Programmable Networks Lecture 3 Stateful applications Sndor Laki
Programmable Networks Lecture 3 – Stateful applications Sándor Laki, Ph. D Communication Networks Laboratory Dept. of Information Systems, Faculty of Informatics ELTE Eötvös Loránd University lakis@elte. hu http: //lakis. web. elte. hu Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
this week • Stateful programming • How to store state information? • Fast reroute – an example application • Probabilistic data structures I • Bloom filters Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
Stateful programming Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
stateless vs stateful stateless objects reinitialized for each packet variables headers stateful objects keep state between packets tables registers counters meters … Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
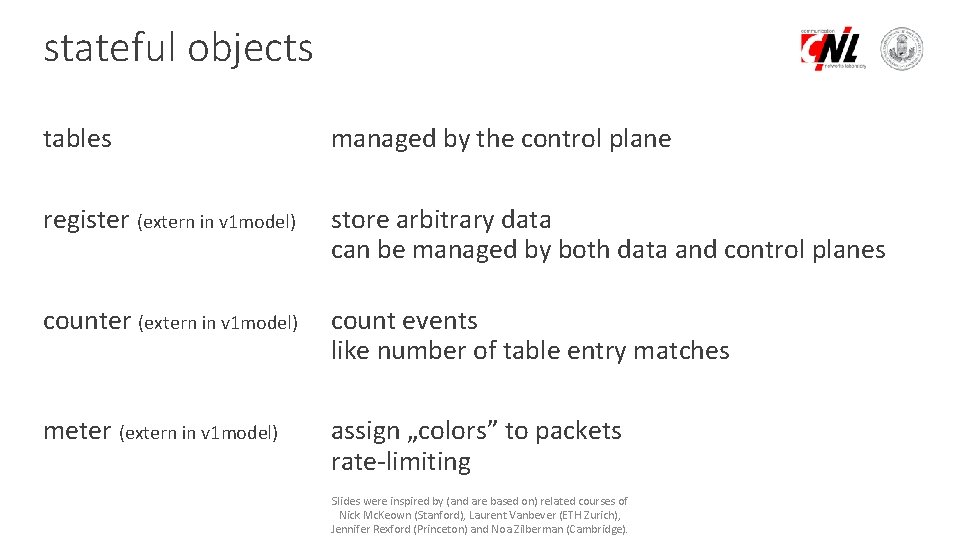
stateful objects tables managed by the control plane register (extern in v 1 model) store arbitrary data can be managed by both data and control planes counter (extern in v 1 model) count events like number of table entry matches meter (extern in v 1 model) assign „colors” to packets rate-limiting Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
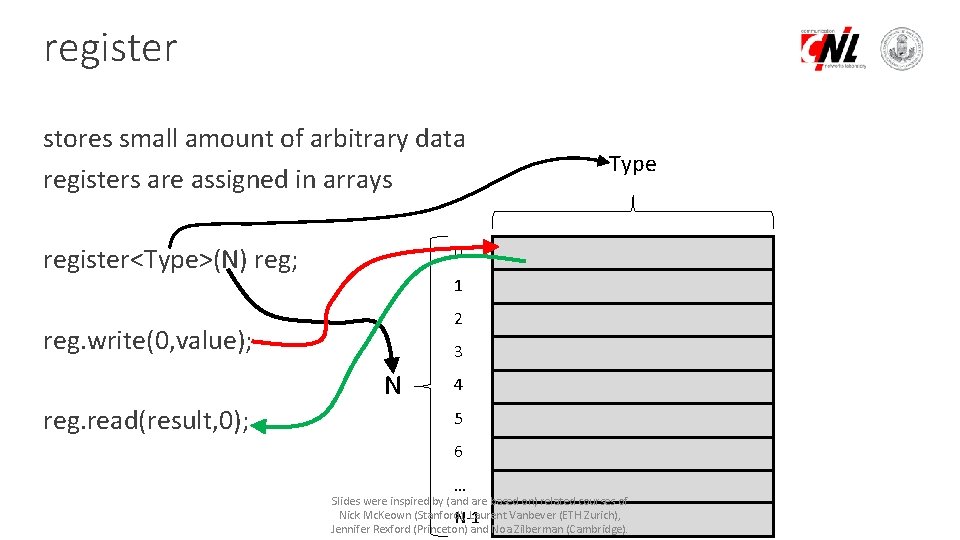
register stores small amount of arbitrary data registers are assigned in arrays 0 register<Type>(N) reg; 1 2 reg. write(0, value); 3 N reg. read(result, 0); Type 4 5 6 … Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), N-1 Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
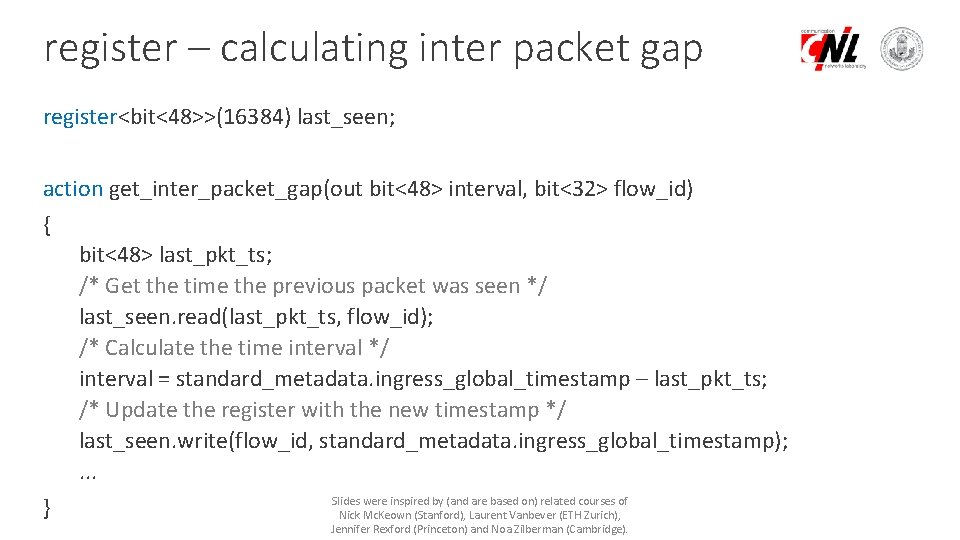
register – calculating inter packet gap register<bit<48>>(16384) last_seen; action get_inter_packet_gap(out bit<48> interval, bit<32> flow_id) { bit<48> last_pkt_ts; /* Get the time the previous packet was seen */ last_seen. read(last_pkt_ts, flow_id); /* Calculate the time interval */ interval = standard_metadata. ingress_global_timestamp – last_pkt_ts; /* Update the register with the new timestamp */ last_seen. write(flow_id, standard_metadata. ingress_global_timestamp); . . . Slides were inspired by (and are based on) related courses of } Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
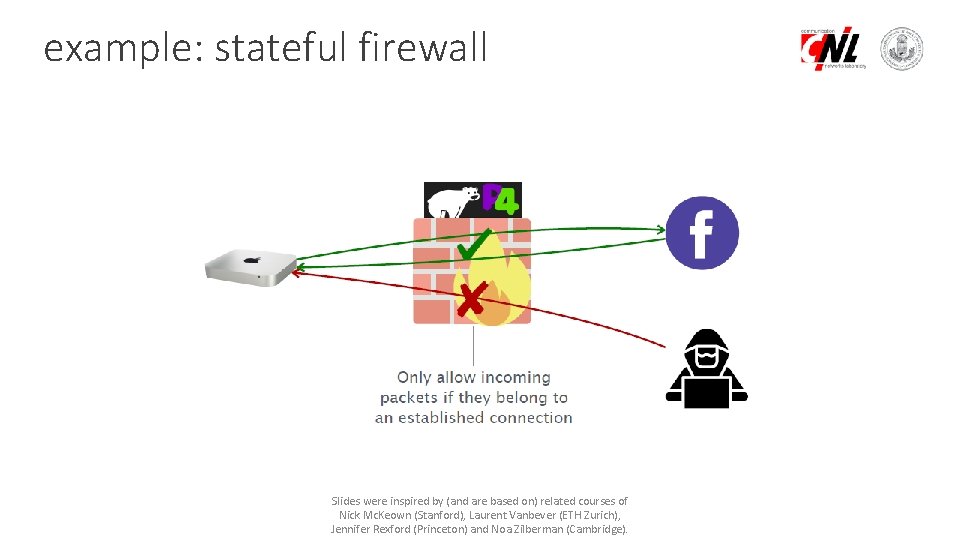
example: stateful firewall Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
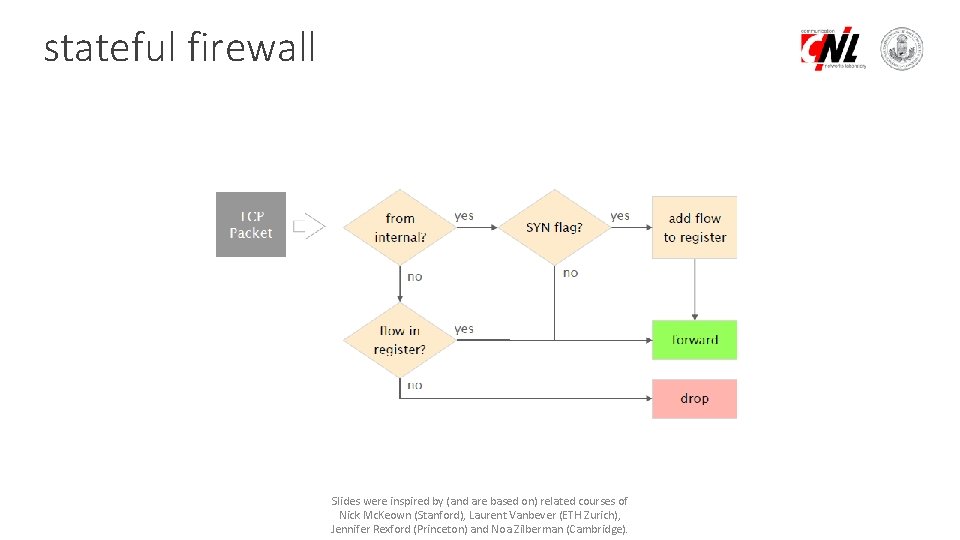
stateful firewall Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
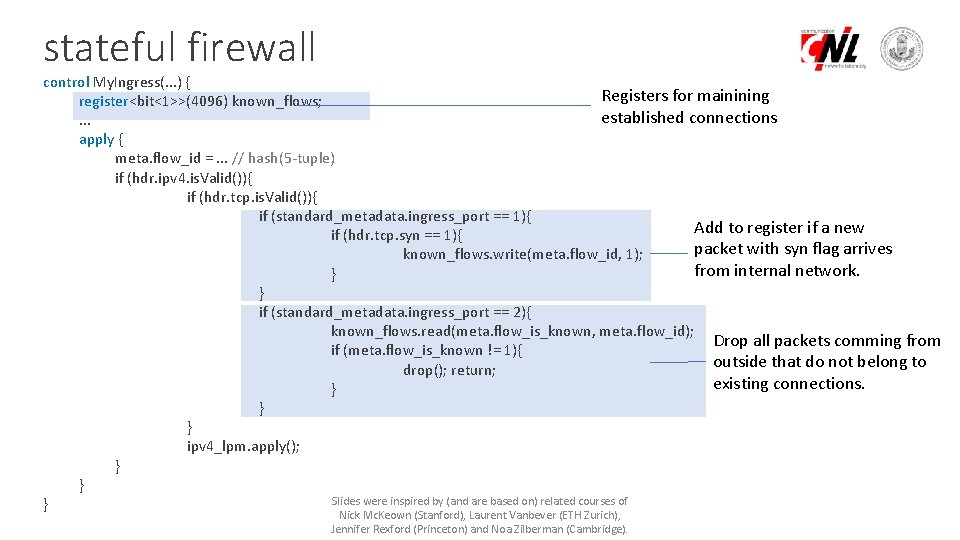
stateful firewall control My. Ingress(. . . ) { Registers for mainining register<bit<1>>(4096) known_flows; established connections. . . apply { meta. flow_id =. . . // hash(5 -tuple) if (hdr. ipv 4. is. Valid()){ if (hdr. tcp. is. Valid()){ if (standard_metadata. ingress_port == 1){ Add to register if a new if (hdr. tcp. syn == 1){ packet with syn flag arrives known_flows. write(meta. flow_id, 1); from internal network. } } if (standard_metadata. ingress_port == 2){ known_flows. read(meta. flow_is_known, meta. flow_id); Drop all packets comming from if (meta. flow_is_known != 1){ outside that do not belong to drop(); return; existing connections. } } } ipv 4_lpm. apply(); } } Slides were inspired by (and are based on) related courses of } Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
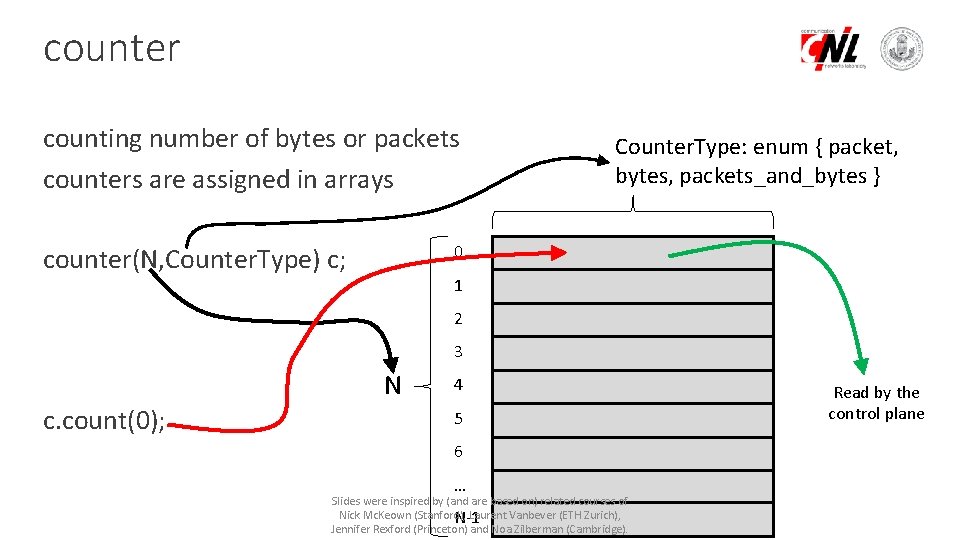
counter counting number of bytes or packets counters are assigned in arrays Counter. Type: enum { packet, bytes, packets_and_bytes } 0 counter(N, Counter. Type) c; 1 2 3 N c. count(0); 4 5 6 … Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), N-1 Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge). Read by the control plane
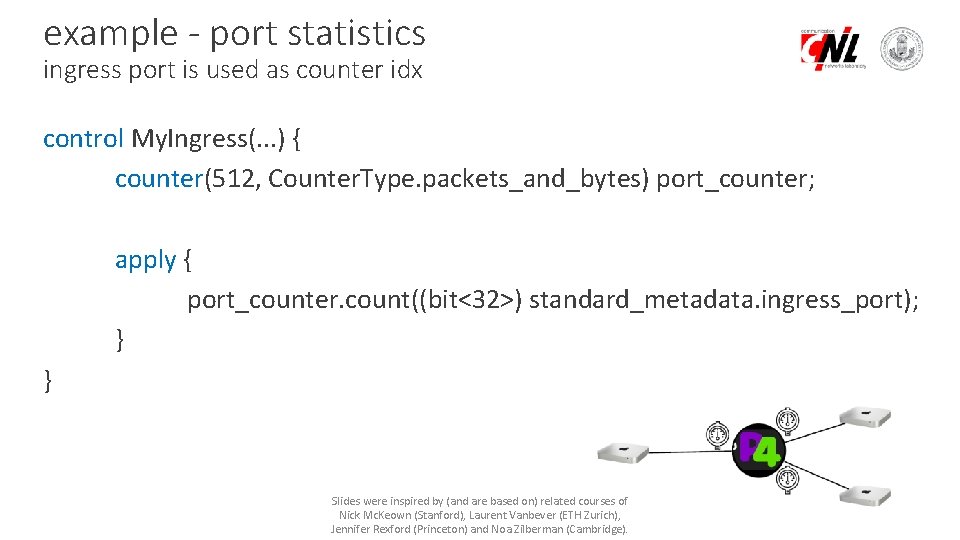
example - port statistics ingress port is used as counter idx control My. Ingress(. . . ) { counter(512, Counter. Type. packets_and_bytes) port_counter; apply { port_counter. count((bit<32>) standard_metadata. ingress_port); } } Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
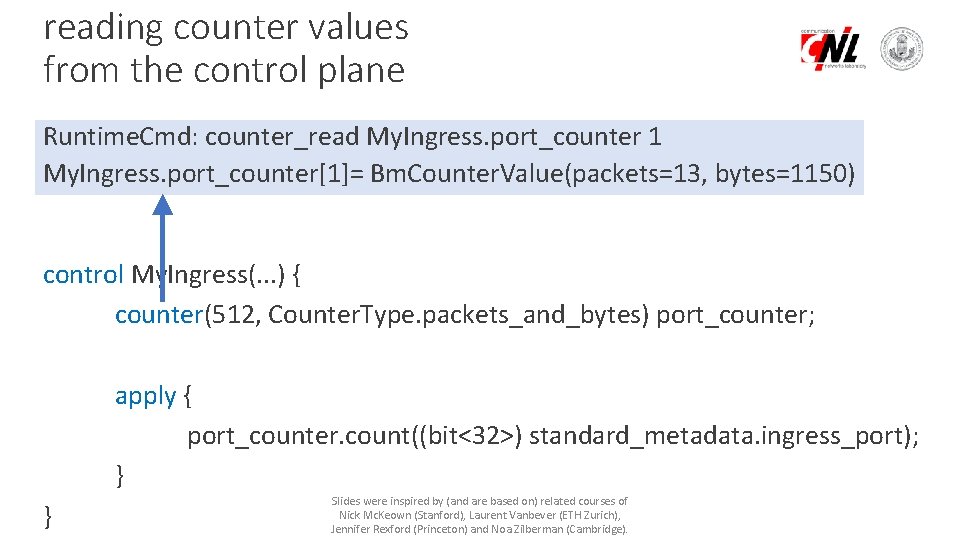
reading counter values from the control plane Runtime. Cmd: counter_read My. Ingress. port_counter 1 My. Ingress. port_counter[1]= Bm. Counter. Value(packets=13, bytes=1150) control My. Ingress(. . . ) { counter(512, Counter. Type. packets_and_bytes) port_counter; apply { port_counter. count((bit<32>) standard_metadata. ingress_port); } } Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
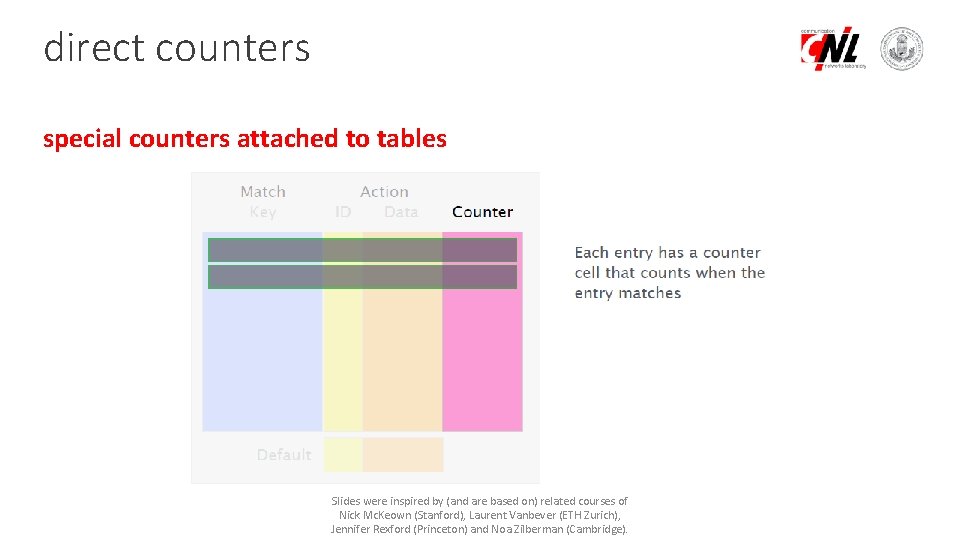
direct counters special counters attached to tables Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
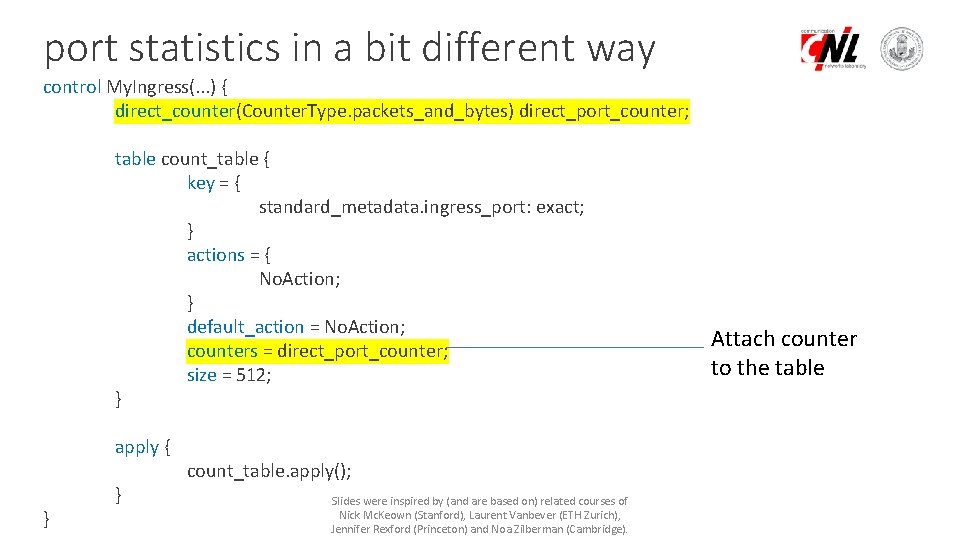
port statistics in a bit different way control My. Ingress(. . . ) { direct_counter(Counter. Type. packets_and_bytes) direct_port_counter; table count_table { key = { standard_metadata. ingress_port: exact; } actions = { No. Action; } default_action = No. Action; counters = direct_port_counter; size = 512; } apply { } } count_table. apply(); Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge). Attach counter to the table
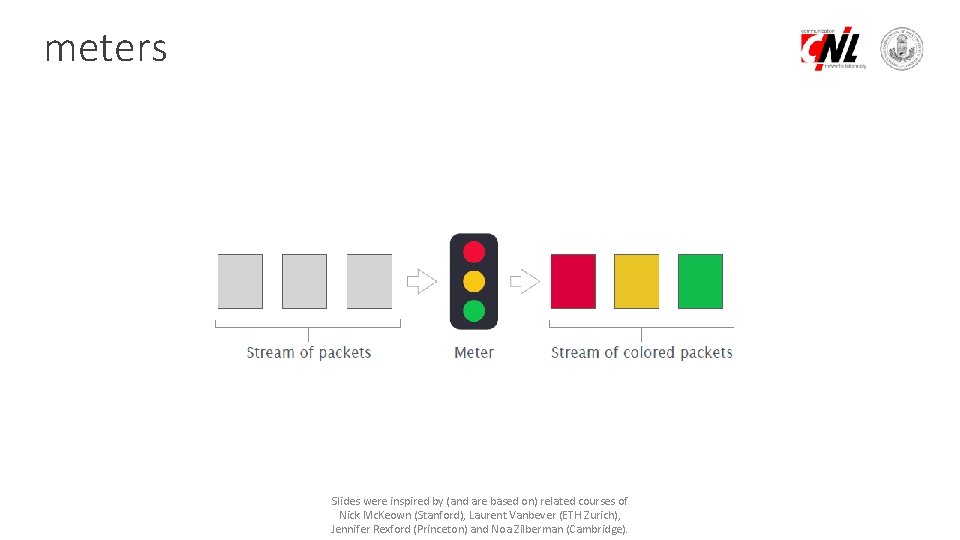
meters Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
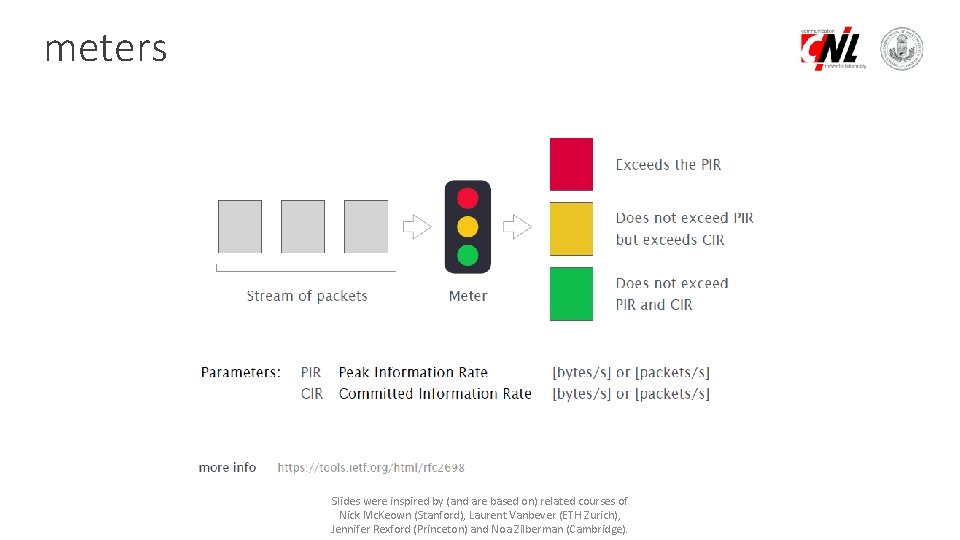
meters Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
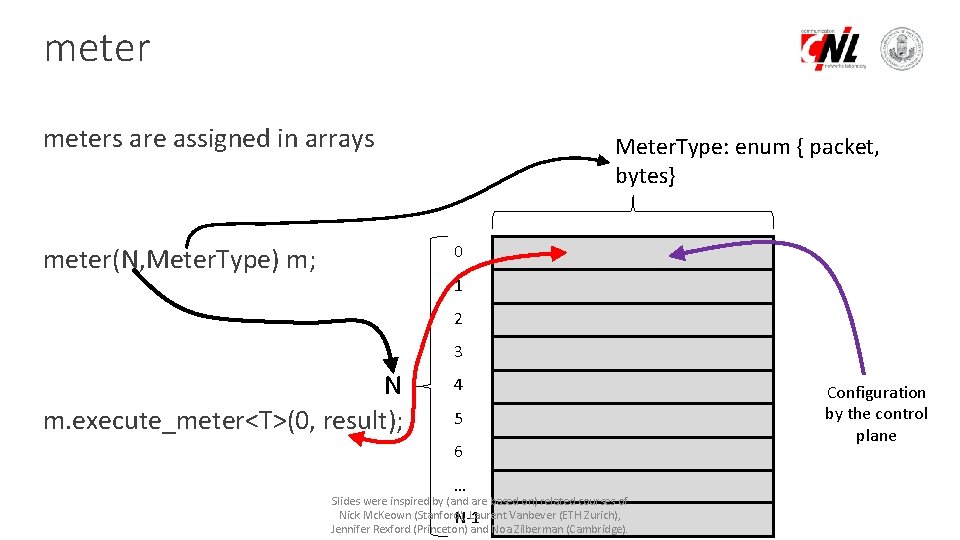
meters are assigned in arrays Meter. Type: enum { packet, bytes} 0 meter(N, Meter. Type) m; 1 2 3 N m. execute_meter<T>(0, result); 4 5 6 … Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), N-1 Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge). Configuration by the control plane
example: rate-limiter Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
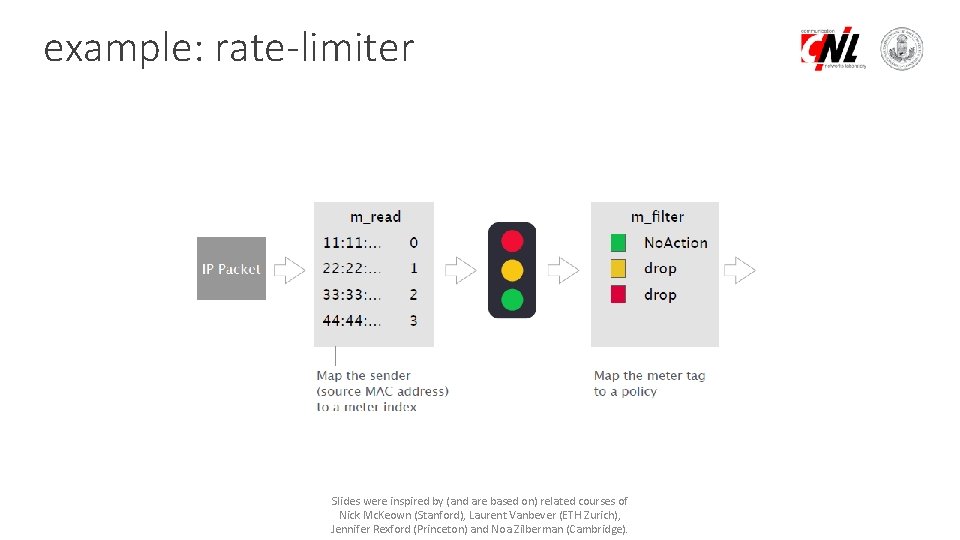
example: rate-limiter Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
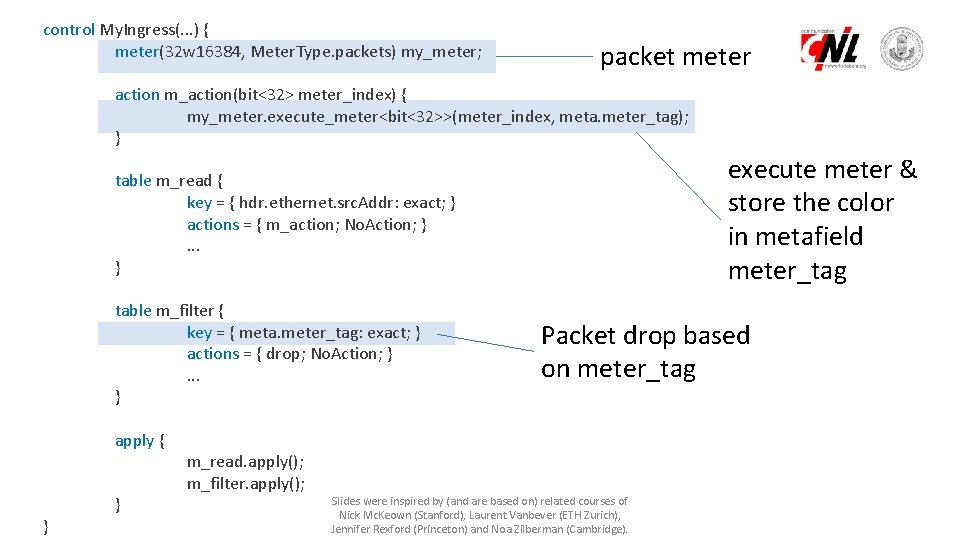
control My. Ingress(. . . ) { meter(32 w 16384, Meter. Type. packets) my_meter; packet meter action m_action(bit<32> meter_index) { my_meter. execute_meter<bit<32>>(meter_index, meta. meter_tag); } execute meter & store the color in metafield meter_tag table m_read { key = { hdr. ethernet. src. Addr: exact; } actions = { m_action; No. Action; }. . . } table m_filter { key = { meta. meter_tag: exact; } actions = { drop; No. Action; }. . . } apply { } } m_read. apply(); m_filter. apply(); Packet drop based on meter_tag Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
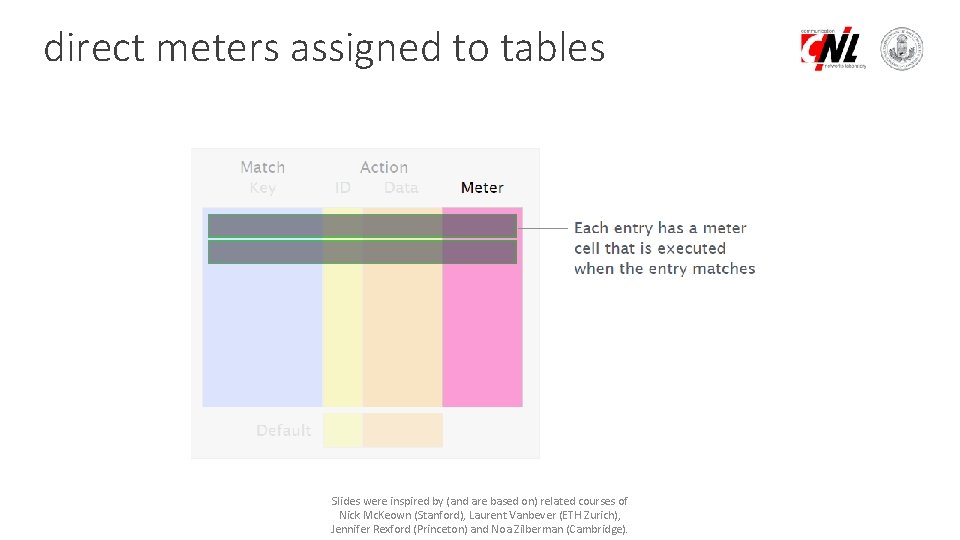
direct meters assigned to tables Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
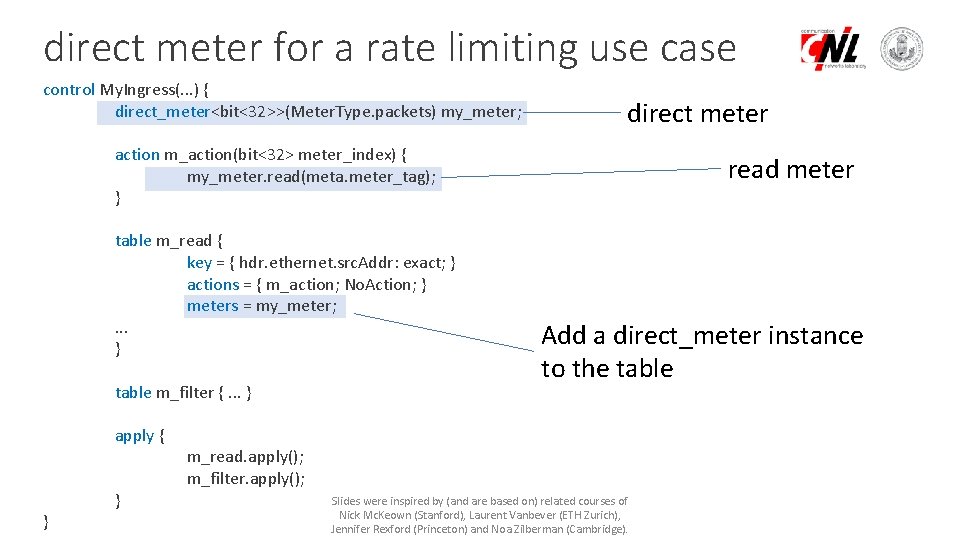
direct meter for a rate limiting use case control My. Ingress(. . . ) { direct_meter<bit<32>>(Meter. Type. packets) my_meter; direct meter action m_action(bit<32> meter_index) { my_meter. read(meta. meter_tag); } table m_read { key = { hdr. ethernet. src. Addr: exact; } actions = { m_action; No. Action; } meters = my_meter; . . . } table m_filter {. . . } apply { } } read meter Add a direct_meter instance to the table m_read. apply(); m_filter. apply(); Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
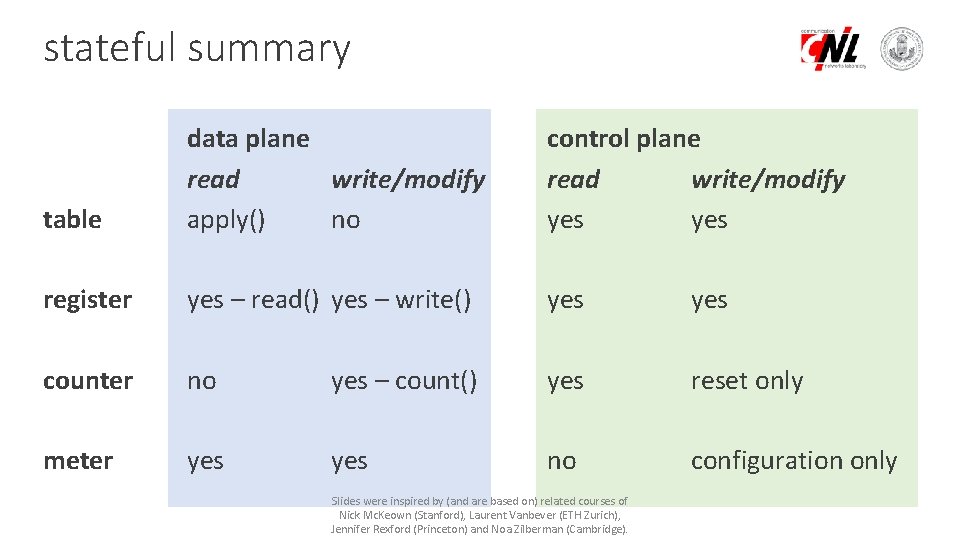
stateful summary table data plane read write/modify apply() no control plane read write/modify yes register yes – read() yes – write() yes counter no yes – count() yes reset only meter yes no configuration only Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
An example application https: //www. net. t-labs. tu-berlin. de/~stefan/neat 18. pdf https: //www. youtube. com/watch? v=G 4 L 2 ys-_W 9 w#t=26 m 26 s https: //p 4. org/assets/P 4 WS_2018/Marco_Chiesa. pdf Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
Probabilistic data structures I. Bloom filters Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
programming advanced data structs building blocks built-in stateful data structures arrays of registers, counters or meters lots of limitations limited number of operations and memory Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
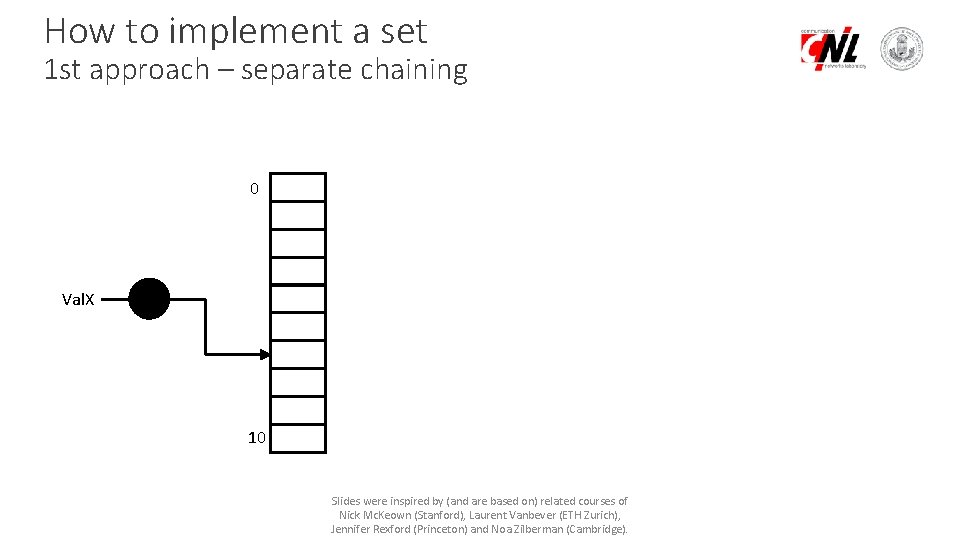
How to implement a set 1 st approach – separate chaining 0 Val. X 10 Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
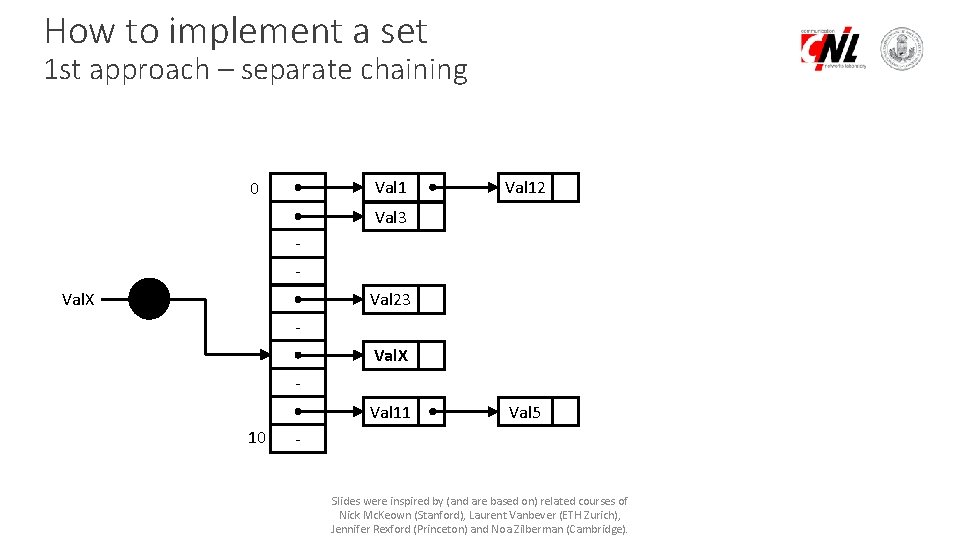
How to implement a set 1 st approach – separate chaining Val 1 0 Val 12 Val 3 Val. X Val 23 Val. X Val 11 10 Val 5 Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
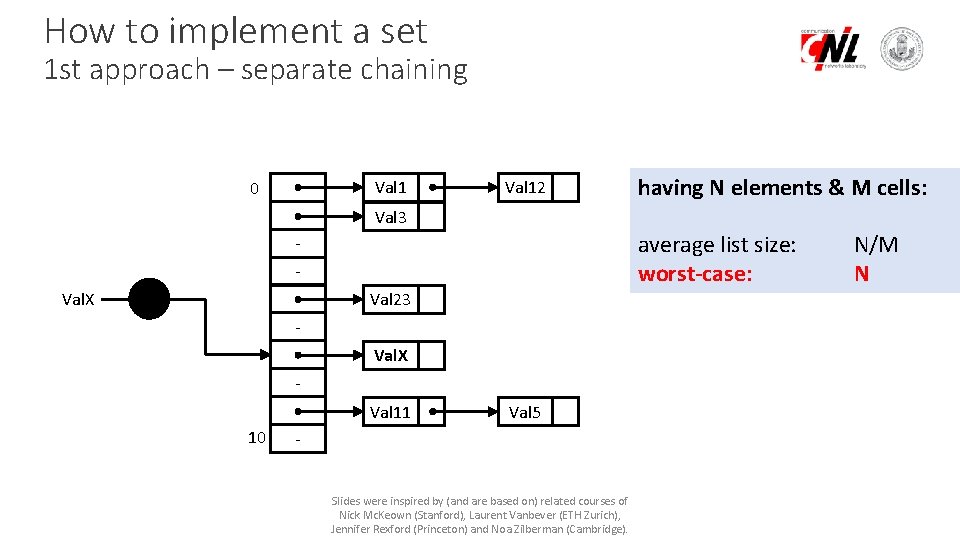
How to implement a set 1 st approach – separate chaining Val 1 0 Val 12 having N elements & M cells: Val 3 average list size: worst-case: Val. X Val 23 Val. X Val 11 10 Val 5 Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge). N/M N
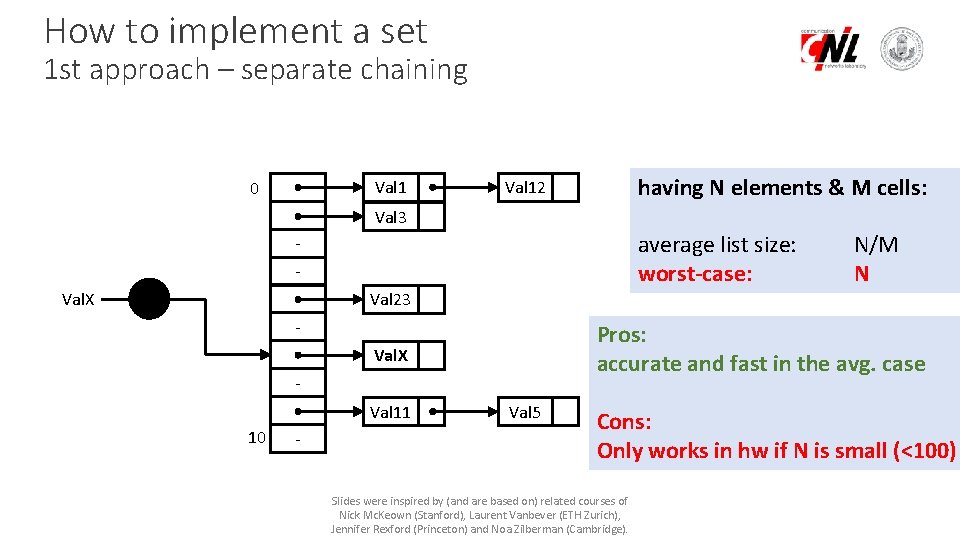
How to implement a set 1 st approach – separate chaining Val 1 0 having N elements & M cells: Val 12 Val 3 average list size: worst-case: Val. X N/M N Val 23 - Pros: accurate and fast in the avg. case Val. X Val 11 10 - Val 5 Cons: Only works in hw if N is small (<100) Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
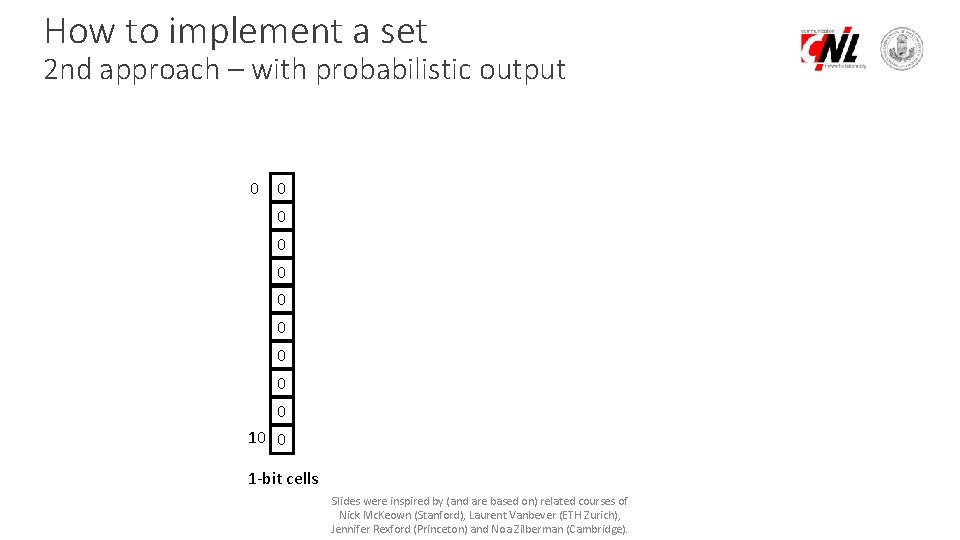
How to implement a set 2 nd approach – with probabilistic output 0 0 0 0 0 10 0 1 -bit cells Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
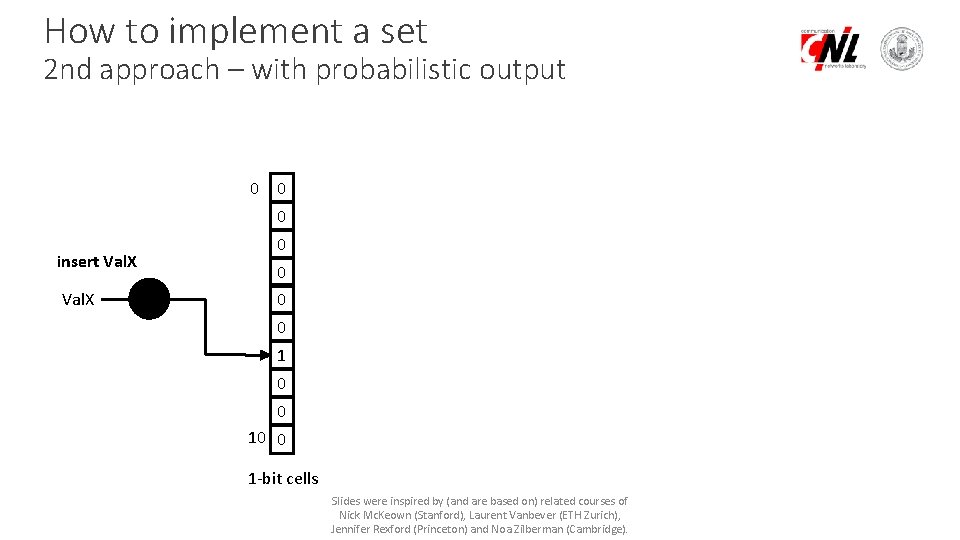
How to implement a set 2 nd approach – with probabilistic output 0 0 0 insert Val. X 0 0 1 -bit cells Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
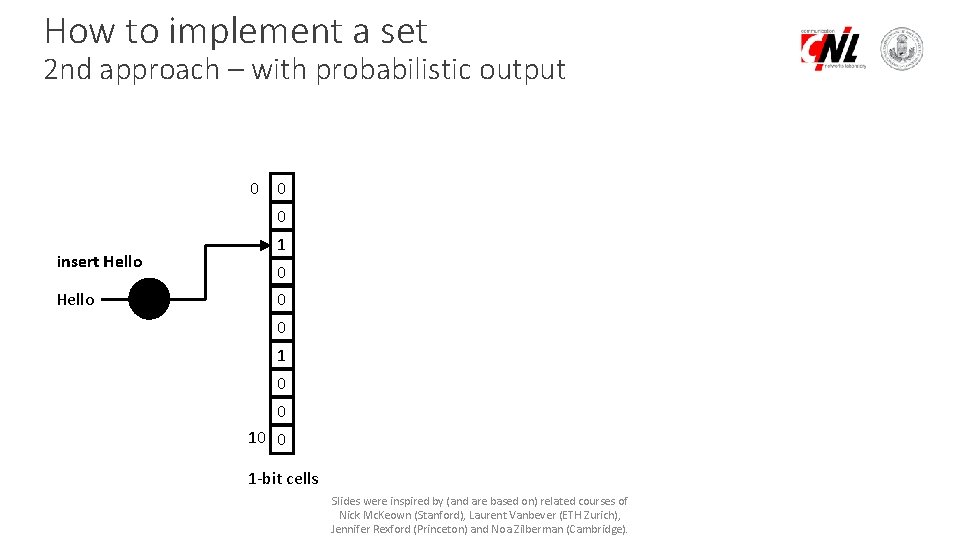
How to implement a set 2 nd approach – with probabilistic output 0 0 0 insert Hello 1 0 0 0 10 0 1 -bit cells Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
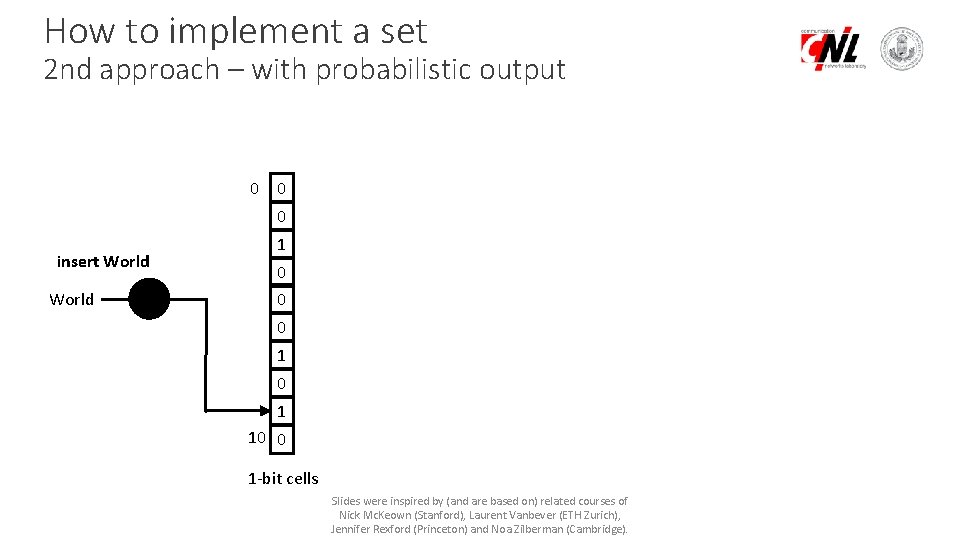
How to implement a set 2 nd approach – with probabilistic output 0 0 0 insert World 1 0 0 0 1 10 0 1 -bit cells Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
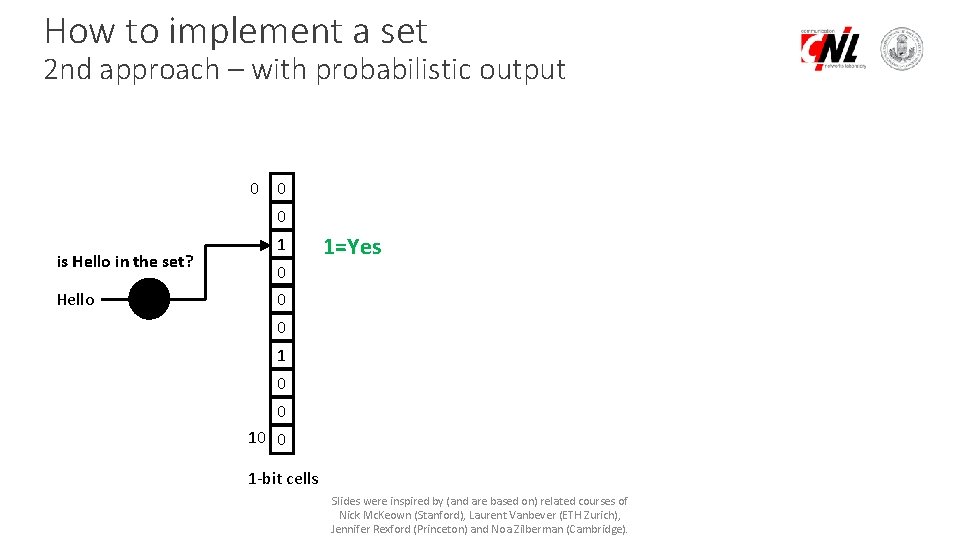
How to implement a set 2 nd approach – with probabilistic output 0 0 0 is Hello in the set? Hello 1 1=Yes 0 0 0 10 0 1 -bit cells Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
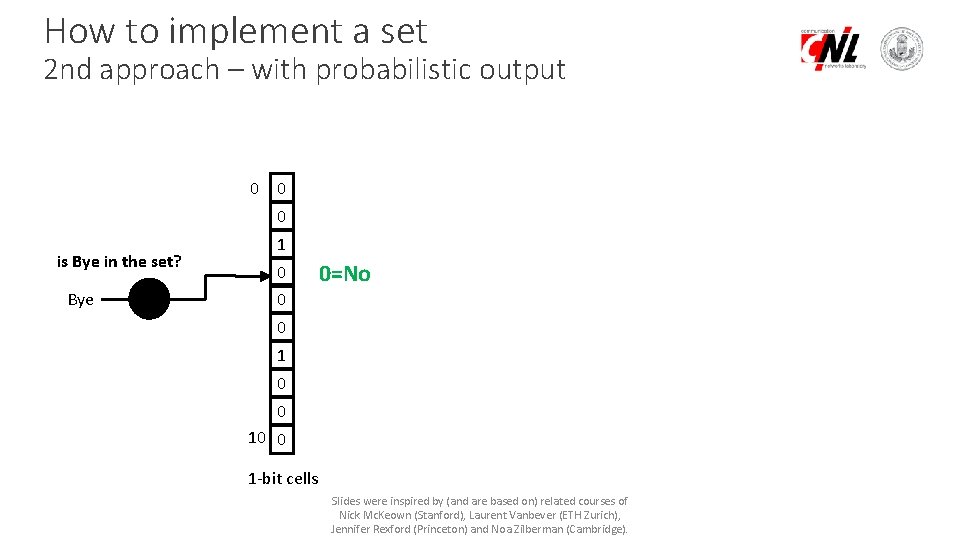
How to implement a set 2 nd approach – with probabilistic output 0 0 0 is Bye in the set? Bye 1 0 0=No 0 0 10 0 1 -bit cells Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
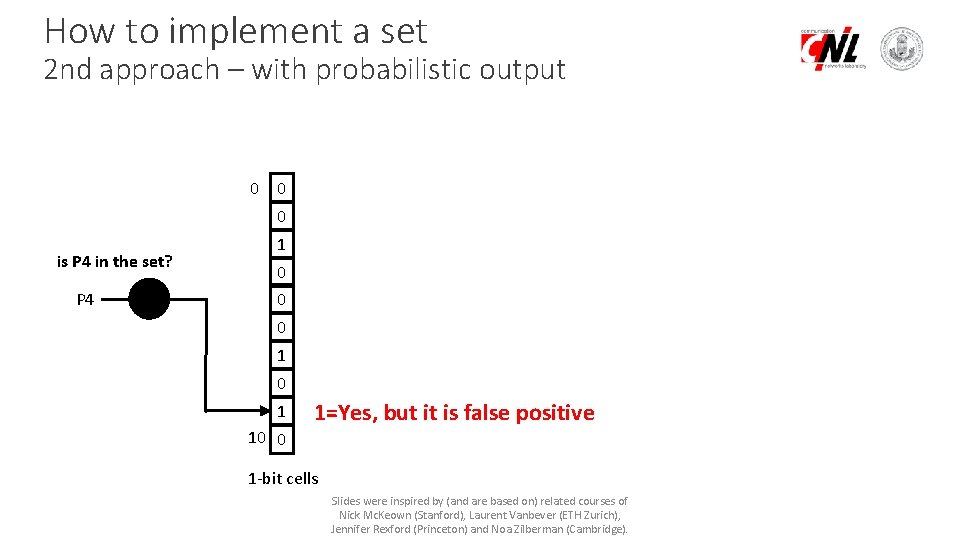
How to implement a set 2 nd approach – with probabilistic output 0 0 0 is P 4 in the set? P 4 1 0 0 0 1 10 0 1=Yes, but it is false positive 1 -bit cells Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
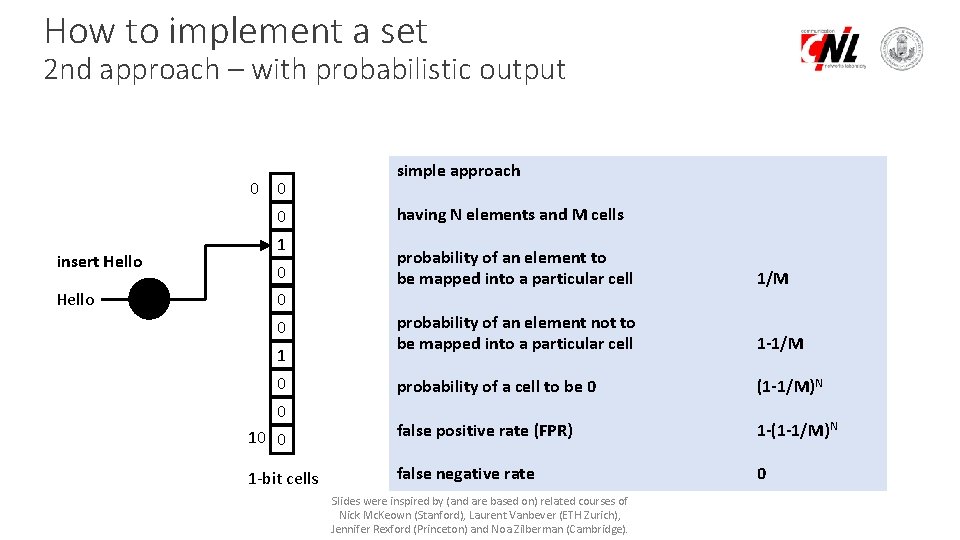
How to implement a set 2 nd approach – with probabilistic output 0 0 0 insert Hello 1 simple approach having N elements and M cells probability of an element to be mapped into a particular cell 1/M probability of an element not to be mapped into a particular cell 1 -1/M probability of a cell to be 0 (1 -1/M)N 10 0 false positive rate (FPR) 1 -(1 -1/M)N 1 -bit cells false negative rate 0 0 1 0 0 Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
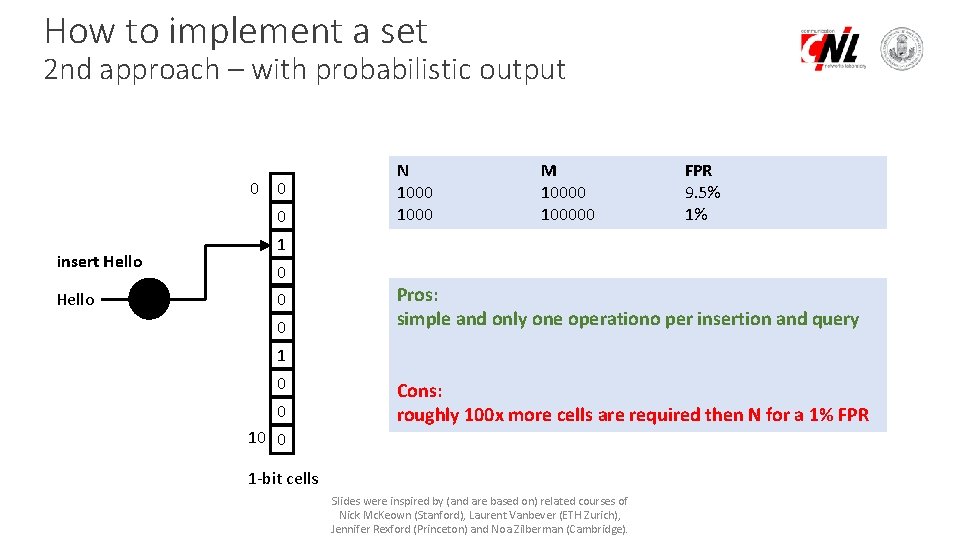
How to implement a set 2 nd approach – with probabilistic output 0 0 0 insert Hello N 1000 M 100000 FPR 9. 5% 1% 1 0 0 0 Pros: simple and only one operationo per insertion and query 1 0 0 10 0 Cons: roughly 100 x more cells are required then N for a 1% FPR 1 -bit cells Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
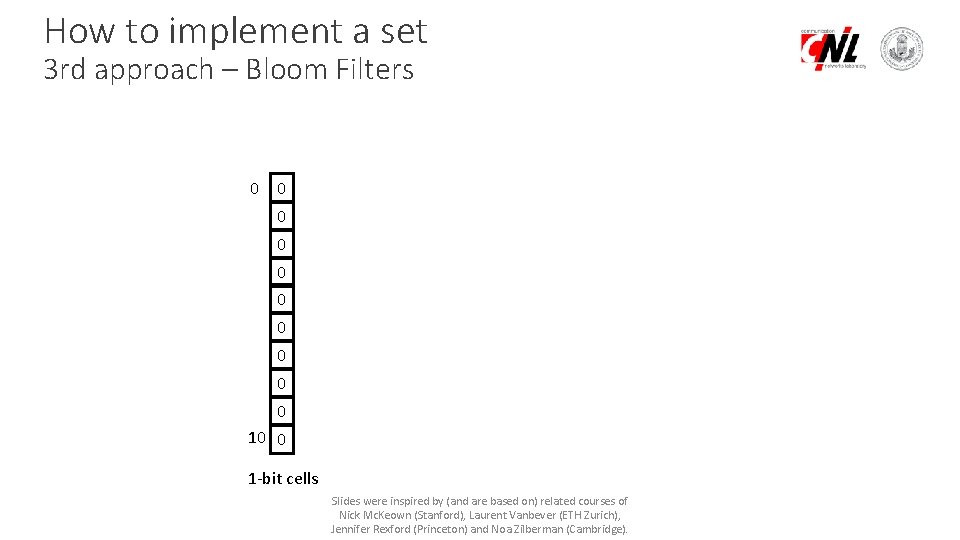
How to implement a set 3 rd approach – Bloom Filters 0 0 0 0 0 10 0 1 -bit cells Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
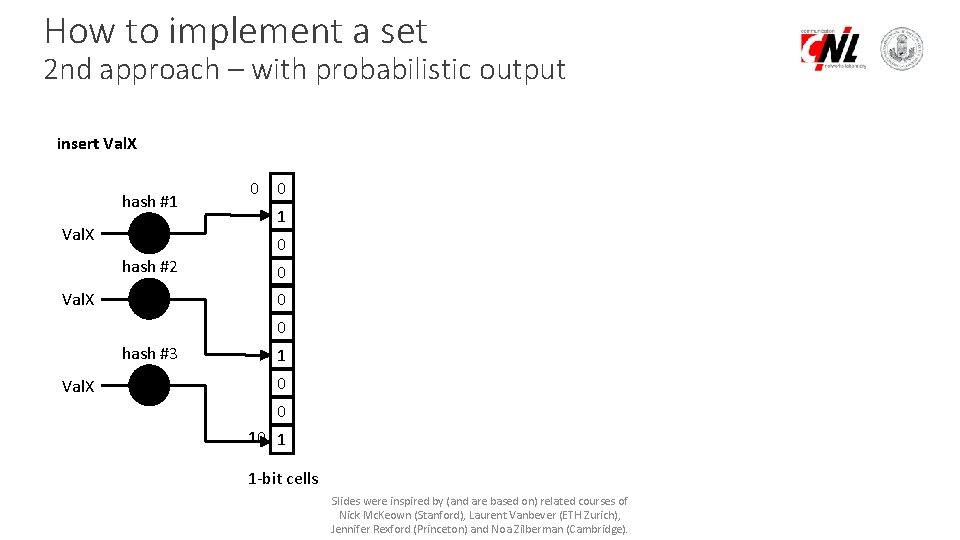
How to implement a set 2 nd approach – with probabilistic output insert Val. X hash #1 Val. X 0 0 1 0 hash #2 Val. X 0 0 0 hash #3 Val. X 1 0 0 10 1 1 -bit cells Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
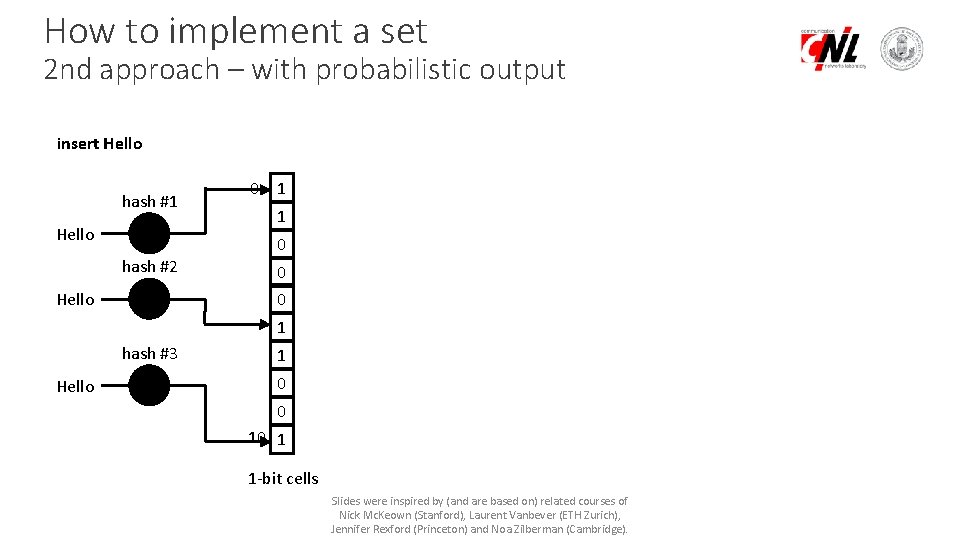
How to implement a set 2 nd approach – with probabilistic output insert Hello hash #1 Hello 0 1 1 0 hash #2 Hello 0 0 1 hash #3 Hello 1 0 0 10 1 1 -bit cells Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
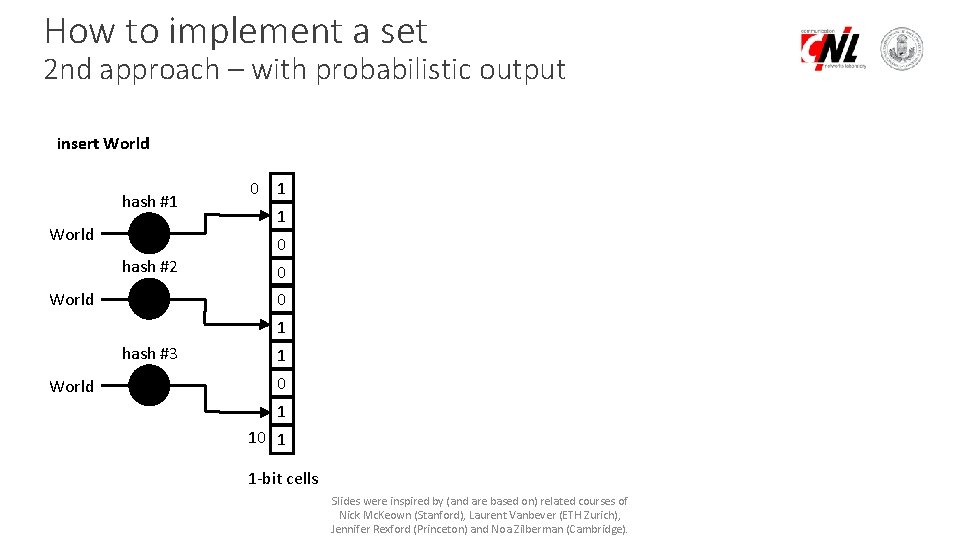
How to implement a set 2 nd approach – with probabilistic output insert World hash #1 World 0 1 1 0 hash #2 World 0 0 1 hash #3 World 1 0 1 1 -bit cells Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
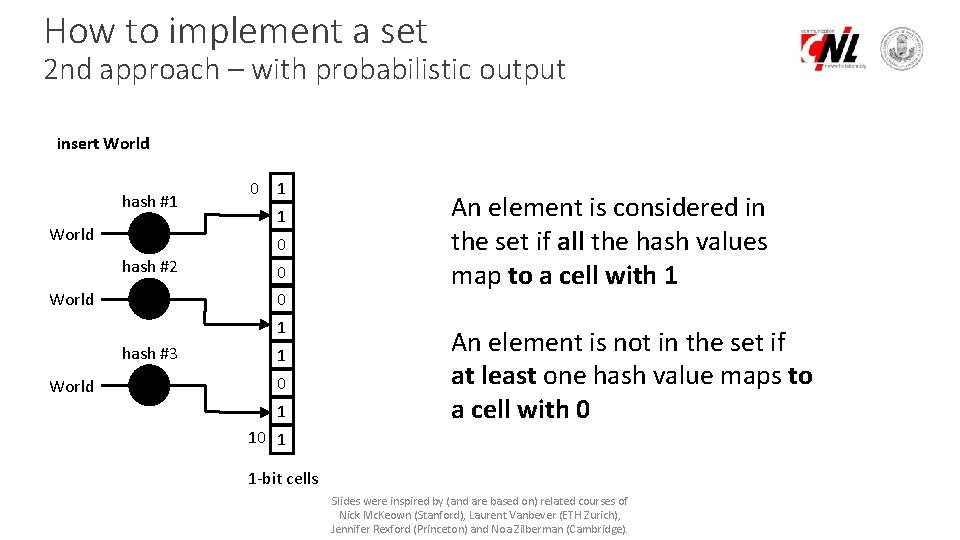
How to implement a set 2 nd approach – with probabilistic output insert World hash #1 World 0 1 1 0 hash #2 World 0 0 1 hash #3 World 1 0 1 An element is considered in the set if all the hash values map to a cell with 1 An element is not in the set if at least one hash value maps to a cell with 0 10 1 1 -bit cells Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
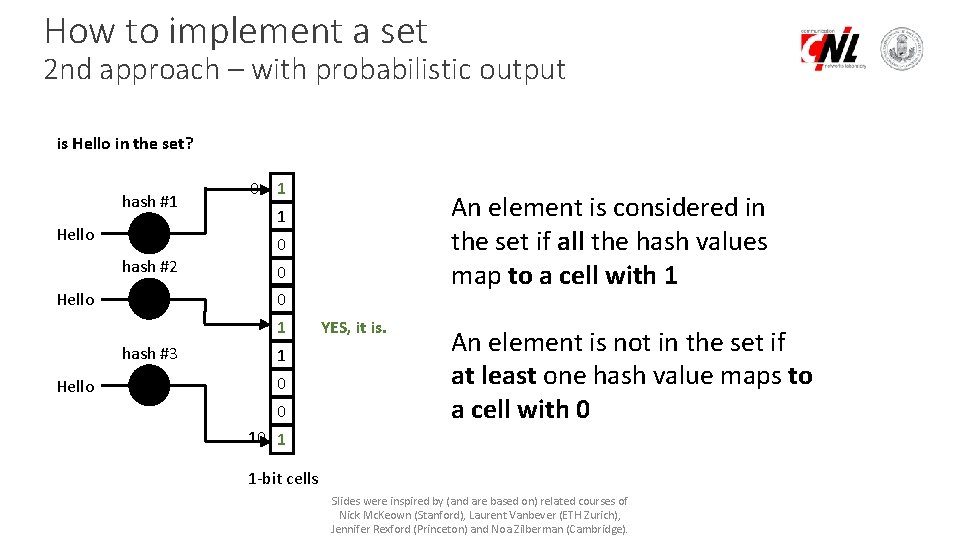
How to implement a set 2 nd approach – with probabilistic output is Hello in the set? hash #1 Hello 0 1 0 hash #2 Hello 0 0 1 hash #3 Hello An element is considered in the set if all the hash values map to a cell with 1 1 1 0 0 YES, it is. An element is not in the set if at least one hash value maps to a cell with 0 10 1 1 -bit cells Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
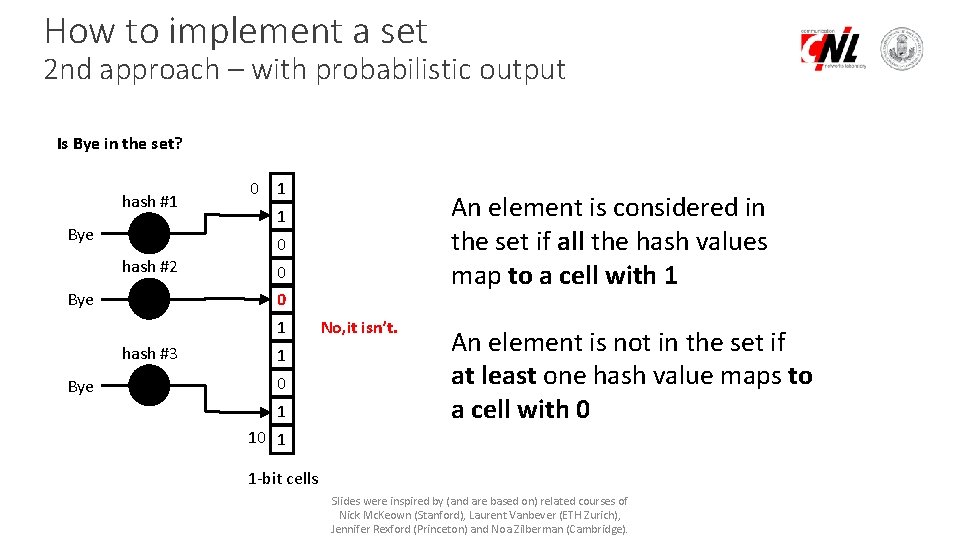
How to implement a set 2 nd approach – with probabilistic output Is Bye in the set? hash #1 Bye 0 1 0 hash #2 Bye 0 0 1 hash #3 Bye An element is considered in the set if all the hash values map to a cell with 1 1 1 0 1 No, it isn’t. An element is not in the set if at least one hash value maps to a cell with 0 10 1 1 -bit cells Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
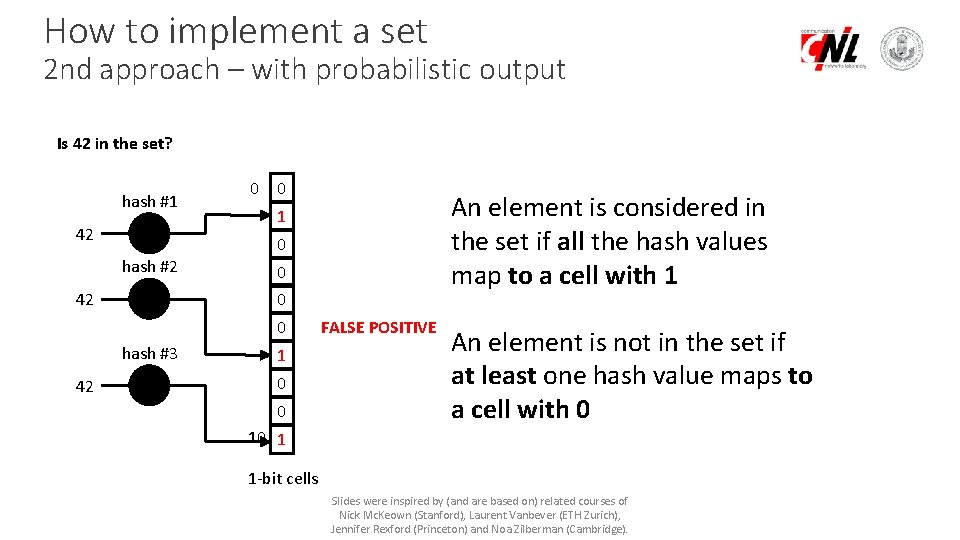
How to implement a set 2 nd approach – with probabilistic output Is 42 in the set? hash #1 42 0 0 0 hash #2 42 0 0 0 hash #3 42 An element is considered in the set if all the hash values map to a cell with 1 1 1 0 0 FALSE POSITIVE An element is not in the set if at least one hash value maps to a cell with 0 10 1 1 -bit cells Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
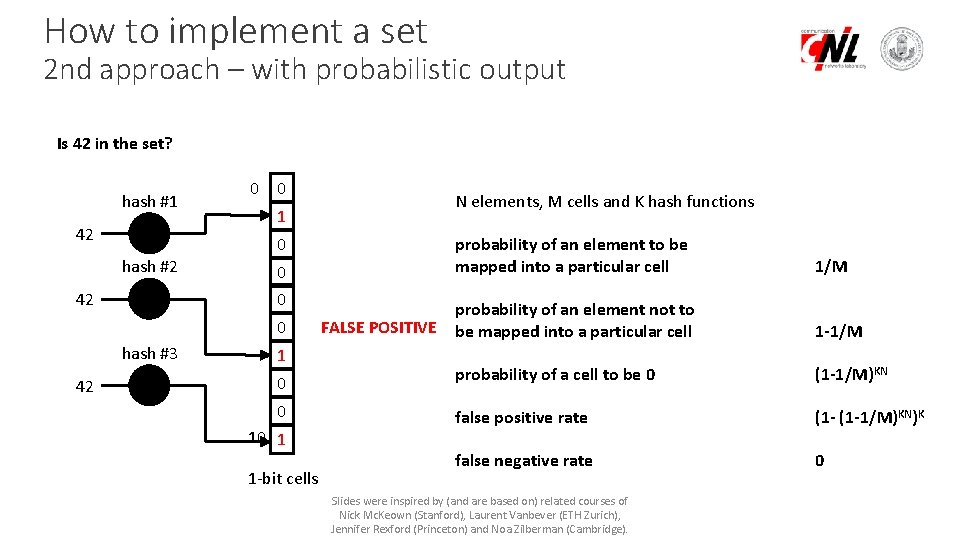
How to implement a set 2 nd approach – with probabilistic output Is 42 in the set? hash #1 42 0 0 1 0 hash #2 42 0 0 0 hash #3 42 N elements, M cells and K hash functions 1 0 0 10 1 1 -bit cells FALSE POSITIVE probability of an element to be mapped into a particular cell 1/M probability of an element not to be mapped into a particular cell 1 -1/M probability of a cell to be 0 (1 -1/M)KN false positive rate (1 -1/M)KN)K false negative rate 0 Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
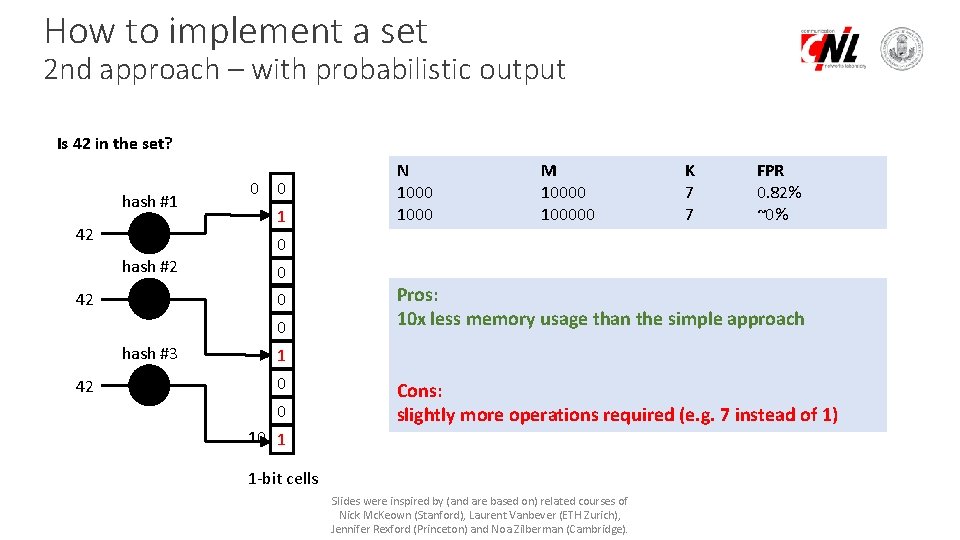
How to implement a set 2 nd approach – with probabilistic output Is 42 in the set? hash #1 42 0 0 1 M 100000 K 7 7 FPR 0. 82% ~0% 0 hash #2 42 0 0 0 hash #3 42 N 1000 Pros: 10 x less memory usage than the simple approach 1 0 0 10 1 Cons: slightly more operations required (e. g. 7 instead of 1) 1 -bit cells Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
Dimension your Bloom Filter • N elements • M cells • K hash functions • FP false positive rate Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
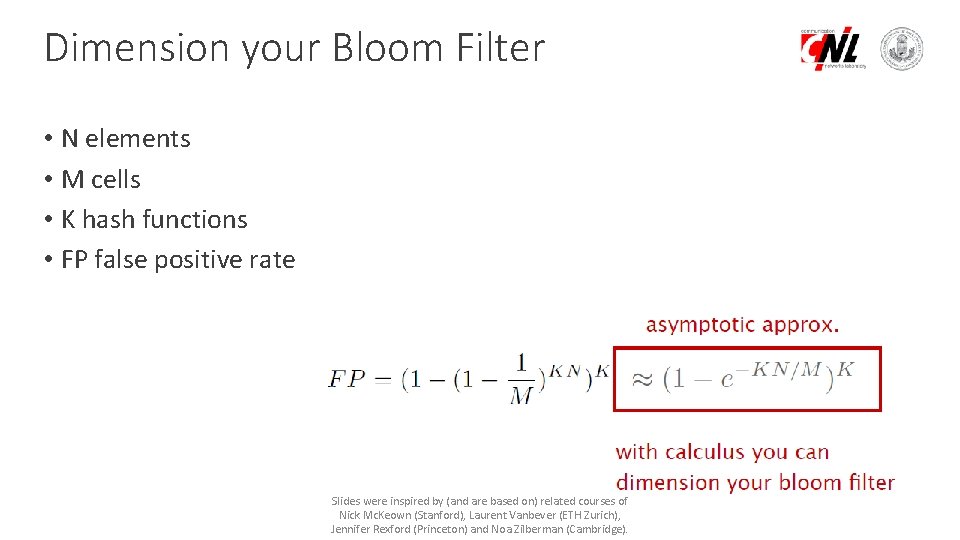
Dimension your Bloom Filter • N elements • M cells • K hash functions • FP false positive rate Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
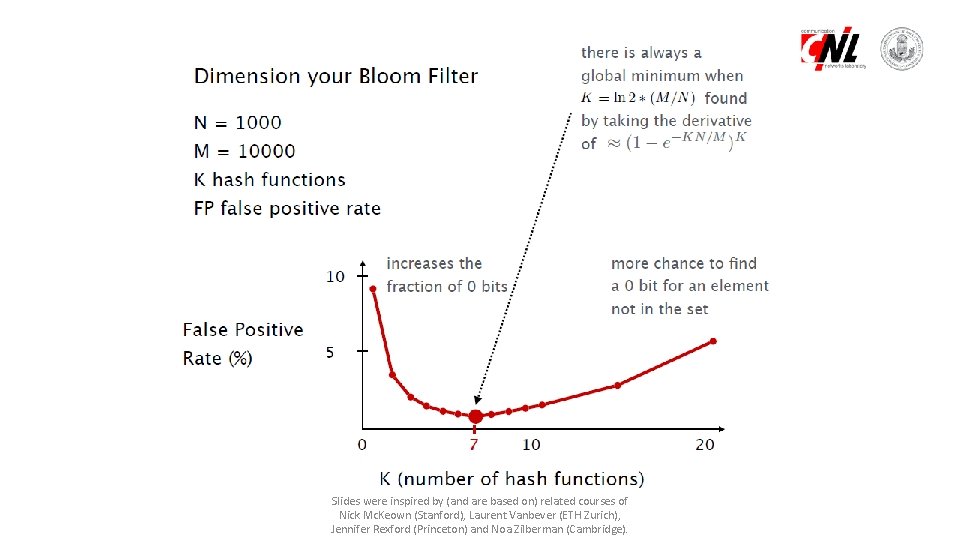
Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
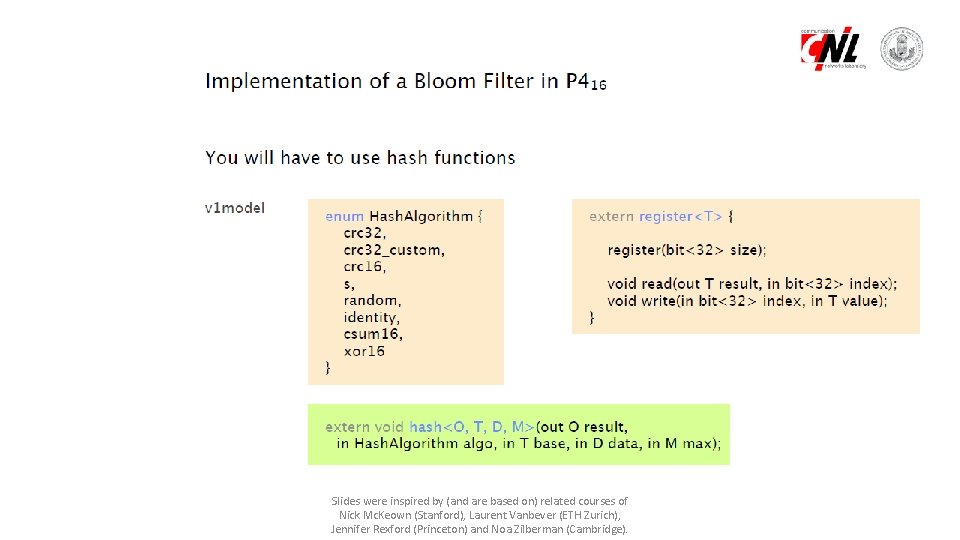
Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
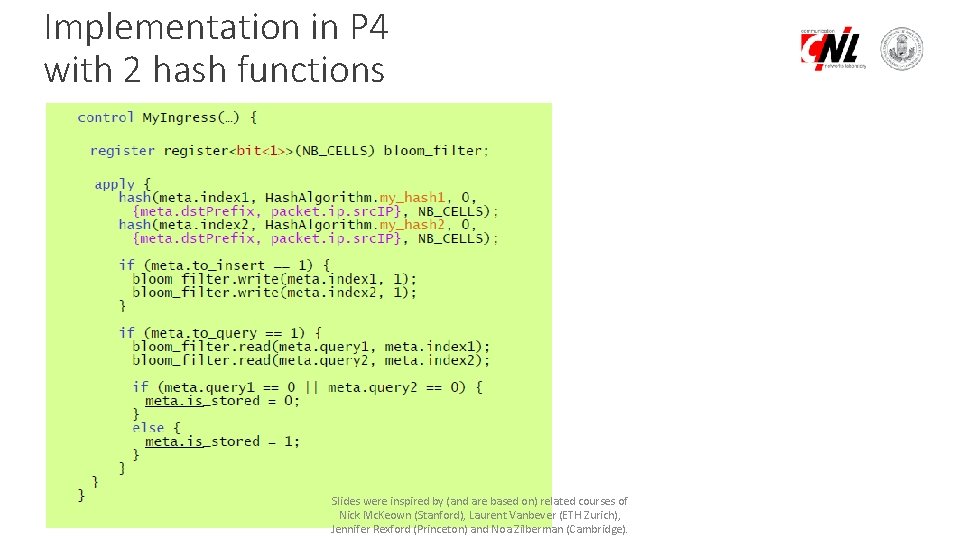
Implementation in P 4 with 2 hash functions Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
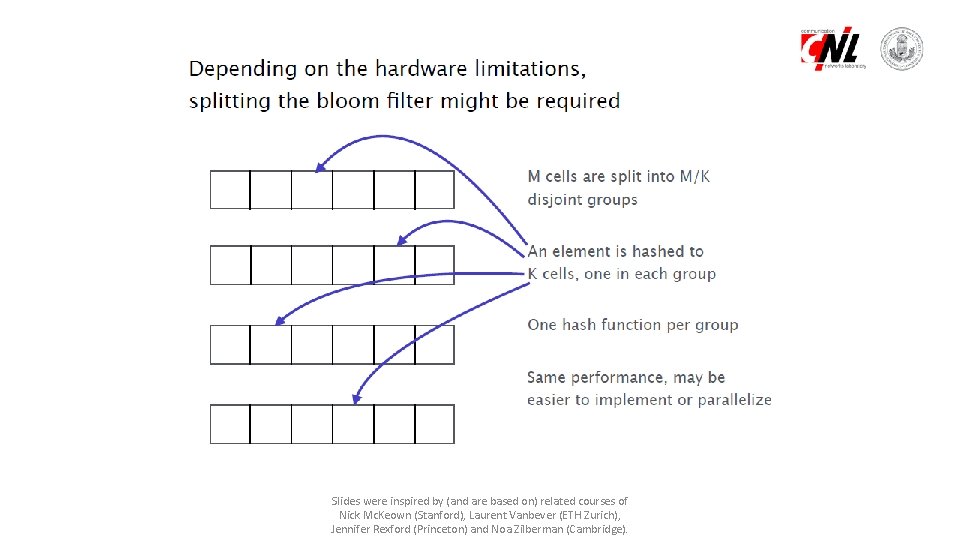
Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
Because deletions are not possible, the controller may need to regularly reset the bloom filters Resetting a bloom filter takes some time during which it is not usable Common trick: use two bloom filters and use one when the controller resets the other one Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
Why deletion is not easy? Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
Solution Counting Bloom Filters Slides were inspired by (and are based on) related courses of Nick Mc. Keown (Stanford), Laurent Vanbever (ETH Zurich), Jennifer Rexford (Princeton) and Noa Zilberman (Cambridge).
- Slides: 59