Information Systems Security Project Java Crypto Distributed Application
Information Systems Security Project: Java Crypto Distributed Application George Hatzivasilis ECE Dept. Hellenic Mediterranean University (HMU) 1
Outline n Crypto technologies – Bouncy Castle crypto library (Java) q Installation – Java Crypto Programming q Symmetric Cryptography – AES example MAC – SHA 2 -512 example Asymmetric Cryptography – RSA example Digital Signatures – SHA 2 -512 with RSA example Certificates – X 509 Certificate example q Sockets – Client/Server example q q 2
Installation – Java Crypto Programming n (Not Required for new Java versions) Java Runtime Environment (JRE), containing Java Cryptography Extension (JCE) q q q n JCE Unlimited Strength Jurisdiction Policy q n JCE provides a framework and implementations for encryption, key generation and key agreement, and Message Authentication Code (MAC) algorithms Support for encryption includes symmetric, asymmetric, block, and stream ciphers The software also supports secure streams and sealed objects Lifts all algorithm limitations imposed by U. S. export restriction policies Bouncycastle Crypto API Provider (Optional) q Complements and substitutes the JCE 3
Installation – Download n Visit Sun Java Downloads q q n http: //www. oracle. com/technetwork/javase/downloads/index. html If you can’t already compile & run Java applications n Download Java Developers Kit (JDK) Download Unlimited Strength Jurisdiction Policy Files Download the Documentation Files (API) for offline viewing. (Optional) Visit Bouncycastle Java q q q http: //www. bouncycastle. org/java. html Download the Provider jar n http: //www. bouncycastle. org/latest_releases. html Follow the installation instructions n http: //www. bouncycastle. org/specifications. html#install 4




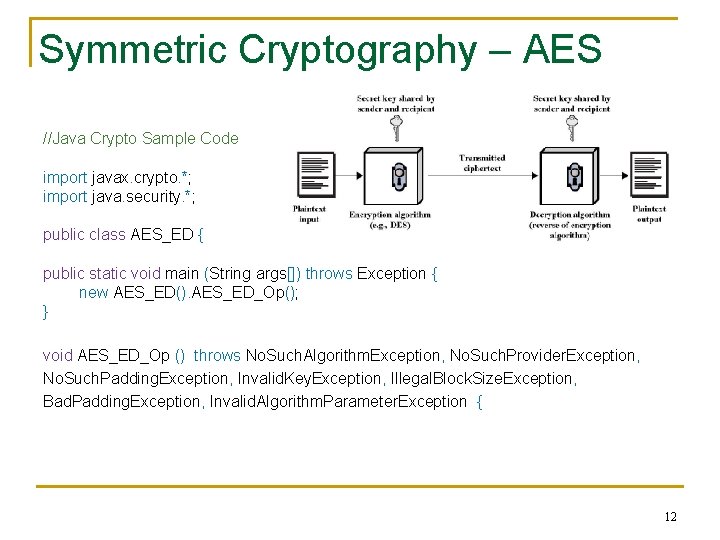
Symmetric Cryptography – AES //Java Crypto Sample Code import javax. crypto. *; import java. security. *; public class AES_ED { public static void main (String args[]) throws Exception { new AES_ED(). AES_ED_Op(); } void AES_ED_Op () throws No. Such. Algorithm. Exception, No. Such. Provider. Exception, No. Such. Padding. Exception, Invalid. Key. Exception, Illegal. Block. Size. Exception, Bad. Padding. Exception, Invalid. Algorithm. Parameter. Exception { 12
![Symmetric Cryptography – AES // secret message byte plaintext [] = {'S', 'E', 'C', Symmetric Cryptography – AES // secret message byte plaintext [] = {'S', 'E', 'C',](http://slidetodoc.com/presentation_image_h/1829485dffd8057b6f37e8b213c33530/image-13.jpg)
Symmetric Cryptography – AES // secret message byte plaintext [] = {'S', 'E', 'C', 'R', 'E', 'T'}; // make a Key. Generator object for AES Key. Generator AES_keygen = Key. Generator. get. Instance ("AES"); // init the generator to produce 256 -bit keys and use a random seed AES_keygen. init (256, new Secure. Random ()); // generate a 256 -bit AES key Secret. Key AES_Key = AES_keygen. generate. Key (); // make a Cipher object for AES with ECB mode and PKCS 5 Padding, // using the Bouncycastle provider Cipher AES_Cipher = Cipher. get. Instance ("AES/ECB/PKCS 5 Padding", "BC"); 13
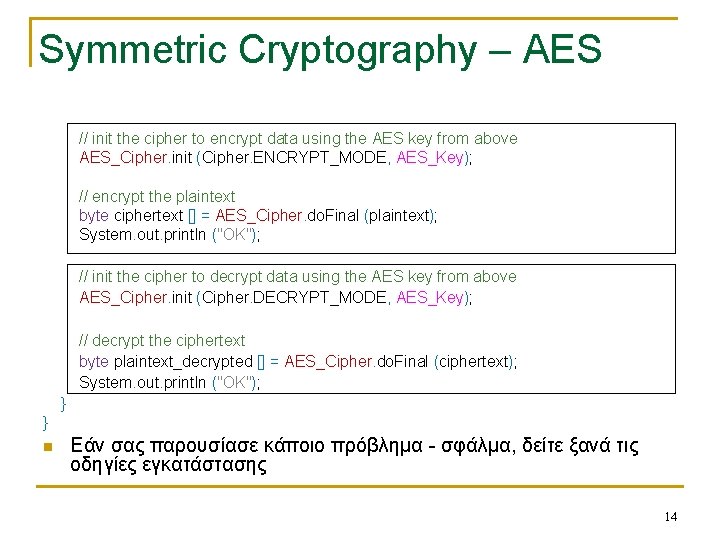
Symmetric Cryptography – AES // init the cipher to encrypt data using the AES key from above AES_Cipher. init (Cipher. ENCRYPT_MODE, AES_Key); // encrypt the plaintext byte ciphertext [] = AES_Cipher. do. Final (plaintext); System. out. println ("OK"); // init the cipher to decrypt data using the AES key from above AES_Cipher. init (Cipher. DECRYPT_MODE, AES_Key); // decrypt the ciphertext byte plaintext_decrypted [] = AES_Cipher. do. Final (ciphertext); System. out. println ("OK"); } } n Εάν σας παρουσίασε κάποιο πρόβλημα - σφάλμα, δείτε ξανά τις οδηγίες εγκατάστασης 14
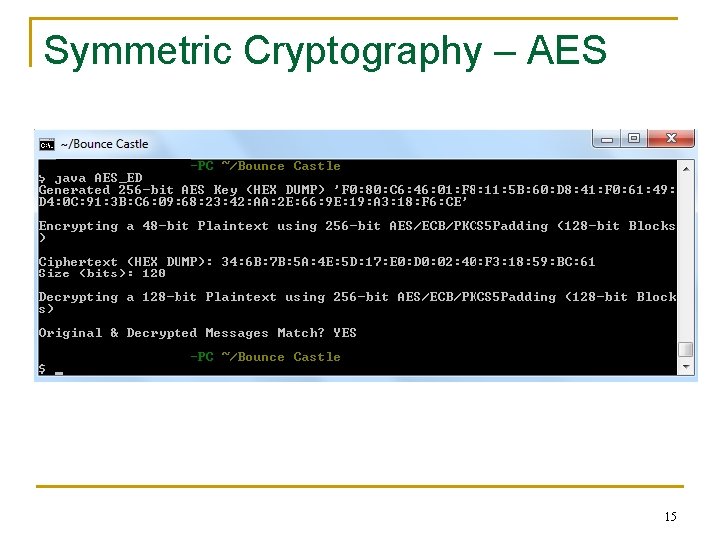
Symmetric Cryptography – AES 15
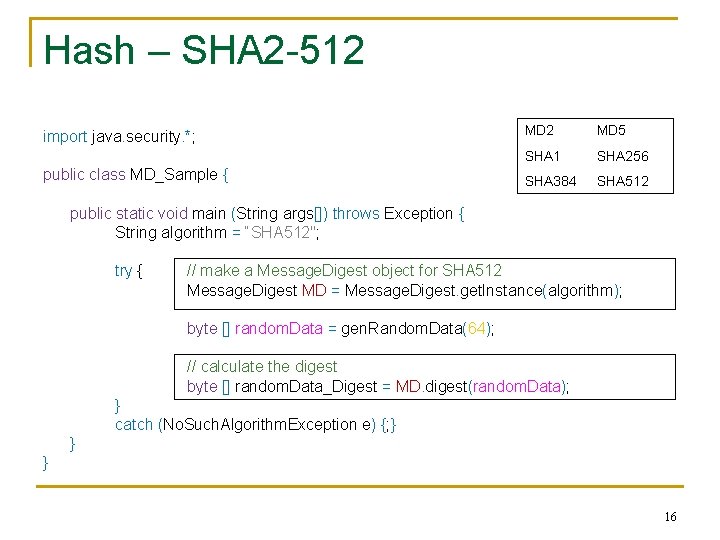
Hash – SHA 2 -512 import java. security. *; public class MD_Sample { MD 2 MD 5 SHA 1 SHA 256 SHA 384 SHA 512 public static void main (String args[]) throws Exception { String algorithm = “SHA 512"; try { // make a Message. Digest object for SHA 512 Message. Digest MD = Message. Digest. get. Instance(algorithm); byte [] random. Data = gen. Random. Data(64); // calculate the digest byte [] random. Data_Digest = MD. digest(random. Data); } catch (No. Such. Algorithm. Exception e) {; } } } 16
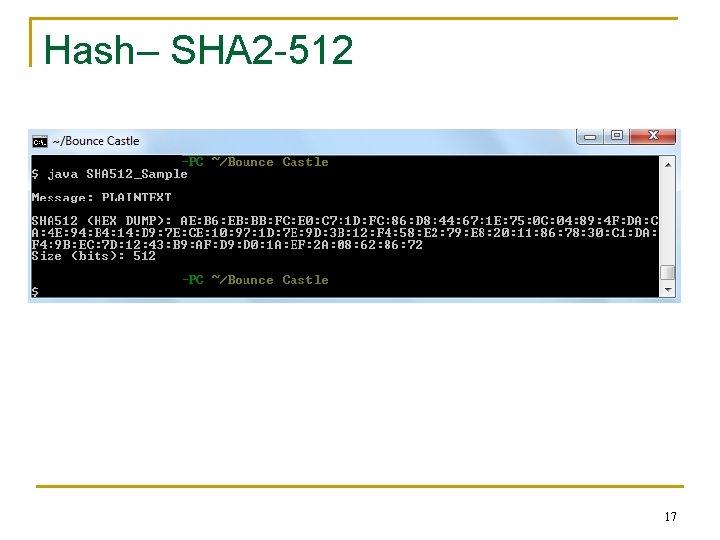
Hash– SHA 2 -512 17
MAC – (H)MAC n HMAC q q q A keyed-hash message authentication code (HMAC) is a specific construction for calculating a message authentication code (MAC) involving a cryptographic hash function in combination with a secret cryptographic key It may be used to simultaneously verify both the data integrity and the authentication of a message Any cryptographic hash function may be used in the calculation of an HMAC; the resulting MAC algorithm is termed HMAC-MD 5 or HMAC-SHA 1, etc The cryptographic strength of the HMAC depends upon the cryptographic strength of the underlying hash function, the size of its hash output, and on the size and quality of the key The design of the HMAC specification was motivated by the existence of attacks on more trivial mechanisms for combining a key with a hash function The Keccak hash function, that was selected by NIST as the SHA-3 competition winner, doesn't need this nested approach and can be used to generate a MAC by simply prepending the key to the message. 18
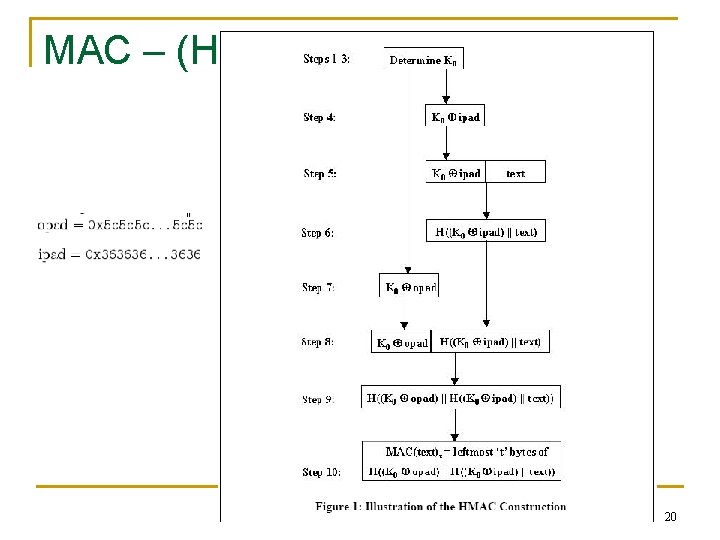
MAC – (H)MAC n HMAC q q Concatenates the secret to the front of the message Digests the combination Concatenates the secret to the front of the digest Digests the combination again HMAC = h(K opad, h(K ipad, message)) where K is the key padded out with extra zeros to the block size of the hash f q q opad, ipad are specified one-block–long padding constants Their values are not critical to the security of the algorithm, but were defined in such a way to have a large Hamming distance (the number of positions at which the corresponding symbols are different) from each other and so the inner and outer keys will have fewer bits in common 19
MAC – (H)MAC 20
MAC – (H)MAC import javax. crypto. *; Hmac. MD 5 Hmac. SHA 384 public class Mac_Sample { public static void main (String args[]) throws Exception { String algorithm = “Hmac. SHA 512"; try { Hmac. SHA 1 Hmac. SHA 512 // make a Mac object for Hmac. SHA 512 Mac my. Mac = Mac. get. Instance(algorithm); // init the mac to encrypt data using a 128 -bit AES key my. Mac. init (get. AESkey(128)); // get. AESkey() must be implemented! byte [] random. Data = gen. Random. Data(64); // calculate the mac byte [] random. Data_Mac = my. Mac. do. Final(random. Data); } catch (No. Such. Algorithm. Exception e) {; } } } 21
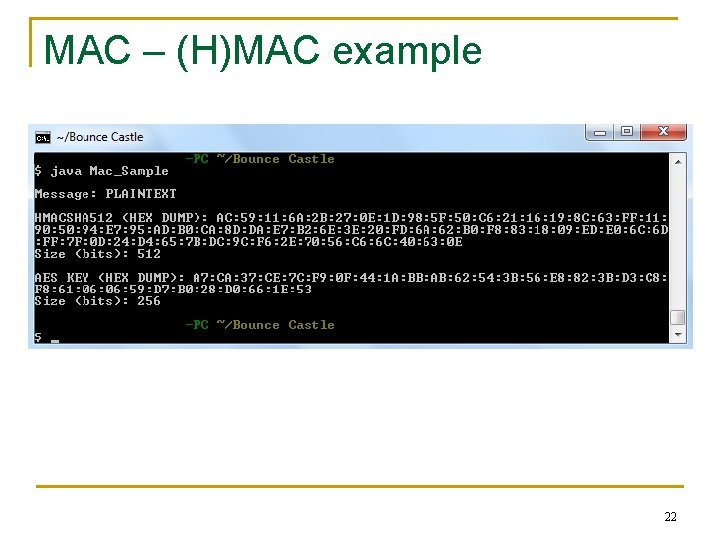
MAC – (H)MAC example 22
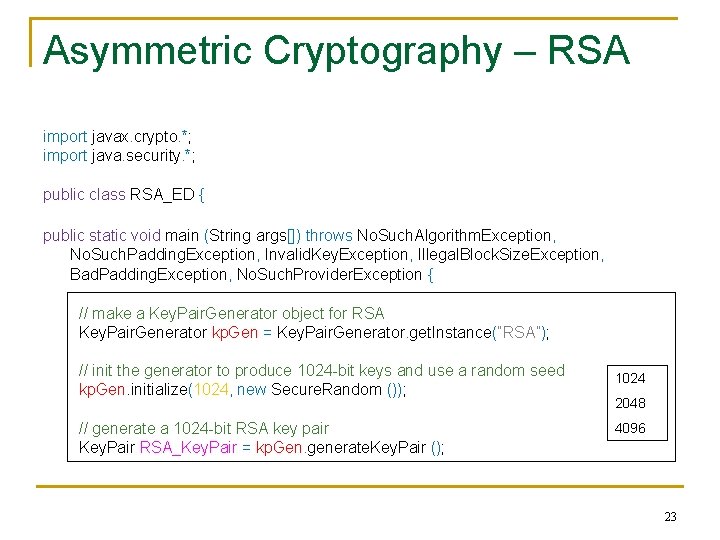
Asymmetric Cryptography – RSA import javax. crypto. *; import java. security. *; public class RSA_ED { public static void main (String args[]) throws No. Such. Algorithm. Exception, No. Such. Padding. Exception, Invalid. Key. Exception, Illegal. Block. Size. Exception, Bad. Padding. Exception, No. Such. Provider. Exception { // make a Key. Pair. Generator object for RSA Key. Pair. Generator kp. Gen = Key. Pair. Generator. get. Instance(“RSA”); // init the generator to produce 1024 -bit keys and use a random seed kp. Gen. initialize(1024, new Secure. Random ()); // generate a 1024 -bit RSA key pair Key. Pair RSA_Key. Pair = kp. Gen. generate. Key. Pair (); 1024 2048 4096 23
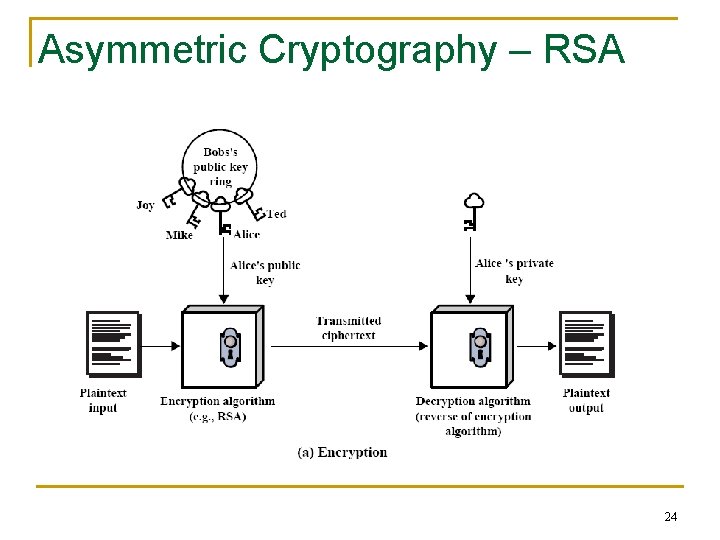
Asymmetric Cryptography – RSA 24
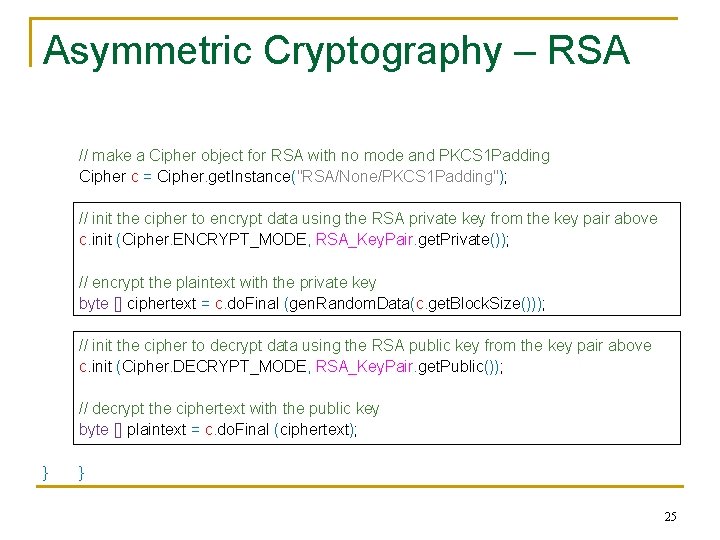
Asymmetric Cryptography – RSA // make a Cipher object for RSA with no mode and PKCS 1 Padding Cipher c = Cipher. get. Instance("RSA/None/PKCS 1 Padding"); // init the cipher to encrypt data using the RSA private key from the key pair above c. init (Cipher. ENCRYPT_MODE, RSA_Key. Pair. get. Private()); // encrypt the plaintext with the private key byte [] ciphertext = c. do. Final (gen. Random. Data(c. get. Block. Size())); // init the cipher to decrypt data using the RSA public key from the key pair above c. init (Cipher. DECRYPT_MODE, RSA_Key. Pair. get. Public()); // decrypt the ciphertext with the public key byte [] plaintext = c. do. Final (ciphertext); } } 25
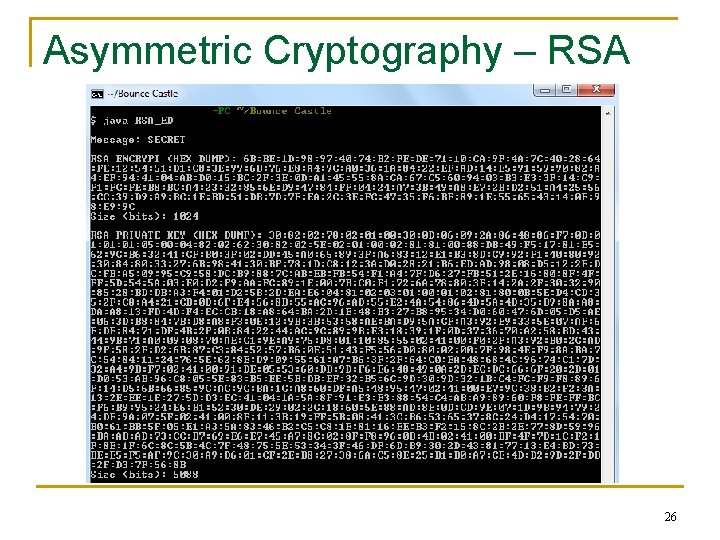
Asymmetric Cryptography – RSA 26
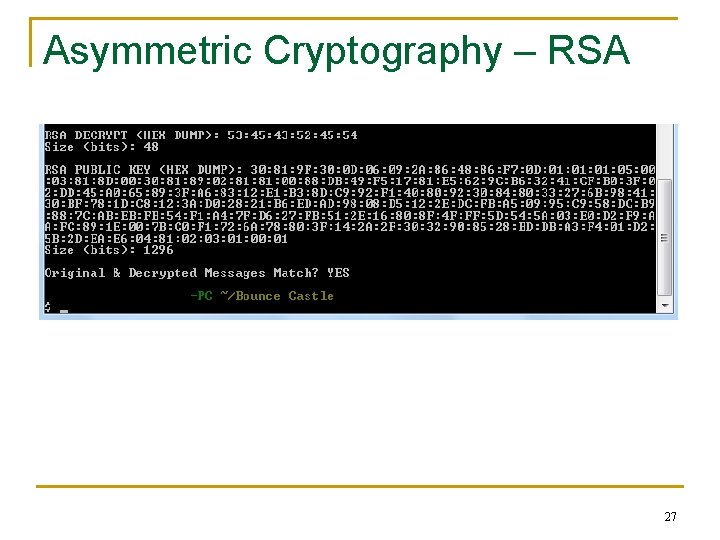
Asymmetric Cryptography – RSA 27
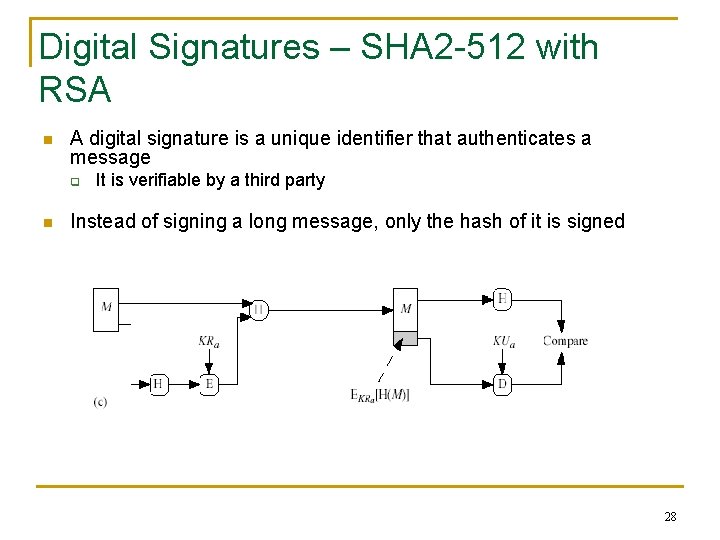
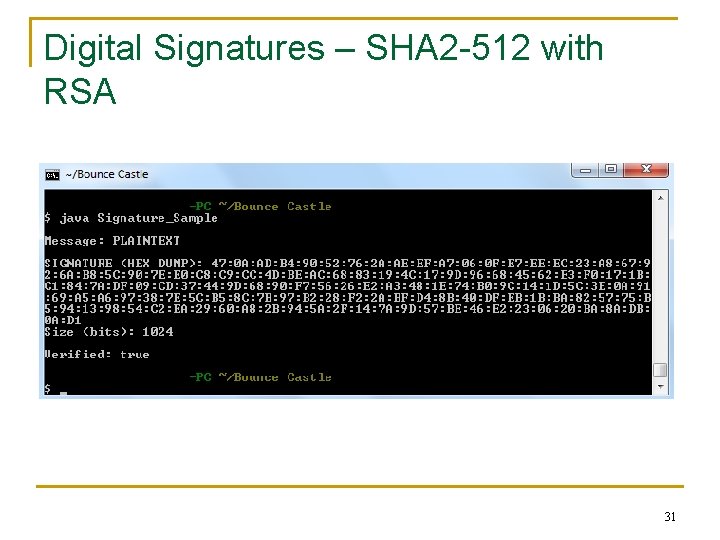
Digital Signatures – SHA 2 -512 with RSA n A digital signature is a unique identifier that authenticates a message q n It is verifiable by a third party Instead of signing a long message, only the hash of it is signed 28
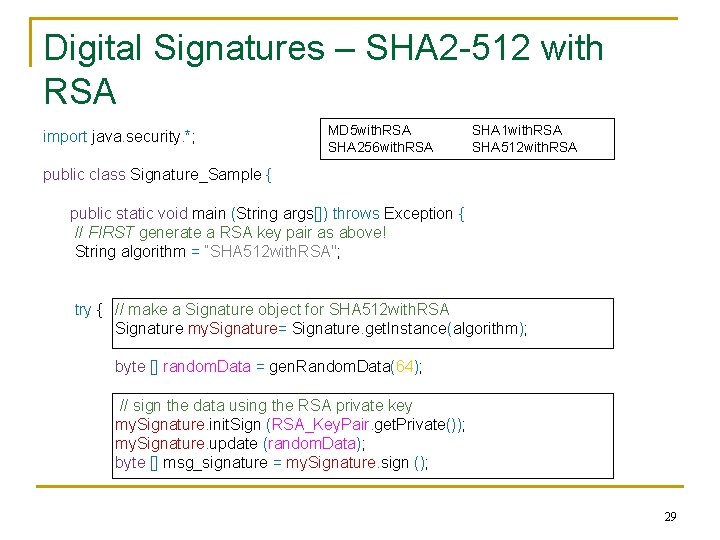
Digital Signatures – SHA 2 -512 with RSA import java. security. *; MD 5 with. RSA SHA 256 with. RSA SHA 1 with. RSA SHA 512 with. RSA public class Signature_Sample { public static void main (String args[]) throws Exception { // FIRST generate a RSA key pair as above! String algorithm = “SHA 512 with. RSA"; try { // make a Signature object for SHA 512 with. RSA Signature my. Signature= Signature. get. Instance(algorithm); byte [] random. Data = gen. Random. Data(64); // sign the data using the RSA private key my. Signature. init. Sign (RSA_Key. Pair. get. Private()); my. Signature. update (random. Data); byte [] msg_signature = my. Signature. sign (); 29
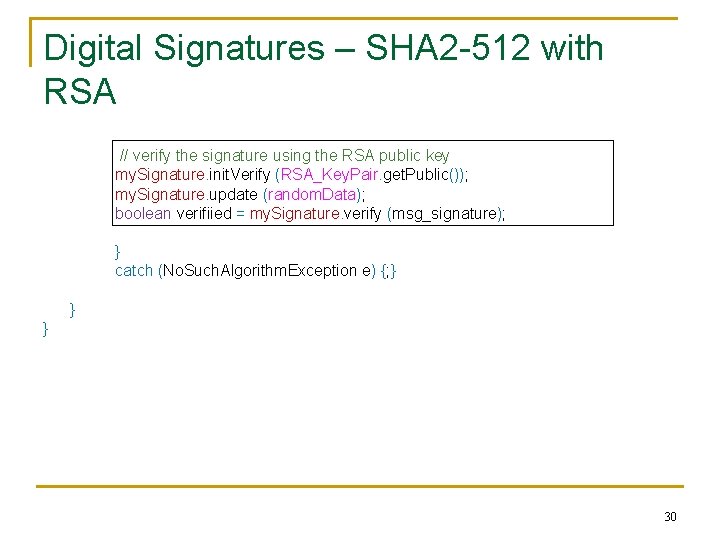
Digital Signatures – SHA 2 -512 with RSA // verify the signature using the RSA public key my. Signature. init. Verify (RSA_Key. Pair. get. Public()); my. Signature. update (random. Data); boolean verifiied = my. Signature. verify (msg_signature); } catch (No. Such. Algorithm. Exception e) {; } } } 30
Digital Signatures – SHA 2 -512 with RSA 31
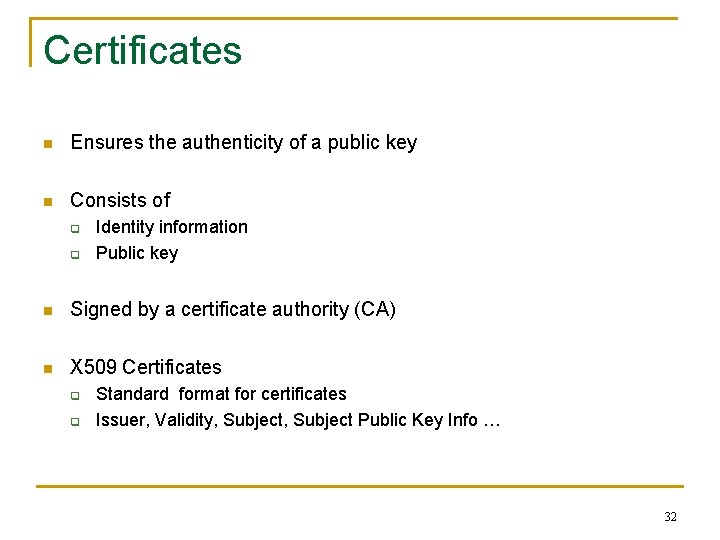
Certificates n Ensures the authenticity of a public key n Consists of q q Identity information Public key n Signed by a certificate authority (CA) n X 509 Certificates q q Standard format for certificates Issuer, Validity, Subject Public Key Info … 32
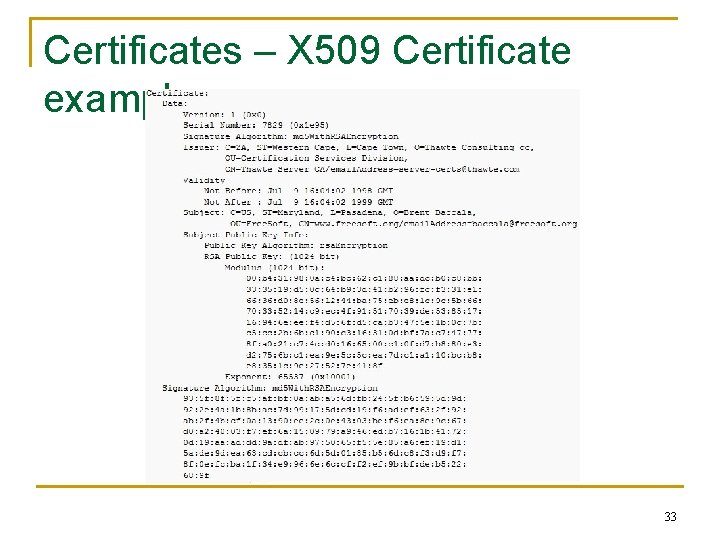
Certificates – X 509 Certificate example 33
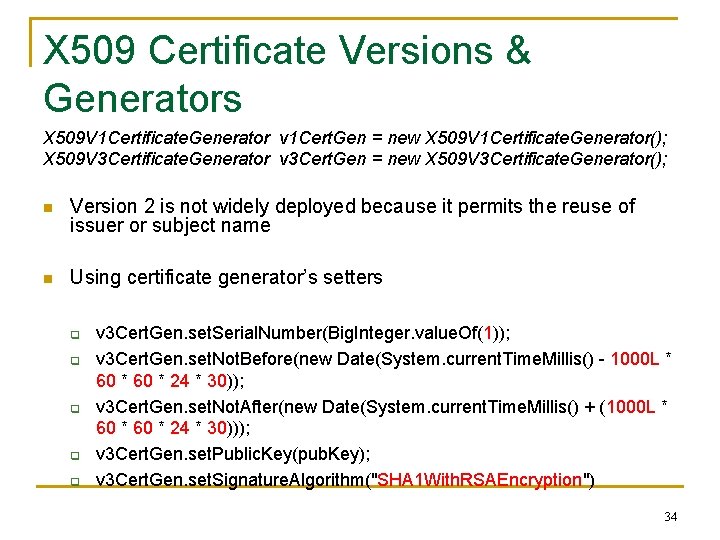
X 509 Certificate Versions & Generators X 509 V 1 Certificate. Generator v 1 Cert. Gen = new X 509 V 1 Certificate. Generator(); X 509 V 3 Certificate. Generator v 3 Cert. Gen = new X 509 V 3 Certificate. Generator(); n Version 2 is not widely deployed because it permits the reuse of issuer or subject name n Using certificate generator’s setters q q q v 3 Cert. Gen. set. Serial. Number(Big. Integer. value. Of(1)); v 3 Cert. Gen. set. Not. Before(new Date(System. current. Time. Millis() - 1000 L * 60 * 24 * 30)); v 3 Cert. Gen. set. Not. After(new Date(System. current. Time. Millis() + (1000 L * 60 * 24 * 30))); v 3 Cert. Gen. set. Public. Key(pub. Key); v 3 Cert. Gen. set. Signature. Algorithm("SHA 1 With. RSAEncryption") 34
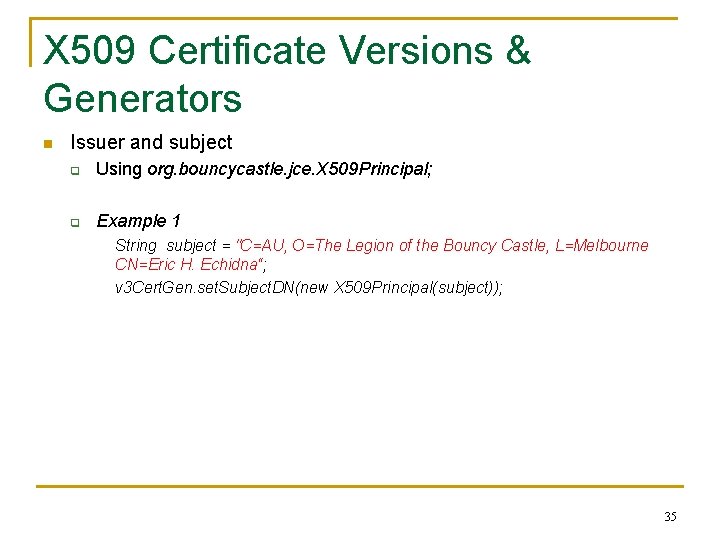
X 509 Certificate Versions & Generators n Issuer and subject q Using org. bouncycastle. jce. X 509 Principal; q Example 1 String subject = "C=AU, O=The Legion of the Bouncy Castle, L=Melbourne CN=Eric H. Echidna“; v 3 Cert. Gen. set. Subject. DN(new X 509 Principal(subject)); 35
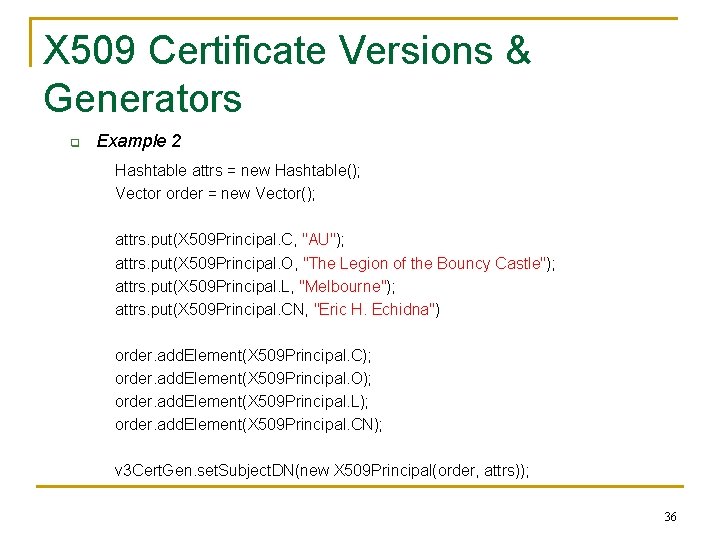
X 509 Certificate Versions & Generators q Example 2 Hashtable attrs = new Hashtable(); Vector order = new Vector(); attrs. put(X 509 Principal. C, "AU"); attrs. put(X 509 Principal. O, "The Legion of the Bouncy Castle"); attrs. put(X 509 Principal. L, "Melbourne"); attrs. put(X 509 Principal. CN, "Eric H. Echidna") order. add. Element(X 509 Principal. C); order. add. Element(X 509 Principal. O); order. add. Element(X 509 Principal. L); order. add. Element(X 509 Principal. CN); v 3 Cert. Gen. set. Subject. DN(new X 509 Principal(order, attrs)); 36
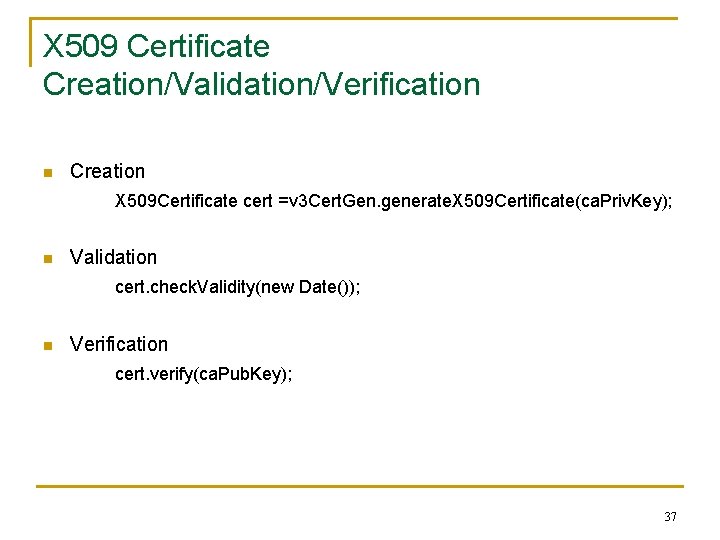
X 509 Certificate Creation/Validation/Verification n Creation X 509 Certificate cert =v 3 Cert. Gen. generate. X 509 Certificate(ca. Priv. Key); n Validation cert. check. Validity(new Date()); n Verification cert. verify(ca. Pub. Key); 37
PKCS#5 Padding n Block cipher modes (e. g. , ECB, CBC) for symmetric-key encryption algorithms require plain text input that is a multiple of the block size, so messages may have to be padded to bring them to this length n PKCS 5 Padding q q A padding scheme described in: RSA Laboratories, "PKCS #5: Password-Based Encryption Standard, " version 1. 5, November 1993 It follows the following rules: n n n q The number of bytes to be padded equals to "8 - number. Of. Bytes(clear. Text) mod 8". So 1 to 8 bytes will be padded to the clear text data depending on the length of the clear text data. All padded bytes have the same value - the number of bytes padded. PKCS 5 Padding schema can also be explained with the diagram below, if M is the original clear text and PM is the padded clear text: If number. Of. Bytes(clear. Text) mod 8 == 7, PM = M + 0 x 01 If number. Of. Bytes(clear. Text) mod 8 == 6, PM = M + 0 x 0202 If number. Of. Bytes(clear. Text) mod 8 == 5, PM = M + 0 x 030303. . . If number. Of. Bytes(clear. Text) mod 8 == 0, PM = M + 0 x 08080808 38
PKCS#1 Padding n In public key cryptography, padding is the process of preparing a message for encryption or signing using a specification or scheme such as PKCS#1 v 1. 5, OAEP, PSSR, IEEE P 1363 EMSA 2 and EMSA 5 q q A modern form of padding for asymmetric primitives is OAEP applied to the RSA algorithm, when it is used to encrypt a limited number of bytes The operation is referred to as "padding" because originally, random material was simply appended to the message to make it long enough for the primitive This form of padding is not secure and is therefore no longer applied A modern padding scheme aims to ensure that the attacker cannot manipulate the plaintext to exploit the mathematical structure of the primitive and will usually be accompanied by a proof, that breaking the padding scheme is as hard as solving the hard problem underlying the primitive 39
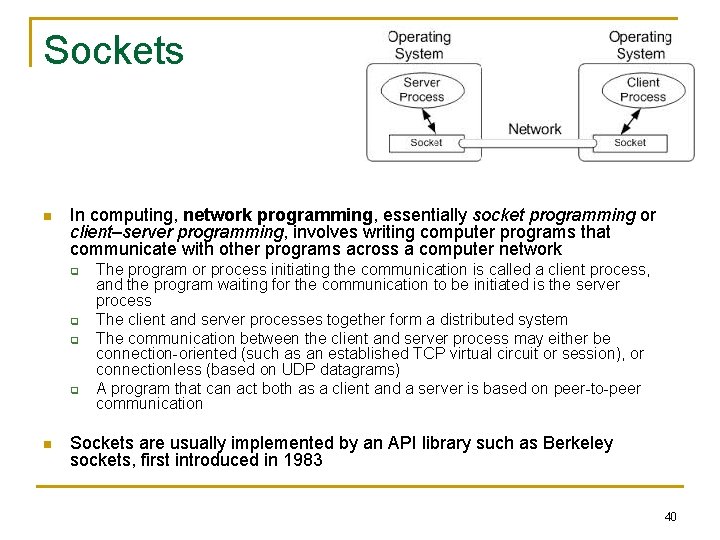
Sockets n In computing, network programming, essentially socket programming or client–server programming, involves writing computer programs that communicate with other programs across a computer network q q n The program or process initiating the communication is called a client process, and the program waiting for the communication to be initiated is the server process The client and server processes together form a distributed system The communication between the client and server process may either be connection-oriented (such as an established TCP virtual circuit or session), or connectionless (based on UDP datagrams) A program that can act both as a client and a server is based on peer-to-peer communication Sockets are usually implemented by an API library such as Berkeley sockets, first introduced in 1983 40
Socket – Client example import java. io. *; import java. net. *; public class Client { public static void main (String args[]) throws IOException { // initialization the client socket Socket my. Socket = null; Print. Writer out = null; Buffered. Reader in = null; 41
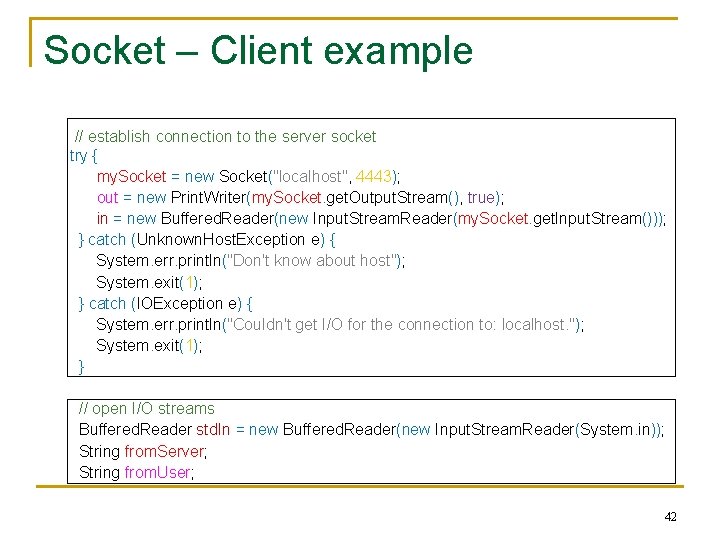
Socket – Client example // establish connection to the server socket try { my. Socket = new Socket("localhost", 4443); out = new Print. Writer(my. Socket. get. Output. Stream(), true); in = new Buffered. Reader(new Input. Stream. Reader(my. Socket. get. Input. Stream())); } catch (Unknown. Host. Exception e) { System. err. println("Don't know about host"); System. exit(1); } catch (IOException e) { System. err. println("Couldn't get I/O for the connection to: localhost. "); System. exit(1); } // open I/O streams Buffered. Reader std. In = new Buffered. Reader(new Input. Stream. Reader(System. in)); String from. Server; String from. User; 42
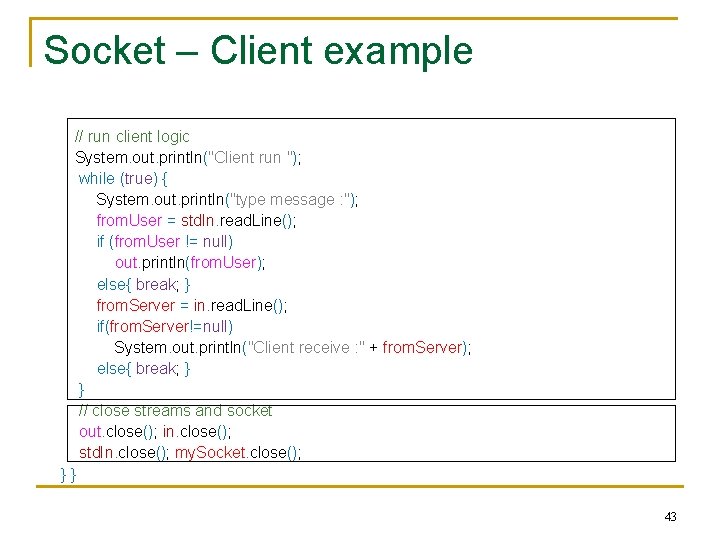
Socket – Client example // run client logic System. out. println("Client run "); while (true) { System. out. println("type message : "); from. User = std. In. read. Line(); if (from. User != null) out. println(from. User); else{ break; } from. Server = in. read. Line(); if(from. Server!=null) System. out. println("Client receive : " + from. Server); else{ break; } } // close streams and socket out. close(); in. close(); std. In. close(); my. Socket. close(); }} 43
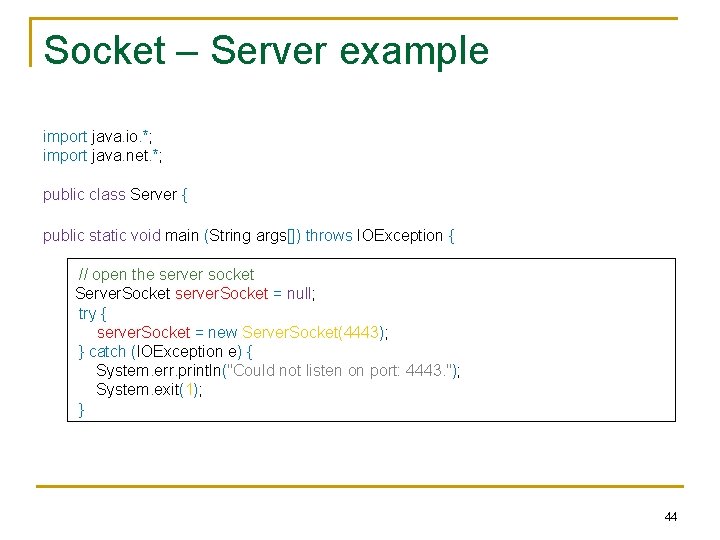
Socket – Server example import java. io. *; import java. net. *; public class Server { public static void main (String args[]) throws IOException { // open the server socket Server. Socket server. Socket = null; try { server. Socket = new Server. Socket(4443); } catch (IOException e) { System. err. println("Could not listen on port: 4443. "); System. exit(1); } 44
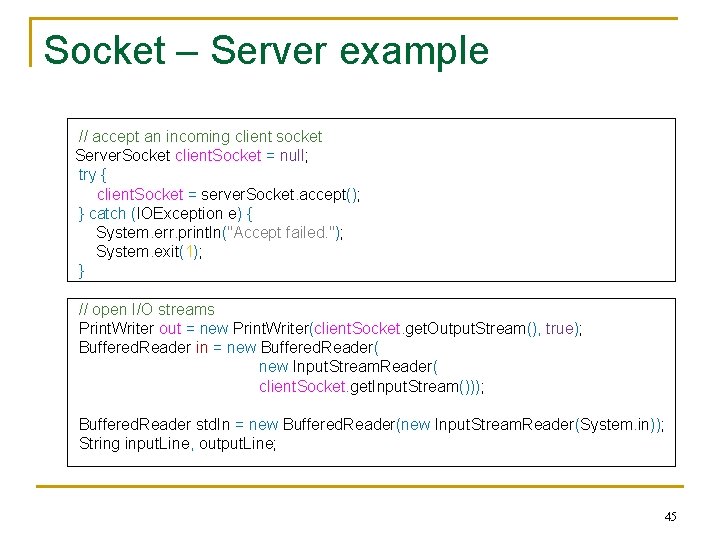
Socket – Server example // accept an incoming client socket Server. Socket client. Socket = null; try { client. Socket = server. Socket. accept(); } catch (IOException e) { System. err. println("Accept failed. "); System. exit(1); } // open I/O streams Print. Writer out = new Print. Writer(client. Socket. get. Output. Stream(), true); Buffered. Reader in = new Buffered. Reader( new Input. Stream. Reader( client. Socket. get. Input. Stream())); Buffered. Reader std. In = new Buffered. Reader(new Input. Stream. Reader(System. in)); String input. Line, output. Line; 45
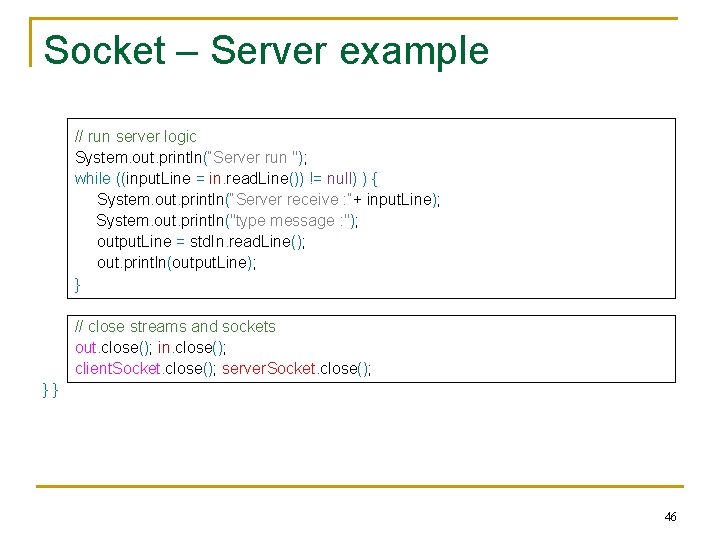
Socket – Server example // run server logic System. out. println(“Server run "); while ((input. Line = in. read. Line()) != null) ) { System. out. println(“Server receive : “+ input. Line); System. out. println("type message : "); output. Line = std. In. read. Line(); out. println(output. Line); } // close streams and sockets out. close(); in. close(); client. Socket. close(); server. Socket. close(); }} 46
References n http: //www. bouncycastle. org/java. html q n http: //www. bouncycastle. org/docs 1. 6/ q n Bouncycastle Java Crypto API Documentation http: //docs. oracle. com/javase/7/docs/api/ q n Bouncycastle Java Crypto API Provider Sun Java API Documentation Online http: //docs. oracle. com/javase/7/docs/technotes/guides/security/crypt o/Crypto. Spec. html q Sun Java Cryptography Architecture Reference Guide 47
References n http: //www. cs. berkeley. edu/~jonah/bc/org/bouncycastle/x 509/packa ge-summary. html q n http: //www. cs. berkeley. edu/~jonah/bc/org/bouncycastle/jce/packagesummary. html q n Generation of X. 509 certificates and X. 509 attribute certificates Utility classes http: //docs. oracle. com/javase/tutorial/networking/sockets/ q Sockets 48
Summary n Crypto technologies – Bouncy Castle crypto library (JAVA) q Installation q Symmetric Cryptography – AES example MAC – SHA 512 example Asymmetric Cryptography – RSA example Digital Signatures – SHA 512 with RSA example Certificates – X 509 Certificate example q Sockets – Client/Server example q q 49
- Slides: 49