Resource Allocation Distributed mutual exclusion Permissionbased Ricart Agrawala
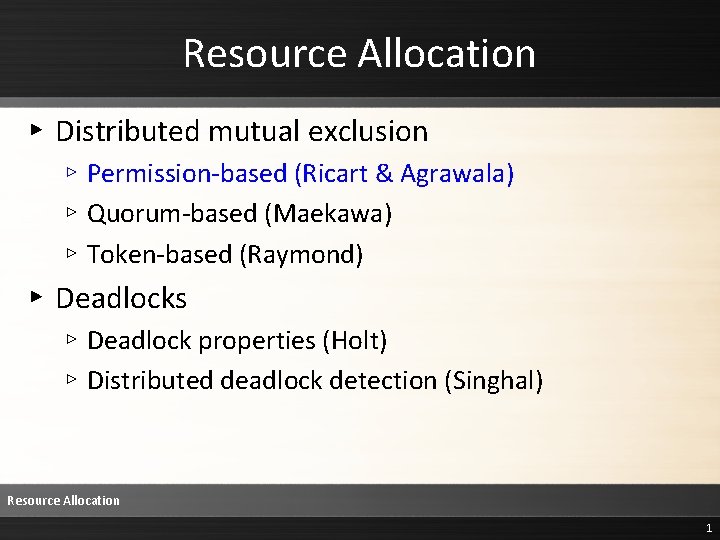
Resource Allocation ▸ Distributed mutual exclusion ▹ Permission-based (Ricart & Agrawala) ▹ Quorum-based (Maekawa) ▹ Token-based (Raymond) ▸ Deadlocks ▹ Deadlock properties (Holt) ▹ Distributed deadlock detection (Singhal) Resource Allocation 1
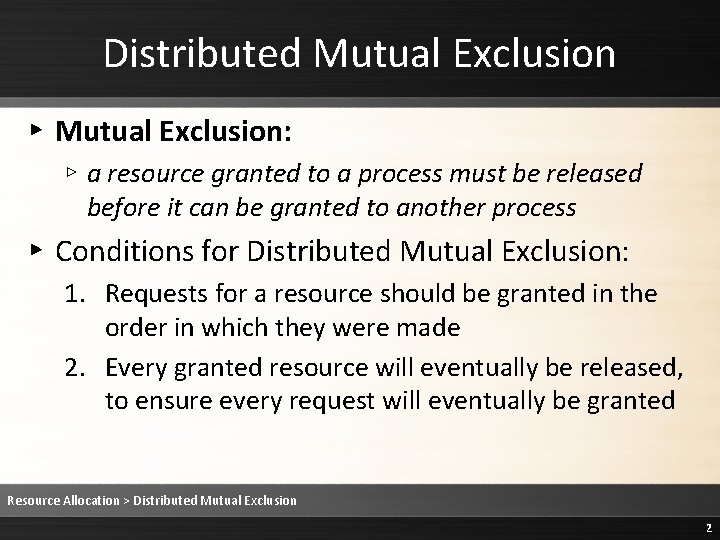
Distributed Mutual Exclusion ▸ Mutual Exclusion: ▹ a resource granted to a process must be released before it can be granted to another process ▸ Conditions for Distributed Mutual Exclusion: 1. Requests for a resource should be granted in the order in which they were made 2. Every granted resource will eventually be released, to ensure every request will eventually be granted Resource Allocation > Distributed Mutual Exclusion 2
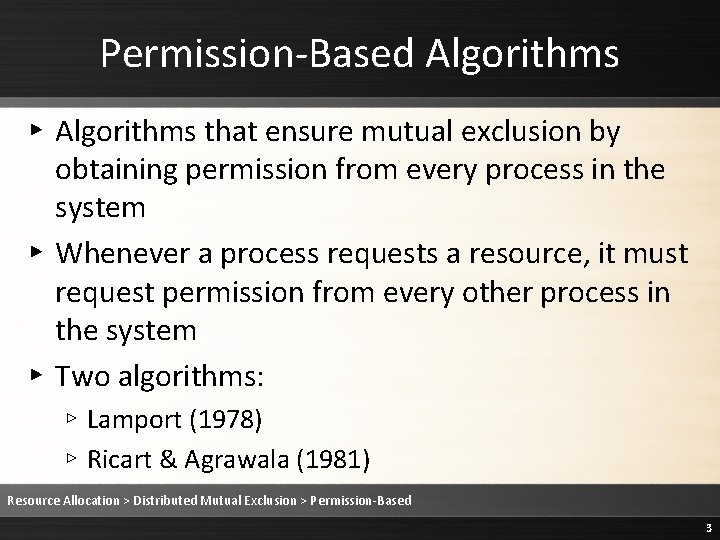
Permission-Based Algorithms ▸ Algorithms that ensure mutual exclusion by obtaining permission from every process in the system ▸ Whenever a process requests a resource, it must request permission from every other process in the system ▸ Two algorithms: ▹ Lamport (1978) ▹ Ricart & Agrawala (1981) Resource Allocation > Distributed Mutual Exclusion > Permission-Based 3
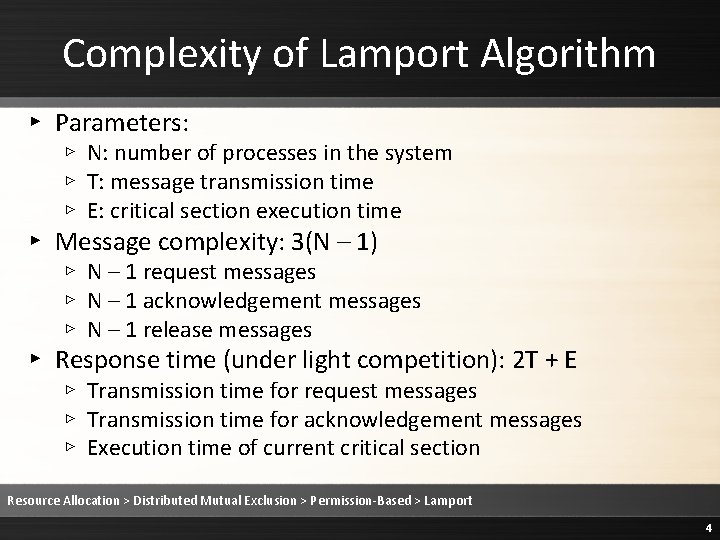
Complexity of Lamport Algorithm ▸ Parameters: ▹ N: number of processes in the system ▹ T: message transmission time ▹ E: critical section execution time ▸ Message complexity: 3(N – 1) ▹ N – 1 request messages ▹ N – 1 acknowledgement messages ▹ N – 1 release messages ▸ Response time (under light competition): 2 T + E ▹ Transmission time for request messages ▹ Transmission time for acknowledgement messages ▹ Execution time of current critical section Resource Allocation > Distributed Mutual Exclusion > Permission-Based > Lamport 4
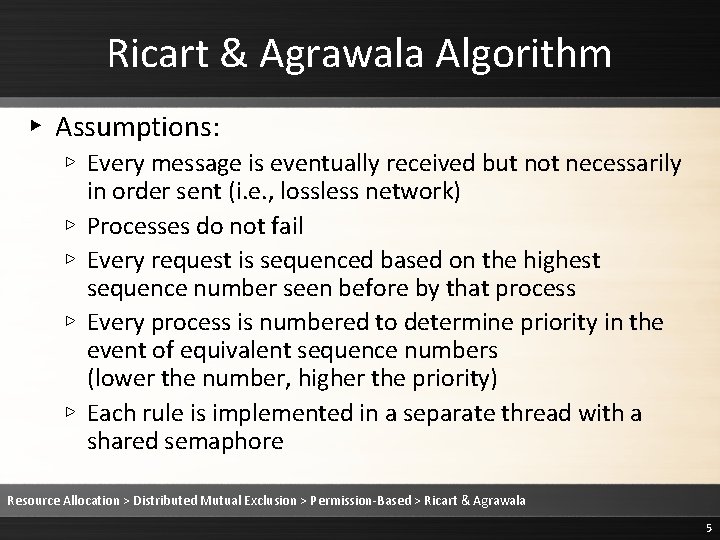
Ricart & Agrawala Algorithm ▸ Assumptions: ▹ Every message is eventually received but not necessarily in order sent (i. e. , lossless network) ▹ Processes do not fail ▹ Every request is sequenced based on the highest sequence number seen before by that process ▹ Every process is numbered to determine priority in the event of equivalent sequence numbers (lower the number, higher the priority) ▹ Each rule is implemented in a separate thread with a shared semaphore Resource Allocation > Distributed Mutual Exclusion > Permission-Based > Ricart & Agrawala 5
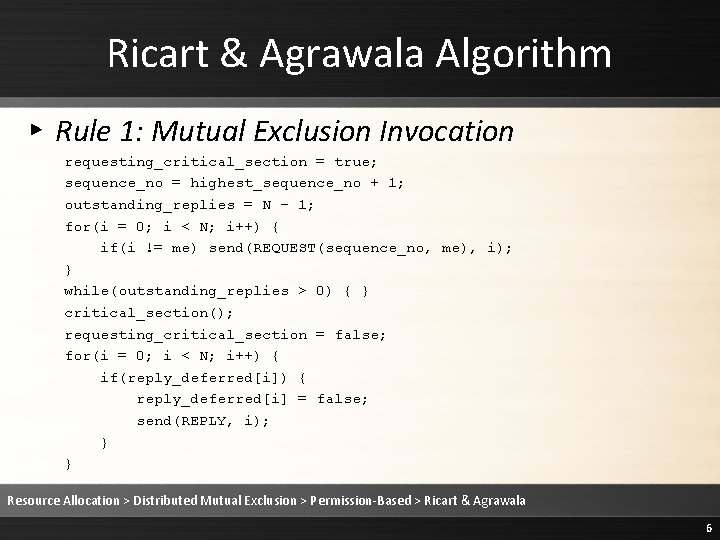
Ricart & Agrawala Algorithm ▸ Rule 1: Mutual Exclusion Invocation requesting_critical_section = true; sequence_no = highest_sequence_no + 1; outstanding_replies = N – 1; for(i = 0; i < N; i++) { if(i != me) send(REQUEST(sequence_no, me), i); } while(outstanding_replies > 0) { } critical_section(); requesting_critical_section = false; for(i = 0; i < N; i++) { if(reply_deferred[i]) { reply_deferred[i] = false; send(REPLY, i); } } Resource Allocation > Distributed Mutual Exclusion > Permission-Based > Ricart & Agrawala 6
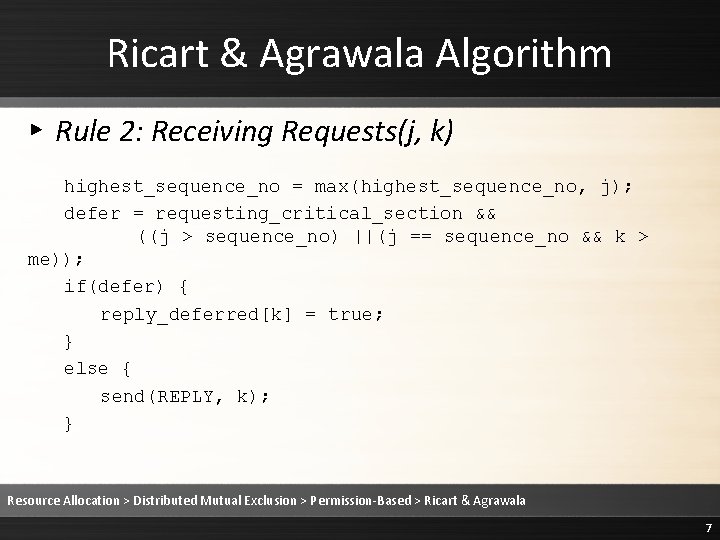
Ricart & Agrawala Algorithm ▸ Rule 2: Receiving Requests(j, k) highest_sequence_no = max(highest_sequence_no, j); defer = requesting_critical_section && ((j > sequence_no) ||(j == sequence_no && k > me)); if(defer) { reply_deferred[k] = true; } else { send(REPLY, k); } Resource Allocation > Distributed Mutual Exclusion > Permission-Based > Ricart & Agrawala 7
Ricart & Agrawala Algorithm ▸ Rule 3: Receiving Replies outstanding_replies--; Resource Allocation > Distributed Mutual Exclusion > Permission-Based > Ricart & Agrawala 8
Complexity of Ricart & Agrawala ▸ Message complexity: 2(N – 1) ▹ N – 1 request messages ▹ N – 1 reply messages ▸ Response time (under light competition): 2 T + E ▹ Transmission time for request messages ▹ Transmission time for reply messages ▹ Execution time of current critical section Resource Allocation > Distributed Mutual Exclusion > Permission-Based > Ricart & Agrawala 9
Deadlock and Starvation ▸ Deadlock: ▹ Occurs when no process in the system is in its critical section and no requesting process can ever proceed to its own critical section ▸ Starvation: ▹ Occurs when one process must wait indefinitely to enter its critical section even though other nodes are entering and exiting their own critical sections Resource Allocation > Distributed Mutual Exclusion > Permission-Based > Ricart & Agrawala 10
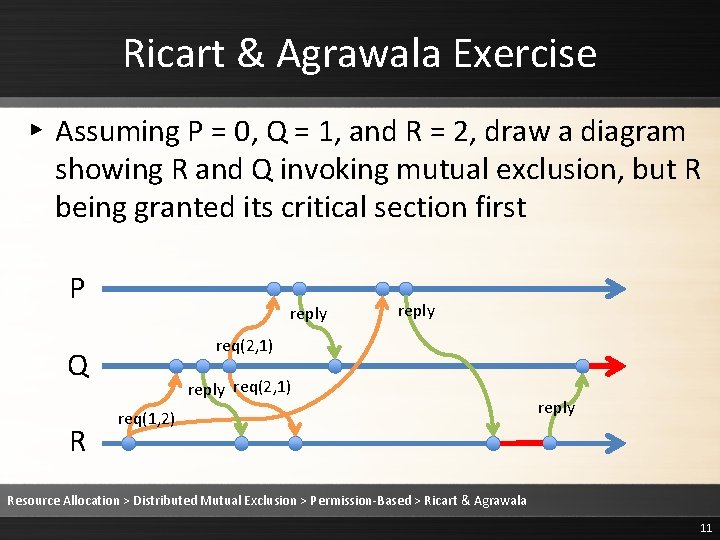
Ricart & Agrawala Exercise ▸ Assuming P = 0, Q = 1, and R = 2, draw a diagram showing R and Q invoking mutual exclusion, but R being granted its critical section first P reply req(2, 1) Q R reply req(2, 1) req(1, 2) reply Resource Allocation > Distributed Mutual Exclusion > Permission-Based > Ricart & Agrawala 11
Resource Allocation ▸ Distributed mutual exclusion ▹ Permission-based (Ricart & Agrawala) ▹ Quorum-based (Maekawa) ▹ Token-based (Raymond) ▸ Deadlocks ▹ Deadlock properties (Holt) ▹ Distributed deadlock detection (Singhal) Resource Allocation 12
Distributed Mutual Exclusion: Quorum-based Algorithms CS/CE/TE 6378 Advanced Operating Systems
Quorum-Based Algorithms ▸ Algorithms that ensure mutual exclusion by obtaining permission from every member of a minimum set of processes (i. e. , a quorum) ▸ Whenever a process requests a resource, it must request permission from every process in its quorum ▸ To avoid violation of mutual exclusion, quorums must adhere to the non-null intersection property Resource Allocation > Distributed Mutual Exclusion > Quorum-Based 14
Non-Null Intersection Property ▸ For any combination of i and j, 1 ≤ i, j ≤ N, Si ∩ S j ≠ Ø ▸ For any pair of processes, their quorums must share at least one member ▸ Two creation methods on order of √N ▹ Projective planes ▹ Square grid Resource Allocation > Distributed Mutual Exclusion > Quorum-Based 15
Quiz Question ▸ Which of the following quorum assignments violates the non-null intersection property? ▹ S 1 = {1, 2} S 2 = {2, 3} S 3 = {3} ▹ S 1 = {1, 2} S 2 = {2, 3} S 3 = {1, 3} ▹ S 1 = {2, 3} S 2 = {1, 3} S 3 = {1, 2} ▹ S 1 = {1, 2, 3} S 2 = {1, 2, 3} S 3 = {1, 2, 3} Resource Allocation > Distributed Mutual Exclusion > Quorum-Based 16
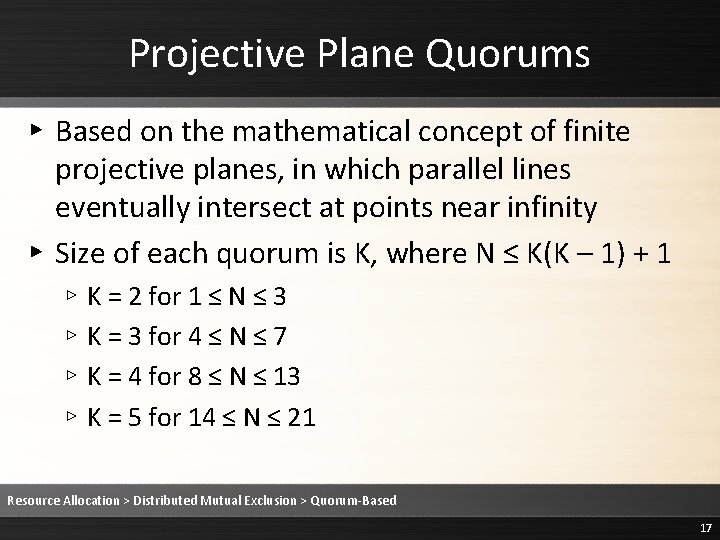
Projective Plane Quorums ▸ Based on the mathematical concept of finite projective planes, in which parallel lines eventually intersect at points near infinity ▸ Size of each quorum is K, where N ≤ K(K – 1) + 1 ▹ K = 2 for 1 ≤ N ≤ 3 ▹ K = 3 for 4 ≤ N ≤ 7 ▹ K = 4 for 8 ≤ N ≤ 13 ▹ K = 5 for 14 ≤ N ≤ 21 Resource Allocation > Distributed Mutual Exclusion > Quorum-Based 17
Projective Plane Example ▸ N = 6, hence K = 3 1 2 3 4 5 6 Resource Allocation > Distributed Mutual Exclusion > Quorum-Based 18
Projective Plane Example ▸ N = 6, hence K = 3 1 2 3 4 5 6 ▸ First, every process should be a member of its own quorum Resource Allocation > Distributed Mutual Exclusion > Quorum-Based 19
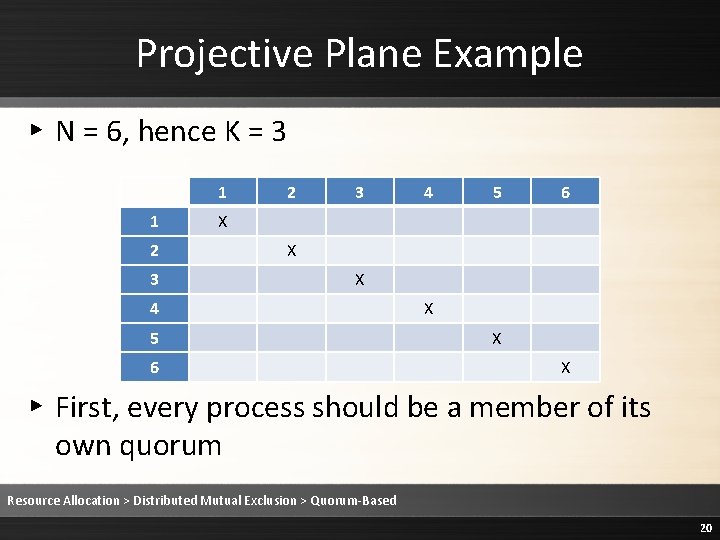
Projective Plane Example ▸ N = 6, hence K = 3 1 1 2 3 4 5 6 X X X ▸ First, every process should be a member of its own quorum Resource Allocation > Distributed Mutual Exclusion > Quorum-Based 20
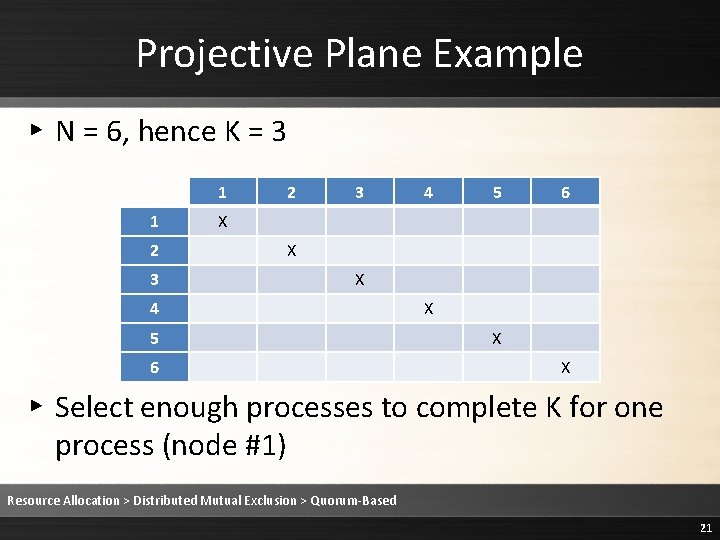
Projective Plane Example ▸ N = 6, hence K = 3 1 1 2 3 4 5 6 X X X ▸ Select enough processes to complete K for one process (node #1) Resource Allocation > Distributed Mutual Exclusion > Quorum-Based 21
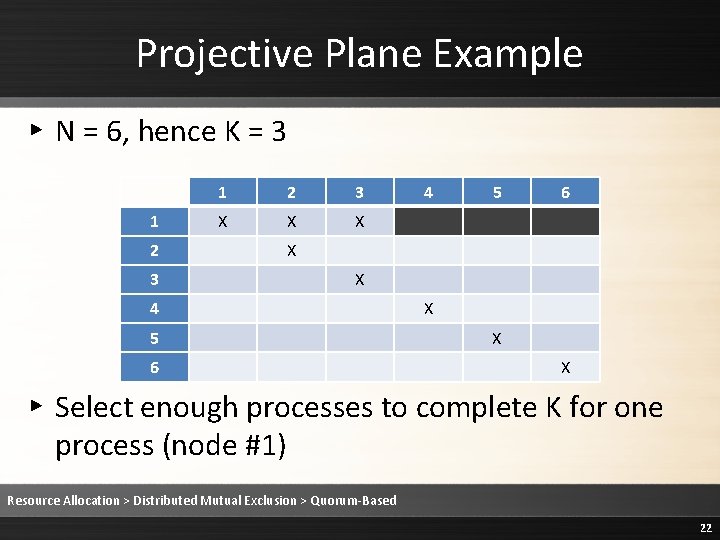
Projective Plane Example ▸ N = 6, hence K = 3 1 2 3 X X X 4 5 6 X X X ▸ Select enough processes to complete K for one process (node #1) Resource Allocation > Distributed Mutual Exclusion > Quorum-Based 22
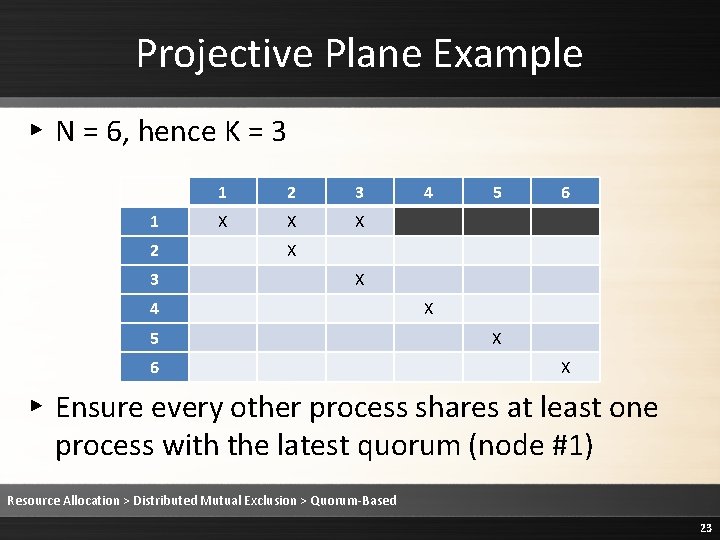
Projective Plane Example ▸ N = 6, hence K = 3 1 2 3 X X X 4 5 6 X X X ▸ Ensure every other process shares at least one process with the latest quorum (node #1) Resource Allocation > Distributed Mutual Exclusion > Quorum-Based 23
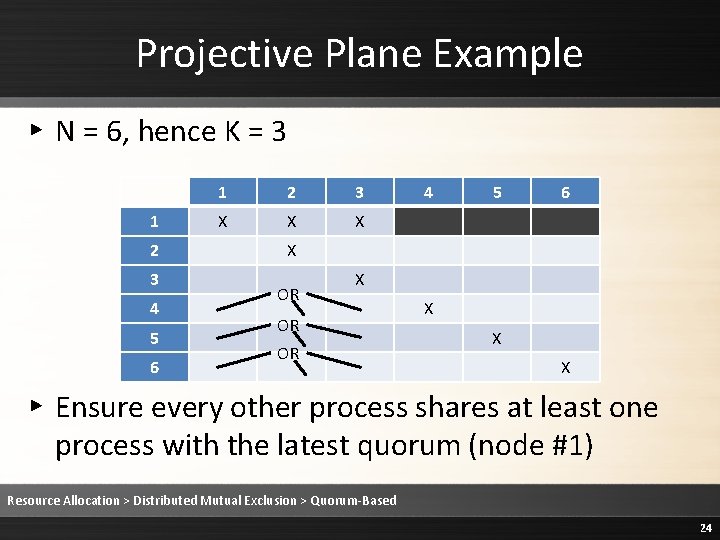
Projective Plane Example ▸ N = 6, hence K = 3 1 2 3 4 5 6 1 2 3 X X X 4 5 6 X OR OR X X X ▸ Ensure every other process shares at least one process with the latest quorum (node #1) Resource Allocation > Distributed Mutual Exclusion > Quorum-Based 24
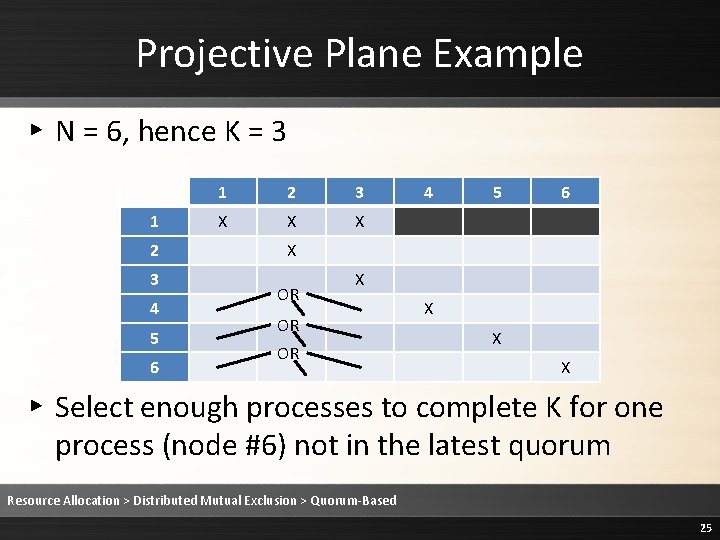
Projective Plane Example ▸ N = 6, hence K = 3 1 2 3 4 5 6 1 2 3 X X X 4 5 6 X OR OR X X X ▸ Select enough processes to complete K for one process (node #6) not in the latest quorum Resource Allocation > Distributed Mutual Exclusion > Quorum-Based 25
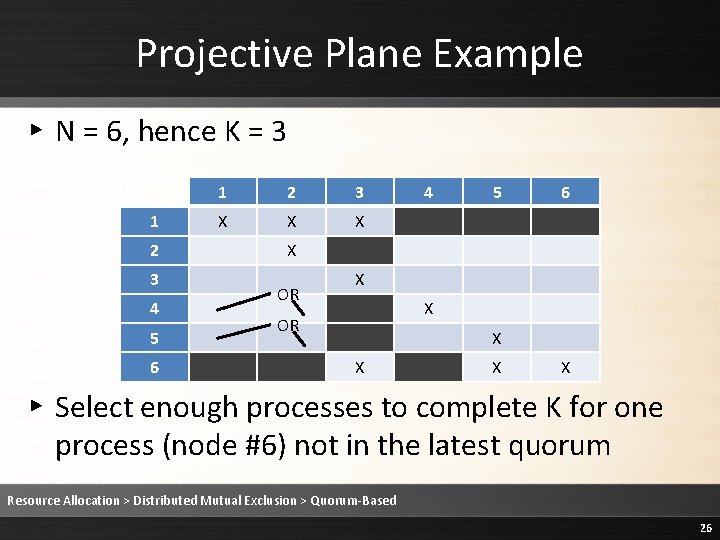
Projective Plane Example ▸ N = 6, hence K = 3 1 2 3 4 5 6 1 2 3 X X X 4 5 6 X OR X X X X ▸ Select enough processes to complete K for one process (node #6) not in the latest quorum Resource Allocation > Distributed Mutual Exclusion > Quorum-Based 26
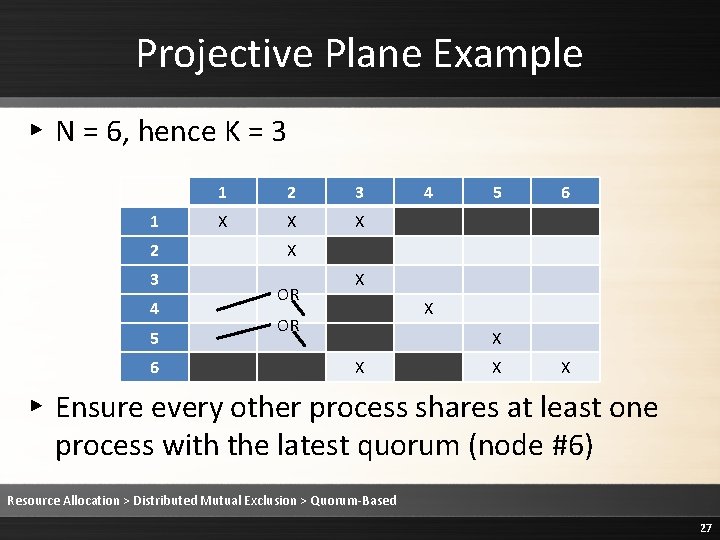
Projective Plane Example ▸ N = 6, hence K = 3 1 2 3 4 5 6 1 2 3 X X X 4 5 6 X OR X X X X ▸ Ensure every other process shares at least one process with the latest quorum (node #6) Resource Allocation > Distributed Mutual Exclusion > Quorum-Based 27
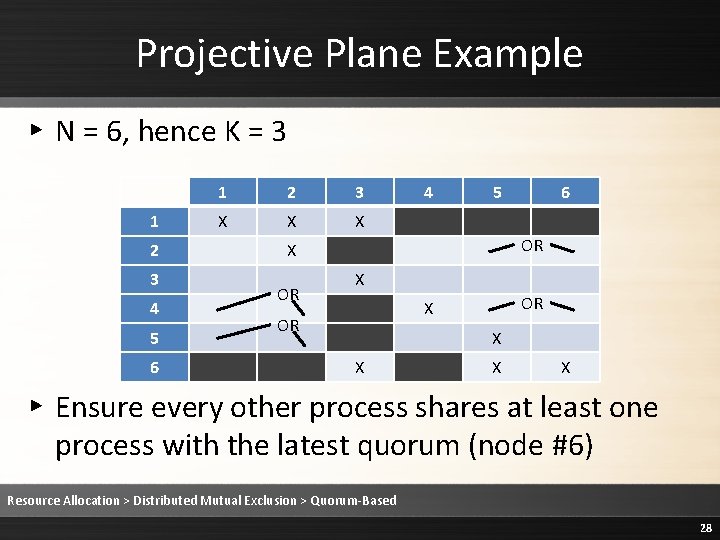
Projective Plane Example ▸ N = 6, hence K = 3 1 2 3 4 5 6 1 2 3 X X X 4 5 OR X OR 6 X OR X X ▸ Ensure every other process shares at least one process with the latest quorum (node #6) Resource Allocation > Distributed Mutual Exclusion > Quorum-Based 28
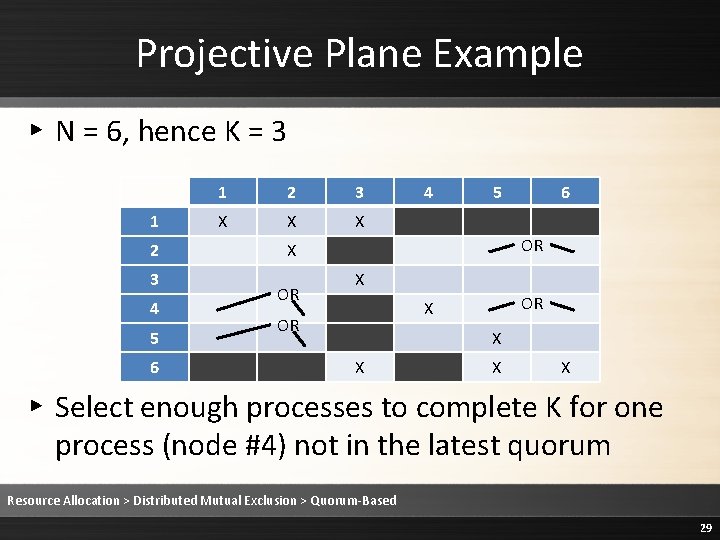
Projective Plane Example ▸ N = 6, hence K = 3 1 2 3 4 5 6 1 2 3 X X X 4 5 OR X OR 6 X OR X X ▸ Select enough processes to complete K for one process (node #4) not in the latest quorum Resource Allocation > Distributed Mutual Exclusion > Quorum-Based 29
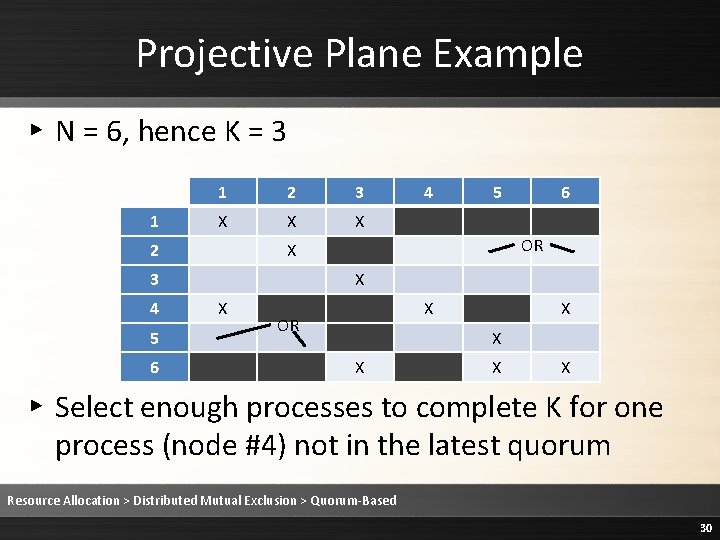
Projective Plane Example ▸ N = 6, hence K = 3 1 1 2 3 X X X 2 5 6 OR X 3 4 4 X X X OR X X X ▸ Select enough processes to complete K for one process (node #4) not in the latest quorum Resource Allocation > Distributed Mutual Exclusion > Quorum-Based 30
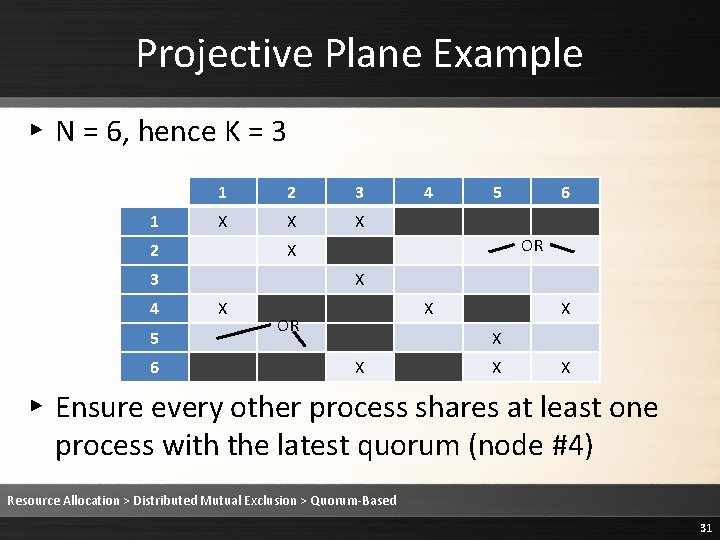
Projective Plane Example ▸ N = 6, hence K = 3 1 1 2 3 X X X 2 5 6 OR X 3 4 4 X X X OR X X X ▸ Ensure every other process shares at least one process with the latest quorum (node #4) Resource Allocation > Distributed Mutual Exclusion > Quorum-Based 31
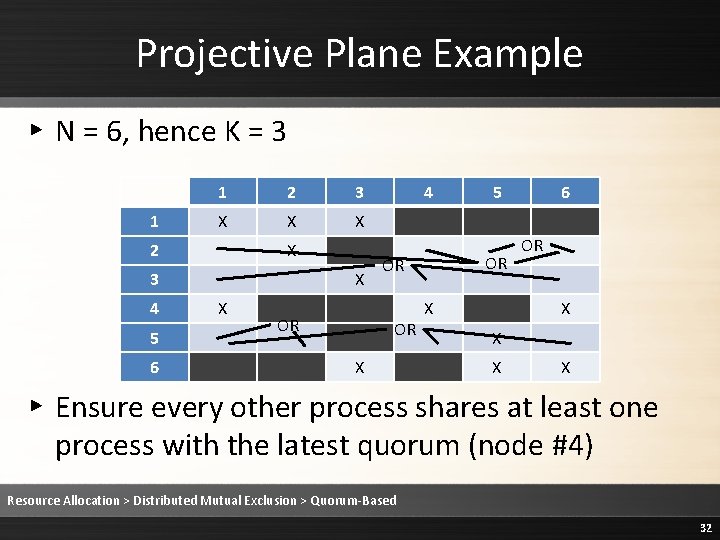
Projective Plane Example ▸ N = 6, hence K = 3 1 1 2 3 X X X 2 X 3 4 5 6 X X OR 4 OR OR OR X 5 X 6 OR X X ▸ Ensure every other process shares at least one process with the latest quorum (node #4) Resource Allocation > Distributed Mutual Exclusion > Quorum-Based 32
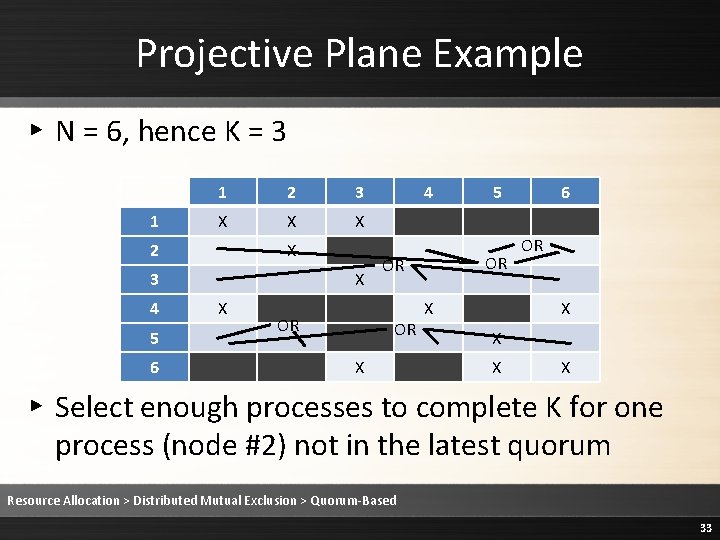
Projective Plane Example ▸ N = 6, hence K = 3 1 1 2 3 X X X 2 X 3 4 5 6 X X OR 4 OR OR OR X 5 X 6 OR X X ▸ Select enough processes to complete K for one process (node #2) not in the latest quorum Resource Allocation > Distributed Mutual Exclusion > Quorum-Based 33
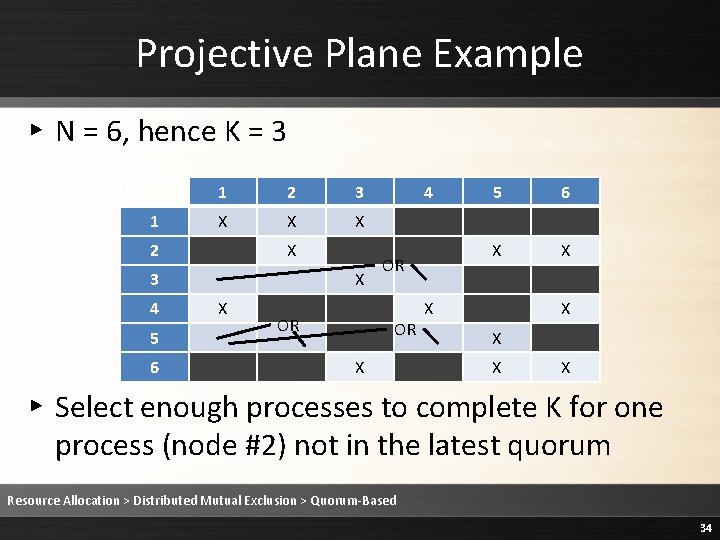
Projective Plane Example ▸ N = 6, hence K = 3 1 1 2 3 X X X 2 X 3 4 5 6 X X OR 4 OR OR X 5 6 X X X X ▸ Select enough processes to complete K for one process (node #2) not in the latest quorum Resource Allocation > Distributed Mutual Exclusion > Quorum-Based 34
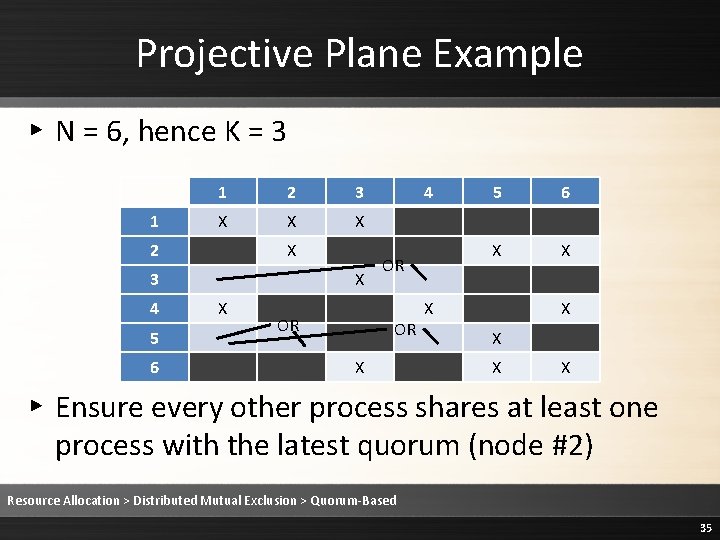
Projective Plane Example ▸ N = 6, hence K = 3 1 1 2 3 X X X 2 X 3 4 5 6 X X OR 4 OR OR X 5 6 X X X X ▸ Ensure every other process shares at least one process with the latest quorum (node #2) Resource Allocation > Distributed Mutual Exclusion > Quorum-Based 35
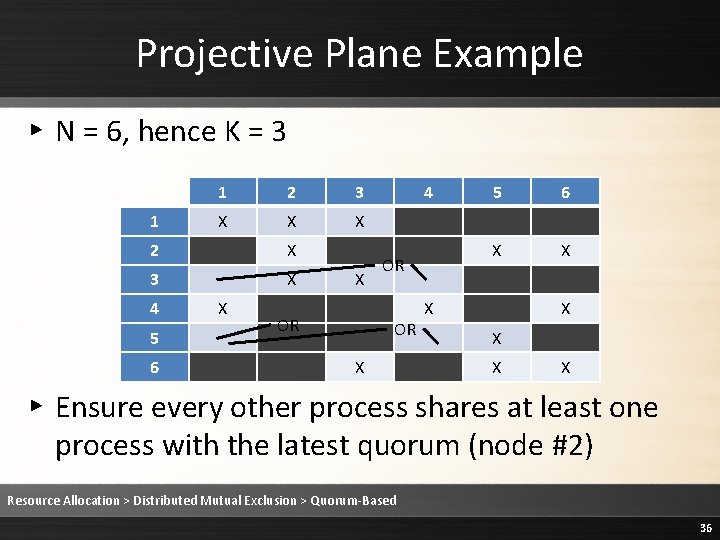
Projective Plane Example ▸ N = 6, hence K = 3 1 1 2 3 X X X 2 X 3 X 4 5 6 X X OR 4 OR OR X 5 6 X X X X ▸ Ensure every other process shares at least one process with the latest quorum (node #2) Resource Allocation > Distributed Mutual Exclusion > Quorum-Based 36
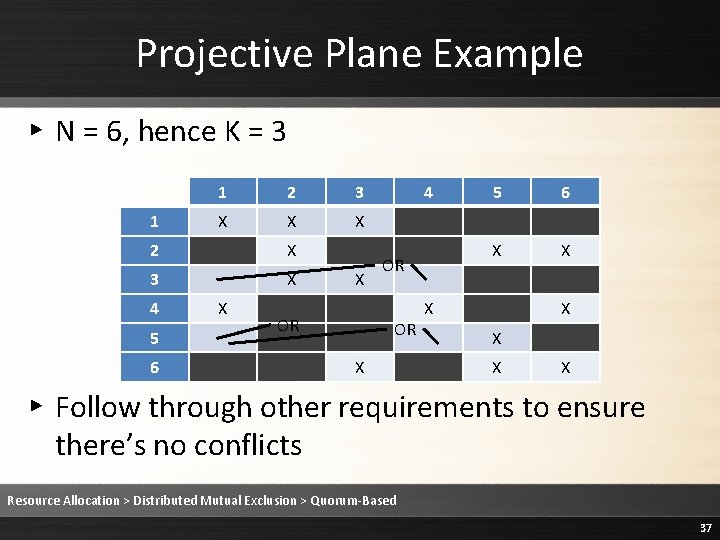
Projective Plane Example ▸ N = 6, hence K = 3 1 1 2 3 X X X 2 X 3 X 4 5 6 X X OR 4 OR OR X 5 6 X X X X ▸ Follow through other requirements to ensure there’s no conflicts Resource Allocation > Distributed Mutual Exclusion > Quorum-Based 37
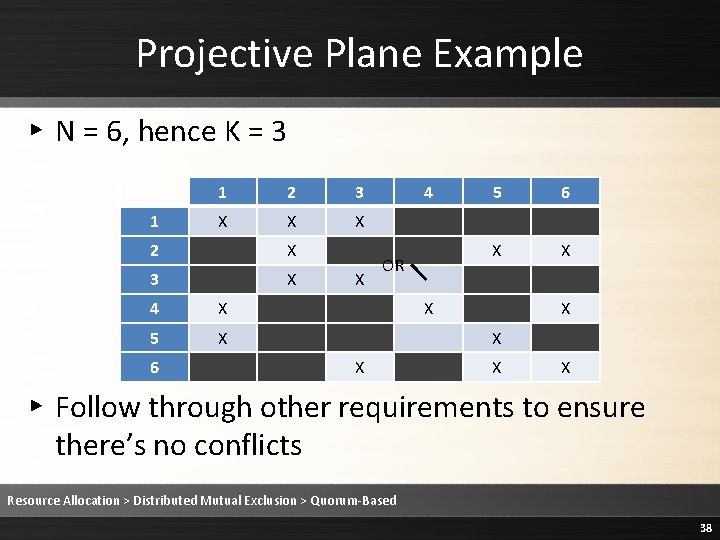
Projective Plane Example ▸ N = 6, hence K = 3 1 1 2 3 X X X 2 X 3 X 4 X 5 X 6 X 4 OR 5 6 X X X X ▸ Follow through other requirements to ensure there’s no conflicts Resource Allocation > Distributed Mutual Exclusion > Quorum-Based 38
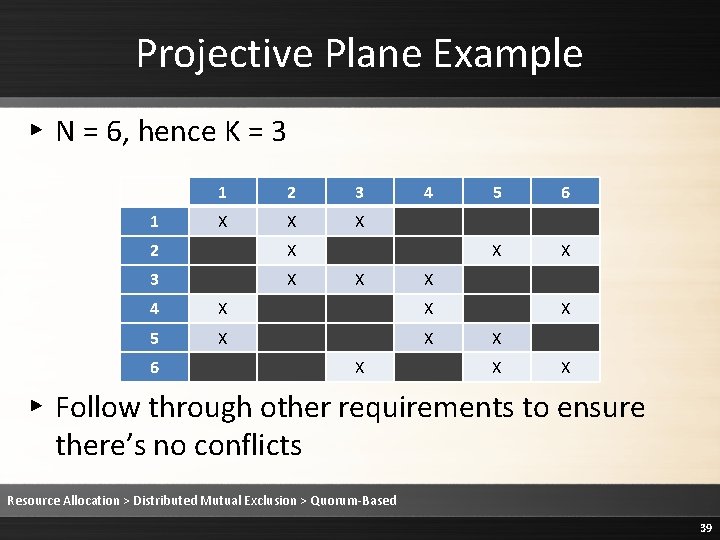
Projective Plane Example ▸ N = 6, hence K = 3 1 1 2 3 X X X 2 X 3 X X 4 X X 5 X X X 6 X X X 4 6 5 X X ▸ Follow through other requirements to ensure there’s no conflicts Resource Allocation > Distributed Mutual Exclusion > Quorum-Based 39
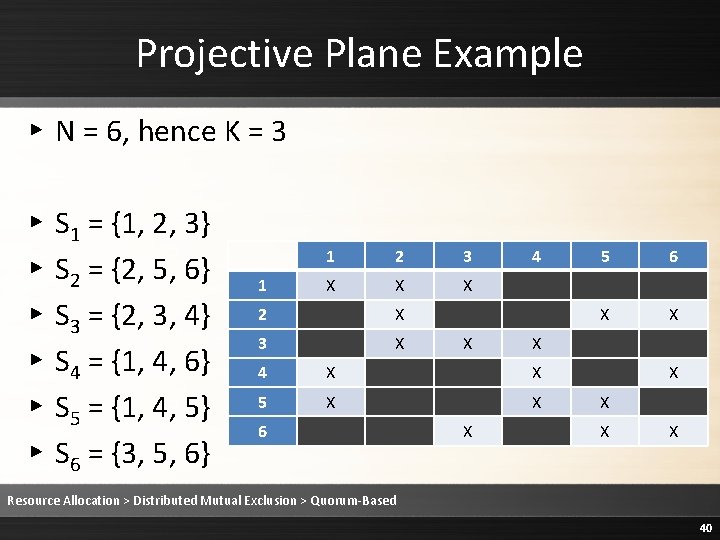
Projective Plane Example ▸ N = 6, hence K = 3 ▸ ▸ ▸ S 1 = {1, 2, 3} S 2 = {2, 5, 6} S 3 = {2, 3, 4} S 4 = {1, 4, 6} S 5 = {1, 4, 5} S 6 = {3, 5, 6} 1 1 2 3 X X X 2 X 3 X X 4 X X 5 X X X 6 X X X 4 6 5 X X Resource Allocation > Distributed Mutual Exclusion > Quorum-Based 40
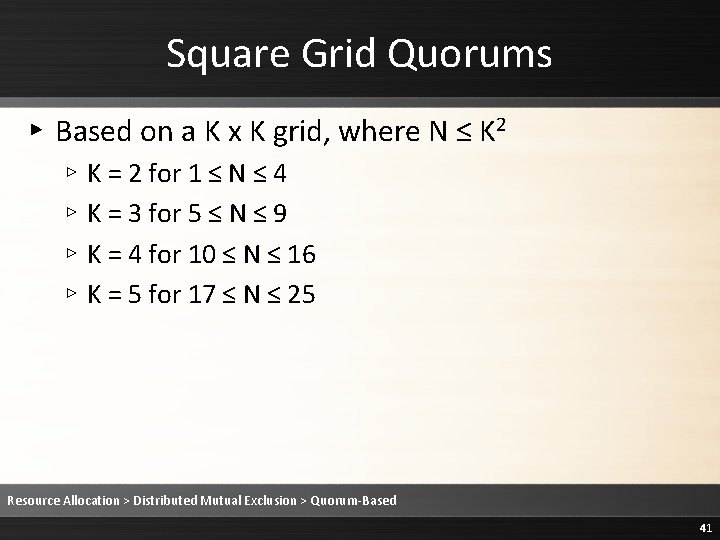
Square Grid Quorums ▸ Based on a K x K grid, where N ≤ K 2 ▹ K = 2 for 1 ≤ N ≤ 4 ▹ K = 3 for 5 ≤ N ≤ 9 ▹ K = 4 for 10 ≤ N ≤ 16 ▹ K = 5 for 17 ≤ N ≤ 25 Resource Allocation > Distributed Mutual Exclusion > Quorum-Based 41
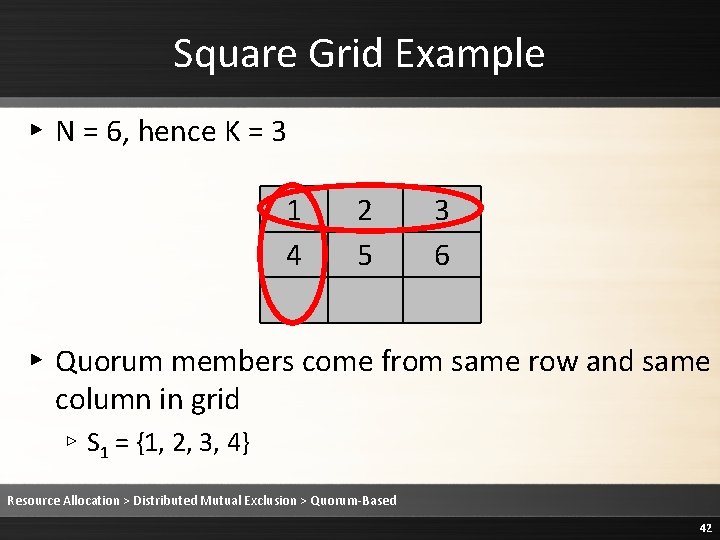
Square Grid Example ▸ N = 6, hence K = 3 1 4 2 5 3 6 ▸ Quorum members come from same row and same column in grid ▹ S 1 = {1, 2, 3, 4} Resource Allocation > Distributed Mutual Exclusion > Quorum-Based 42
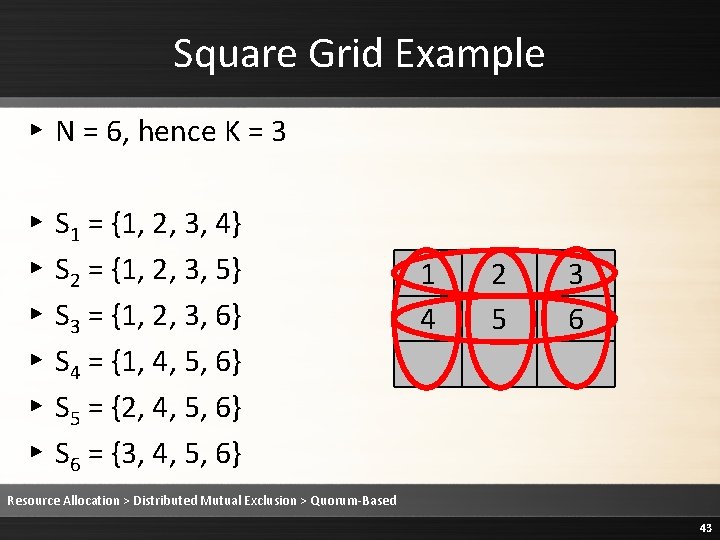
Square Grid Example ▸ N = 6, hence K = 3 ▸ ▸ ▸ S 1 = {1, 2, 3, 4} S 2 = {1, 2, 3, 5} S 3 = {1, 2, 3, 6} S 4 = {1, 4, 5, 6} S 5 = {2, 4, 5, 6} S 6 = {3, 4, 5, 6} 1 4 2 5 3 6 Resource Allocation > Distributed Mutual Exclusion > Quorum-Based 43
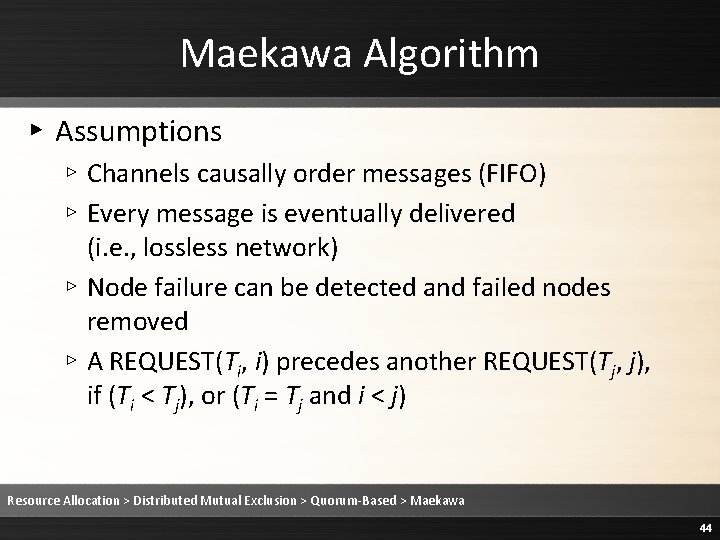
Maekawa Algorithm ▸ Assumptions ▹ Channels causally order messages (FIFO) ▹ Every message is eventually delivered (i. e. , lossless network) ▹ Node failure can be detected and failed nodes removed ▹ A REQUEST(Ti, i) precedes another REQUEST(Tj, j), if (Ti < Tj), or (Ti = Tj and i < j) Resource Allocation > Distributed Mutual Exclusion > Quorum-Based > Maekawa 44
Maekawa Algorithm ▸ Rule 1 When process i invokes mutual exclusion, it sends a REQUEST(TS, i) message to all processes in its quorum Si, where Ts is greater than any timestamp received by process i. Resource Allocation > Distributed Mutual Exclusion > Quorum-Based > Maekawa 45
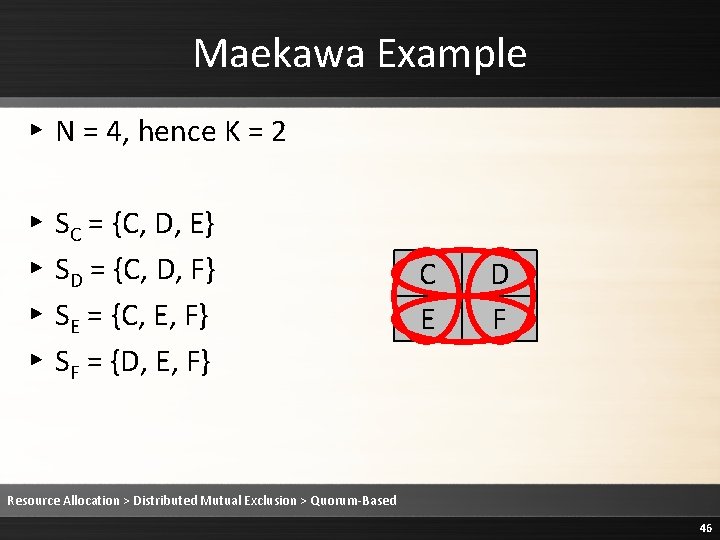
Maekawa Example ▸ N = 4, hence K = 2 ▸ ▸ SC = {C, D, E} SD = {C, D, F} SE = {C, E, F} SF = {D, E, F} C E D F Resource Allocation > Distributed Mutual Exclusion > Quorum-Based 46
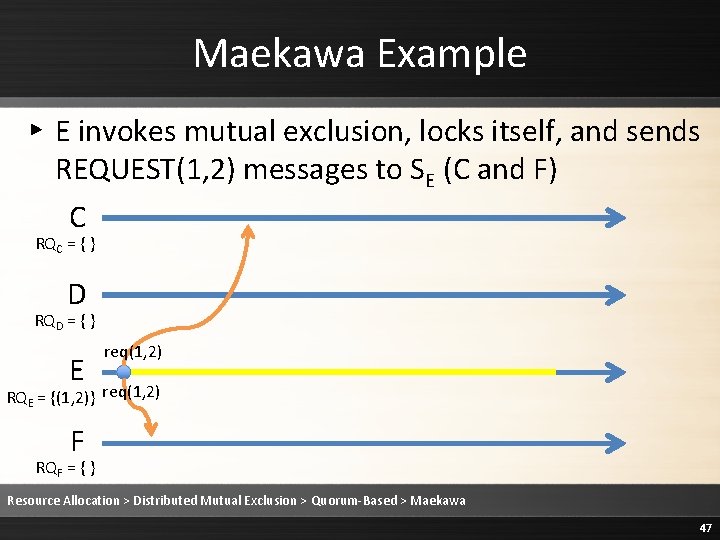
Maekawa Example ▸ E invokes mutual exclusion, locks itself, and sends REQUEST(1, 2) messages to SE (C and F) C RQC = { } D RQD = { } E req(1, 2) RQE = {(1, 2)} req(1, 2) F RQF = { } Resource Allocation > Distributed Mutual Exclusion > Quorum-Based > Maekawa 47
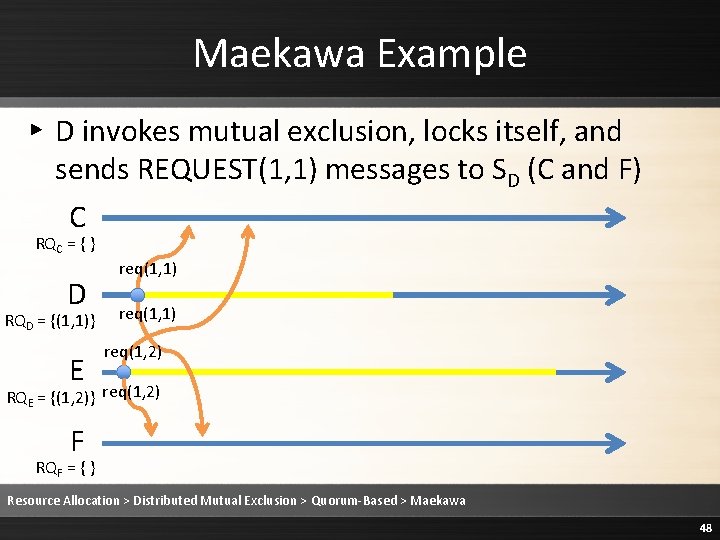
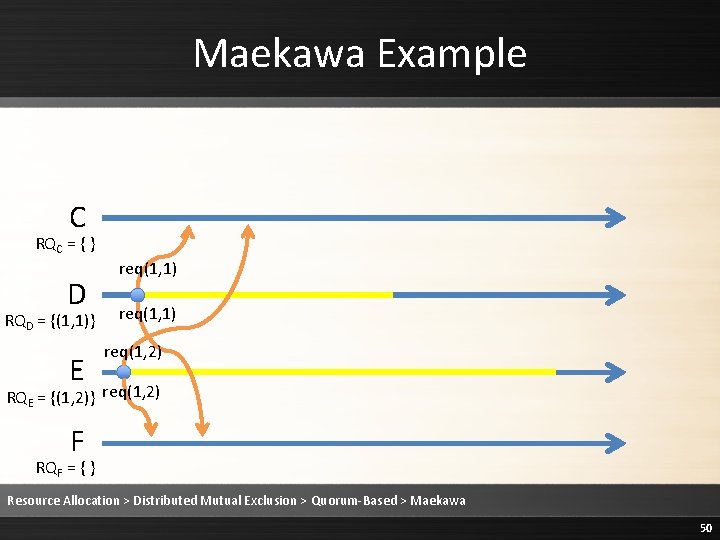
Maekawa Example ▸ D invokes mutual exclusion, locks itself, and sends REQUEST(1, 1) messages to SD (C and F) C RQC = { } D RQD = {(1, 1)} E req(1, 1) req(1, 2) RQE = {(1, 2)} req(1, 2) F RQF = { } Resource Allocation > Distributed Mutual Exclusion > Quorum-Based > Maekawa 48
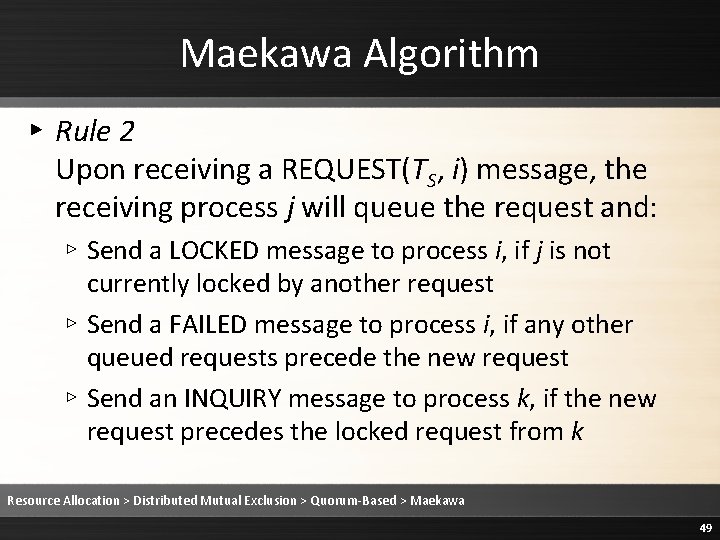
Maekawa Algorithm ▸ Rule 2 Upon receiving a REQUEST(TS, i) message, the receiving process j will queue the request and: ▹ Send a LOCKED message to process i, if j is not currently locked by another request ▹ Send a FAILED message to process i, if any other queued requests precede the new request ▹ Send an INQUIRY message to process k, if the new request precedes the locked request from k Resource Allocation > Distributed Mutual Exclusion > Quorum-Based > Maekawa 49
Maekawa Example C RQC = { } D RQD = {(1, 1)} E req(1, 1) req(1, 2) RQE = {(1, 2)} req(1, 2) F RQF = { } Resource Allocation > Distributed Mutual Exclusion > Quorum-Based > Maekawa 50
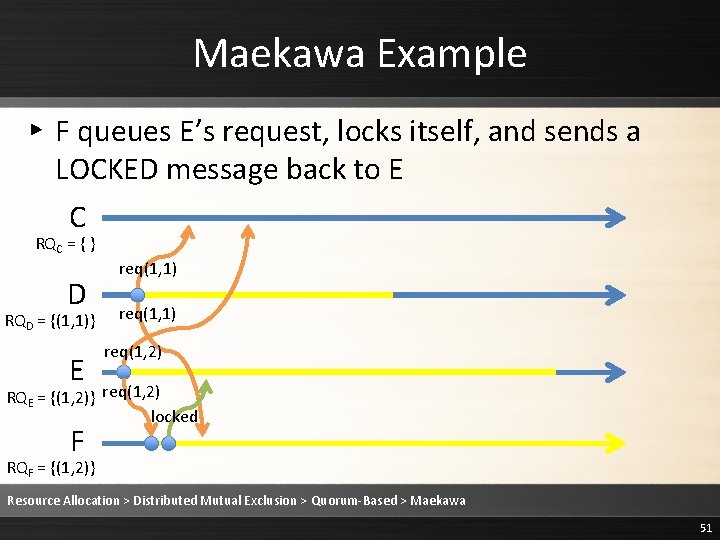
Maekawa Example ▸ F queues E’s request, locks itself, and sends a LOCKED message back to E C RQC = { } D RQD = {(1, 1)} E req(1, 1) req(1, 2) RQE = {(1, 2)} req(1, 2) locked F RQF = {(1, 2)} Resource Allocation > Distributed Mutual Exclusion > Quorum-Based > Maekawa 51
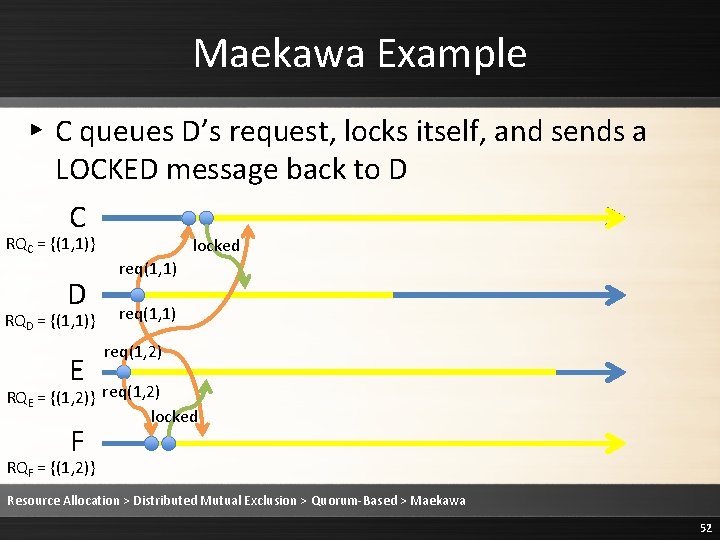
Maekawa Example ▸ C queues D’s request, locks itself, and sends a LOCKED message back to D C RQC = {(1, 1)} D RQD = {(1, 1)} E locked req(1, 1) req(1, 2) RQE = {(1, 2)} req(1, 2) locked F RQF = {(1, 2)} Resource Allocation > Distributed Mutual Exclusion > Quorum-Based > Maekawa 52
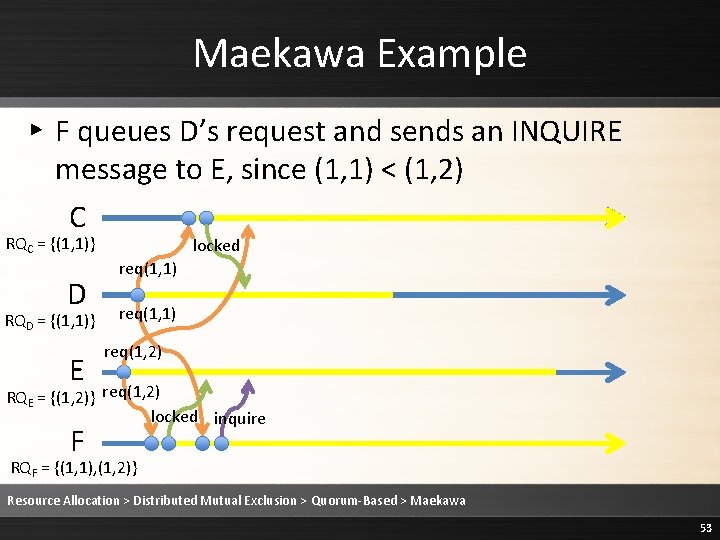
Maekawa Example ▸ F queues D’s request and sends an INQUIRE message to E, since (1, 1) < (1, 2) C RQC = {(1, 1)} D RQD = {(1, 1)} E locked req(1, 1) req(1, 2) RQE = {(1, 2)} req(1, 2) locked inquire F RQF = {(1, 1), (1, 2)} Resource Allocation > Distributed Mutual Exclusion > Quorum-Based > Maekawa 53
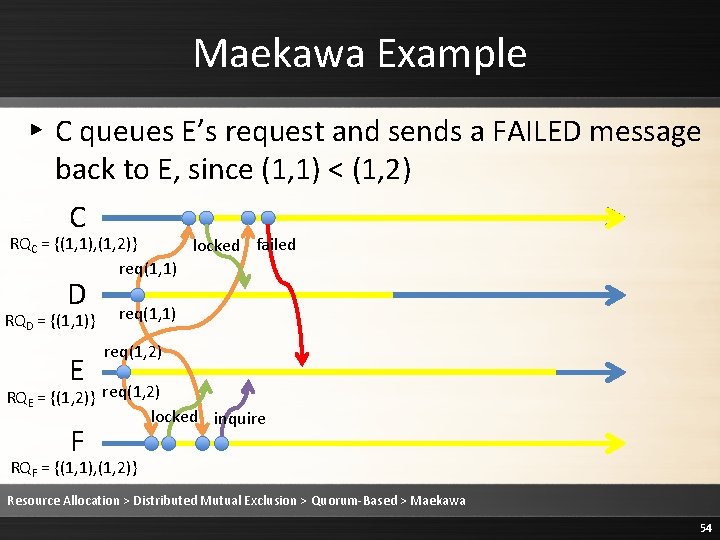
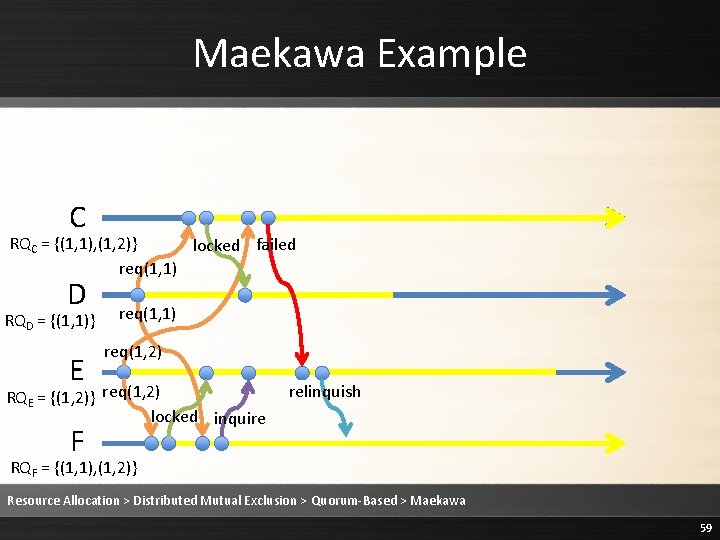
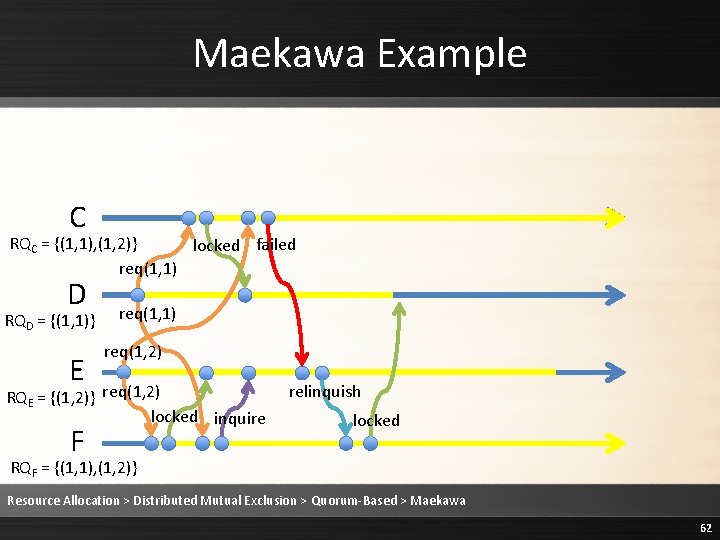
Maekawa Example ▸ C queues E’s request and sends a FAILED message back to E, since (1, 1) < (1, 2) C RQC = {(1, 1), (1, 2)} locked failed req(1, 1) D RQD = {(1, 1)} E req(1, 1) req(1, 2) RQE = {(1, 2)} req(1, 2) locked inquire F RQF = {(1, 1), (1, 2)} Resource Allocation > Distributed Mutual Exclusion > Quorum-Based > Maekawa 54

Maekawa Algorithm ▸ Rule 3 Upon receiving an INQUIRE message, the receiving process i will return a RELINQUISH message if it has received or will ever receive a FAILED message. Resource Allocation > Distributed Mutual Exclusion > Quorum-Based > Maekawa 55
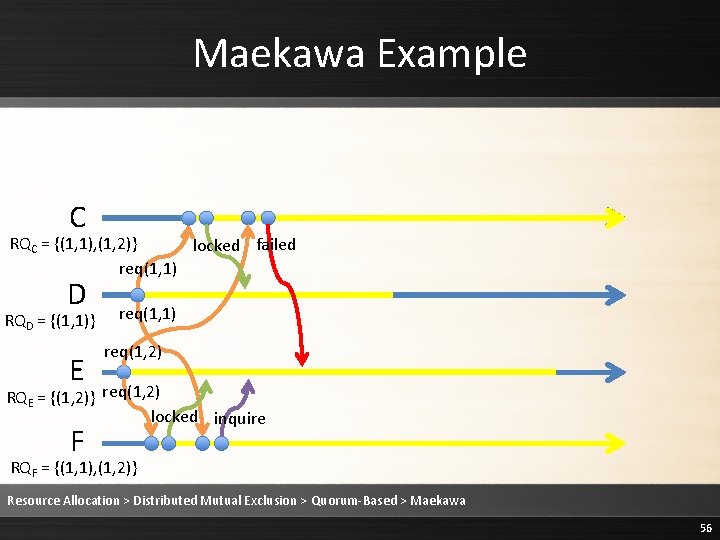
Maekawa Example C RQC = {(1, 1), (1, 2)} locked failed req(1, 1) D RQD = {(1, 1)} E req(1, 1) req(1, 2) RQE = {(1, 2)} req(1, 2) locked inquire F RQF = {(1, 1), (1, 2)} Resource Allocation > Distributed Mutual Exclusion > Quorum-Based > Maekawa 56
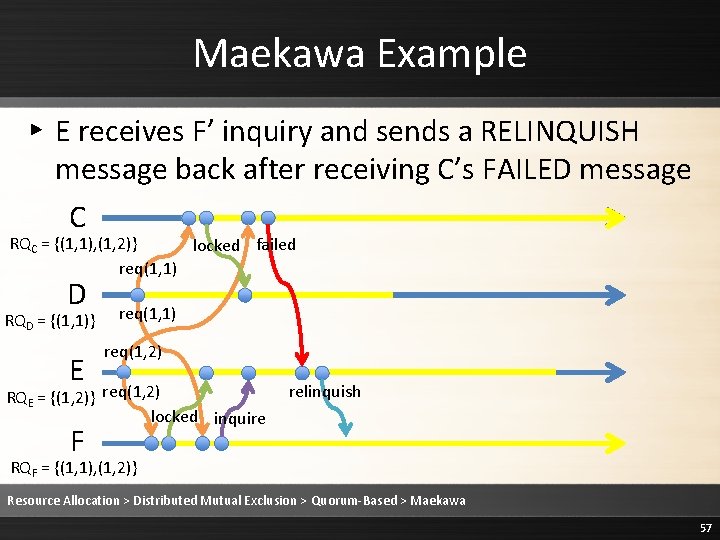
Maekawa Example ▸ E receives F’ inquiry and sends a RELINQUISH message back after receiving C’s FAILED message C RQC = {(1, 1), (1, 2)} locked failed req(1, 1) D RQD = {(1, 1)} E req(1, 1) req(1, 2) RQE = {(1, 2)} req(1, 2) locked inquire relinquish F RQF = {(1, 1), (1, 2)} Resource Allocation > Distributed Mutual Exclusion > Quorum-Based > Maekawa 57
Maekawa Algorithm ▸ Rule 4 Upon receiving a RELINQUISH message, the receiving process j will lock itself for the most preceding request in its queue and will send a LOCKED message to the sender of that request. Resource Allocation > Distributed Mutual Exclusion > Quorum-Based > Maekawa 58
Maekawa Example C RQC = {(1, 1), (1, 2)} locked failed req(1, 1) D RQD = {(1, 1)} E req(1, 1) req(1, 2) RQE = {(1, 2)} req(1, 2) locked inquire relinquish F RQF = {(1, 1), (1, 2)} Resource Allocation > Distributed Mutual Exclusion > Quorum-Based > Maekawa 59
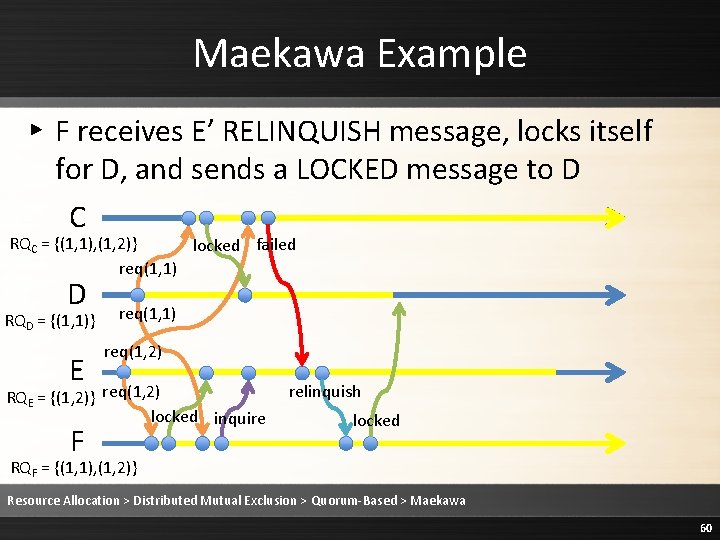
Maekawa Example ▸ F receives E’ RELINQUISH message, locks itself for D, and sends a LOCKED message to D C RQC = {(1, 1), (1, 2)} locked failed req(1, 1) D RQD = {(1, 1)} E req(1, 1) req(1, 2) RQE = {(1, 2)} req(1, 2) locked inquire F relinquish locked RQF = {(1, 1), (1, 2)} Resource Allocation > Distributed Mutual Exclusion > Quorum-Based > Maekawa 60
Maekawa Algorithm ▸ Rule 5 Upon receiving a LOCKED message from every member of Si, process i enters its critical section. Resource Allocation > Distributed Mutual Exclusion > Quorum-Based > Maekawa 61
Maekawa Example C RQC = {(1, 1), (1, 2)} locked failed req(1, 1) D RQD = {(1, 1)} E req(1, 1) req(1, 2) RQE = {(1, 2)} req(1, 2) locked inquire F relinquish locked RQF = {(1, 1), (1, 2)} Resource Allocation > Distributed Mutual Exclusion > Quorum-Based > Maekawa 62
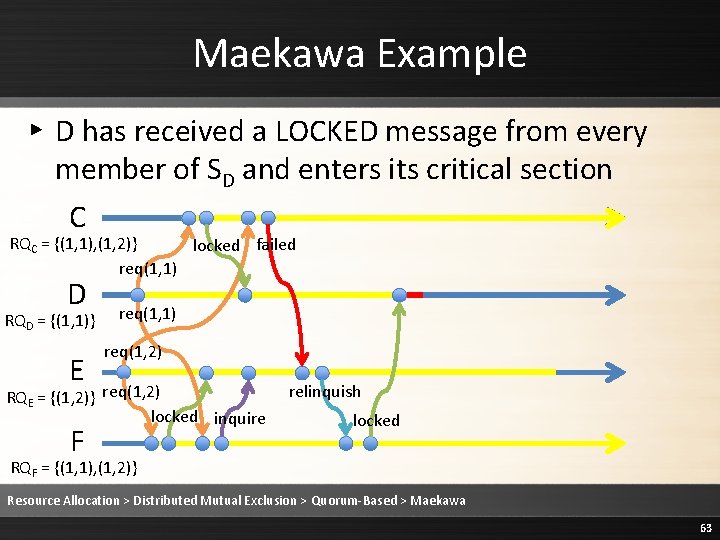
Maekawa Example ▸ D has received a LOCKED message from every member of SD and enters its critical section C RQC = {(1, 1), (1, 2)} locked failed req(1, 1) D RQD = {(1, 1)} E req(1, 1) req(1, 2) RQE = {(1, 2)} req(1, 2) locked inquire F relinquish locked RQF = {(1, 1), (1, 2)} Resource Allocation > Distributed Mutual Exclusion > Quorum-Based > Maekawa 63
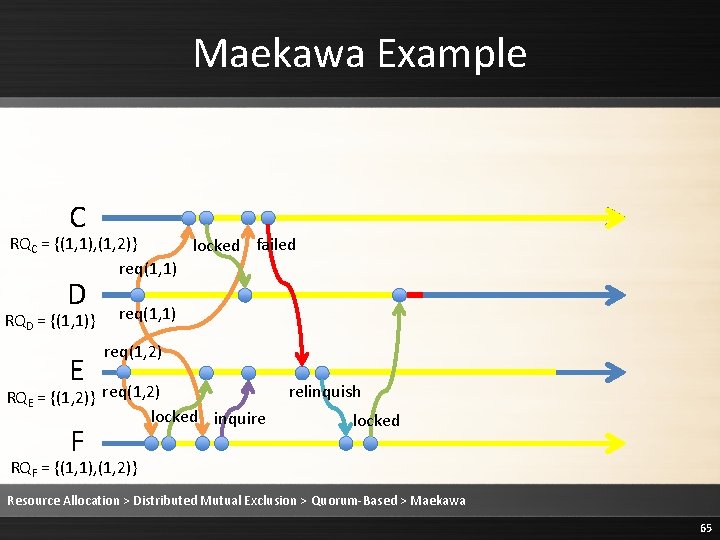
Maekawa Algorithm ▸ Rule 6 When process i exits critical section, it sends a RELEASE message to all processes in Si. , after deleting its own request from its own queue. Resource Allocation > Distributed Mutual Exclusion > Quorum-Based > Maekawa 64
Maekawa Example C RQC = {(1, 1), (1, 2)} locked failed req(1, 1) D RQD = {(1, 1)} E req(1, 1) req(1, 2) RQE = {(1, 2)} req(1, 2) locked inquire F relinquish locked RQF = {(1, 1), (1, 2)} Resource Allocation > Distributed Mutual Exclusion > Quorum-Based > Maekawa 65
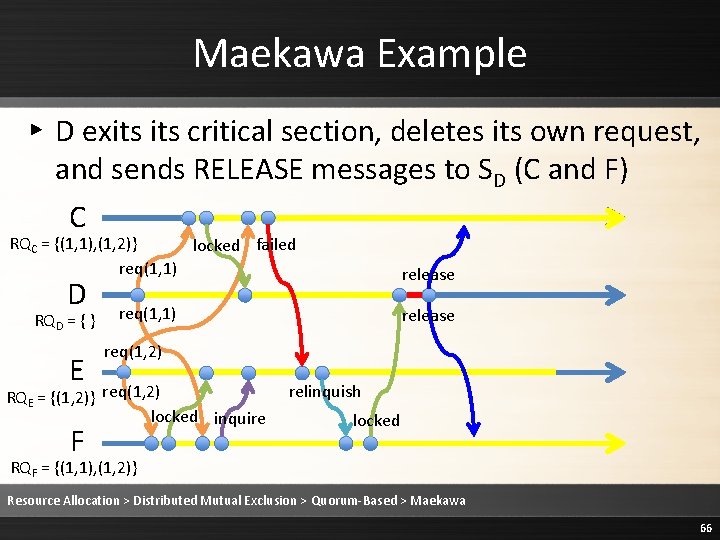
Maekawa Example ▸ D exits critical section, deletes its own request, and sends RELEASE messages to SD (C and F) C RQC = {(1, 1), (1, 2)} locked failed req(1, 1) release D RQD = { } E req(1, 2) RQE = {(1, 2)} req(1, 2) locked inquire F relinquish locked RQF = {(1, 1), (1, 2)} Resource Allocation > Distributed Mutual Exclusion > Quorum-Based > Maekawa 66
Maekawa Algorithm ▸ Rule 7 Upon receiving a RELEASE message from process i, process j deletes i’s request from its queue. If there are remaining requests, j locks itself for the most preceding request and sends a LOCKED message to process k, the request’s originator. If there are no remaining requests, j unlocks itself. Resource Allocation > Distributed Mutual Exclusion > Quorum-Based > Maekawa 67
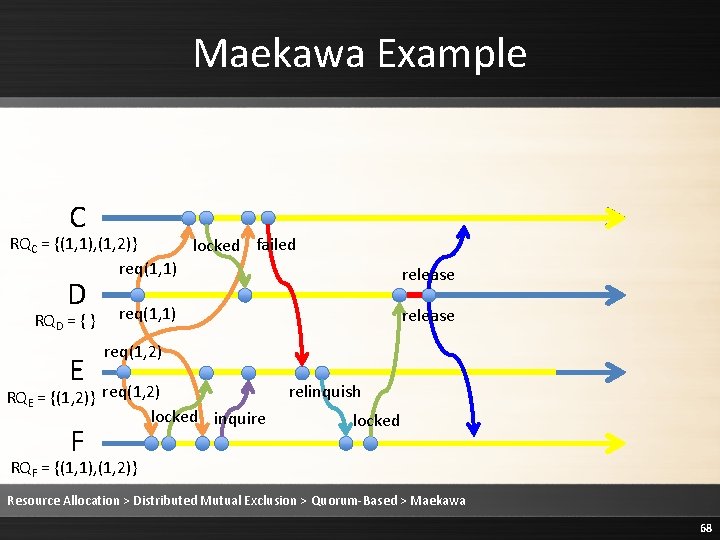
Maekawa Example C RQC = {(1, 1), (1, 2)} locked failed req(1, 1) release D RQD = { } E req(1, 2) RQE = {(1, 2)} req(1, 2) locked inquire F relinquish locked RQF = {(1, 1), (1, 2)} Resource Allocation > Distributed Mutual Exclusion > Quorum-Based > Maekawa 68
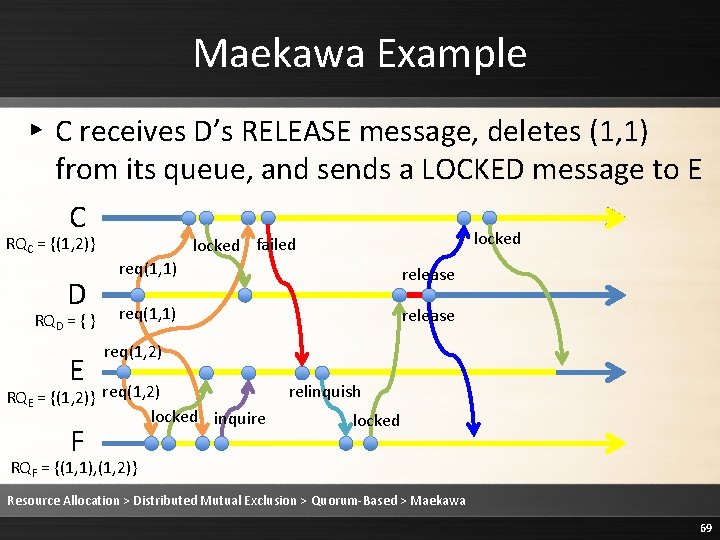
Maekawa Example ▸ C receives D’s RELEASE message, deletes (1, 1) from its queue, and sends a LOCKED message to E C RQC = {(1, 2)} D RQD = { } E req(1, 1) release req(1, 2) RQE = {(1, 2)} req(1, 2) locked inquire F locked failed relinquish locked RQF = {(1, 1), (1, 2)} Resource Allocation > Distributed Mutual Exclusion > Quorum-Based > Maekawa 69
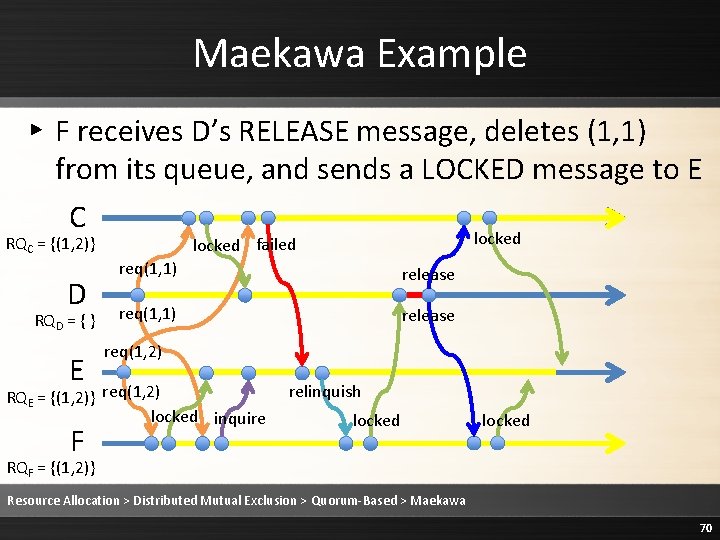
Maekawa Example ▸ F receives D’s RELEASE message, deletes (1, 1) from its queue, and sends a LOCKED message to E C RQC = {(1, 2)} D RQD = { } E req(1, 1) release req(1, 2) RQE = {(1, 2)} req(1, 2) locked inquire F locked failed relinquish locked RQF = {(1, 2)} Resource Allocation > Distributed Mutual Exclusion > Quorum-Based > Maekawa 70
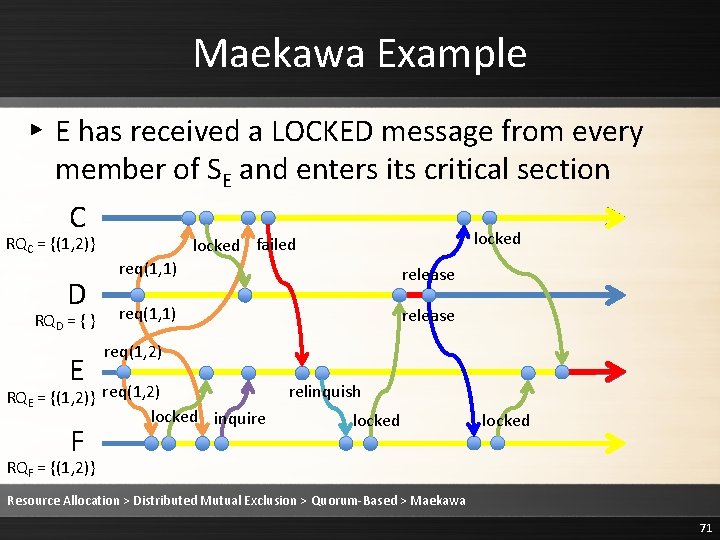
Maekawa Example ▸ E has received a LOCKED message from every member of SE and enters its critical section C RQC = {(1, 2)} D RQD = { } E req(1, 1) release req(1, 2) RQE = {(1, 2)} req(1, 2) locked inquire F locked failed relinquish locked RQF = {(1, 2)} Resource Allocation > Distributed Mutual Exclusion > Quorum-Based > Maekawa 71
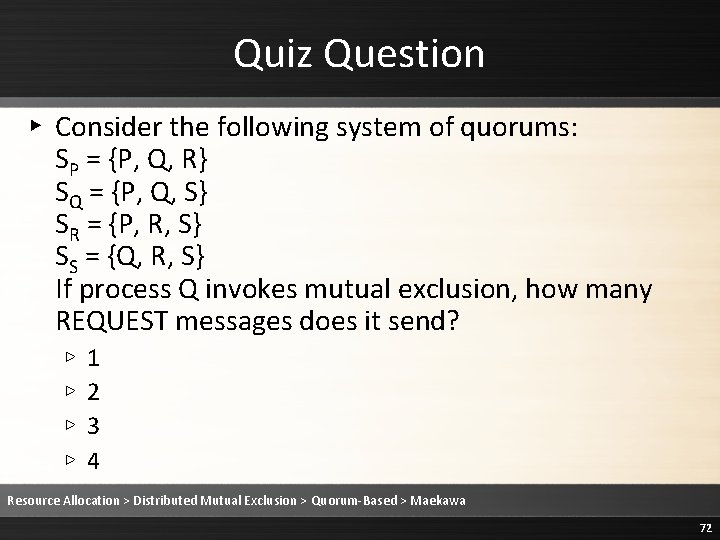
Quiz Question ▸ Consider the following system of quorums: SP = {P, Q, R} SQ = {P, Q, S} SR = {P, R, S} SS = {Q, R, S} If process Q invokes mutual exclusion, how many REQUEST messages does it send? ▹ ▹ 1 2 3 4 Resource Allocation > Distributed Mutual Exclusion > Quorum-Based > Maekawa 72
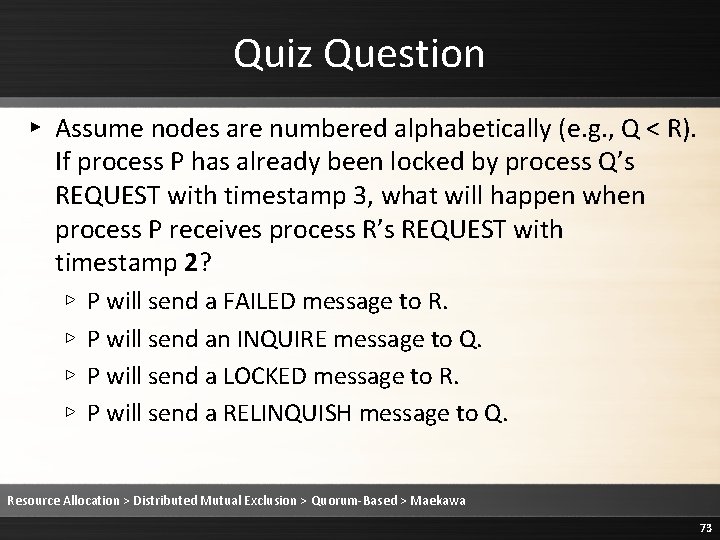
Quiz Question ▸ Assume nodes are numbered alphabetically (e. g. , Q < R). If process P has already been locked by process Q’s REQUEST with timestamp 3, what will happen when process P receives process R’s REQUEST with timestamp 2? ▹ ▹ P will send a FAILED message to R. P will send an INQUIRE message to Q. P will send a LOCKED message to R. P will send a RELINQUISH message to Q. Resource Allocation > Distributed Mutual Exclusion > Quorum-Based > Maekawa 73
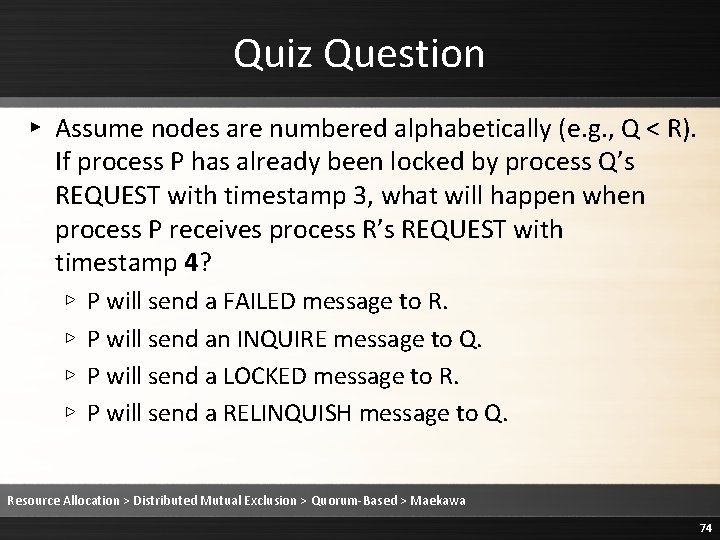
Quiz Question ▸ Assume nodes are numbered alphabetically (e. g. , Q < R). If process P has already been locked by process Q’s REQUEST with timestamp 3, what will happen when process P receives process R’s REQUEST with timestamp 4? ▹ ▹ P will send a FAILED message to R. P will send an INQUIRE message to Q. P will send a LOCKED message to R. P will send a RELINQUISH message to Q. Resource Allocation > Distributed Mutual Exclusion > Quorum-Based > Maekawa 74
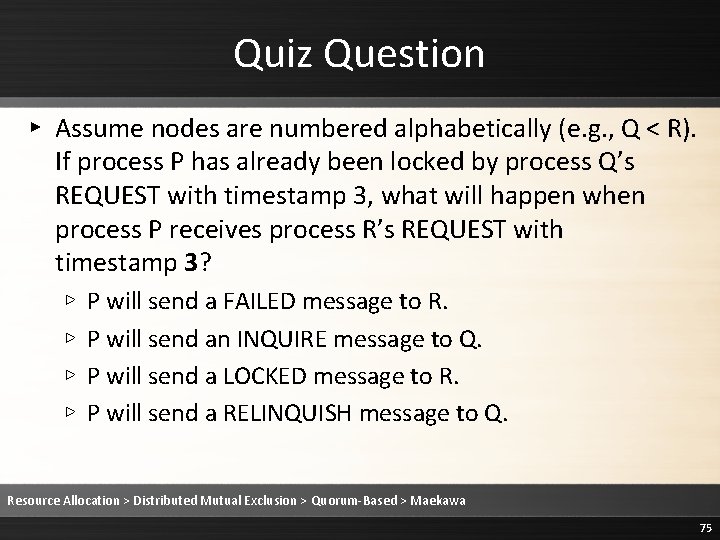
Quiz Question ▸ Assume nodes are numbered alphabetically (e. g. , Q < R). If process P has already been locked by process Q’s REQUEST with timestamp 3, what will happen when process P receives process R’s REQUEST with timestamp 3? ▹ ▹ P will send a FAILED message to R. P will send an INQUIRE message to Q. P will send a LOCKED message to R. P will send a RELINQUISH message to Q. Resource Allocation > Distributed Mutual Exclusion > Quorum-Based > Maekawa 75
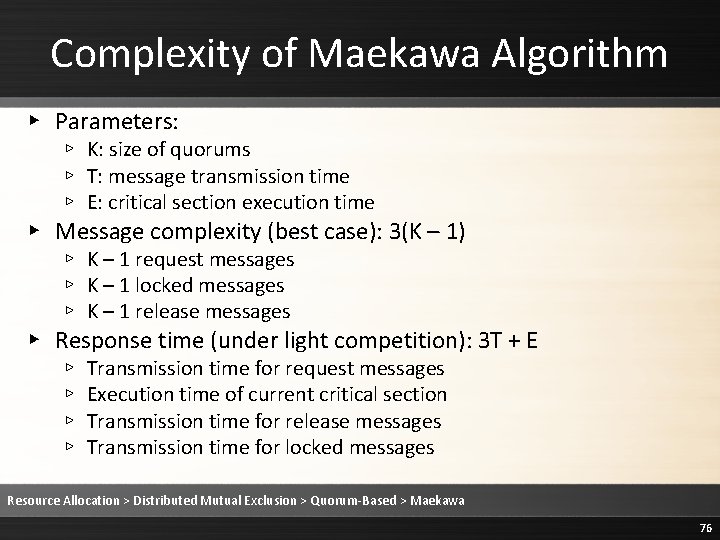
Complexity of Maekawa Algorithm ▸ Parameters: ▹ K: size of quorums ▹ T: message transmission time ▹ E: critical section execution time ▸ Message complexity (best case): 3(K – 1) ▹ K – 1 request messages ▹ K – 1 locked messages ▹ K – 1 release messages ▸ Response time (under light competition): 3 T + E ▹ ▹ Transmission time for request messages Execution time of current critical section Transmission time for release messages Transmission time for locked messages Resource Allocation > Distributed Mutual Exclusion > Quorum-Based > Maekawa 76
- Slides: 76