Outlines Introduction About packet filtering Stateless packet filtering

Outlines: • Introduction • About packet filtering • Stateless packet filtering • Stateful packet filtering
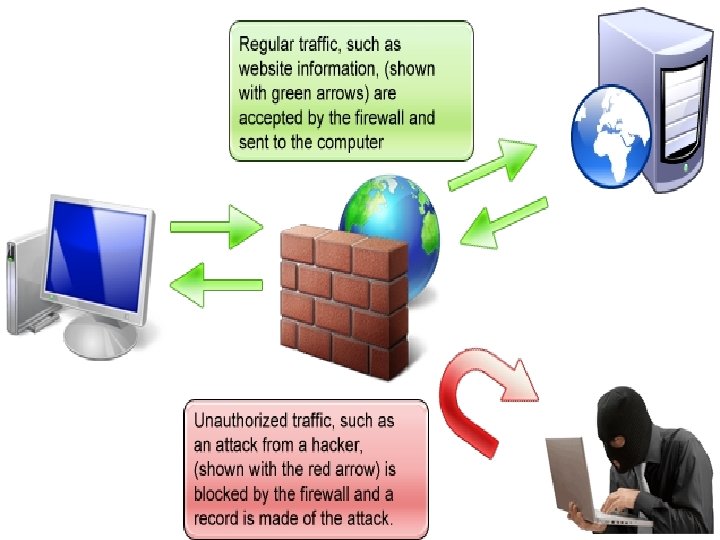
1 -introduction Most organizations need to control the traffic that crosses in and out their networks. The firewall: is a primary control point for these tasks, is a subsystem of computer software or hardware that intercepts data packets before allowing them into or out of a network. Act like a security guard at the entrance of the building , using a sensible security policy and a security rule set written to the DB to makes decisions.
Introduction (cont. ) : In order for the firewall to perform its job several conflicting issues to be addressed : 1 - the firewall must be able to observe all the traffic obviously, a firewall cannot control traffic that bypasses it. 2 -the firewall must be able to differentiate between various types of traffic, and apply the appropriate filtering decisions. 3 -the firewall must work fast enough so that it does not become a bottleneck.
First generation: packet filtering Packet filtering: is operation of inspects each packet passing through the network and accepts or rejects it based on userdefined rules. There are two types of the packet filtering generation: 1 -stateless 2 -stateful
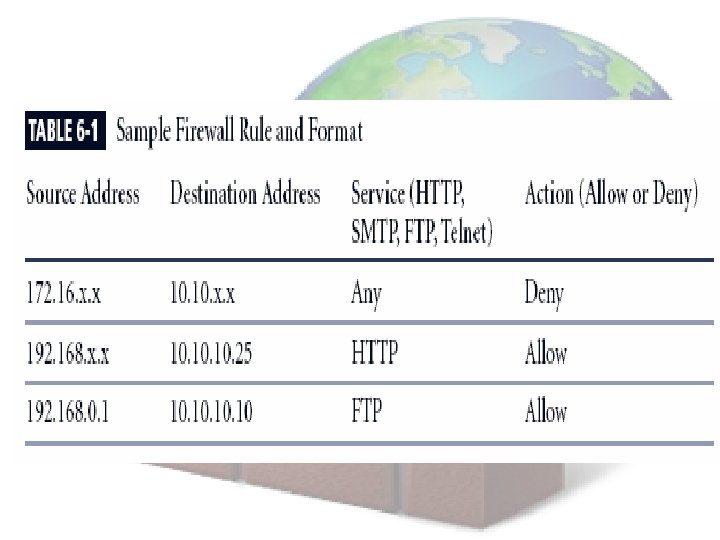
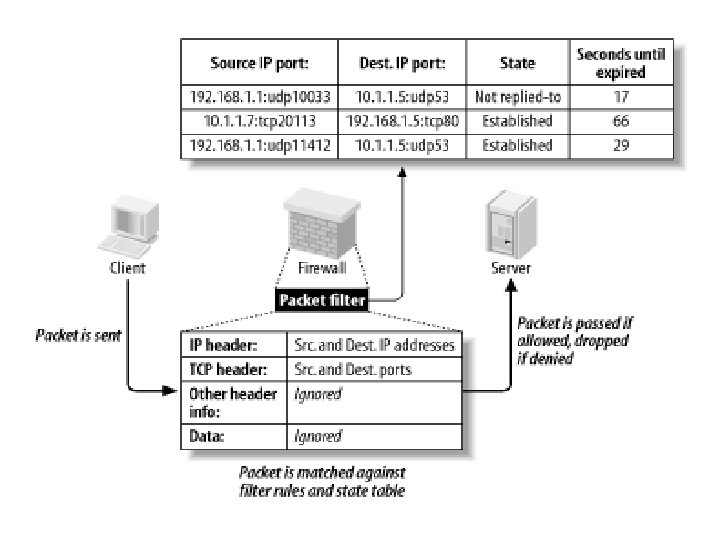
1 -Stateless packet filtering • What it is? Most first generation firewalls used stateless packet filtering. Stateless packet filtering means : 1 - the firewall keeps no state , the filtering decision is made separately for every packet, and does not take into account any earlier decisions made on related packets. 2 -the filtering decision is based on five basic fields : source and destination IP addresses , Protocol , source and destination port numbers.
Stateless packet filtering (cont. ): • Packet filters: are rules that inspect the information in the packet header of every packet arriving at the firewall, so it can make a decision • The typical actions that a basic packet filter can take are: 1 -pass: let the packet through 2 -drop: do not forward the packet. No indication is sent back to the sender. 3 -reject: same as drop, except that a special ICMP packet is sent back to the sender informing it that the packet was filtered.
Filtering IP packet • firewall inspected the IP header and TCP or UDP header of each packet, made a decision based on the IP addresses used and the specific port number. • an IP packet never passes any router or firewall without undergoing some modifications (ex. TTL).
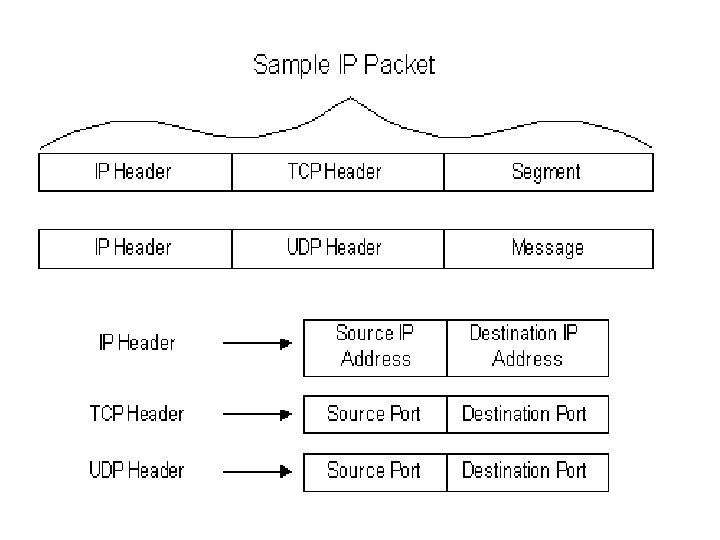
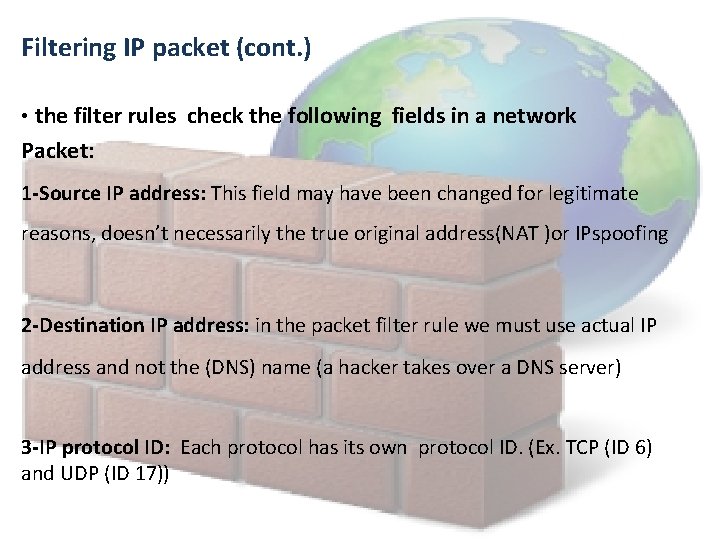
Filtering IP packet (cont. ) • the filter rules check the following fields in a network Packet: 1 -Source IP address: This field may have been changed for legitimate reasons, doesn’t necessarily the true original address(NAT )or IPspoofing 2 -Destination IP address: in the packet filter rule we must use actual IP address and not the (DNS) name (a hacker takes over a DNS server) 3 -IP protocol ID: Each protocol has its own protocol ID. (Ex. TCP (ID 6) and UDP (ID 17))
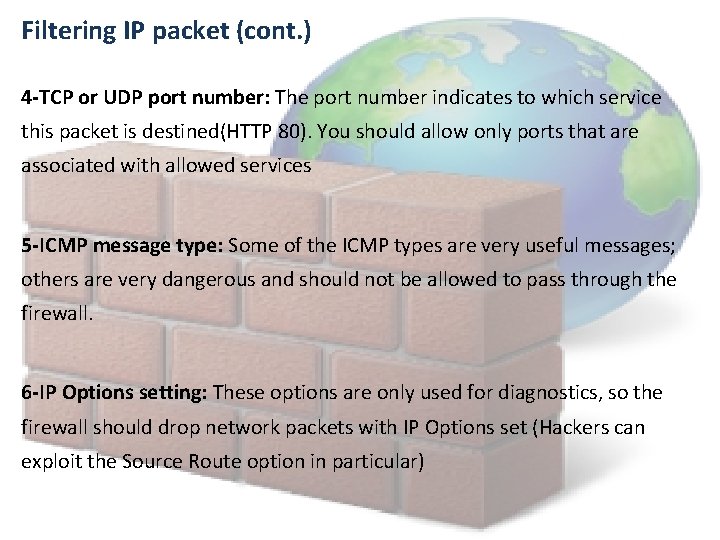
Filtering IP packet (cont. ) 4 -TCP or UDP port number: The port number indicates to which service this packet is destined(HTTP 80). You should allow only ports that are associated with allowed services 5 -ICMP message type: Some of the ICMP types are very useful messages; others are very dangerous and should not be allowed to pass through the firewall. 6 -IP Options setting: These options are only used for diagnostics, so the firewall should drop network packets with IP Options set (Hackers can exploit the Source Route option in particular)
Limitation of stateless: Since the firewall does not keep state , it doesn't remember whether a flow is already establish and what source port number the client selected. Thus , the firewall has to rely on source-port filtering which it is unreliable and risky.
Stateful packet filtering • This type keeps an entry in cache for each open flow. the first packet of anew flow matches by firewall against the rule-base. if it is allow to pass, firewall insert a new entry into the cache • When a subsequent packet reaches the firewall, the firewall checks whether an entry for the flow it belongs to already exists in the cache. If the flow is listed in the cache the packet is allowed through immediately. If no such flow exist, then the packet is matched against the rule base and is handled accordingly
Stateful packet filtering(cont. ) Advantages of stateful filtering: The main Advantage of a stateful is that it is inherently more secure and redues to the administrator overhead of writing source filtering rules. Limitation of stateful filtering: An established flow is allowed through the firewall only an entry in the cache. Therefore , if the cache entry is removed while the flow is still active all remaining traffic will be dropped , this can happen in two situation:
Stateful packet filtering(cont. ) 1 - cache table overflow: the cache table grows dynamically , as more connections are activated concurrently. 2 - time-out too short: when it is too short , then the cache entry may be evicted simply because the flow was quiet for too long.
References: ØPacket filtering and stateful firewalls- avishai wool Ph. D ØFirewalls for dummies 2 nd edition - by Brian Komar, Ronald Beekelaar, and Joern Wettern, Ph. D

• And we hope your network to be secure
- Slides: 20