Direct Link Networks 2 1 Hardware Building Blocks
Direct Link Networks 2. 1 Hardware Building Blocks 2. 2 Encoding 2. 3 Framing 2. 4 Error Detection 2. 5 Reliable Transmission 2. 6 Ethernet (802. 3) 2. 7 Rings (802. 5, FDDI, RPR) 2. 8 Wireless 1
o Simplest network n two hosts are directly connected by some physical medium o Medium n a length of wire, a piece of optical fiber, or air through which electromagnetic radiation (e. g. , radio waves) can be transmitted 2
o Five issues before the nodes can successfully exchange packets n encoding o encode bits onto transmission medium so that they can be understood by a receiving host n framing o delineate the sequence of bits transmitted over the link into complete messages (frames) that can be delivered to the end node n error detection o detect transmitted frames errors and take appropriate action 3
n reliable delivery o make a link appear reliable in spite of the fact that it corrupts frames from time to time n media access control o mediate multiple hosts access to a link (opposed to point-to-point link) 4
2. 1 Hardware Building Blocks o Networks are constructed from two classes of hardware building blocks n nodes n links 5
Node o Nodes n general-purpose computers o like a desktop workstation, a multiprocessor, or a PC n special-purpose hardware o considering performance and cost a network node o most commonly a switch or router inside the network, rather than a host, is implemented by special-purpose hardware 6
o Assume a node is a workstation-class machine n serve as a host that users run application programs on n serve as a switch that forwards messages from one link to another (within a network) n serve as a router that forwards internet packets from one network to another 7
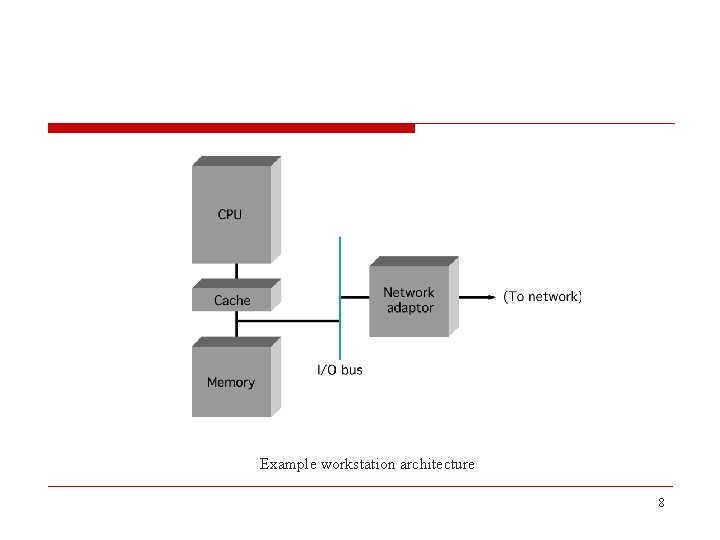
Example workstation architecture 8
o A workstation-class machine n memory o the memory on any given machine is finite, it maybe 64 MB, 1 GB or more, but it is not infinite n memory is one of the two scarce resources (the other is link bandwidth) because, on any node that forwards packets, those packets must be buffered in memory while waiting their turn to be transmitted over an outgoing link n Must be carefully managed 9
o Second, while CPUs are becoming faster at an unbelievable pace, the same is not true of memory n recent performance trends show processor speeds doubling every 18 months, but memory latency improving at a rate of only 7% each year n the network software needs to be careful about how it uses memory and, in particular, about how many times it accesses memory as it processes each message 10
n network adaptor o the component connects the rest of the workstation to the link o more than just a physical connection, it is an active intermediary between node and link, with its own internal processor o role n transmit data from the workstation onto the link n receive data from the link, storing it for the workstation 11
o the adaptor implements nearly all the networking functionality, e. g. n break data into frames that the link can transport n detect errors introduced as a frame travels over the link n follow fairness rules that allow a link to be shared by multiple workstations 12
o two main components n a bus interface that understands how to communicate with the host n a link interface that understands how to use the link n there is a communication path between these two components, over which incoming and outgoing data is passed 13
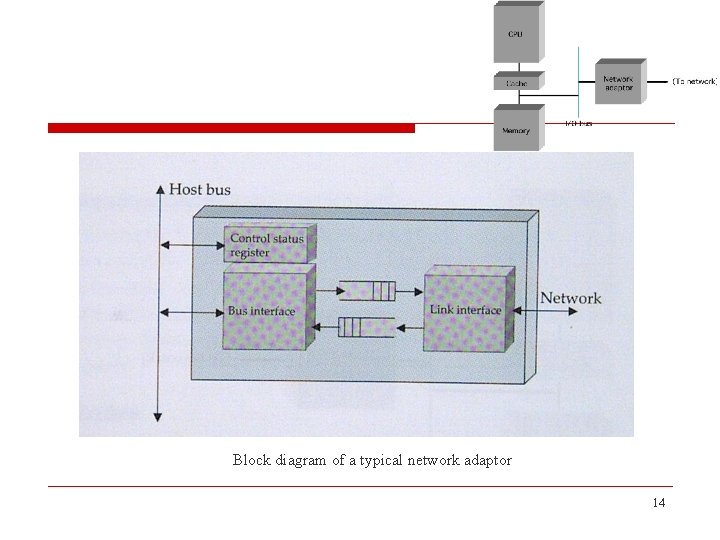
Block diagram of a typical network adaptor 14
o the adaptor exports a control status register (CSR) that is readable and writeable from the CPU n CSR is typically located at some address in the memory, thereby making it possible for the CPU to read and write just like any other memory location n software on the host - device driver - writes to the CSR to instruct it to transmit and/or receive data and reads from the CSR to learn the current state of the adaptor o to notify the host of an asynchronous event such as the reception of a frame, the adaptor interrupts the host 15
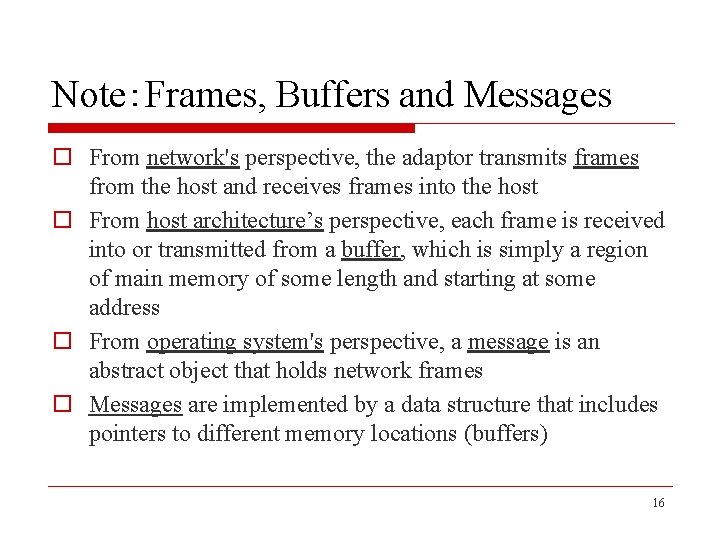
Note:Frames, Buffers and Messages o From network's perspective, the adaptor transmits frames from the host and receives frames into the host o From host architecture’s perspective, each frame is received into or transmitted from a buffer, which is simply a region of main memory of some length and starting at some address o From operating system's perspective, a message is an abstract object that holds network frames o Messages are implemented by a data structure that includes pointers to different memory locations (buffers) 16
n One of the most important issues in network adaptor design is o how bytes of data are transferred between the adaptor and the host memory n direct memory access (DMA) § the adaptor directly reads and writes the hosts memory without any CPU involvement § the host simply gives the adaptor a memory address and the adaptor reads from (or writes to) it 17
n programmed I/O (PIO) § the CPU is directly responsible for moving data between the adaptor and the host memory § to send a frame, the CPU executes a tight loop that first reads a word from host memory and then writes it to the adaptor § to receive a frame, the CPU reads words from the adaptor and writes them to memory 18
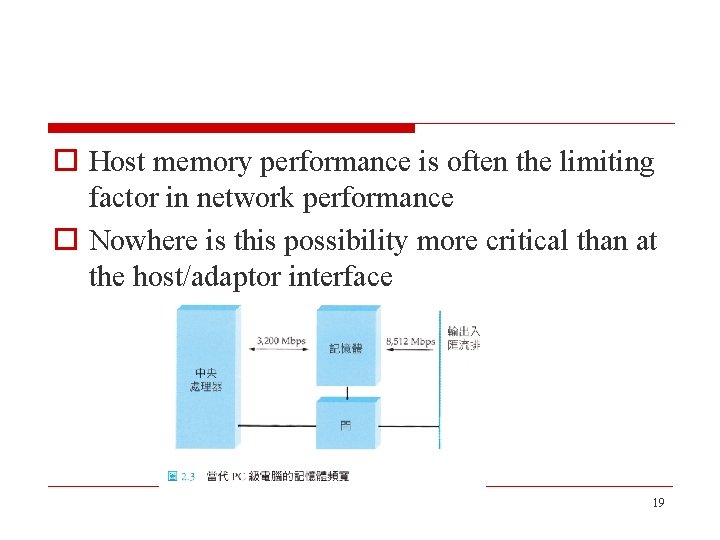
o Host memory performance is often the limiting factor in network performance o Nowhere is this possibility more critical than at the host/adaptor interface 19
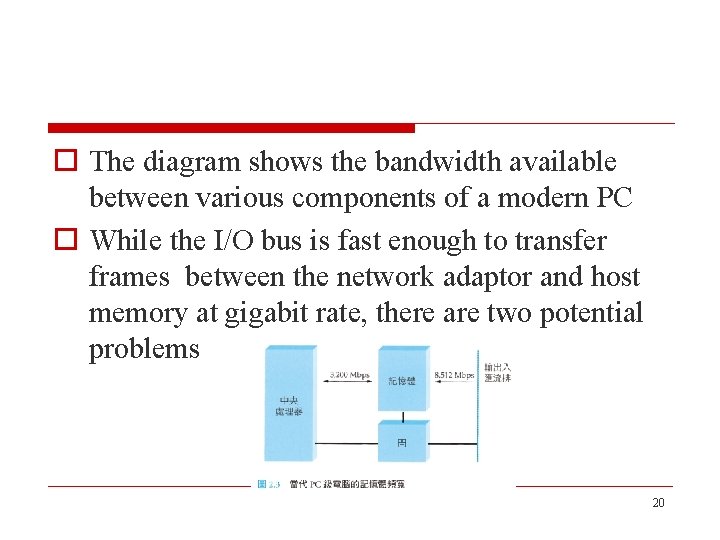
o The diagram shows the bandwidth available between various components of a modern PC o While the I/O bus is fast enough to transfer frames between the network adaptor and host memory at gigabit rate, there are two potential problems 20
n The advertised I/O bus speed corresponds to its peak bandwidth; o It is the product of the bus’s width and clock speed o e. g. a 64 -bit-wide bus running at 133 MHz has a peak transfer rate of 8512 Mbps o The real limitation is the size of the data block that is being transferred across the I/O bus since there is a certain amount of overhead involved in each bus transfer 21
o e. g, on some architectures, it takes 8 clock cycles to acquire the bus for the purpose of transferring data from the adaptor to host memory o The overhead is independent of the number of data bytes transferred o e. g. , if you want to transfer a 64 -byte payload across the I/O bus (this happens to be the size of a minimum Ethernet packet), then the whole transfer takes 16 cycles n 8 cycles to acquire the bus and 8 cycles to transfer the data (the bus is 64 bits wide, it can transfer 8 bytes during each clock cycle; 64 bytes requires 8 cycles). 22
o The above example shows that the maximum sustained bandwidth you can achieve for such packets is only half the peak (i. e. , 4256 Mbps) o The second problem is the memory/CPU bandwidth n In the above example, it is 3200 MBps (25. 6 Gbps) n This a measured number rather than an advertised peak rate 23
n Because it needs to copy the data from one buffer to another, possibly multiple memory access is required n In particular, if the memory/CPU path is crossed n times, then it might be the case that the bandwidth your application sees is 3200/n MBps n The performance might be better if the data is cached, but often caches don’t help with data arriving from the network 24
o The main point of this discussion is that we must be aware of the limits memory bandwidth places on network performance o If carefully designed, the system can work around these limits n For example, to integrate the buffers used by the device driver, the OS, and the application in a way that minimizes data copies 25
n the effective throughput of the memory system is defined by the same two formulas o Throughput = Transfer. Size/Transfer. Time o Transfer. Time = RTT + 1/Bandwidth × Transfer. Size n in the case of the memory system, the transfer size corresponds to a unit of data we can move across the bus in one transfer n RTT corresponds to the memory latency, that is, whether the memory is on-chip cache, off-chip cache, or main memory o the larger the transfer size and the smaller the latency (RTT), the better the effective throughput 26
Link o Network links are implemented on a variety of different physical media n n twisted pair (home phone) coaxial cable (TV) optical fiber (high-bandwidth, long-distance links) space (the stuff that radio waves, microwaves, infrared beams propagate through) o The physical media is used to propagate signals 27
o The signals are electromagnetic waves traveling at the speed of light n the speed of light is, medium dependent electromagnetic waves traveling through copper and fiber do so at about two-thirds the speed of light in a vacuum o One property of an electromagnetic wave is frequency, measured in hertz, with which the wave oscillates o The distance between a pair of adjacent maxima or minima of a wave, typically measured in meters, is called the waves wavelength 28
o Electromagnetic waves travel at the speed of light, that speed divided by the wave's frequency is equal to its wavelength n example:a 300 -Hz wave traveling through copper would have a wavelength of Speed. Of. Light. In. Copper ÷ Frequency = (2/3 × 108) ÷ 300 = 667 × 103 meters 29
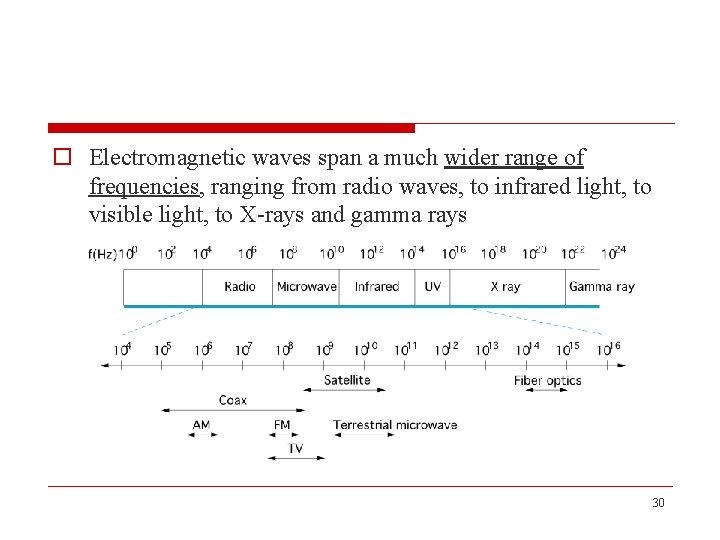
o Electromagnetic waves span a much wider range of frequencies, ranging from radio waves, to infrared light, to visible light, to X-rays and gamma rays 30
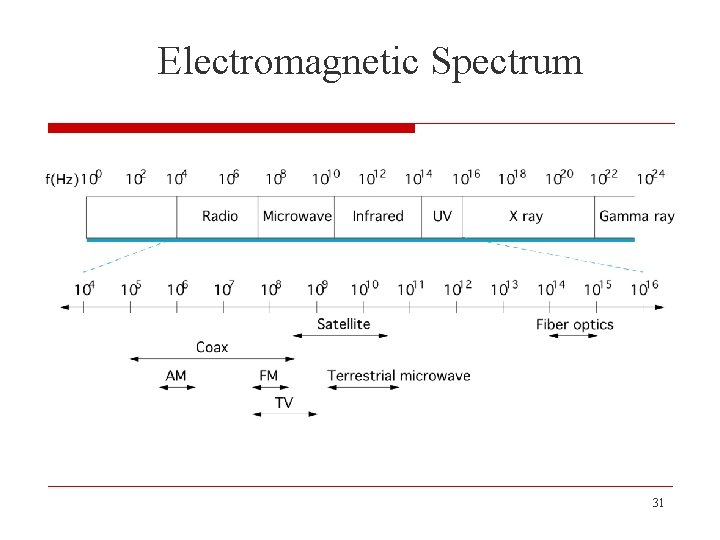
Electromagnetic Spectrum 31
o Links n a physical medium carrying signals in the form of electromagnetic waves at the speed of light n transmits all sorts of information, including binary data (1 s and 0 s), we say that the binary data is encoded in the signal 32
o The problem of encoding binary data onto electromagnetic signals can be divided into two layers n lower layer o concerned with modulation - varying the frequency, amplitude, or phase of the signal to effect the transmission of information o example: vary the power (amplitude) of a single wavelength n upper layer o encoding binary data onto “high” signals and “low” signals 33
o Because the issue of modulation is secondary to our discussion of links as building block for computer networks, we consider only the upper layer o Which is concerned with the much simpler problem of encoding binary data onto these two signals (Section 2. 2) 34
o How many bitstreams can be encoded on a link at a given time is another attribute of a link n for share access to the link, the answer is only one (multiple-access links) n for point-to-point links o it is often that two bitstreams can be simultaneously transmitted over the link at the same time, one going in each direction (full-duplex) o if data flowing in only one direction at a time - such a link is called half-duplex - requires that the two nodes connected to the link alternate using it 35
o Different link types to build a computer network n cables o if the nodes you want to connect are in the same room, in the same building, or even on the same site (e. g. , a campus), then you can buy a piece of cable and physically string between the nodes n leased lines o if the two nodes you want to connect are on opposite sides of the country, or even across, you are recommended to lease a dedicated link from the telephone company n last-mile links o if you can't afford a dedicated leased line then go for "last-mile" links, a less expensive option, they often span the last mile from the home to a network service provider 36
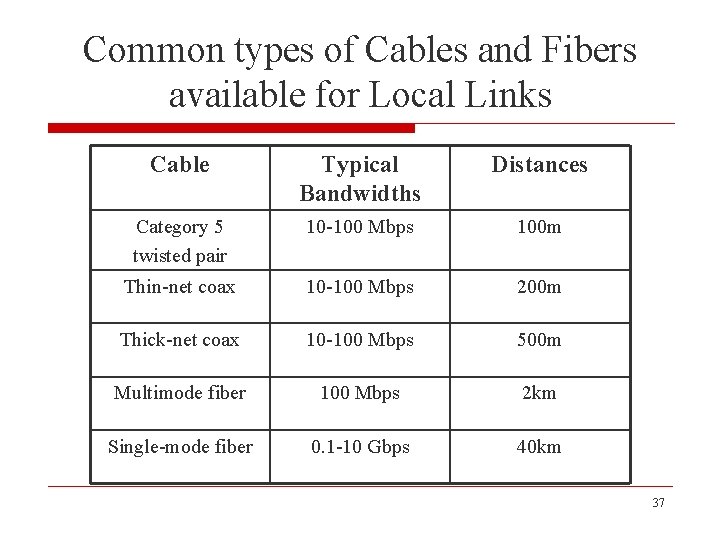
Common types of Cables and Fibers available for Local Links Cable Typical Bandwidths Distances Category 5 twisted pair 10 -100 Mbps 100 m Thin-net coax 10 -100 Mbps 200 m Thick-net coax 10 -100 Mbps 500 m Multimode fiber 100 Mbps 2 km Single-mode fiber 0. 1 -10 Gbps 40 km 37
o Category 5 (Cat-5) twisted pair --- it uses a thicker gauge than the twisted pair you find in your home -- is quickly becoming the within-building norm o Because of the difficulty and cost in pulling new cable through a building, every effort is made to make new technologies use existing cable n Gigabit Ethernet , for example, has been designed to run over Cat-5 wiring n Fiber is typically used to connect buildings at a site 38
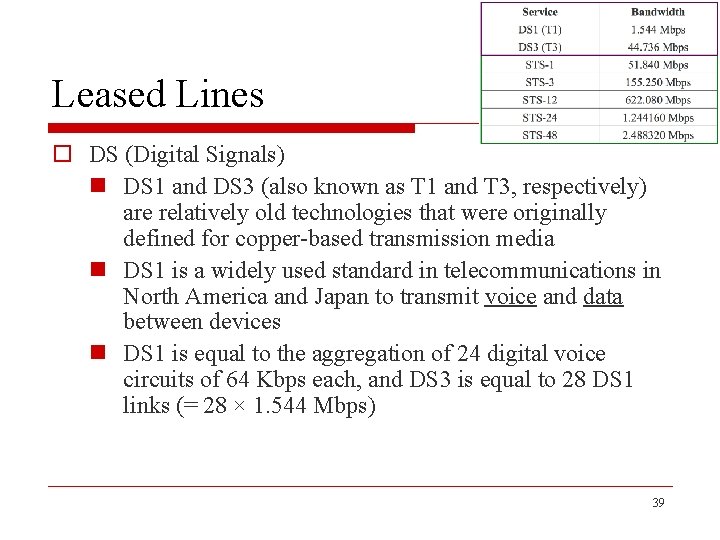
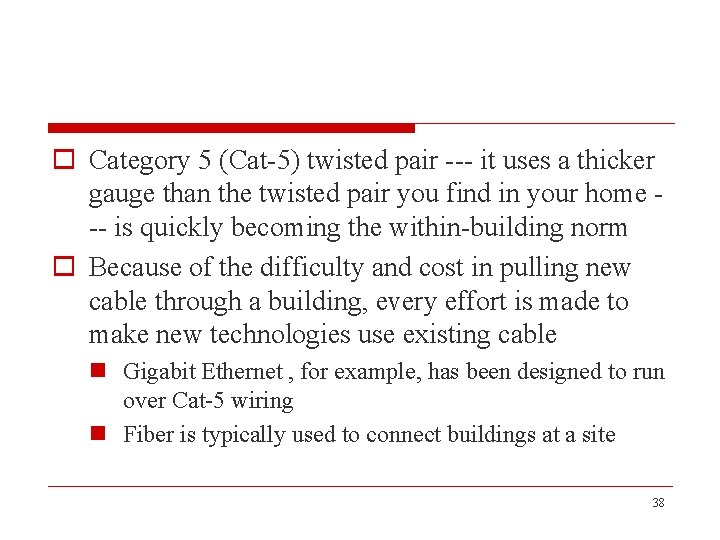
Leased Lines o DS (Digital Signals) n DS 1 and DS 3 (also known as T 1 and T 3, respectively) are relatively old technologies that were originally defined for copper-based transmission media n DS 1 is a widely used standard in telecommunications in North America and Japan to transmit voice and data between devices n DS 1 is equal to the aggregation of 24 digital voice circuits of 64 Kbps each, and DS 3 is equal to 28 DS 1 links (= 28 × 1. 544 Mbps) 39
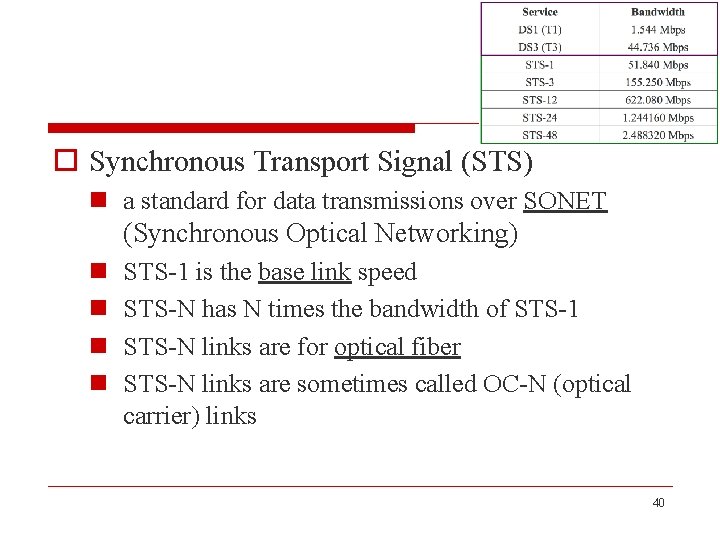
o Synchronous Transport Signal (STS) n a standard for data transmissions over SONET (Synchronous Optical Networking) n n STS-1 is the base link speed STS-N has N times the bandwidth of STS-1 STS-N links are for optical fiber STS-N links are sometimes called OC-N (optical carrier) links 40
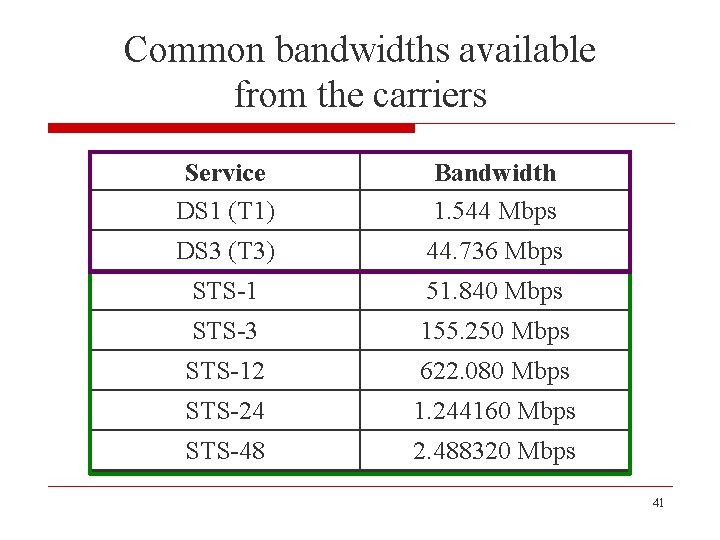
Common bandwidths available from the carriers Service DS 1 (T 1) Bandwidth 1. 544 Mbps DS 3 (T 3) 44. 736 Mbps STS-1 51. 840 Mbps STS-3 155. 250 Mbps STS-12 622. 080 Mbps STS-24 1. 244160 Mbps STS-48 2. 488320 Mbps 41
o Difference between STS and OC n STS refers to the electrical transmission on the devices connected to the link n OC refers to the actual optical signal that is propagated over the fiber o Synchronous optical networking n a method for communicating digital information using lasers or light-emitting diodes (LEDs) over optical fiber 42
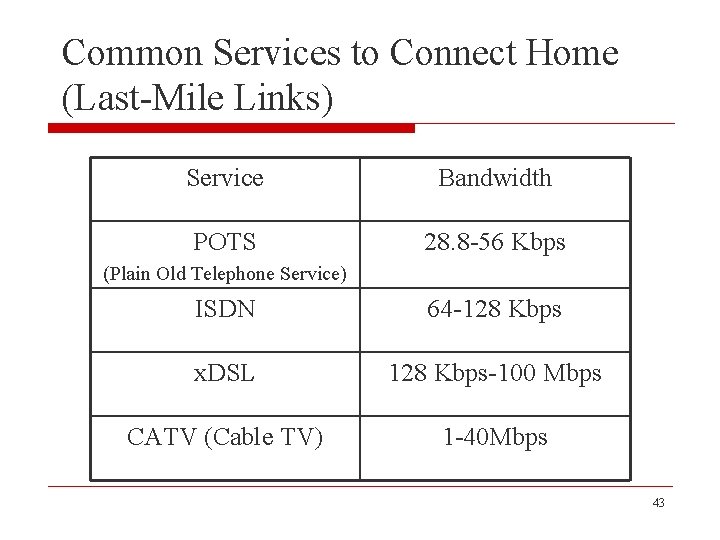
Common Services to Connect Home (Last-Mile Links) Service Bandwidth POTS 28. 8 -56 Kbps (Plain Old Telephone Service) ISDN 64 -128 Kbps x. DSL 128 Kbps-100 Mbps CATV (Cable TV) 1 -40 Mbps 43

Plain Old Telephone Service (POTS) o The first option is a conventional modern over POTS o POTS is a term which describes the voice-grade telephone service o The technology is already at its bandwidth limit 44
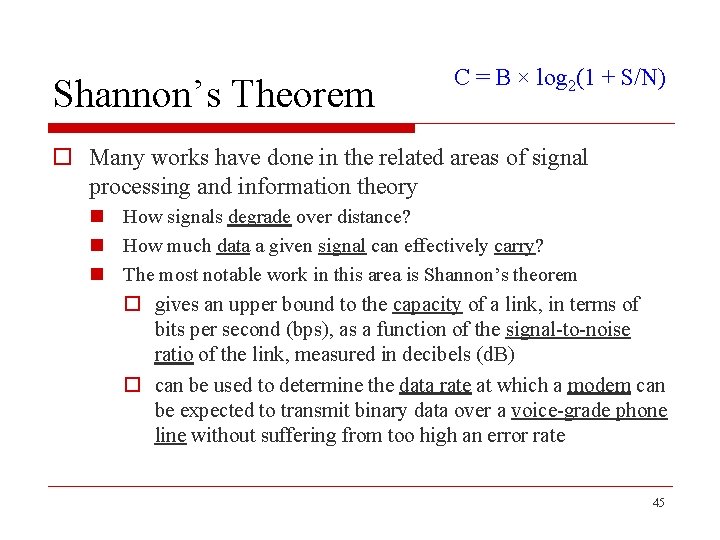
Shannon’s Theorem C = B × log 2(1 + S/N) o Many works have done in the related areas of signal processing and information theory n How signals degrade over distance? n How much data a given signal can effectively carry? n The most notable work in this area is Shannon’s theorem o gives an upper bound to the capacity of a link, in terms of bits per second (bps), as a function of the signal-to-noise ratio of the link, measured in decibels (d. B) o can be used to determine the data rate at which a modem can be expected to transmit binary data over a voice-grade phone line without suffering from too high an error rate 45
o Example n assume that a voice-grade phone connection supports a frequency range of 300 to 3, 300 Hz n Shannon’s theorem is typically given by the following formula: C = B × log 2(1 + S/N) n where o C is the achievable channel capacity measured in hertz o B is the bandwidth of the line (3, 300 Hz - 300 Hz = 3, 000 Hz) o S is the average signal power o N is the average noise power 46
C = B × log 2(1 + S/N) n the signal-to-noise ratio (S/N) is usually expressed in decibels, related as follows: d. B = 10 × log 10(S/N) n assuming a typical decibel ratio of 30 d. B, this means that S/N = 1, 000 n thus, we have C = 3, 000 × log 2(l 001) n which equals approximately 30 Kbps, roughly the limit of a 28. 8 Kbps modem 47
o Given this fundamental limit, why is it possible for a 56 Kbps modems? o reason-1 n such rates depend on improved line quality, i. e. , a higher signal-to-noise ratio than 30 d. B o reason-2 n the phone system is changed to have largely eliminated analog lines that are bandwidth limited to 3, 300 Hz 48
Integrated Services Digital Network (ISDN) o An ISDN connection includes two 64 Kbps channels n one can be used to transmit data n another can be used for digitized voice o a device that encodes analog voice into a digital ISDN link is called a CODEC (coder / decoder) o When the voice channel is not in use, it can be combined with the data channel to support up to 128 Kbps of data bandwidth 49
Digital Subscriber Loop or Digital Subscriber Line (DSL or x. DSL) o A family of technologies that provide digital data transmission over the wires of a local telephone network n High Data Rate Digital Subscriber Line (HDSL) n Symmetric Digital Subscriber Line (SDSL) n Asymmetric Digital Subscriber Line (ADSL) n ISDN Digital Subscriber Line (IDSL) n Rate-Adaptive Digital Subscriber Line (RADSL) n Very High Speed Digital Subscriber Line (VDSL) n Very High Speed Digital Subscriber Line 2 (VDSL 2) n Symmetric High-speed Digital Subscriber Line (G. SHDSL) n Powerline Digital Subscriber Line (PDSL) n Uni-DSL (UDSL) 50
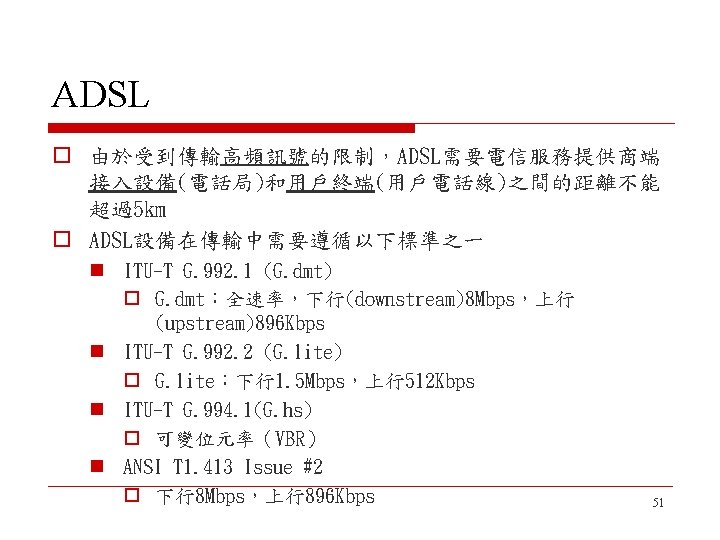
o 更快更新的標準 n ITU G. 992. 3/4 o ADSL 2 下行12 Mbps,上行1. 0 Mbps n ITU G. 992. 3/4 o Annex J ADSL 2 下行12 Mbps,上行3. 5 Mbps n ITU G. 992. 5 o ADSL 2+ 下行24 Mbps,上行1. 0 Mbps n ITU G. 992. 5 o Annex M ADSL 2+ 下行24 Mbps,上行3. 5 Mbps o 當電信服務提供商的設備端和用戶終端之間距離小於 1. 3 km 時,還可使用速率更高的VDSL(下行55. 2 Mbps,上行 19. 2 Mbps) 52
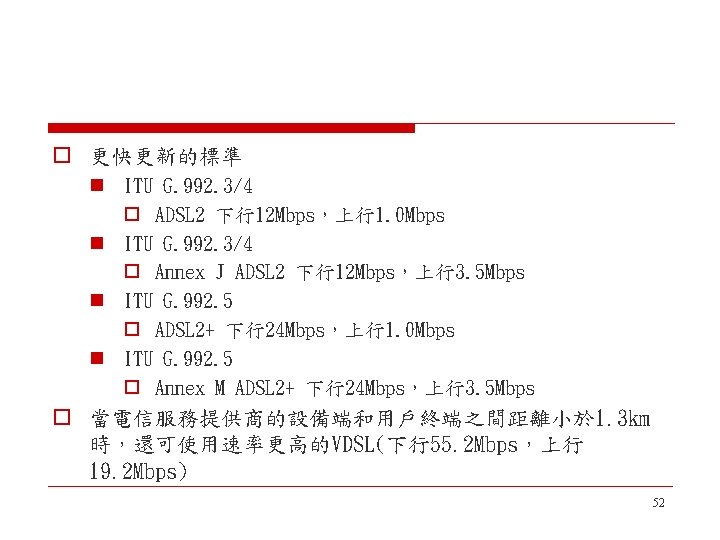
Central office Local loop Subscriber premises ADSL Wiring Standard twisted pair Connecting residence ADSL modem Digital connection To local network To analog phone CO’s ADSL modem To telephone switch Digital connection To provider Telephone central office 53
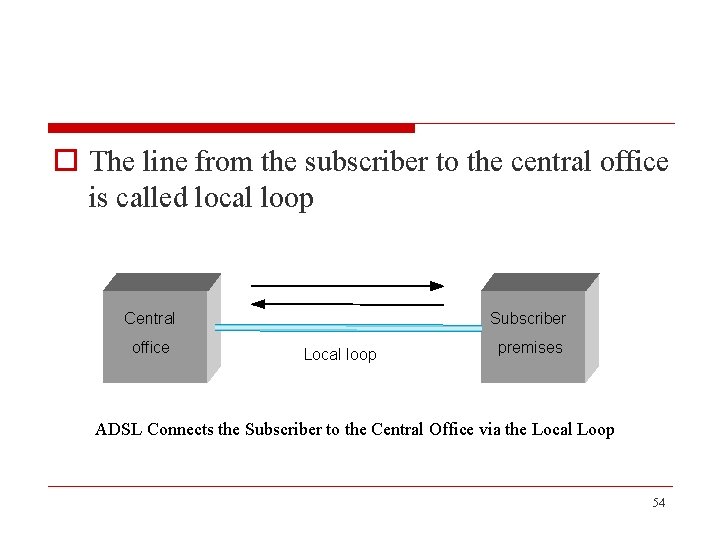
o The line from the subscriber to the central office is called local loop Central office Subscriber Local loop premises ADSL Connects the Subscriber to the Central Office via the Local Loop 54
VDSL o Very high data rate digital subscriber line o Symmetric n Ranging from 12. 96 to 55. 2 Mbps o Runs over much shorter distances (1, 000 to 4, 500 feet) n Which means it will not typically reach from the home to the central office 55
VDSL o The telephone company would have to put VDSL transmission hardware in neighborhoods n Fiber to the neighborhood o put VDSL transmission hardware in neighborhoods, with some other technology (e. g. , STS-N running over fiber) connecting the neighborhood to the central office 56
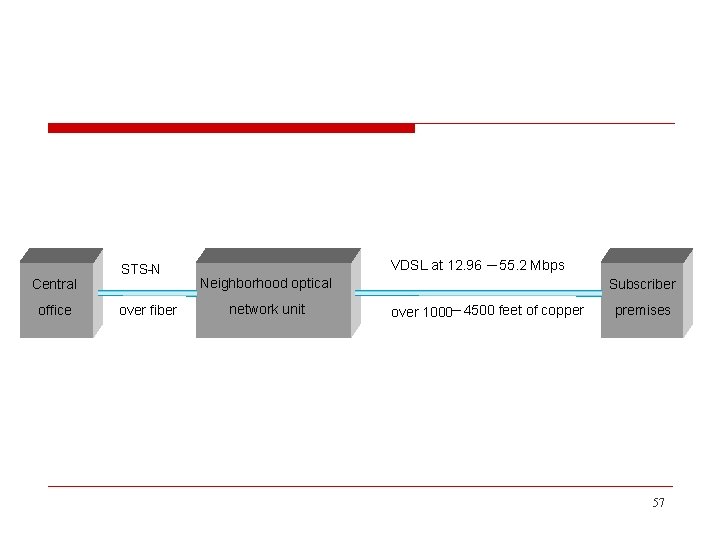
Central office STS-N over fiber VDSL at 12. 96 ─ 55. 2 Mbps Neighborhood optical network unit Subscriber over 1000─ 4500 feet of copper premises 57

Cable TV (CATV) o Cable moderns are an alternative to the various types of DSL o This technology uses the CATV infrastructure o Some subset of the available CATV channels are made available for transmitting digital data 58
o o Like ADSL, CATV is used in an asymmetric way Downstream: 40 Mbps / channel Upstream: 20 Mbps / channel Unlike DSL, the bandwidth is shared among all subscribers in a neighborhood 59
Wireless Links o Wireless links transmit electromagnetic signals - radio, microwave, infrared, or even visible light - through space, even through vacuum o The availability to exchange signals without physical connectivity is what makes mobile communication devices possible o The further ability to broadcast that signal, and the fact that the hardware and power burden is primarily on the transmitting end, makes wireless communication wellsuited to television and radio broadcasting 60
Wireless Links o Because wireless links all share the same wire, the challenge is to share it efficiently, without unduly interfering with each other o Most of this sharing is accomplished by dividing the “wire” along the dimensions of frequency or space n Exclusive use of a particular frequency in a particular geographic area may be allocated to an individual entity such as a corporation 61
Wireless Links o It is feasible to limit the area covered by an electromagnetic signal because such signals weaken, or attenuate, with the distance from their origin o To reduce the area covered by your signal, reduce the power of your transmitter 62

o Frequencies allocations are determined by government agencies such as the Federal Communication Commission (FCC) in the United States o Specific bands (frequency ranges) are allocated to certain uses n some bands are reserved for government use n other bands are reserved for uses such as AM radio, FM radio, television, satellite communication, and cell phones n specific frequencies within these bands are then licensed to individual organizations for use within certain geographical areas 63
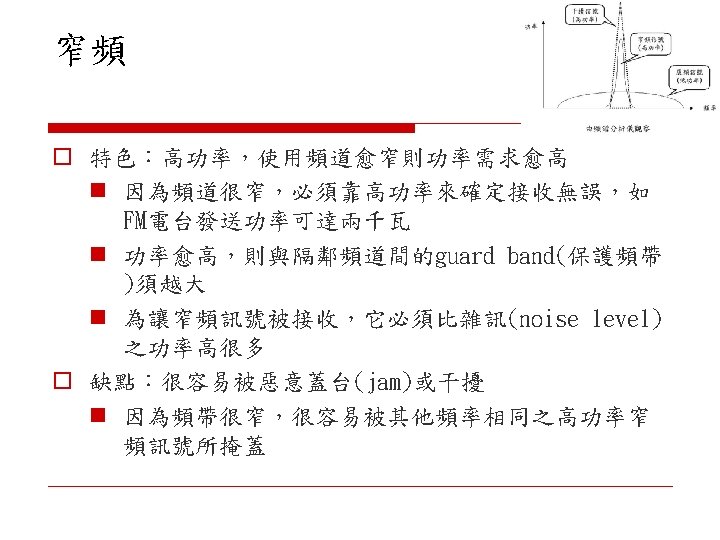
o Several frequency bands set aside for "license-exempt" usage - bands in which a license is not needed n devices that use license-exempt frequencies are still subject to certain restrictions o 1 st restriction: a limit on transmission power n this limits the range of a signal, making it less likely to interfere with another signal n example, a cordless phone might have a range of about 100 feet o 2 nd restriction: requires use of spread spectrum techniques 64
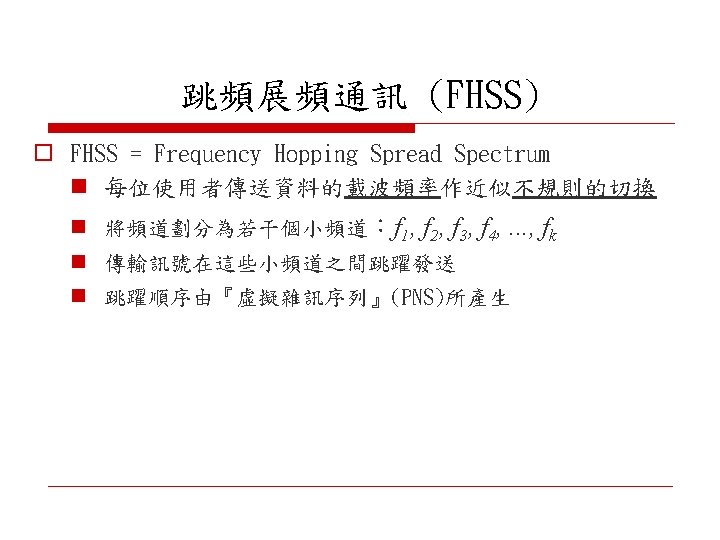
o Spread spectrum n spread the signal over a wider frequency band than normal in such a way as to minimize the impact of interference from other devices n originally designed for military use, so these “other devices” were often attempting to jam (蓋台) the signal o Spread spectrum techniques n frequency hopping spread spectrum (FHSS) n direct sequence spread spectrum (DSSS) 65
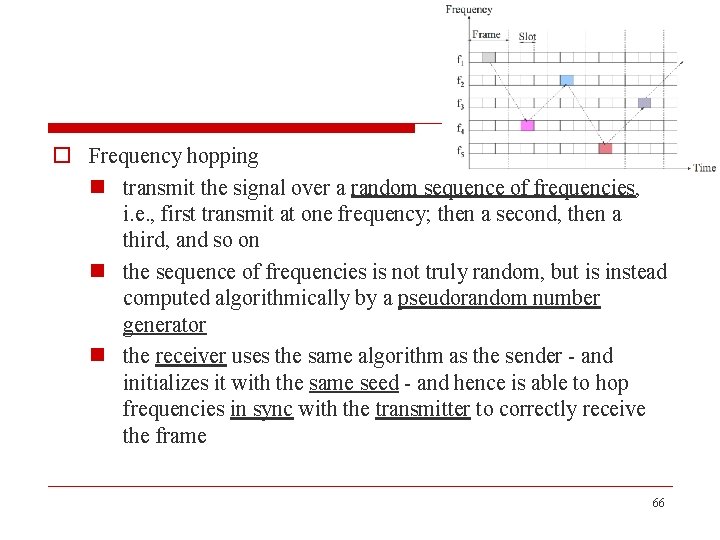
o Frequency hopping n transmit the signal over a random sequence of frequencies, i. e. , first transmit at one frequency; then a second, then a third, and so on n the sequence of frequencies is not truly random, but is instead computed algorithmically by a pseudorandom number generator n the receiver uses the same algorithm as the sender - and initializes it with the same seed - and hence is able to hop frequencies in sync with the transmitter to correctly receive the frame 66
o Direct sequence n add redundancy for greater tolerance of interference n each bit of data is represented by multiple bits in the transmitted signal n if some of the transmitted bits are damaged by interference, there is usually enough redundancy to recover the original bit n for each bit the sender wants to transmit, it actually sends the exclusive-OR of that bit and n random bits n as with frequency hopping, the sequence of random bits is generated by a pseudorandom number generator known to both the sender and the receiver 67
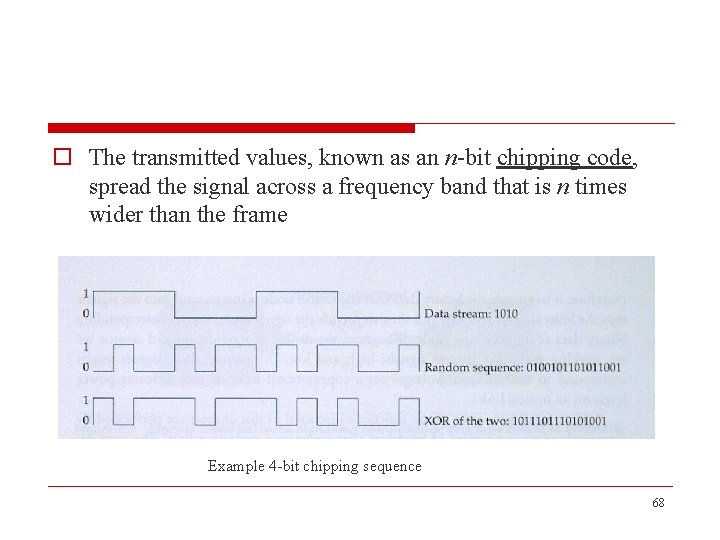
o The transmitted values, known as an n-bit chipping code, spread the signal across a frequency band that is n times wider than the frame Example 4 -bit chipping sequence 68
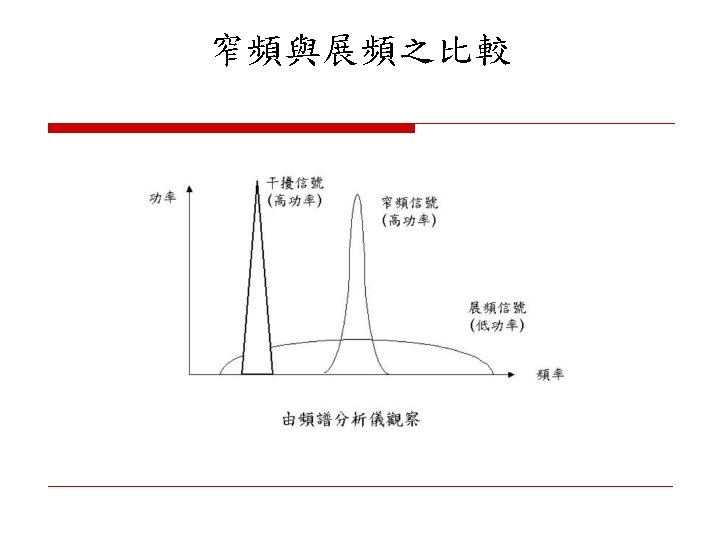
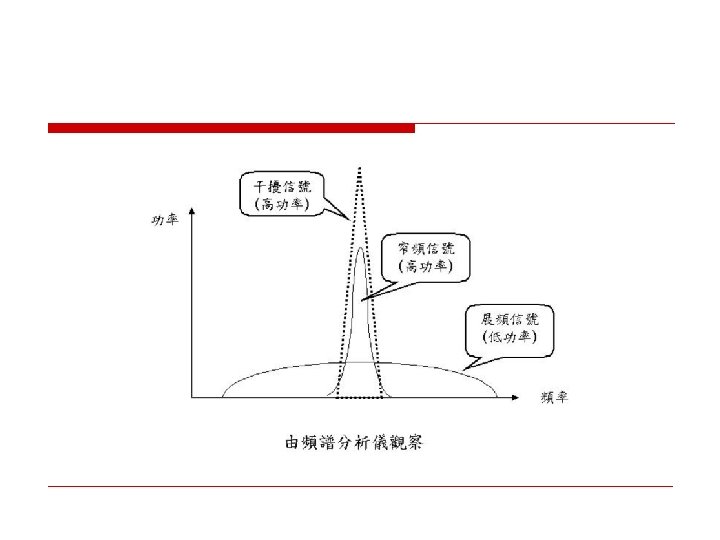
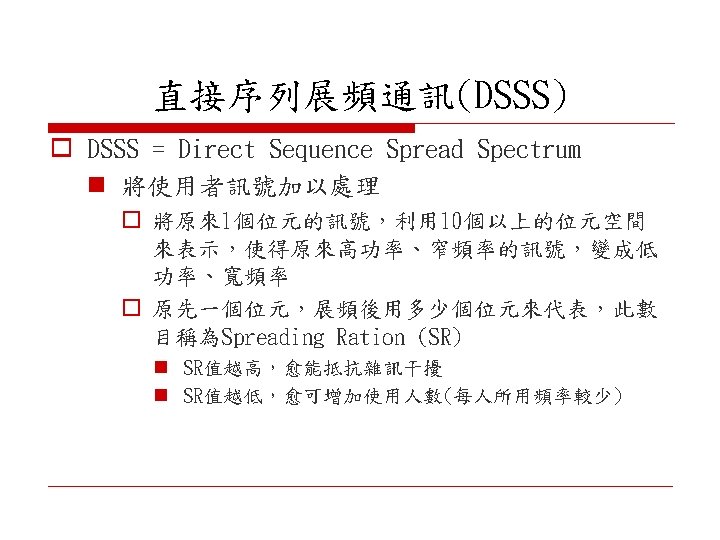
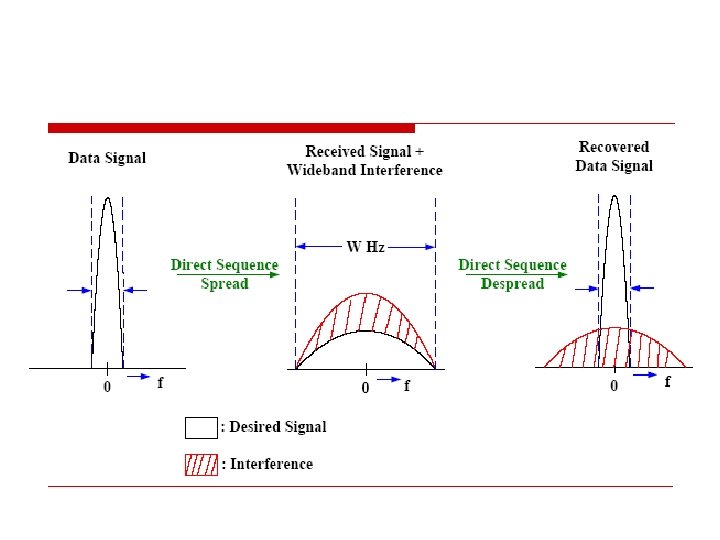
o DSSS operation flow n 原傳送的data signal o 經DSSS展頻後,即使受到干擾(interference),在 接收後可用pseudo code做de-spread將整個能量集 中,得到原來的data signal n 干擾部份 o 因為不是用pseudo code產生,在de-spread後,仍 會散布於整個頻道
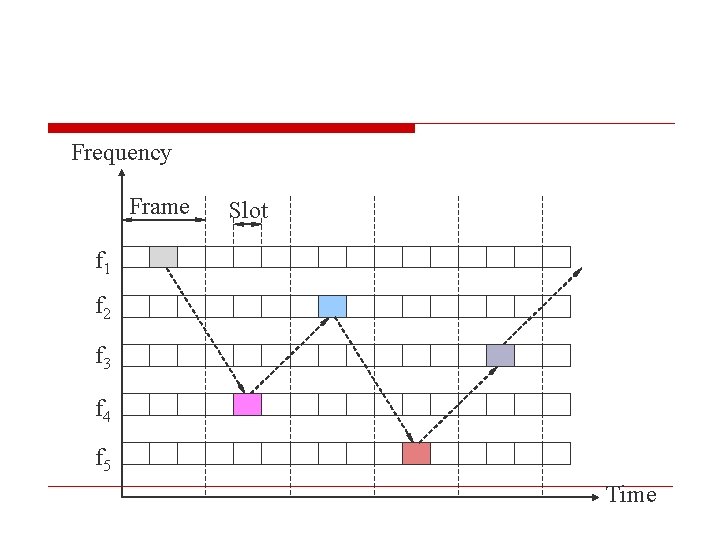
Frequency Frame Slot f 1 f 2 f 3 f 4 f 5 Time
License & License-Exempt Frequencies o It is these license-exempt frequencies, with their spread spectrum techniques and limited range, that are used by 802. 11 (Wi-Fi), 802. 15. 1 (Bluetooth), and some flavors of 802. 16 (Wi. MAX) o Different parts of the electromagnetic spectrum have different properties, making some better suited to communication and some less so n E. g. , some can penetrate buildings and some cannot 84
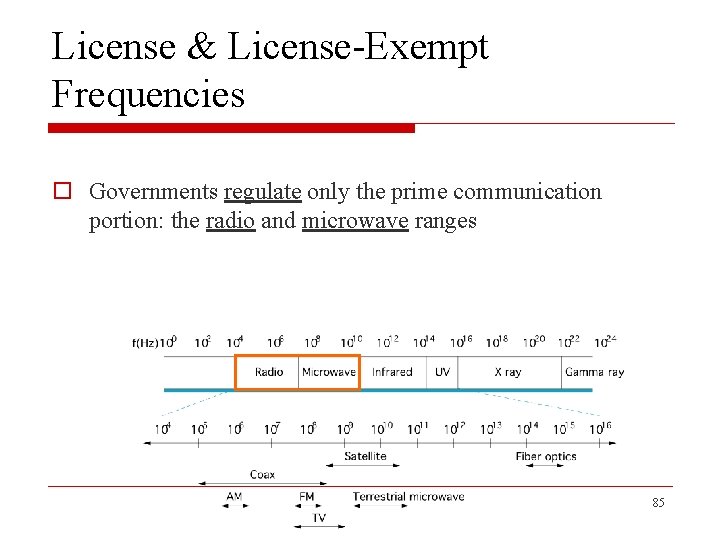
License & License-Exempt Frequencies o Governments regulate only the prime communication portion: the radio and microwave ranges 85
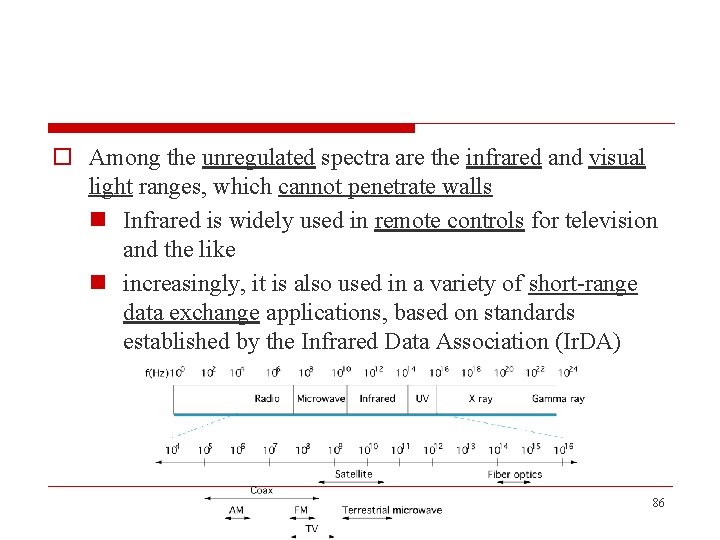
o Among the unregulated spectra are the infrared and visual light ranges, which cannot penetrate walls n Infrared is widely used in remote controls for television and the like n increasingly, it is also used in a variety of short-range data exchange applications, based on standards established by the Infrared Data Association (Ir. DA) 86
o For example, Ir. DA has defined a standard for "Point & Pay, ¨ using infrared to conduct n a financial transaction between a handheld device, such as a mobile phone or PDA n a stationary financial terminal such as a cash register 87
o Visual light or infrared can also be focused by a laser to provide a high-bandwidth link between two stationary points - even though no mobility is involved - in situations where a wired link is less practical for some reason n example, two buildings belonging to the same organization but separated by a busy highway could communicate with lasers 88
2. 2 Encoding o Link n a physical medium carrying signals (including 1 s and 0 s) in the form of electromagnetic waves n binary data is encoded in the signal o Network adaptor n contain a signaling component that encode bits into signals at the sending node and decode signals into bits at the receiving node 89
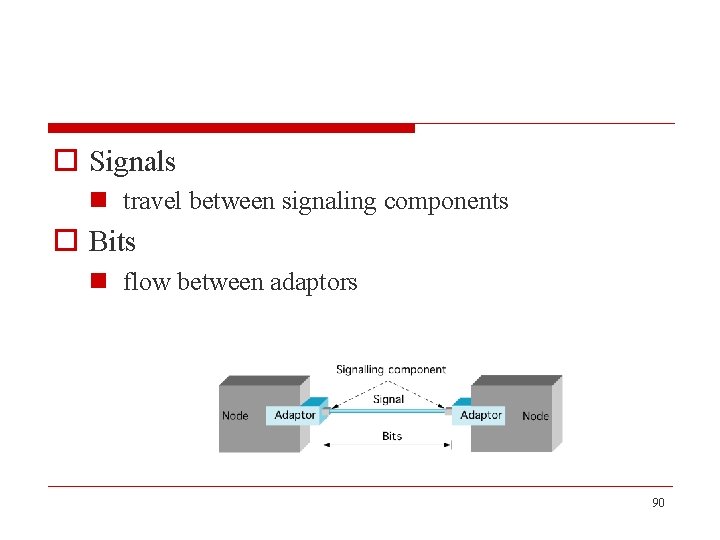
o Signals n travel between signaling components o Bits n flow between adaptors 90
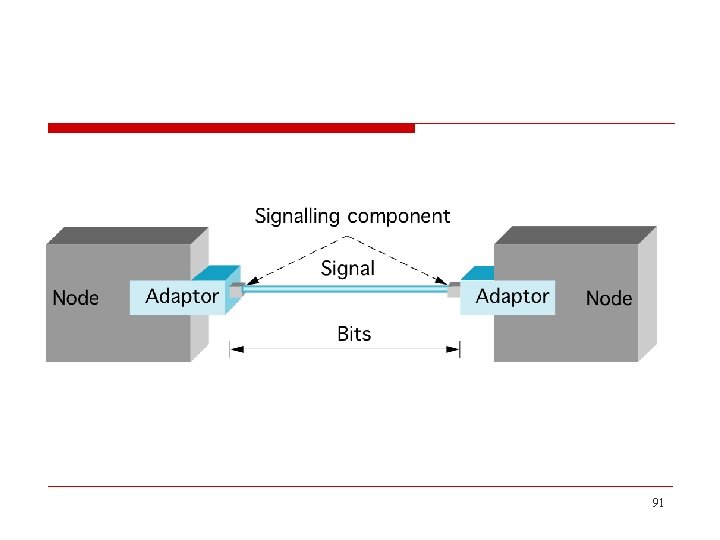
91
o Encoding n the process of transforming information from one format into another o Electronic encoding n transforms a signal into a form optimized for transmission or storage, generally done with a codec 92
o Encoder n a device used to change a signal (such as a bitstream) or data into a code n the code may serve any of a number of purposes such as compressing information for transmission or storage, encrypting or adding redundancies to the input code, or translating from one code to another n Our problem is to encode bits onto signals 93
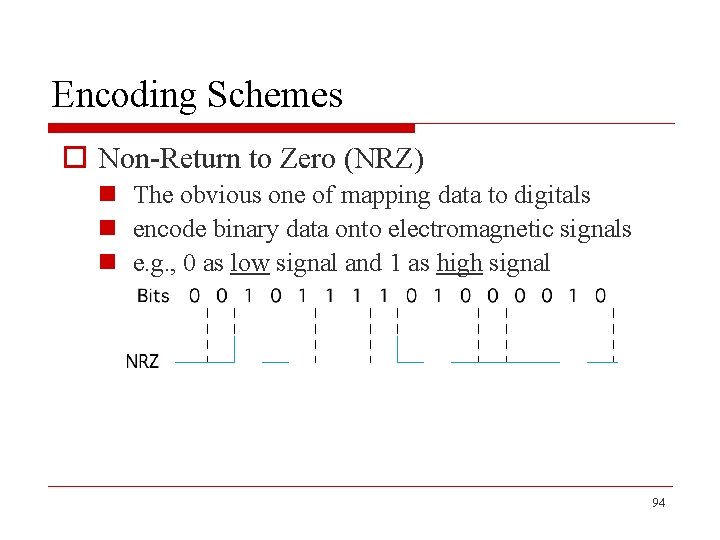
Encoding Schemes o Non-Return to Zero (NRZ) n The obvious one of mapping data to digitals n encode binary data onto electromagnetic signals n e. g. , 0 as low signal and 1 as high signal 94
o The problem with NRZ is that a sequence of several consecutive 1 s means that the signal stays high on the link for an extended period of time o Similarly, several consecutive 0 s means that the signal stays low for a long time 95
o There are two fundamental problems caused by long strings of 1 s or 0 s n Baseline wander: o the receiver keeps an average of the signal it has seen so far, and then uses this average to distinguish between low and high signals n The receiver concludes that it has just seen a 0 whenever the signal is significantly lower than this average, vice versa o Too many consecutive 1 s or 0 s cause this average to change, making it difficult to detect a significant change 96
n The second problem is that frequent transitions from high to low and vice versa are necessary to enable clock recovery n The clock recovery problem is that both the encoding and the decoding processes are driven by a clock—every clock cycle the sender transmits a bit and the receiver recovers a bit n The clocks have to be precisely synchronized n Whenever the signal changes, then the receiver knows it is at a clock cycle boundary, it can resynchronize itself 97
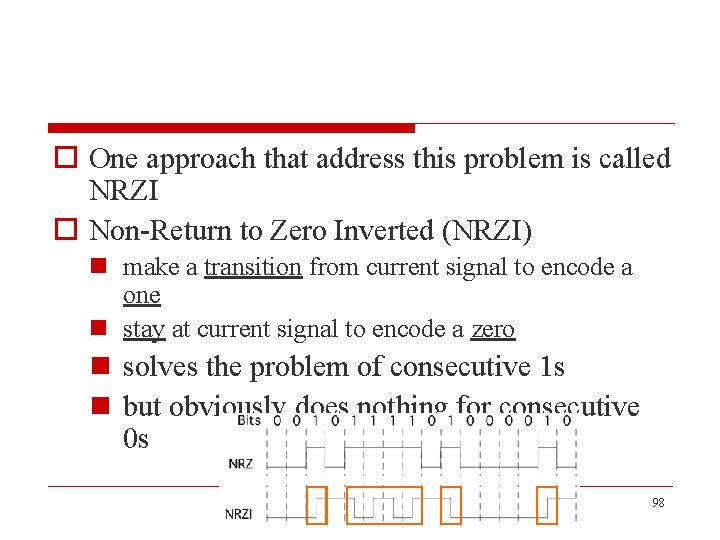
o One approach that address this problem is called NRZI o Non-Return to Zero Inverted (NRZI) n make a transition from current signal to encode a one n stay at current signal to encode a zero n solves the problem of consecutive 1 s n but obviously does nothing for consecutive 0 s 98
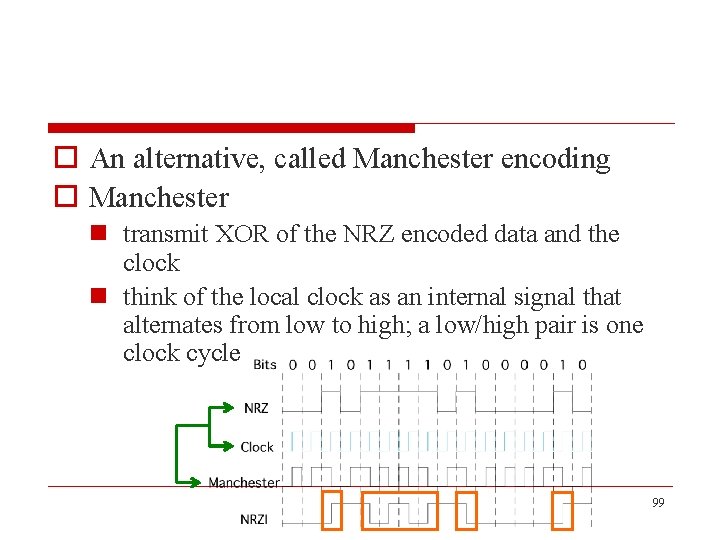
o An alternative, called Manchester encoding o Manchester n transmit XOR of the NRZ encoded data and the clock n think of the local clock as an internal signal that alternates from low to high; a low/high pair is one clock cycle 99
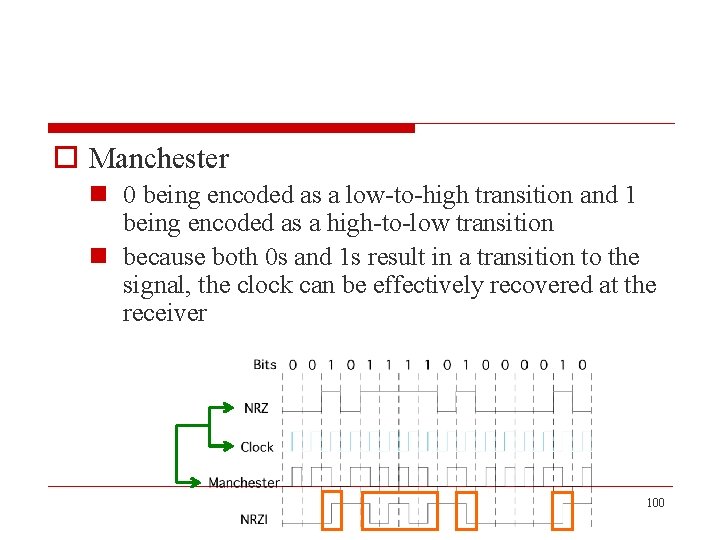
o Manchester n 0 being encoded as a low-to-high transition and 1 being encoded as a high-to-low transition n because both 0 s and 1 s result in a transition to the signal, the clock can be effectively recovered at the receiver 100
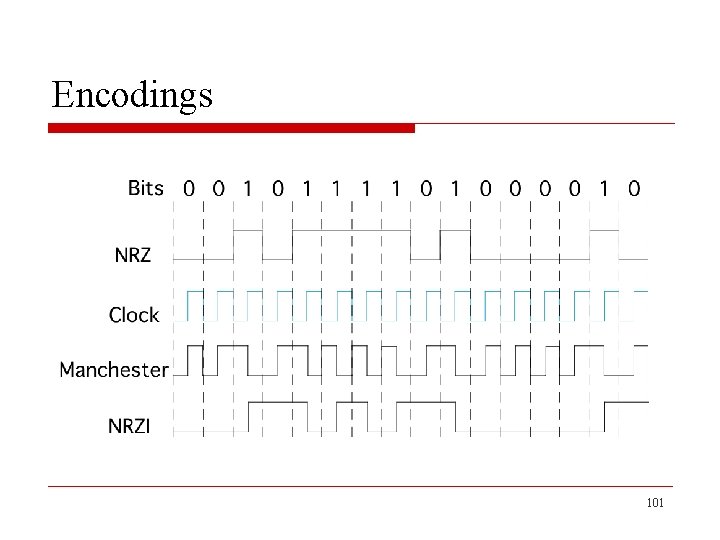
Encodings 101
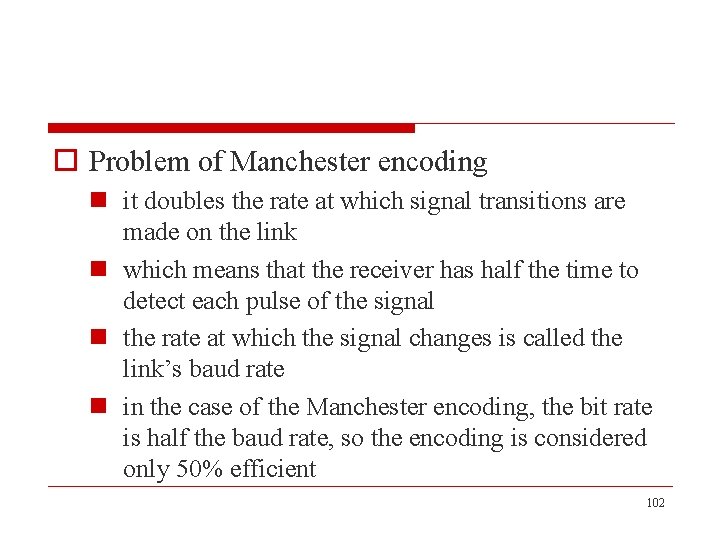
o Problem of Manchester encoding n it doubles the rate at which signal transitions are made on the link n which means that the receiver has half the time to detect each pulse of the signal n the rate at which the signal changes is called the link’s baud rate n in the case of the Manchester encoding, the bit rate is half the baud rate, so the encoding is considered only 50% efficient 102
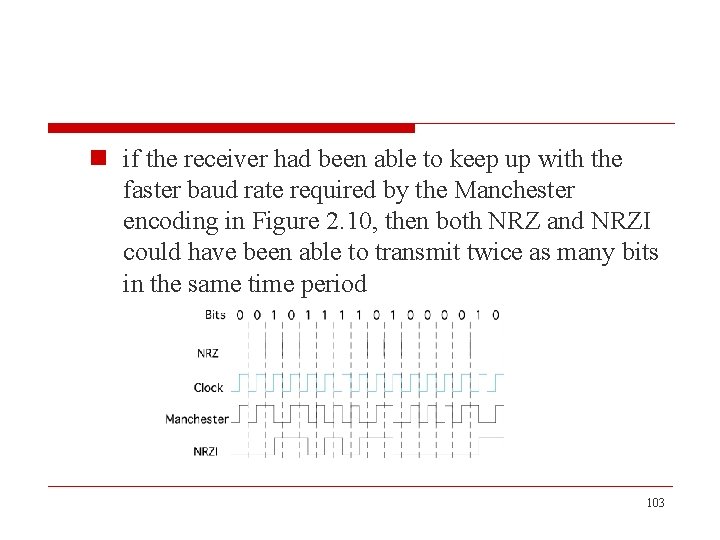
n if the receiver had been able to keep up with the faster baud rate required by the Manchester encoding in Figure 2. 10, then both NRZ and NRZI could have been able to transmit twice as many bits in the same time period 103
Bit Rates and Baud Rates o bit rate and baud rate are not the same thing o the Manchester encoding is an example of a case in which a link’s baud rate is greater than its bit rate o a bit rate greater than the baud rate is also possible n this imply that more than one bit is encoded on each pulse sent over the link 104
o ex. n suppose you could transmit four distinguished signals over a link rather than just two n on an analog link, for example, these four signals might corresponding to four different frequencies n given four different signals, it is possible to encode two bits of information on each signal o the first signal means 00, the second signal means 01, . . o a sender transmit 1000 pulse per second would be able to send 2. 000 bits 105
o a final encoding we consider is called 4 B/5 B o attempts to address the inefficiency of the Manchester encoding without suffering from the problem of having extended durations of high or low signals o 4 B/5 B n idea o insert extra bits into the bitstream so as to break up long sequences of 0 s or 1 s n every 4 bits of data encoded in a 5 -bit code that is then transmitted to the receiver, hence the name 4 B/5 B 106
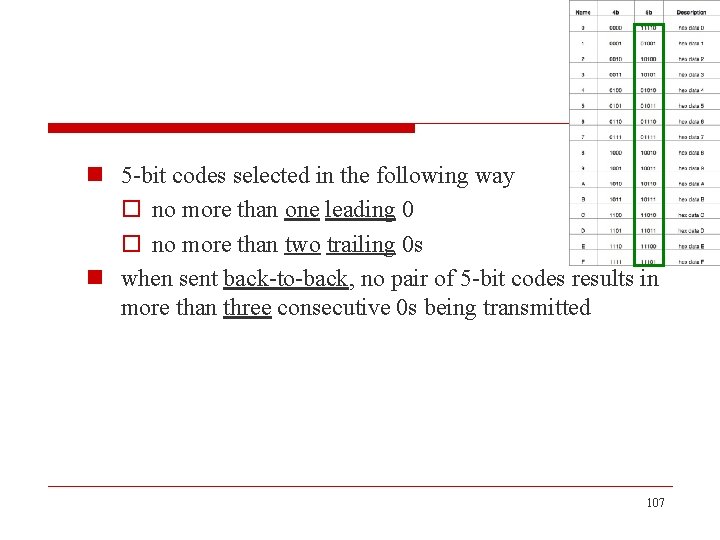
n 5 -bit codes selected in the following way o no more than one leading 0 o no more than two trailing 0 s n when sent back-to-back, no pair of 5 -bit codes results in more than three consecutive 0 s being transmitted 107
n the resulting 5 -bit codes are transmitted using NRZI n which explains why the code is only concerned about consecutive 0 s o NRZI already solves the problems of consecutive 1 s n the 4 B/5 B encoding results in 80% efficiency 108
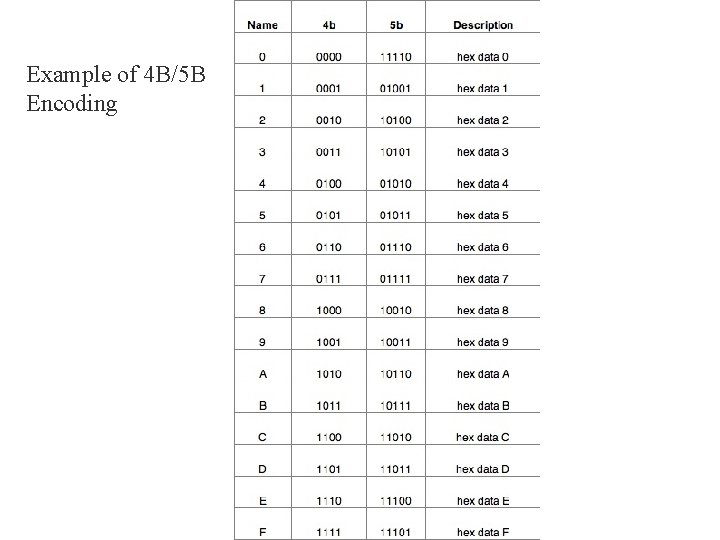
Example of 4 B/5 B Encoding
o The table gives the 5 -bit codes that correspond to each of the 16 possible 4 -bit data symbols n 5 bits are enough to encode 32 different codes, and we are using only 16 of these for data n 16 codes (=1+1+1+7+6) left for other purposes o code 11111: used when the line is idle o code 00000: used when the line is dead o code 00100: interpreted to mean halt o 7 codes are not valid because they violate the "one leading 0, two trailing 0 s, " rule o 6 codes represent various control symbols, e. g. used in framing protocols of FDDI 110
2. 3 Framing o Break sequence of bits into a frame n We are focusing on packet-switched networks n Blocks of data (frames) are exchanged between nodes o It is the network adaptor that enables the nodes to exchange frames n When node A wishes to transmit a frame to node B, it tells its adaptor to transmit a frame from the node’s memory 111
n This results in a sequence of bits being sent over the link n The adaptor on node B then collects together the sequence of bits arriving on the link and deposits the corresponding frame in B’s memory o Determine where the frame begins and ends is the central challenge faced by the adaptor 112
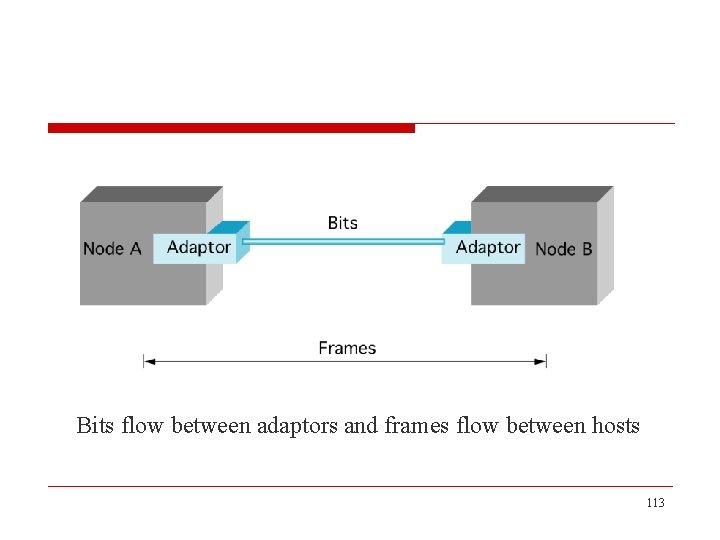
Bits flow between adaptors and frames flow between hosts 113
Approaches o Byte-Oriented Protocols n one of the oldest approaches to framing n root in connecting terminals to mainframes n view each frame as a collection of bytes (characters) rather than a collection of bits 114
n examples o sentinel-based approaches n Binary Synchronous Communication (BISYNC) n Point-to-Point Protocol (PPP) o byte-counting approach n Digital Data Communications Message Protocol (DDCMP) 115
o Bit-Oriented Protocols n views the frame as a collection of bits n these bits might come from o some character set, such as ASCII o pixel values in an image o instructions and operands from an executable file n example o High-Level Data Link Control (HDLC) 116
o Clock-Based Framing n Synchronous Optical Network (SONET) 117
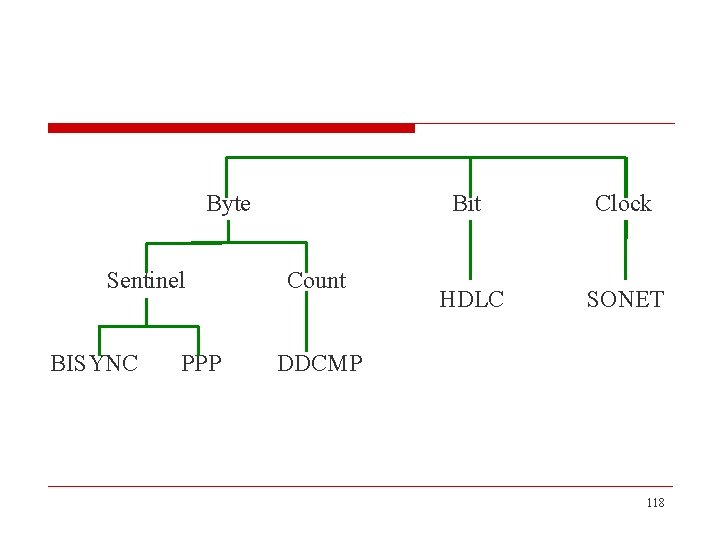
Byte Sentinel BISYNC PPP Count Bit Clock HDLC SONET DDCMP 118
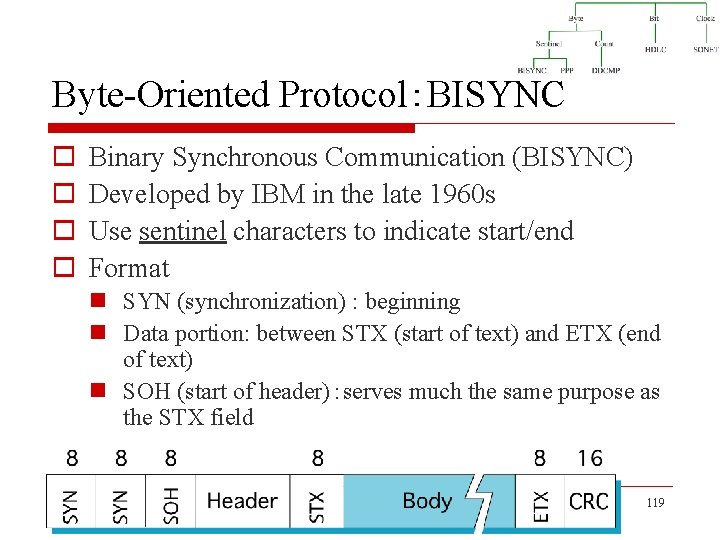
Byte-Oriented Protocol:BISYNC o o Binary Synchronous Communication (BISYNC) Developed by IBM in the late 1960 s Use sentinel characters to indicate start/end Format n SYN (synchronization) : beginning n Data portion: between STX (start of text) and ETX (end of text) n SOH (start of header):serves much the same purpose as the STX field 119
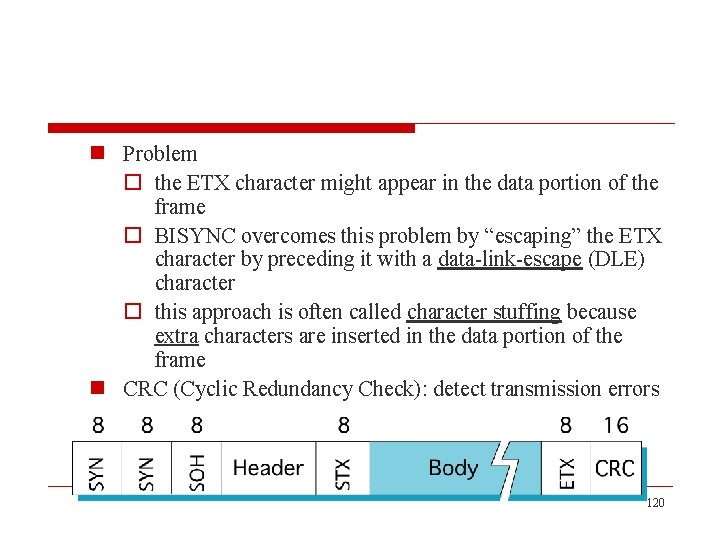
n Problem o the ETX character might appear in the data portion of the frame o BISYNC overcomes this problem by “escaping” the ETX character by preceding it with a data-link-escape (DLE) character o this approach is often called character stuffing because extra characters are inserted in the data portion of the frame n CRC (Cyclic Redundancy Check): detect transmission errors 120
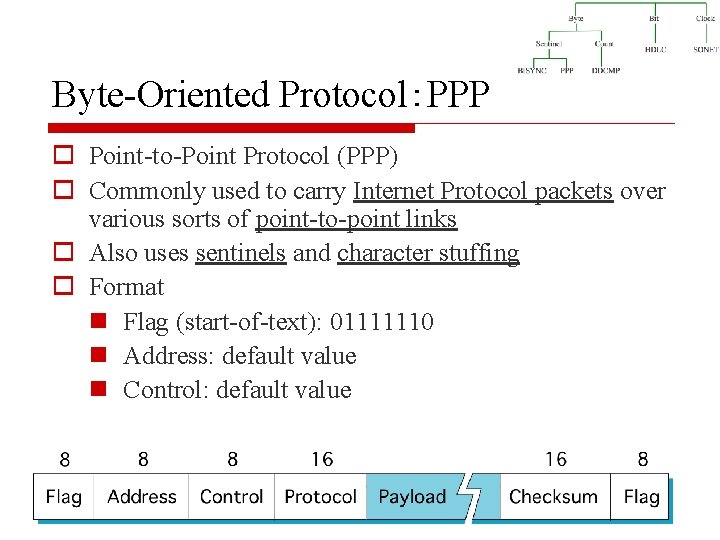
Byte-Oriented Protocol:PPP o Point-to-Point Protocol (PPP) o Commonly used to carry Internet Protocol packets over various sorts of point-to-point links o Also uses sentinels and character stuffing o Format n Flag (start-of-text): 01111110 n Address: default value n Control: default value 121
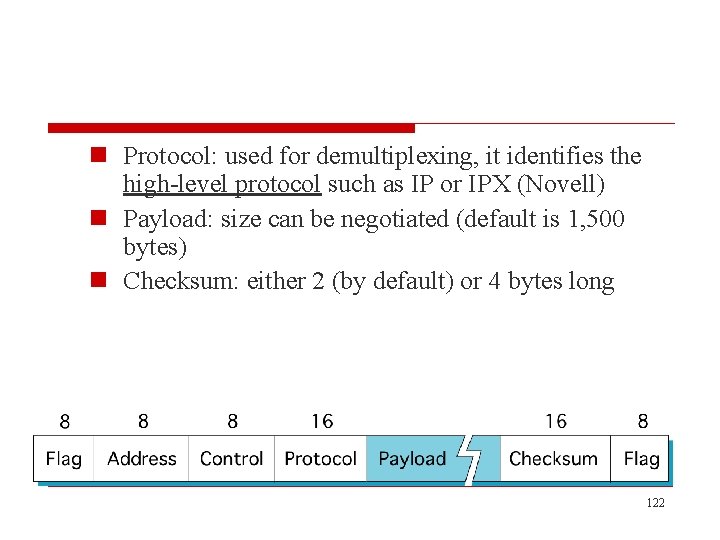
n Protocol: used for demultiplexing, it identifies the high-level protocol such as IP or IPX (Novell) n Payload: size can be negotiated (default is 1, 500 bytes) n Checksum: either 2 (by default) or 4 bytes long 122
o Several of the field sizes of the PPP frame format are negotiated rather than fixed n this negotiation is conducted by a protocol called Link Control Protocol (LCP) n PPP and LCP work in tandem n LCP sends control messages encapsulated in PPP frames and then turns around and changes PPP’s frame format based on the information contained in those control messages 123
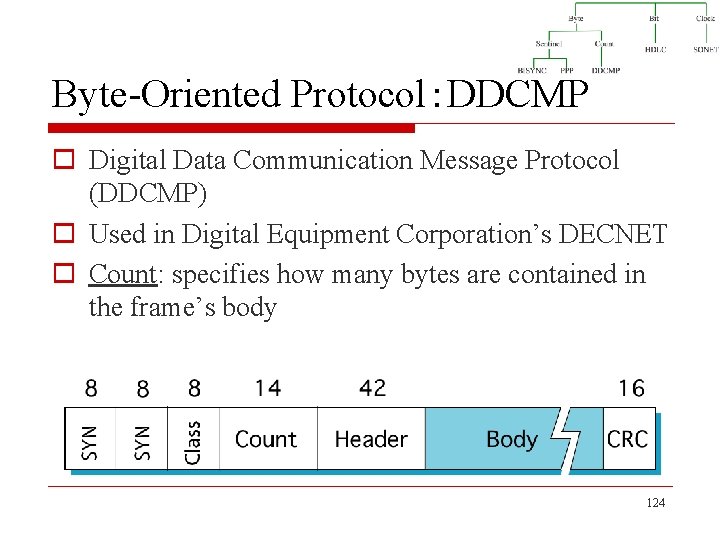
Byte-Oriented Protocol:DDCMP o Digital Data Communication Message Protocol (DDCMP) o Used in Digital Equipment Corporation’s DECNET o Count: specifies how many bytes are contained in the frame’s body 124
o One danger with this approach n a transmission error could corrupt the count field, in which case the end of the frame would not be correctly detected n should this happen, the receiver will accumulate as many bytes as the bad COUNT field indicates and then use the error detection field to determine that the frame is bad (framing error) n the receiver will then wait until it sees the next SYN character to start collecting the bytes that make up the next frame 125
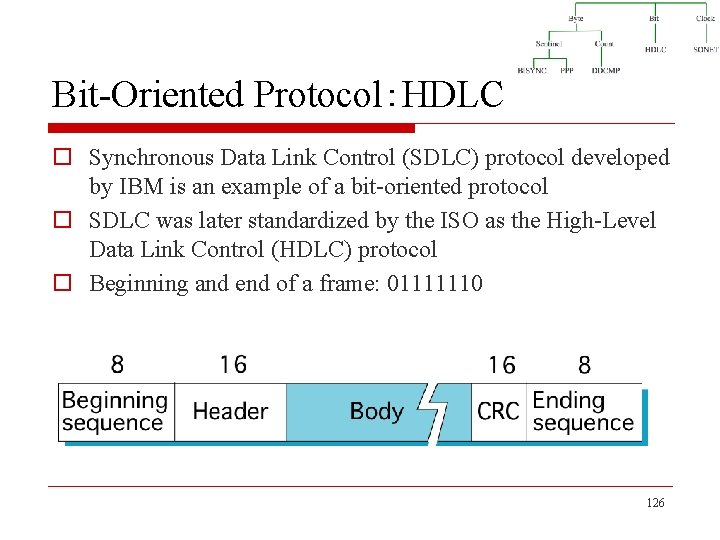
Bit-Oriented Protocol:HDLC o Synchronous Data Link Control (SDLC) protocol developed by IBM is an example of a bit-oriented protocol o SDLC was later standardized by the ISO as the High-Level Data Link Control (HDLC) protocol o Beginning and end of a frame: 01111110 126
o Because this sequence (01111110) might appear anywhere in the body of the frame n in fact, the bits 01111110 might cross byte boundaries n bit-oriented protocols use the analog of the DLE (datalink-escape) character, a technique known as bit stuffing o Operation flow of bit stuffing n on the sending side o any time five consecutive 1 s have been transmitted from the body of the message (i. e. , excluding when the sender is trying to transmit the distinguished 01111110 sequence), the sender inserts a 0 before transmitting the next bit 127
n on the receiving side o should five consecutive 1 s arrive, the receiver makes its decision based on the next bit it sees n if the next bit is a 0, it must have been stuffed, and so the receiver removes it n if the next bit is a 1, then one of two things is true § either this is the end-of-frame marker or an error has been introduced into the bitstream 128
§ by looking at the next bit § if it sees a 0 (i. e. , 01111110), then it is the end-of-frame marker § if it sees a 1 (i. e. , 01111111), then there must have been an error and the whole frame is discarded, in this case, the receiver has to wait for the next 01111110 before it can start receiving again 129
Clock-Based Framing:SONET o Synchronous Optical Network (SONET) n first proposed by Bell Communications Research (Bellcore) n then developed under the American National Standards Institute (ANSI) for digital transmission over optical fiber, it has since been adopted by the ITU-T o The dominant standard for long-distance transmission of data over optical networks 130
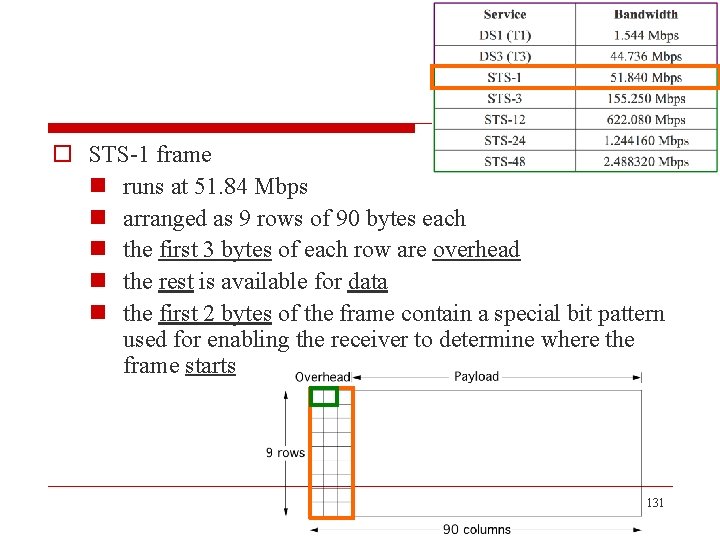
o STS-1 frame n runs at 51. 84 Mbps n arranged as 9 rows of 90 bytes each n the first 3 bytes of each row are overhead n the rest is available for data n the first 2 bytes of the frame contain a special bit pattern used for enabling the receiver to determine where the frame starts 131
o Frame overhead n bits that are added at regular intervals to a digital signal at the sending end of a digital link and used to provide network functions such as framing, operations, administration, and maintenance n the overhead bytes of a SONET frame are encoded using NRZ 132
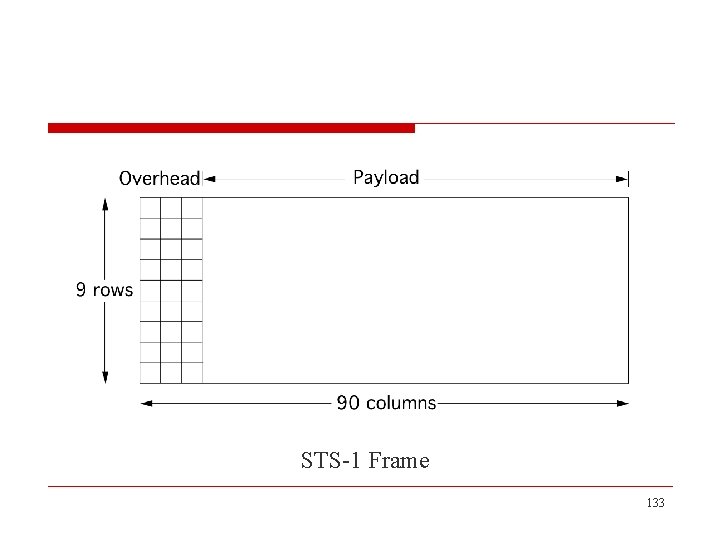
STS-1 Frame 133
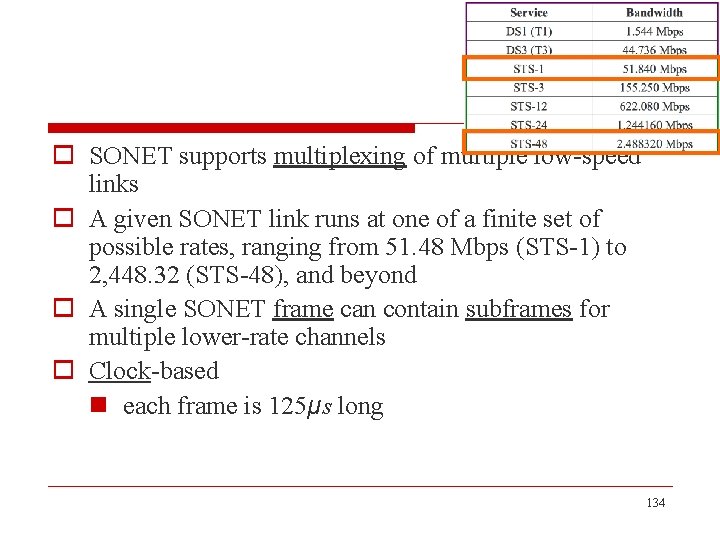
o SONET supports multiplexing of multiple low-speed links o A given SONET link runs at one of a finite set of possible rates, ranging from 51. 48 Mbps (STS-1) to 2, 448. 32 (STS-48), and beyond o A single SONET frame can contain subframes for multiple lower-rate channels o Clock-based n each frame is 125μs long 134
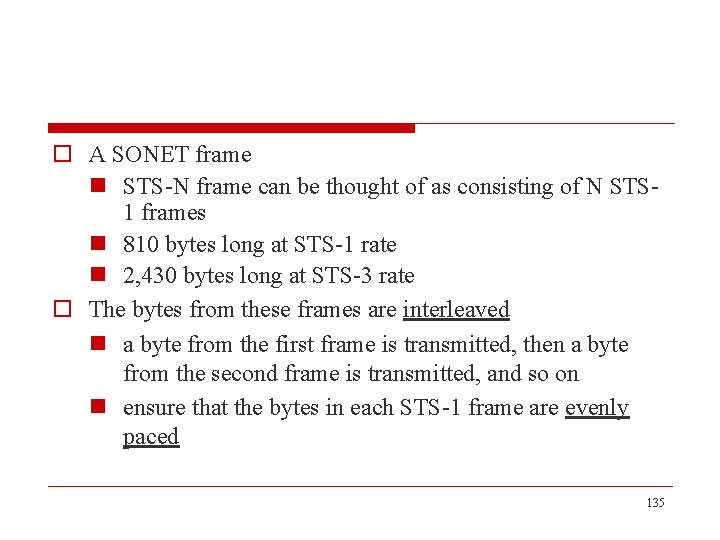
o A SONET frame n STS-N frame can be thought of as consisting of N STS 1 frames n 810 bytes long at STS-1 rate n 2, 430 bytes long at STS-3 rate o The bytes from these frames are interleaved n a byte from the first frame is transmitted, then a byte from the second frame is transmitted, and so on n ensure that the bytes in each STS-1 frame are evenly paced 135
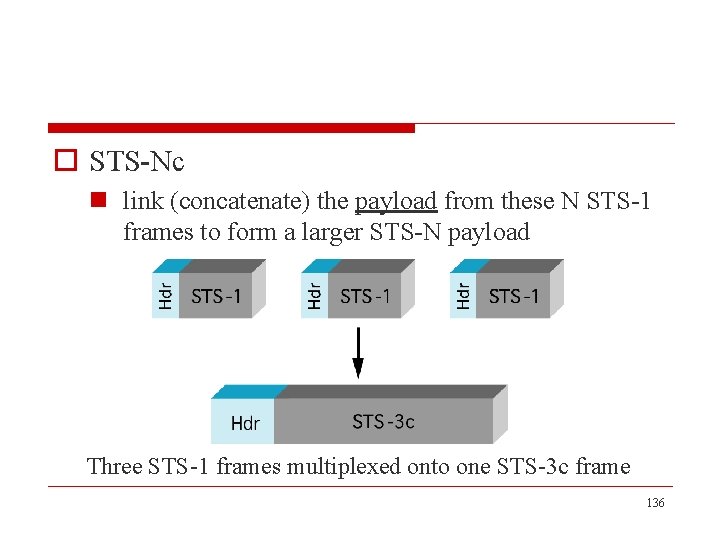
o STS-Nc n link (concatenate) the payload from these N STS-1 frames to form a larger STS-N payload Three STS-1 frames multiplexed onto one STS-3 c frame 136
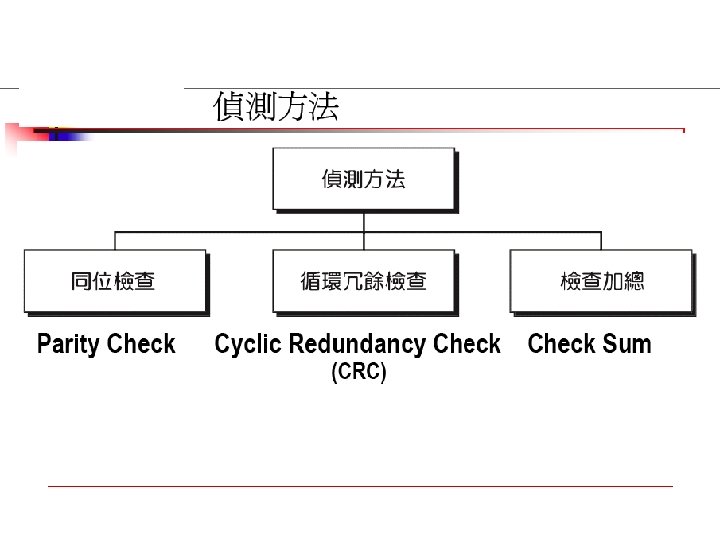
2. 4 Error Detection o Two basic approaches that can be taken when the recipient of a message detects an error n one is to notify the sender that the message was corrupted so that the sender can retransmit a copy of the message n alternatively, there are some types of error detection algorithms that allow the recipient to reconstruct the correct message even after it has been corrupted; such algorithms rely on error correcting codes 137
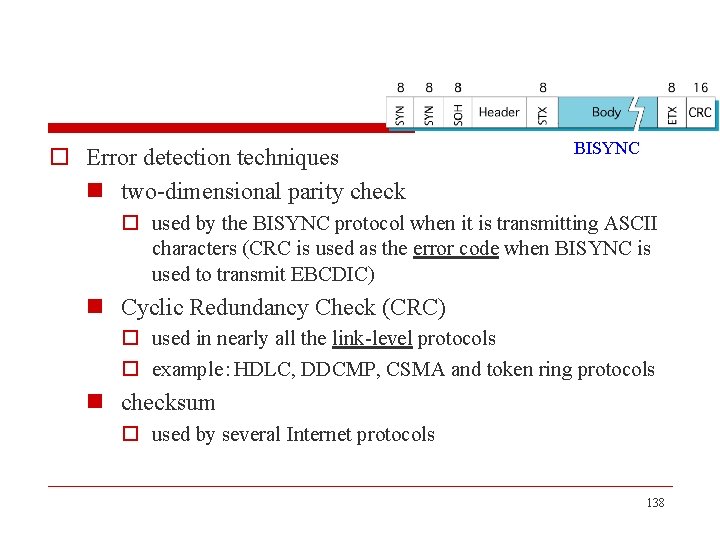
o Error detection techniques n two-dimensional parity check BISYNC o used by the BISYNC protocol when it is transmitting ASCII characters (CRC is used as the error code when BISYNC is used to transmit EBCDIC) n Cyclic Redundancy Check (CRC) o used in nearly all the link-level protocols o example:HDLC, DDCMP, CSMA and token ring protocols n checksum o used by several Internet protocols 138
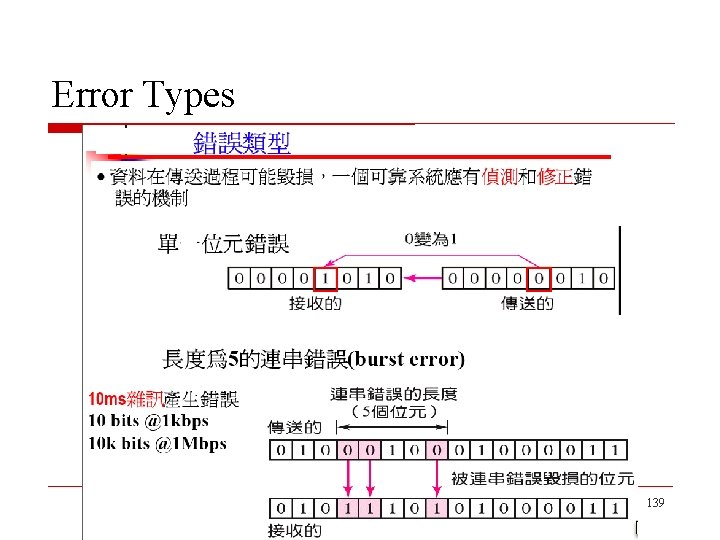
Error Types 139
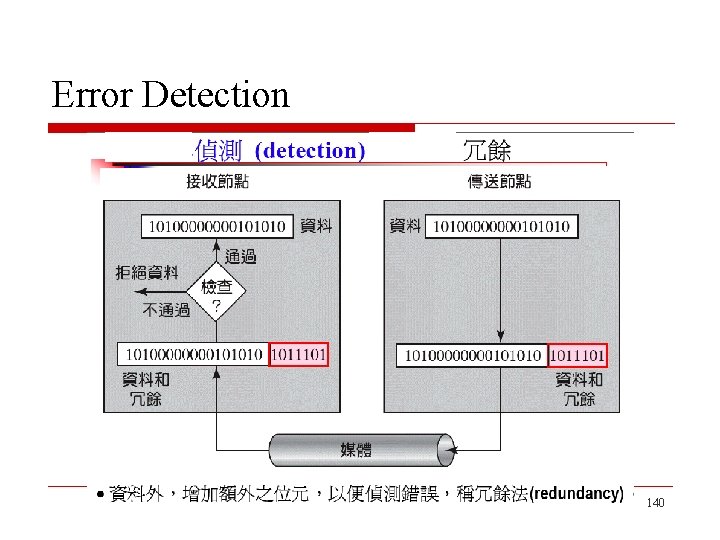
Error Detection 140
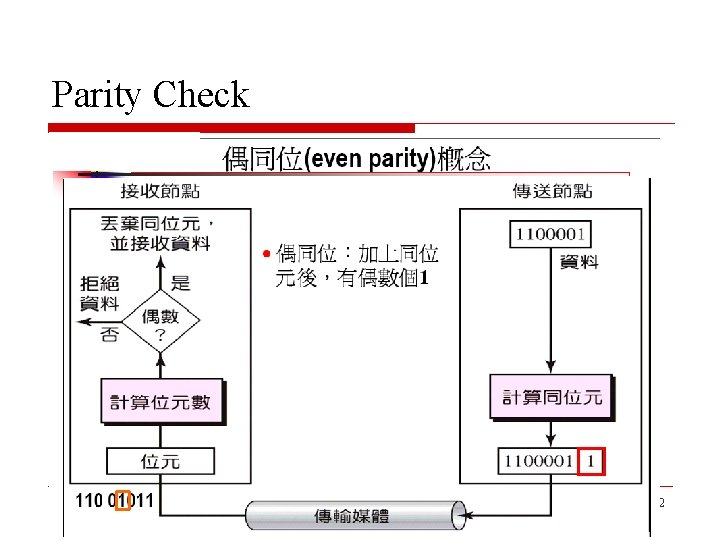
Parity Check 142
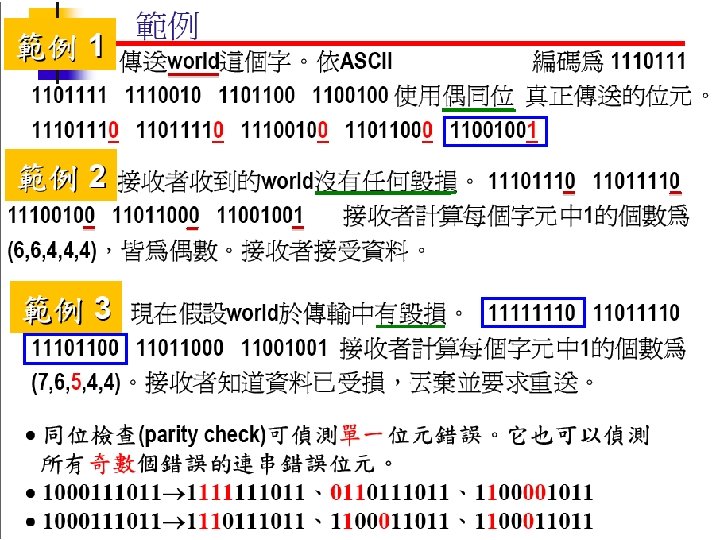
143
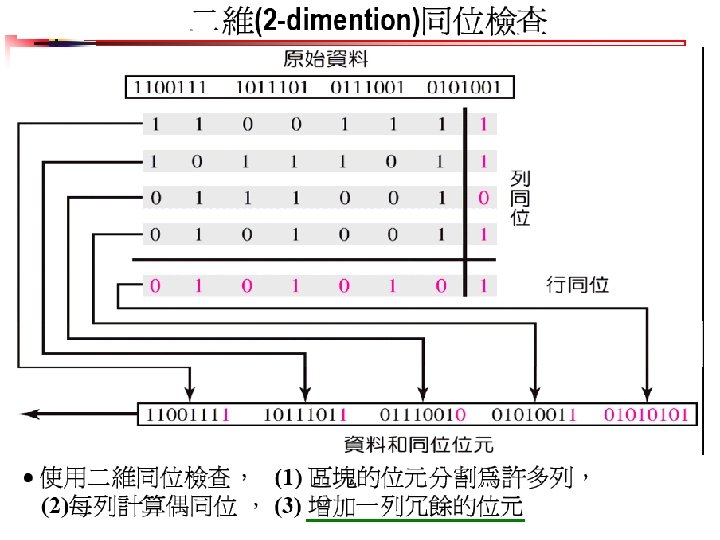
144
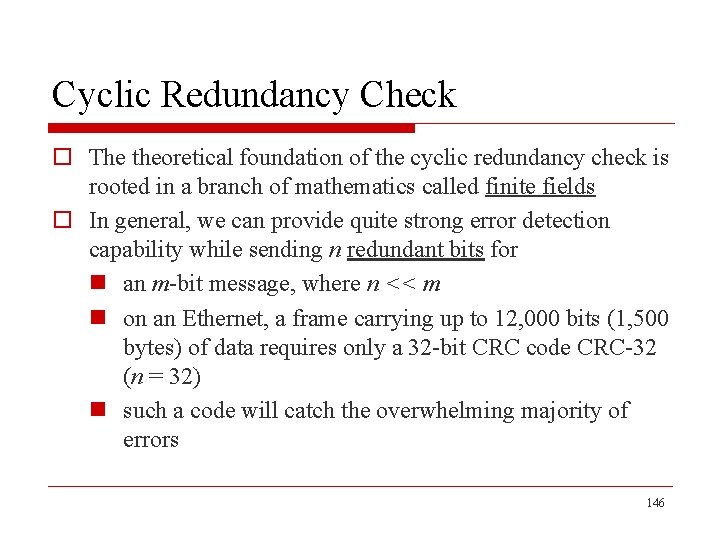
Cyclic Redundancy Check o The theoretical foundation of the cyclic redundancy check is rooted in a branch of mathematics called finite fields o In general, we can provide quite strong error detection capability while sending n redundant bits for n an m-bit message, where n << m n on an Ethernet, a frame carrying up to 12, 000 bits (1, 500 bytes) of data requires only a 32 -bit CRC code CRC-32 (n = 32) n such a code will catch the overwhelming majority of errors 146
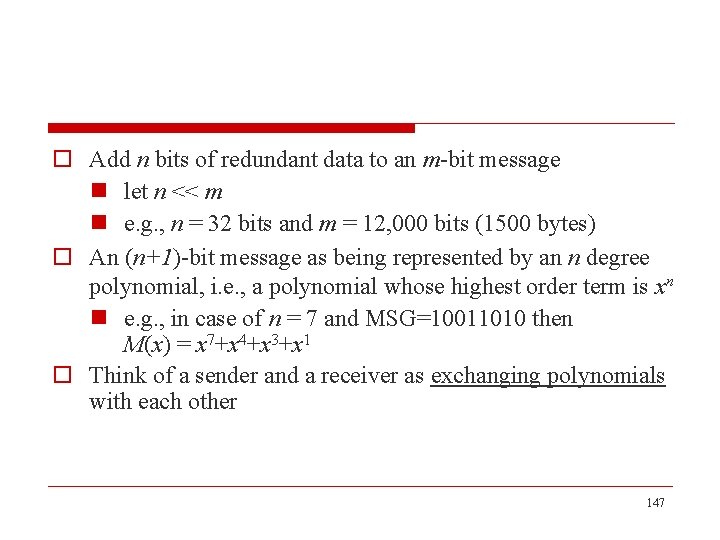
o Add n bits of redundant data to an m-bit message n let n << m n e. g. , n = 32 bits and m = 12, 000 bits (1500 bytes) o An (n+1)-bit message as being represented by an n degree polynomial, i. e. , a polynomial whose highest order term is xn n e. g. , in case of n = 7 and MSG=10011010 then M(x) = x 7+x 4+x 3+x 1 o Think of a sender and a receiver as exchanging polynomials with each other 147
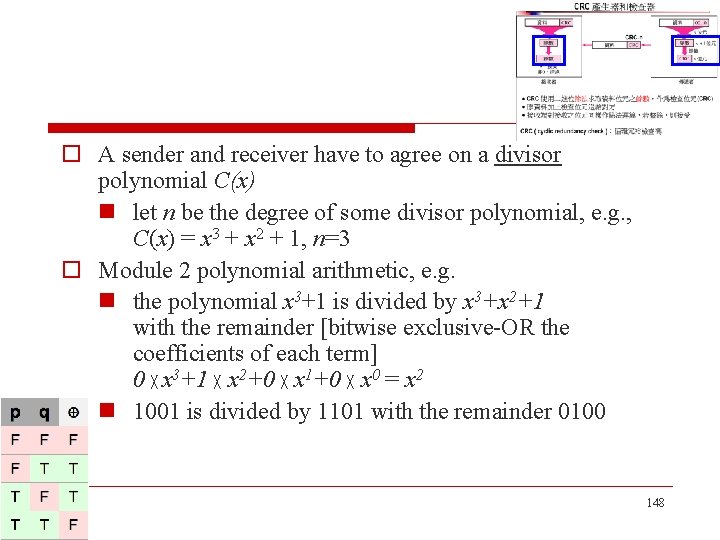
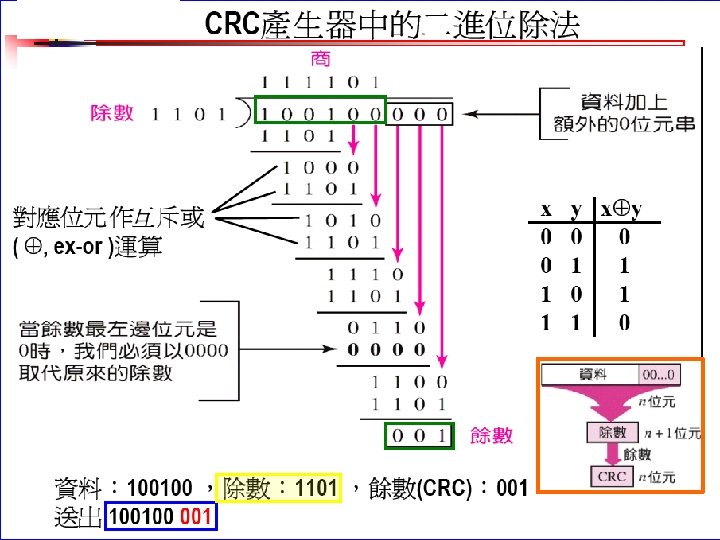
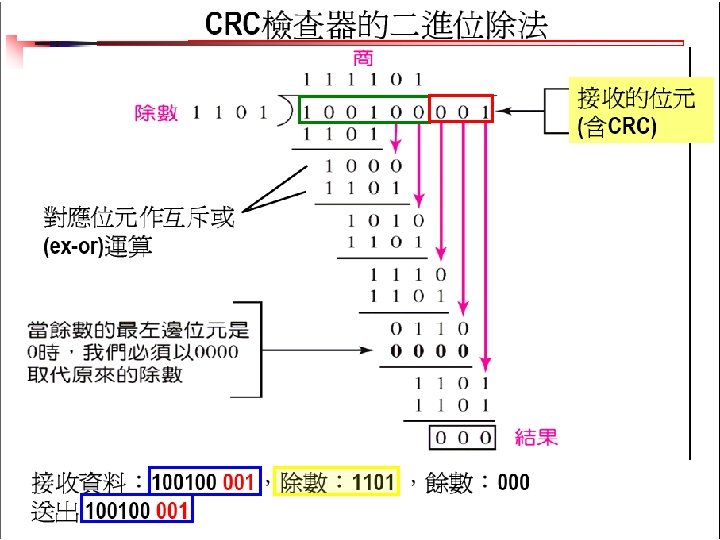
o A sender and receiver have to agree on a divisor polynomial C(x) n let n be the degree of some divisor polynomial, e. g. , C(x) = x 3 + x 2 + 1, n=3 o Module 2 polynomial arithmetic, e. g. n the polynomial x 3+1 is divided by x 3+x 2+1 with the remainder [bitwise exclusive-OR the coefficients of each term] 0 ╳ x 3+1 ╳ x 2+0 ╳ x 1+0 ╳ x 0 = x 2 n 1001 is divided by 1101 with the remainder 0100 148
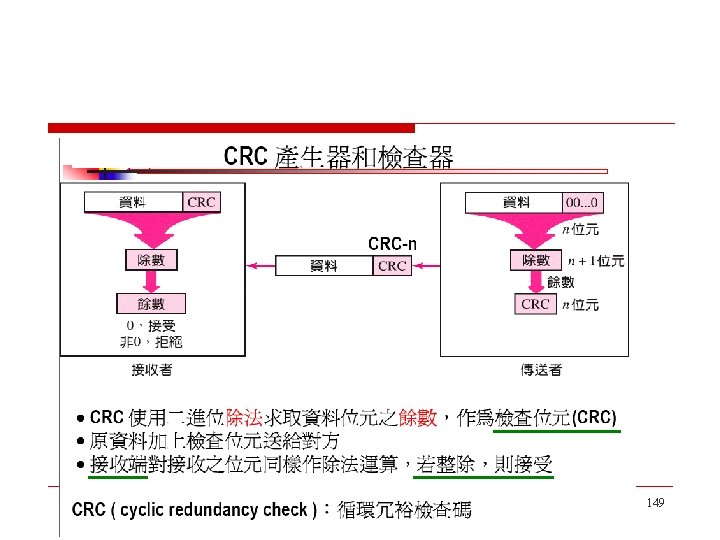
149
150
151
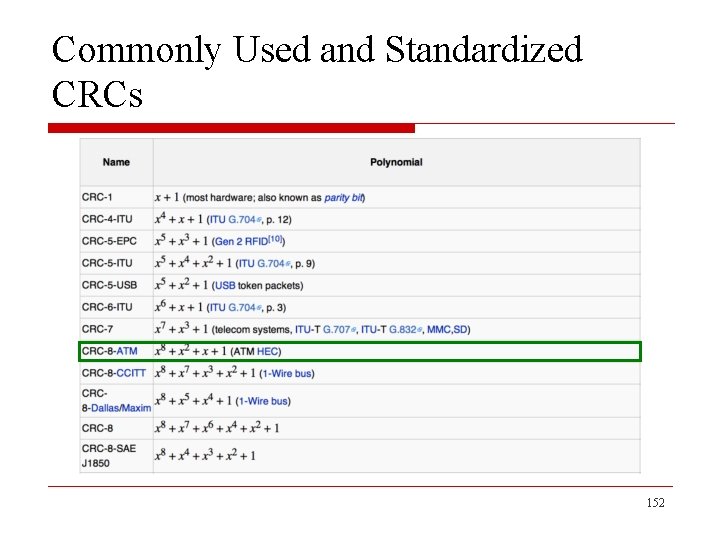
Commonly Used and Standardized CRCs 152
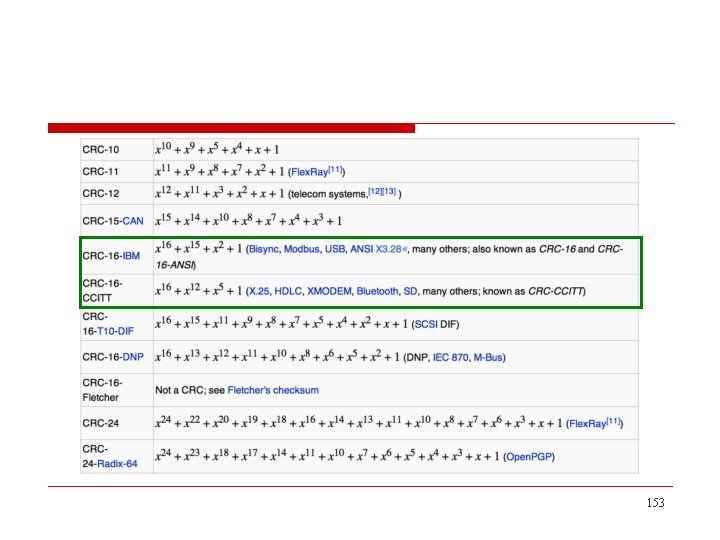
153
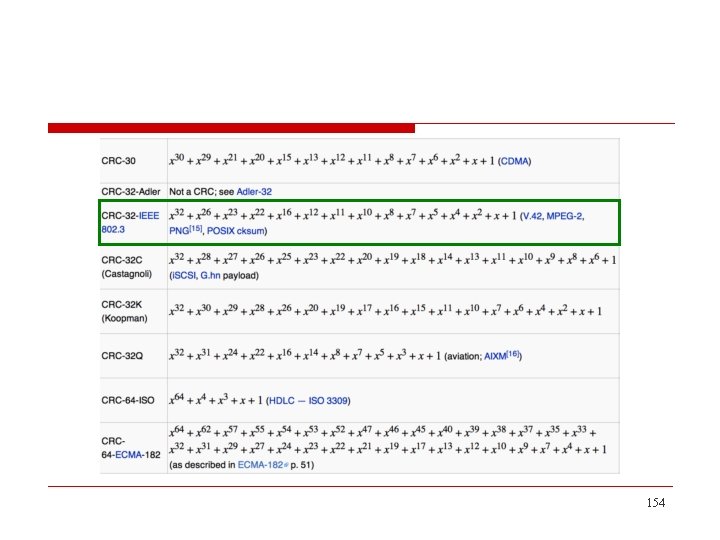
154
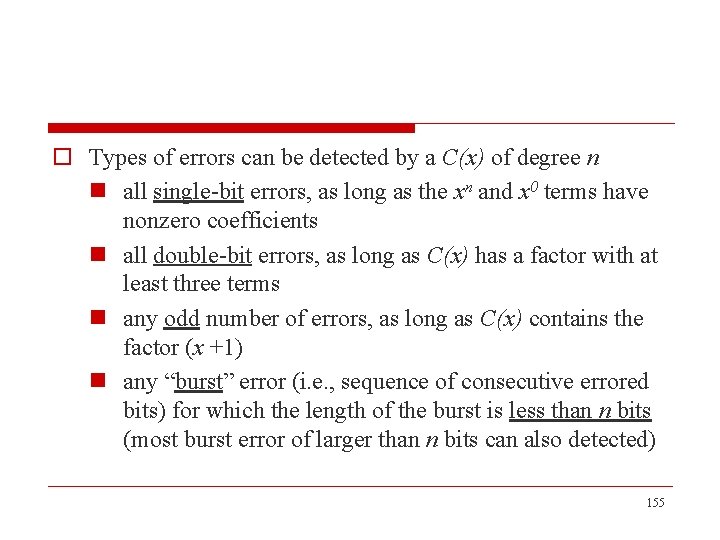
o Types of errors can be detected by a C(x) of degree n n all single-bit errors, as long as the xn and x 0 terms have nonzero coefficients n all double-bit errors, as long as C(x) has a factor with at least three terms n any odd number of errors, as long as C(x) contains the factor (x +1) n any “burst” error (i. e. , sequence of consecutive errored bits) for which the length of the burst is less than n bits (most burst error of larger than n bits can also detected) 155
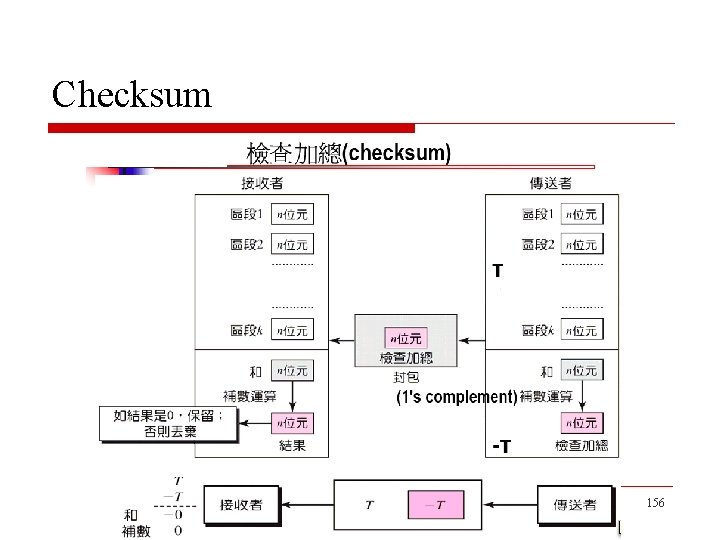
Checksum 156
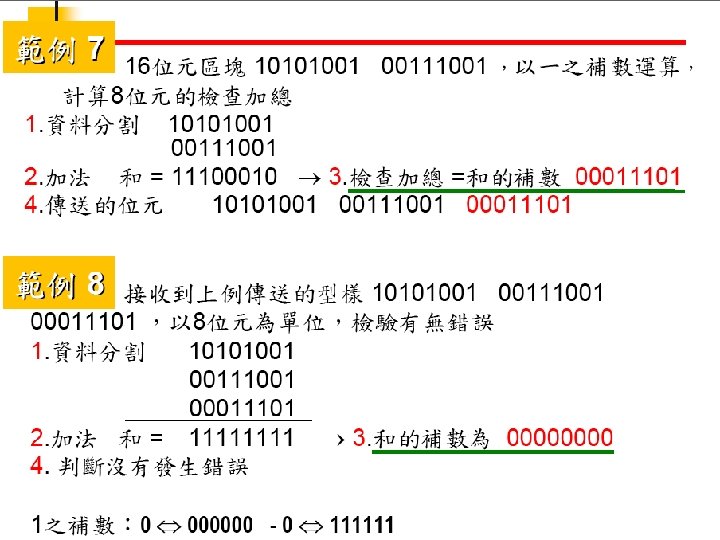
157
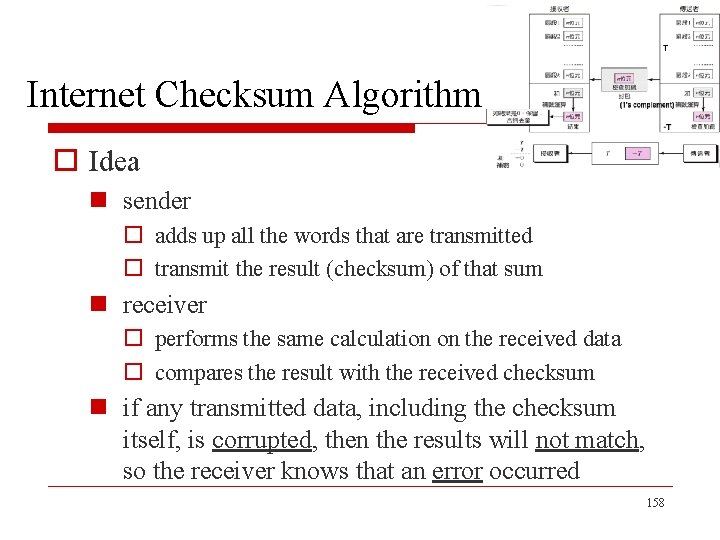
Internet Checksum Algorithm o Idea n sender o adds up all the words that are transmitted o transmit the result (checksum) of that sum n receiver o performs the same calculation on the received data o compares the result with the received checksum n if any transmitted data, including the checksum itself, is corrupted, then the results will not match, so the receiver knows that an error occurred 158
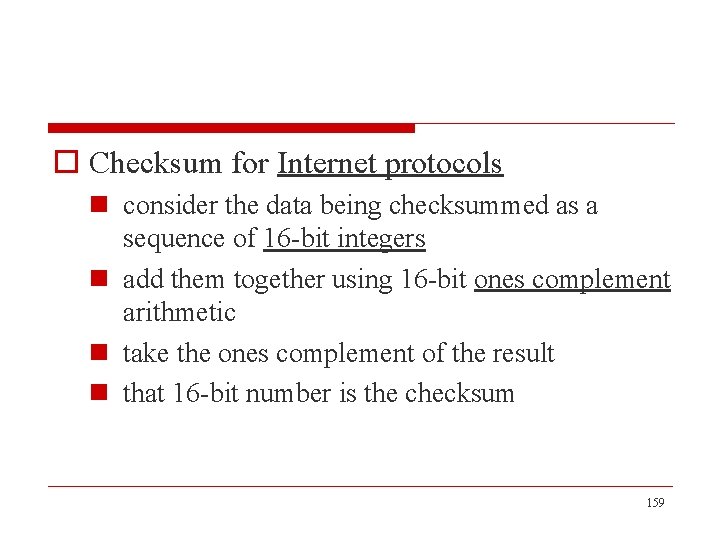
o Checksum for Internet protocols n consider the data being checksummed as a sequence of 16 -bit integers n add them together using 16 -bit ones complement arithmetic n take the ones complement of the result n that 16 -bit number is the checksum 159
o Ones complement arithmetic n a negative integer -x is represented as the complement of x, i. e. , each bit of x is inverted n when adding numbers in ones complement arithmetic, a carryout from the most significant bit needs to be added to the result 160
n example, the addition of -5 and -3 in ones complement arithmetic on 4 -bit integers o +5 is 0101, so -5 is 1010 o +3 is 0011, so -3 is 1100 o add 1010 and 1100, we get 0110 o add carryout to 0110, we get 0111, which is the ones complement representation of -8 161
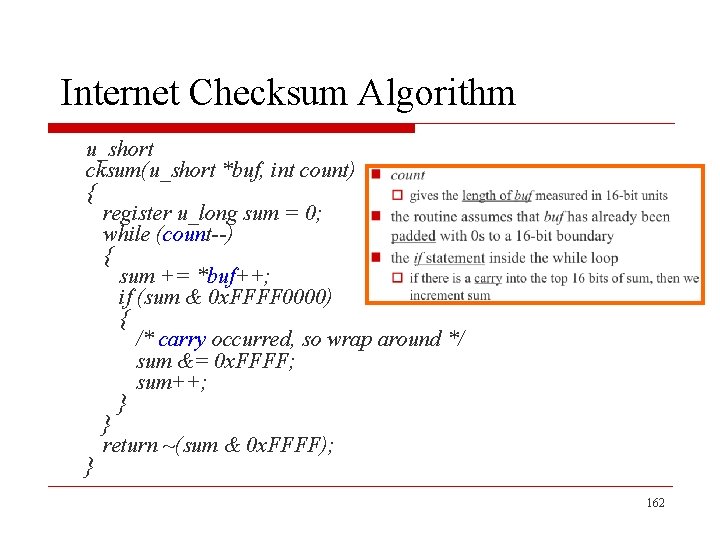
Internet Checksum Algorithm u_short cksum(u_short *buf, int count) { register u_long sum = 0; while (count--) { sum += *buf++; if (sum & 0 x. FFFF 0000) { /* carry occurred, so wrap around */ sum &= 0 x. FFFF; sum++; } } return ~(sum & 0 x. FFFF); } 162
n count o gives the length of buf measured in 16 -bit units n the routine assumes that buf has already been padded with 0 s to a 16 -bit boundary n the if statement inside the while loop o if there is a carry into the top 16 bits of sum, then we increment sum 163
- Slides: 163