Direct Link Networks Textbook Computer Networks A Systems
Direct Link Networks Textbook: Computer Networks: A Systems Approach, L. Peterson, B. Davie, Morgan Kaufmann Chapter 2. Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 1
Direct Links: Outline • Physical Layer – Link technologies – Encoding • Link Layer – – Framing Error Detection Reliable Transmission (ARQ protocols) Medium Access Control: • Existing protocols: Ethernet, Token Rings, Wireless Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 2
Link Technologies • Cables: – – Cat 5 twisted pair, 10 -100 Mbps, 100 m Thin-net coax, 10 -100 Mbps, 200 m Thick-net coax, 10 -100 Mbps, 500 m Fiber, 100 Mbps-2. 4 Gbps, 2 -40 km • Leased Lines: – Copper based: T 1 (1. 544 Mbps), T 3 (44. 736 Mbps) – Optical fiber: STS-1 (51. 84 Mbps), STS-N (N*51. 84 Mbps) • Last-Mile Links: – POTS (56 Kbps), ISDN (2*64 Kbps) – x. DSL: ADSL (16 -640 Kbps, 1. 554 -8. 448 Mbps), VDSL (12. 96 Mbps 55. 2 Mbps) – CATV: 40 Mbps downstream, 20 Mbps upstream • Wireless Links: Cellular, Satellite, Wireless Local Loop Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 3
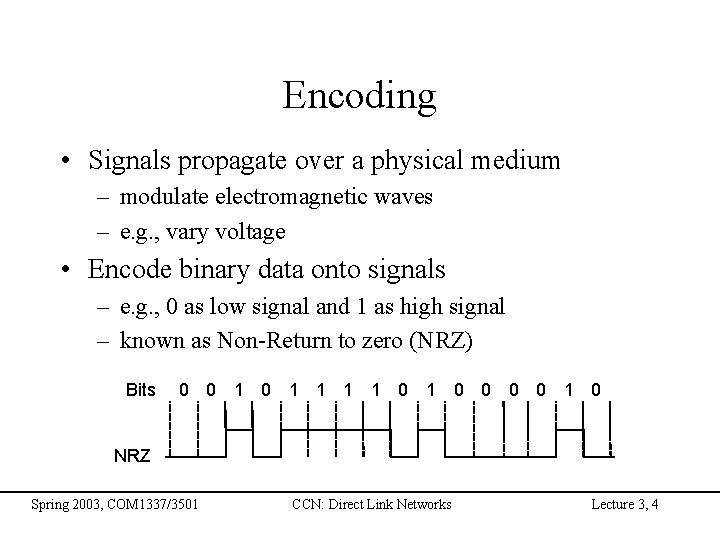
Encoding • Signals propagate over a physical medium – modulate electromagnetic waves – e. g. , vary voltage • Encode binary data onto signals – e. g. , 0 as low signal and 1 as high signal – known as Non-Return to zero (NRZ) Bits 0 0 1 1 1 1 0 0 0 0 1 0 NRZ Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 4
Problem: Consecutive 1 s or 0 s • Low signal (0) may be interpreted as no signal • High signal (1) leads to baseline wander – Receiver compares rx_signal to avg_signal • Clock drift: Unable to recover clock Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 5
Alternative Encodings • Non-return to Zero Inverted (NRZI) – make a transition from current signal to encode a one; stay at current signal to encode a zero – solves the problem of consecutive ones • Manchester – transmit XOR of the NRZ encoded data and the clock – only 50% efficient. Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 6
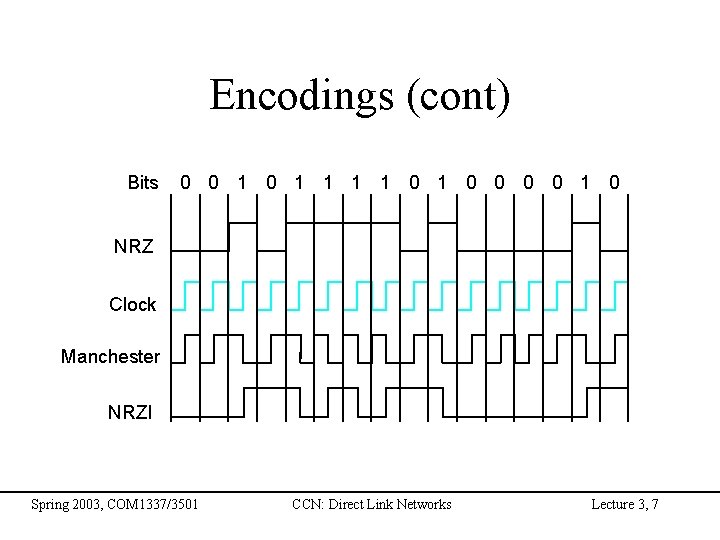
Encodings (cont) Bits 0 0 1 1 1 1 0 0 0 0 1 0 NRZ Clock Manchester NRZI Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 7
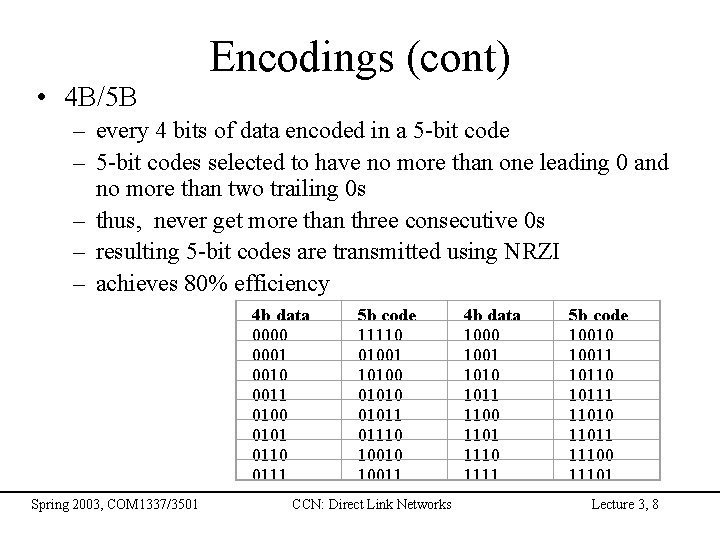
• 4 B/5 B Encodings (cont) – every 4 bits of data encoded in a 5 -bit code – 5 -bit codes selected to have no more than one leading 0 and no more than two trailing 0 s – thus, never get more than three consecutive 0 s – resulting 5 -bit codes are transmitted using NRZI – achieves 80% efficiency 4 b data 0000 0001 0010 0011 0100 0101 0110 0111 Spring 2003, COM 1337/3501 5 b code 11110 01001 10100 01011 01110 10011 CCN: Direct Link Networks 4 b data 1000 1001 1010 1011 1100 1101 1110 1111 5 b code 10010 10011 10110 10111 11010 11011 11100 11101 Lecture 3, 8
Framing • The physical layer provides a mean to transmit a sequence of bits • How can one determine the beginning/end of a frame? • Solutions: – – Character-based framing (use special control characters) Bit-oriented framing with flags Length counts Clock based Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 9
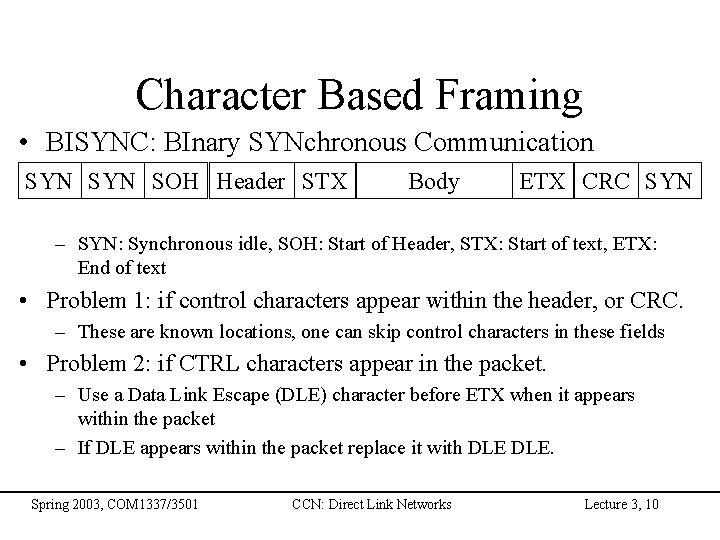
Character Based Framing • BISYNC: BInary SYNchronous Communication SYN SOH Header STX Body ETX CRC SYN – SYN: Synchronous idle, SOH: Start of Header, STX: Start of text, ETX: End of text • Problem 1: if control characters appear within the header, or CRC. – These are known locations, one can skip control characters in these fields • Problem 2: if CTRL characters appear in the packet. – Use a Data Link Escape (DLE) character before ETX when it appears within the packet – If DLE appears within the packet replace it with DLE. Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 10
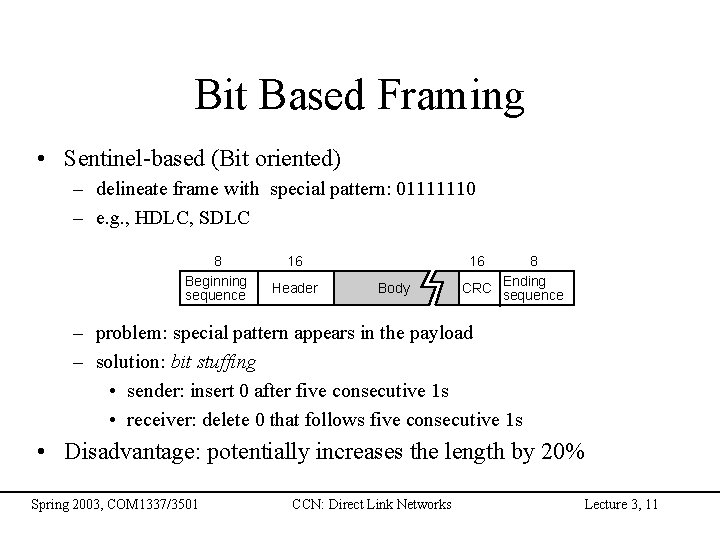
Bit Based Framing • Sentinel-based (Bit oriented) – delineate frame with special pattern: 01111110 – e. g. , HDLC, SDLC 8 Beginning sequence 16 Header 16 Body 8 CRC Ending sequence – problem: special pattern appears in the payload – solution: bit stuffing • sender: insert 0 after five consecutive 1 s • receiver: delete 0 that follows five consecutive 1 s • Disadvantage: potentially increases the length by 20% Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 11
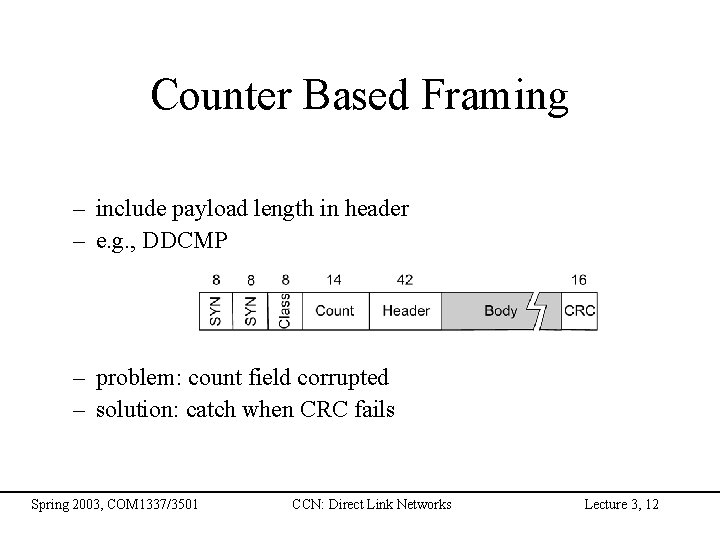
Counter Based Framing – include payload length in header – e. g. , DDCMP – problem: count field corrupted – solution: catch when CRC fails Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 12

Clock Based Framing • SONET: Synchronous Optical Network • Each frame is 125 micro-seconds long: 810 bytes for STS-1 • STS-n (STS-1 = 51. 84 Mbps) Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 13
Direct Links: Outline • Physical Layer – Link technologies – Encoding • Link Layer – – Framing Error Detection Reliable Transmission (ARQ protocols) Medium Access Control (MAC): • Existing protocols: Ethernet, Token Rings, Wireless Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 14
Error Detection • Bits can get corrupted on transmissions • How to detect, and if possible, correct them • Error detection techniques: – Parity bit – Internet checksum – Cyclic redundancy check (CRC) Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 15
Parity Bit • Simplest of all techniques • Single parity bit – Add a bit that takes the XOR of all the data bits – What kind of errors can it detect? • Two dimensional parity: – – Arrange the data in a 2 D matrix Take the parity along each row and row column Send the data with the parity bits What kind of errors can it detect? Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 16
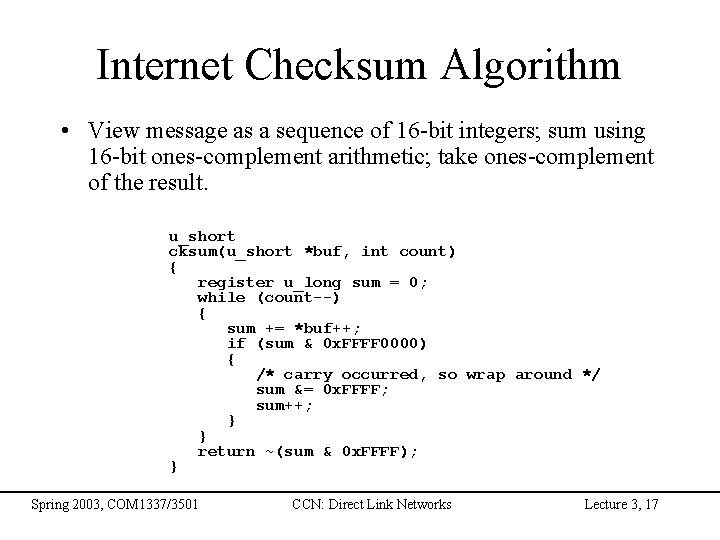
Internet Checksum Algorithm • View message as a sequence of 16 -bit integers; sum using 16 -bit ones-complement arithmetic; take ones-complement of the result. u_short cksum(u_short *buf, int count) { register u_long sum = 0; while (count--) { sum += *buf++; if (sum & 0 x. FFFF 0000) { /* carry occurred, so wrap around */ sum &= 0 x. FFFF; sum++; } } return ~(sum & 0 x. FFFF); } Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 17
Cyclic Redundancy Check • Add k bits of redundant data to an n-bit message – want k << n – e. g. , k = 32 and n = 12, 000 (1500 bytes) • Represent n-bit message as n-1 degree polynomial – e. g. , MSG=10011010 as M(x) = x 7 + x 4 + x 3 + x 1 • Let k be the degree of some divisor polynomial – e. g. , C(x) = x 3 + x 2 + 1 Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 18

CRC (cont) • Transmit polynomial P(x) that is evenly divisible by C(x) – shift left k bits, i. e. , M(x)xk – subtract remainder of M(x)xk / C(x) from M(x)xk • Receiver polynomial P(x) + E(x) – E(x) = 0 implies no errors • Divide (P(x) + E(x)) by C(x); remainder zero if: – E(x) was zero (no error), or – E(x) is exactly divisible by C(x) Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 19

Selecting C(x) • All single-bit errors, as long as the xk and x 0 terms have non -zero coefficients. • Any odd number of errors, as long as C(x) contains the factor (x + 1) • Any ‘burst’ error (i. e. , sequence of consecutive error bits) for which the length of the burst is less than k bits. • Most burst errors of larger than k bits can also be detected • See Table 2. 6 on page 102 for common C(x) Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 20

Direct Links: Outline • Physical Layer – Link technologies – Encoding • Link Layer – – Framing Error Detection Reliable Transmission (ARQ protocols) Medium Access Control (MAC): • Existing protocols: Ethernet, Token Rings, Wireless Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 21

Reliable Transmission: ARQ • Automatic Repeat re. Quest (ARQ) • Underlying physical channel: – Each transmitted frame may be delayed by an arbitrary and variable time – Some frames might be lost and may never arrive – Assume that error detection works correctly – Frames that arrive are assumed to do so in order, with or without errors (this assumption is not always necessary, true for direct links) • Correctness of ARQ protocol: each packet is released to the network layer once and only once, without error • Efficiency: Use of link bandwidth (effective throughput) Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 22

Acknowledgements & Timeouts Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 23
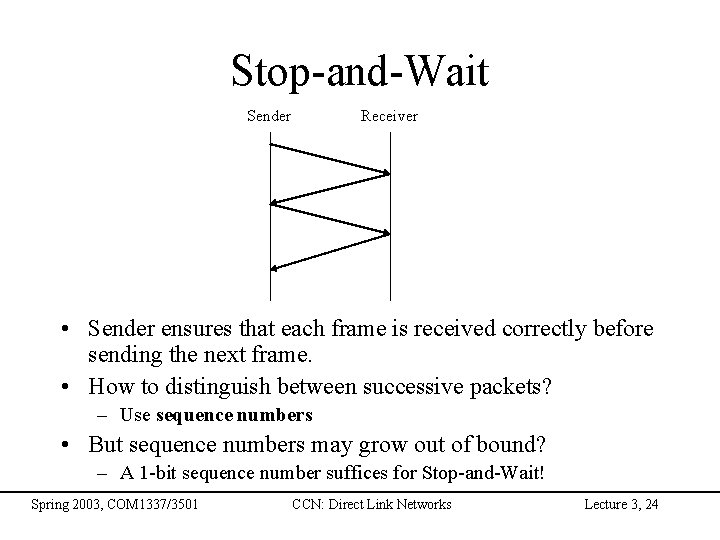
Stop-and-Wait Sender Receiver • Sender ensures that each frame is received correctly before sending the next frame. • How to distinguish between successive packets? – Use sequence numbers • But sequence numbers may grow out of bound? – A 1 -bit sequence number suffices for Stop-and-Wait! Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 24
Problems with Stop-and-Wait • Keeping the pipe full • Example – 1. 5 Mbps link x 45 ms RTT = 67. 5 Kb (8 KB) – 1 KB frames implies 1/8 th link utilization • How to keep the pipe full? – Send more frames without waiting for acks Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 25

Sliding Window • Allow multiple outstanding (un-ACKed) frames • Upper bound on un-ACKed frames, called window … Receiver … Time Sender Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 26
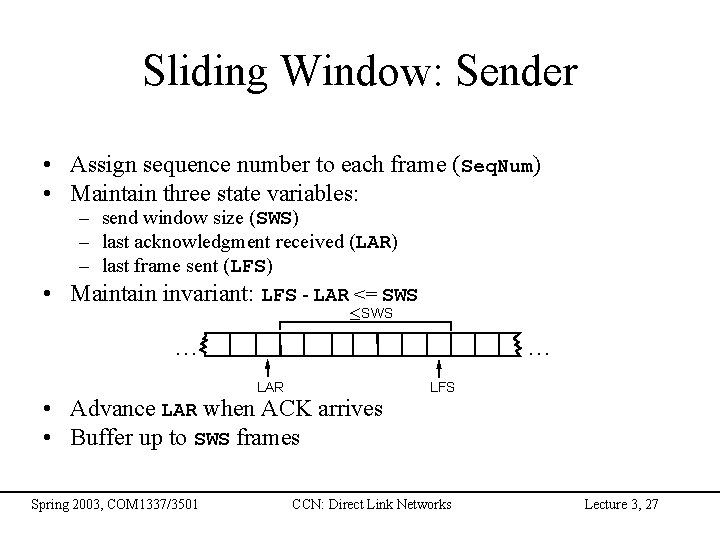
Sliding Window: Sender • Assign sequence number to each frame (Seq. Num) • Maintain three state variables: – send window size (SWS) – last acknowledgment received (LAR) – last frame sent (LFS) • Maintain invariant: LFS - LAR <= SWS £ SWS … … LAR • Advance LAR when ACK arrives • Buffer up to SWS frames Spring 2003, COM 1337/3501 LFS CCN: Direct Link Networks Lecture 3, 27
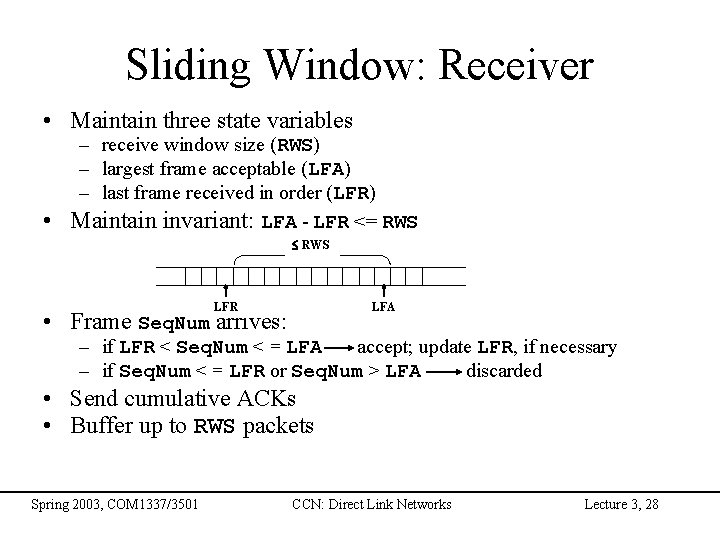
Sliding Window: Receiver • Maintain three state variables – receive window size (RWS) – largest frame acceptable (LFA) – last frame received in order (LFR) • Maintain invariant: LFA - LFR <= RWS LFR LFA • Frame Seq. Num arrives: – if LFR < Seq. Num < = LFA accept; update LFR, if necessary – if Seq. Num < = LFR or Seq. Num > LFA discarded • Send cumulative ACKs • Buffer up to RWS packets Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 28
Buffer Sizes • SWS set to bandwidth-delay product estimate • For RWS, two common settings – RWS = 1: receiver will not buffer any frames that arrive out of order – RWS = SWS • Does not make sense to set RWS > SWS Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 29
Sequence Number Space • Seq. Num field is finite; sequence numbers wrap around • Sequence number space must be larger then number of outstanding frames • If RWS=SWS, SWS <= Max. Seq. Num-1 is not sufficient – – – suppose 3 -bit Seq. Num field (0. . 7) SWS=RWS=7 sender transmit frames 0. . 6 arrive successfully, but ACKs lost sender retransmits 0. . 6 receiver expecting 7, 0. . 5, but receives second incarnation of 0. . 5 • SWS < (Max. Seq. Num+1)/2 is correct rule • Intuitively, Seq. Num “slides” between two halves of sequence number space Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 30

Concurrent Logical Channels • Multiplex 8 logical channels over a single link • Run stop-and-wait on each logical channel • Maintain three state bits per channel – channel busy – current sequence number out – next sequence number in • Header: 3 -bit channel num, 1 -bit sequence num – 4 -bits total • Separates reliability from order • Data link layer protocol used in ARPANET Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 31
Direct Links: Outline • Physical Layer – Link technologies – Encoding • Link Layer – – Framing Error Detection Reliable Transmission (ARQ protocols) Medium Access Control (MAC): • Existing protocols: Ethernet, Token Rings, Wireless Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 32
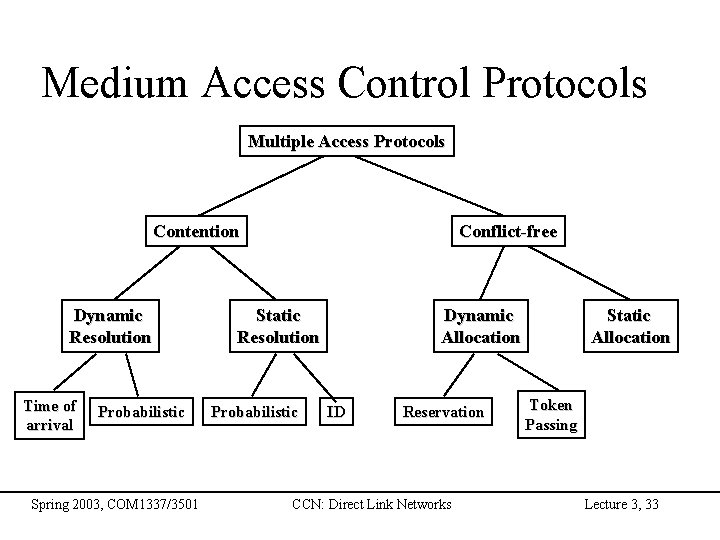
Medium Access Control Protocols Multiple Access Protocols Contention Dynamic Resolution Time of arrival Probabilistic Spring 2003, COM 1337/3501 Conflict-free Static Resolution Probabilistic Dynamic Allocation ID Reservation CCN: Direct Link Networks Static Allocation Token Passing Lecture 3, 33
MAC Protocols: Evaluation • • Throughput Delay Buffering Stability We also generally assume that: – channel is errorless – feedback is available Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 34
Carrier Sense Protocols • Use the fact that in some networks you can sense the medium to check whether it is currently free – – 1 -persistent CSMA non-persistent CSMA p-persistent protocol CSMA with collision Detection (CSMA/CD) • 1 -persistent CSMA – when a station has a packet: • it waits until the medium is free to transmit the packet • if a collision occurs, the station waits a random amount of time – first transmission results in a collision if several stations are waiting for the channel Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 35
Carrier Sense Protocols (Cont’d) • non-persistent CSMA – when a station has a packet: • if the medium is free, transmit the packet • otherwise wait for a random period of time and repeat the algorithm – higher delays, but better performance than pure ALOHA • p-persistent protocol – when a station has a packet wait until the medium is free: • transmit the packet with probability p • wait for next slot with probability 1 -p – better throughput than other schemes but higher delay • CSMA with Collision Detection (CSMA/CD) – stations abort their transmission when they detect a collision – e. g. , Ethernet, IEEE 802. 3 Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 36
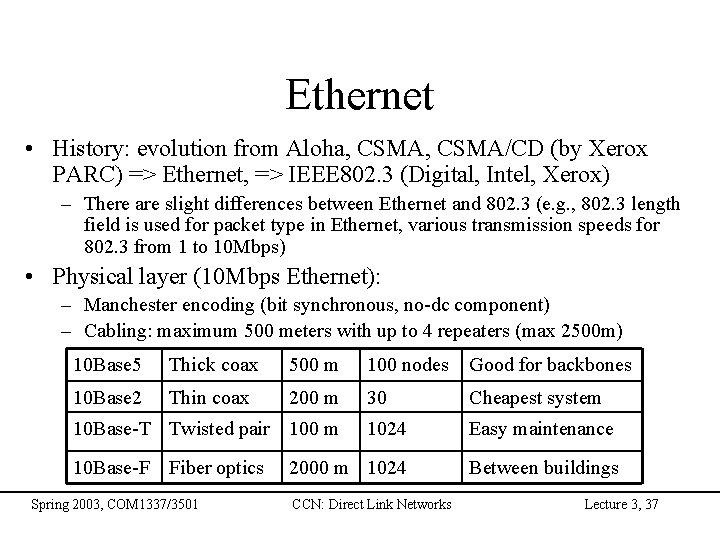
Ethernet • History: evolution from Aloha, CSMA/CD (by Xerox PARC) => Ethernet, => IEEE 802. 3 (Digital, Intel, Xerox) – There are slight differences between Ethernet and 802. 3 (e. g. , 802. 3 length field is used for packet type in Ethernet, various transmission speeds for 802. 3 from 1 to 10 Mbps) • Physical layer (10 Mbps Ethernet): – Manchester encoding (bit synchronous, no-dc component) – Cabling: maximum 500 meters with up to 4 repeaters (max 2500 m) 10 Base 5 Thick coax 500 m 100 nodes Good for backbones 10 Base 2 Thin coax 200 m 30 Cheapest system 1024 Easy maintenance 2000 m 1024 Between buildings 10 Base-T Twisted pair 100 m 10 Base-F Fiber optics Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 37
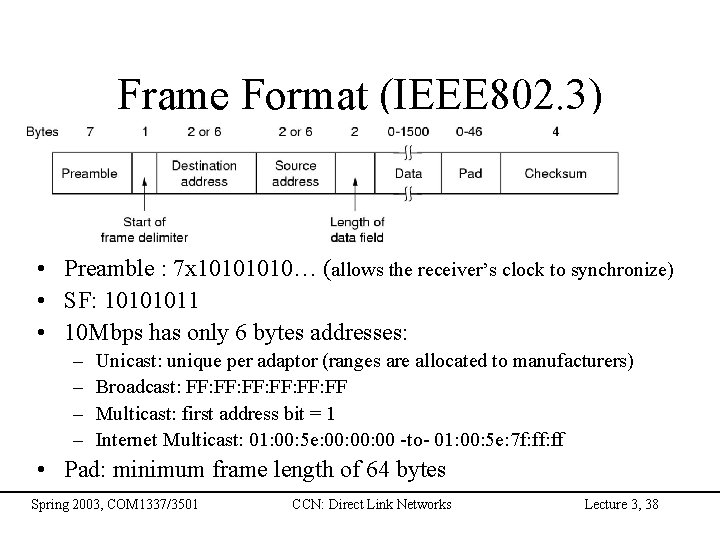
Frame Format (IEEE 802. 3) • Preamble : 7 x 1010… (allows the receiver’s clock to synchronize) • SF: 10101011 • 10 Mbps has only 6 bytes addresses: – – Unicast: unique per adaptor (ranges are allocated to manufacturers) Broadcast: FF: FF: FF Multicast: first address bit = 1 Internet Multicast: 01: 00: 5 e: 00: 00 -to- 01: 00: 5 e: 7 f: ff • Pad: minimum frame length of 64 bytes Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 38
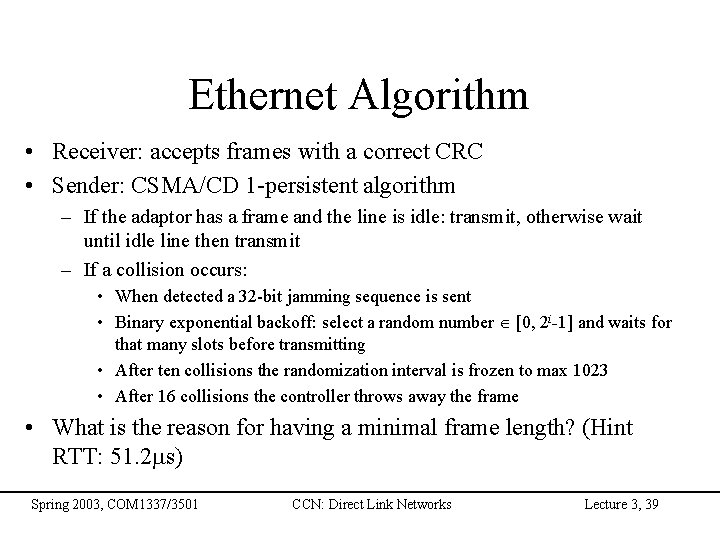
Ethernet Algorithm • Receiver: accepts frames with a correct CRC • Sender: CSMA/CD 1 -persistent algorithm – If the adaptor has a frame and the line is idle: transmit, otherwise wait until idle line then transmit – If a collision occurs: • When detected a 32 -bit jamming sequence is sent • Binary exponential backoff: select a random number [0, 2 i-1] and waits for that many slots before transmitting • After ten collisions the randomization interval is frozen to max 1023 • After 16 collisions the controller throws away the frame • What is the reason for having a minimal frame length? (Hint RTT: 51. 2 ms) Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 39

Ethernet Performance • Assume that retransmissions occur with probability p, k stations ready to transmit: – – – Probability that a station acquires the channel: A=kp(1 -p)k-1 Maximum: when p=1/k, k-> A->1/e Probability that a contention interval has exactly j slots is: A(1 -A)j-1 Mean number of slots per contention is: 1/A -> e = 2. 718… Slot duration: 2 t = 51. 2 ms Channel efficiency: P/(P+2 te), where P is transmission time for a packet Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 40
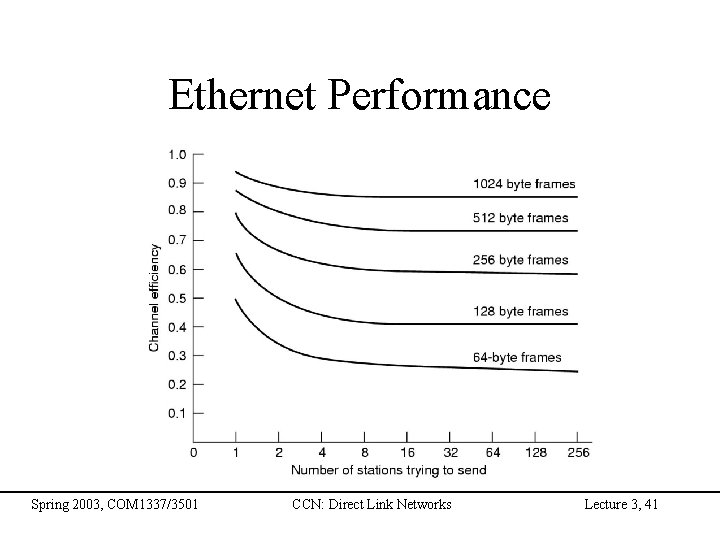
Ethernet Performance Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 41
Ethernet Capture Effect • A and B have a large queue of packets • There exists a situation where B will keep increasing its backoff interval (and finally dropping its packet) while A is transmitting its packets • One of the reasons why frame is dropped after 16 collisions Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 42
Token Passing MAC • Token Bus (IEEE 802. 4): – – – broadcast bus logical ring token: special control frame only the token holder station can transmit frames 0, 2, 4, 6: traffic priority classes • Token Ring (initiated by IBM => IEEE 802. 5 => FDDI): – token regenerated/modified at each node – stations have two modes: • listen (forwards bits with delay 1) • transmit (seizes the first token by transforming into the start of frame) Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 43
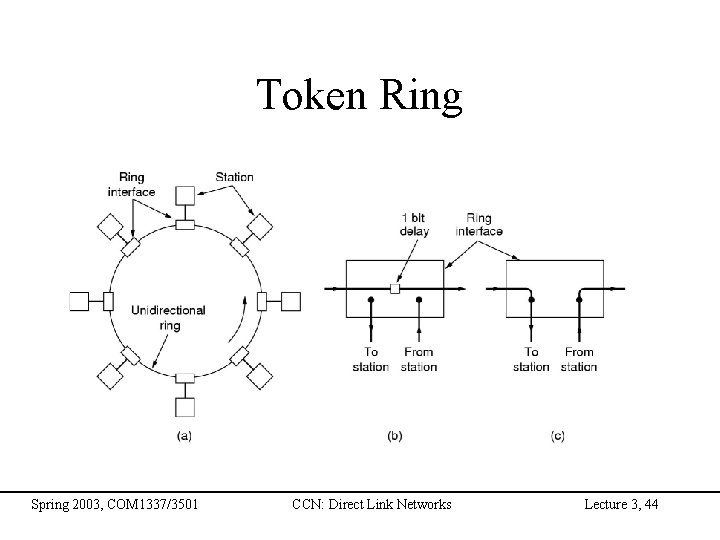
Token Ring Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 44
Token Ring (cont) • Idea – – Frames flow in one direction: upstream to downstream special bit pattern (token) rotates around ring must capture token before transmitting release token after done transmitting • immediate release • delayed release – remove your frame when it comes back around – stations get round-robin service • Frame Format 8 8 48 48 Start of frame Control Dest addr Src addr Spring 2003, COM 1337/3501 32 Body CCN: Direct Link Networks 8 CRC End of frame 24 Status Lecture 3, 45

Fiber Distributed Data Interface • Evolution of IEEE 802. 5 • Designed for fiber (100 Mbps) but also supports coax and twisted pair • Architecture: dual ring – Tolerates one broken link or one station failure • Stations buffer at least 9 bits and at most 80 bits • Uses 4 B/5 B encoding • Specific Timed-Token Algorithm Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 46
Token Times • Token Holding Time (THT) – upper limit on how long a station can hold the token • Token Rotation Time (TRT) – how long it takes the token to traverse the ring. – TRT <= Active. Nodes x THT + Ring. Latency • Target Token Rotation Time (TTRT) – agreed-upon upper bound on TRT Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 47

Token Maintenance • Lost Token – no token when initializing ring – bit error corrupts token pattern – node holding token crashes • Generating a Token (and agreeing on TTRT) – – execute when join ring or suspect a failure send a claim frame that includes the node’s TTRT bid when receive claim frame, update the bid and forward if your claim frame makes it all the way around the ring: • your bid was the lowest • everyone knows TTRT • you insert new token Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 48
Maintenance (cont) • Monitoring for a Valid Token – should periodically see valid transmission (frame or token) – maximum gap = ring latency + max frame < = 2. 5 ms – set timer at 2. 5 ms and send claim frame if it fires Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 49
Ad Hoc Wireless Networks • Physical transmission: spread-spectrum radio and diffused infrared • Key issue: collision avoidance, as for the Ethernet – More complex than the Ethernet because the nodes are not directly connected with one another – Multi-hop network • Potential problems: – Hidden terminal problem – Exposed terminal problem Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 50
802. 11: Multiple Access with Collision Avoidance (MACA 1990) • MACA is designed for ad-hoc wireless networks • When a station S 1 has a packet to transmit to station S 2 – S 1 senses the channel. If the channel is busy defers the transmission until idle – if channel is idle S 1 sends a special packet called Request-To-Send (RTS) to S 2 – (if the RTS is correctly received by S 2) S 2 sends a Clear-To-Send (CTS), CTS includes the frame length – (if the CTS is correctly received by S 1) S 1 starts the data transmission • Stations which sense: – RTS: defer transmission until after CTS – CTS: defer transmission until the transmission of data completes • If a station does not receive CTS in response to its RTS, it invokes an exponential backoff Spring 2003, COM 1337/3501 CCN: Direct Link Networks Lecture 3, 51
- Slides: 51