Introduction to RBAC Wojciech Sliwinski BECO for the
Introduction to RBAC Wojciech Sliwinski BE/CO for the CMW/RBAC team BE-ICS BASICS 23/06/2017
Motivation for RBAC Machine Safety ▪ Enormous energy stored in the LHC magnets and beams ▪ Potential machine damage is a serious concern ▪ Prevent from invoking machine protection systems Machine Performance ▪ Do not mess with a fine tuned system ▪ Access denied during certain machine states Commissioning feedback ▪ Hardware and software commissioning ▪ Debugging Proposal: Role-Based Access Control BE-ICS BASICS: Introduction to RBAC 2
RBAC inception Common effort of: CO, OP, EPC, IT Security & Fermilab ▪ Design document prepared in 2007 ▪ EDMS: https: //edms. cern. ch/document/805654/0. 3 Stick to industry standards where possible Reuse the existing IT services Initially implemented by CO & Fermilab Before the LHC startup CO took over the project RBAC became part of the CMW infrastructure BE-ICS BASICS: Introduction to RBAC 3
Scope of RBAC � RBAC infrastructure provided by CO Does not prevent hackers from doing damage Protects against human mistakes ▪ A well meaning person from doing wrong thing at the wrong time ▪ An ignorant person from doing anything at anytime Original scope: LHC machine Can be deployed anywhere in the Controls Infrastructure Aims to enhance the overall Machine Safety Provides Authentication (A 1) and Authorization (A 2) services Complements ▪ Hardware Protection (BIS, PIS) ▪ CNIC effort (access control into Technical Network) ▪ MCS (Management of Critical Settings) BE-ICS BASICS: Introduction to RBAC 4
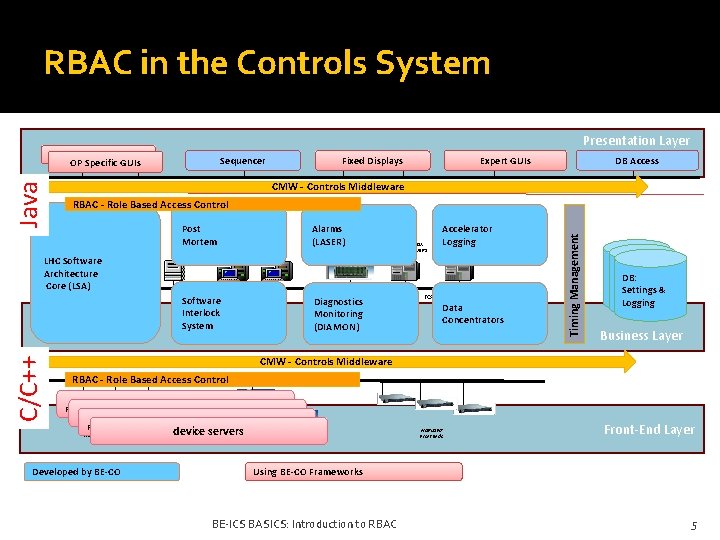
RBAC in the Controls System Presentation Layer OP Specific GUIs Sequencer TCP/IP communication services CMW - Controls Middleware RBAC - Role Based Access Control FILE SERVERS Post Mortem APPLICATION SERVERS CERN GIGABIT ETHERNET TECHNICAL NETWORK LHC Software Architecture Core (LSA) C/C++ DB Access Expert GUIs Fixed Displays Software Interlock System Alarms (LASER) TIMING GENERATION Diagnostics Monitoring (DIAMON) SCADA SERVERS Accelerator Logging TCP/IP communication services Data Concentrators Timing Management Java OP Specific GUIs DB DB DB: & Settings & Logging Business Layer CMW - Controls Middleware TCP/IP communication services RBAC - Role Based Access Control Front-End FESA servers RTFront-End Lynx/OS VME Front Ends Developed by BE-CO device servers PLC WORLDFIP Front Ends Front-End Layer Using BE-CO Frameworks BE-ICS BASICS: Introduction to RBAC 5
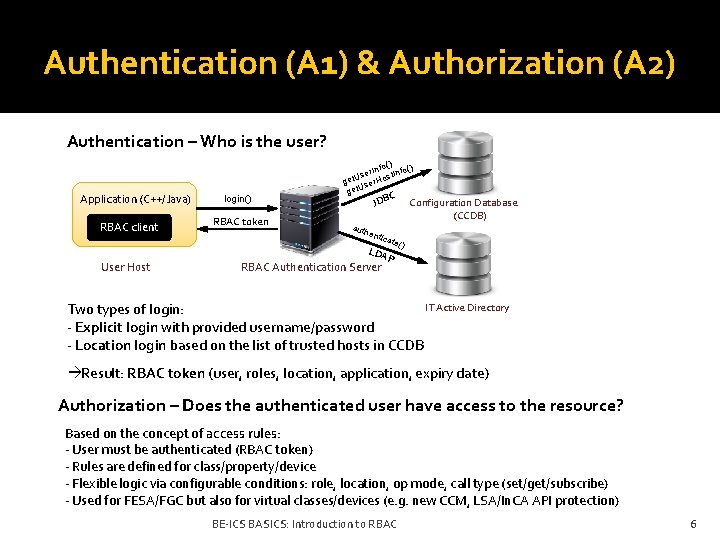
Authentication (A 1) & Authorization (A 2) Authentication – Who is the user? Application (C++/Java) RBAC client User Host login() RBAC token o() r. Inf t. Info() e s s U get ser. Ho U t ge C JDB auth enti c Configuration Database (CCDB) ate( ) LDA RBAC Authentication Server P IT Active Directory Two types of login: - Explicit login with provided username/password - Location login based on the list of trusted hosts in CCDB Result: RBAC token (user, roles, location, application, expiry date) Authorization – Does the authenticated user have access to the resource? Based on the concept of access rules: - User must be authenticated (RBAC token) - Rules are defined for class/property/device - Flexible logic via configurable conditions: role, location, op mode, call type (set/get/subscribe) - Used for FESA/FGC but also for virtual classes/devices (e. g. new CCM, LSA/In. CA API protection) BE-ICS BASICS: Introduction to RBAC 6
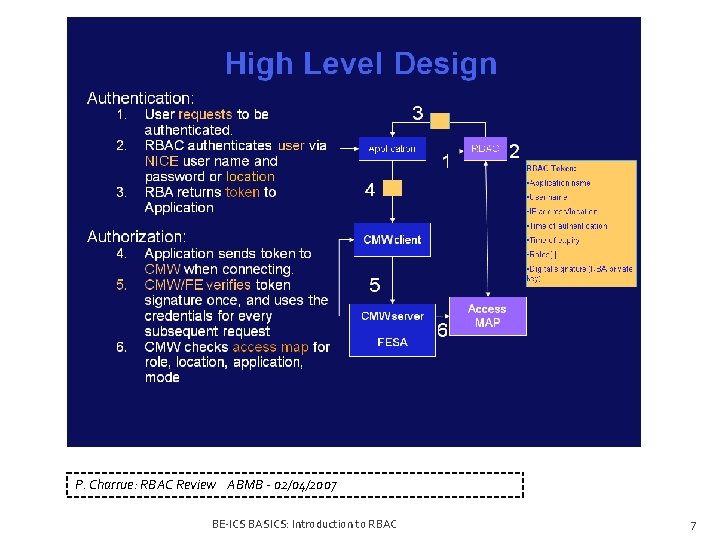
P. Charrue: RBAC Review ABMB - 02/04/2007 BE-ICS BASICS: Introduction to RBAC 7
RBAC architecture BE-ICS BASICS: Introduction to RBAC 8
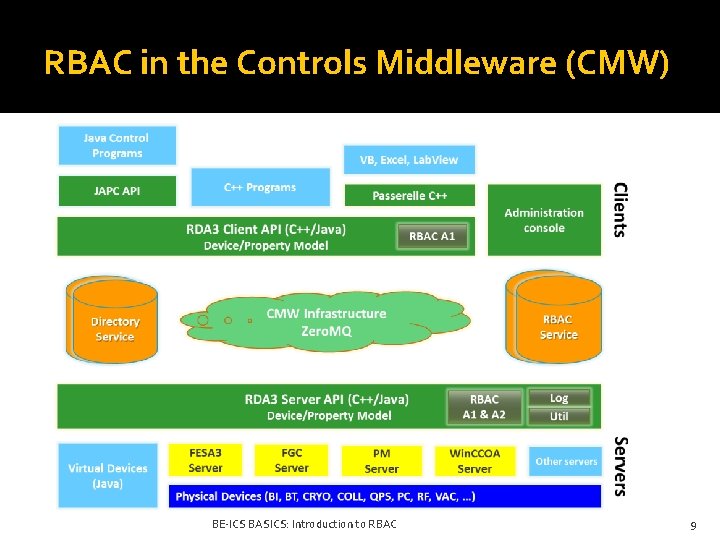
RBAC in the Controls Middleware (CMW) BE-ICS BASICS: Introduction to RBAC 9
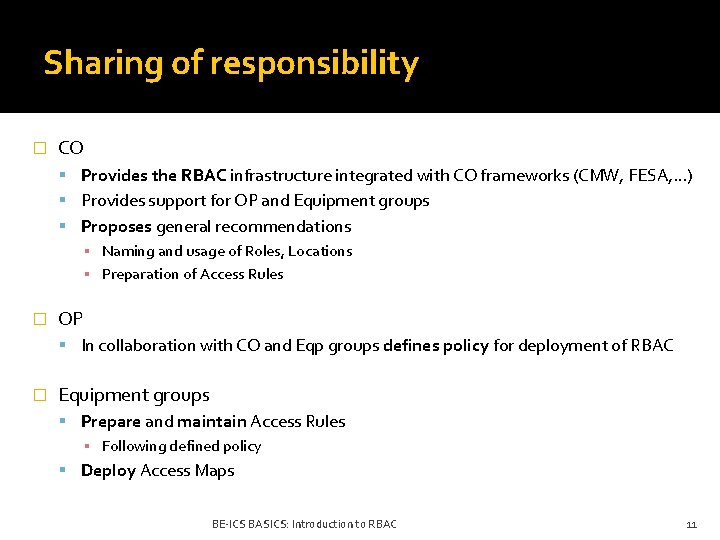
Sharing of responsibility � CO Provides the RBAC infrastructure integrated with CO frameworks (CMW, FESA, . . . ) Provides support for OP and Equipment groups Proposes general recommendations ▪ Naming and usage of Roles, Locations ▪ Preparation of Access Rules � OP In collaboration with CO and Eqp groups defines policy for deployment of RBAC � Equipment groups Prepare and maintain Access Rules ▪ Following defined policy Deploy Access Maps BE-ICS BASICS: Introduction to RBAC 11
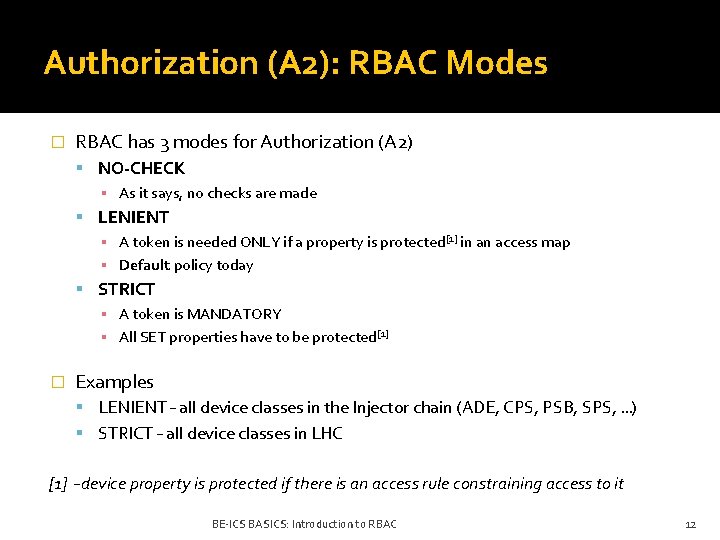
Authorization (A 2): RBAC Modes � RBAC has 3 modes for Authorization (A 2) NO-CHECK ▪ As it says, no checks are made LENIENT ▪ A token is needed ONLY if a property is protected[1] in an access map ▪ Default policy today STRICT ▪ A token is MANDATORY ▪ All SET properties have to be protected[1] � Examples LENIENT – all device classes in the Injector chain (ADE, CPS, PSB, SPS, …) STRICT – all device classes in LHC [1] – device property is protected if there is an access rule constraining access to it BE-ICS BASICS: Introduction to RBAC 12
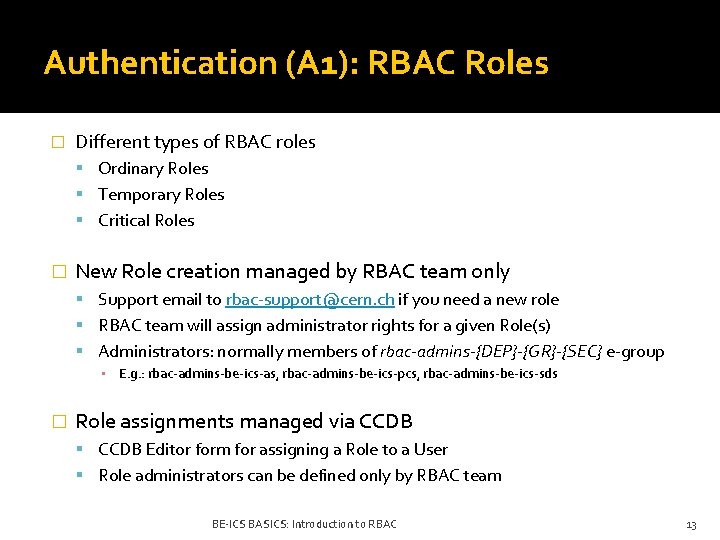
Authentication (A 1): RBAC Roles � Different types of RBAC roles Ordinary Roles Temporary Roles Critical Roles � New Role creation managed by RBAC team only Support email to rbac-support@cern. ch if you need a new role RBAC team will assign administrator rights for a given Role(s) Administrators: normally members of rbac-admins-{DEP}-{GR}-{SEC} e-group ▪ E. g. : rbac-admins-be-ics-as, rbac-admins-be-ics-pcs, rbac-admins-be-ics-sds � Role assignments managed via CCDB Editor form for assigning a Role to a User Role administrators can be defined only by RBAC team BE-ICS BASICS: Introduction to RBAC 13
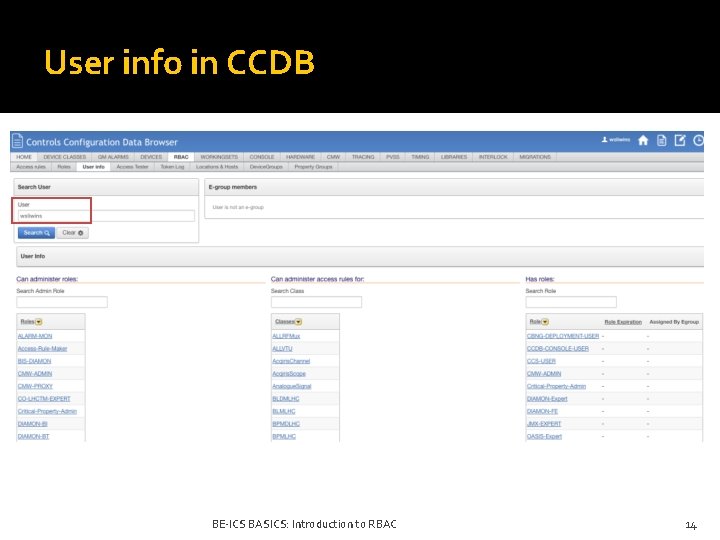
User info in CCDB BE-ICS BASICS: Introduction to RBAC 14
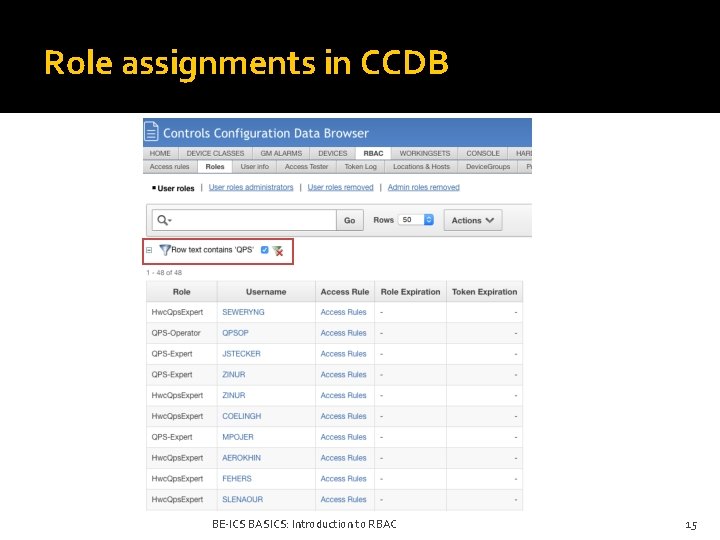
Role assignments in CCDB BE-ICS BASICS: Introduction to RBAC 15
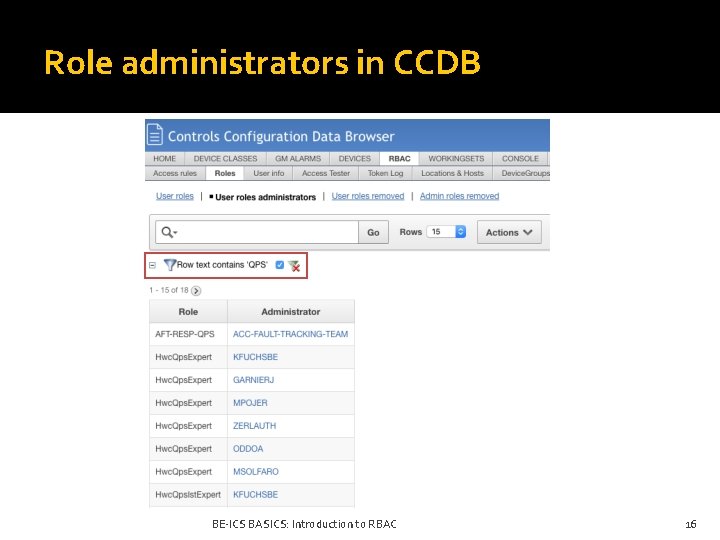
Role administrators in CCDB BE-ICS BASICS: Introduction to RBAC 16
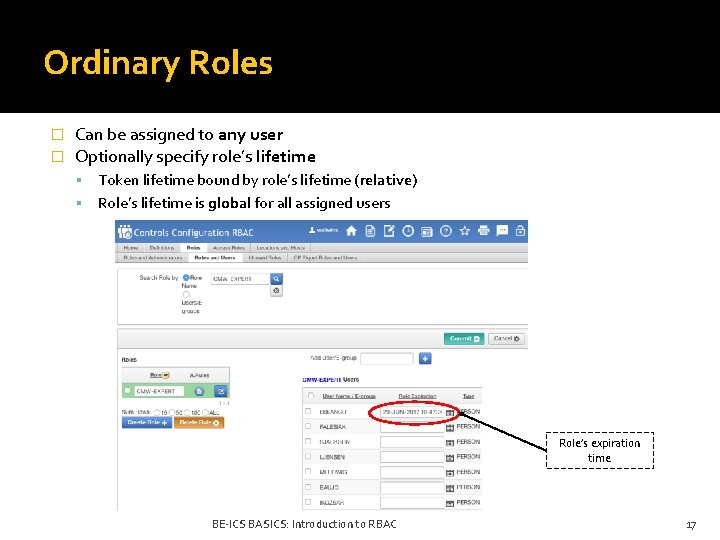
Ordinary Roles � � Can be assigned to any user Optionally specify role’s lifetime Token lifetime bound by role’s lifetime (relative) Role’s lifetime is global for all assigned users Role’s expiration time BE-ICS BASICS: Introduction to RBAC 17
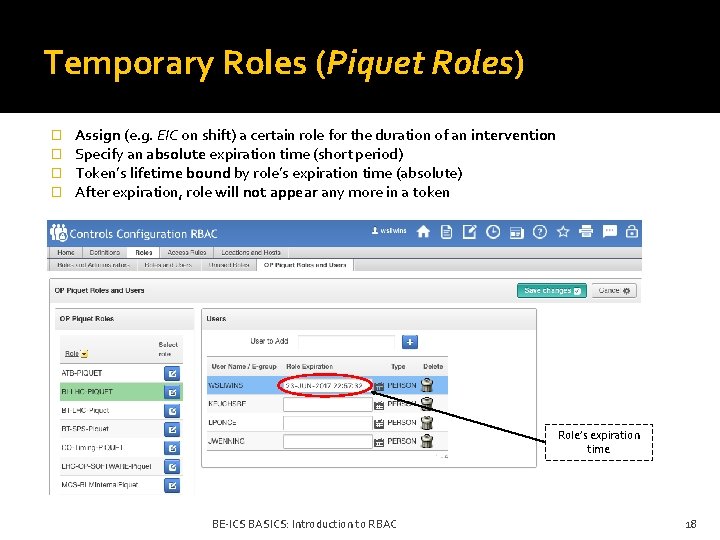
Temporary Roles (Piquet Roles) � � Assign (e. g. EIC on shift) a certain role for the duration of an intervention Specify an absolute expiration time (short period) Token’s lifetime bound by role’s expiration time (absolute) After expiration, role will not appear any more in a token Role’s expiration time BE-ICS BASICS: Introduction to RBAC 18
Temporary Roles � Name convention for Piquet Roles {GRP}-LHC-Piquet (e. g. BI-LHC-Piquet, RF-LHC-Piquet) NO users in these ROLES except when needed � Requested by OP & Eqp groups Hardware interventions during operations Roles for temporary staff, contractors, etc. BE-ICS BASICS: Introduction to RBAC 19
Critical Roles � Critical Roles / MCS (Management of Critical Settings) Roles Short lifetime roles with elevated level of access rights Give access to critical equipment (e. g. BLMs, Kickers, Coll. ) Should be only used by eqp. Experts and selected Operators MCS Roles already widely used for control of critical equipment Moreover RBAC provides: ▪ Critical Roles management ▪ Public & Private keys management for Critical Roles ▪ Service for signing the equipment settings Used mainly in LHC & SPS BE-ICS BASICS: Introduction to RBAC 20
Roles access privileges - recommendations � Operator Role Can always access equipment but only from CCC E. g. : LHC-Operator, SPS-Operator � Expert Role NON-OPERATIONAL mode: access from any Location OPERATIONAL mode: access only from CCC E. g. : BI-BPM-EXPERT, RF-Expert, SMP-EXPERT � Piquet Role Can always access equipment, from any Location Role is normally empty (not assigned) EIC assigns it only for a duration of an intervention BE-ICS BASICS: Introduction to RBAC 21
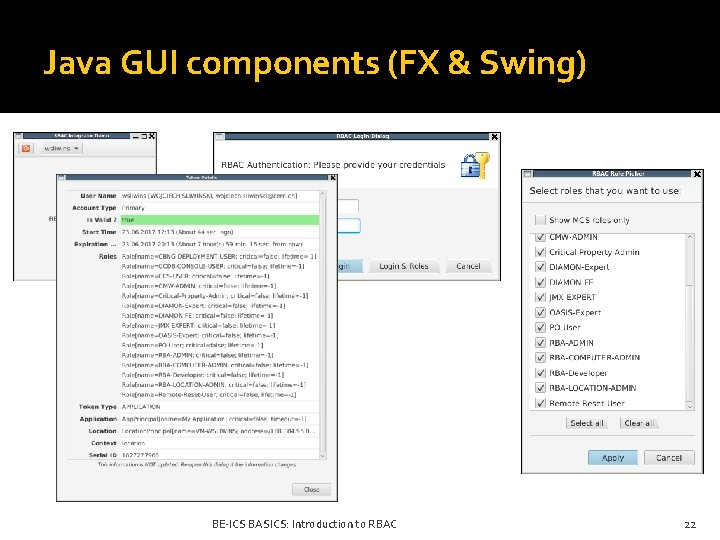
Java GUI components (FX & Swing) BE-ICS BASICS: Introduction to RBAC 22
RBAC Access Control Workflow � A 1: user/service must be authenticated Use Java GUI components or Java/C++ RBAC Login Service API Obtain a valid RBAC token � A 2: access rules have to be defined for a given device class Request RBAC Admin rights for your class(es) (email to: rbac-support@cern. ch) Request access to CCDB RBAC Editor from CCS team Use CCDB RBAC Editor to edit access rules (follow conventions) Remember about: CCC access, Expert access, Piquet access & Operational Mode � A 2: use RBAC CLI tools to generate access map files for CMW server(s) RBAC CLI: rbac-maps-class, rbac-maps-fec, rbac-maps-server � Tools deploy new access maps in the NFS location for a given CMW server (FESA, FGCD, Win. CCOA) A 2: use RBAC CLI tools to reload access map in CMW server(s) Reload using RBAC CLI tools (’-r’ option) or CMW Admin GUI Eventually restart CMW server(s) BE-ICS BASICS: Introduction to RBAC 23
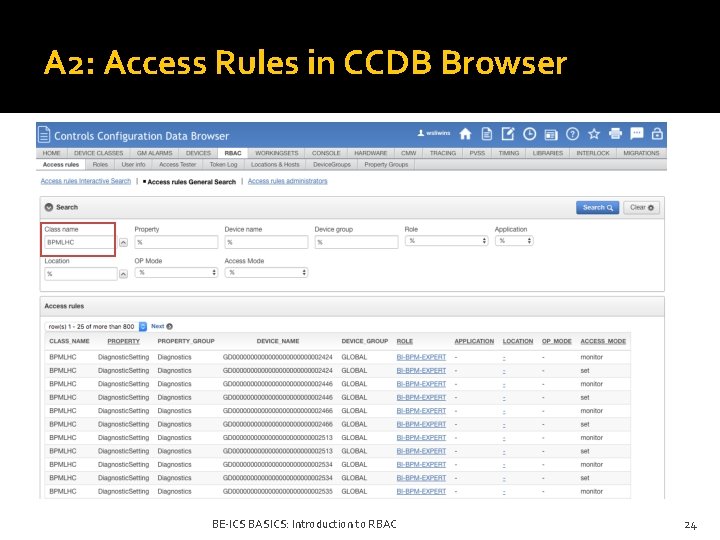
A 2: Access Rules in CCDB Browser BE-ICS BASICS: Introduction to RBAC 24
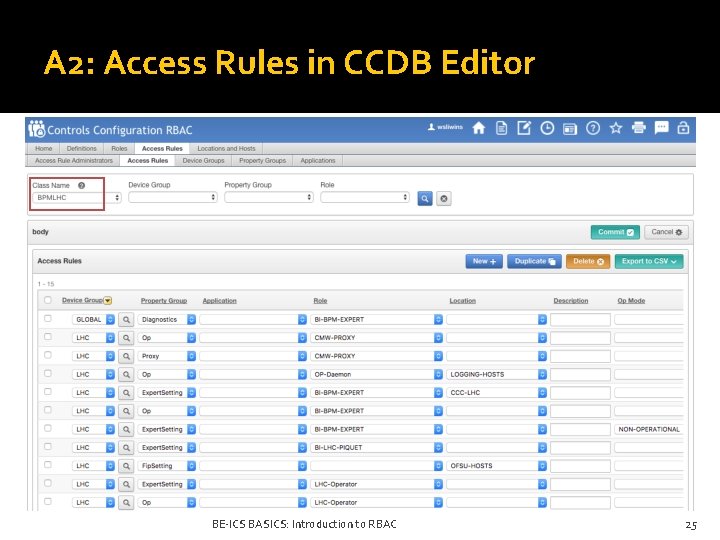
A 2: Access Rules in CCDB Editor BE-ICS BASICS: Introduction to RBAC 25
Status & Future plans � RBAC is deployed in the Accelerator Complex together with the CMW framework � It is a critical service with a redundant, highly-available server architecture � It is used to secure access in: FESA, FGCD, Win. CCOA, Remote. Reset, … � It is used to secure access to middle-tier services, e. g. : LSA/In. CA, SIS, PMA � It integrates with CERN SSO for web applications (see ACW from BE-CO-DS) � Future plans: Integration with Kerberos (system) authentication Improved RBAC Login Service API by LS 2 BE-ICS BASICS: Introduction to RBAC 26
- Slides: 25