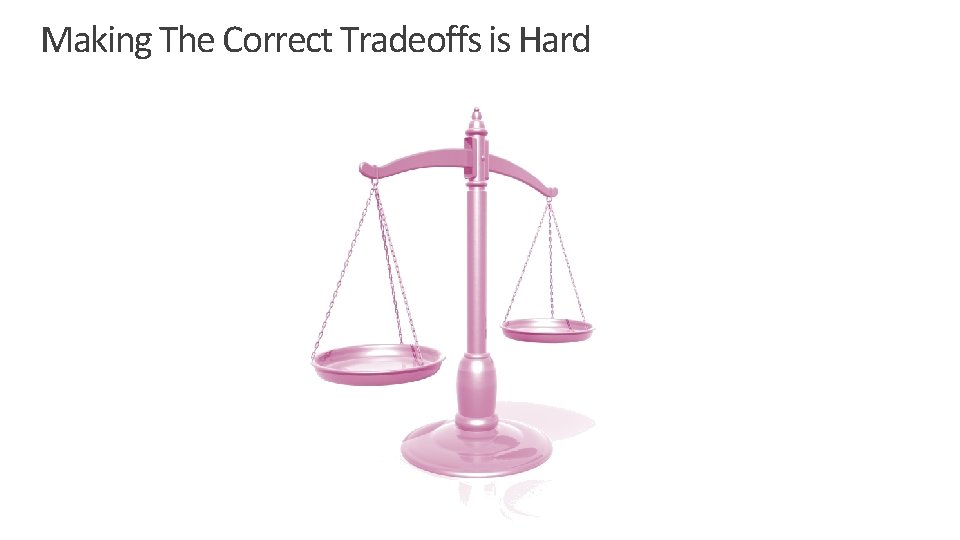
Internet Explorer 8: Secure by default Security Feature Improvements Create security features that address the top vulnerabilities today and in the future Secure Features Provide Security and Compatibility Reduce attack surface of existing code by closing legacy holes Users understand that improved security is a reason to upgrade Apply security-focused rigors against new code
A Little History Securing Your Infrastructure Trust User Input At Your Own Peril SQL Injection Attacks Cross Site Scripting Attacks Click. Jacking Attacks Native JSON Building Mash-Ups

Creating Secure Connections
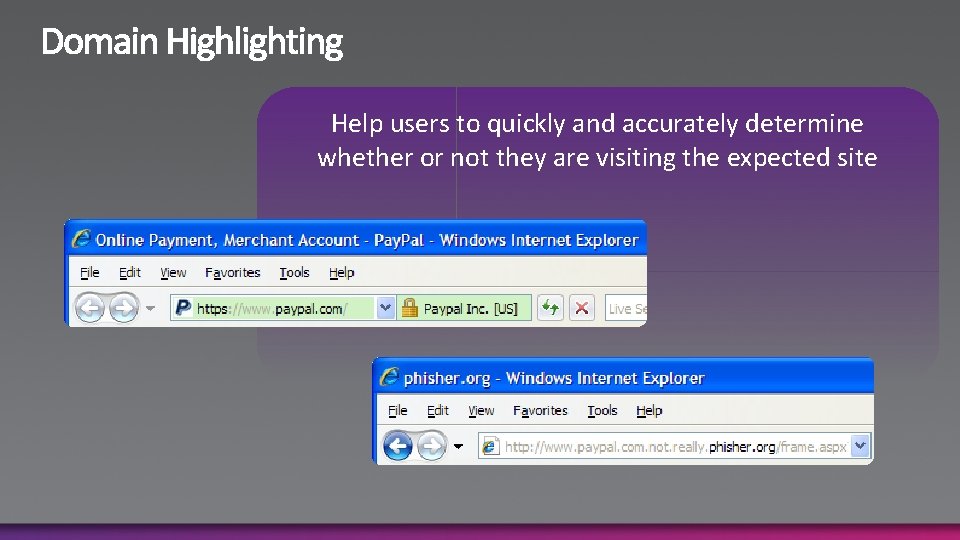
Help users to quickly and accurately determine whether or not they are visiting the expected site
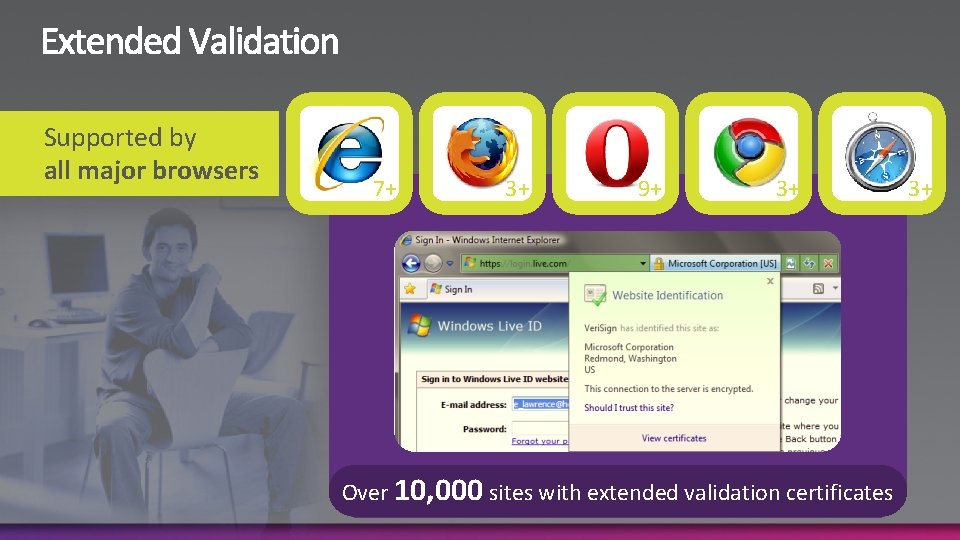
Supported by all major browsers 7+ 3+ 9+ 3+ Over 10, 000 sites with extended validation certificates 3+
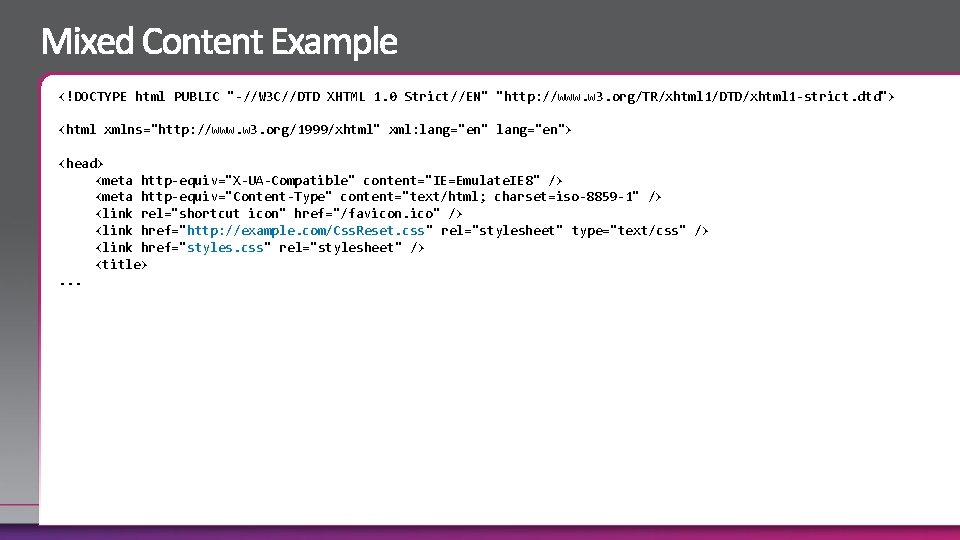
<!DOCTYPE html PUBLIC "-//W 3 C//DTD XHTML 1. 0 Strict//EN" "http: //www. w 3. org/TR/xhtml 1/DTD/xhtml 1 -strict. dtd"> <html xmlns="http: //www. w 3. org/1999/xhtml" xml: lang="en"> <head> <meta http-equiv="X-UA-Compatible" content="IE=Emulate. IE 8" /> <meta http-equiv="Content-Type" content="text/html; charset=iso-8859 -1" /> <link rel="shortcut icon" href="/favicon. ico" /> <link href="http: //example. com/Css. Reset. css" rel="stylesheet" type="text/css" /> <link href="styles. css" rel="stylesheet" /> <title>. . .
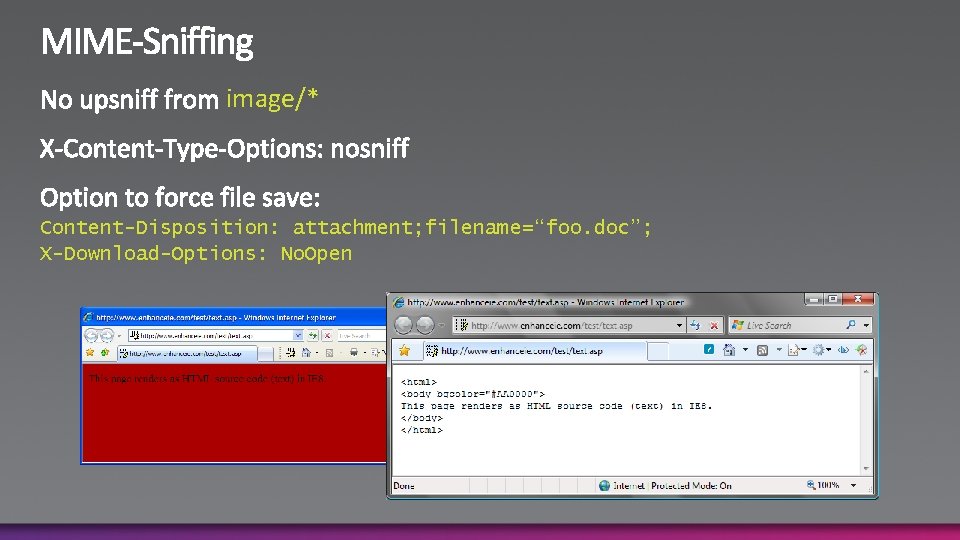
image/* Content-Disposition: attachment; filename=“foo. doc”; X-Download-Options: No. Open
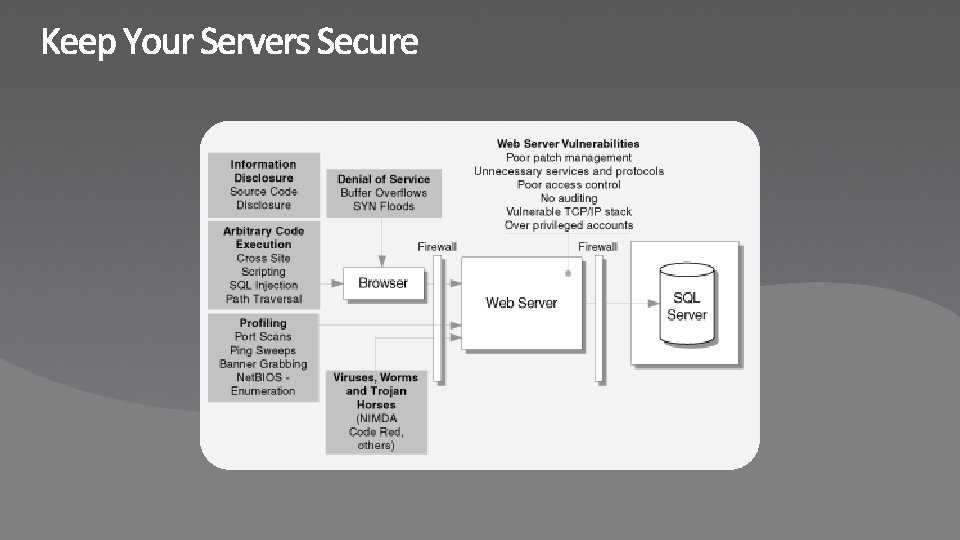
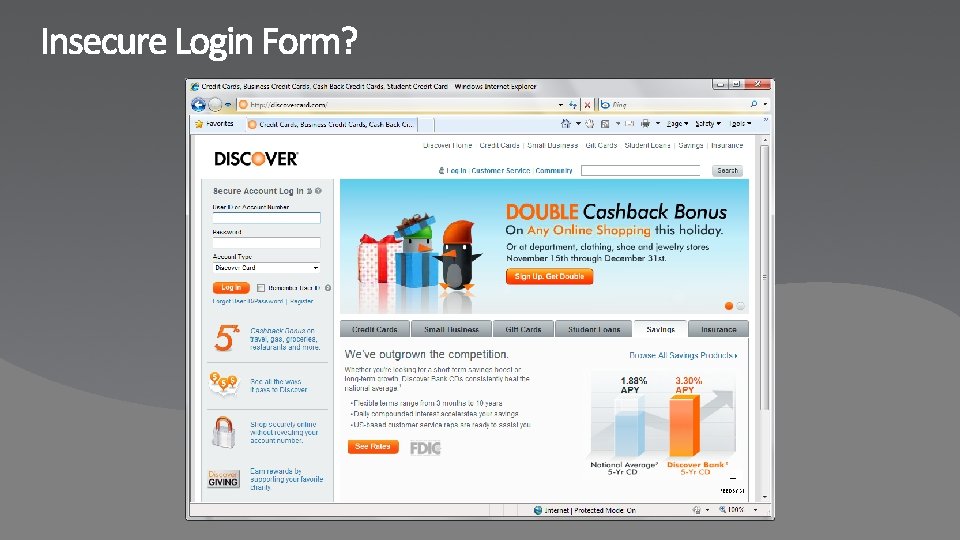
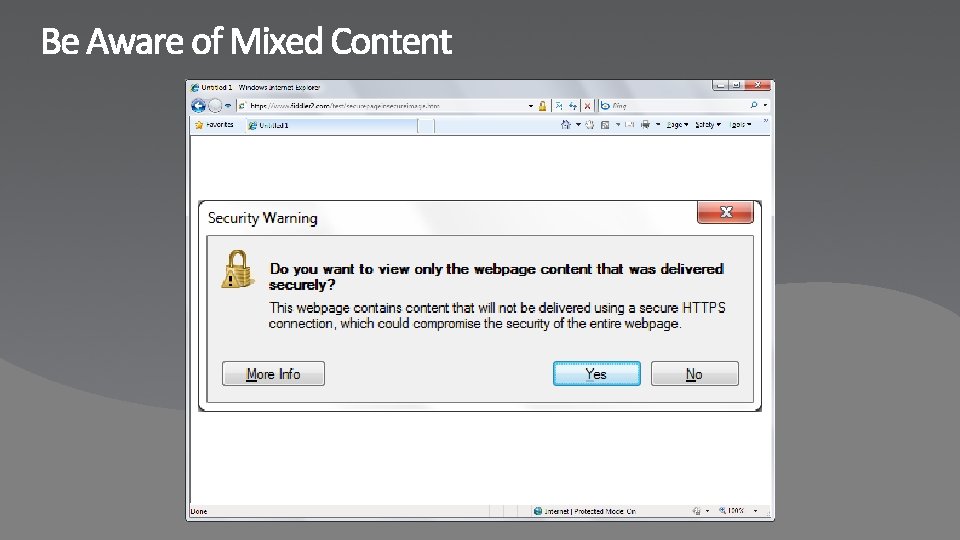
Ensure you’re using SSL when appropriate Check users aren’t being prompted for mixed content? Make sure you’re servers up to date Use best-practices for user accounts, and passwords
A Little History Securing Your Infrastructure Trust User Input At Your Own Peril SQL Injection Attacks Cross Site Scripting Attacks Click. Jacking Attacks Native JSON Building Mash-Ups
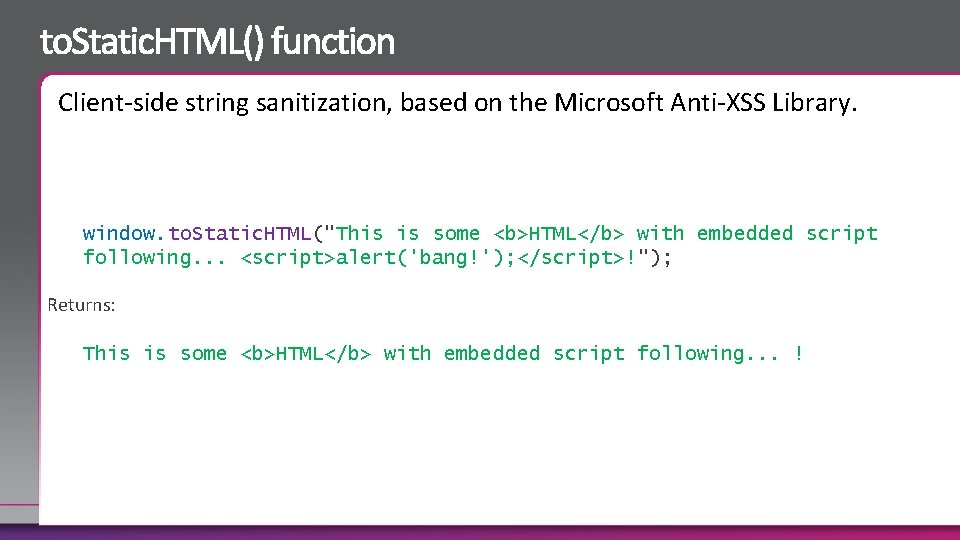
Client-side string sanitization, based on the Microsoft Anti-XSS Library. window. to. Static. HTML("This is some <b>HTML</b> with embedded script following. . . <script>alert('bang!'); </script>!"); Returns: This is some <b>HTML</b> with embedded script following. . . !
Don’t rely on client side validation for input Use to. Static. HTML() as one method to sanitize data
A Little History Securing Your Infrastructure Trust User Input At Your Own Peril SQL Injection Attacks Cross Site Scripting Attacks Click. Jacking Attacks Native JSON Building Mash-Ups
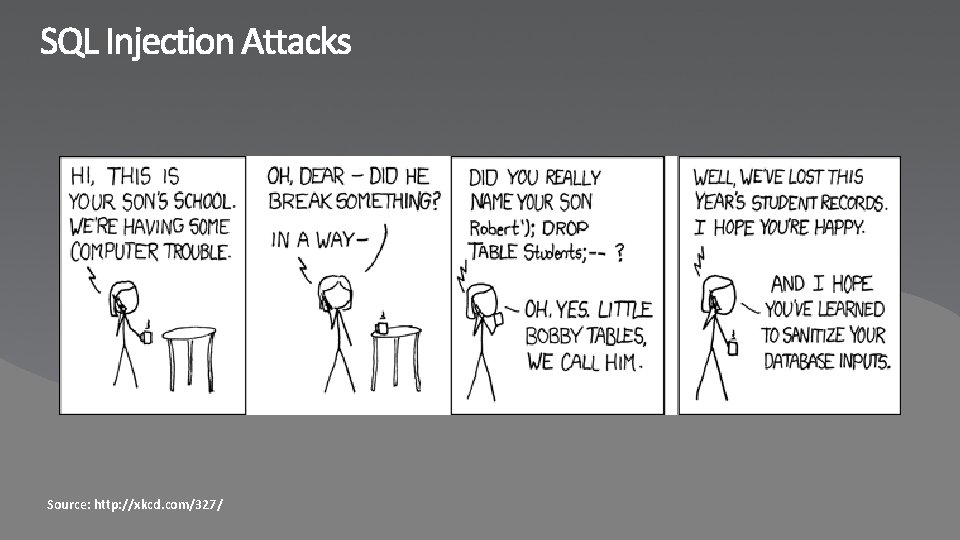
Source: http: //xkcd. com/327/
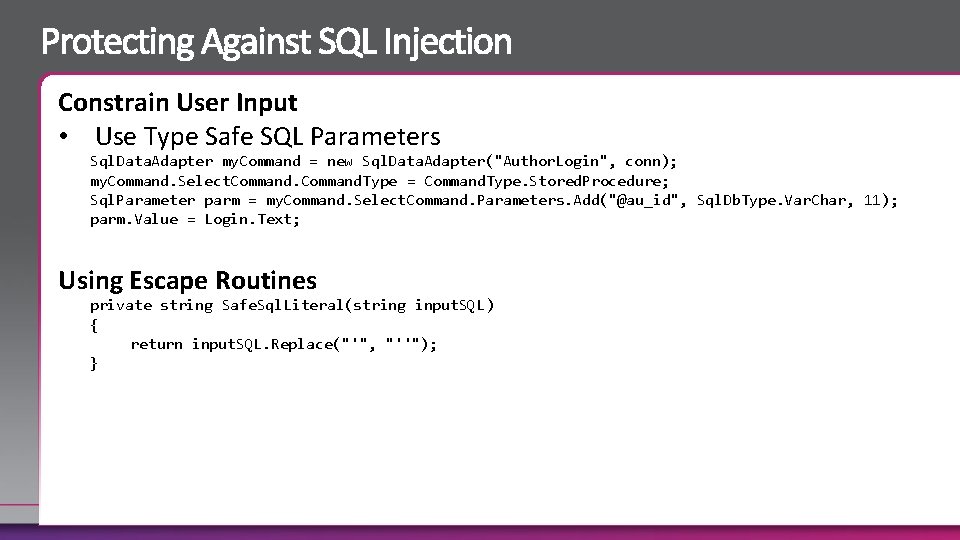
Constrain User Input • Use Type Safe SQL Parameters Sql. Data. Adapter my. Command = new Sql. Data. Adapter("Author. Login", conn); my. Command. Select. Command. Type = Command. Type. Stored. Procedure; Sql. Parameter parm = my. Command. Select. Command. Parameters. Add("@au_id", Sql. Db. Type. Var. Char, 11); parm. Value = Login. Text; Using Escape Routines private string Safe. Sql. Literal(string input. SQL) { return input. SQL. Replace("'", "''"); }
Assume all user input is evil! Use parameterized statements instead of building queries
A Little History Securing Your Infrastructure Trust User Input At Your Own Peril SQL Injection Attacks Cross Site Scripting Attacks Click. Jacking Attacks Native JSON Building Mash-Ups
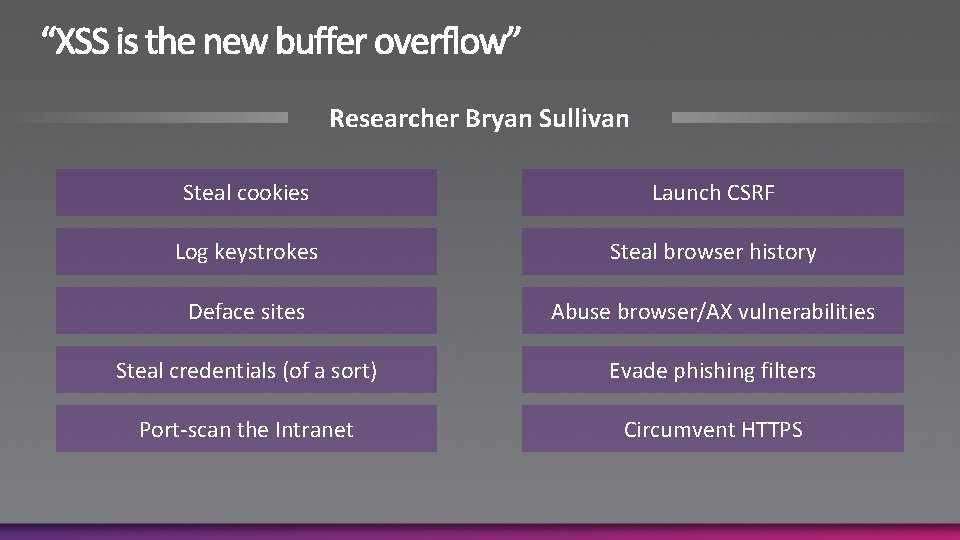
Researcher Bryan Sullivan Steal cookies Launch CSRF Log keystrokes Steal browser history Deface sites Abuse browser/AX vulnerabilities Steal credentials (of a sort) Evade phishing filters Port-scan the Intranet Circumvent HTTPS
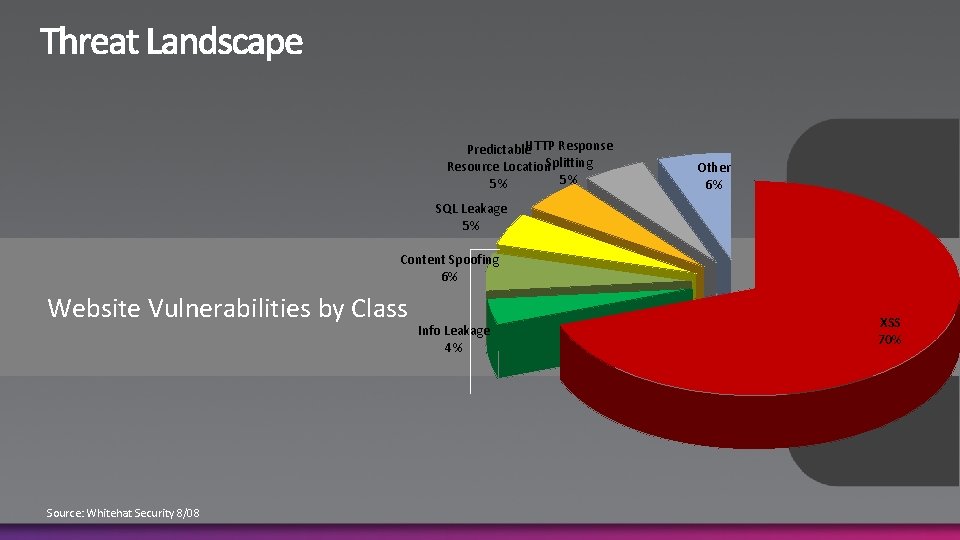
Predictable. HTTP Response Resource Location. Splitting 5% 5% Other 6% SQL Leakage 5% Content Spoofing 6% Website Vulnerabilities by Class Source: Whitehat Security 8/08 Info Leakage 4% XSS 70%
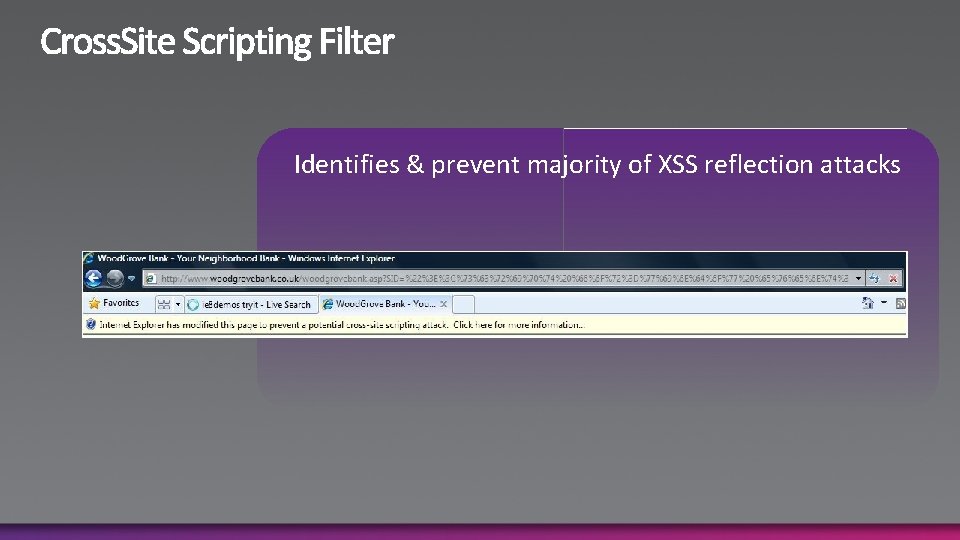
Identifies & prevent majority of XSS reflection attacks
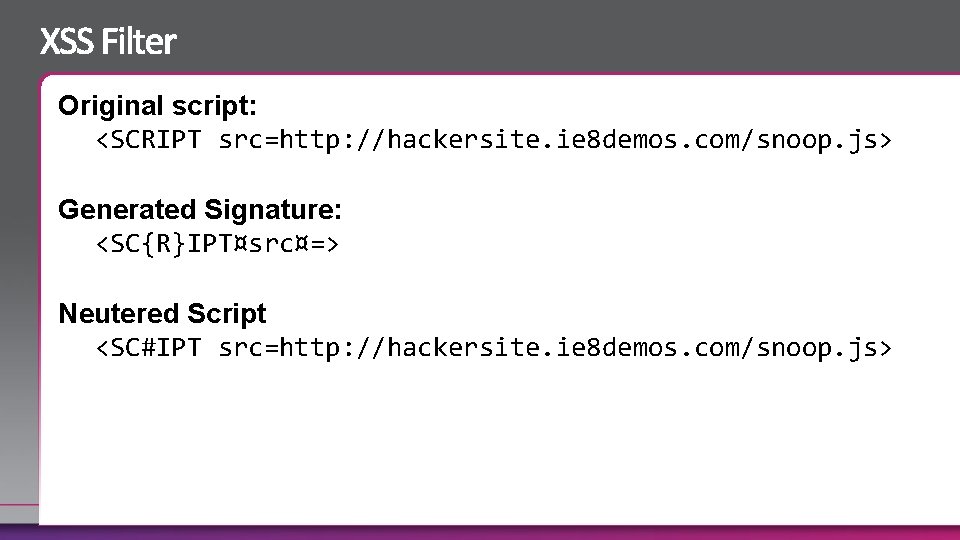
Original script: <SCRIPT src=http: //hackersite. ie 8 demos. com/snoop. js> Generated Signature: <SC{R}IPT¤src¤=> Neutered Script <SC#IPT src=http: //hackersite. ie 8 demos. com/snoop. js>
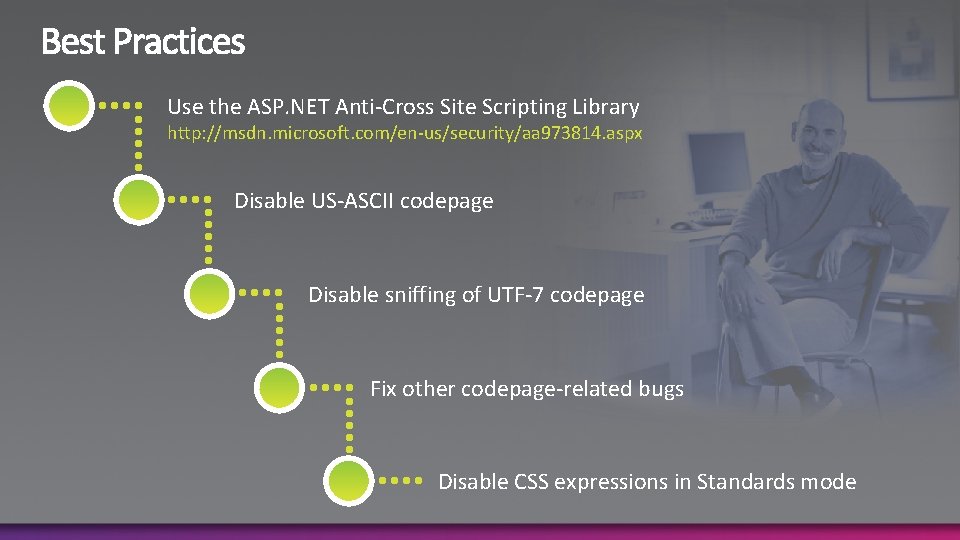
Use the ASP. NET Anti-Cross Site Scripting Library http: //msdn. microsoft. com/en-us/security/aa 973814. aspx Disable US-ASCII codepage Disable sniffing of UTF-7 codepage Fix other codepage-related bugs Disable CSS expressions in Standards mode
A Little History Securing Your Infrastructure Trust User Input At Your Own Peril SQL Injection Attacks Cross Site Scripting Attacks Click. Jacking Attacks Native JSON Building Mash-Ups

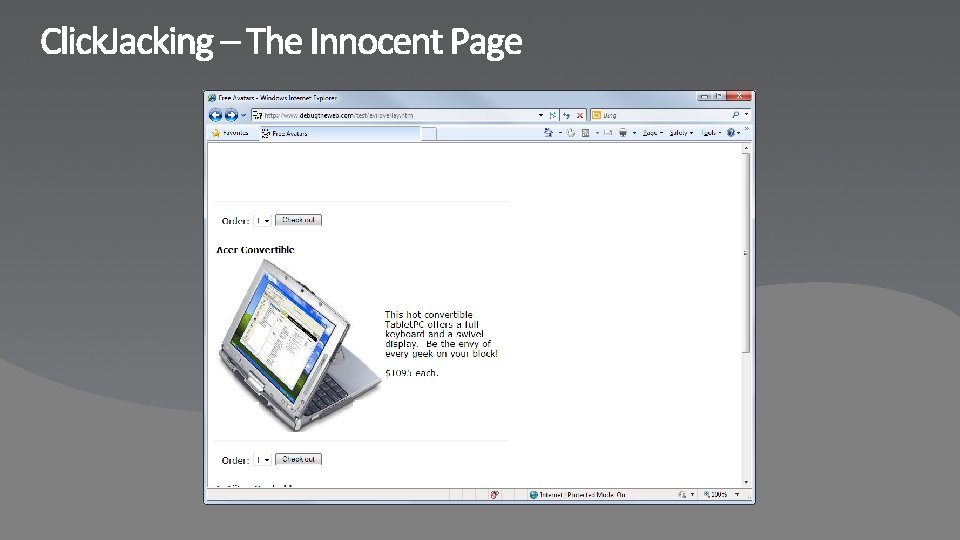
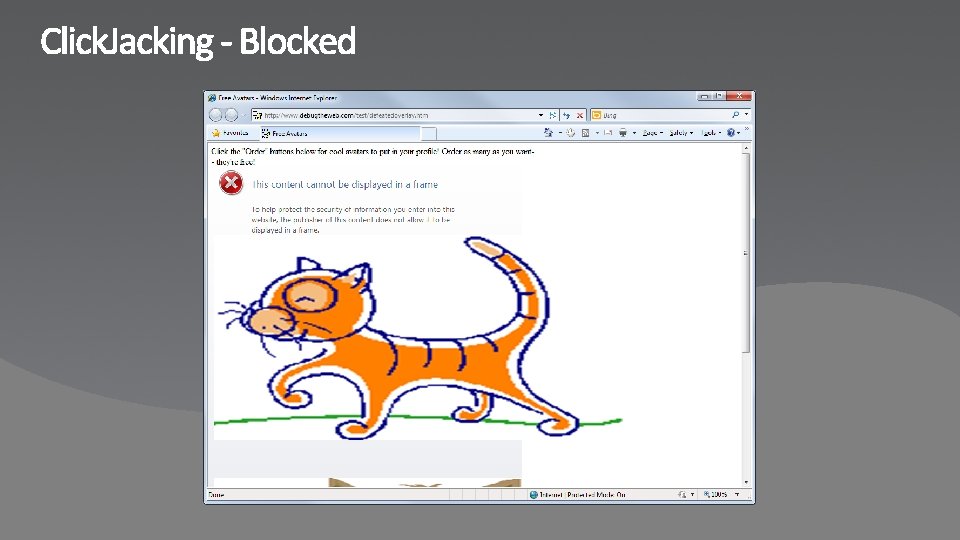
Click. Jacking
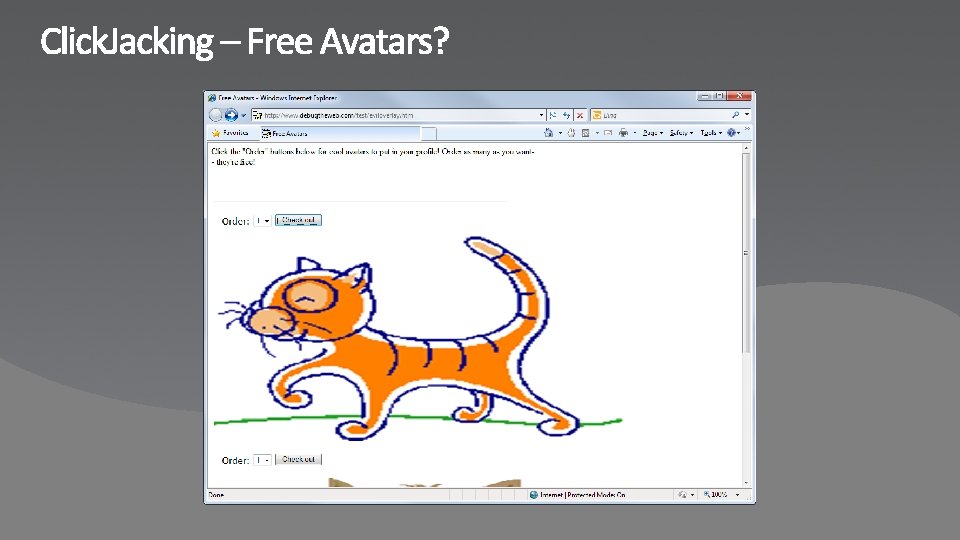
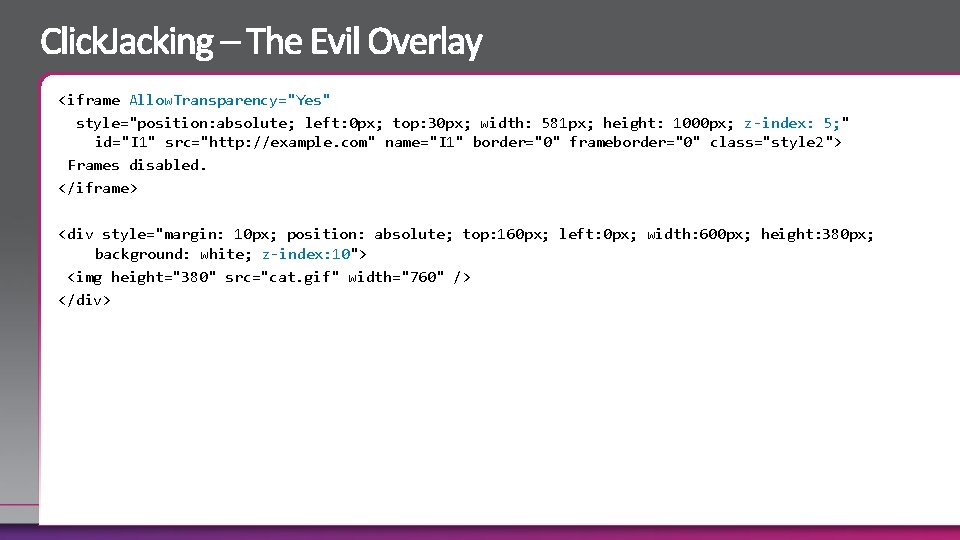
<iframe Allow. Transparency="Yes" style="position: absolute; left: 0 px; top: 30 px; width: 581 px; height: 1000 px; z-index: 5; " id="I 1" src="http: //example. com" name="I 1" border="0" frameborder="0" class="style 2"> Frames disabled. </iframe> <div style="margin: 10 px; position: absolute; top: 160 px; left: 0 px; width: 600 px; height: 380 px; background: white; z-index: 10"> <img height="380" src="cat. gif" width="760" /> </div>
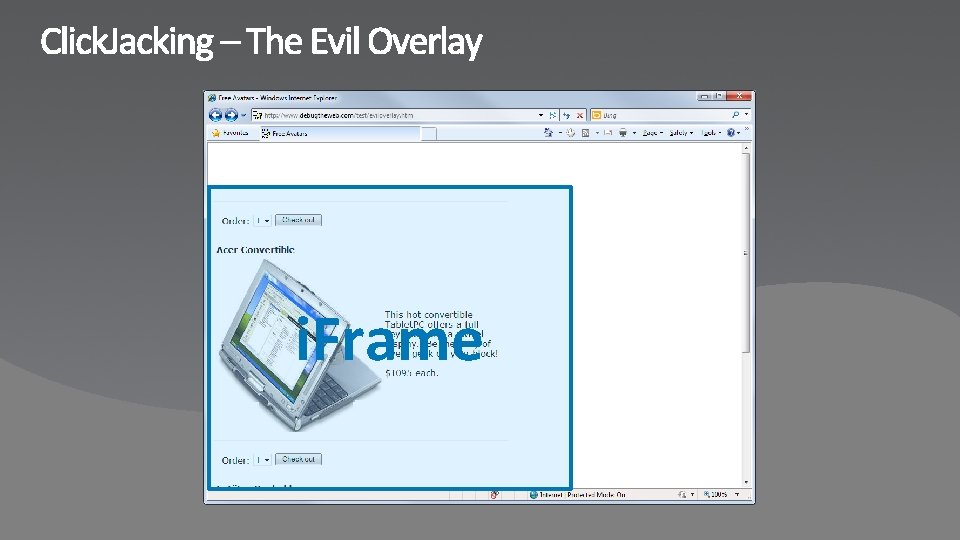
i. Frame
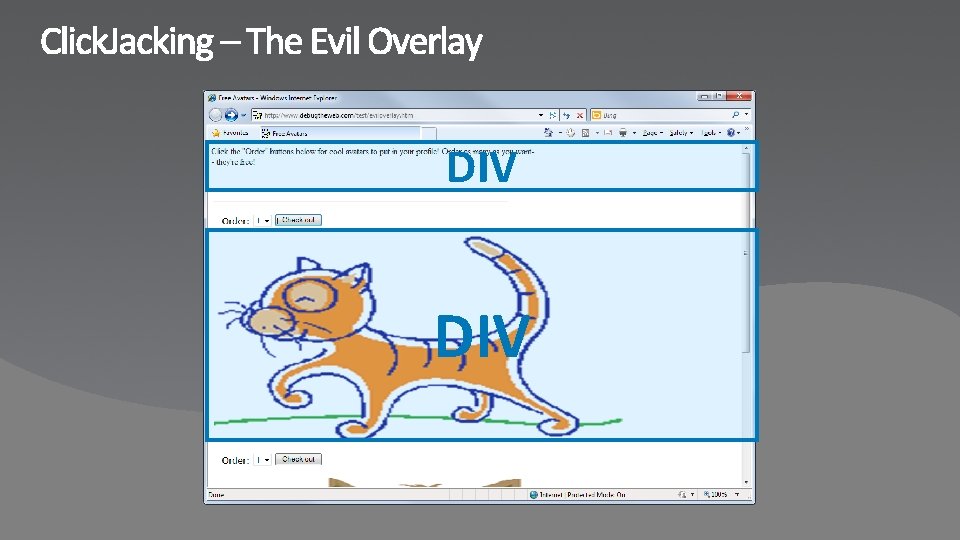
DIV
Blocked By X-Frame-Option
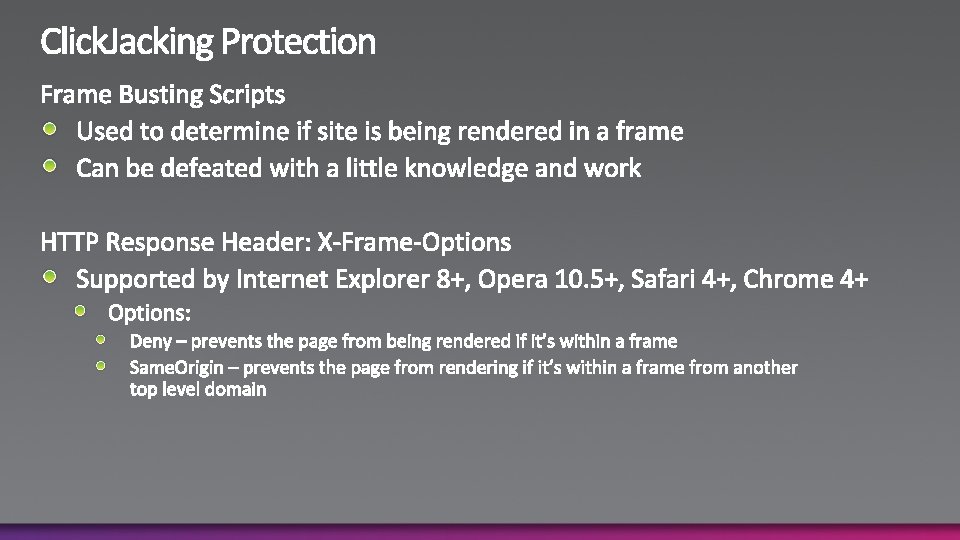
Use HTTP Response Header X-Frame-Options Don’t use “sameorigin” if you have any page on your domain which accepts an arbitrary URL to frame
A Little History Securing Your Infrastructure Trust User Input At Your Own Peril SQL Injection Attacks Cross Site Scripting Attacks Click. Jacking Attacks Native JSON Building Mash-Ups
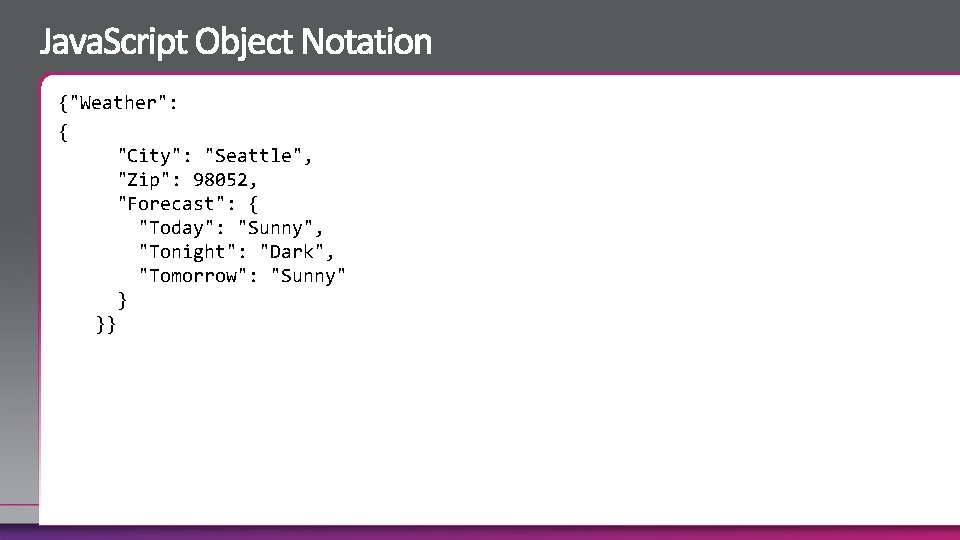
{"Weather": { "City": "Seattle", "Zip": 98052, "Forecast": { "Today": "Sunny", "Tonight": "Dark", "Tomorrow": "Sunny" } }}
Based on Douglas Crockford’s implementation of JSON 2 and standardized in ECMAScript 5 JSON. stringify() JSON. parse()
Use JSON over eval() to transfer data between client and server Check for native JSON support before using other libraries
A Little History Securing Your Infrastructure Trust User Input At Your Own Peril SQL Injection Attacks Cross Site Scripting Attacks Click. Jacking Attacks Native JSON Building Mash-Ups
Securing Mash Ups
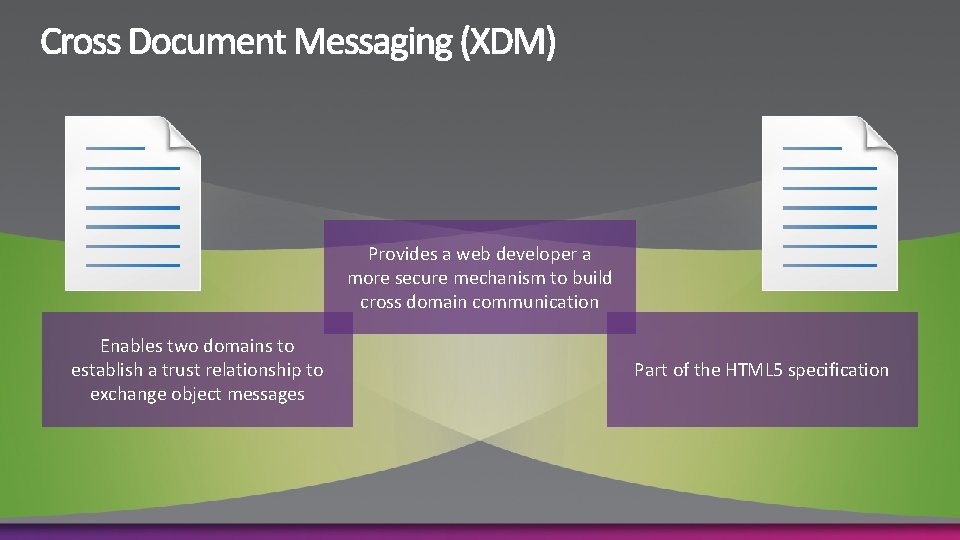
Provides a web developer a more secure mechanism to build cross domain communication Enables two domains to establish a trust relationship to exchange object messages Part of the HTML 5 specification
![// Find target frame var o. Frame = document. get. Elements. By. Tag. Name('iframe')[0]; // Find target frame var o. Frame = document. get. Elements. By. Tag. Name('iframe')[0];](http://slidetodoc.com/presentation_image_h2/a7f1bdcf0e6faa1604281f0ca6827119/image-58.jpg)
// Find target frame var o. Frame = document. get. Elements. By. Tag. Name('iframe')[0]; // post. Message will only deliver the 'Hello’ // message if the frame is currently // at the expected target site o. Frame. content. Window. post. Message('Hello', 'http: //recipient. example. com');
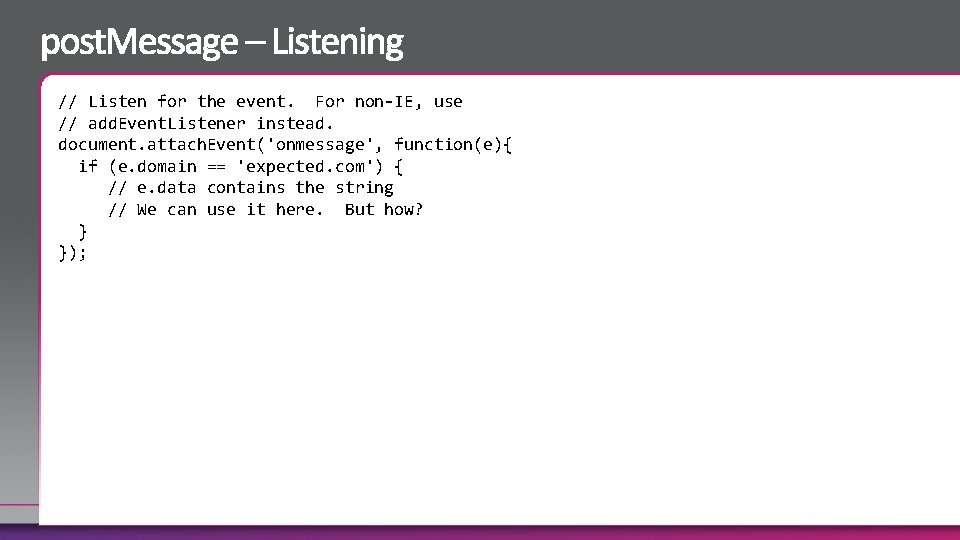
// Listen for the event. For non-IE, use // add. Event. Listener instead. document. attach. Event('onmessage', function(e){ if (e. domain == 'expected. com') { // e. data contains the string // We can use it here. But how? } });
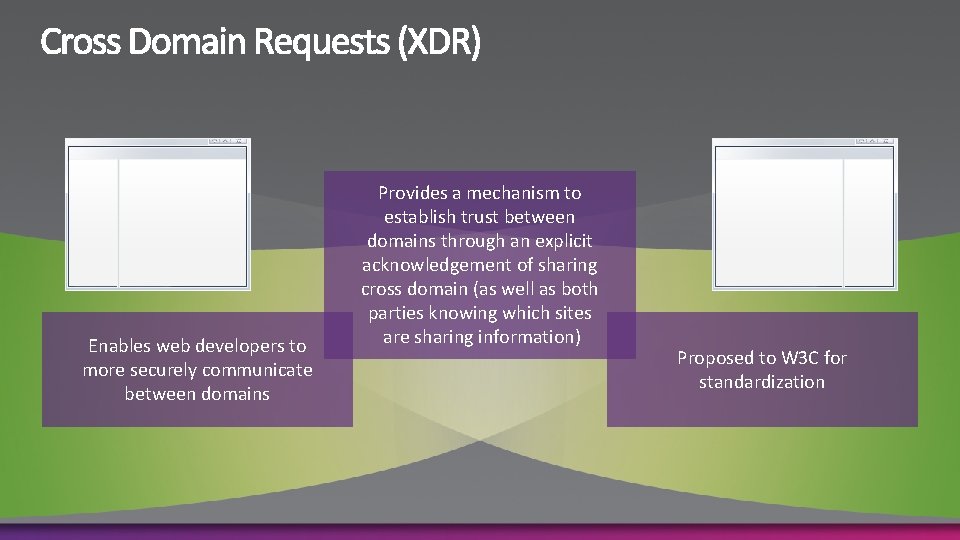
Enables web developers to more securely communicate between domains Provides a mechanism to establish trust between domains through an explicit acknowledgement of sharing cross domain (as well as both parties knowing which sites are sharing information) Proposed to W 3 C for standardization
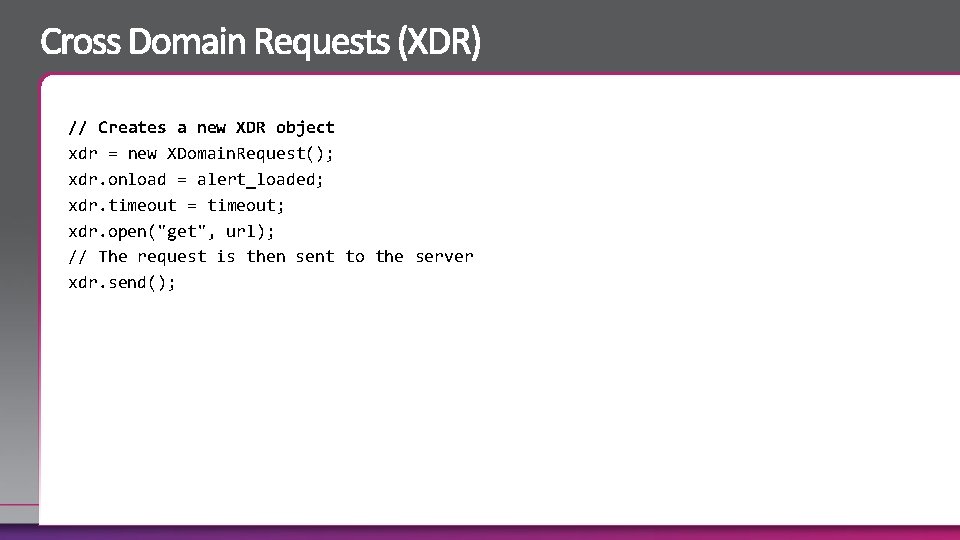
// Creates a new XDR object xdr = new XDomain. Request(); xdr. onload = alert_loaded; xdr. timeout = timeout; xdr. open("get", url); // The request is then sent to the server xdr. send();
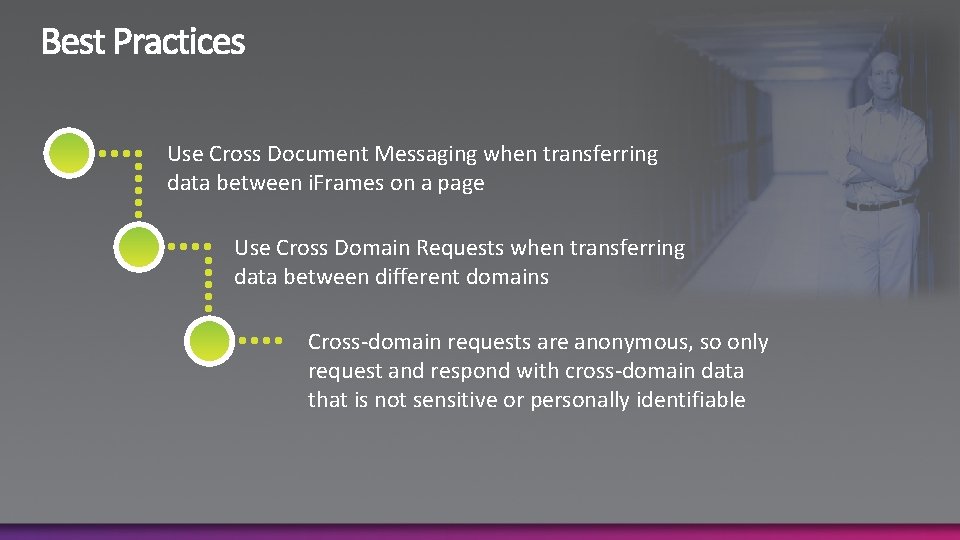
Use Cross Document Messaging when transferring data between i. Frames on a page Use Cross Domain Requests when transferring data between different domains Cross-domain requests are anonymous, so only request and respond with cross-domain data that is not sensitive or personally identifiable

Pete Le. Page plepage@microsoft. com Microsoft Corp http: //Pete. Le. Page. com Twitter: http: //twitter. com/petele
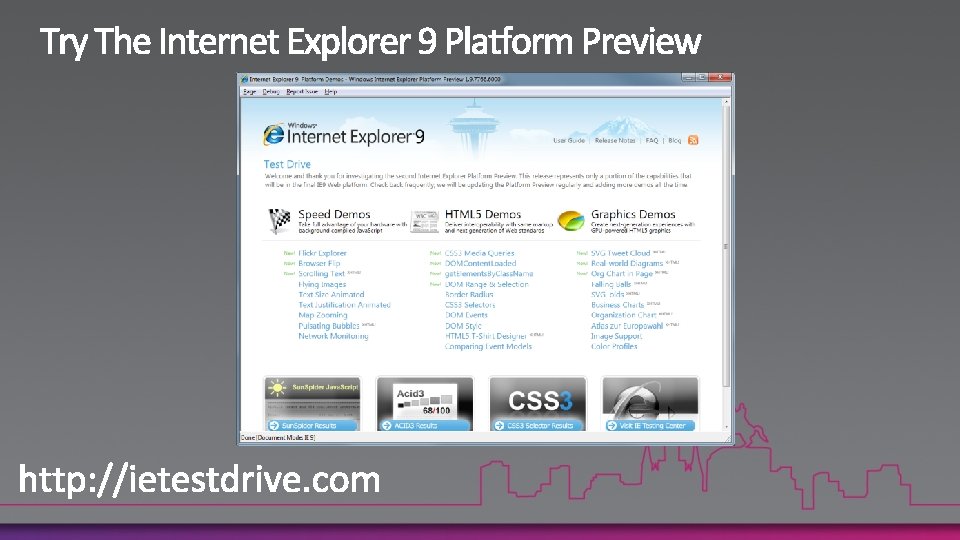
http: //www. asp. net/ http: //silverlight/ http: //www. microsoft. com/expression/ http: //www. microsoft. com/windows/internet-explorer/default. aspx
www. microsoft. com/teched www. microsoft. com/learning http: //microsoft. com/technet http: //microsoft. com/msdn
Sign up for Tech·Ed 2011 and save $500 starting June 8 – June 31 st http: //northamerica. msteched. com/registration You can also register at the North America 2011 kiosk located at registration Join us in Atlanta next year

- Slides: 71