Chapter 10 Mutual Exclusion Distributed Algorithms Nancy A
Chapter 10: Mutual Exclusion Distributed Algorithms Nancy A. Lynch Presented By: R. Whittlesey-Harris
Contents Introduction n Asynchronous Shared Memory Model n Mutual Exclusion Problem n Dijkstra’s Algorithm n Stronger Conditions n Lockout-Free ME Algorithms n 12/3/2020 2
Introduction Asynchronous algorithms differ from synchronous algorithms in that they must handle uncertainty due to asynchrony and distribution n The Mutual Exclusion problem exists in both centralized and distributed OSs. n 12/3/2020 3
Introduction This chapter presents several mutual exclusion algorithms for the read/write shared memory model n A Lower Bound is given for the number of read/write shared variables required to solve the problem n 12/3/2020 4
Introduction n Upper and Lower bound results are provided for the case of shared variables that are read-modify-write 12/3/2020 5
Asynchronous Shared Memory Model n The system has a collection of processes (1. . n) and shared variables n n Each process i is some form of state machine with a set statei of states and a subset starti of statesi that indicate the start states Process i has labeled actions which describe the activities for which it participates • Actions are classified as, input, output, or internal • Internal actions are classified as • Those that involve a single shared memory variable • Those that involve the local computation only 12/3/2020 6
Asynchronous Shared Memory Model n Add Figure 10. 1 12/3/2020 7
Asynchronous Shared Memory Model n n Since there are no messages in this model, there are no message-generation functions The system transition relation, trans, is a set of triples, (s, , s’), where s and s’ are automaton states n n Combination of states for all processes and values for all the shared variables, called “automaton states” is the label of an input, output or internal action 12/3/2020 8
Asynchronous Shared Memory Model n (s, , s’) trans • From automaton state s, it is possible to go to automaton state s’ as a result of performing action n n The model allows for non-determinism (for convenience) System is input-enabled n n n Input actions can always occur Controlled by an arbitrary external user Output and internal steps may be enabled only in a subset of states n Controlled by the system itself 12/3/2020 9
Asynchronous Shared Memory Model n Locality restrictions are placed on the set of transitions n n n For transitions that don’t involve shared memory, the state of the process that performs the action is the only involved For transitions that involve a process i, and a shared variable x, only the state of process i and the value of x are involved Enabling of a shared memory action depends only on the process state and not the value of the shared variable accessed 12/3/2020 10
Asynchronous Shared Memory Model n n Resulting changes to the process state and the variable value may depend on the variable value Shared variable steps are constrained to be either read or write Read step involves changing the process state based on its previous state and the value in the variable read; however this variable does not change n Write step involves writing a designated value to a shared variable, overwriting what was there previous. It may also involve changing the process state 12/3/2020 11 n
Asynchronous Shared Memory Model n Processes take steps one at a time in an arbitrary order Execution is formalized as an alternating sequence, s 0, 1 , s 1, …. , consisting of automaton states alternated with actions belonging to a particular process n May be finite or infinite n 12/3/2020 12
Asynchronous Shared Memory Model n One exception to the arbitrariness in the order of process steps exists n It is not allowed for a process to stop taking steps when it is supposed to be taking steps • When the process is in a state in which some locally controlled action is enabled 12/3/2020 13
Asynchronous Shared Memory Model n The fairness condition for this shared memory system is defined below, • For Process i, we assume one of the following holds, • The entire execution is finite, and in the final state no locally controlled action of process i is enabled • The execution is infinite, and there are either infinitely many occurrences of locally controlled actions of I, ore else infinitely many places where no such action is enabled 12/3/2020 14
Mutual Exclusion Problem n n n Allocation of a single, indivisible, nonshareable resource amongst n users, U 1…Un A user with access to the resource is modeled as being in the critical region, otherwise the user is in the remainder region A user executes a trying protocol in order to gain access to its critical region 12/3/2020 15
Mutual Exclusion Problem The exit protocol is executed after the user is done with the resource n The user moves in a cycle through its remainder region (R) to its trying region (T) to its critical region (C) and then to its exit region (E) and then back again to (R) n n Figure 10. 2 shows this cycle 12/3/2020 16
Mutual Exclusion Problem n Add Figure 10. 2 12/3/2020 17
Mutual Exclusion Problem Processes are numbered 1. . n corresponding to one user Ui n Inputs to process i are the tryi and exiti actions n tryi models a request by user Ui for access to a shared resource n exiti models an announcement by user Ui that it is done with the resource n 12/3/2020 18
Mutual Exclusion Problem n Outputs of the process i are criti, and remi n n Criti models the granting of the resource to Ui Remi tells Ui that it can continue with the rest of its work Try, crit, exit, and rem are the external actions of the system The processes are responsible for performing the trying and exit protocols n Each Process, i, acts as an agent on behalf of user Ui 12/3/2020 19
Mutual Exclusion Problem Each user, Ui, 1 i n, is modeled as a state machine that communicates with its agent process using the tryi, criti, exiti, and remi actions n Figure 10. 3 depicts the external interface (external signature) n 12/3/2020 20
Mutual Exclusion Problem n Insert Figure 10. 3 12/3/2020 21
Mutual Exclusion Problem n n n Assume that Ui obeys the cyclic region protocol We define a sequence of tryi, criti, exiti and remi action to be well-formed for user i if it is a prefix of the cyclically ordered sequence tryi, criti, exiti, remi, tryi, … Ui is required to preserve the trace property (as defined in 8. 5. 4) defined by the set of sequences that are well-formed for user i 12/3/2020 22
Mutual Exclusion Problem n For executions that observe the cyclic order of actions, we say that Ui is n n n Initially in its remainder region in between any remi event and the following tryi event In its trying region in between any tryi event and the following criti event In its critical region in between any criti event and the following exiti event • Ui should be thought of as being free to use the resource at this time n In its exit region in between any exiti event and the following remi event 12/3/2020 23
Mutual Exclusion Problem n Add Figure 10. 4 12/3/2020 24
Mutual Exclusion Problem n Let A be a shared memory system. For A to solve the mutual exclusion problem, the combination of A and the users must satisfy the following conditions, n Well-formedness: In any execution, and for any I, the subsequence describing the interactions between Ui and A is well-formed for i 12/3/2020 25
Mutual Exclusion Problem n n Mutual Exclusion: There is no reachable system state (that is a combination of an automaton state for A and states for all the Ui) in which more than one user is in the critical region C Progress: At any point in a fair execution 1. (Progress for the trying region) If at least one user is in T and no user is in C, then at some point some user enters C 2. (Progress for the exit region) If at least one user is in E, then at some later point some user enters R 12/3/2020 26
Mutual Exclusion Problem n n n Shared memory system A solves the mutual exclusion problem provided that it solves the above for every collection of users Progress condition assumes the system is far (all processes and users continue taking steps) Fairness is not required for wellformedness and mutual exclusion n Safety properties not liveness 12/3/2020 27
Mutual Exclusion Problem n Trace Properties (as defined in section 8. 5. 2) n E. g. , define trace property P, where sig(P) has all the try, crit, exit, and rem actions as outputs and traces(P) is the set of sequences of these actions that satisfy the following conditions 1. is well-formed for each i 2. does not contain two crit events without an intervening exit event 12/3/2020 28
Mutual Exclusion Problem 3. At any point in , (a) If some process’s last event is try and no process’s last event is crit, then there is a later crit event (b) If some process’s last event is exit, then there is a later rem event n An equivalent restatement of the mutual exclusion problem is n The requirement that all combinations B of A with users, fairtraces(B) traces(P) 12/3/2020 29
Mutual Exclusion Problem n Shared Responsibility for progress n Responsibility does not rest only with the protocol (as given by the correctness conditions) but with the users as well • If user Ui gets the resource but never returns it, the entire system grinds to a halt 12/3/2020 30
Mutual Exclusion Problem n Lockout n n Progress as defined does not guarantee access to a shared resource It is a “global” notion of progress • some user reaches its critical region n Restricting process activity n A process within the shared memory system can have a locally controlled action enabled only when its user is in the trying or exit regions • A process can be actively engaged in executing the protocol only while it has active requests (each process is an agent for its user) 12/3/2020 31
Mutual Exclusion Problem n Read/write shared variables n n n Also known as registers In one step, a process can read or write a single shared variable Two actions involving process i and register x are 1. (read) Process i reads register x and uses the value read to modify the state of process i 2. (write) Process i writes a value determined from process i’s state to register x 12/3/2020 32
Mutual Exclusion Problem n Lemma 10. 1 12/3/2020 33
Mutual Exclusion Problem n Proof: n n n Assume each user always returns the resource Let be a finite execution of B ending in s If process i is either in its trying or exit region in state s and no locally controlled action of process i is enabled in s • Then, no events involving i occur in any execution of B that extend 12/3/2020 34
Mutual Exclusion Problem n Let ’ be a fair execution of B that extends in which no try events occur after the prefix • Repeated use of the progress assumption, with the fact that users always return the resource, imply that process i must eventually perform either a criti or a remi action • This contradicts the fact that ’ contains no further actions of i 12/3/2020 35
Dijkstra’s Algorithm First mutual exclusion algorithm for the asynchronous read/write shared memory model – developed in 1965 n Algorithm called Dijkstra. ME n 12/3/2020 36
Dijkstra’s Algorithm n Add Algorithm 12/3/2020 37
Dijkstra’s Algorithm n Shared Variables n Multi-writer/multi-reader variable • turn {1. . n} an integer n Single-writer/multi-read variable • flag(i), 1 i n – values from {0, 1, 2} • Writable by process i only, but readable by all processes 12/3/2020 38
Dijkstra’s Algorithm n First Stage n n Set flag = 1 Check turn repeatedly to see if turn=i If not & the current owner of turn is not currently active, set turn=i and move to stage two Second Stage n n n Set flag = 2 Check that no other process is in stage 2 If no other process is in stage 2, get the critical region, otherwise go to the first stage 12/3/2020 39
Dijkstra’s Algorithm n n After leaving C, lower flag to 0 The state of each process should consist of the values of its local variables and some other information, including n n Temporary variables needed to remember values just read from shared variables A program counter to say where the process is in its code Temporary variables introduced by the flow of control of the program (e. g. , loop) A region designation, R , T , C, or E 12/3/2020 40
Dijkstra’s Algorithm n Start state of each process should consist of, Specified initial values for local variables, n Arbitrary values for temporary variables and n The program counter and region designation indicating the remainder region n 12/3/2020 41
Dijkstra’s Algorithm n Dijkstra’s algorithm has many ambiguities which should be state explicitly in an automaton n S. A. when a tryi action occurs, i’s program counter should move to state L and i’s region designation should become T 12/3/2020 42
Dijkstra’s Algorithm n Dijkstra’s algorithm does not specify which portions of the code comprise of indivisible steps (necessary for reasoning) n Indivisible steps are, • The try, crit, exit, and rem steps at the user interface, • Writes and read to and from the shared variables, and • Some local computations 12/3/2020 43
Dijkstra’s Algorithm Note, the test for whether flag(turn) = 0 does not require two separate reads since turn was just read and a local copy can be used n Dijkstra’s algorithm is rewritten to rid the code of the ambiguities n 12/3/2020 44
Dijkstra’s Algorithm n Region designation R, T, C, and E are encoded into the program counter • R corresponds to rem • T corresponds to set-flag-1, test-turn, testflag, set-turn, set-flag-2, check and leavetry • C corresponds to crit; and • E corresponds to reset and leave-exit n Note that each code fragment is performed indivisibly 12/3/2020 45
Dikstra’s Algorithm n Add rewritten Algorithm 12/3/2020 46
Dijkstra’s Algorithm n Add rewritten algorithm 12/3/2020 47
Dijkstra’s Algorithm n Correctness Argument Lemma 10. 2: Dijkstra. ME guarantees well-formedness for each user n Proof: Inspection of code shows that it preserves well-formedness for each user n • By assumption, the users also preserve well -formedness, theorem 8. 11 implies that the system produces only well-formed sequences 12/3/2020 48
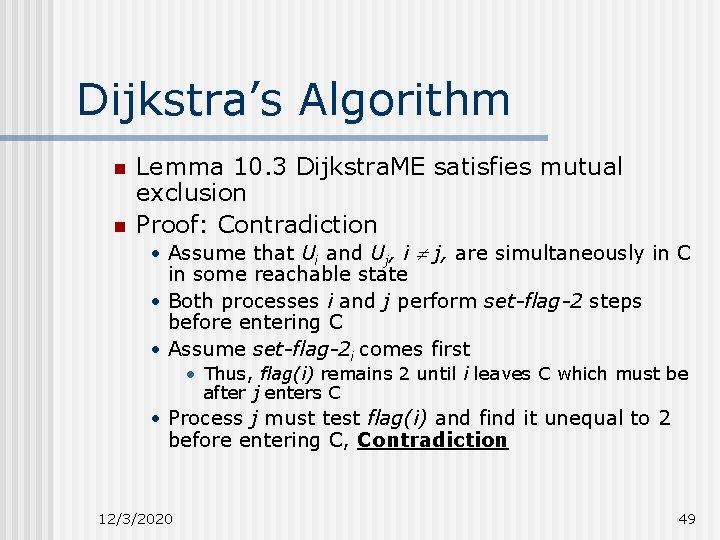
Dijkstra’s Algorithm n n Lemma 10. 3 Dijkstra. ME satisfies mutual exclusion Proof: Contradiction • Assume that Ui and Uj, i j, are simultaneously in C in some reachable state • Both processes i and j perform set-flag-2 steps before entering C • Assume set-flag-2 i comes first • Thus, flag(i) remains 2 until i leaves C which must be after j enters C • Process j must test flag(i) and find it unequal to 2 before entering C, Contradiction 12/3/2020 49

Dijkstra’s Algorithm n Add Figure 10. 5 12/3/2020 50
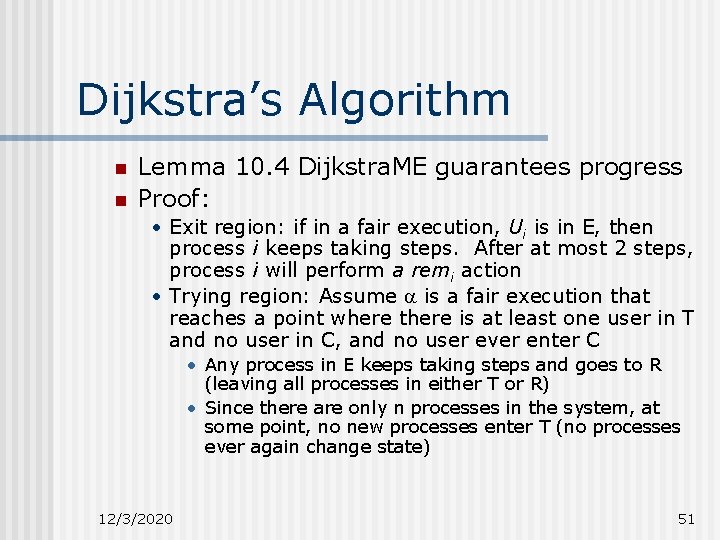
Dijkstra’s Algorithm n n Lemma 10. 4 Dijkstra. ME guarantees progress Proof: • Exit region: if in a fair execution, Ui is in E, then process i keeps taking steps. After at most 2 steps, process i will perform a remi action • Trying region: Assume is a fair execution that reaches a point where there is at least one user in T and no user in C, and no user ever enter C • Any process in E keeps taking steps and goes to R (leaving all processes in either T or R) • Since there are only n processes in the system, at some point, no new processes enter T (no processes ever again change state) 12/3/2020 51
Dijkstra’s Algorithm • Thus, has a suffix 1 in which there is a fixed nonempty set of processes in T taking steps forever • Call these processes contenders • After at most a single step in 1, each contender i ensures that flag(i) 1 and remains 1 for the rest of 1 • Thus if turn is modified during 1 it is changed to a contender’s index 12/3/2020 52
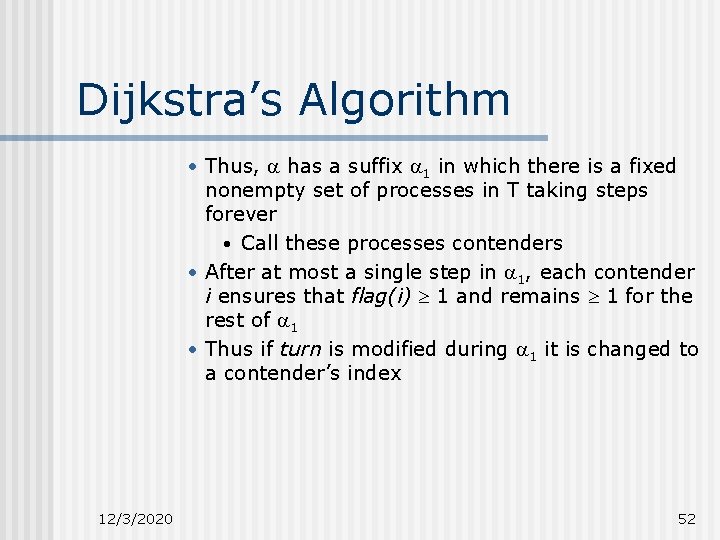
Dijkstra’s Algorithm n n Claim 10. 5 In 1, turn eventually acquires a contender’s index Proof: Assume the value of turn remains equal to the index of a non-contender throughout 1 • If pci reaches test-turn (beginning of while loop) then i will set turn to i • The only way i does not reach test-turn is if i succeeds in its checks of all other processes’s flags and proceeds to leave-try • But, by assumption of 1, i does not reach C and therefore, check must fail taking i back to set-flag-1 where it proceeds to test-turn 12/3/2020 53
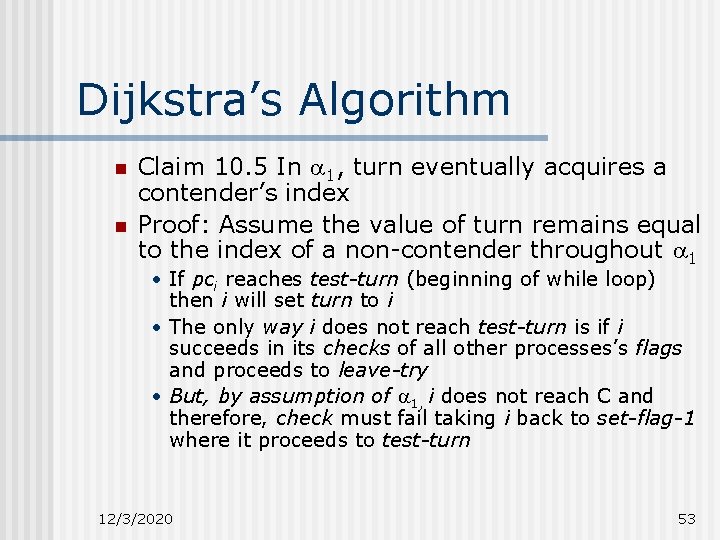
Dijkstra’s Algorithm • In test-turn, i sets turn = i and since i is a contender, this is a contradiction • Let 2 be a suffix of 1 in which the value of turn is stabilized at some contender’s index, i • Claim: In 2, any contender j i eventually ends up with its program counter looping forever in the while loop • If it ever reaches check, since it does not reach C, it must eventually return to set-flag-1, but then will be stuck looping forever • Turn = i j and flag(i) 0 throughout 2 12/3/2020 54
Dijkstra’s Algorithm • Let 3 be a suffix of 2 in which all contenders other than i loop forever between test-turn and test-flag • All contenders other than i have there flag = 1 throughout 3 • In 3, process i has nothing to stand in the way of its reaching C Add Figure 10. 6 12/3/2020 55
Dijkstra’s Algorithm n Theorem 10. 6 Dijkstra. ME solves the mutual exclusion problem n Proof of Lemma 10. 3 • Assertion 10. 3. 1: In any reachable system state |{i : pci = criti}| 1 • Prove as a consequences of assertions 10. 3. 2 and 10. 3. 3 • Assertion 10. 3. 2: In any reachable system state, if pci {leave-try, crit, reset}, then |Si| = n • Assertion 10. 3. 3: In any reachable system state, there do not exist i and j, i j, such that i Sj and j Si 12/3/2020 56
Dijkstra’s Algorithm • Assume, for contradiction, there are two distinct processes, i and j, in some reachable system state, s. t. pci = pcj = crit • By Assertion 10. 3. 2, |Si| = |Sj| = n • Then j Si and i Sj which contradicts Assertion 10. 3. 3 • Assertion 10. 3. 2 is proved by induction • All processes are in R in the initial state • Inductive Step: 1. consider all the types of actions one at a time. 2. Only steps that could cause a violation are those that cause pci to enter the set of listed values and those that reset Si to (checki, reseti) 12/3/2020 57
Dijkstra’s Algorithm For checki, the only the contradiction pci {leave-try, crit, reset} is true after the step is if |Si| = n • For reseti, the process leaves the indicated set of values after the step so the statement is true vacuously • Assertion 10. 3. 3 is proved by three additional assertions, • Assertion 10. 3. 4: In any reachable system state, if Si , then pci {check, leave-try, crit, reset} • Si in the initial system state • 12/3/2020 58
Dijkstra’s Algorithm • Inductive Step: 1. Only events that can cause a violation of this statement are events that cause Si to become unequal to and events that cause pci to leave the set of listed values {set-flag 2, checki, reseti} • However, set-flag-2 sets pci = check • When checki causes pci to leave the set of listed values it also sets Si = • Thus all these events preserve the condition 12/3/2020 59
Dijkstra’s Algorithm • • 12/3/2020 Assertion 10. 3. 5: In any reachable system state, if pci {check, leave-try, crit, reset}, then flag(i) = 2 • Proved by induction on the length of an execution as well It follows that, Assertion 10. 3. 6: In any reachable system state, if Si , then flag(i) = 2 Assertion 10. 3. 3 is proved by induction on the length of an execution. • All sets, Si = • Inductive Step: 1. The only event that could cause a violation is one that adds an element j to Si for some i and j, i j; check(j)i for some i and j, i j 60
Dijkstra’s Algorithm • Consider case where j gets added to Si as a result of a check(j)i event; it must follow that flag(j) 2 when this event occurs • However, Assertion 10. 3. 6 implies that Sj = , so i Sj n Running Time n n An upper bound on the time from any point in an execution when some process is in T and no one is in C, until someone enters C Assume that each step occurs at some point in real-time and that execution begins at realtime 0 12/3/2020 61
Dijkstra’s Algorithm Impose an upper bound of l on the time between successive steps of each process n Assume an upper bound of c on the maximum time that any user spends in the critical region n Theorem 10. 7: In Dijkstra. ME, suppose that at a particular time some user is in T and no user is in C. Then, within O(ln), some user enters C n 12/3/2020 62
Dijkstra’s Algorithm n Proof: Suppose the lemma is false and consider an execution in which at some point process i is in T and no process is in C for at least kln, (for some large constant k) 1. Time elapsed from the starting point until there is no process in either C or E is at most O(l) 2. Additional time until process i performs a test-turni is at most O(l n) • 12/3/2020 i can at worst spend this much time checking flags in the second stage before returning to set-flag-1 63
Dijkstra’s Algorithm 3. Additional time from when i does test-turni until the value of turn is a contender index is at most O(l ) • • 12/3/2020 If at the time i does test-turni, turn already holds a contender index, so suppose this is not the case If turn = j and j is not a contender, within O(l) after the test, i performs a test-flag(j)i. • If i finds flag(j) = 0 then i sets turn = i, which is the index of the contender and we are done; • If it finds flag(j)i 0 then it follows that in between the test-turni and test-flag(j)i, j entered the trying region and became a contender. • If turn has not changed in the interim, turn is equal to the index of a contender (j) and we are done • If turn has changed, then it must have been set to the index of a contender 64
Dijkstra’s Algorithm 4. After an additional time O(l ), a point is reached at which the value of turn has stabilized to the index of some contender; and no process advances again to set-turn or set-flag-2 (until time kl n) 5. By an additional time O(l n), all contenders other than j will have their program counters in {test-turn, test-flag}, otherwise they would reach C. 6. An additional time O(l n), j must succeed in entering C which contradicts the assumption that no process enters C within this amount of time. 12/3/2020 65
Dijkstra’s Algorithm n Add figure 10. 7 12/3/2020 66
Stronger Conditions n Dijkstra. ME does not guarantee the critical region will be granted fairly to users n It may grant a particular user access to the critical region repeatedly while other users wait, trying forever • Called Lockout or starvation 12/3/2020 67
Stronger Conditions n To distinguish between the two types of fairness discussed thus far, the follow are defined Low-level fairness - process execution fairness n High-level fairness - resource access fairness n n High-level fairness may be less critical in practice 12/3/2020 68
Stronger Conditions n Dijkstra. ME’s multi-write/multi-read variable, turn, is difficult and expensive to implement in many kinds of multiprocessor systems n Single-write/multi-read and singlewrite/single-read variables are easier to implement 12/3/2020 69
Stronger Conditions n Three notions of resource allocation fairness are defined for an algorithm A, with users U 1, …, Un n Lockout-freedom – The following hold for any low-level-fair execution, 1. (Lockout-freedom for the trying region) If all users always return the resource, then any user that reaches T eventually enters C 2. (Lockout-freedom for the exit region) Any user that reaches E eventually enters R 12/3/2020 70
Stronger Conditions n Time bound b – The following hold for any low-level-fair execution with associated times, 1. (Time bound b for the trying region) If each user always returns the resource within time c of when it is granted, an the time between successive steps of each process in T or E is at most l, then any user that reaches T enters C within time b 2. (Time bound b for the exit region) If the time between successive steps of each process in T or E is at most l, then any user that reaches E enters R within time b n b is typically a function of l and c 12/3/2020 71
Stronger Conditions n Number of bypasses a – For any interval of an execution starting when a process i has performed a locally controlled step in T, and throughout it’s remainder in T, • Any other user j, j i, can only enter C at most a times 12/3/2020 72
Stronger Conditions n Implications among the fairness conditions are, n Theorem 10. 8 – Let A be a mutual exclusion algorithm, let U 1, …, Un be a collection of users, and let B be the composition of A with U 1, …, Un. If B has an infinite bypass bound and is lockout-free for the exit region, then B is lockout free. • Proof: If i is in T in a low-level-fair execution of B where all users always return the resource, suppose for contradiction, i never enters C 12/3/2020 73
Stronger Conditions • Lemma 10. 1 implies that i must perform a locally controlled action in T, if not done so already. Repeated use of the progress condition and assumption that users always return the resource implies that infinitely many total region changes occur. With this, some process other than i must enter C an infinite number of times while i remains in T, which violates the bypass bound. 12/3/2020 74
Stronger Conditions n Theorem 10. 9, Let A be a ME algorithm, let U 1, …, Un be a collection of user, and let B be the composition of A with U 1, …, Un. If B has any time bound b (for both the T and E regions), then B is lockoutfree 12/3/2020 75
Stronger Conditions n Proof: If i is in T in a low-level-fair execution of B where all users always return the resource: • Times are associated with the events in the execution in any monotone non-decreasing, unbounded way, so that the times for the steps of each process is at most l and the times for all critical regions is at most c. • i enters C in at most time b since the algorithm satisfies the time bound b, and thus i eventually enters C as needed. 12/3/2020 76
Lockout-Free ME Algorithms n Two-Process Algorithm: Peterson 2 P i {0, 1} n ī = |1 -i|, i. e, counting mod 2 n Add Peterson 2 P algorithm (pg, 279) 12/3/2020 77
Lockout-Free ME Algorithms n Peterson 2 P algorithm • i initially sets flag to 1 and proceeds to set turn to i • i waits until either they other process flag is 0 (leaves the CS) or turn i (other process wants to compete for CS) • Temporary variables, a region designator and a program counter are added to translate the program into a state machine 12/3/2020 78
Lockout-Free ME Algorithms n Add rewritten algorithm (pgs, 280281) 12/3/2020 79
Lockout-Free ME Algorithms n Lemma 10. 10 Peterson 2 p satisfies mutual exclusion • Proof: • Assertion 10. 5. 1 In any reachable system state, if flag(i) = 0, then pci {leave-exit, rem, setflag} Show by induction using assertion 10. 5. 1 • Assertion 10. 5. 2 In any reachable system state, if pci {check-flag, check-turn, leave-try, crit, reset} then turn i 12/3/2020 80
Lockout-Free ME Algorithms Key events are, 1. “Successful” check-flagi events, (those that cause pci to reach leave-try); flag(ī) must be = 0 which implies by Assertion 10. 5. 1 that pci {checkflag, check-turn, leave-try, crit, reset} 2. “Successful” check-turni events; turn i 3. Set-turnī events, which cause pcī to take on the value check-flag; turn i 4. Set-turni events, which falsify the conclusion turn i; pci = check-flag If both i and ī are in C, then assertion 10. 5. 2 applied twice implies that both turn i and turn ī which is a contradiction • • 12/3/2020 81
Lockout-Free ME Algorithms n Lemma 10. 11 Peterson 2 P guarantees progress • Proof: Contradiction: is a low-level-fair execution that reaches a point where at least one of the processes, i, is in T and neither process is in C and neither process ever enters C. 1. If ī is in T sometime after , then both processes must get stuck in their check loops which cannot happen since turn must stabilize to a value favorable to one of them 2. If ī is never in T after , then we see that flag(ī) eventually becomes and stays equal to 0, contradicting the assumption that i is stuck in its check loop 12/3/2020 82
Lockout-Free ME Algorithms n Lemma 10. 12 Peterson 2 P is lockout-free • Proof: Consider the trying region, show the stronger condition of two-bounded bypass and invoke Theorem 10. 8 • Suppose at some point in the execution, , process i remains in T and process ī enters C three times • The 2 nd and 3 rd times, ī sets turn = ī and then sees turn = i; it cannot see flag(i) = 0 since flag(i) remains at 1 (there at least 2 occurrences of set-turni after because only i can set turn to i). But since set-turni is only performed once during one of i’s trying regions, this is a contradiction. 12/3/2020 83
Lockout-Free ME Algorithms n Theorem 10. 13 Peterson 2 P solves the mutual exclusion problem and guarantees lockout-freedom • Given from above n Complexity Analysis n Let l be the upper bound on process step time and c be the upper bound on critical section time 12/3/2020 84
Lockout-Free ME Algorithms n Theorem 10. 14 In Peterson 2 P, the time from when a particular process i enters T until it enters C is at most c + O(l) • Proof Sketch: • Suppose the time bound does not hold • i is in T but does not enter C for at least c + kl after that point • Within time at most 3 l, process i performs checkflagi and will not succeed in any of its checks, otherwise it will enter C within O(l). • When check-flagi is performed, it must find flag(ī) = 1 since i would reach C otherwise within o(l). • By assertion 10. 5. 1, pci {set-turn, check-flag, check-turn, leave-try, crit, reset} 12/3/2020 85
Lockout-Free ME Algorithms • Either criti occurs within an additional time O(l), or reseti occurs within additional time c+ O(l) • Based on the value of turn and where the processes are in their code • The former case means that i would reach C too early so the latter case is the only choice • i performs check-flagi again, within an additional O(l); flag(ī) = 1 (ī has entered T) after the resetī. • Either turn has already taken the value ī or will do so within additional time l • Within at most another O(l), process i finds favorable conditions for it to enter C which contradicts the assumption that i does not enter C within this amount of time. See Figure 10. 8 for the events 12/3/2020 86
Lockout-Free ME Algorithms n An n-Process Algorithm n Use the idea of Peterson 2 P iteratively in a series of n-1 competitions at levels 1, 2, …, n-1 • The algorithm ensures at least one loser for each competition • n processes may compete at level 1 but at most n-1 processes can win • n-k processes can win at level k (in general) • Processes are 1. . n 12/3/2020 87
Lockout-Free ME Algorithms n Add Peterson. NP algorithm (pg 284) 12/3/2020 88
Lockout-Free ME Algorithms Process i completes one competition per level 1. . n-1 n Each level k has its own turn(k) n At each level k, i sets turn(k) = i and waits to see if either all the other processes’ flag variables are less than k or that turn(k) i (no other process is involved in the competition and no other process has reset the turn(k) variable) n 12/3/2020 89
Lockout-Free ME Algorithms n Ambiguities need to be resolved to translate the code into a state machine • Local variable level keeps track of which competition the process is engaged in (or ready to engage in) and, • S keeps track of processes that have been observed to have flag values smaller than k Add rewritten Peterson. NP algorithm (pgs 285 -286) 12/3/2020 90
Lockout-Free ME Algorithms We say, process i is a winner at level k if either leveli > k for leveli = k and pci {leave-try, crit, reset} n We say process i is a competitor at level k if it is either a winner at level k or else leveli = k and pci {check-flag, check-turn} n 12/3/2020 91
Lockout-Free ME Algorithms n Lemma 10. 15 Peterson. NP satisfies mutual exclusion • Proof: • Assertion 10. 5. 3 In any reachable system state of Peterson. NP, the following are true: 1. If process i is a competitor at level k, if pci = check-flag and if any process j i in Si is a competitor at level k, then turn(k) i. 2. If process i is a winner at level k and if any other process is a competitor at level k, then turn(k) i. Proof left as an exercise. 12/3/2020 92
Lockout-Free ME Algorithms • Assertion 10. 5. 4 In any reachable system state of Peterson. NP, if there is a competitor at level k, then the value of turn(k) is the index of some competitor at level k. • Proof left as an exercise • Assertion 10. 5. 5 In any reachable system state of Peterson. NP and for any k, 1 k n -1, there at most n-k winners at level k • Basis: k = 1 • Inductive step: Assume the statement for k, 1 k n-2 and show it for k+1; 12/3/2020 93
Lockout-Free ME Algorithms • Contradiction: if the statement is false for k+1, there are strictly more than n-(k+1) winners at level k+1; • Let W be the set of winners • Every winner at level k+1 is also a winner at level k, (# of winners at level k is at most n-k). Thus, W is also the set of winners at level k and |W| = n -k 2, Thus, • Assertion 10. 5. 3 implies that the value of turn(k+1) cannot be the index of any of the processes in W and, • Assertion 10. 5. 4 implies that the value of turn(k+1) is the index of some competitor at level k+1. But since every competitor at level K+1 is a winner at level k, and so is in W. Therefore a contradiction. 12/3/2020 94
Lockout-Free ME Algorithms n Theorem 10. 16 In Peterson. NP, the time from when a particular process i enters T until it n-1 n enters C is at most 2 c + O(2 nl) • Proof: Recurrence • Define T(0) to be the maximum time from when a process enters T until it enters C. • Define T(k) to be the max time from when a process becomes a winner at level k until it enters C; for k, 1 k n-1. • Bound T(0) • We know T(n-1) l (by the code) since only one step is needed to enter C after winning the final competition • 1 k n-2 12/3/2020 95
Lockout-Free ME Algorithms If process i has won at level k if k 1, or has just entered T if k = 0 • Within time 2 l, process i performs set-turni setting turn(K+1) = i • Let be the set-turni event • Consider these two cases, 1. If turn(k+1) gets set to a value other than i within time T(k+1) + c + (2 n + 2)l after , then i wins at level k+1 within an additional time nl. With additional time T(k+1), i enters C. The total time from until i enters C is at most 2 T(k+1) + c + (3 n+2)l. 2. Assume that turn(k+1) does not get set to any value other than i within time T(k+1) + c+ (2 n+2)l after . No process can set its flag to k+1 within time T(k+1) + c + (2 n + 2)l after . • 12/3/2020 96
Lockout-Free ME Algorithms • Let I be the set of processes j i for which flag(j) k+1 when occurs. Then each process in I wins at level k+1 within time at most nl after (it finds turn(k+1) unequal to its index), then enters C within additional time T(k+1), then leaves C within additional time c and performs reset within additional time l. (within time nl +T(k+1)+c+l = T(k+1)+c+(n+1)l after , all processes in I set their flags to 0) • Within time T(k+1)+c+(n+1)l after , all processes j i for which flag(j) k+1 when occurs, set their flags to 0. 12/3/2020 97
Lockout-Free ME Algorithms • For an additional time nl after than, no process sets its flag to k+1. Which is significant time for process i to detect that all the flag variables are less than k+1 and to win at level k+1 (within T(k+1) + c+(2 n+1)l) after and enters C within another T(k+1) • So, total time from until i’s entrance into C is at most 2 T(k+1)+c+(2 n+1)l. • The worst case time is at most 2 l + max of the times in the two cases, 2 t(k+1)+c+(3 n+4)l. • Solving for the recurrence for T(0): T(k) 2 T(k+1)+c+(3 n+4)l for 0 k n-2 T(n-1) l 12/3/2020 98
Lockout-Free ME Algorithms n Theorem 10. 17 Peterson. NP solves the mutual exclusion problem and is lockout free seen from above n Tournament Algorithm n n Assume the number of processes, n, is a power of 2 (starting at 0) Each process engages in a series of log n competitions • Arranged in a complete n-leaf binary tournament tree) • n leaves correspond left-to-right to the n processes 0, …, n-1 12/3/2020 99
Lockout-Free ME Algorithms n The following are defined for 0 i n-1 and 1 k log n • comp(i, k) – the level k competition of process i, is the string consisting of high-order log n-k bits of the binary representation of i • can be used as a name for the internal node that is the level k ancestor of i’s leaf • Root is named by (empty string) • role(i, k) – the role of process i in the level k competition of process i, is the (log n-k+1)st bit of the binary representation of i • indicates whether i’s leaf is a descendant of the left or right child of the node for competition comp(i, k). 12/3/2020 100
Lockout-Free ME Algorithms • opponents(i, k) – the opponents of process i in the level k competition of process i, is the set of process indices with the same high-order log n-k bits as i and the opposite (log n-k+1)st bit • the processes in opponents(i, k) are those whose leaves are descendants of the opposite child node comp(i, k) (of the child that is not an ancestor of i’s leaf). 12/3/2020 101
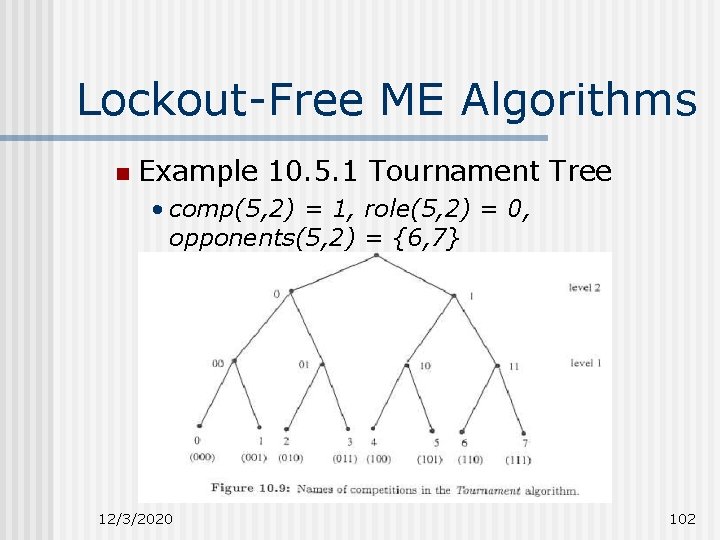
Lockout-Free ME Algorithms n Example 10. 5. 1 Tournament Tree • comp(5, 2) = 1, role(5, 2) = 0, opponents(5, 2) = {6, 7} 12/3/2020 102

Lockout-Free ME Algorithms n Add Tournament Algorithm (pg 291) 12/3/2020 103
Lockout-Free ME Algorithms For each competition, the process only checks the flags of its components in that competition n Lemma 10. 18 The Tournament algorithm satisfies mutual exclusion n • Proof Sketch: • Assertion 10. 5. 6 In any reachable system state of the Tournament algorithm, and for any k, 1 k log n, at most one process from any subtree rooted at level k is a winner at level k. 12/3/2020 104
Lockout-Free ME Algorithms • Assertion 10. 5. 7 If process i is a winner at level k and if any level-k opponent of i is a competitor at level k, then turn(comp(i, k)) role(i, k). • Must be strengthened to include some information about what happens inside the waitfor loop after the process has discovered that some of its opponents have flag variables with the values that are strictly less than k. n Theorem 10. 19 In The Tournament algorithm, the time from when a particular process I enters T until it enters C is at most (n 1)c+O(n 2 l). 12/3/2020 105
Lockout-Free ME Algorithms • Proof: • Define T(0) = max time from when a process enters T until it enters C. • T(k) = max time from when a process wins at level k until it enters C, for k, 1 k log n. • Bound T(0) • T(log n) l since only one step is needed to enter C after winning the final competition • Bound T(k) in terms of T(k+1), 0 k log n-1 • If process i has just won at level k if k 1 or has just entered T if k = 0, let x denote comp(i, k+1). • Within time 2 l, process i sets the turn(x) variable to role(i, k+1). Let denote this event and consider two cases, 12/3/2020 106
Lockout-Free ME Algorithms 1. If turn(x) gets changed within time T(k+1)+c+(2 k+1+4)l after , then i wins at level k+1 within an additional time (2 k+1)l. And within additional time T(k+1), i enters C. Total time from until i’s entrance to C is at most 2 T(k+1)+c+(2 k+1+2 k+5)l. 2. If turn(x) does not get changed within the time T(k+1)+c+(2 k+1+4)l after . Then no level k+1 opponent of i can set its flag to k+1 within time T(k+1)+c+(2 k+1+3)l after . If j is a level k+1 opponent of i for which flag(j) k+1 when occurs, then within time (2 k+1)l + T(k+1)+c+l = T(k+1)+c+(2 k+2)l after , process j sets its flag to 0. 12/3/2020 107
Lockout-Free ME Algorithms • Within time T(k+1)+c+(2 k+2)l after , all level k+1 opponents j of i for which flag(j) k+1 when occurs, set their flags to 0. • For an additional time (2 k+1)l after that, no process sets its flag to k+1 which is sufficient time for process i to detect that all its level k+1 opponents’ flag variables are less than k+1 and to win. • Wins within T(k+1)+c+(2 k+1+3)l after . • Within another T(k+1), i enters C. • Total time from until i’s entrance in C is at most 2 T(k+1)+c+(2 k+1+2 k+7)l • The worst case time is at most 2 l plus the max of the times in the two cases 12/3/2020 108
Lockout-Free ME Algorithms • Solve the recurrence for T(0) T(k) 2 T(k+1)+c+(2 k+1+2 k+7)l, for 0 k log n-1 T(log n) l See Recurrence Solution page 293 n Theorem 10. 20 The Tournament algorithm solves the mutual exclusion problem and is lockout-free • From above 12/3/2020 109
Lockout-Free ME Algorithms n Bounded Bypass • The Tournament algorithm does not guarantee any bound on the number of bypasses. • Consider an execution in which process 0 enters the tournament at its leaf and takes steps with intervening times exactly equal to the assumed upper bound l. • Process n-1 enters the tournament at its leaf going much faster. • Process n-1 can reach the top and win and can repeat this arbitrarily many times before process 0 even wins at level 1. • Since we have not assumed any lower bound on process step times • No process is locked out for very long. 12/3/2020 110
- Slides: 110