Chapter 2 Application Layer Computer Networking A Top
![Electronic Mail: SMTP [RFC 2821] r uses TCP to reliably transfer email message from Electronic Mail: SMTP [RFC 2821] r uses TCP to reliably transfer email message from](https://slidetodoc.com/presentation_image_h2/4a99530aa69bf381732372294b4d87d9/image-9.jpg)
- Slides: 49
Chapter 2 Application Layer Computer Networking: A Top Down Approach , 5 th edition. Jim Kurose, Keith Ross Addison-Wesley, July 2009. 2: Application Layer 1
Chapter 2: Application layer r 2. 1 Principles of network applications r 2. 2 Web and HTTP r 2. 3 FTP r 2. 4 Electronic Mail m SMTP, POP 3, IMAP r 2. 5 DNS r 2. 6 P 2 P file sharing r 2. 7 Socket programming with TCP r 2. 8 Socket programming with UDP r 2. 9 Building a Web server 2: Application Layer 2
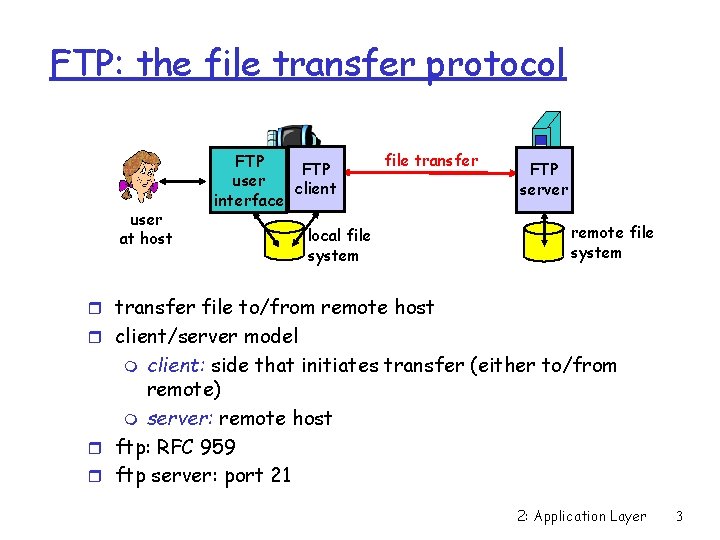
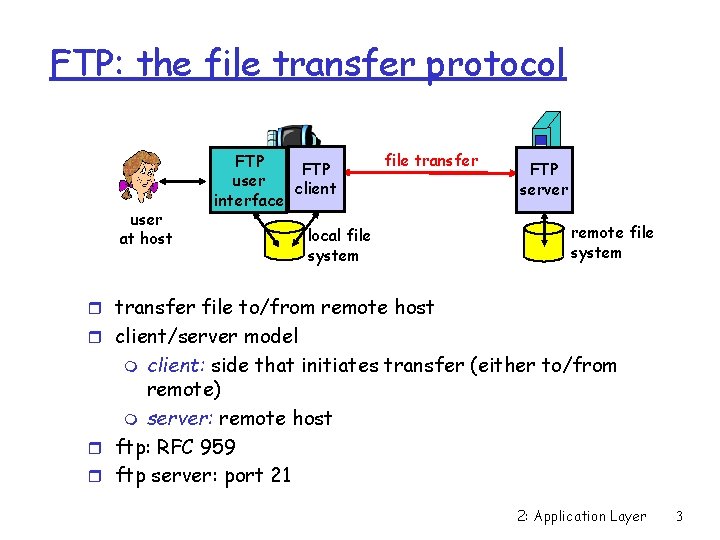
FTP: the file transfer protocol user at host FTP user client interface file transfer local file system FTP server remote file system r transfer file to/from remote host r client/server model client: side that initiates transfer (either to/from remote) m server: remote host r ftp: RFC 959 r ftp server: port 21 m 2: Application Layer 3
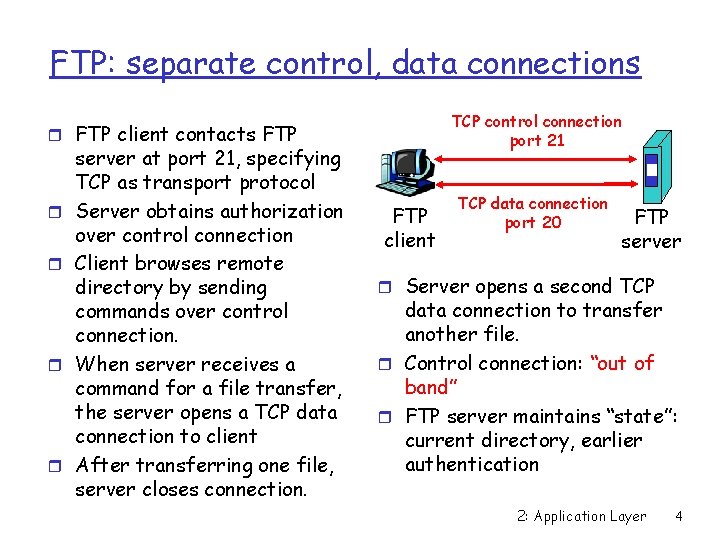
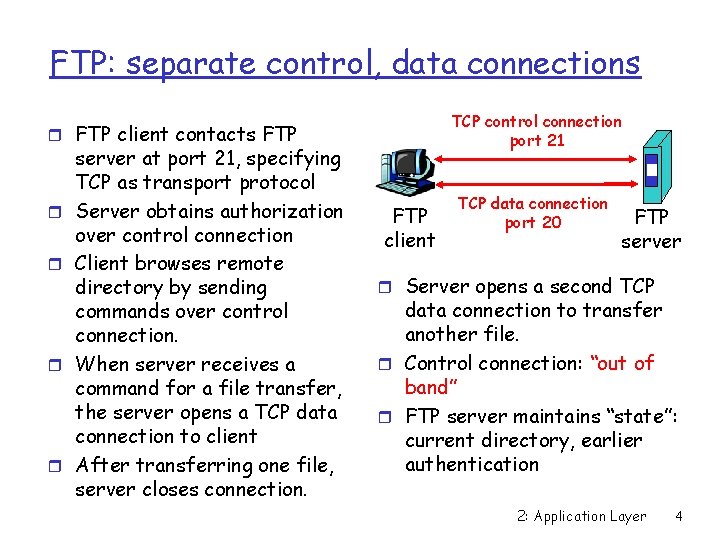
FTP: separate control, data connections TCP control connection port 21 r FTP client contacts FTP r r server at port 21, specifying TCP as transport protocol Server obtains authorization over control connection Client browses remote directory by sending commands over control connection. When server receives a command for a file transfer, the server opens a TCP data connection to client After transferring one file, server closes connection. FTP client TCP data connection port 20 FTP server r Server opens a second TCP data connection to transfer another file. r Control connection: “out of band” r FTP server maintains “state”: current directory, earlier authentication 2: Application Layer 4
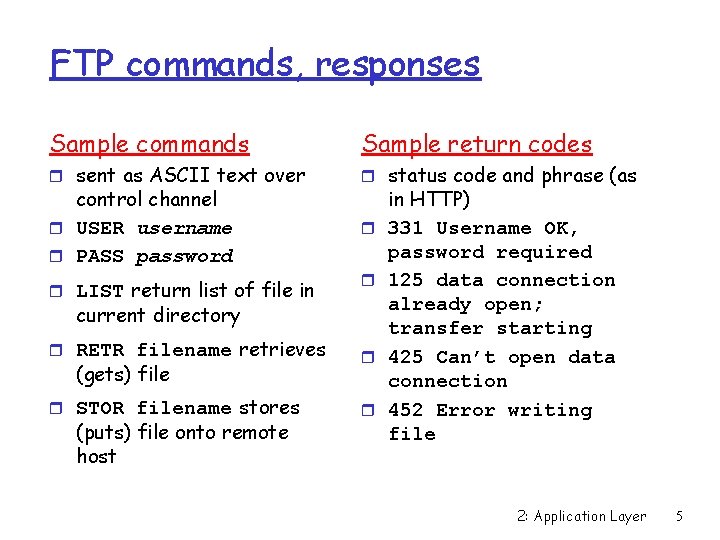
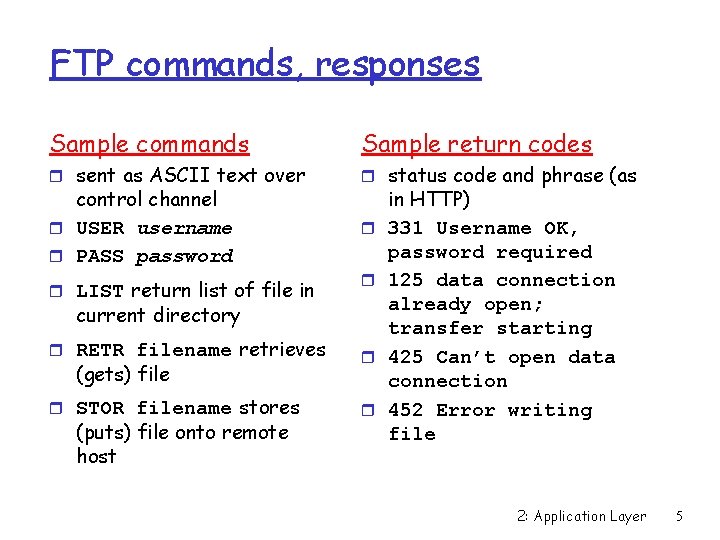
FTP commands, responses Sample commands Sample return codes r sent as ASCII text over r status code and phrase (as control channel r USER username r PASS password r LIST return list of file in r r current directory r RETR filename retrieves r r STOR filename stores r (gets) file (puts) file onto remote host in HTTP) 331 Username OK, password required 125 data connection already open; transfer starting 425 Can’t open data connection 452 Error writing file 2: Application Layer 5
Chapter 2: Application layer r 2. 1 Principles of network applications r 2. 2 Web and HTTP r 2. 3 FTP r 2. 4 Electronic Mail m SMTP, POP 3, IMAP r 2. 5 DNS r 2. 6 P 2 P file sharing r 2. 7 Socket programming with TCP r 2. 8 Socket programming with UDP r 2. 9 Building a Web server 2: Application Layer 6
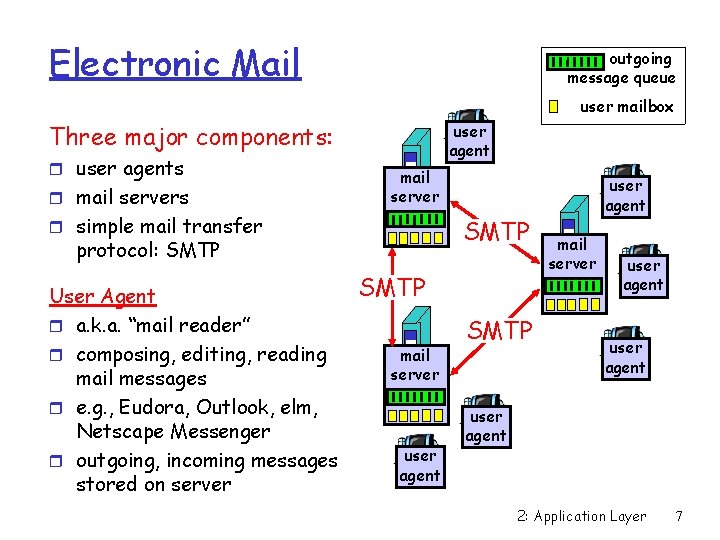
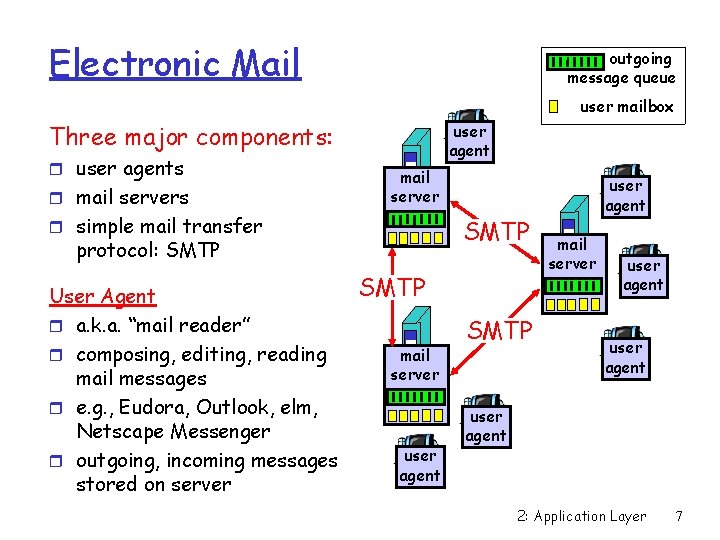
Electronic Mail outgoing message queue user mailbox Three major components: r user agents r mail servers user agent mail server r simple mail transfer SMTP protocol: SMTP User Agent r a. k. a. “mail reader” r composing, editing, reading mail messages r e. g. , Eudora, Outlook, elm, Netscape Messenger r outgoing, incoming messages stored on server SMTP mail server user agent SMTP user agent mail server user agent 2: Application Layer 7
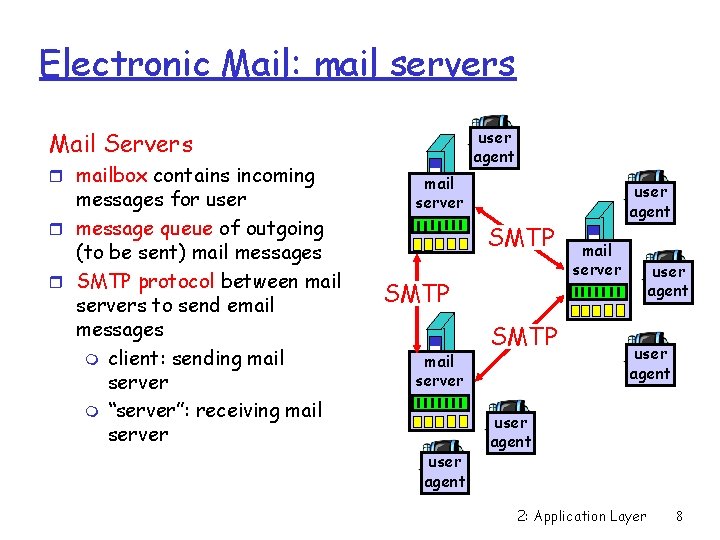
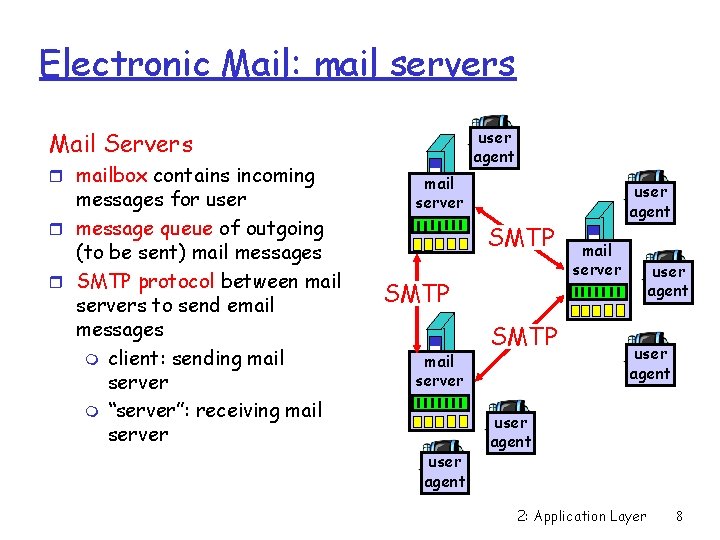
Electronic Mail: mail servers user agent Mail Servers r mailbox contains incoming messages for user r message queue of outgoing (to be sent) mail messages r SMTP protocol between mail servers to send email messages m client: sending mail server m “server”: receiving mail server SMTP mail server user agent SMTP user agent mail server user agent 2: Application Layer 8
![Electronic Mail SMTP RFC 2821 r uses TCP to reliably transfer email message from Electronic Mail: SMTP [RFC 2821] r uses TCP to reliably transfer email message from](https://slidetodoc.com/presentation_image_h2/4a99530aa69bf381732372294b4d87d9/image-9.jpg)
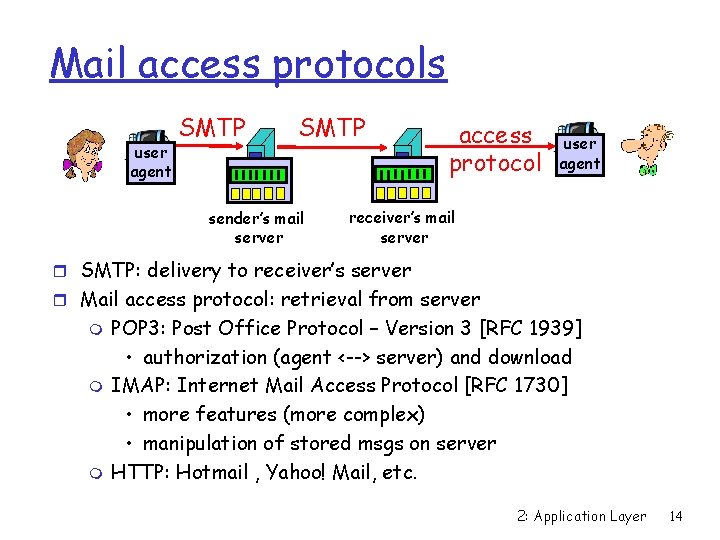
Electronic Mail: SMTP [RFC 2821] r uses TCP to reliably transfer email message from client to server, port 25 r direct transfer: sending server to receiving server r three phases of transfer m handshaking (greeting) m transfer of messages m closure r command/response interaction m commands: ASCII text m response: status code and phrase r Messages must be in 7 -bit ASCII 2: Application Layer 9
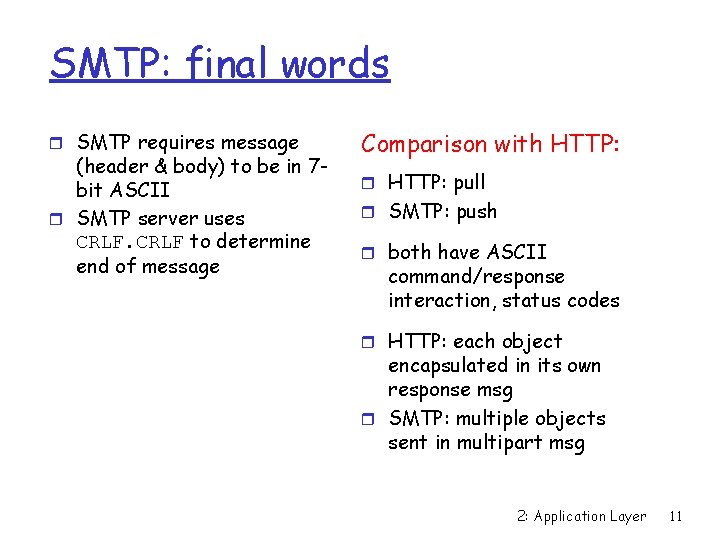
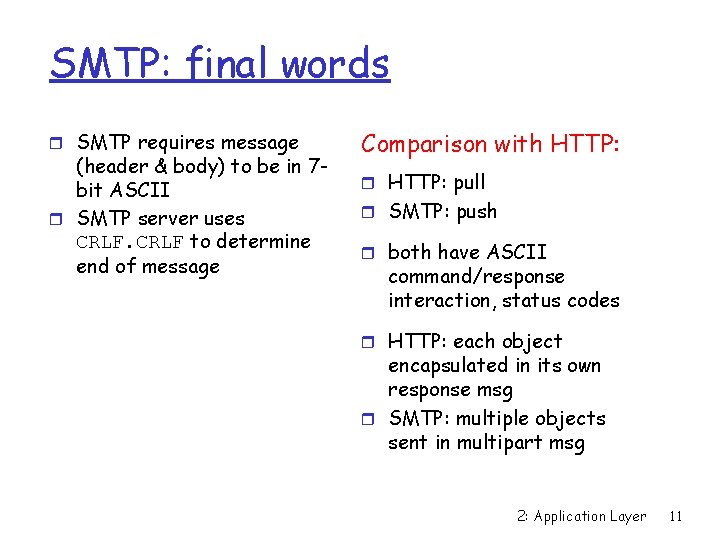
Scenario: Alice sends message to Bob 4) SMTP client sends Alice’s message over the TCP connection 5) Bob’s mail server places the message in Bob’s mailbox 6) Bob invokes his user agent to read message 1) Alice uses UA to compose message and “to” bob@someschool. edu 2) Alice’s UA sends message to her mail server; message placed in message queue 3) Client side of SMTP opens TCP connection with Bob’s mail server 1 user agent 2 mail server 3 mail server 4 5 6 user agent 2: Application Layer 10
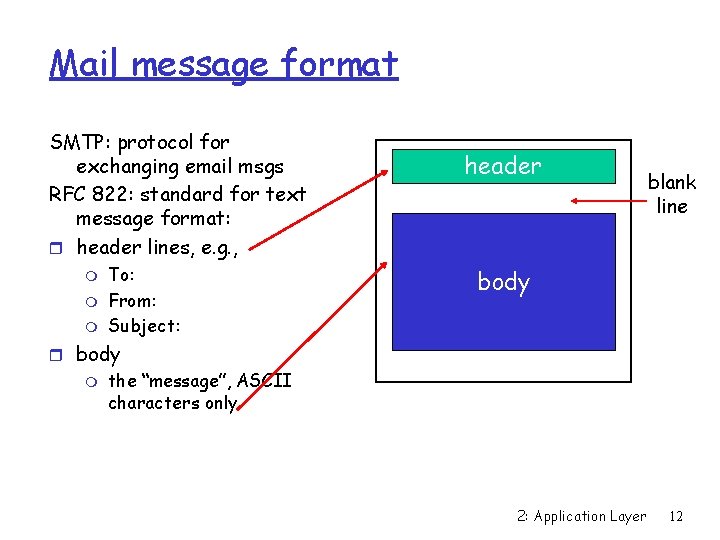
SMTP: final words r SMTP requires message (header & body) to be in 7 bit ASCII r SMTP server uses CRLF to determine end of message Comparison with HTTP: r HTTP: pull r SMTP: push r both have ASCII command/response interaction, status codes r HTTP: each object encapsulated in its own response msg r SMTP: multiple objects sent in multipart msg 2: Application Layer 11
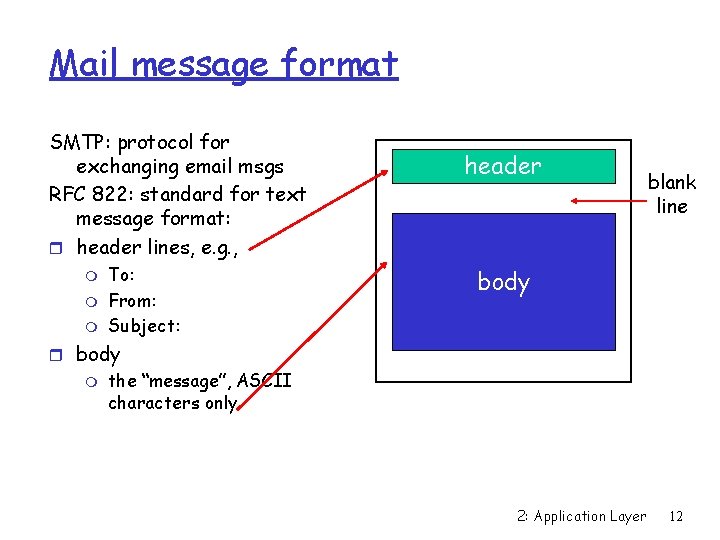
Mail message format SMTP: protocol for exchanging email msgs RFC 822: standard for text message format: r header lines, e. g. , m m m To: From: Subject: header blank line body r body m the “message”, ASCII characters only 2: Application Layer 12
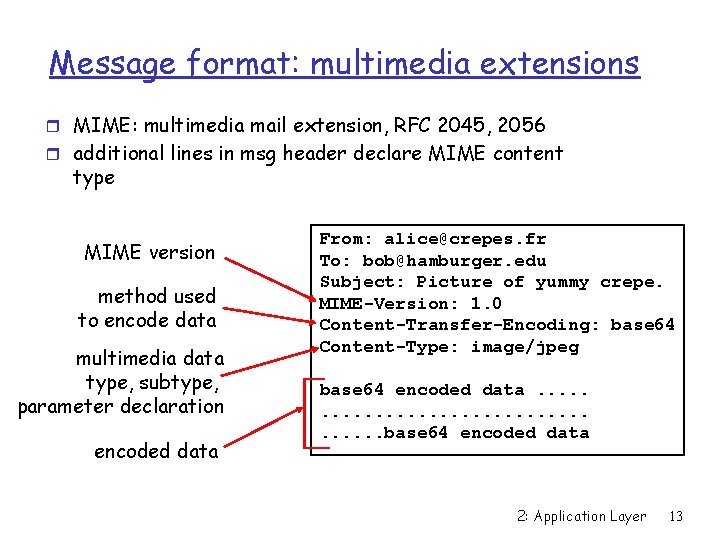
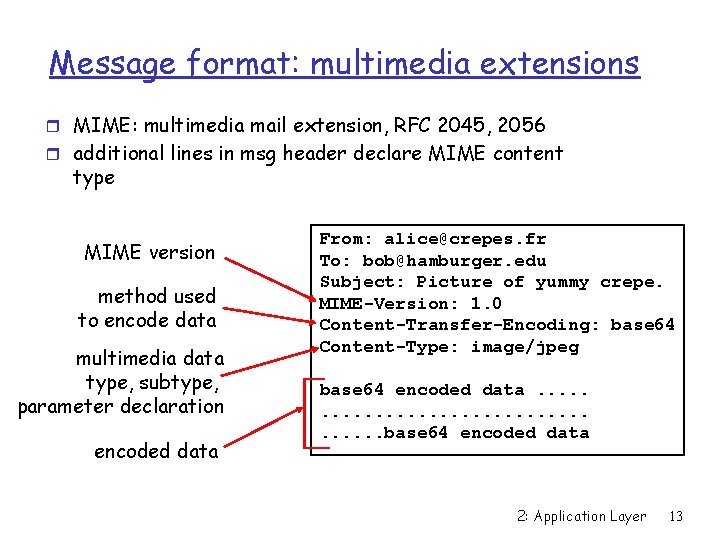
Message format: multimedia extensions r MIME: multimedia mail extension, RFC 2045, 2056 r additional lines in msg header declare MIME content type MIME version method used to encode data multimedia data type, subtype, parameter declaration encoded data From: alice@crepes. fr To: bob@hamburger. edu Subject: Picture of yummy crepe. MIME-Version: 1. 0 Content-Transfer-Encoding: base 64 Content-Type: image/jpeg base 64 encoded data. . . . . base 64 encoded data 2: Application Layer 13
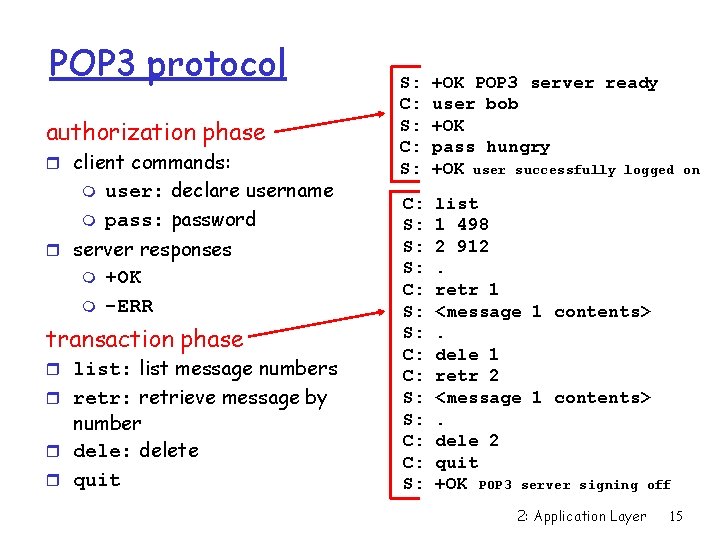
Mail access protocols user agent SMTP sender’s mail server access protocol user agent receiver’s mail server r SMTP: delivery to receiver’s server r Mail access protocol: retrieval from server m m m POP 3: Post Office Protocol – Version 3 [RFC 1939] • authorization (agent <--> server) and download IMAP: Internet Mail Access Protocol [RFC 1730] • more features (more complex) • manipulation of stored msgs on server HTTP: Hotmail , Yahoo! Mail, etc. 2: Application Layer 14
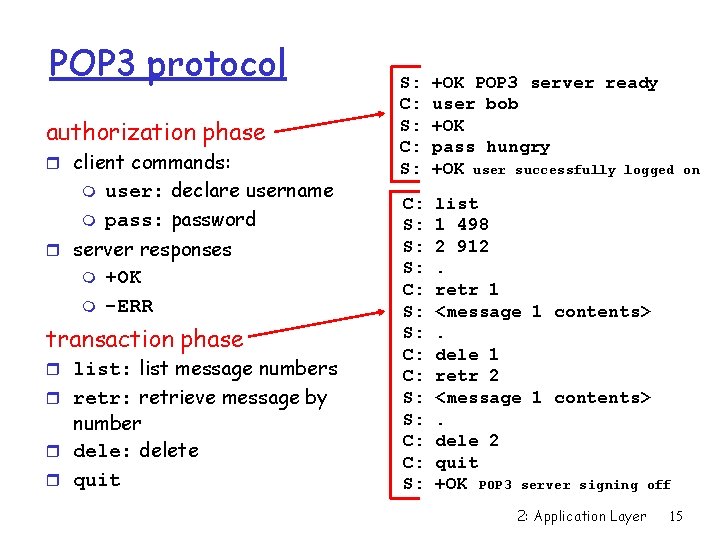
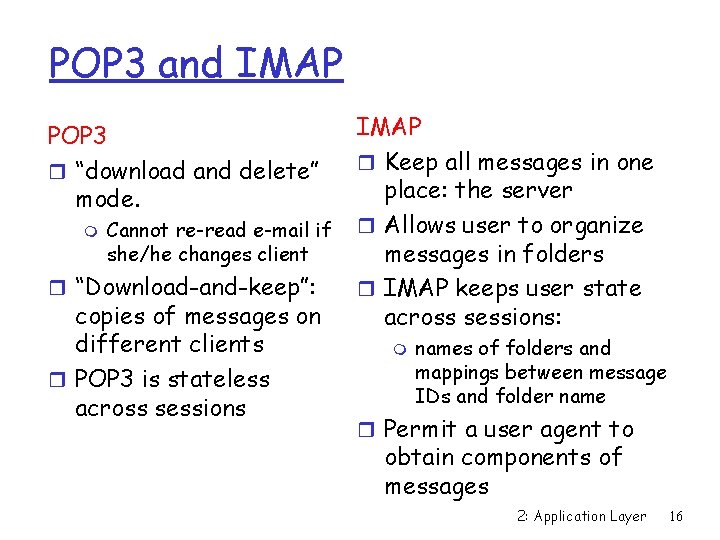
POP 3 protocol authorization phase r client commands: m m user: declare username pass: password r server responses m m +OK -ERR transaction phase r list: list message numbers r retr: retrieve message by number r dele: delete r quit S: C: S: +OK POP 3 server ready user bob +OK pass hungry +OK user successfully logged C: S: S: S: C: C: S: list 1 498 2 912. retr 1 <message 1 contents>. dele 1 retr 2 <message 1 contents>. dele 2 quit +OK POP 3 server signing off 2: Application Layer 15 on
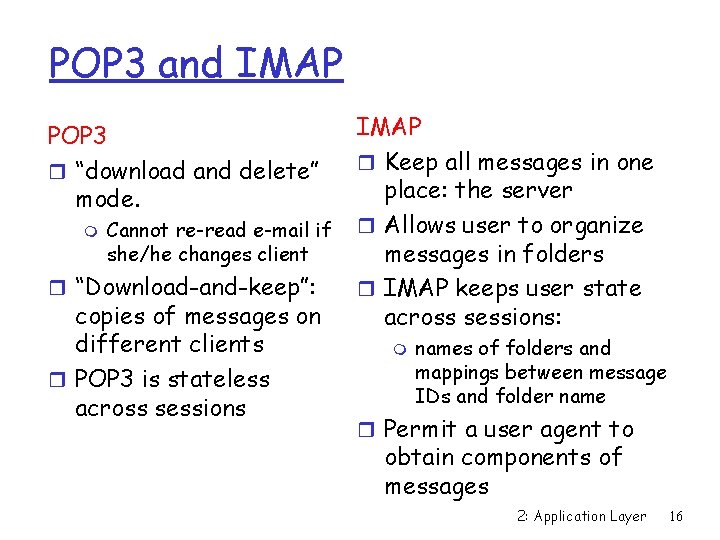
POP 3 and IMAP POP 3 r “download and delete” mode. m Cannot re-read e-mail if she/he changes client r “Download-and-keep”: copies of messages on different clients r POP 3 is stateless across sessions IMAP r Keep all messages in one place: the server r Allows user to organize messages in folders r IMAP keeps user state across sessions: m names of folders and mappings between message IDs and folder name r Permit a user agent to obtain components of messages 2: Application Layer 16
Chapter 2: Application layer r 2. 1 Principles of network applications r 2. 2 Web and HTTP r 2. 3 FTP r 2. 4 Electronic Mail m SMTP, POP 3, IMAP r 2. 5 DNS r 2. 6 P 2 P file sharing r 2. 7 Socket programming with TCP r 2. 8 Socket programming with UDP r 2. 9 Building a Web server 2: Application Layer 17
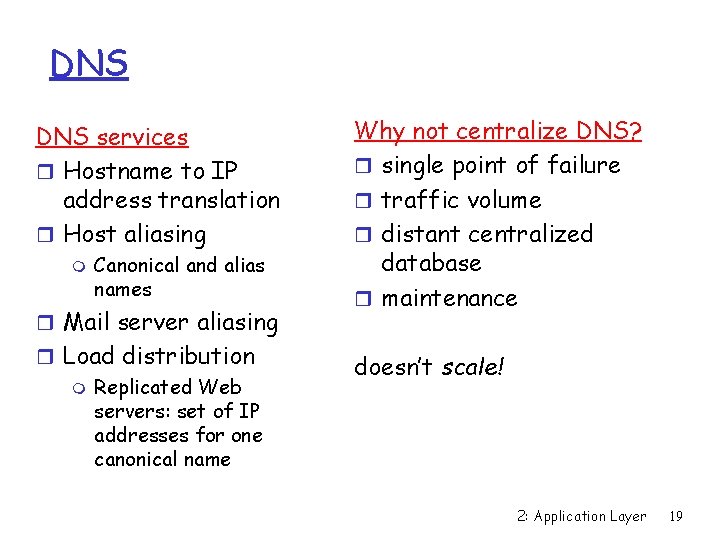
DNS: Domain Name System People: many identifiers: m SSN, name, passport # Internet hosts, routers: m m IP address (32 bit) used for addressing datagrams “name”, e. g. , www. yahoo. com - used by humans Q: map between IP addresses and name ? Domain Name System: r distributed database implemented in hierarchy of many name servers r application-layer protocol host, routers, name servers to communicate to resolve names (address/name translation) m core Internet function, implemented as application -layer protocol 2: Application Layer 18
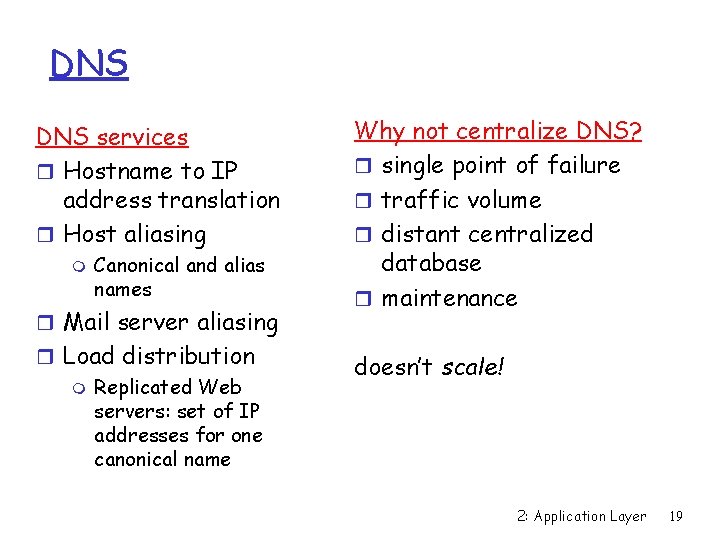
DNS services r Hostname to IP address translation r Host aliasing m Canonical and alias names r Mail server aliasing r Load distribution m Replicated Web servers: set of IP addresses for one canonical name Why not centralize DNS? r single point of failure r traffic volume r distant centralized database r maintenance doesn’t scale! 2: Application Layer 19
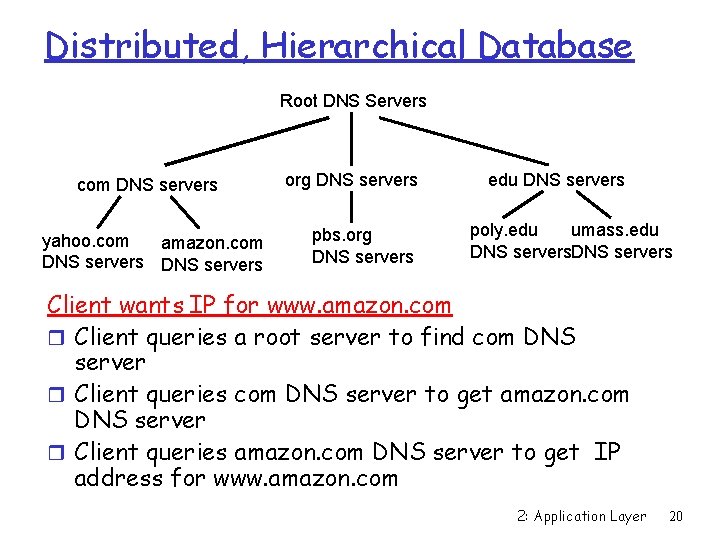
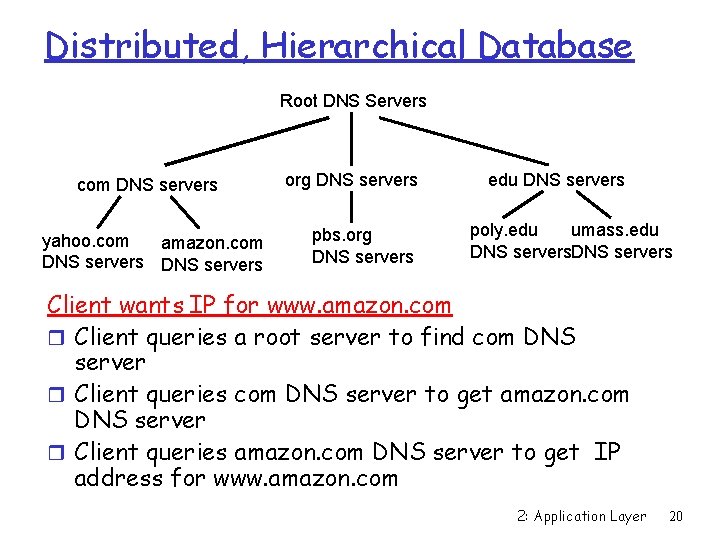
Distributed, Hierarchical Database Root DNS Servers com DNS servers yahoo. com amazon. com DNS servers org DNS servers pbs. org DNS servers edu DNS servers poly. edu umass. edu DNS servers Client wants IP for www. amazon. com r Client queries a root server to find com DNS server r Client queries com DNS server to get amazon. com DNS server r Client queries amazon. com DNS server to get IP address for www. amazon. com 2: Application Layer 20
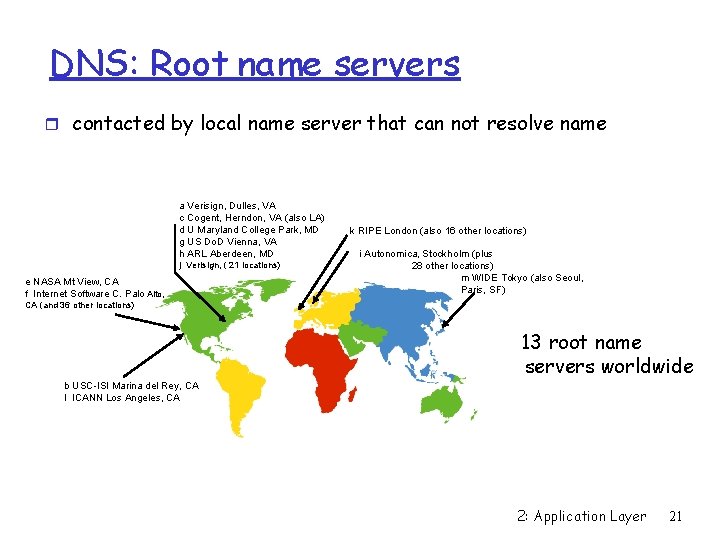
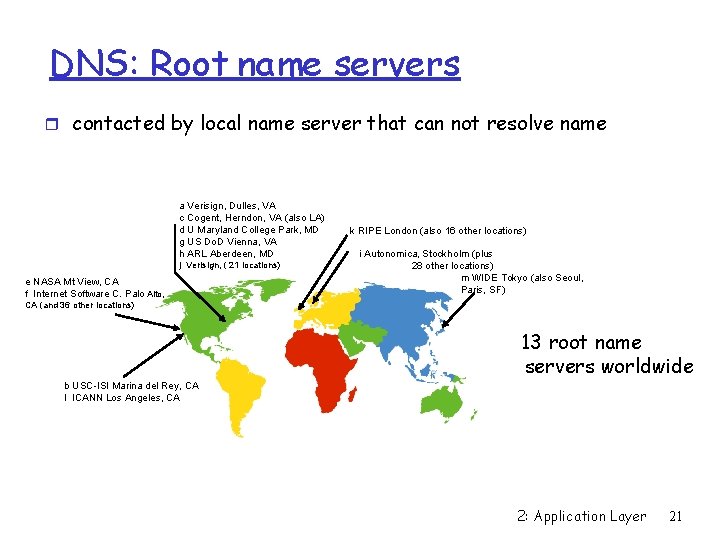
DNS: Root name servers r contacted by local name server that can not resolve name a Verisign, Dulles, VA c Cogent, Herndon, VA (also LA) d U Maryland College Park, MD g US Do. D Vienna, VA h ARL Aberdeen, MD j Verisign, ( 21 locations) e NASA Mt View, CA f Internet Software C. Palo Alto, k RIPE London (also 16 other locations) i Autonomica, Stockholm (plus 28 other locations) m WIDE Tokyo (also Seoul, Paris, SF) CA (and 36 other locations) 13 root name servers worldwide b USC-ISI Marina del Rey, CA l ICANN Los Angeles, CA 2: Application Layer 21
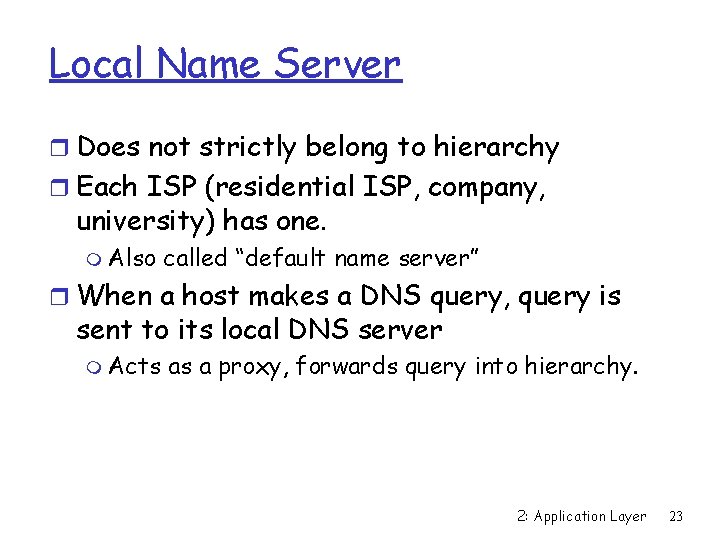
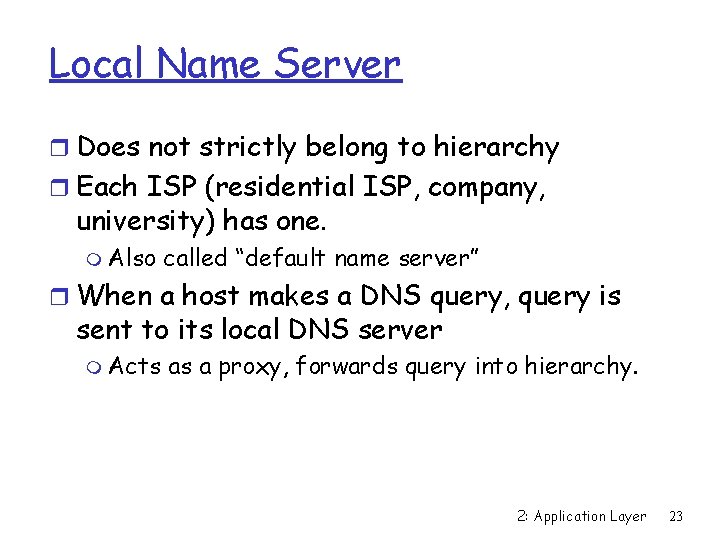
TLD and Authoritative Servers r Top-level domain (TLD) servers: responsible for com, org, net, edu, etc, and all top-level country domains uk, fr, ca, jp. m Network solutions maintains servers for com TLD m Educause for edu TLD r Authoritative DNS servers: organization’s DNS servers, providing authoritative hostname to IP mappings for organization’s servers (e. g. , Web and mail). m Can be maintained by organization or service provider 2: Application Layer 22
Local Name Server r Does not strictly belong to hierarchy r Each ISP (residential ISP, company, university) has one. m Also called “default name server” r When a host makes a DNS query, query is sent to its local DNS server m Acts as a proxy, forwards query into hierarchy. 2: Application Layer 23
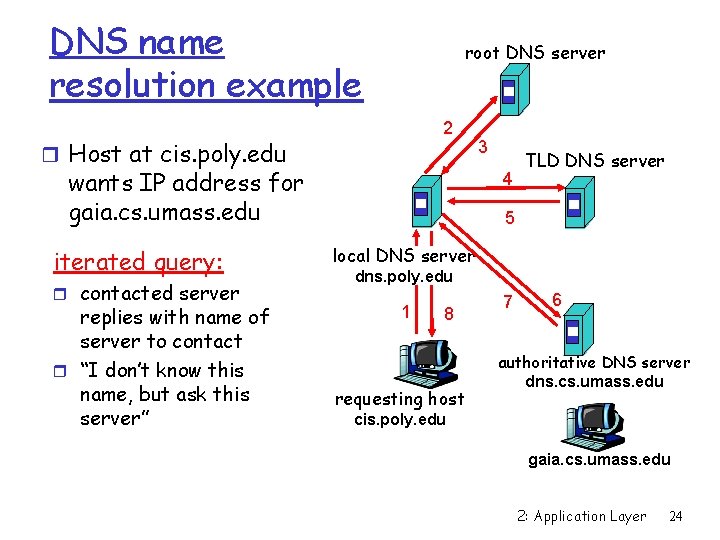
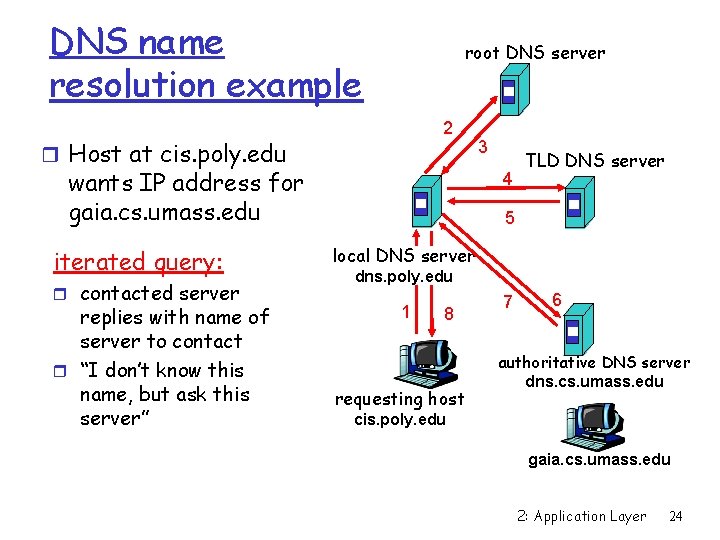
DNS name resolution example root DNS server 2 r Host at cis. poly. edu wants IP address for gaia. cs. umass. edu iterated query: r contacted server replies with name of server to contact r “I don’t know this name, but ask this server” 3 4 TLD DNS server 5 local DNS server dns. poly. edu 1 8 requesting host 7 6 authoritative DNS server dns. cs. umass. edu cis. poly. edu gaia. cs. umass. edu 2: Application Layer 24
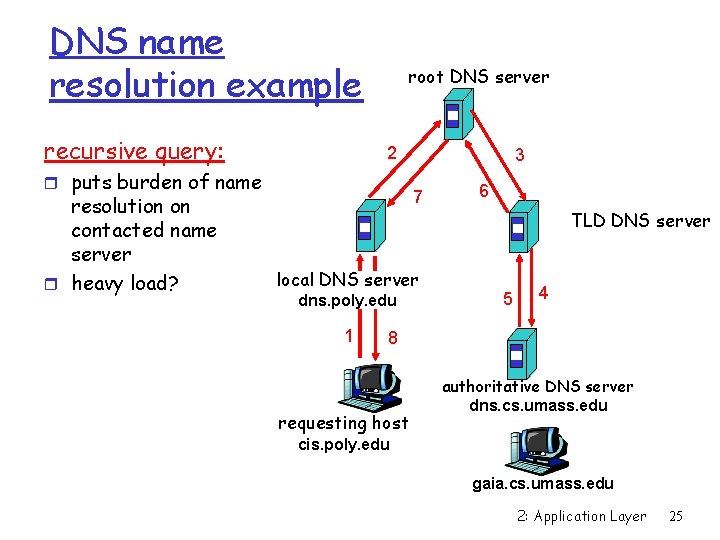
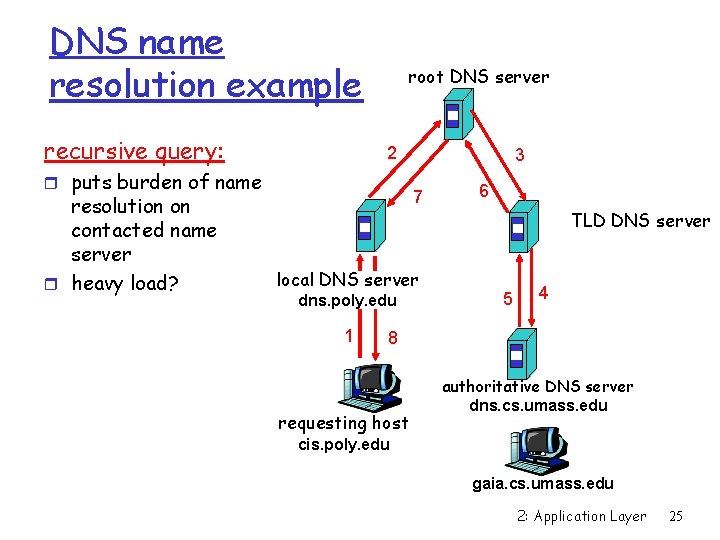
DNS name resolution example recursive query: root DNS server 2 r puts burden of name resolution on contacted name server r heavy load? 3 7 local DNS server dns. poly. edu 1 6 TLD DNS server 5 4 8 requesting host authoritative DNS server dns. cs. umass. edu cis. poly. edu gaia. cs. umass. edu 2: Application Layer 25
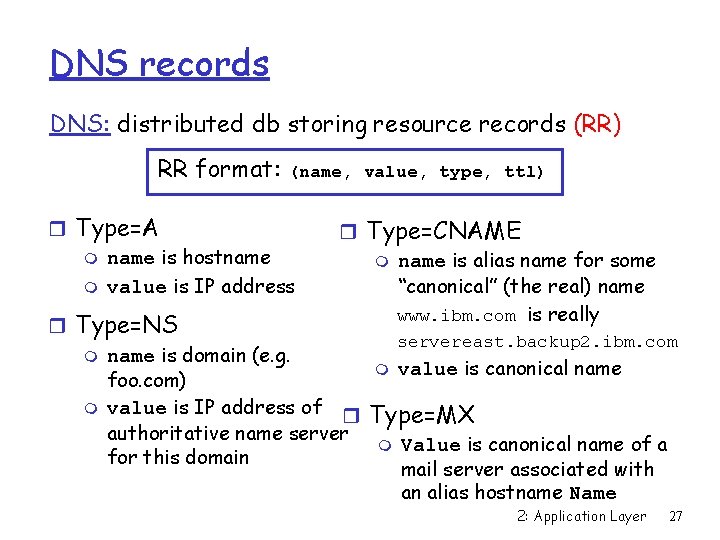
DNS: caching and updating records r once (any) name server learns mapping, it caches mapping m cache entries timeout (disappear) after some time m TLD servers typically cached in local name servers • Thus root name servers not often visited r update/notify mechanisms under design by IETF m RFC 2136 2: Application Layer 26
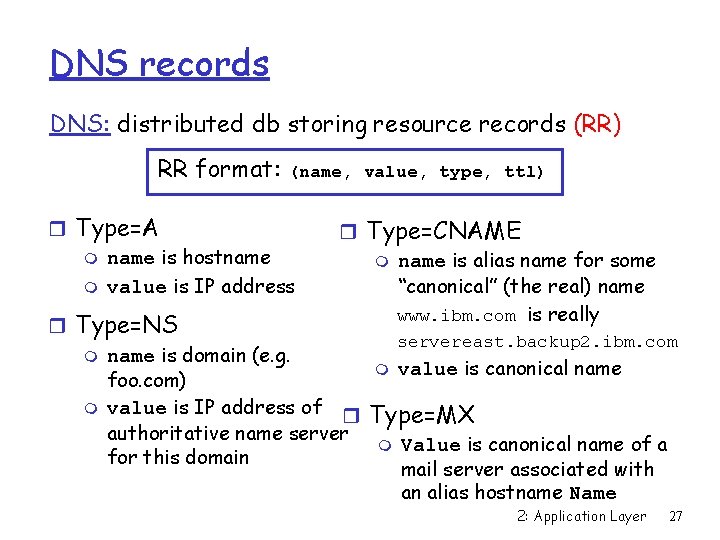
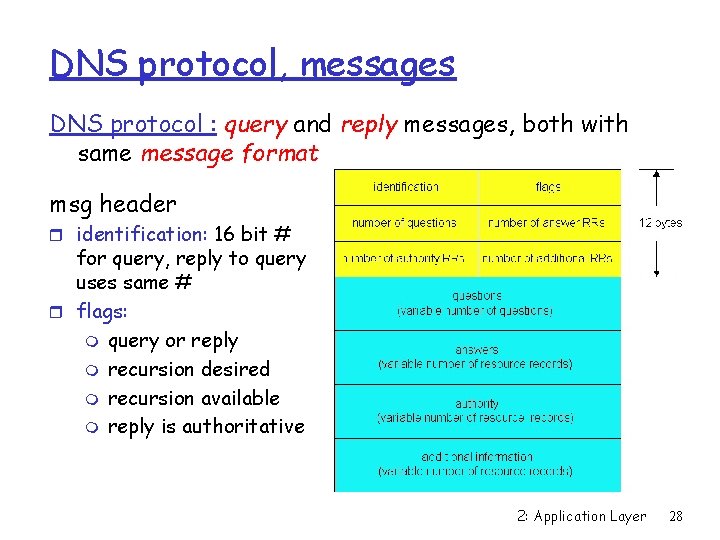
DNS records DNS: distributed db storing resource records (RR) RR format: (name, value, type, ttl) r Type=A m name is hostname m value is IP address r Type=CNAME m name is alias name for some “canonical” (the real) name www. ibm. com is really r Type=NS servereast. backup 2. ibm. com m name is domain (e. g. m value is canonical name foo. com) m value is IP address of r Type=MX authoritative name server m Value is canonical name of a for this domain mail server associated with an alias hostname Name 2: Application Layer 27
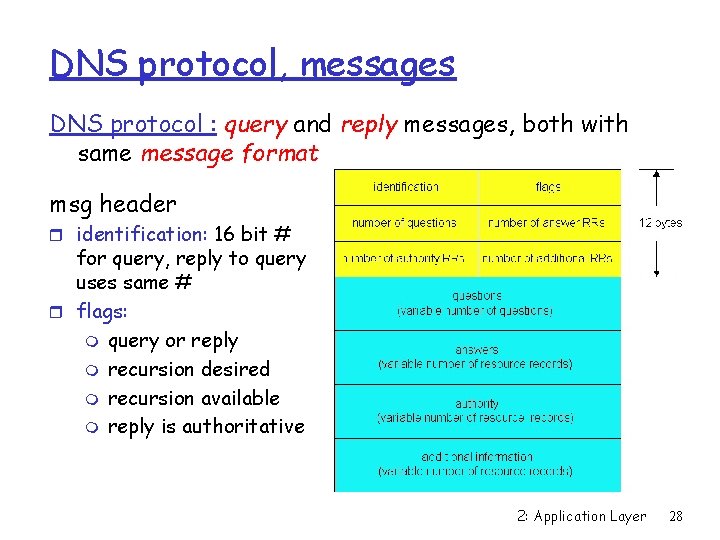
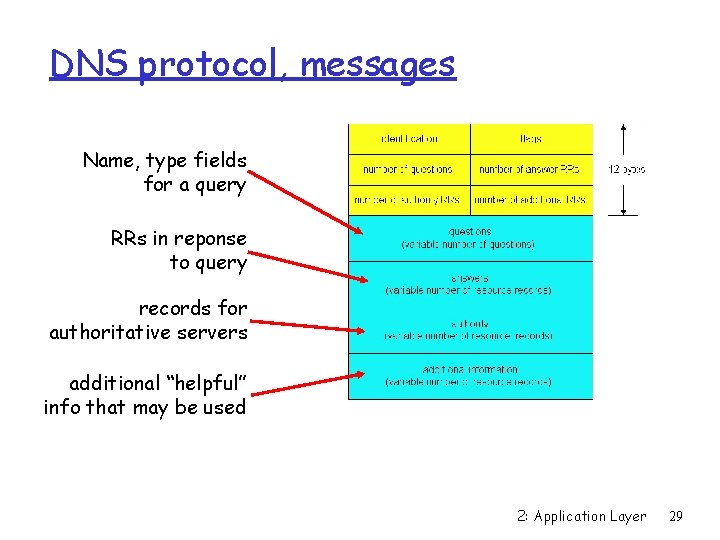
DNS protocol, messages DNS protocol : query and reply messages, both with same message format msg header r identification: 16 bit # for query, reply to query uses same # r flags: m query or reply m recursion desired m recursion available m reply is authoritative 2: Application Layer 28
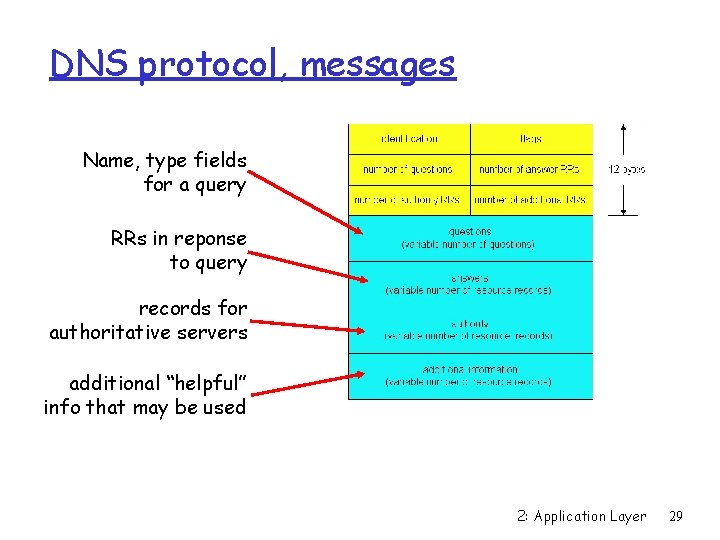
DNS protocol, messages Name, type fields for a query RRs in reponse to query records for authoritative servers additional “helpful” info that may be used 2: Application Layer 29
Inserting records into DNS r Example: just created startup “Network Utopia” r Register name networkuptopia. com at a registrar (e. g. , Network Solutions) m m Need to provide registrar with names and IP addresses of your authoritative name server Registrar inserts two RRs into the com TLD server: (networkutopia. com, dns 1. networkutopia. com, NS) (dns 1. networkutopia. com, 212. 1, A) r Put in authoritative server: Type A record for www. networkuptopia. com and Type MX record for mail. networkutopia. com 2: Application Layer 30
Chapter 2: Application layer r 2. 1 Principles of network applications m m app architectures app requirements r 2. 2 Web and HTTP r 2. 4 Electronic Mail m SMTP, POP 3, IMAP r 2. 5 DNS r 2. 6 P 2 P Applications r 2. 7 Socket programming with TCP r 2. 8 Socket programming with UDP r 2. 9 Building a Web server 2: Application Layer 31
P 2 P file sharing Example r Alice runs P 2 P client application on her notebook computer r Intermittently connects to Internet; gets new IP address for each connection r Asks for “Hey Jude” r Application displays other peers that have copy of Hey Jude. r Alice chooses one of the peers, Bob. r File is copied from Bob’s PC to Alice’s notebook: HTTP r While Alice downloads, other users uploading from Alice. r Alice’s peer is both a Web client and a transient Web server. All peers are servers = highly scalable! 2: Application Layer 32
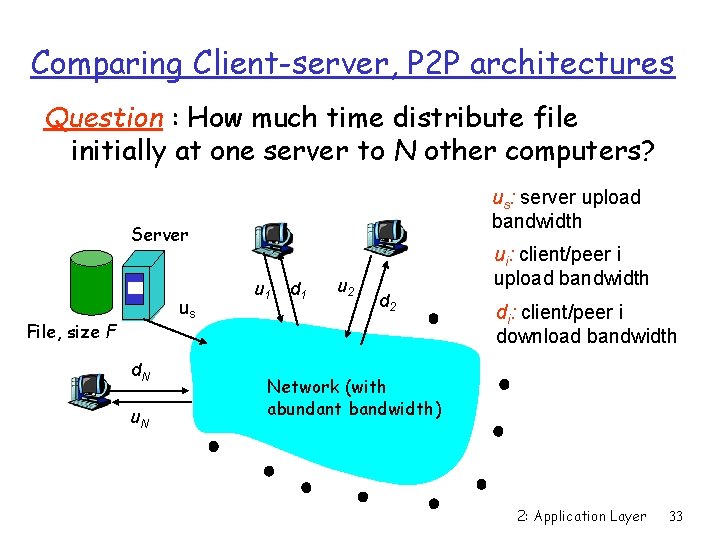
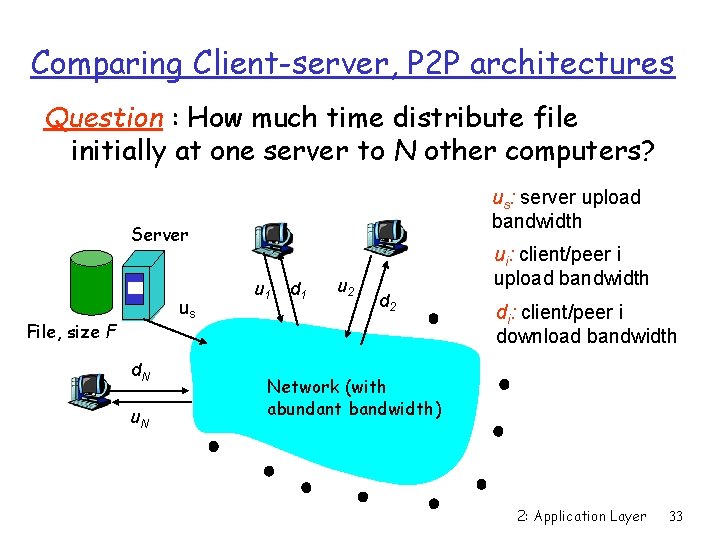
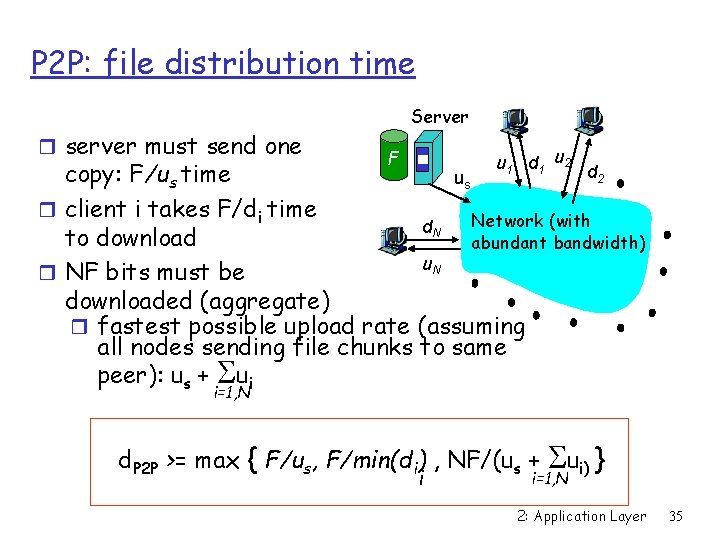
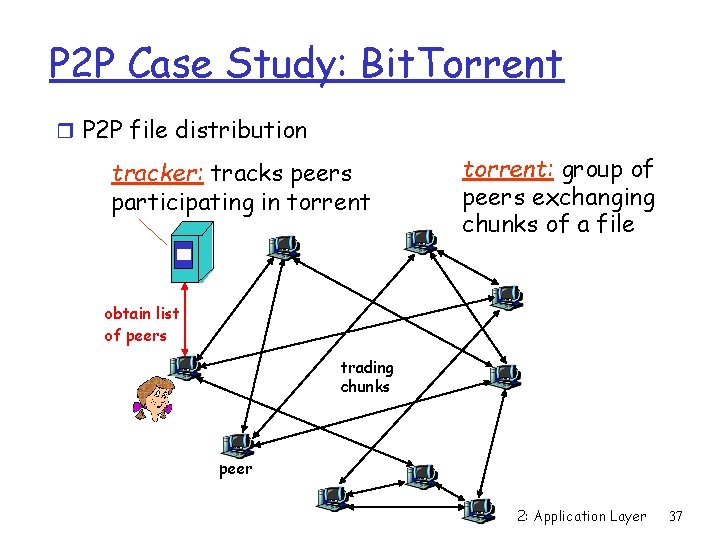
Comparing Client-server, P 2 P architectures Question : How much time distribute file initially at one server to N other computers? us: server upload bandwidth Server us File, size F d. N u 1 d 1 u 2 ui: client/peer i upload bandwidth d 2 di: client/peer i download bandwidth Network (with abundant bandwidth) 2: Application Layer 33
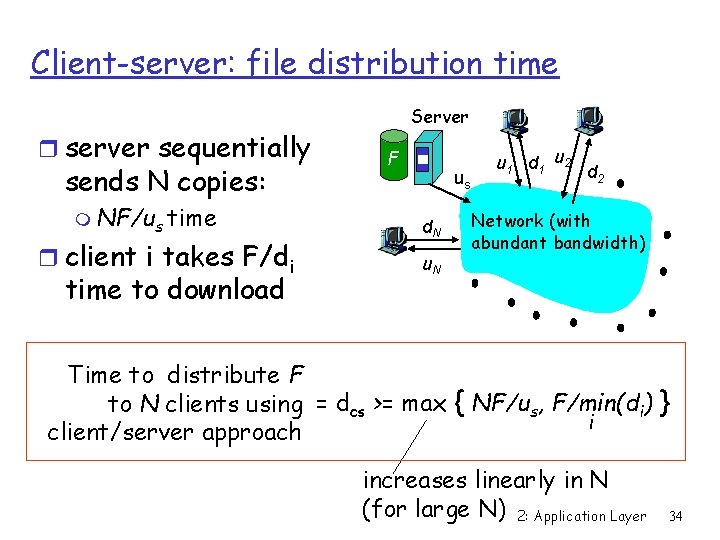
Client-server: file distribution time r server sequentially sends N copies: m NF/us time r client i takes F/di time to download Server F us d. N u 1 d 1 u 2 d 2 Network (with abundant bandwidth) Time to distribute F to N clients using = dcs >= max { NF/us, F/min(di) } i client/server approach increases linearly in N (for large N) 2: Application Layer 34
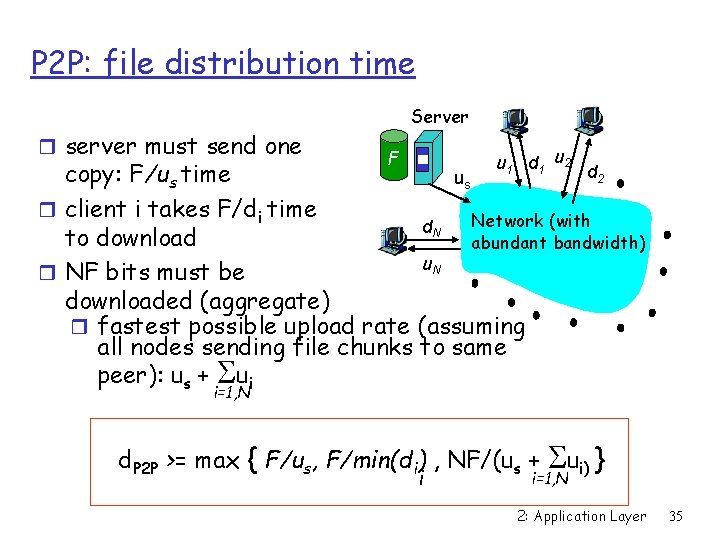
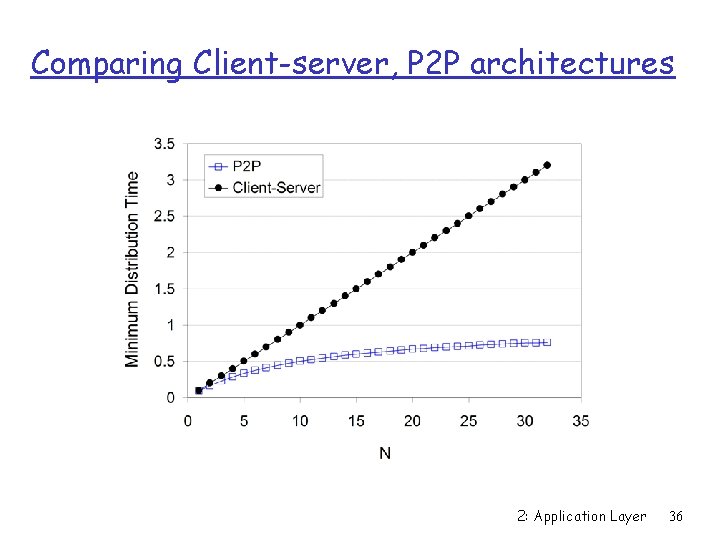
P 2 P: file distribution time r server must send one Server F u 1 d 1 u 2 d 2 copy: F/us time us r client i takes F/di time Network (with d. N to download abundant bandwidth) u. N r NF bits must be downloaded (aggregate) r fastest possible upload rate (assuming all nodes sending file chunks to same peer): us + Sui i=1, N S ui) } i=1, N d. P 2 P >= max { F/us, F/min(di) , NF/(us + i 2: Application Layer 35
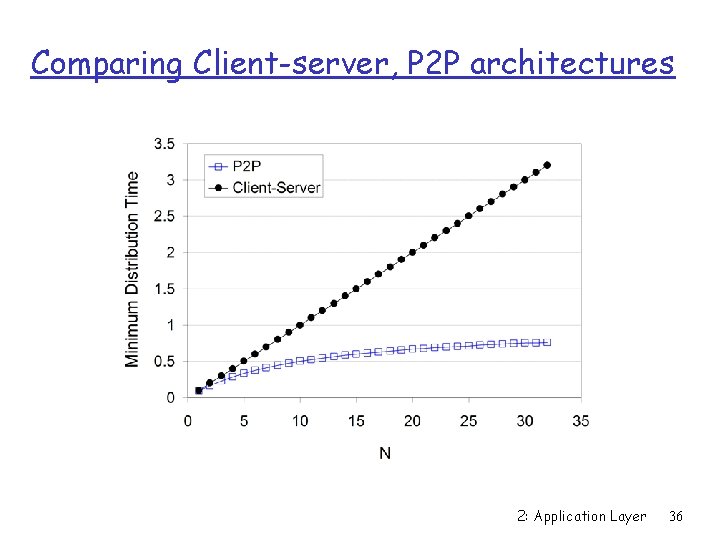
Comparing Client-server, P 2 P architectures 2: Application Layer 36
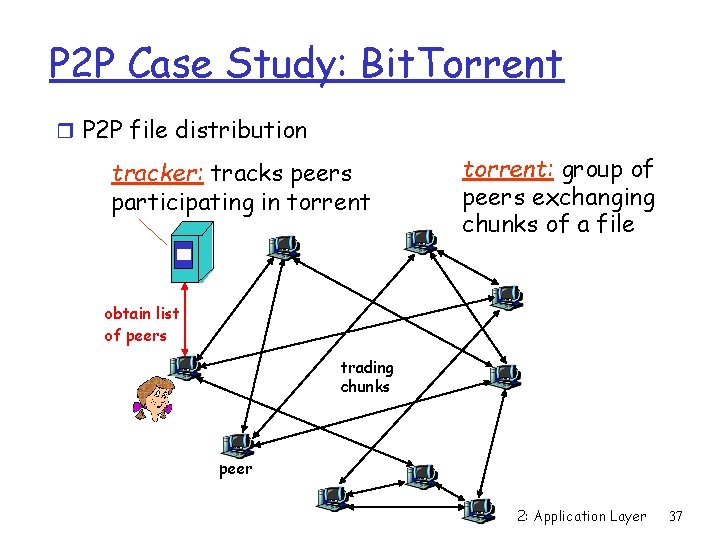
P 2 P Case Study: Bit. Torrent r P 2 P file distribution tracker: tracks peers participating in torrent: group of peers exchanging chunks of a file obtain list of peers trading chunks peer 2: Application Layer 37
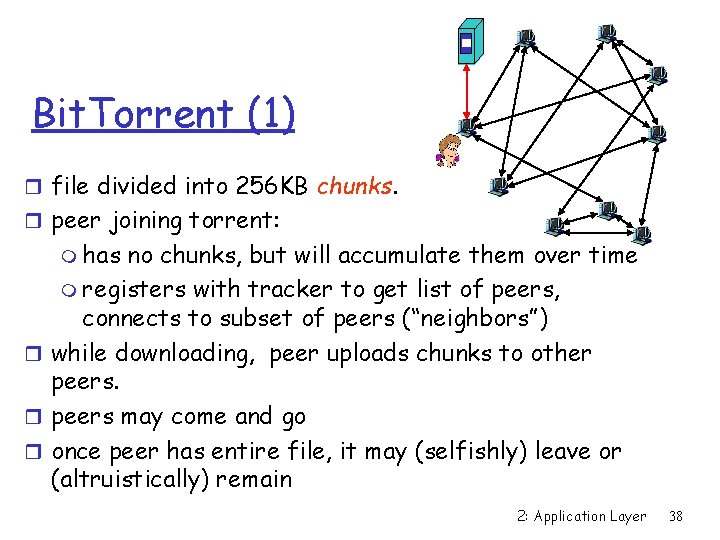
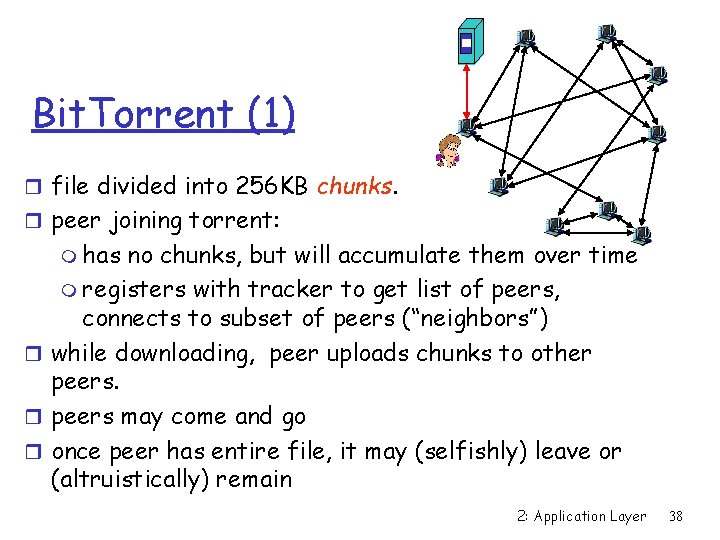
Bit. Torrent (1) r file divided into 256 KB chunks. r peer joining torrent: m has no chunks, but will accumulate them over time m registers with tracker to get list of peers, connects to subset of peers (“neighbors”) r while downloading, peer uploads chunks to other peers may come and go r once peer has entire file, it may (selfishly) leave or (altruistically) remain 2: Application Layer 38
Bit. Torrent (2) Pulling Chunks r at any given time, different peers have different subsets of file chunks r periodically, a peer (Alice) asks each neighbor for list of chunks that they have. r Alice issues requests for her missing chunks m rarest first Sending Chunks: tit-for-tat r Alice sends chunks to four neighbors currently sending her chunks at the highest rate m re-evaluate top 4 every 10 secs r every 30 secs: randomly select another peer, starts sending chunks m newly chosen peer may join top 4 2: Application Layer 39
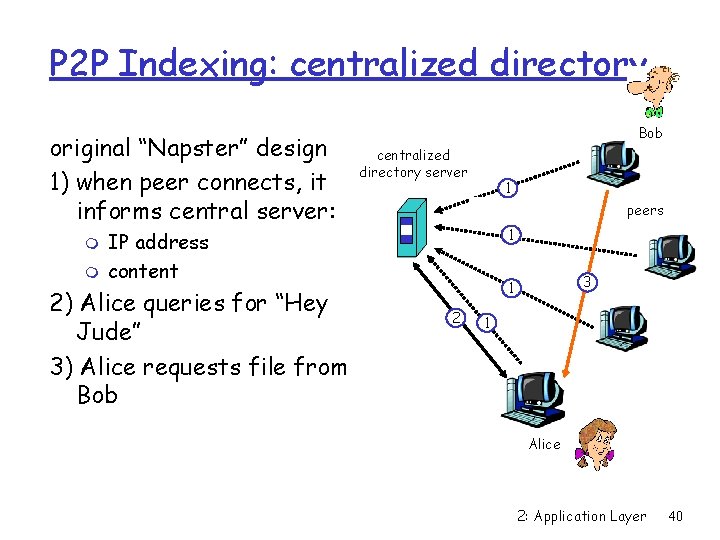
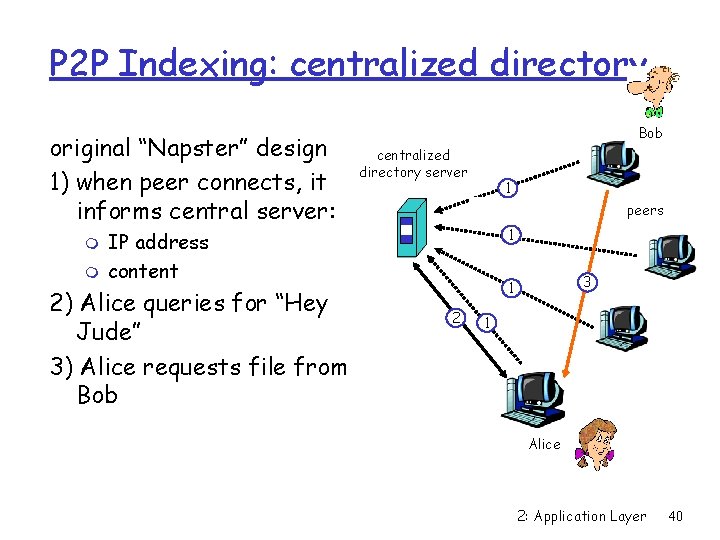
P 2 P Indexing: centralized directory original “Napster” design 1) when peer connects, it informs central server: m m Bob centralized directory server 1 peers 1 IP address content 2) Alice queries for “Hey Jude” 3) Alice requests file from Bob 3 1 2 1 Alice 2: Application Layer 40
P 2 P: problems with centralized directory r Single point of failure r Performance bottleneck r Copyright infringement file transfer is decentralized, but locating content is highly centralized 2: Application Layer 41
Query flooding: Gnutella r fully distributed m no central server r public domain protocol r many Gnutella clients implementing protocol overlay network: graph r edge between peer X and Y if there’s a TCP connection r all active peers and edges form overlay net r Edge is not a physical link r Peer will typically be connected with < 10 overlay neighbors 2: Application Layer 42
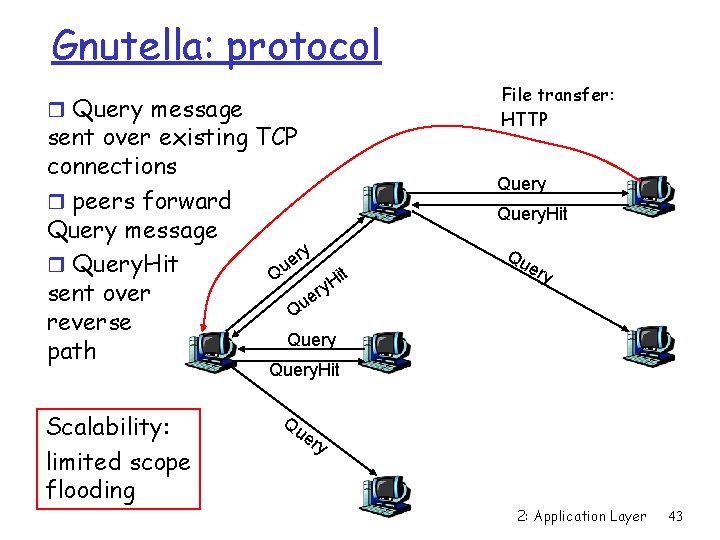
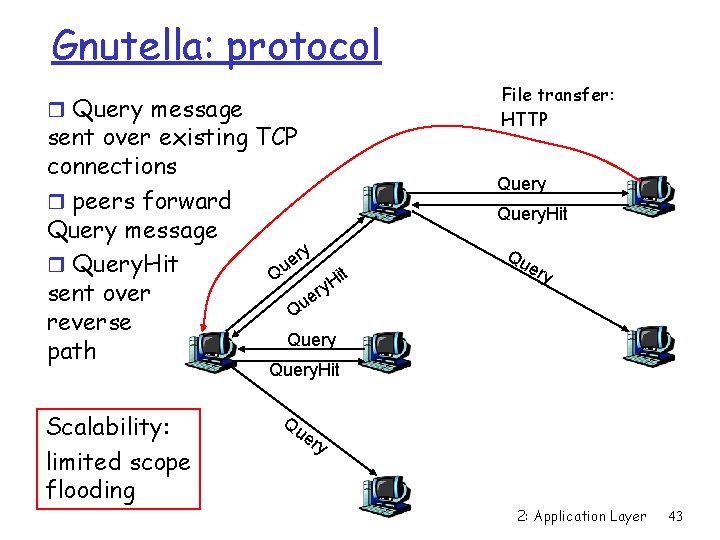
Gnutella: protocol r Query message sent over existing TCP connections r peers forward Query message ry e r Query. Hit it Qu H ry sent over e Qu reverse Query path File transfer: HTTP Query. Hit Qu ery Query. Hit Scalability: limited scope flooding Qu er y 2: Application Layer 43
Gnutella: Peer joining Joining peer X must find some other peer in Gnutella network: use list of candidate peers 2. X sequentially attempts to make TCP with peers on list until connection setup with Y 3. X sends Ping message to Y; Y forwards Ping message. 4. All peers receiving Ping message respond with Pong message 5. X receives many Pong messages. It can then setup additional TCP connections Peer leaving: see homework problem! 1. 2: Application Layer 44
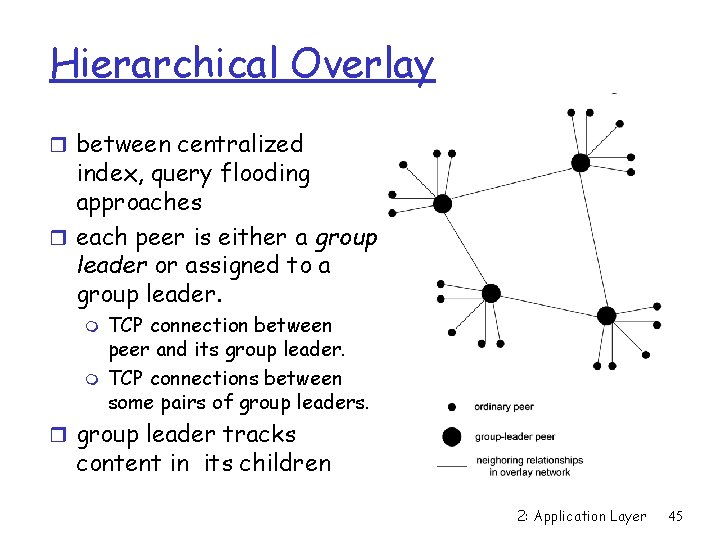
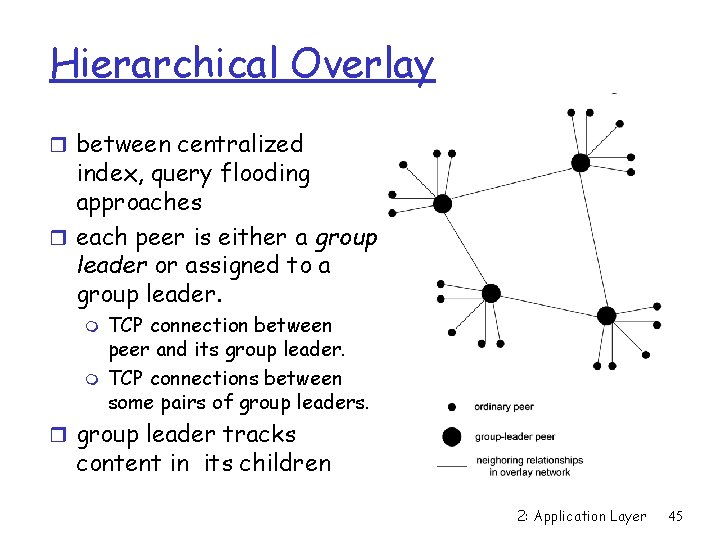
Hierarchical Overlay r between centralized index, query flooding approaches r each peer is either a group leader or assigned to a group leader. m m TCP connection between peer and its group leader. TCP connections between some pairs of group leaders. r group leader tracks content in its children 2: Application Layer 45
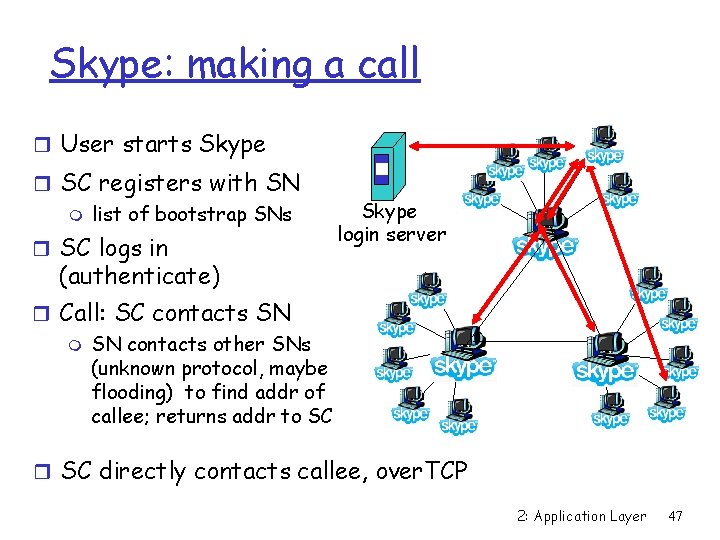
P 2 P Case study: Skype clients (SC) r P 2 P (pc-to-pc, pc-to- phone, phone-to-pc) Voice-Over-IP (Vo. IP) Skype application login server m also IM r proprietary application -layer protocol (inferred via reverse engineering) r hierarchical overlay Supernode (SN) 2: Application Layer 46
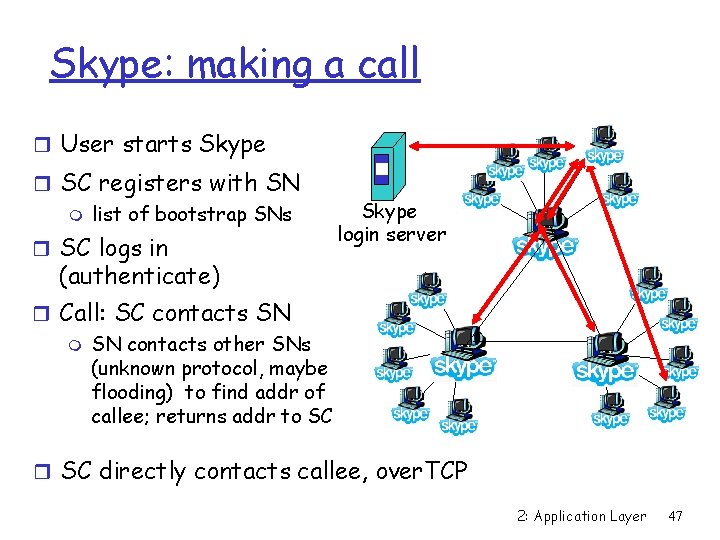
Skype: making a call r User starts Skype r SC registers with SN m list of bootstrap SNs r SC logs in Skype login server (authenticate) r Call: SC contacts SN m SN contacts other SNs (unknown protocol, maybe flooding) to find addr of callee; returns addr to SC r SC directly contacts callee, over. TCP 2: Application Layer 47
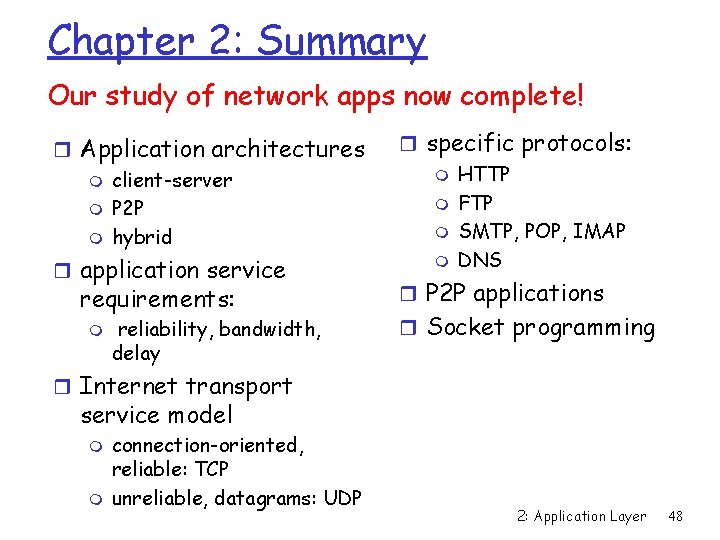
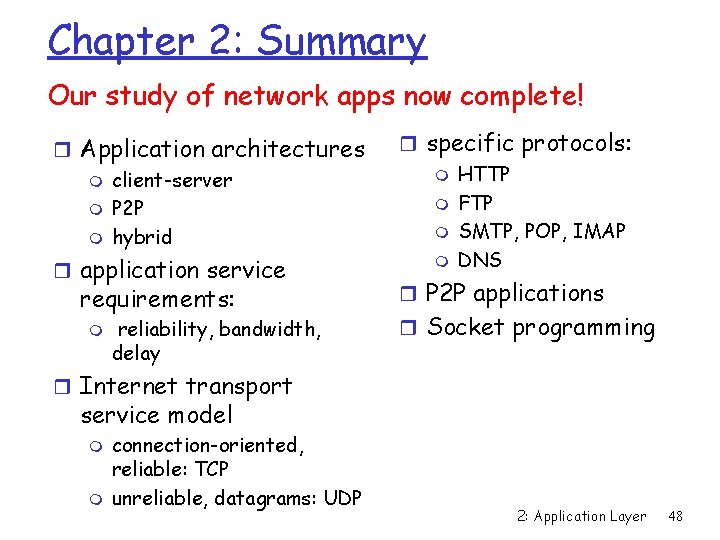
Chapter 2: Summary Our study of network apps now complete! r Application architectures m client-server m P 2 P m hybrid r application service requirements: m reliability, bandwidth, delay r specific protocols: m HTTP m FTP m SMTP, POP, IMAP m DNS r P 2 P applications r Socket programming r Internet transport service model m m connection-oriented, reliable: TCP unreliable, datagrams: UDP 2: Application Layer 48
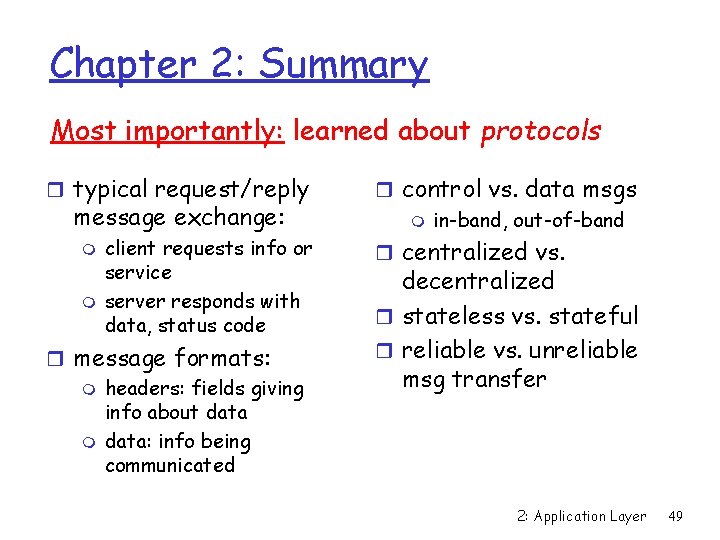
Chapter 2: Summary Most importantly: learned about protocols r typical request/reply message exchange: m m client requests info or service server responds with data, status code r message formats: m headers: fields giving info about data m data: info being communicated r control vs. data msgs m in-band, out-of-band r centralized vs. decentralized r stateless vs. stateful r reliable vs. unreliable msg transfer 2: Application Layer 49