RACBVHs RandomAccessible Compressed Bounding Volume Hierarchies TaeJoon Kim
RACBVHs: Random-Accessible Compressed Bounding Volume Hierarchies Tae-Joon Kim Bochang Moon Duksu Kim Sung-Eui Yoon KAIST (Korea Advanced Institute of Science and Technology) To appear at IEEE TVCG 09
Goal § Design a compact representation for interactive geometric and graphics applications of massive models § Support random access § Support various applications § Improve performance of applications
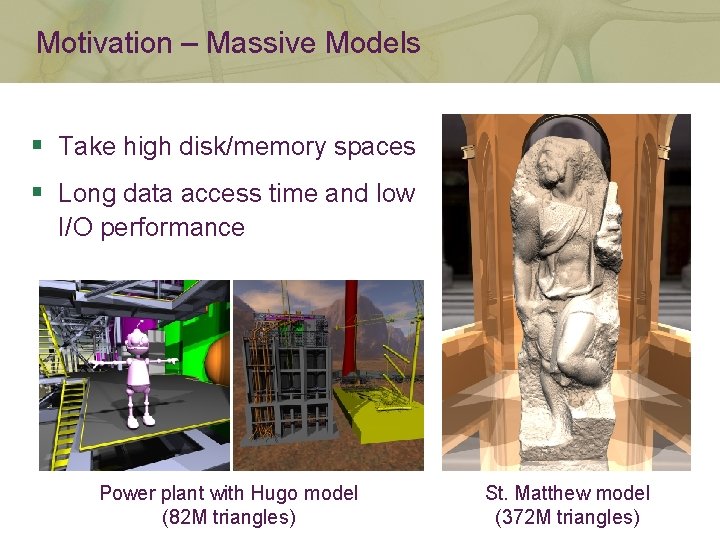
Motivation – Massive Models § Take high disk/memory spaces § Long data access time and low I/O performance Power plant with Hugo model (82 M triangles) St. Matthew model (372 M triangles)
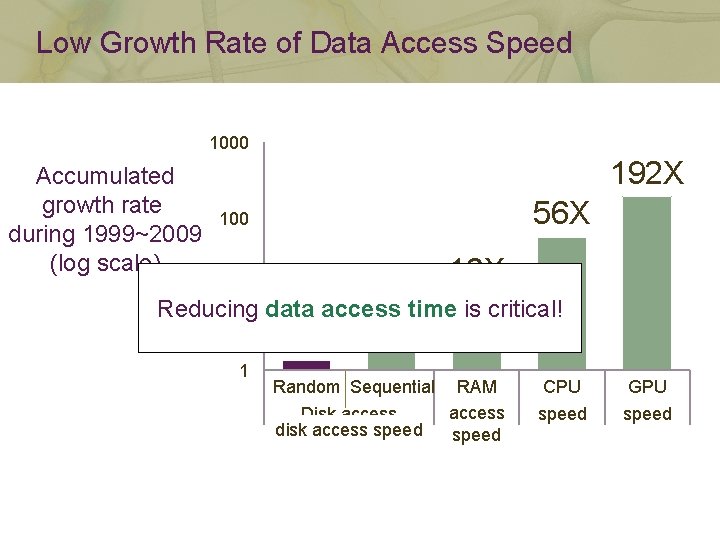
Low Growth Rate of Data Access Speed 1000 Accumulated growth rate during 1999~2009 (log scale) 192 X 56 X 100 10 X 4. 5 X Reducing data access time is critical! 10 1. 3 X 1 Random Sequential RAM access Disk access disk access speed CPU speed GPU speed
Large Scale Applications § Ray tracing § Collision detection § Visibility queries § Dynamic simulation § Motion planning
Large Scale Applications § Common geometric data structures § Meshes § Acceleration hierarchies § k-d trees § Bounding volume hierarchies (BVHs) § Usually require random access on meshes and hierarchies Supporting random access is important!
Our Approach § Compress bounding volume hierarchies (BVHs) to reduce expensive data access time § Support random access § Support fast runtime decompression for performance improvements § Provide general API for various applications Random-Accessible Compressed BVHs
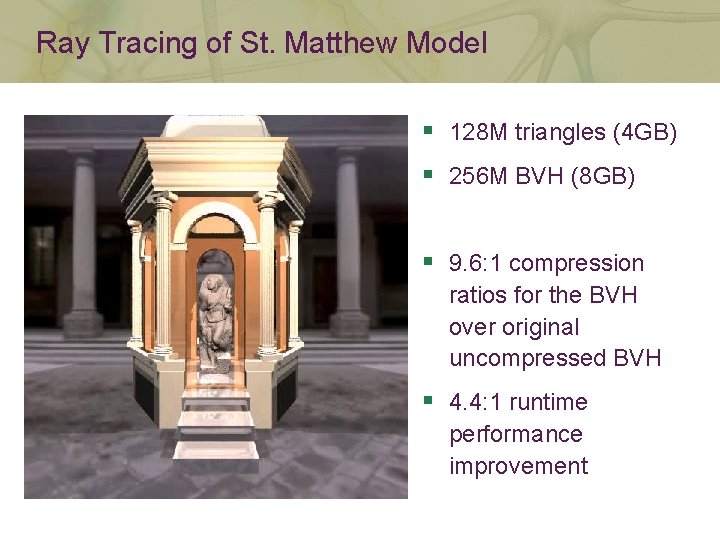
Ray Tracing of St. Matthew Model § 128 M triangles (4 GB) § 256 M BVH (8 GB) § 9. 6: 1 compression ratios for the BVH over original uncompressed BVH § 4. 4: 1 runtime performance improvement
Related Work § Mesh compression § Compression and random access § Tree and BVH compression
Mesh Compression § Designed to achieve a maximum compression ratio or efficient transmission § [Touma and Gotsman 98, Devillers and Gandoin 00] § Encode vertices § [Alliez and Desbrun 01, Kälberer et al. 05] Do not directly support random access § Encode edges § [Isenburg and Snoeyink 00] § Encode faces § [Gumhold and Strasser 98, Rossignac 99, Lee et al. 02]
Compression and Random Access § Quite common in video & audio encoding § E. g. , MPEG video § Single or multi-resolution mesh compression § [Choe et al. 04, Yoon and Lindstrom 07, Choe et al. 09] § [Gobbetti et al. 06, Kim et al. 06] § Regular volumetric grids and images § [Ihm and Park 99, Rodler 99, Lefebvre and Hoppe 06]
Tree and BVH Compression § Tree compression § [Zaks 80, Zerling 85, Katajainen and Makinen 90] § Do not support random access § Encode bounding volumes § Quantization: [Cline et al. 06, Mahovsky 05, Terdiman 03] § Hierarchical encoding: [Rusinkiewicz and Levoy 00, Hubo et al. 06] § Encode tree structures § Assume a particular tree structure: [Lauterbach et al. 07 and 08] § Assume a particular layout for the tree: [Lefebvre and Hoppe 07]

Outline § Overview § Compression at preprocessing § Runtime data access framework § Results
Outline § Overview § Compression at preprocessing § Runtime data access framework § Results
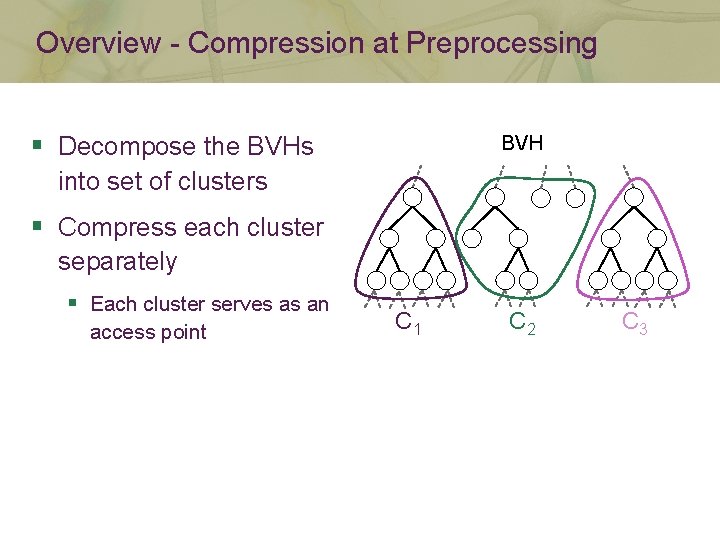
Overview - Compression at Preprocessing § Decompose the BVHs BVH into set of clusters § Compress each cluster separately § Each cluster serves as an access point C 1 C 2 C 3
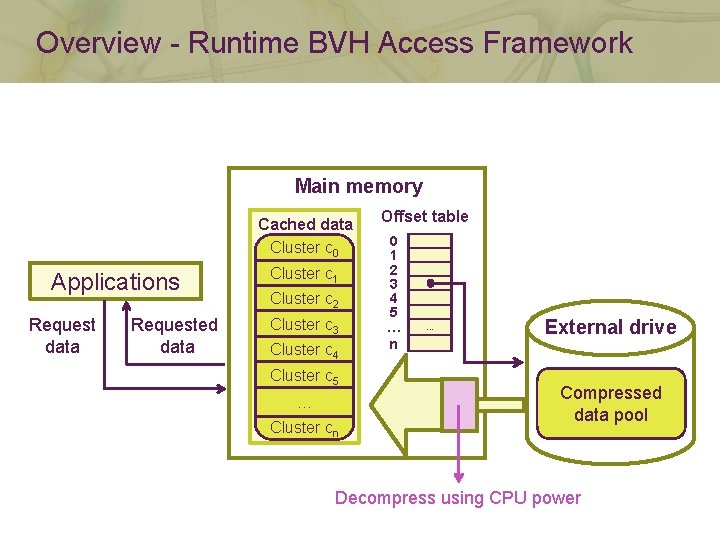
Overview - Runtime BVH Access Framework Main memory Cached data Cluster c 0 Applications Request data Requested data Cluster c 1 Cluster c 2 Cluster c 3 Cluster c 4 Cluster c 5 … Cluster cn Offset table 0 1 2 3 4 5 … n … External drive Compressed data pool Decompress using CPU power
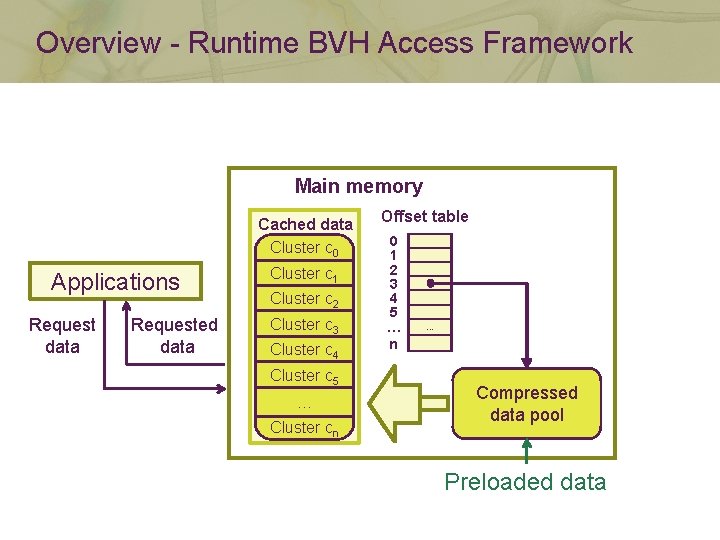
Overview - Runtime BVH Access Framework Main memory Cached data Cluster c 0 Applications Request data Requested data Cluster c 1 Cluster c 2 Cluster c 3 Cluster c 4 Cluster c 5 … Cluster cn Offset table 0 1 2 3 4 5 … n … Compressed data pool Preloaded data
Outline § Overview § Compression at preprocessing § Runtime data access framework § Results
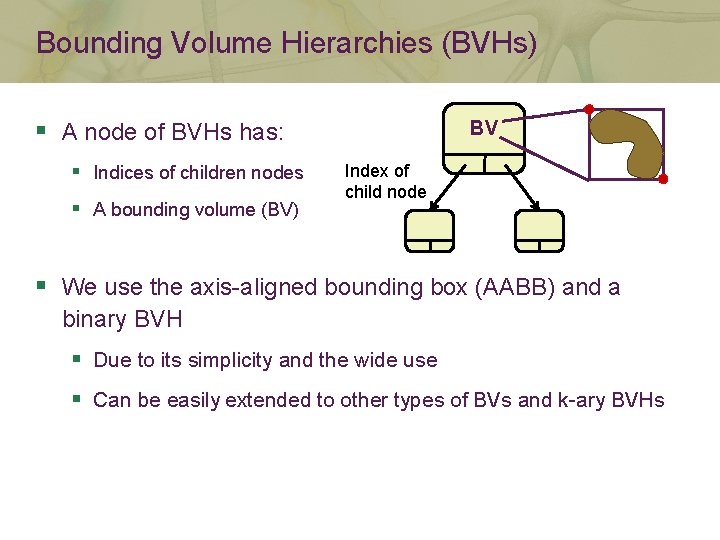
Bounding Volume Hierarchies (BVHs) § A node of BVHs has: § Indices of children nodes § A bounding volume (BV) BV Index of child node § We use the axis-aligned bounding box (AABB) and a binary BVH § Due to its simplicity and the wide use § Can be easily extended to other types of BVs and k-ary BVHs
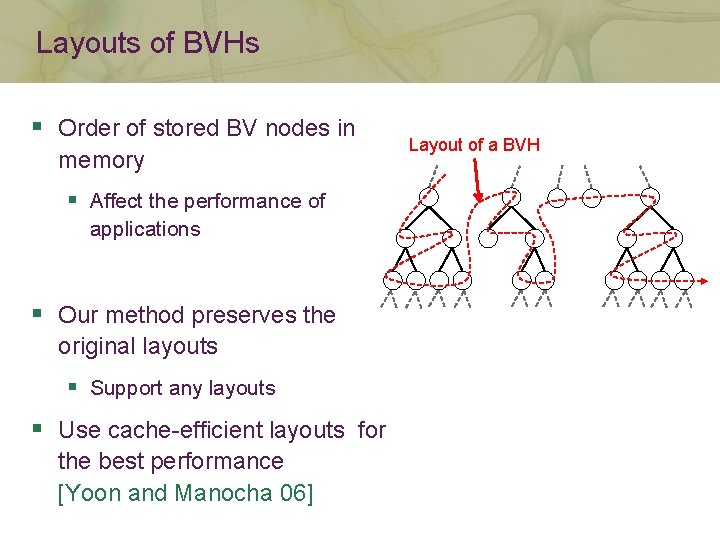
Layouts of BVHs § Order of stored BV nodes in memory § Affect the performance of applications § Our method preserves the original layouts § Support any layouts § Use cache-efficient layouts for the best performance [Yoon and Manocha 06] Layout of a BVH
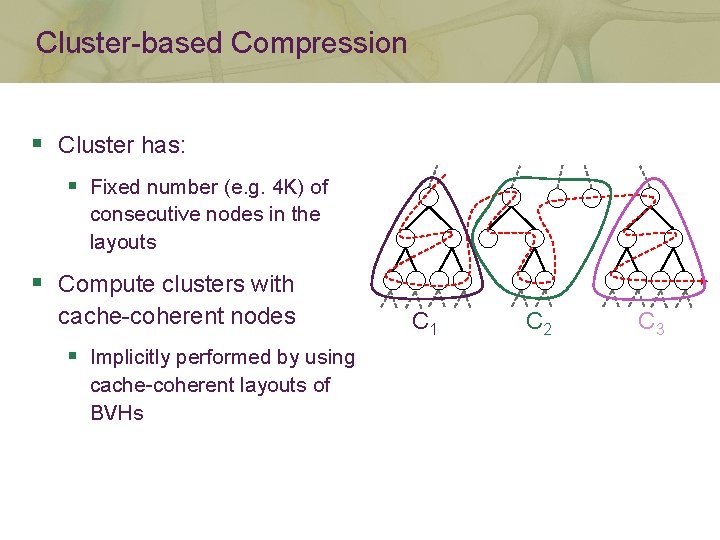
Cluster-based Compression § Cluster has: § Fixed number (e. g. 4 K) of consecutive nodes in the layouts § Compute clusters with cache-coherent nodes § Implicitly performed by using cache-coherent layouts of BVHs C 1 C 2 C 3
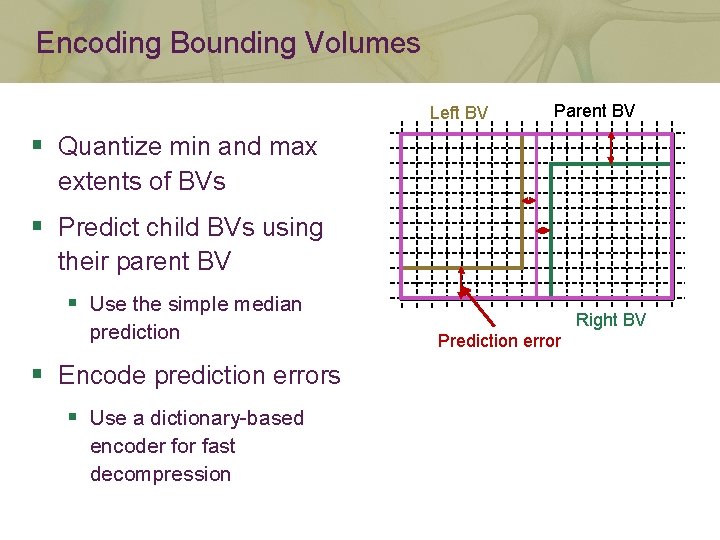
Encoding Bounding Volumes Left BV Parent BV § Quantize min and max extents of BVs § Predict child BVs using their parent BV § Use the simple median prediction § Encode prediction errors § Use a dictionary-based encoder for fast decompression Right BV Prediction error
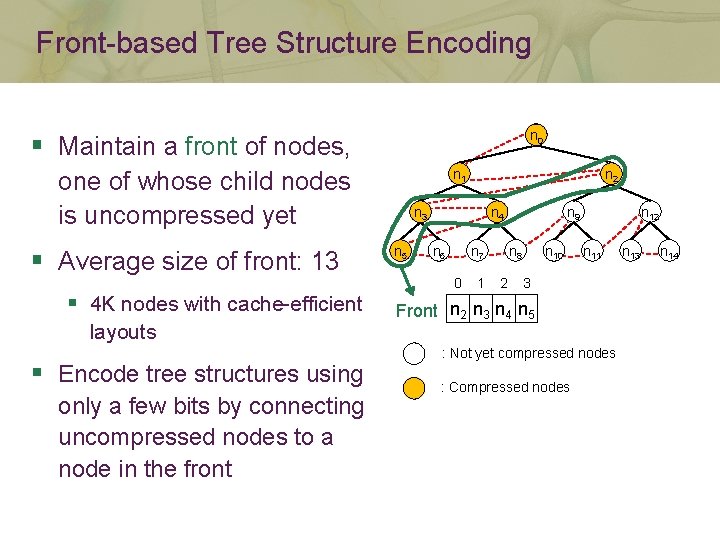
Front-based Tree Structure Encoding n 0 § Maintain a front of nodes, n 1 one of whose child nodes is uncompressed yet § Average size of front: 13 § 4 K nodes with cache-efficient layouts § Encode tree structures using only a few bits by connecting uncompressed nodes to a node in the front n 2 n 3 n 5 n 4 n 6 n 7 0 1 n 9 n 8 2 n 10 n 12 n 11 3 Front n 2 n 3 n 4 n 5 : Not yet compressed nodes : Compressed nodes n 13 n 14
Outline § Overview § Compression at preprocessing § Runtime data access framework § Results
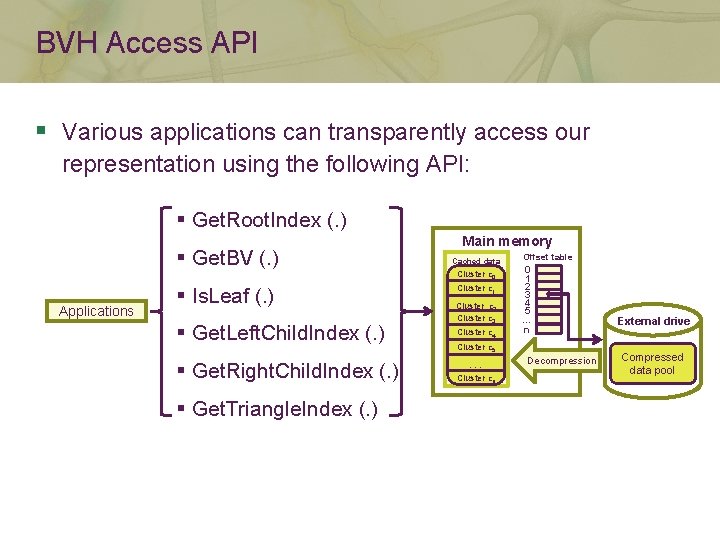
BVH Access API § Various applications can transparently access our representation using the following API: § Get. Root. Index (. ) § Get. BV (. ) Applications § Is. Leaf (. ) § Get. Left. Child. Index (. ) § Get. Right. Child. Index (. ) § Get. Triangle. Index (. ) Main memory Cached data Cluster c 0 Cluster c 1 Cluster c 2 Cluster c 3 Cluster c 4 Offset table 0 1 2 3 4 5 … n … Cluster c 5 … Cluster cn Decompression External drive Compressed data pool
Outline § Overview § Compression at preprocessing § Runtime data access framework § Results
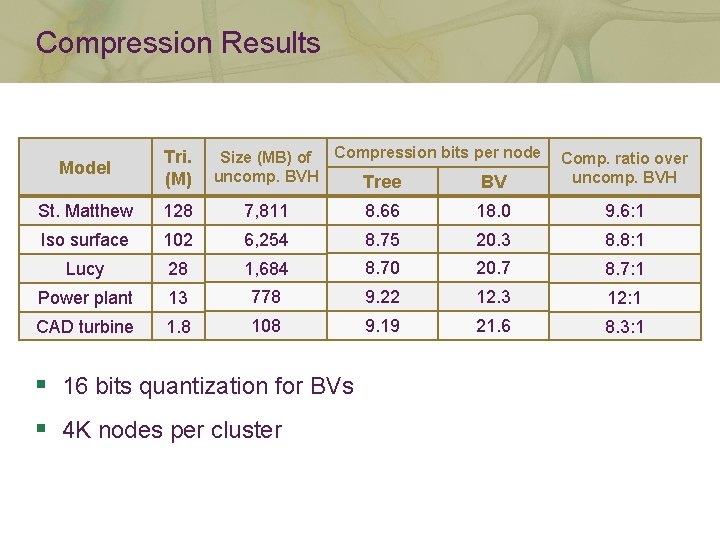
Compression Results Size (MB) of Compression bits per node uncomp. BVH Tree BV Model Tri. (M) St. Matthew 128 7, 811 8. 66 18. 0 9. 6: 1 Iso surface 102 6, 254 8. 75 20. 3 8. 8: 1 Lucy 28 1, 684 8. 70 20. 7 8. 7: 1 Power plant 13 778 9. 22 12. 3 12: 1 CAD turbine 1. 8 108 9. 19 21. 6 8. 3: 1 § 16 bits quantization for BVs § 4 K nodes per cluster Comp. ratio over uncomp. BVH
Benchmark Applications § Ray tracing § Typically traverses large portions of BVHs § Collision detection § Accesses smaller and more localized portions of BVHs than ray tracing
Video for Benchmark Applications
Performance Improvement § Mainly due to higher I/O performance § Reduce the data size by using compression → Reduce or remove the expensive disk I/O time § Use CPU power to efficiently decompress the data
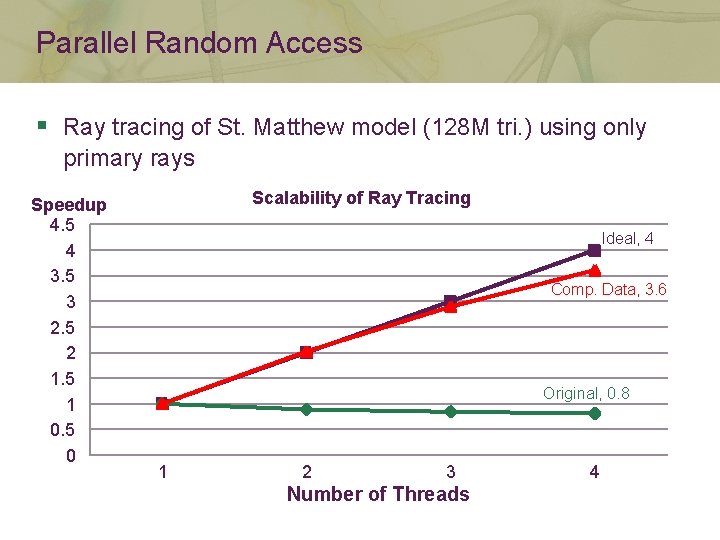
Parallel Random Access § Ray tracing of St. Matthew model (128 M tri. ) using only primary rays Speedup 4. 5 4 3. 5 3 2. 5 2 1. 5 1 0. 5 0 Scalability of Ray Tracing Ideal, 4 Comp. Data, 3. 6 Original, 0. 8 1 2 3 Number of Threads 4
Limitation § Lower (by up to 3%) the performance with small models which can fit in main memory § Overhead of identifying clusters § Less tight BVs due to a conservative quantization
Summary & Conclusion § Low storage requirement § Achieve up to a 12: 1 compression ratio § Improved performance with random accessibility § Achieve a 4: 1 runtime performance improvement § Wide applicability § Allows various applications to access the compressed BVHs § High scalability § Achieve a 3. 6: 1 performance improvement when using 4 threads over single thread
Future Work § Compact in-core representations § Apply to highly parallel architectures § GPU § Larrabee § Apply to levels-of-detail (LOD) hierarchies
Acknowledgments § Members of SGLab. in KAIST § Model contributors § Funding agencies § KAIST seed grant § Ministry of Knowledge Economy § Samsung § Microsoft Research Asia § Korea Research Foundation
Any Questions? Q&A Thank you!
- Slides: 36