Data and Network Security Lab Sharif University of
Data and Network Security Lab Sharif University of Technology Department of Computer Engineering One-way Functions and Permutations Author & Instructor: Mohammad Sadeq Dousti Sharif University Introduction to Modern Cryptography 1 / 50
Copyright Notice q q These set of slides are licensed under Creative Commons Attribution-Non. Commercial-Share. Alike (CC BY-NC-SA) 4. 0. Basically, this license allows others to use the slides verbatim, and even modify and incorporate them into their own work, as long as: 1. 2. 3. q They credit the original author(s); Their work is used non-commercially; They license their work under CC BY-NC-SA 4. 0. For further information, please consult: o o https: //creativecommons. org/licenses/by-nc-sa/4. 0 https: //creativecommons. org/licenses/by-ncsa/4. 0/legalcode Sharif University Introduction to Modern Cryptography 2 / 50
Outline q q q q One-way Functions (OWF) Hard-core Predicates One-way Permutations (OWP) Trapdoor Permutations (TDP) Claw-free Functions and Permutations (CFFs & CFPs) Impagliazzo’s five worlds Impagliazzo–Rudich theorem Sharif University Introduction to Modern Cryptography 3 / 50
One-way Functions OWF Sharif University Introduction to Modern Cryptography 4 / 50
One-wayness: Intuition q Easy to go in one direction Hard to go in the other direction q Example: q Easy to break a glass o Hard to reconstruct it o Author: Jef Poskanzer https: //commons. wikimedia. org/wiki/File: Broken_glass. jpg Sharif University Introduction to Modern Cryptography 5 / 50
How to define one-way functions? q How to capture the following notion: The function is easy to compute Probabilistic Polynomial Time (PPT) o It is hard to invert o q Easy to compute: o q Function f is easy to compute if there exists an efficient Turing machine M such that for all inputs x {0, 1}*, we have M(x) = f (x). Order of quantifiers: M x o Why not x M ? Sharif University Introduction to Modern Cryptography 6 / 50
How to define one-way functions? (Cont’d) q How to capture the following notion: The function is easy to compute o It is hard to invert o q Hard to invert; Three approaches: Easy case o Worst case o Average case o q Easy case is meaningless… o Why? Sharif University Introduction to Modern Cryptography 7 / 50
Hard to invert in the worst case q q No PPT algorithm can invert the function for all inputs. Formalization o q We overlooked the fact that M is probabilistic. We should talk about the output probability of M. Function f is hard to invert if for any efficient Turing machine M, there exist an input x {0, 1}* such that M (f (x)) f 1( f (x)). Order of quantifiers: M x o Why not x M ? We overlooked the fact that f can q Not useful in cryptography. shrink the input. M must be given the length of the o Why? input, |x|, as well. Sharif University Introduction to Modern Cryptography 8 / 50
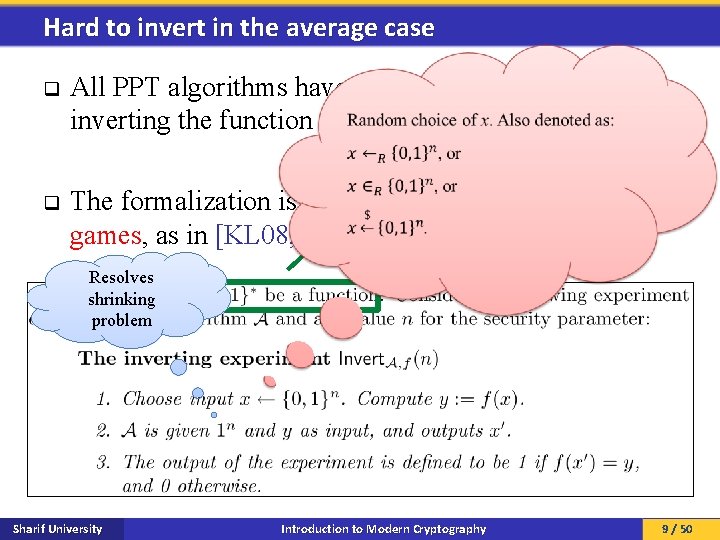
Hard to invert in the average case q q All PPT algorithms have a negligible chance of inverting the function for random inputs. Syntax The formalization is best captured by the notion of games, as in [KL 08, section 6. 1]: Resolves shrinking problem Sharif University Introduction to Modern Cryptography 9 / 50
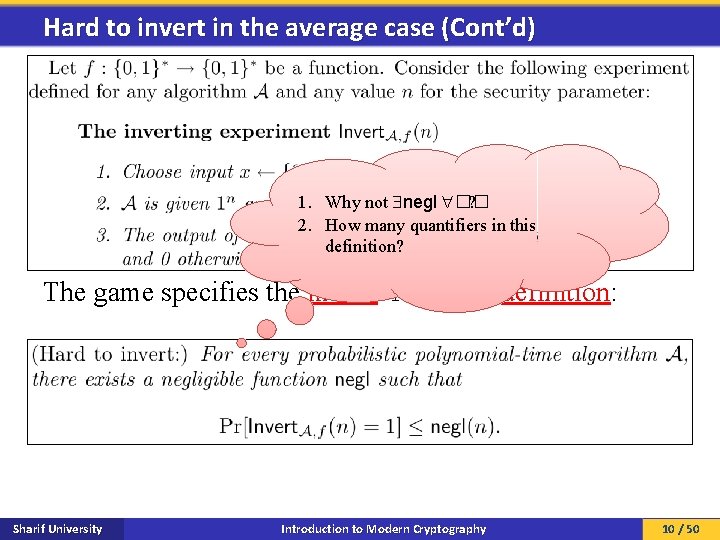
Hard to invert in the average case (Cont’d) 1. Why not negl �� ? 2. How many quantifiers in this definition? The game specifies the model. Now, the definition: Sharif University Introduction to Modern Cryptography 10 / 50
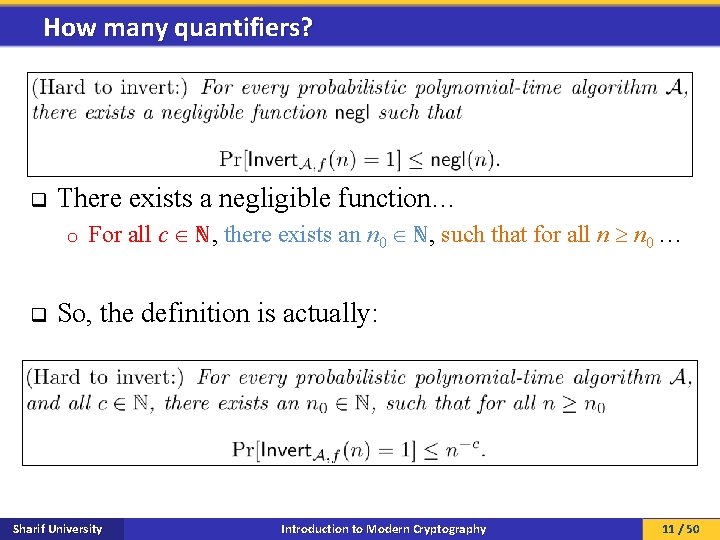
How many quantifiers? q There exists a negligible function… o q For all c ℕ, there exists an n 0 ℕ, such that for all n n 0 … So, the definition is actually: Sharif University Introduction to Modern Cryptography 11 / 50
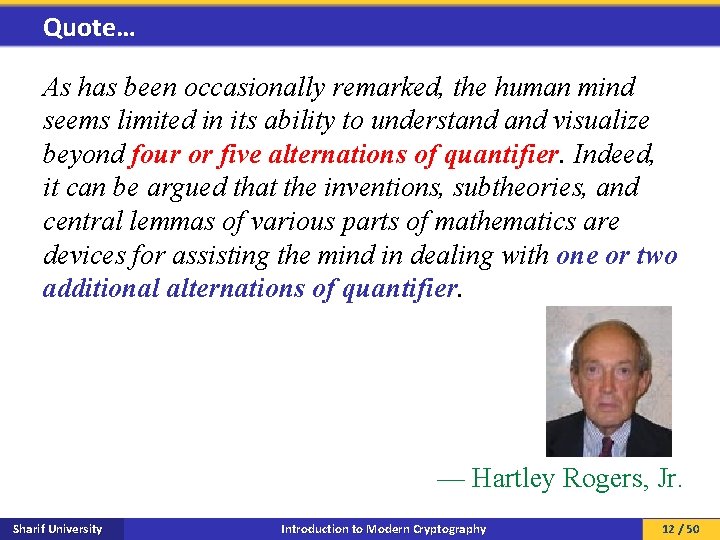
Quote… As has been occasionally remarked, the human mind seems limited in its ability to understand visualize beyond four or five alternations of quantifier. Indeed, it can be argued that the inventions, subtheories, and central lemmas of various parts of mathematics are devices for assisting the mind in dealing with one or two additional alternations of quantifier. — Hartley Rogers, Jr. Sharif University Introduction to Modern Cryptography 12 / 50
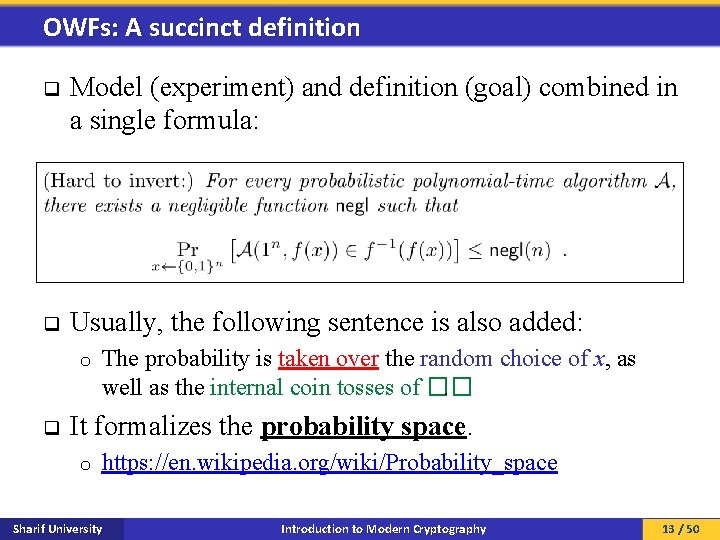
OWFs: A succinct definition q Model (experiment) and definition (goal) combined in a single formula: q Usually, the following sentence is also added: o q The probability is taken over the random choice of x, as well as the internal coin tosses of ��. It formalizes the probability space. o https: //en. wikipedia. org/wiki/Probability_space Sharif University Introduction to Modern Cryptography 13 / 50
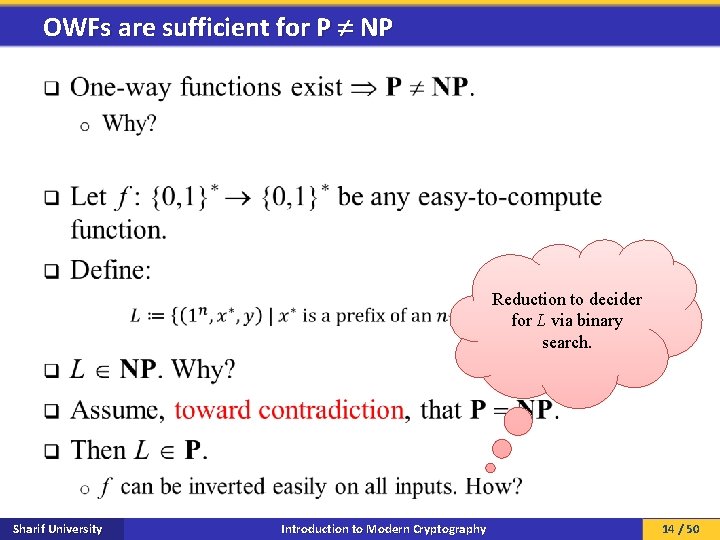
OWFs are sufficient for P NP q Reduction to decider for L via binary search. Sharif University Introduction to Modern Cryptography 14 / 50
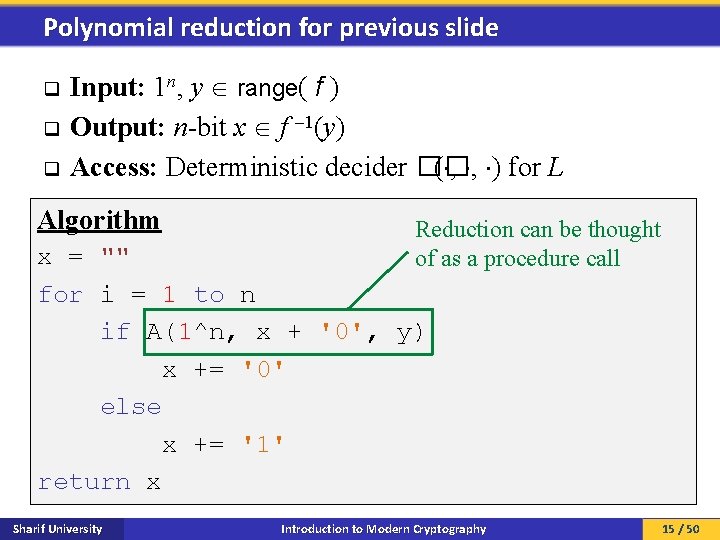
Polynomial reduction for previous slide q q q Input: 1 n, y range( f ) Output: n-bit x f 1(y) Access: Deterministic decider �� ( , , ) for L Algorithm Reduction can be thought of as a procedure call x = "" for i = 1 to n if A(1^n, x + '0', y) x += '0' else x += '1' return x Sharif University Introduction to Modern Cryptography 15 / 50
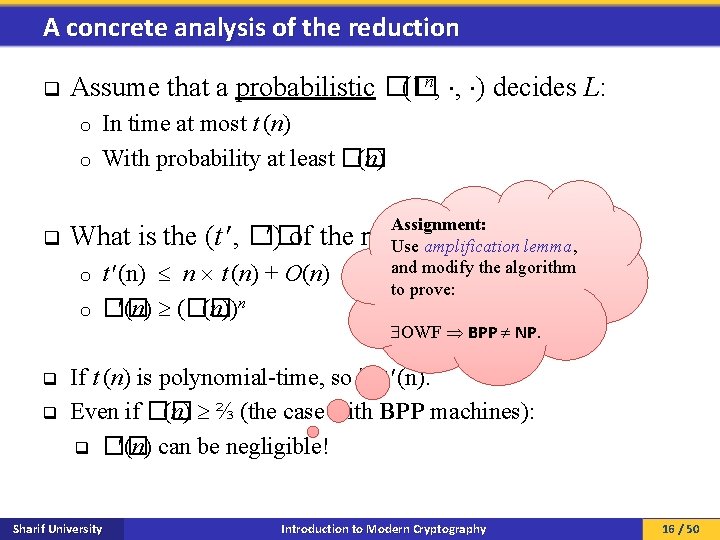
A concrete analysis of the reduction q Assume that a probabilistic �� (1 n, , ) decides L: In time at most t (n) o With probability at least �� (n) o Assignment: q What is the (t , �� ) of the reduction? Use amplification lemma, and modify the algorithm o t (n) n t (n) + O(n) to prove: o q q �� (n) (�� (n))n OWF BPP NP. If t (n) is polynomial-time, so is t (n). Even if �� (n) ⅔ (the case with BPP machines): q �� (n) can be negligible! Sharif University Introduction to Modern Cryptography 16 / 50
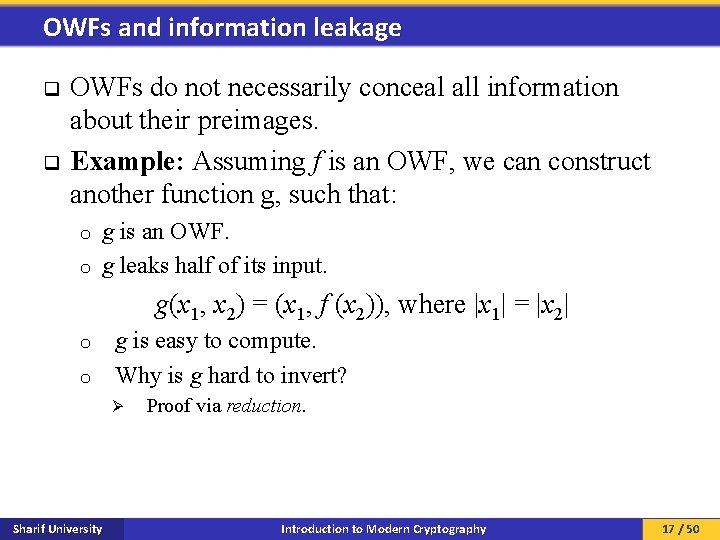
OWFs and information leakage q q OWFs do not necessarily conceal all information about their preimages. Example: Assuming f is an OWF, we can construct another function g, such that: g is an OWF. o g leaks half of its input. o g(x 1, x 2) = (x 1, f (x 2)), where |x 1| = |x 2| o o g is easy to compute. Why is g hard to invert? Ø Sharif University Proof via reduction. Introduction to Modern Cryptography 17 / 50
Why is g hard to invert: The reduction q q g(x 1, x 2) = (x 1, f T(x(n) T 2)), where |x 1| = |x 2| (n) + O(n) ℱ �� Let �� be an adversary who inverts g in time t and ϵ (n) �� What happens if we let x 1ℱ = 0 n? �� with probability ϵ��. If T�� (n) is a polynomial, so is Tℱ(n). Ø The input distribution of �� changes. We construct an adversary ℱ who, uses �� as a If ϵ�� (n) is not negligible, so is ϵℱ(n). Ø �� can always fail on other input and with subroutine, and inverts f in time t ℱ Ø Contradiction: f is an OWF. distributions! probability ϵℱ. n, ℱy) is closely related to (t We show that (t , ϵ�� ). Requires O(n) time to ℱ, ϵ �� Algorithm ℱ(1 2) read x 1 from random tape, Inverting f is reduced to inverting g. and write it to �� 's input o x 1 If g is easy to invert, so is f. {0, 1}^n tape. o But f is an OWF (by assumption). (z 1, x 2) = �� (1^n, x 1, y 2) o So, g must be hard to invert. return x 2 Sharif University Introduction to Modern Cryptography 18 / 50
Hard-Core Predicates Sharif University Introduction to Modern Cryptography 19 / 50
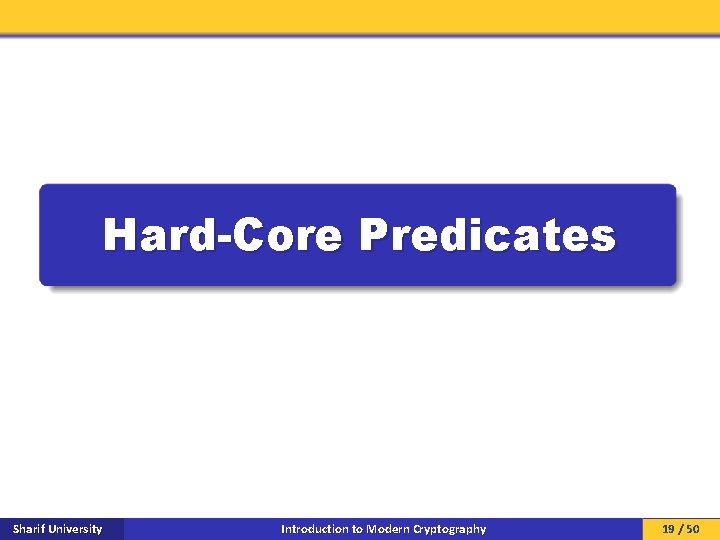
Hard-core predicates q Informally: A predicate hc, such that: A general o Given x, hc(x) is easy to compute; function, not necessarily an o Given f (x), the value of hc(x) is hard to guess (with OWF. probability better than ½). q q q Hard-core predicates for OWFs capture the hardness of inverting OWFs. They are useful for constructing PRGs from OWFs (later in this course). Every OWF must have a hard-core predicate. o Why? [KL 08, p. 199] Sharif University Introduction to Modern Cryptography 20 / 50
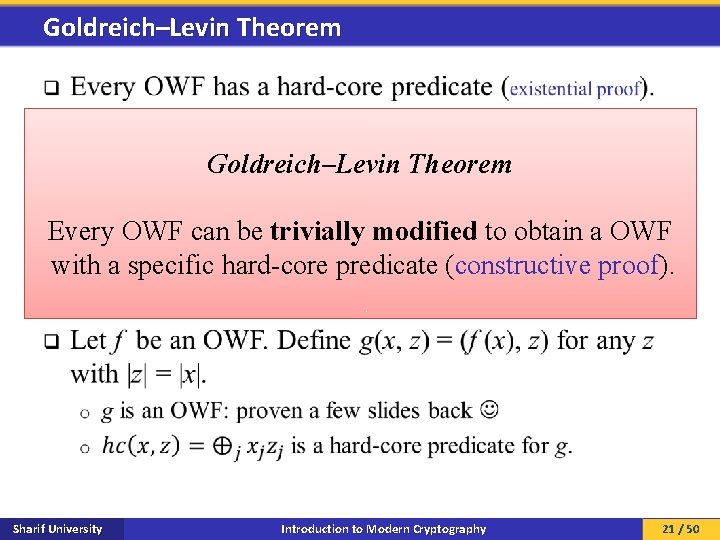
Goldreich–Levin Theorem q Goldreich–Levin Theorem Every OWF can be trivially modified to obtain a OWF with a specific hard-core predicate (constructive proof). Sharif University Introduction to Modern Cryptography 21 / 50
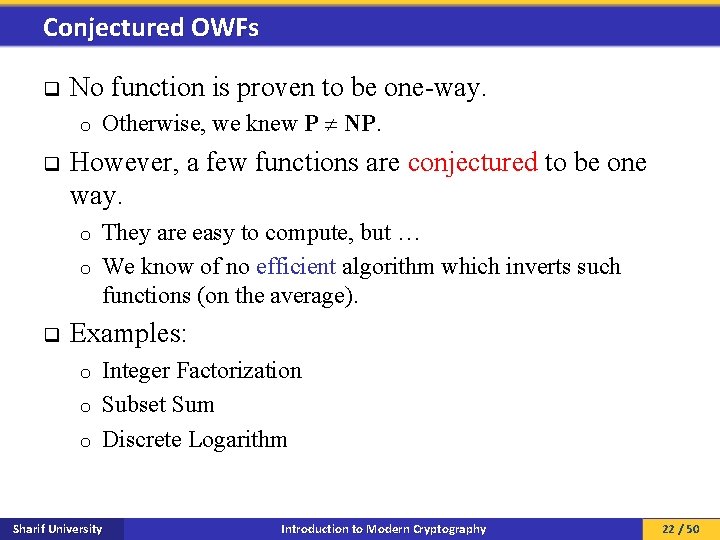
Conjectured OWFs q No function is proven to be one-way. o q Otherwise, we knew P NP. However, a few functions are conjectured to be one way. They are easy to compute, but … o We know of no efficient algorithm which inverts such functions (on the average). o q Examples: Integer Factorization o Subset Sum o Discrete Logarithm o Sharif University Introduction to Modern Cryptography 22 / 50
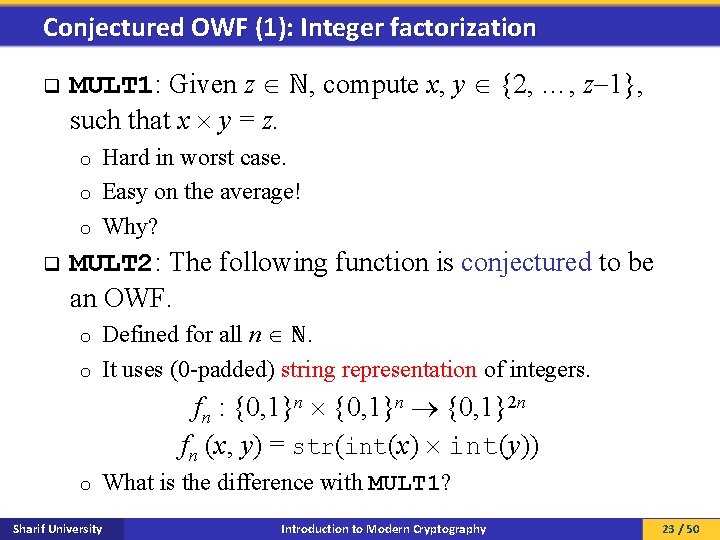
Conjectured OWF (1): Integer factorization q MULT 1: Given z ℕ, compute x, y {2, …, z 1}, such that x y = z. Hard in worst case. o Easy on the average! o Why? o q MULT 2: The following function is conjectured to be an OWF. Defined for all n ℕ. o It uses (0 -padded) string representation of integers. o fn : {0, 1}n {0, 1}2 n fn (x, y) = str(int(x) int(y)) o What is the difference with MULT 1? Sharif University Introduction to Modern Cryptography 23 / 50
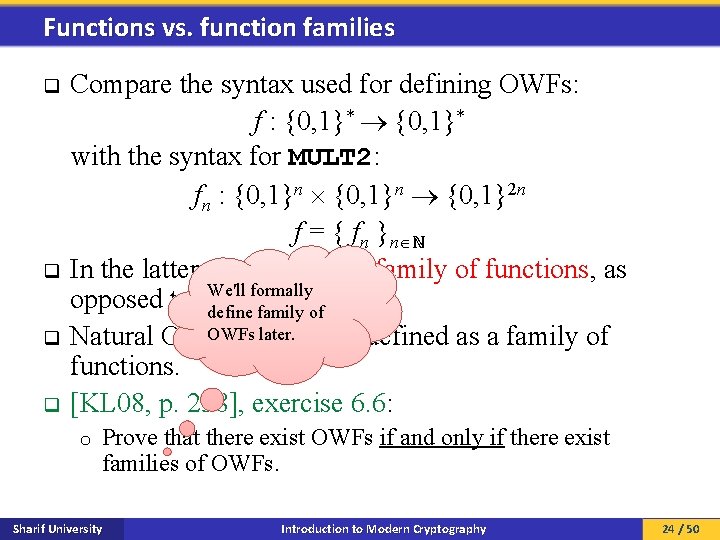
Functions vs. function families Compare the syntax used for defining OWFs: f : {0, 1}* with the syntax for MULT 2: fn : {0, 1}n {0, 1}2 n f = { fn }n ℕ q In the latter, f is an infinite family of functions, as We'll formally opposed to a single function. define family of OWFs later. q Natural OWFs are mostly defined as a family of functions. q [KL 08, p. 238], exercise 6. 6: q o Prove that there exist OWFs if and only if there exist families of OWFs. Sharif University Introduction to Modern Cryptography 24 / 50
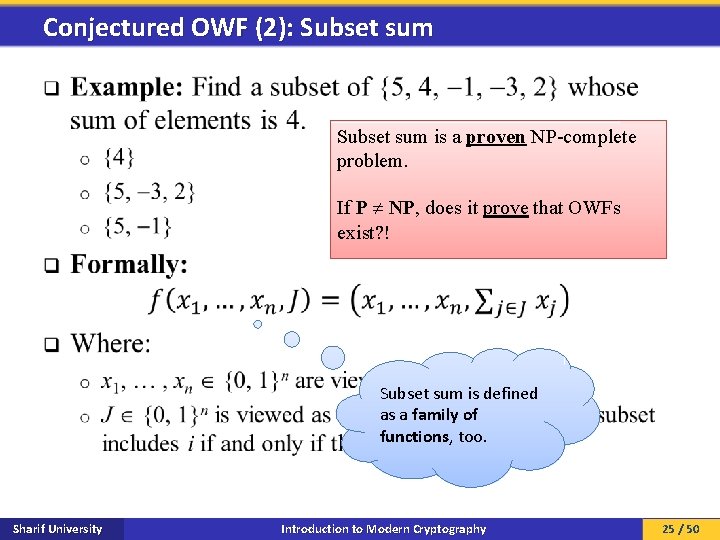
Conjectured OWF (2): Subset sum q Subset sum is a proven NP-complete problem. If P NP, does it prove that OWFs exist? ! Subset sum is defined as a family of functions, too. Sharif University Introduction to Modern Cryptography 25 / 50
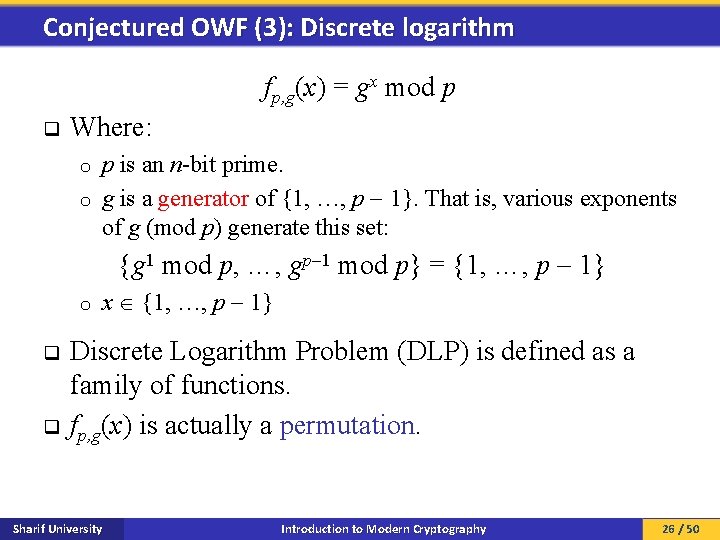
Conjectured OWF (3): Discrete logarithm fp, g(x) = gx mod p q Where: p is an n-bit prime. o g is a generator of {1, …, p 1}. That is, various exponents of g (mod p) generate this set: o {g 1 mod p, …, gp 1 mod p} = {1, …, p 1} o q q x {1, …, p 1} Discrete Logarithm Problem (DLP) is defined as a family of functions. fp, g(x) is actually a permutation. Sharif University Introduction to Modern Cryptography 26 / 50
One-way Permutations OWP Sharif University Introduction to Modern Cryptography 27 / 50
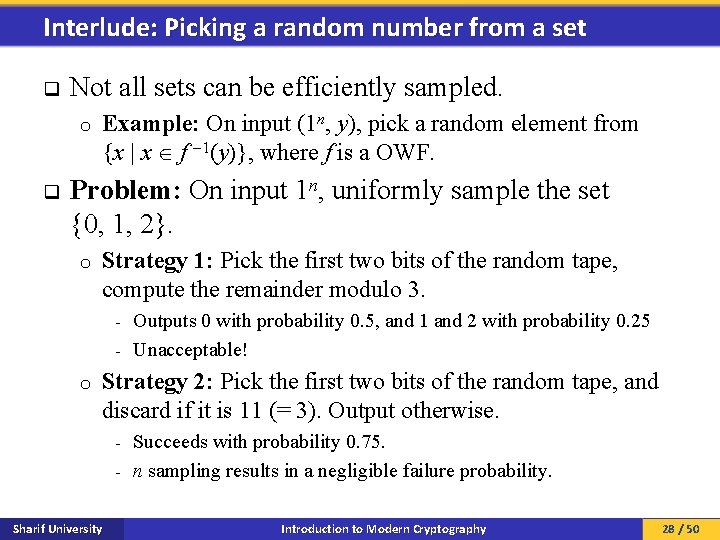
Interlude: Picking a random number from a set q Not all sets can be efficiently sampled. o q Example: On input (1 n, y), pick a random element from {x | x f 1(y)}, where f is a OWF. Problem: On input 1 n, uniformly sample the set {0, 1, 2}. o Strategy 1: Pick the first two bits of the random tape, compute the remainder modulo 3. Outputs 0 with probability 0. 5, and 1 and 2 with probability 0. 25 - Unacceptable! - o Strategy 2: Pick the first two bits of the random tape, and discard if it is 11 (= 3). Output otherwise. Succeeds with probability 0. 75. - n sampling results in a negligible failure probability. - Sharif University Introduction to Modern Cryptography 28 / 50
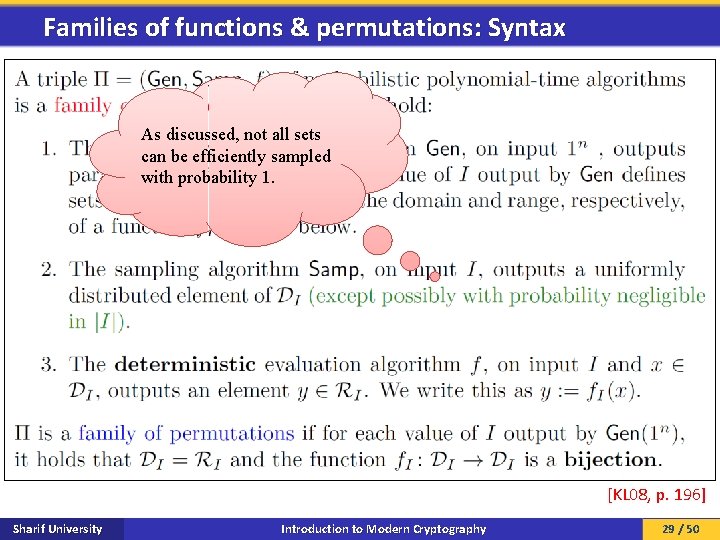
Families of functions & permutations: Syntax As discussed, not all sets can be efficiently sampled with probability 1. [KL 08, p. 196] Sharif University Introduction to Modern Cryptography 29 / 50
![OWFs and OWPs Assignment [KL 08, p. 238], exercise 6. 6: Prove that there OWFs and OWPs Assignment [KL 08, p. 238], exercise 6. 6: Prove that there](http://slidetodoc.com/presentation_image_h/e31adfd5bde488e83c82b7f692ee6a41/image-30.jpg)
OWFs and OWPs Assignment [KL 08, p. 238], exercise 6. 6: Prove that there exist OWFs if and only if there exist families of OWFs. Discuss why your proof does not carry over to the case of OWPs. [KL 08, p. 197] Sharif University Introduction to Modern Cryptography 30 / 50
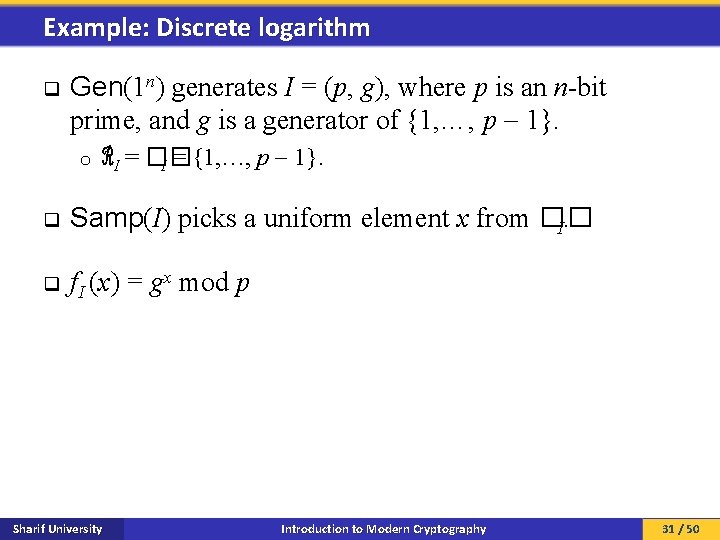
Example: Discrete logarithm q Gen(1 n) generates I = (p, g), where p is an n-bit prime, and g is a generator of {1, …, p 1}. o q ℛI = �� I = {1, …, p 1}. Samp(I) picks a uniform element x from �� I. q f. I (x) = gx mod p Sharif University Introduction to Modern Cryptography 31 / 50
Trapdoor Permutations TDP Sharif University Introduction to Modern Cryptography 32 / 50
![TDP [KL 08, p. 374] Sharif University Introduction to Modern Cryptography 33 / 50 TDP [KL 08, p. 374] Sharif University Introduction to Modern Cryptography 33 / 50](http://slidetodoc.com/presentation_image_h/e31adfd5bde488e83c82b7f692ee6a41/image-33.jpg)
TDP [KL 08, p. 374] Sharif University Introduction to Modern Cryptography 33 / 50
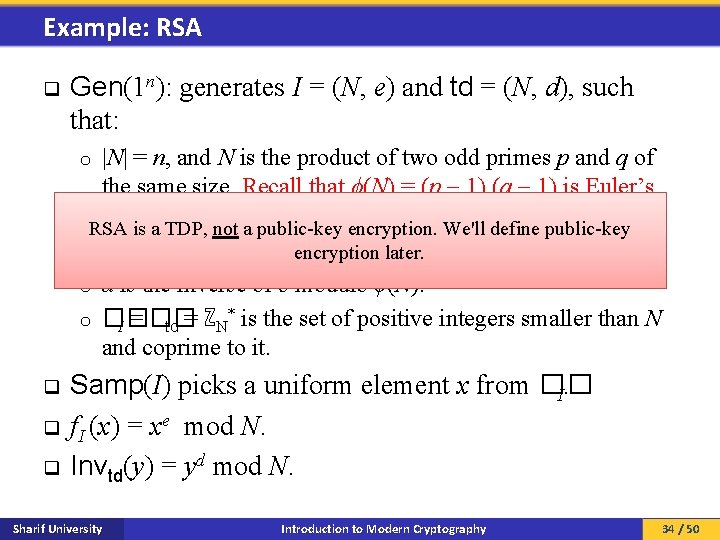
Example: RSA q Gen(1 n): generates I = (N, e) and td = (N, d), such that: |N| = n, and N is the product of two odd primes p and q of the same size. Recall that ϕ(N) = (p 1) (q 1) is Euler’s totient. RSA is a TDP, not a public-key encryption. We'll define public-key o e is a number such that gcd(e, ϕ(N)) = 1. encryption later. o d is the inverse of e modulo ϕ(N). * is the set of positive integers smaller than N o �� = ℤ I td N and coprime to it. o q q q Samp(I) picks a uniform element x from �� I. f. I (x) = xe mod N. Invtd(y) = yd mod N. Sharif University Introduction to Modern Cryptography 34 / 50
Claw-Free Functions/ Permutations CFF / CFP Sharif University Introduction to Modern Cryptography 35 / 50
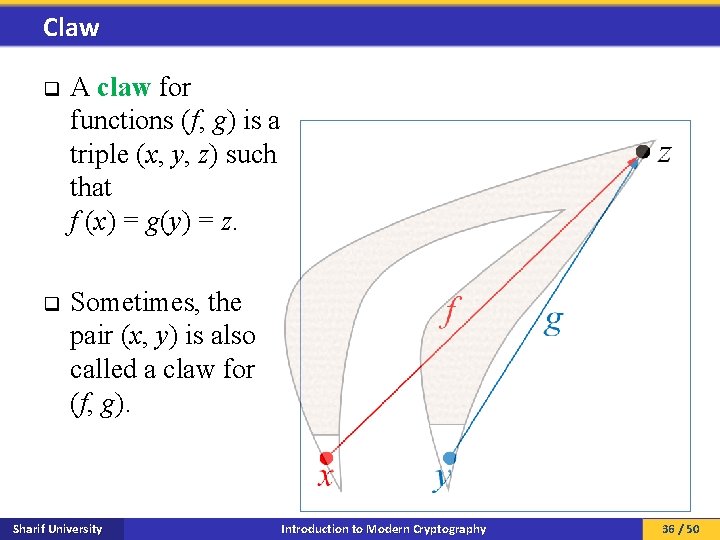
Claw q A claw for functions (f, g) is a triple (x, y, z) such that f (x) = g(y) = z. q Sometimes, the pair (x, y) is also called a claw for (f, g). Sharif University Introduction to Modern Cryptography 36 / 50
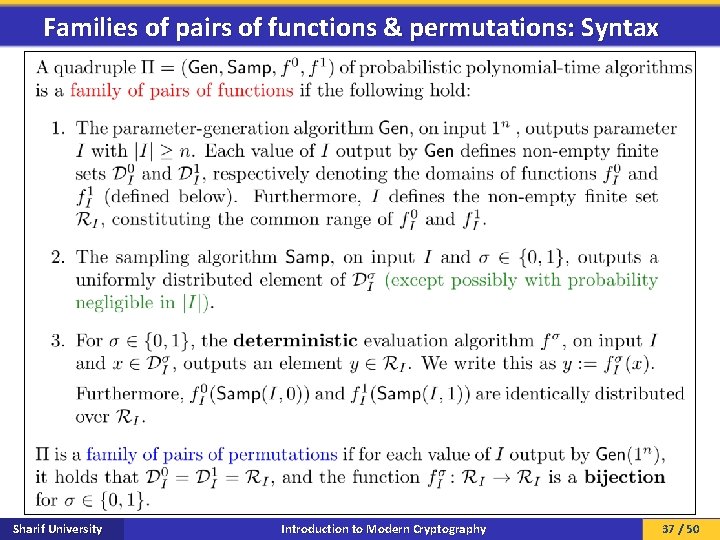
Families of pairs of functions & permutations: Syntax Sharif University Introduction to Modern Cryptography 37 / 50
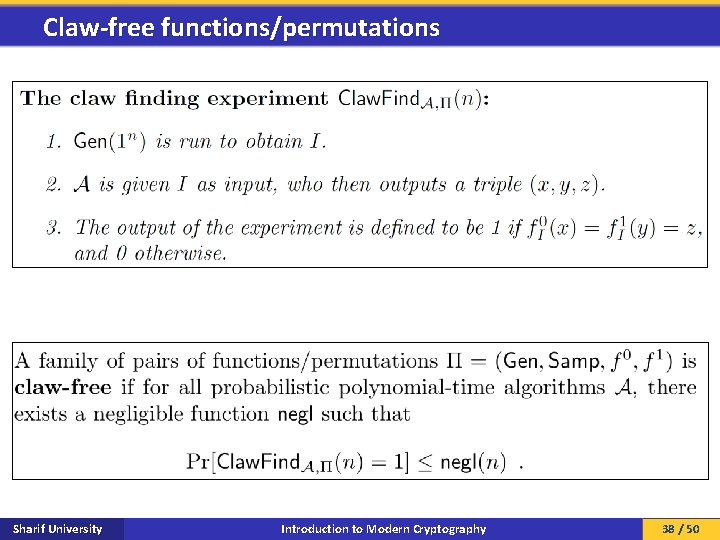
Claw-free functions/permutations Sharif University Introduction to Modern Cryptography 38 / 50
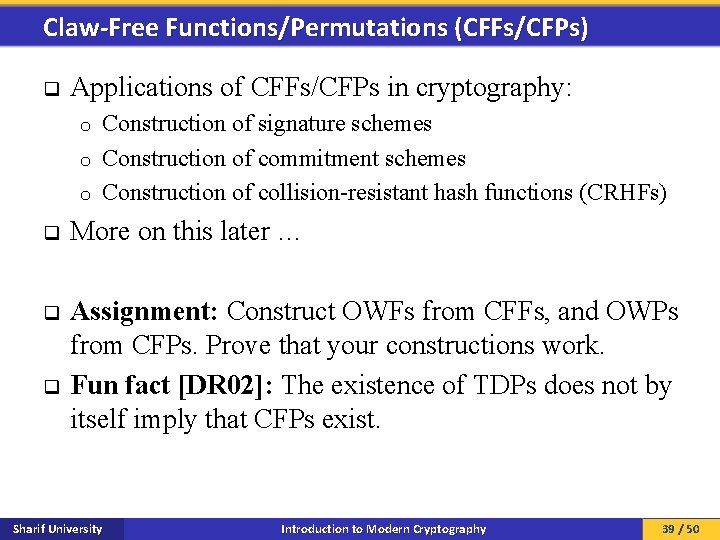
Claw-Free Functions/Permutations (CFFs/CFPs) q Applications of CFFs/CFPs in cryptography: Construction of signature schemes o Construction of commitment schemes o Construction of collision-resistant hash functions (CRHFs) o q More on this later … q Assignment: Construct OWFs from CFFs, and OWPs from CFPs. Prove that your constructions work. Fun fact [DR 02]: The existence of TDPs does not by itself imply that CFPs exist. q Sharif University Introduction to Modern Cryptography 39 / 50
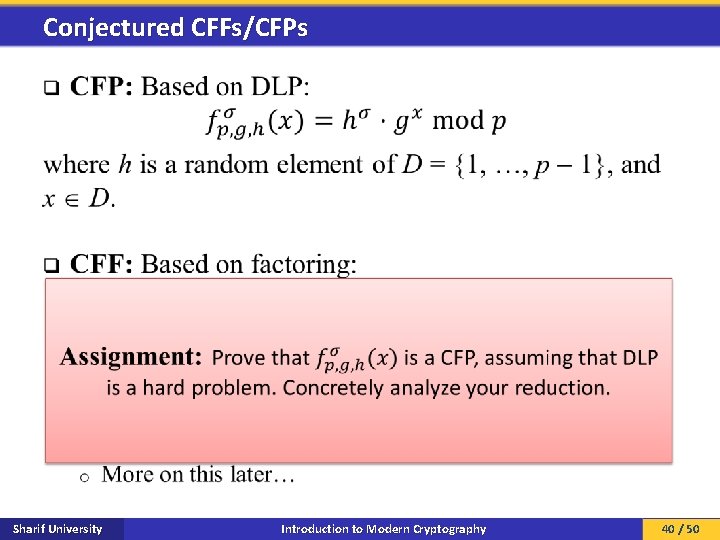
Conjectured CFFs/CFPs q Sharif University Introduction to Modern Cryptography 40 / 50
![Impagliazzo’s five worlds [Imp 95] Sharif University Introduction to Modern Cryptography 41 / 50 Impagliazzo’s five worlds [Imp 95] Sharif University Introduction to Modern Cryptography 41 / 50](http://slidetodoc.com/presentation_image_h/e31adfd5bde488e83c82b7f692ee6a41/image-41.jpg)
Impagliazzo’s five worlds [Imp 95] Sharif University Introduction to Modern Cryptography 41 / 50
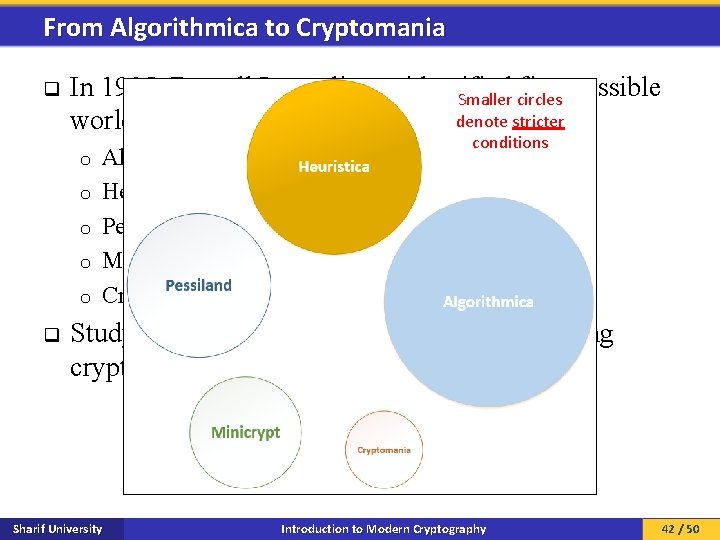
From Algorithmica to Cryptomania q In 1995, Russell Impagliazzo identified five possible Smaller circles denote stricter worlds: o o o q Algorithmica Heuristica Pessiland Minicrypt Cryptomania conditions Studying these worlds can help in understanding cryptography. Sharif University Introduction to Modern Cryptography 42 / 50
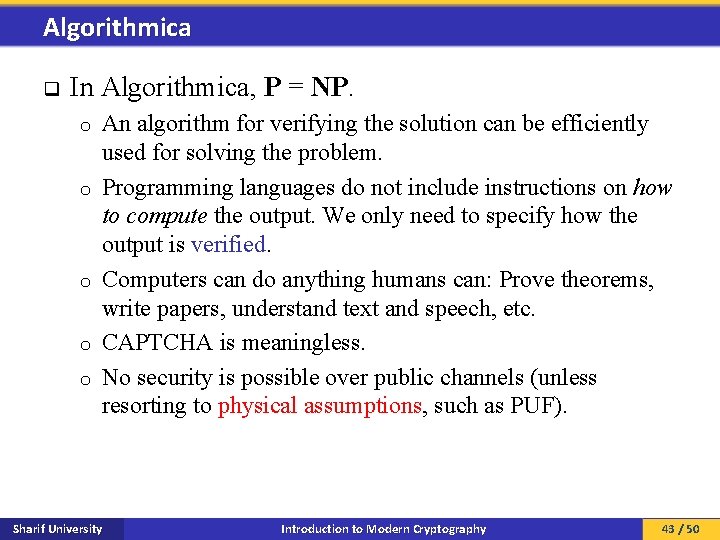
Algorithmica q In Algorithmica, P = NP. o o o An algorithm for verifying the solution can be efficiently used for solving the problem. Programming languages do not include instructions on how to compute the output. We only need to specify how the output is verified. Computers can do anything humans can: Prove theorems, write papers, understand text and speech, etc. CAPTCHA is meaningless. No security is possible over public channels (unless resorting to physical assumptions, such as PUF). Sharif University Introduction to Modern Cryptography 43 / 50
Heuristica q In Heuristica, P NP, but NP is not hard on average. NP is hard in the worst case. o If we choose any problem at random (or based on any distribution), it will be easy with very high probability. o Finding a hard problem is itself intractable! o In terms of security/cryptography, same as Algorithmica. o Sharif University Introduction to Modern Cryptography 44 / 50
Pessiland q In Pessiland, there are hard-on-average problems but no OWFs. Easy to generate hard NP problems. o No way to generate hard solved NP problems. o Why? o Let Gen(1 n) be the algorithm generating hard NP problems with OWFs are essential for their solution. most cryptographic tasks - If you have the randomness of Gen, you can generate the solution. [IL 89]. n - Gen(1 ) is not an OWF (they don’t exist). - As such, given the problem, one can invert Gen to find the randomness. - No known way of making use of the hard problems of Pessiland in cryptography. o A problem that no one knows the answer to cannot be used to distinguish legitimate users from adversaries. o Sharif University Introduction to Modern Cryptography 45 / 50
Minicrypt q In Minicrypt, OWFs exist, but private communications over public channels (secret-key agreement) with strangers is impossible. Pseudo-random generators exist o Digital signatures exist o - Identification and message authentication is possible Secret-key agreement is possible using pre-shared secrets (i. e. , no strangers) o Zero-knowledge protocols exist o BUT: o E-Voting is impossible - Anonymous cash is impossible - … - Sharif University Introduction to Modern Cryptography 46 / 50
Cryptomania q In Cryptomania, secret-key agreement with strangers is possible. Groups of people can jointly agree on a secret over a public channel. o The group can agree to jointly compute an arbitrary function of secret inputs without compromising their secrets. o E-Voting is possible - Anonymous cash is possible - q q If TDPs exist, we are in Cryptomania. How about OWPs? o Next slides… Sharif University Introduction to Modern Cryptography 47 / 50
![Impagliazzo–Rudich theorem [IR 88] Sharif University Introduction to Modern Cryptography 48 / 50 Impagliazzo–Rudich theorem [IR 88] Sharif University Introduction to Modern Cryptography 48 / 50](http://slidetodoc.com/presentation_image_h/e31adfd5bde488e83c82b7f692ee6a41/image-48.jpg)
Impagliazzo–Rudich theorem [IR 88] Sharif University Introduction to Modern Cryptography 48 / 50
Limits on Provable Consequences of OWPs q q q We believe OWPs exist. We believe secret-key agreement (with strangers) is possible. Can we construct SKAs from OWPs? Impagliazzo & Rudich provide strong evidence that “ OWP SKA” is not provable by standard techniques. Standard technique: A normal reduction (which uses the adversary as a subroutine). [IR 88] shows that proving “ OWP SKA” is as hard as proving “P NP”. Sharif University Introduction to Modern Cryptography 49 / 50
References q q Sections 6. 1, 7. 4. 1, and 10. 7 of [KL 08] Sections 1. 3 and chapter 2 of [Gol 01] [DR 02] Y. Dodis and L. Reyzin. On the Power of Claw-Free Permutations. In SCN ’ 02, 2002. [Gol 01] O. Goldreich. Foundations of Cryptography Volume 1: Basic Tools. Cambridge University Press, 2001. [Imp 95] R. Impagliazzo. A Personal View of Average-Case Complexity. In SCT ’ 95, 1995. [IL 89] R. Impagliazzo and M. Luby. One-way Functions are Essential for Complexity Based Cryptography. In FOCS ’ 89, 1989. [IR 88] R. Impagliazzo and S. Rudich. Limits on the Provable Consequences of One-way Permutations. In CRYPTO ’ 88, 1988. [KL 08] J. Katz and Y. Lindell. Introduction to Modern Cryptography: Principles and Protocols. CRC Press, 2007. Sharif University Introduction to Modern Cryptography 50 / 50
- Slides: 50