Marko Bejuk Static analysis tools 932021 1 Since
Marko Bejuk Static analysis tools 9/3/2021 1
Since human beings themselves are not fully debugged yet there will be bugs in your code no matter what you do. 9/3/2021 2
Introduction: • What are static analysis tools? – Examination of the source code – Detection of possible faults and anomalies • What is their main characteristics? • What is their intention? – Drawing verifiers intention to anomalies in the program 9/3/2021 3
Introduction: • Stages involved in static anlysis include – Control flow analysis • Loops with multiple exit • Unreachable code • Unconditional branches – Data use analysis • Use of variables » Variables used before initialization » Variables declared but never used » Undeclared variables • Ineffective tests 9/3/2021 4
Introduction: • Stages involved in static anlysis include – Interface analysis • Consistency of routine • Procedure declarations » Parameter type mismatches » Parameter number mismatches – Information flow analysis – Path analysis 9/3/2021 5
SPLint: • Secure Programming Lint • SPLint is a tool for statically checking C programms for security vulnerabilities and programming mistakes • Splint checking can be customized to select what classes of errors are reported using command line flags and stylized comments in the code 9/3/2021 6
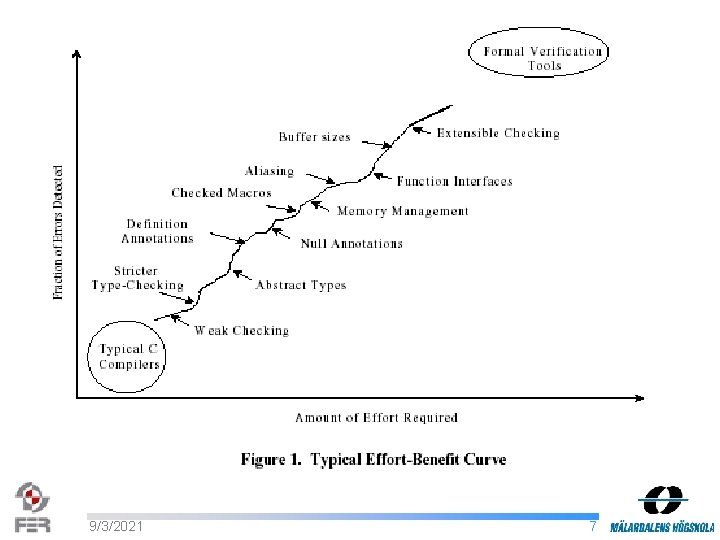
9/3/2021 7
SPLint: • Operation – Splint invoking splint *. c splint -weak *. c – Warnings sample. c: (in function faucet) sample. c: 11: 12: Fresh storage x not released before return A memory leak has been detected. Storage allocated locally is not released before the last reference to it is lost. (Use -mustfreefresh to inhibit warning) 9/3/2021 8
SPLint: – Flags • Several hundred flags • For controlling checking and message reporting • Preceded by + or – – Stylized comments • Provide extra information about a type, variable or function interface to improve checking, or to control flag settings locally /*@null@*/ /*@+charint -modifies =showfunc@*/ 9/3/2021 9
SPLint: • Problems detected by Splint include: – Null dereferences detection • null annotation is used to indicate that a pointer value may be NULL • Splint will report an error when a possibly null pointer is passed as a parameter, returned as a result, or assigned to an external reference with no null qualifier 9/3/2021 10
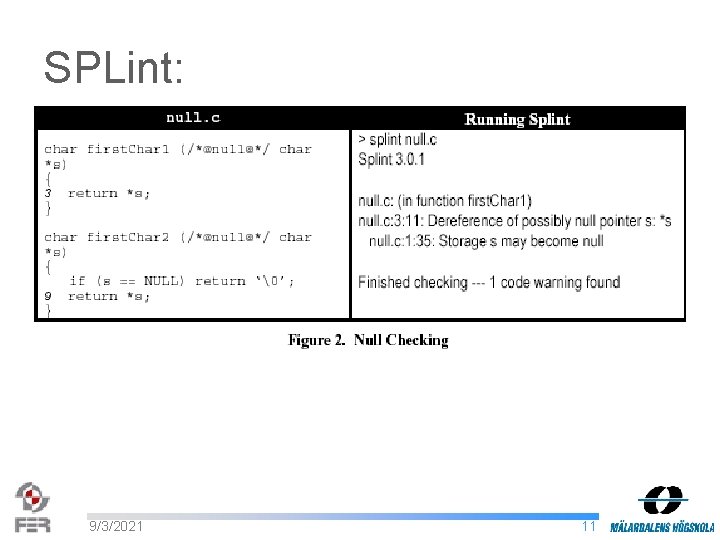
SPLint: 9/3/2021 11
Splint: • Problems detected by Splint include: – Undefined values • Value used before defined • Undefined parameters memory allocator may return allocated but undefined storage /*@out@*/ annotation used to denote a pointer to storage that may be undefined /*@in@*/ annotation can be used to denote a parameter that must be completely defined • Partially defined structured 9/3/2021 12
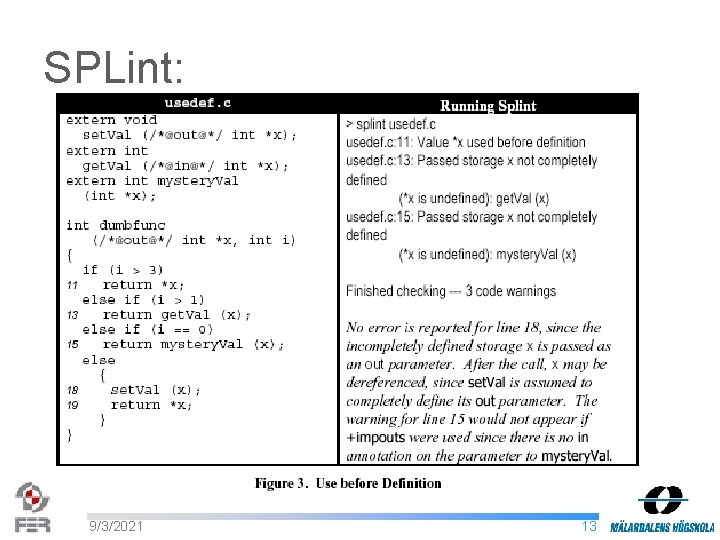
SPLint: 9/3/2021 13
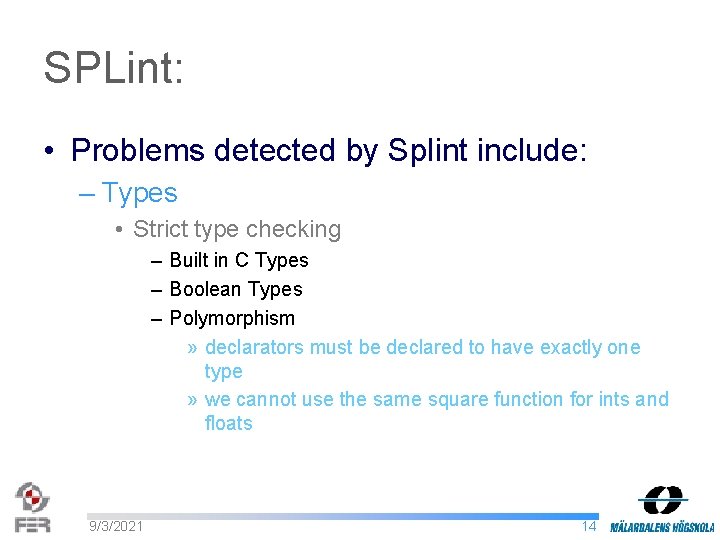
SPLint: • Problems detected by Splint include: – Types • Strict type checking – Built in C Types – Boolean Types – Polymorphism » declarators must be declared to have exactly one type » we cannot use the same square function for ints and floats 9/3/2021 14
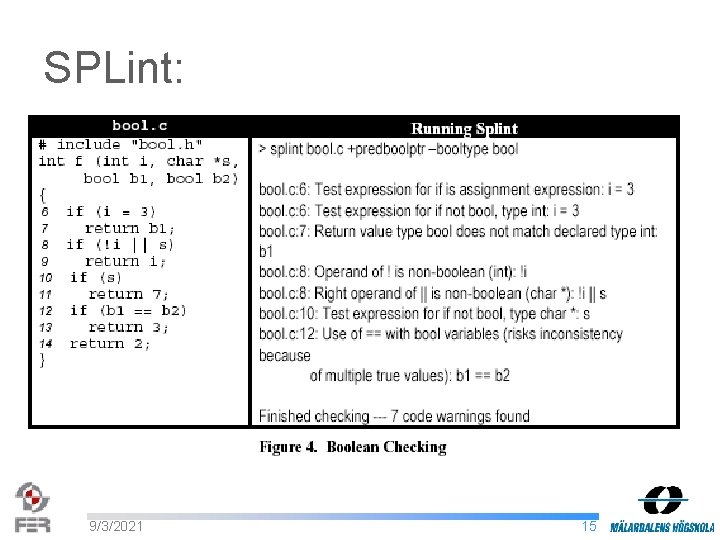
SPLint: 9/3/2021 15
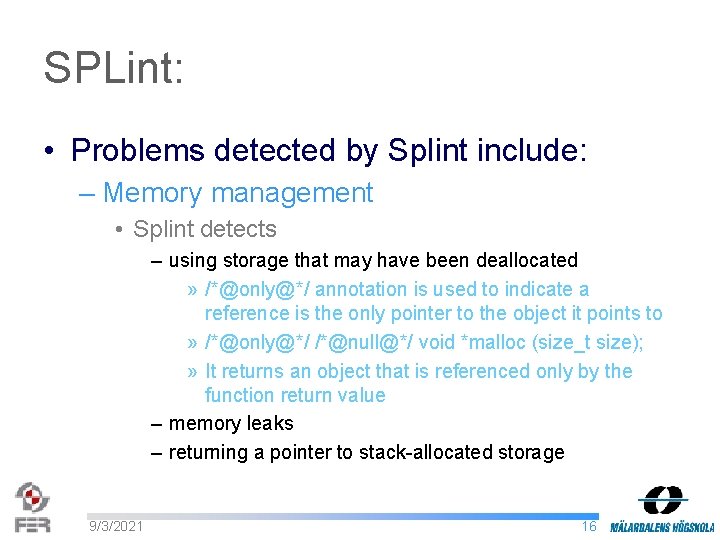
SPLint: • Problems detected by Splint include: – Memory management • Splint detects – using storage that may have been deallocated » /*@only@*/ annotation is used to indicate a reference is the only pointer to the object it points to » /*@only@*/ /*@null@*/ void *malloc (size_t size); » It returns an object that is referenced only by the function return value – memory leaks – returning a pointer to stack-allocated storage 9/3/2021 16
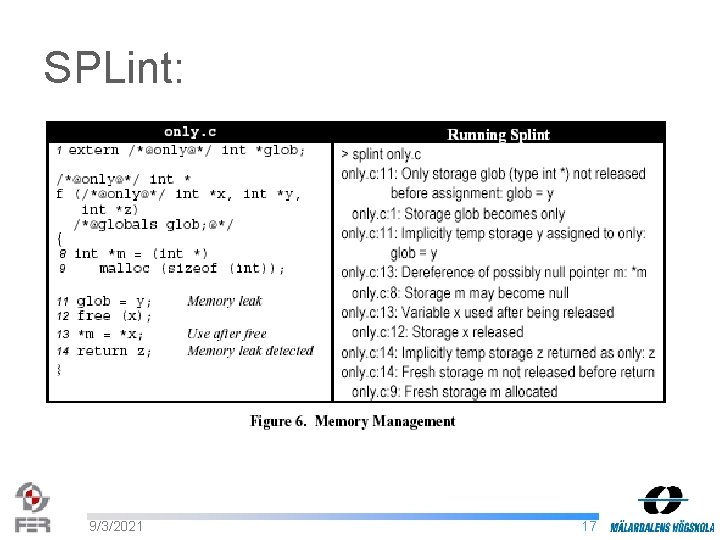
SPLint: 9/3/2021 17
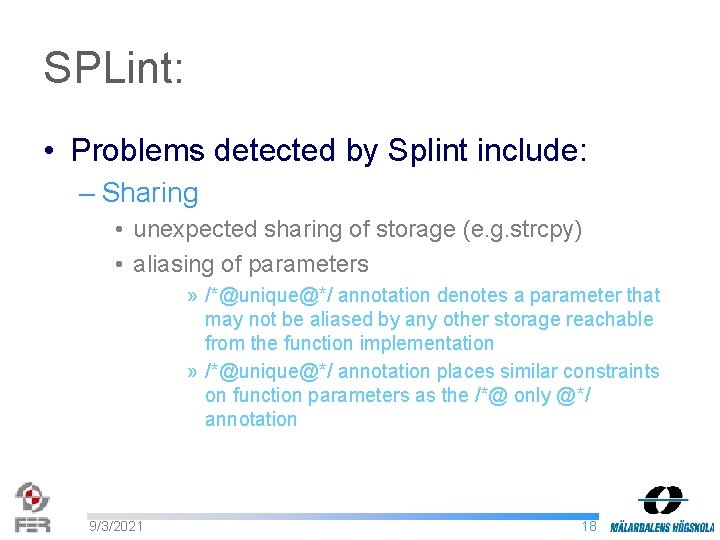
SPLint: • Problems detected by Splint include: – Sharing • unexpected sharing of storage (e. g. strcpy) • aliasing of parameters » /*@unique@*/ annotation denotes a parameter that may not be aliased by any other storage reachable from the function implementation » /*@unique@*/ annotation places similar constraints on function parameters as the /*@ only @*/ annotation 9/3/2021 18
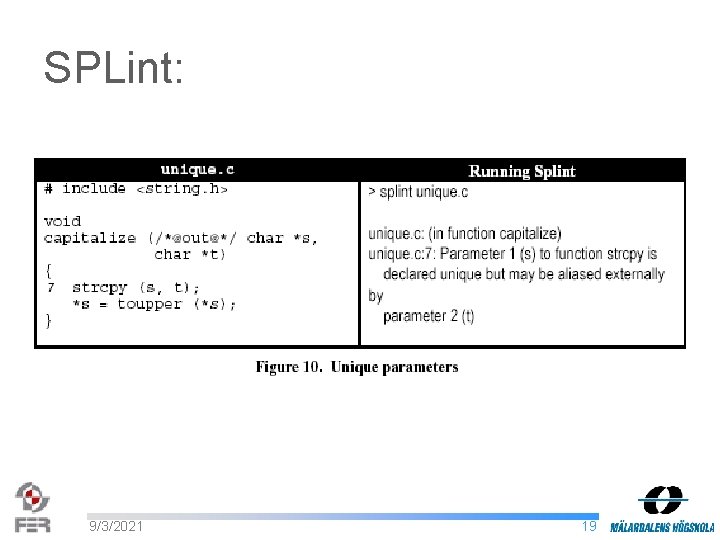
SPLint: 9/3/2021 19
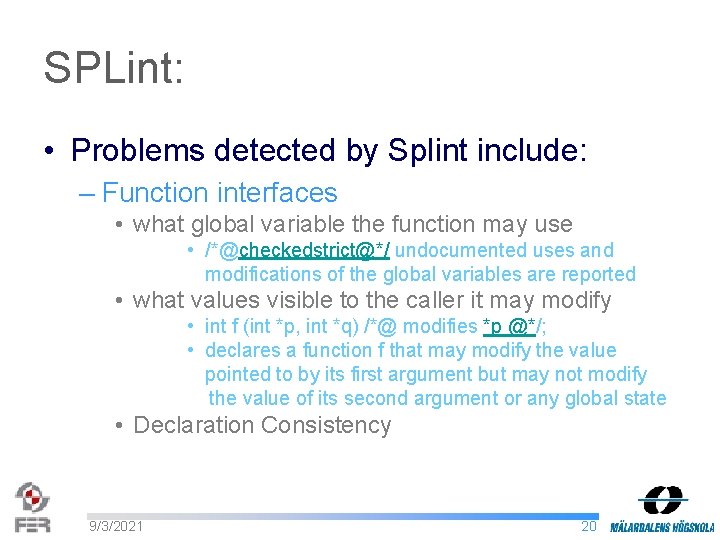
SPLint: • Problems detected by Splint include: – Function interfaces • what global variable the function may use • /*@checkedstrict@*/ undocumented uses and modifications of the global variables are reported • what values visible to the caller it may modify • int f (int *p, int *q) /*@ modifies *p @*/; • declares a function f that may modify the value pointed to by its first argument but may not modify the value of its second argument or any global state • Declaration Consistency 9/3/2021 20
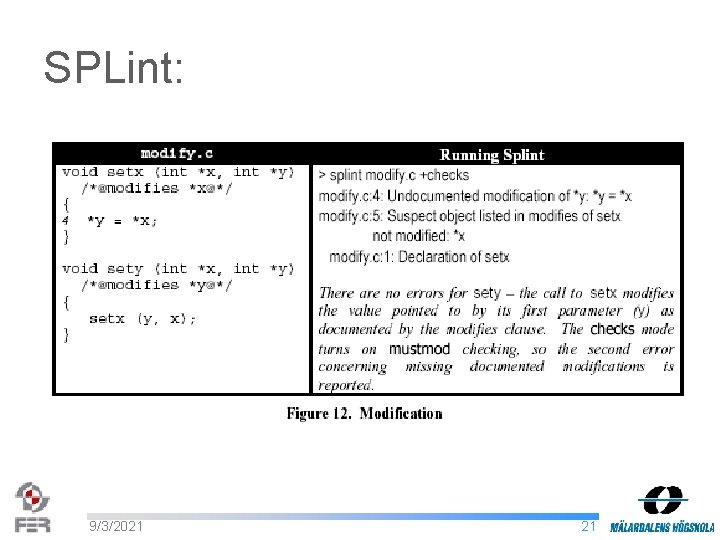
SPLint: 9/3/2021 21
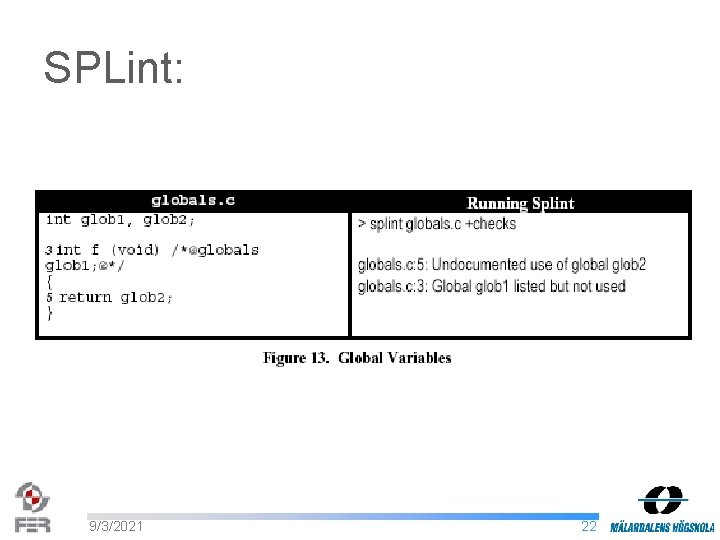
SPLint: 9/3/2021 22
SPLint: • Problems detected by Splint include: – Control flow • Execution » noreturn annotation is used to denote a function that never returns » extern /*@noreturn@*/ void fatalerror /*@observer@*/ char *s); if (x == NULL) fatalerror ("Yikes!"); *x = 3; • Undefined Behavior • Problematic Control Structures » Likely Infinite Loops » Switches 9/3/2021 23
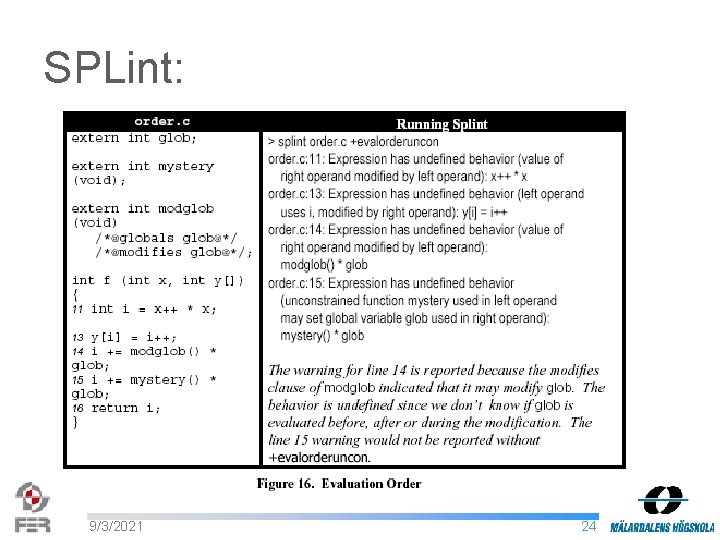
SPLint: 9/3/2021 24
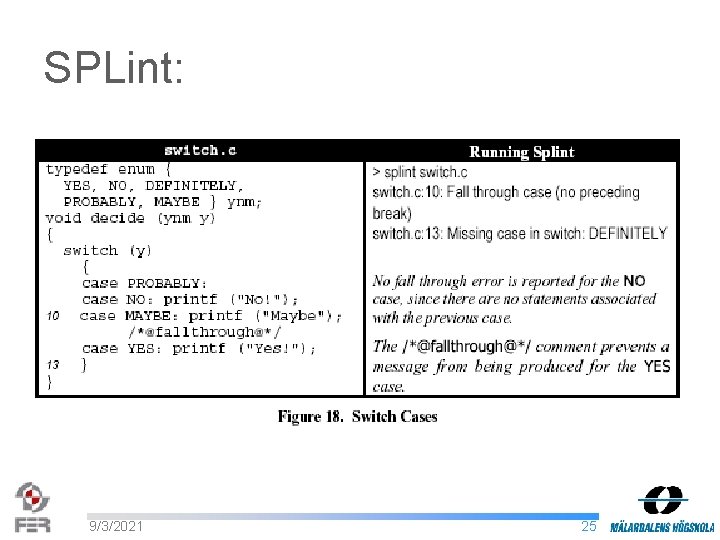
SPLint: 9/3/2021 25

SPLint: • Problems detected by Splint include: – Buffer sizes » Security issue • Checking Accesses » Splint models blocks of contiguous memory using two properties: max. Set and max. Read » max. Set(b) denotes the highest address beyond b that can be safely used as an lvalue » max. Read denotes the highest index of a buffer that can be safely used an rvalue • Annotating Buffer Sizes » requires and ensures clauses that specify assumptions about buffer sizes 9/3/2021 26
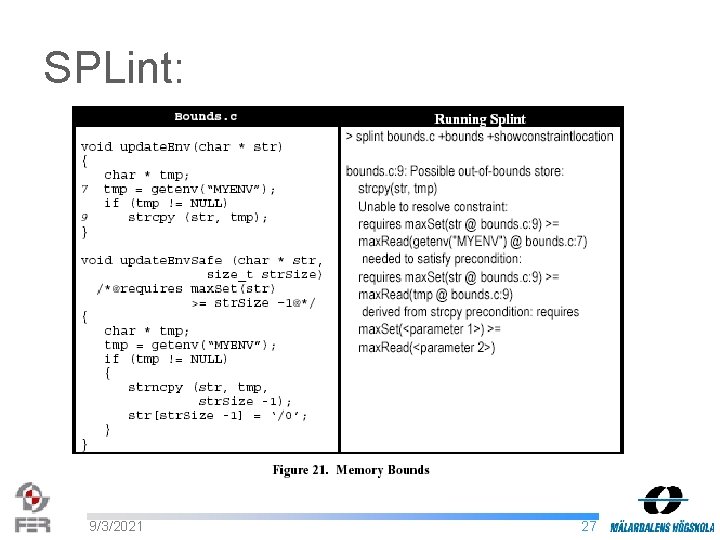
SPLint: 9/3/2021 27
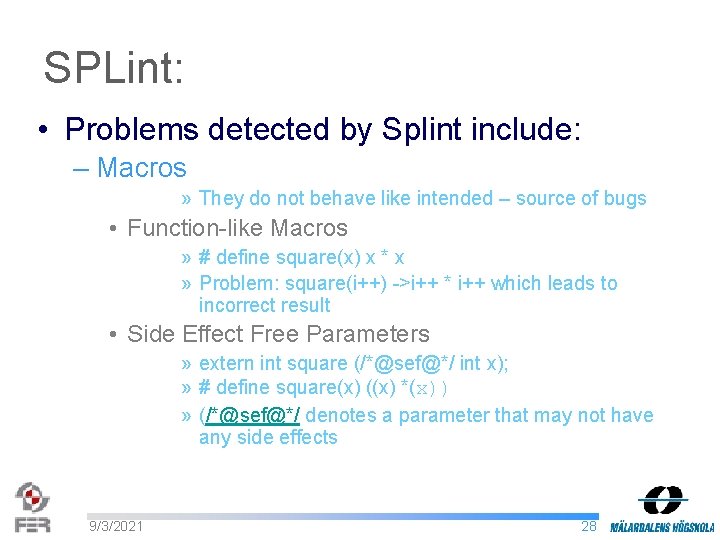
SPLint: • Problems detected by Splint include: – Macros » They do not behave like intended – source of bugs • Function-like Macros » # define square(x) x * x » Problem: square(i++) ->i++ * i++ which leads to incorrect result • Side Effect Free Parameters » extern int square (/*@sef@*/ int x); » # define square(x) ((x) *(x)) » (/*@sef@*/ denotes a parameter that may not have any side effects 9/3/2021 28
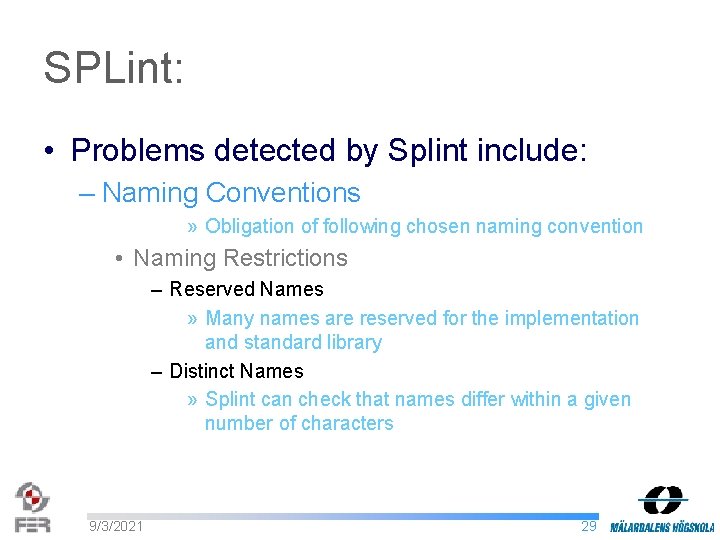
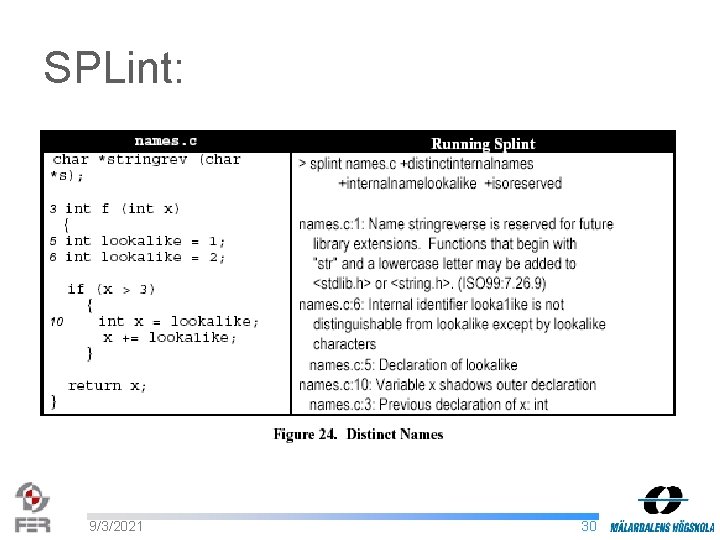
SPLint: • Problems detected by Splint include: – Naming Conventions » Obligation of following chosen naming convention • Naming Restrictions – Reserved Names » Many names are reserved for the implementation and standard library – Distinct Names » Splint can check that names differ within a given number of characters 9/3/2021 29
SPLint: 9/3/2021 30
SPLint: • Problems detected by Splint include: – Completeness » warnings for unused declarations and exported declarations that are not used externally • Unused Declarations » Splint detects constants, functions, parameters, variables, types, enumerator members, and structure or union fields that are declared but never used » /*@unused@*/ annotation can be used before a declaration to indicate that the item declared need not be used 9/3/2021 31
SPLint: • Problems detected by Splint include: – Libraries and header file inclusion » Checking modules in a large program 9/3/2021 32
Conclusion: • Tool-based analysis cannot replace inspections – They cannot detect incorrect initializations – Incorrect arguments passed to a function 9/3/2021 33
- Slides: 33