Chapter 5 Link Layer and LANs Computer Networking
![Random MAC (Medium Access Control) Techniques r ALOHA (‘ 70) [packet radio network] m Random MAC (Medium Access Control) Techniques r ALOHA (‘ 70) [packet radio network] m](https://slidetodoc.com/presentation_image/12b3c7e65ce896a34f2c440a9640e7eb/image-12.jpg)

- Slides: 43
Chapter 5 Link Layer and LANs Computer Networking: A Top Down Approach Jim Kurose, Keith Ross Addison-Wesley. 5: Data. Link Layer 5 -1
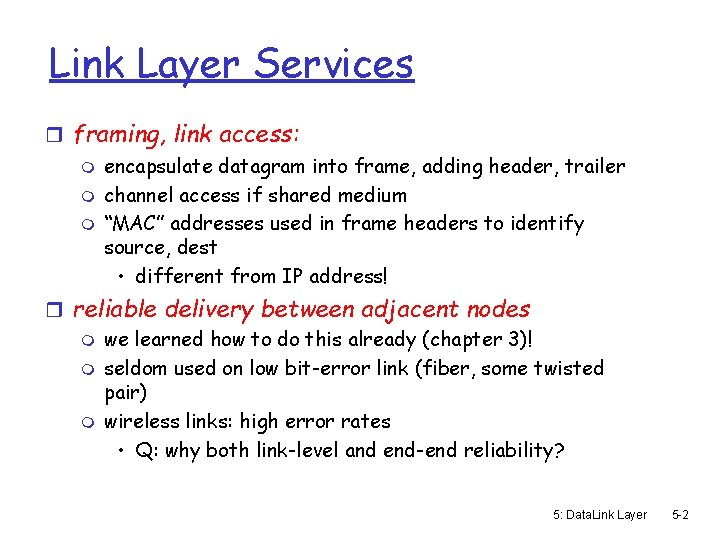
Link Layer Services r framing, link access: m encapsulate datagram into frame, adding header, trailer m channel access if shared medium m “MAC” addresses used in frame headers to identify source, dest • different from IP address! r reliable delivery between adjacent nodes m we learned how to do this already (chapter 3)! m seldom used on low bit-error link (fiber, some twisted pair) m wireless links: high error rates • Q: why both link-level and end-end reliability? 5: Data. Link Layer 5 -2
Link Layer Services (more) r flow control: m pacing between adjacent sending and receiving nodes r error detection: m errors caused by signal attenuation, noise. m receiver detects presence of errors: • signals sender for retransmission or drops frame r error correction: m receiver identifies and corrects bit error(s) without resorting to retransmission r half-duplex and full-duplex m with half duplex, nodes at both ends of link can transmit, but not at same time 5: Data. Link Layer 5 -3
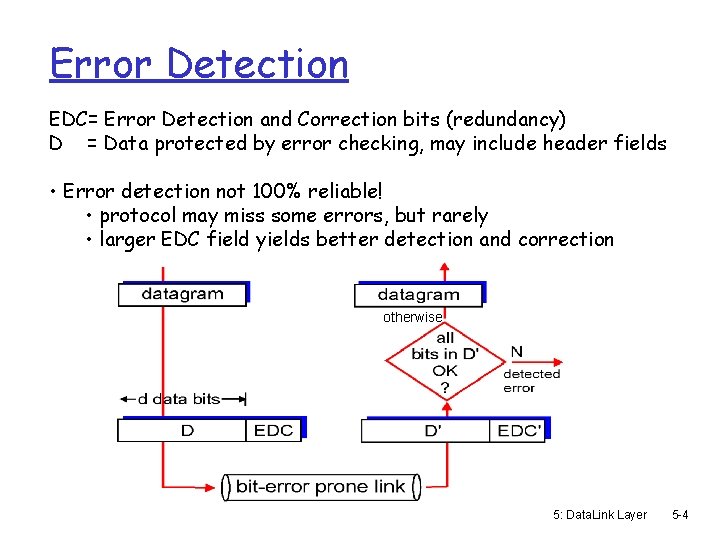
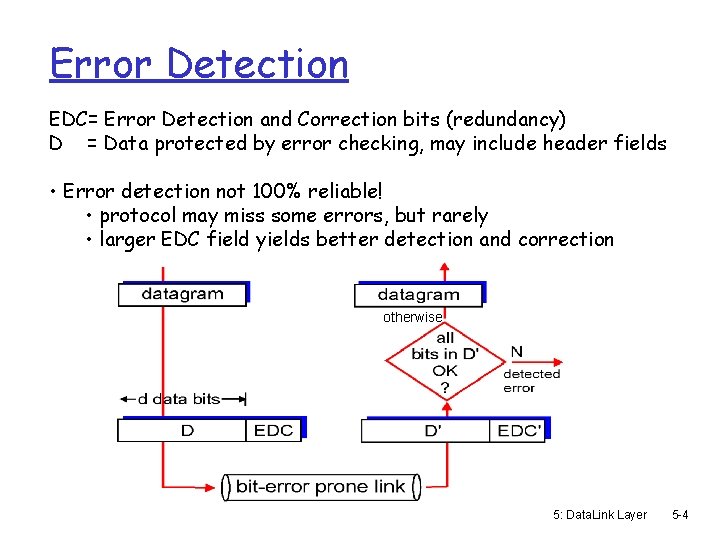
Error Detection EDC= Error Detection and Correction bits (redundancy) D = Data protected by error checking, may include header fields • Error detection not 100% reliable! • protocol may miss some errors, but rarely • larger EDC field yields better detection and correction otherwise 5: Data. Link Layer 5 -4
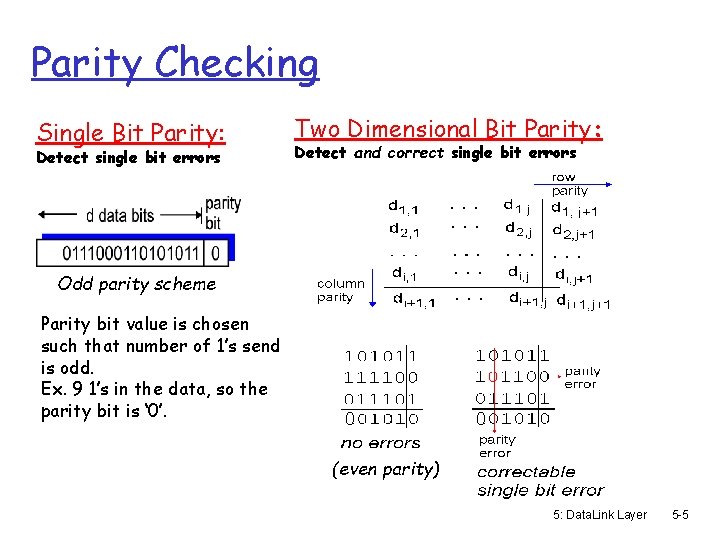
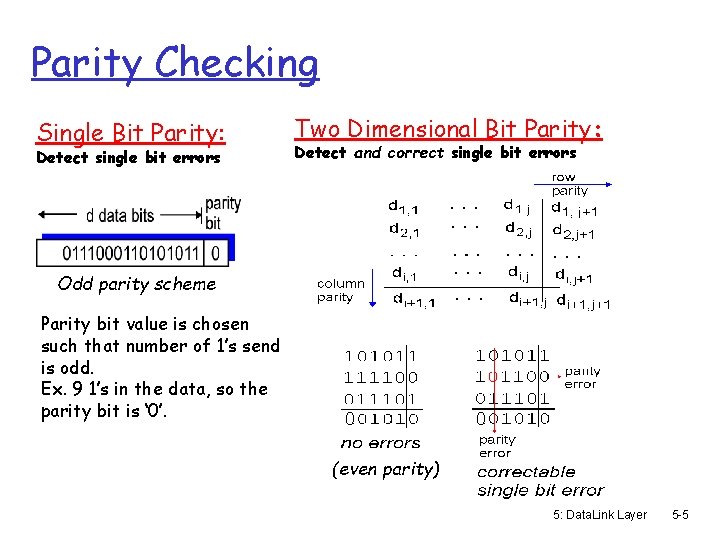
Parity Checking Single Bit Parity: Detect single bit errors Two Dimensional Bit Parity: Detect and correct single bit errors Odd parity scheme Parity bit value is chosen such that number of 1’s send is odd. Ex. 9 1’s in the data, so the parity bit is ‘ 0’. 0 0 (even parity) 5: Data. Link Layer 5 -5
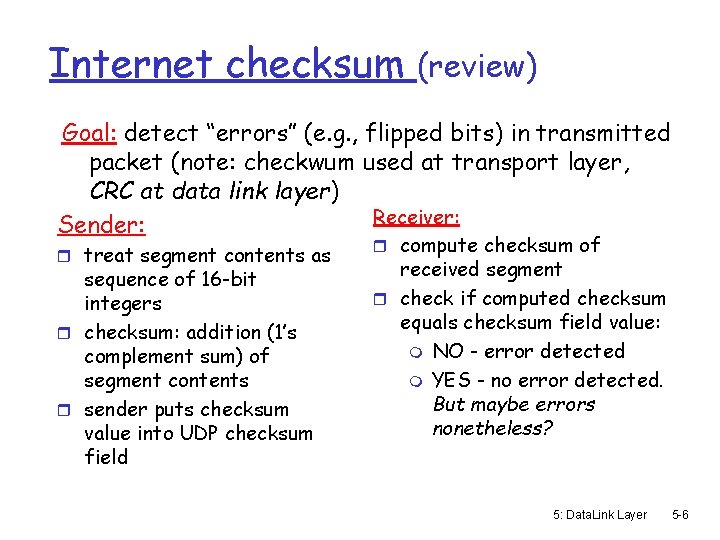
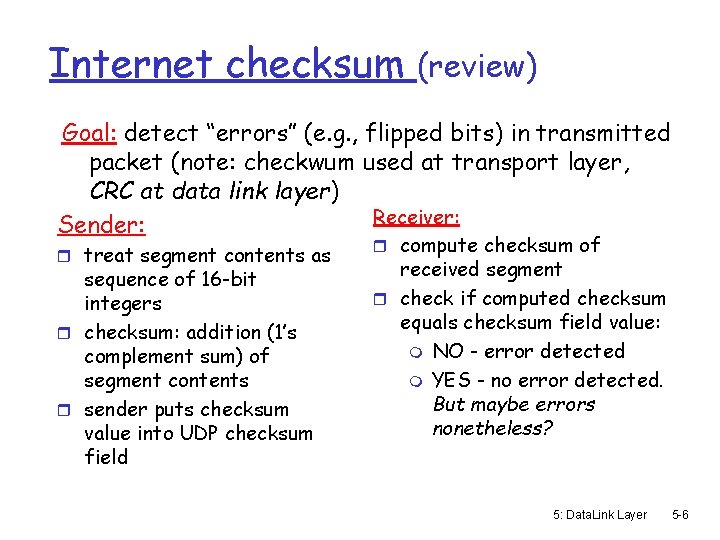
Internet checksum (review) Goal: detect “errors” (e. g. , flipped bits) in transmitted packet (note: checkwum used at transport layer, CRC at data link layer) Receiver: Sender: r treat segment contents as sequence of 16 -bit integers r checksum: addition (1’s complement sum) of segment contents r sender puts checksum value into UDP checksum field r compute checksum of received segment r check if computed checksum equals checksum field value: m NO - error detected m YES - no error detected. But maybe errors nonetheless? 5: Data. Link Layer 5 -6
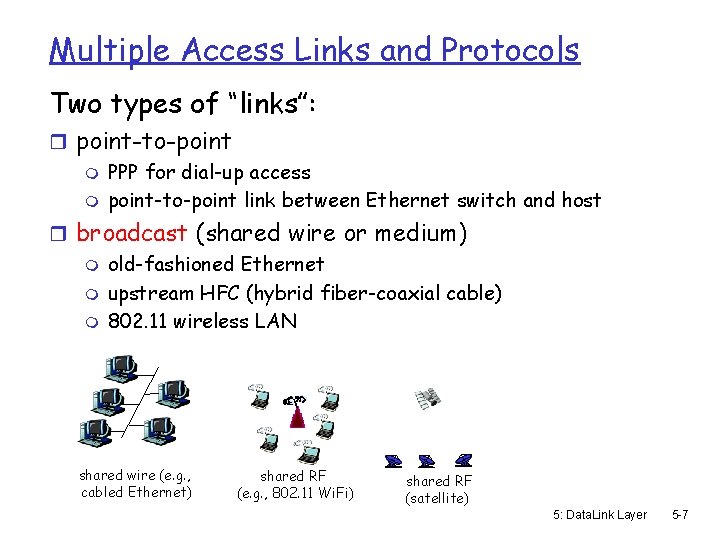
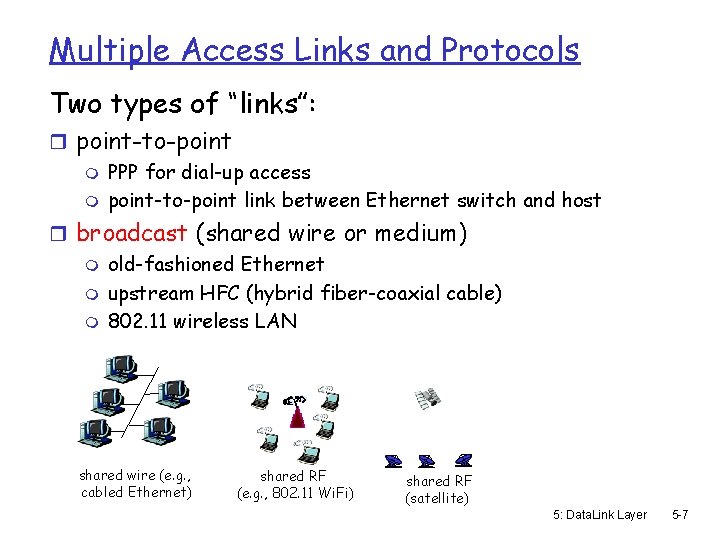
Multiple Access Links and Protocols Two types of “links”: r point-to-point m PPP for dial-up access m point-to-point link between Ethernet switch and host r broadcast (shared wire or medium) m old-fashioned Ethernet m upstream HFC (hybrid fiber-coaxial cable) m 802. 11 wireless LAN shared wire (e. g. , cabled Ethernet) shared RF (e. g. , 802. 11 Wi. Fi) shared RF (satellite) 5: Data. Link Layer 5 -7
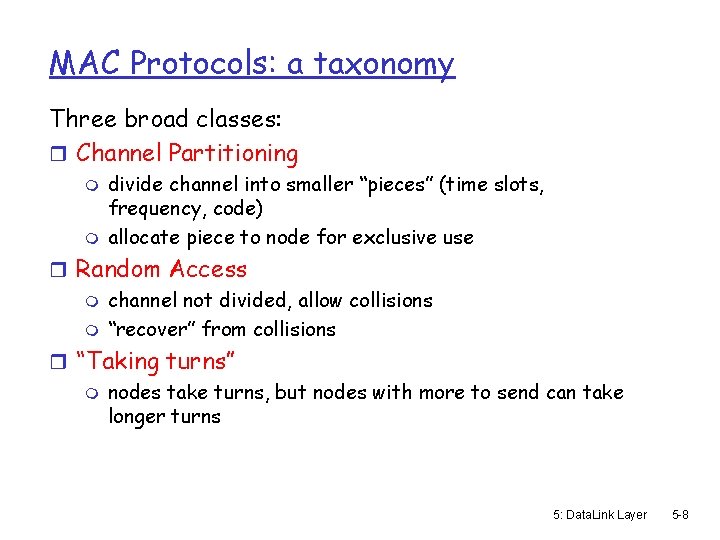
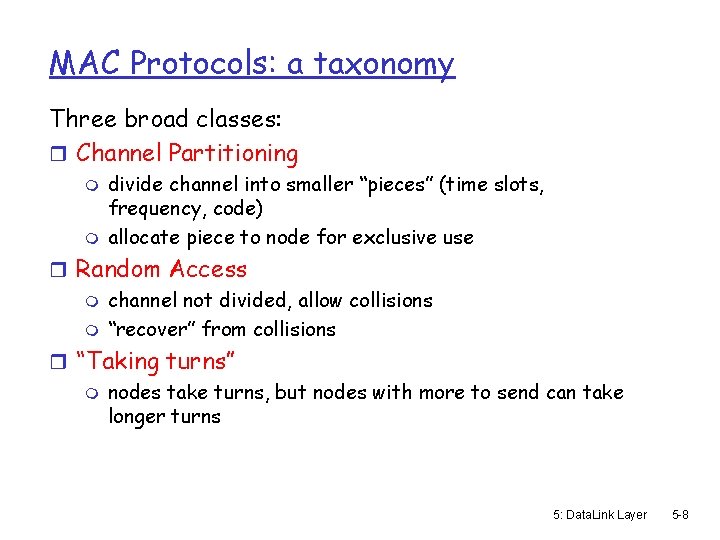
MAC Protocols: a taxonomy Three broad classes: r Channel Partitioning m m divide channel into smaller “pieces” (time slots, frequency, code) allocate piece to node for exclusive use r Random Access m channel not divided, allow collisions m “recover” from collisions r “Taking turns” m nodes take turns, but nodes with more to send can take longer turns 5: Data. Link Layer 5 -8
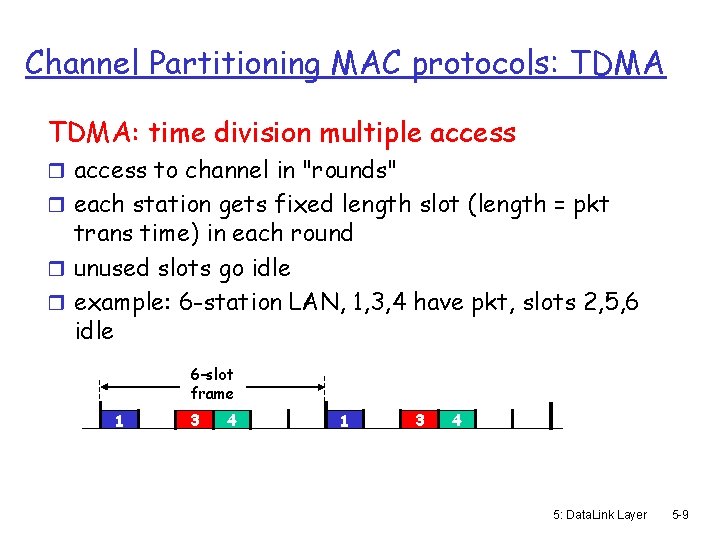
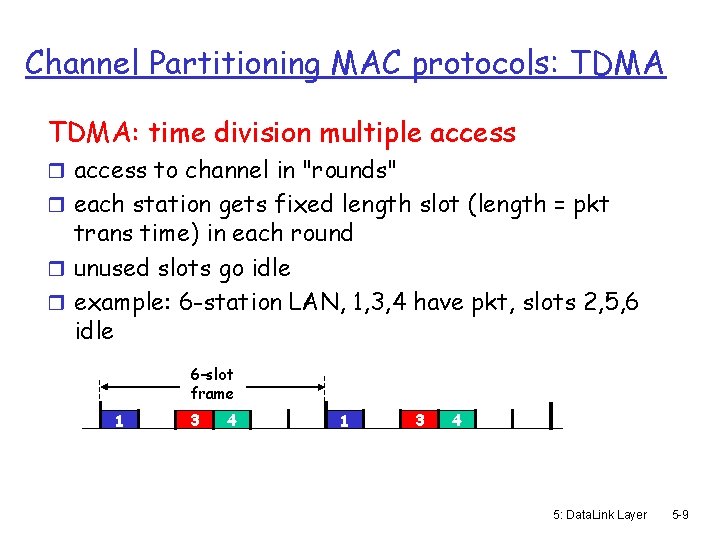
Channel Partitioning MAC protocols: TDMA: time division multiple access r access to channel in "rounds" r each station gets fixed length slot (length = pkt trans time) in each round r unused slots go idle r example: 6 -station LAN, 1, 3, 4 have pkt, slots 2, 5, 6 idle 6 -slot frame 1 3 4 5: Data. Link Layer 5 -9
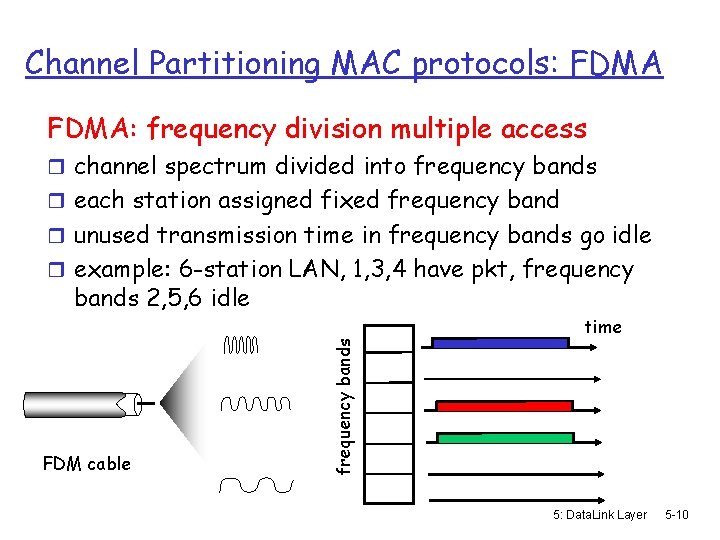
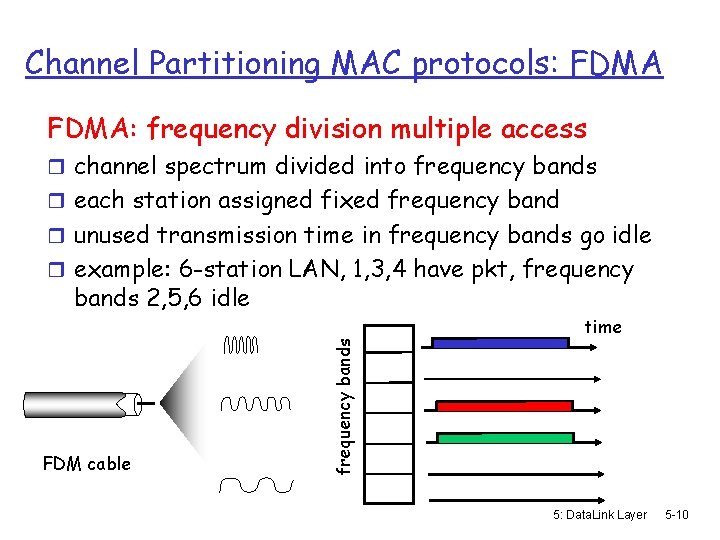
Channel Partitioning MAC protocols: FDMA: frequency division multiple access r channel spectrum divided into frequency bands r each station assigned fixed frequency band r unused transmission time in frequency bands go idle r example: 6 -station LAN, 1, 3, 4 have pkt, frequency bands 2, 5, 6 idle frequency bands FDM cable time 5: Data. Link Layer 5 -10
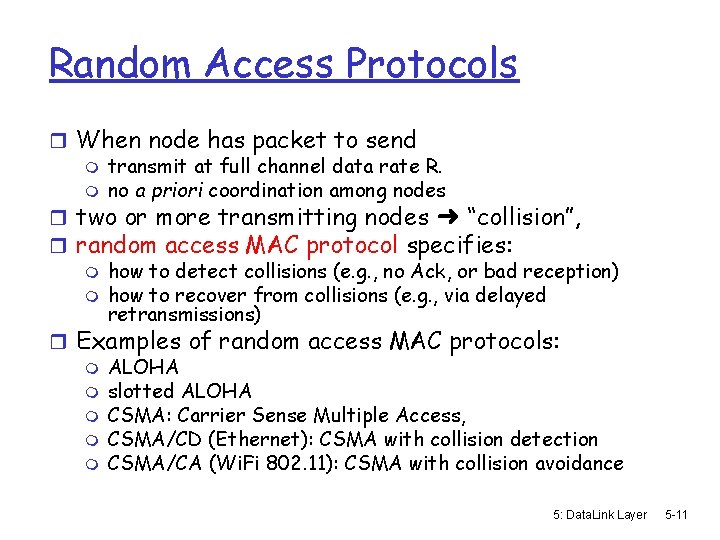
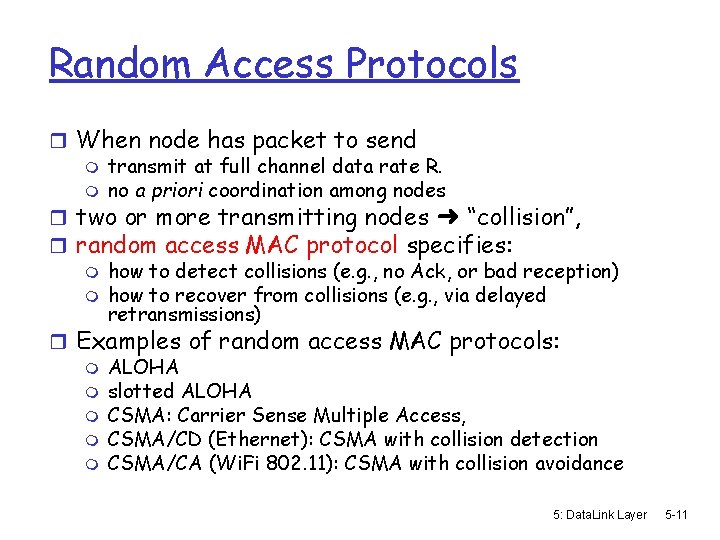
Random Access Protocols r When node has packet to send m transmit at full channel data rate R. m no a priori coordination among nodes r two or more transmitting nodes ➜ “collision”, r random access MAC protocol specifies: m how to detect collisions (e. g. , no Ack, or bad reception) m how to recover from collisions (e. g. , via delayed retransmissions) r Examples of random access MAC protocols: m ALOHA m slotted ALOHA m CSMA: Carrier Sense Multiple Access, m CSMA/CD (Ethernet): CSMA with collision detection m CSMA/CA (Wi. Fi 802. 11): CSMA with collision avoidance 5: Data. Link Layer 5 -11
![Random MAC Medium Access Control Techniques r ALOHA 70 packet radio network m Random MAC (Medium Access Control) Techniques r ALOHA (‘ 70) [packet radio network] m](https://slidetodoc.com/presentation_image/12b3c7e65ce896a34f2c440a9640e7eb/image-12.jpg)
Random MAC (Medium Access Control) Techniques r ALOHA (‘ 70) [packet radio network] m A station sends whenever it has a packet/frame m Listens for round-trip-time delay for Ack m If no Ack then re-send packet/frame after random delay • too short more collisions • too long under utilization m No carrier sense is used m If two stations transmit about the same time frames collide m Utilization of ALOHA is low ~18% 5: Data. Link Layer 5 -12
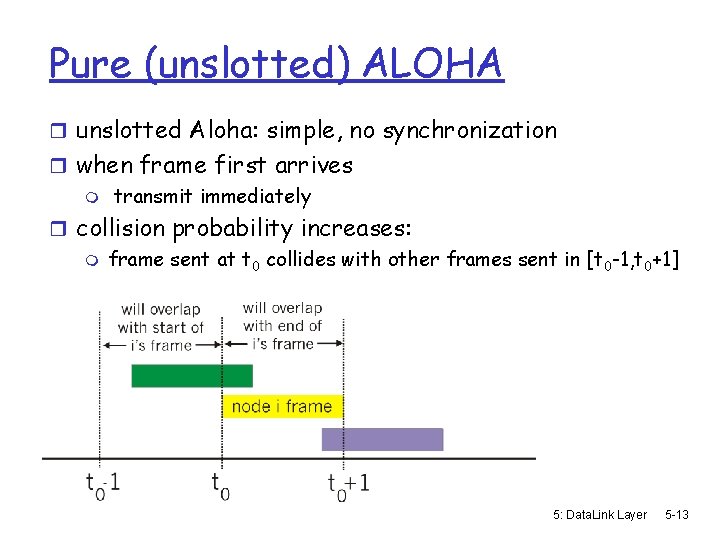
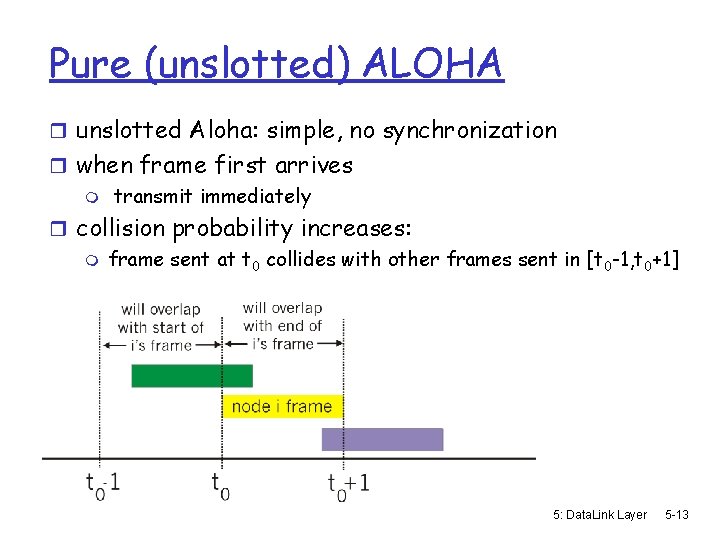
Pure (unslotted) ALOHA r unslotted Aloha: simple, no synchronization r when frame first arrives m transmit immediately r collision probability increases: m frame sent at t 0 collides with other frames sent in [t 0 -1, t 0+1] 5: Data. Link Layer 5 -13
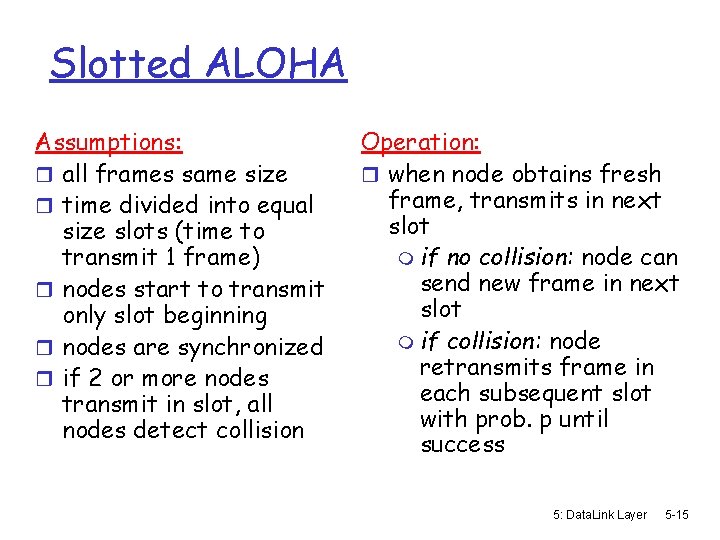
Pure Aloha efficiency P(success by given node) = P(node transmits). P(no other node transmits in [t 0 -1, t 0]. P(no other node transmits in [t 0, t 0+1] = p. (1 -p)N-1 = p. (1 -p)2(N-1) … choosing optimum p and then letting n -> infty. . . = 1/(2 e) =. 18 Very bad, can we do better? 5: Data. Link Layer 5 -14
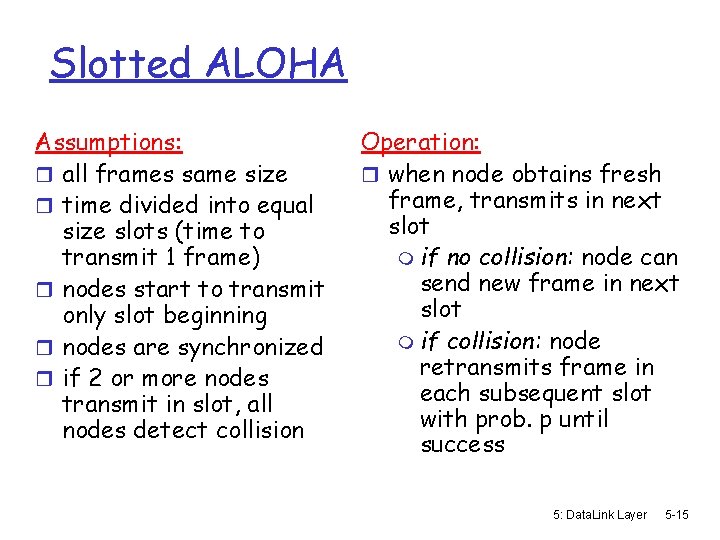
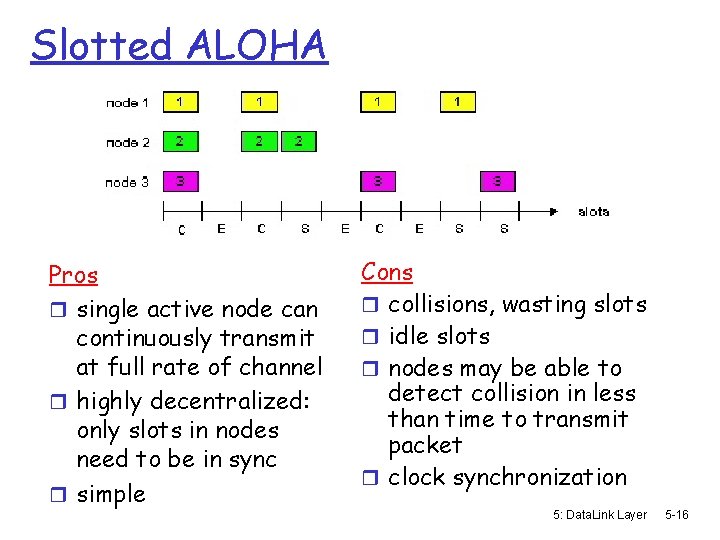
Slotted ALOHA Assumptions: r all frames same size r time divided into equal size slots (time to transmit 1 frame) r nodes start to transmit only slot beginning r nodes are synchronized r if 2 or more nodes transmit in slot, all nodes detect collision Operation: r when node obtains fresh frame, transmits in next slot m if no collision: node can send new frame in next slot m if collision: node retransmits frame in each subsequent slot with prob. p until success 5: Data. Link Layer 5 -15
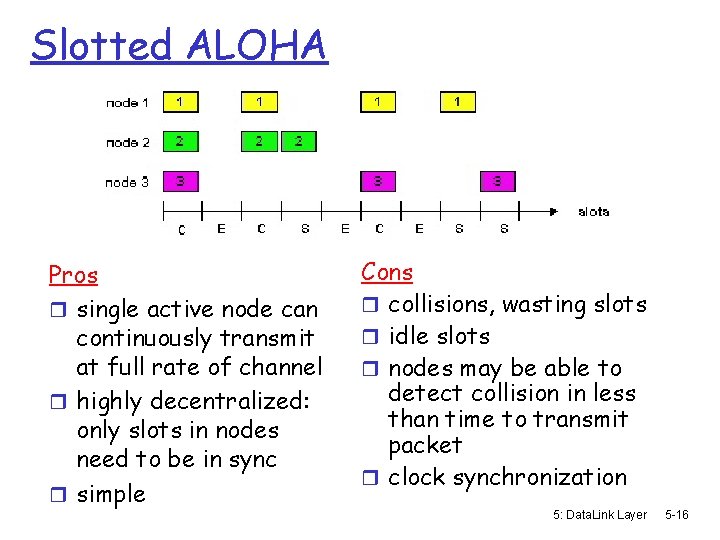
Slotted ALOHA Pros r single active node can continuously transmit at full rate of channel r highly decentralized: only slots in nodes need to be in sync r simple Cons r collisions, wasting slots r idle slots r nodes may be able to detect collision in less than time to transmit packet r clock synchronization 5: Data. Link Layer 5 -16
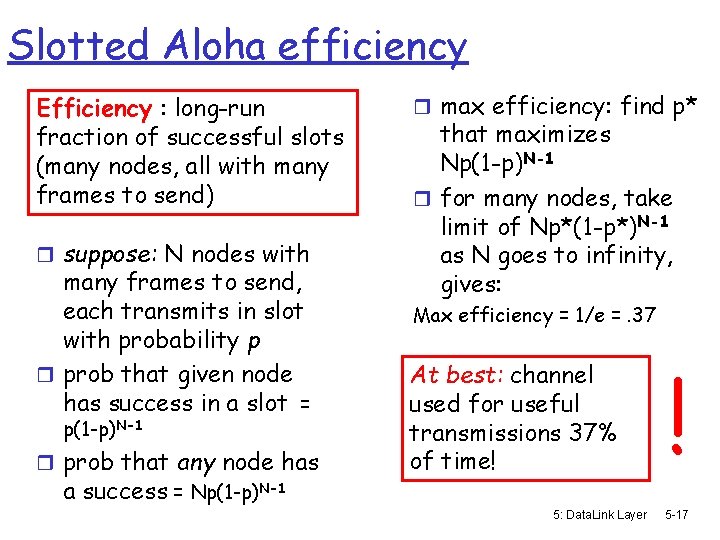
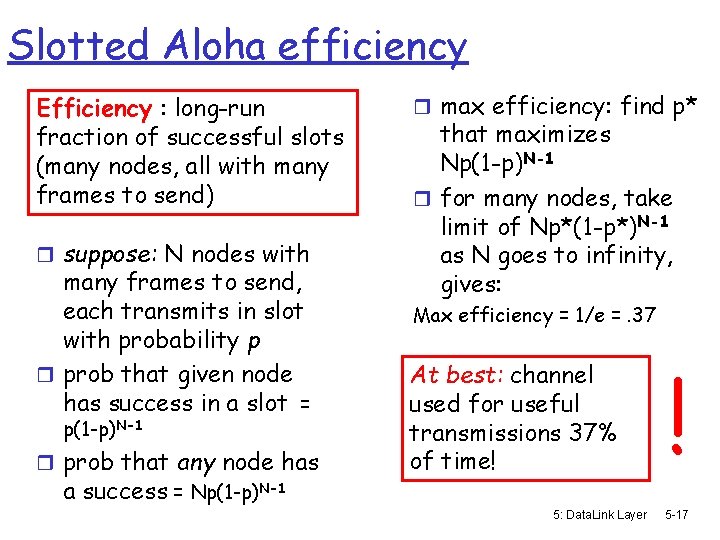
Slotted Aloha efficiency Efficiency : long-run fraction of successful slots (many nodes, all with many frames to send) r suppose: N nodes with many frames to send, each transmits in slot with probability p r prob that given node has success in a slot = p(1 -p)N-1 r prob that any node has a success = Np(1 -p)N-1 r max efficiency: find p* that maximizes Np(1 -p)N-1 r for many nodes, take limit of Np*(1 -p*)N-1 as N goes to infinity, gives: Max efficiency = 1/e =. 37 At best: channel used for useful transmissions 37% of time! 5: Data. Link Layer ! 5 -17
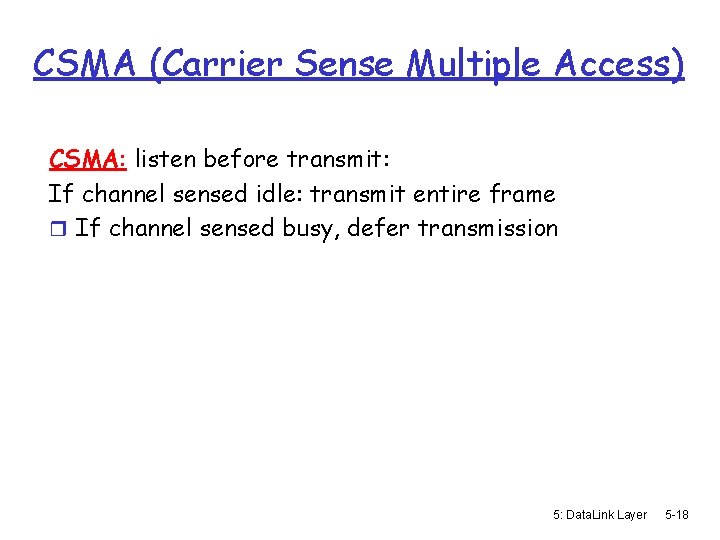
CSMA (Carrier Sense Multiple Access) CSMA: listen before transmit: If channel sensed idle: transmit entire frame r If channel sensed busy, defer transmission 5: Data. Link Layer 5 -18
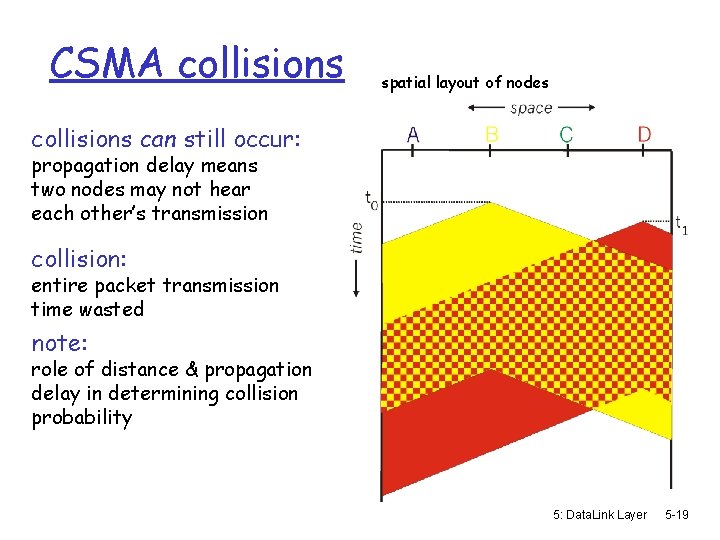
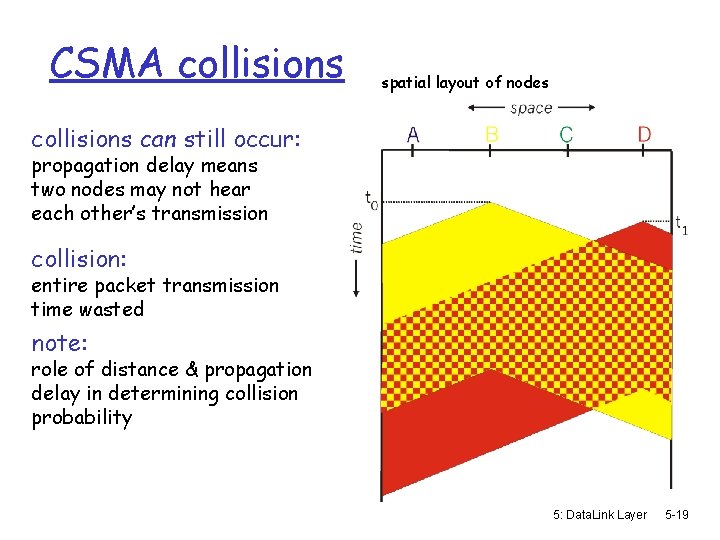
CSMA collisions spatial layout of nodes collisions can still occur: propagation delay means two nodes may not hear each other’s transmission collision: entire packet transmission time wasted note: role of distance & propagation delay in determining collision probability 5: Data. Link Layer 5 -19
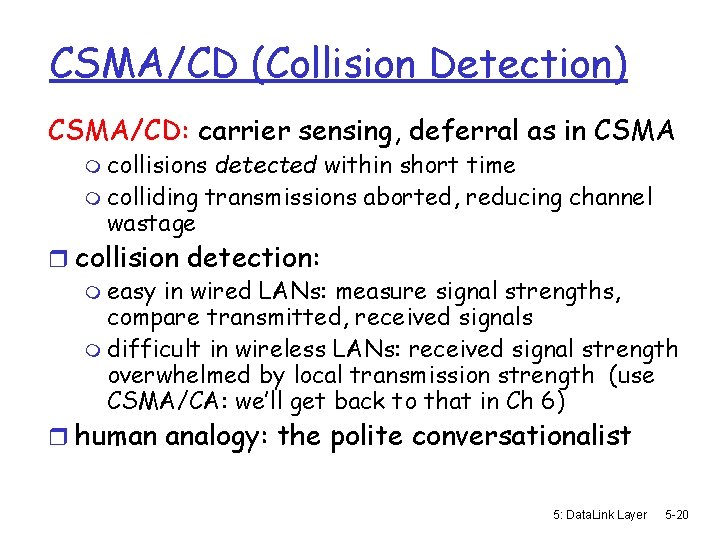
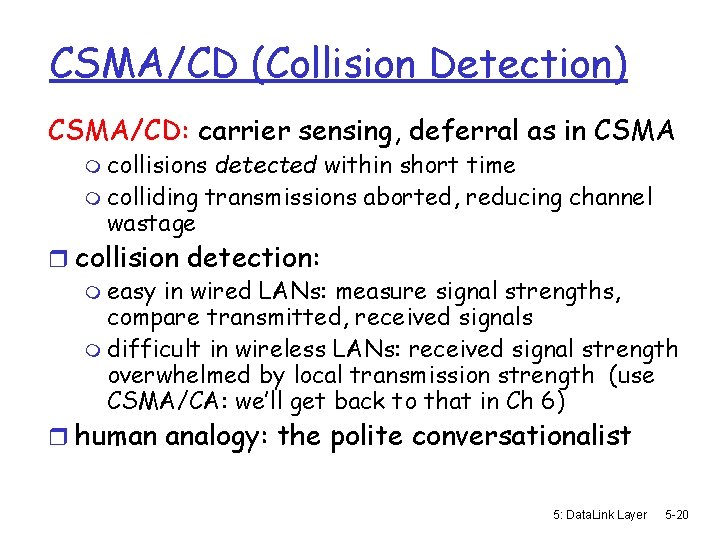
CSMA/CD (Collision Detection) CSMA/CD: carrier sensing, deferral as in CSMA m collisions detected within short time m colliding transmissions aborted, reducing channel wastage r collision detection: m easy in wired LANs: measure signal strengths, compare transmitted, received signals m difficult in wireless LANs: received signal strength overwhelmed by local transmission strength (use CSMA/CA: we’ll get back to that in Ch 6) r human analogy: the polite conversationalist 5: Data. Link Layer 5 -20
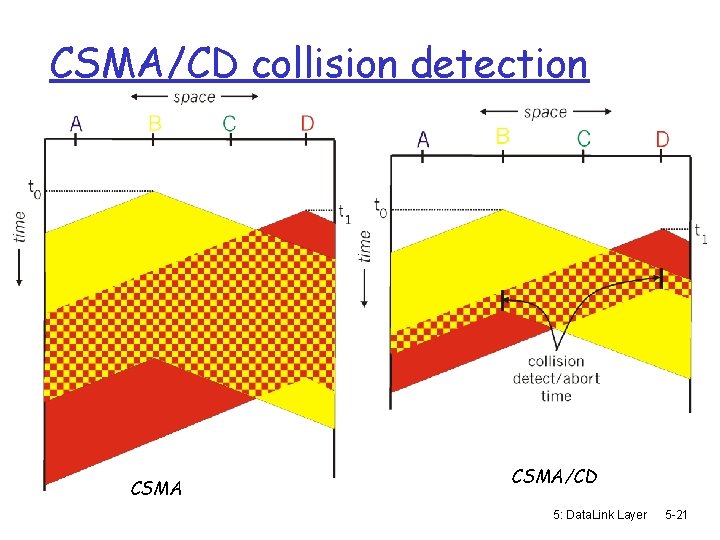
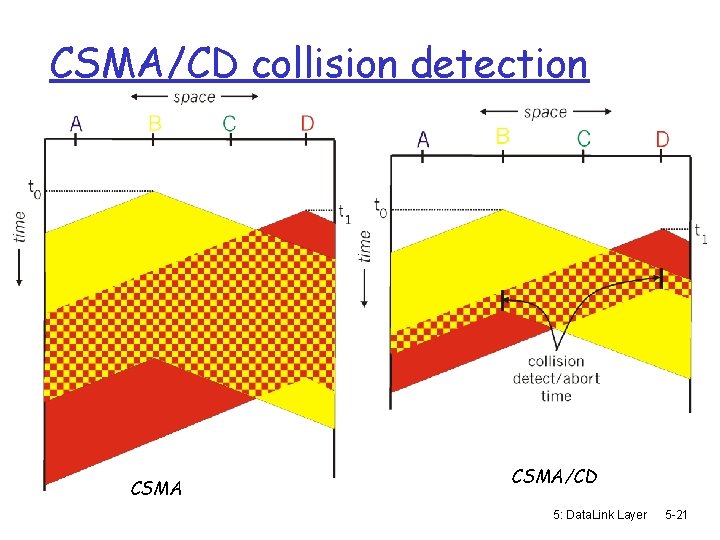
CSMA/CD collision detection CSMA/CD 5: Data. Link Layer 5 -21
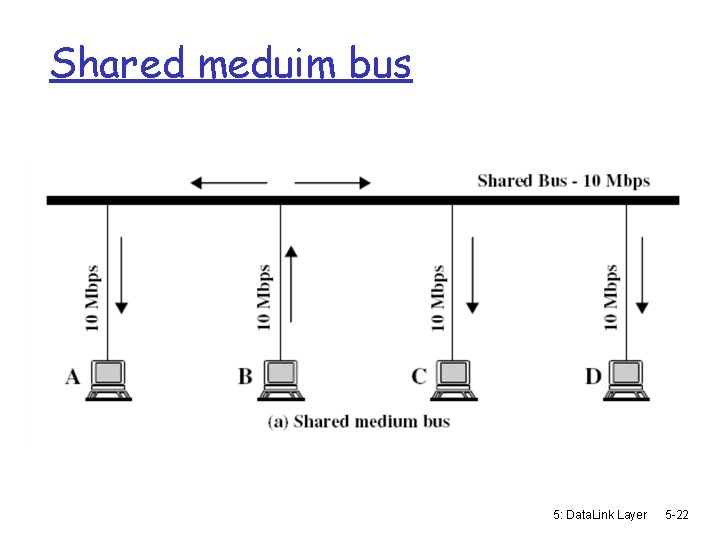
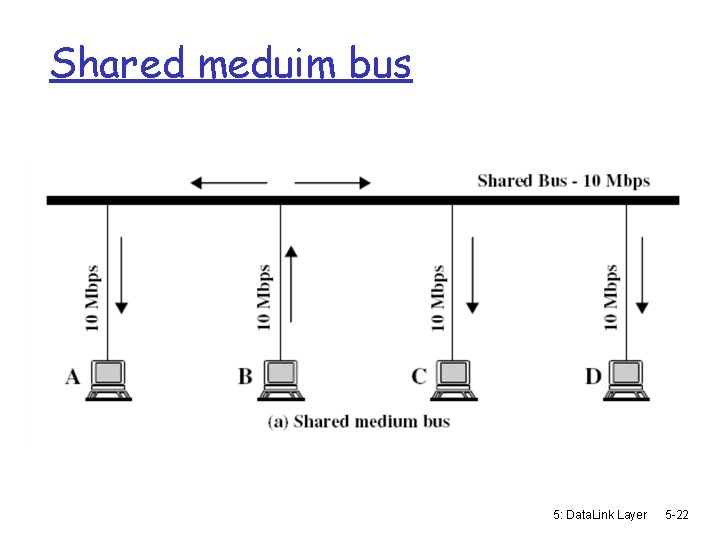
Shared meduim bus 5: Data. Link Layer 5 -22
More on CSMA/CD and Ethernet - uses broadcast and filtration: all stations on the bus receive the frame, but only the station with the appropriate data link D-L (MAC) destination address picks up the frame. For multicast, filteration may be done at the D-L layer or at the network layer (with more overhead) 5: Data. Link Layer 5 -23
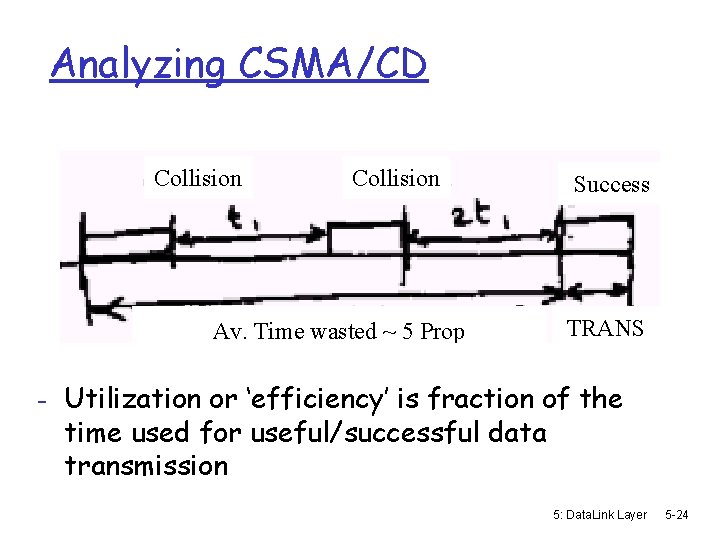
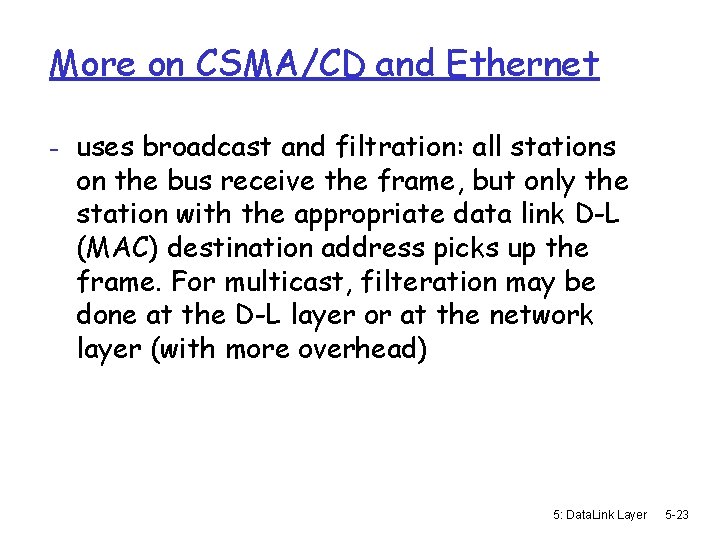
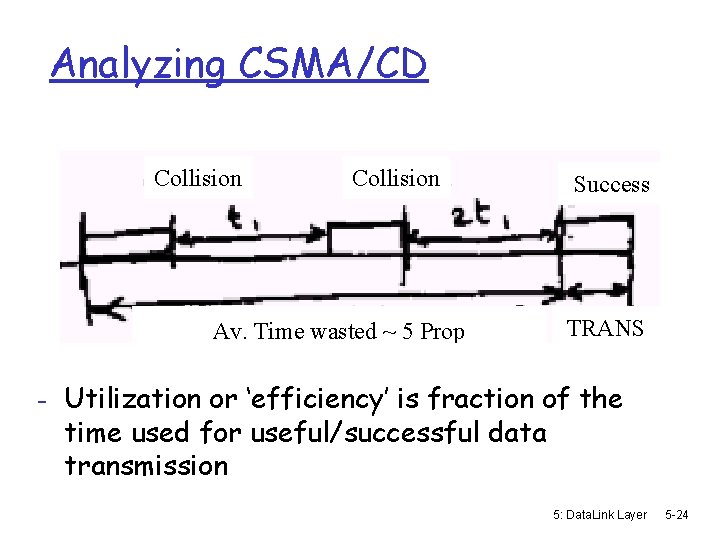
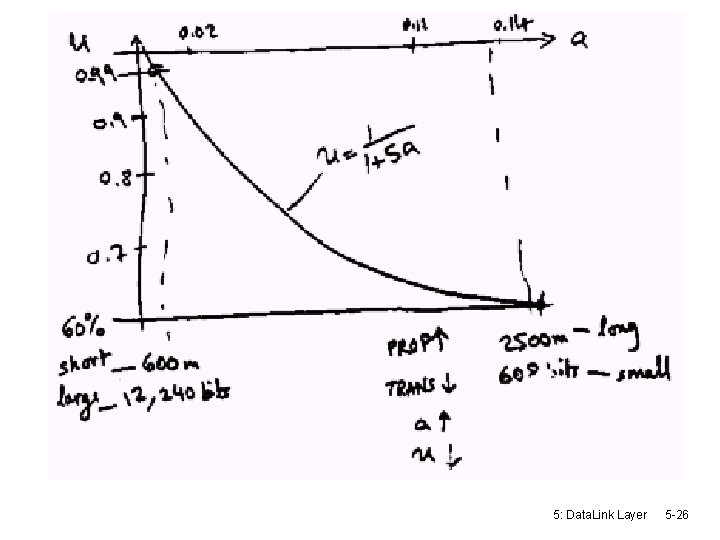
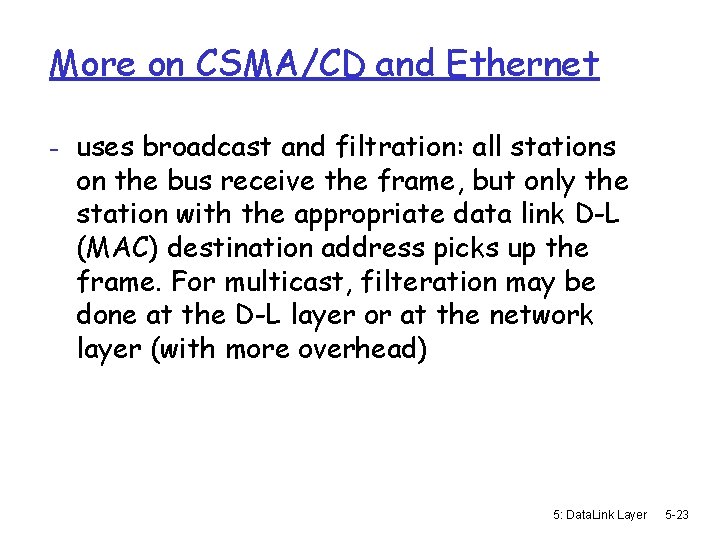
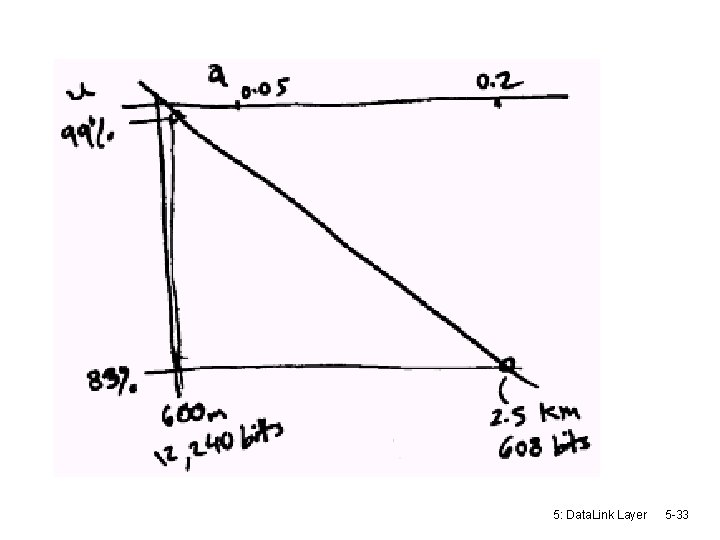
Analyzing CSMA/CD Collision Av. Time wasted ~ 5 Prop Success TRANS - Utilization or ‘efficiency’ is fraction of the time used for useful/successful data transmission 5: Data. Link Layer 5 -24
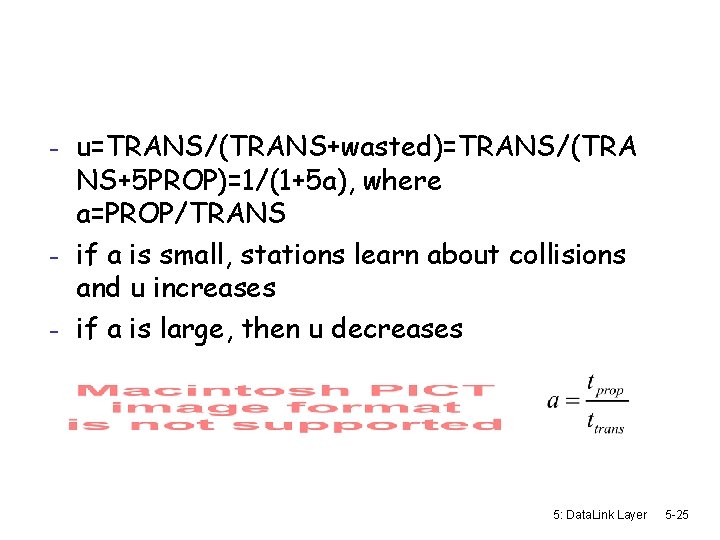
- u=TRANS/(TRANS+wasted)=TRANS/(TRA NS+5 PROP)=1/(1+5 a), where a=PROP/TRANS - if a is small, stations learn about collisions and u increases - if a is large, then u decreases 5: Data. Link Layer 5 -25
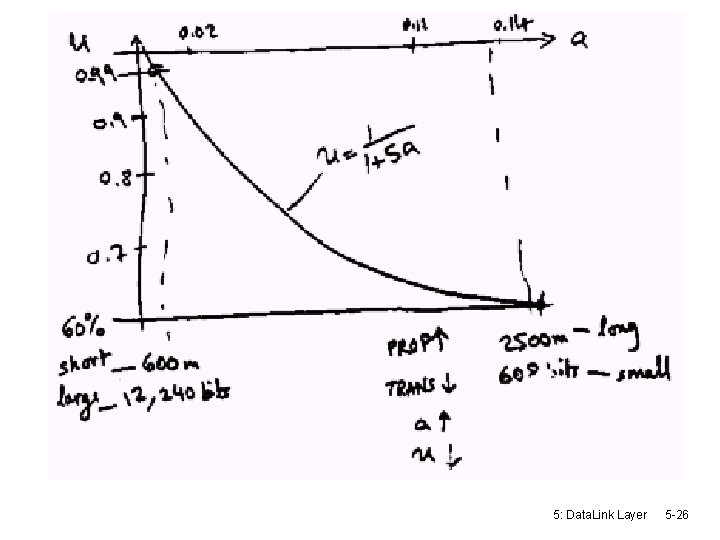
5: Data. Link Layer 5 -26
Collision detection in Wireless r Need special equipment to detect collision at receiver r We care about the collision at the reciever m 1. no-collision detected at sender but collision detected at receiver m 2. collision at sender but no collision at receiver r Neighborhood of sender and receiver are not the same (it’s not a shared wire, but define relatively (locally) to a node [hidden terminal problem] r … more later 5: Data. Link Layer 5 -27
“Taking Turns” MAC protocols channel partitioning MAC protocols: m share channel efficiently and fairly at high load m inefficient at low load: delay in channel access, 1/N bandwidth allocated even if only 1 active node! Random access MAC protocols m efficient at low load: single node can fully utilize channel m high load: collision overhead “taking turns” protocols look for best of both worlds! 5: Data. Link Layer 5 -28
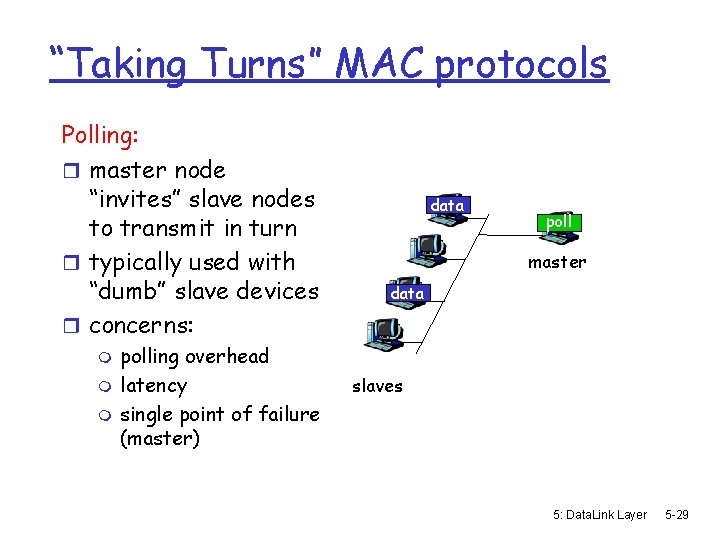
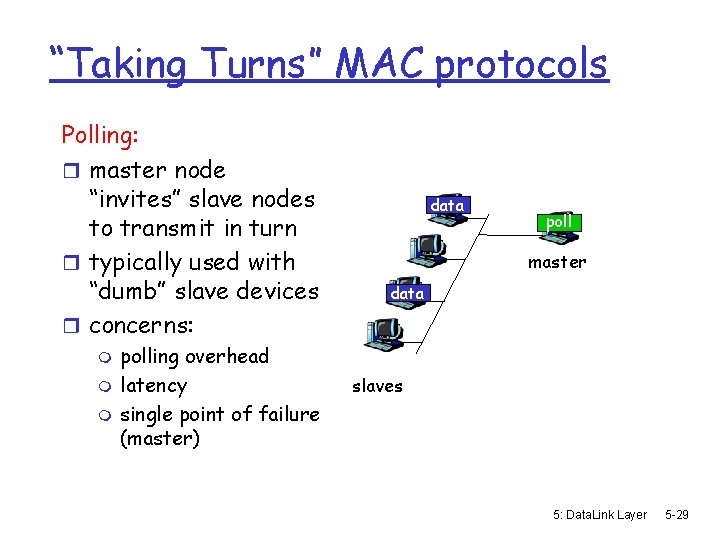
“Taking Turns” MAC protocols Polling: r master node “invites” slave nodes to transmit in turn r typically used with “dumb” slave devices r concerns: m m m polling overhead latency single point of failure (master) data poll master data slaves 5: Data. Link Layer 5 -29
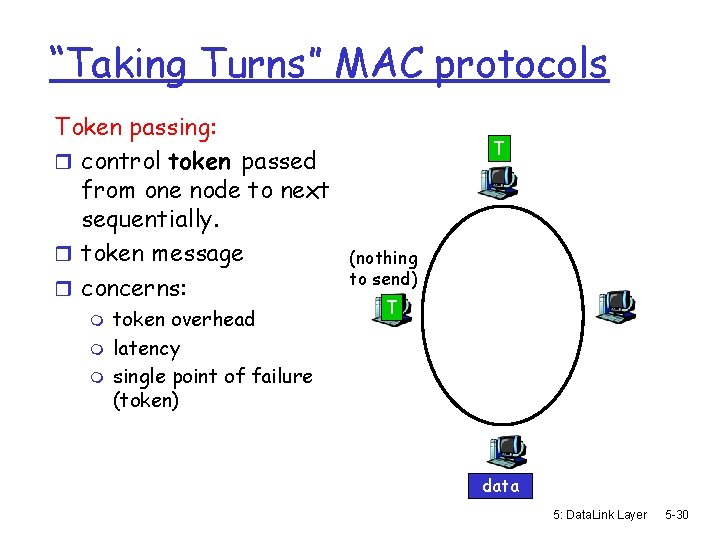
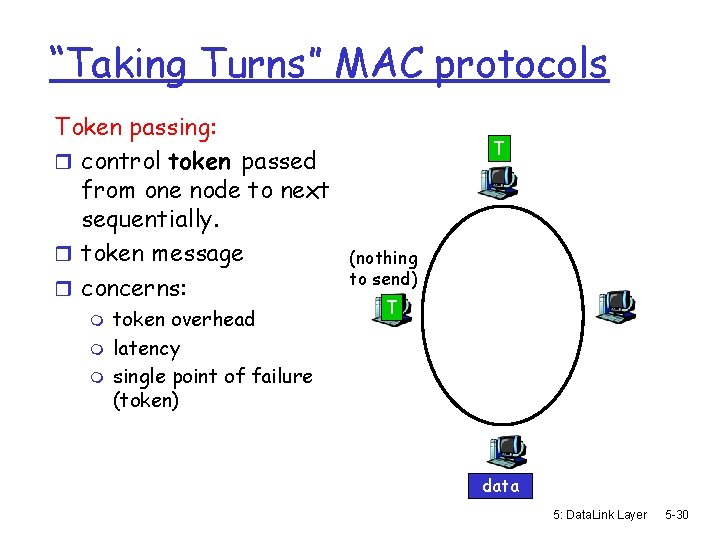
“Taking Turns” MAC protocols Token passing: r control token passed from one node to next sequentially. r token message r concerns: m m m token overhead latency single point of failure (token) T (nothing to send) T data 5: Data. Link Layer 5 -30
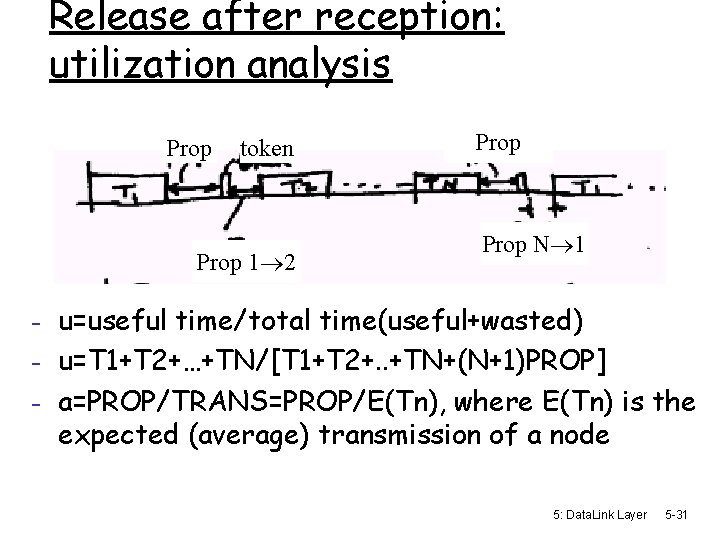
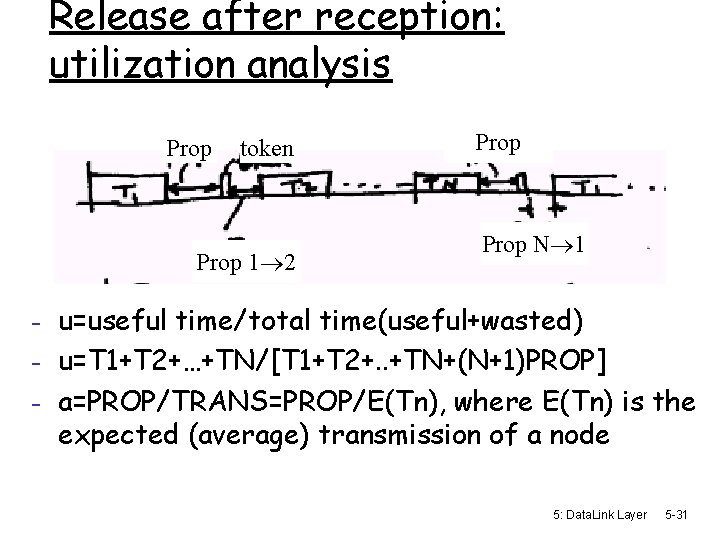
Release after reception: utilization analysis Prop token Prop 1 2 Prop N 1 - u=useful time/total time(useful+wasted) - u=T 1+T 2+…+TN/[T 1+T 2+. . +TN+(N+1)PROP] - a=PROP/TRANS=PROP/E(Tn), where E(Tn) is the expected (average) transmission of a node 5: Data. Link Layer 5 -31
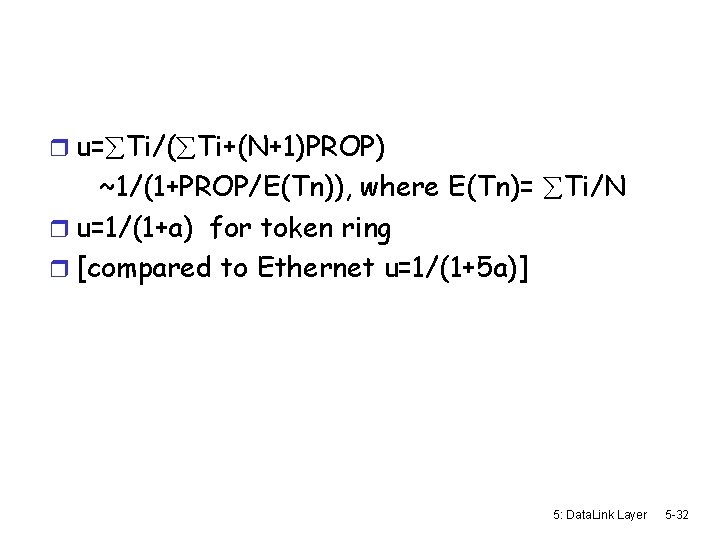
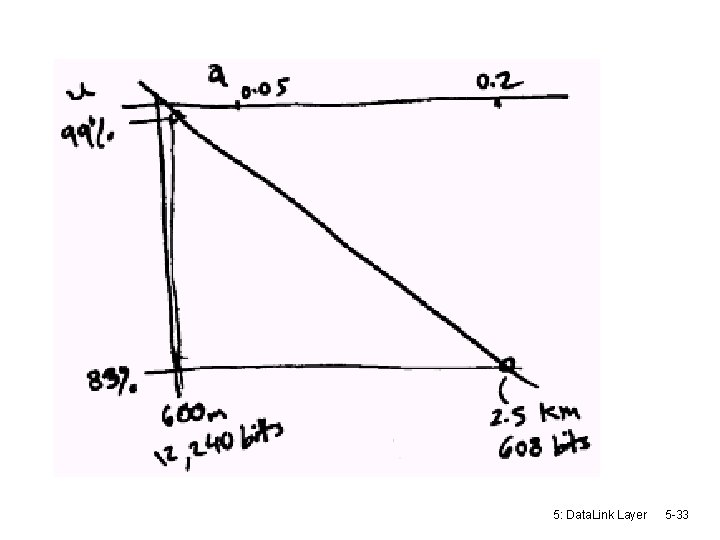
r u= Ti/( Ti+(N+1)PROP) ~1/(1+PROP/E(Tn)), where E(Tn)= Ti/N r u=1/(1+a) for token ring r [compared to Ethernet u=1/(1+5 a)] 5: Data. Link Layer 5 -32
5: Data. Link Layer 5 -33
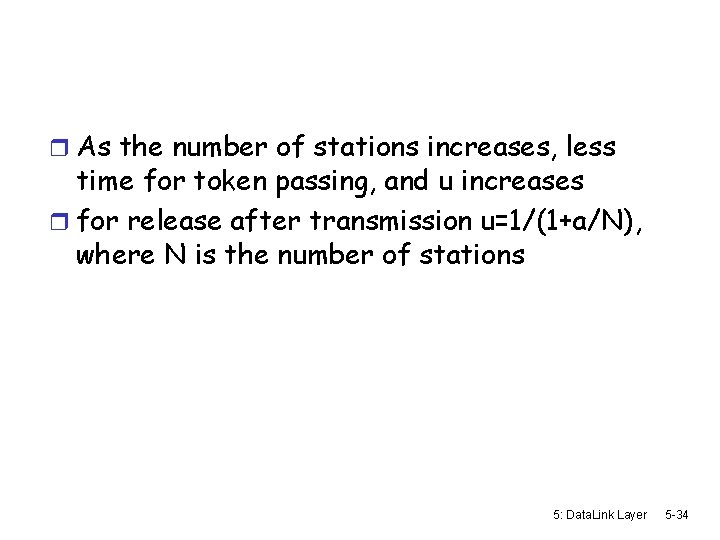
r As the number of stations increases, less time for token passing, and u increases r for release after transmission u=1/(1+a/N), where N is the number of stations 5: Data. Link Layer 5 -34
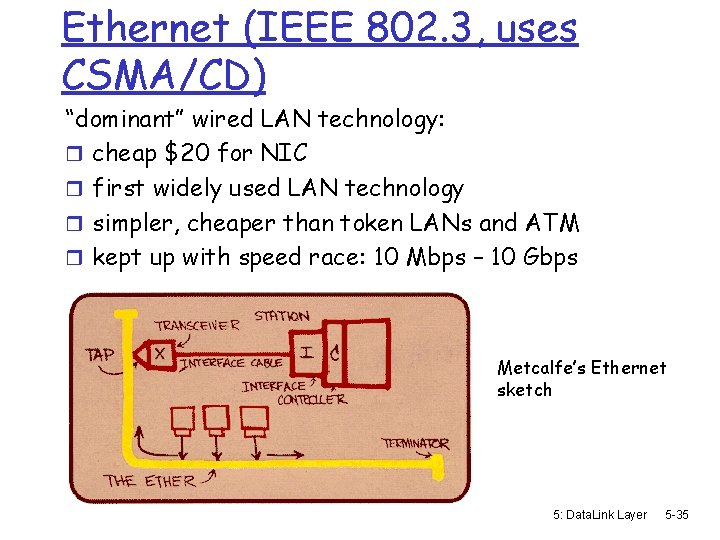
Ethernet (IEEE 802. 3, uses CSMA/CD) “dominant” wired LAN technology: r cheap $20 for NIC r first widely used LAN technology r simpler, cheaper than token LANs and ATM r kept up with speed race: 10 Mbps – 10 Gbps Metcalfe’s Ethernet sketch 5: Data. Link Layer 5 -35
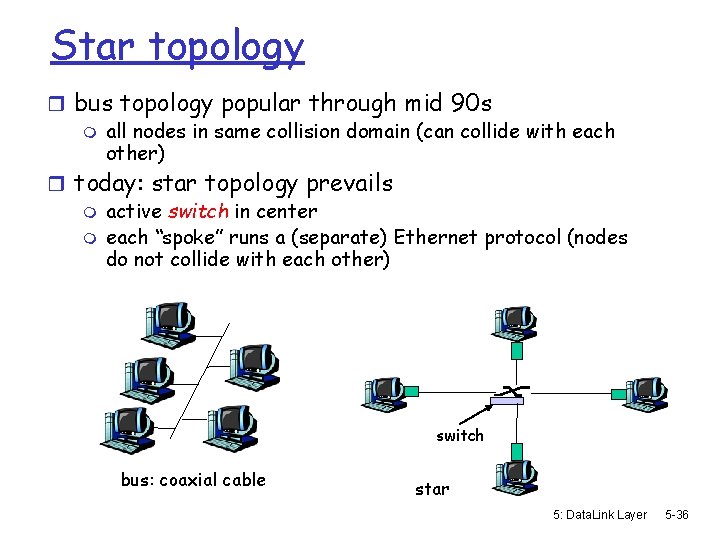
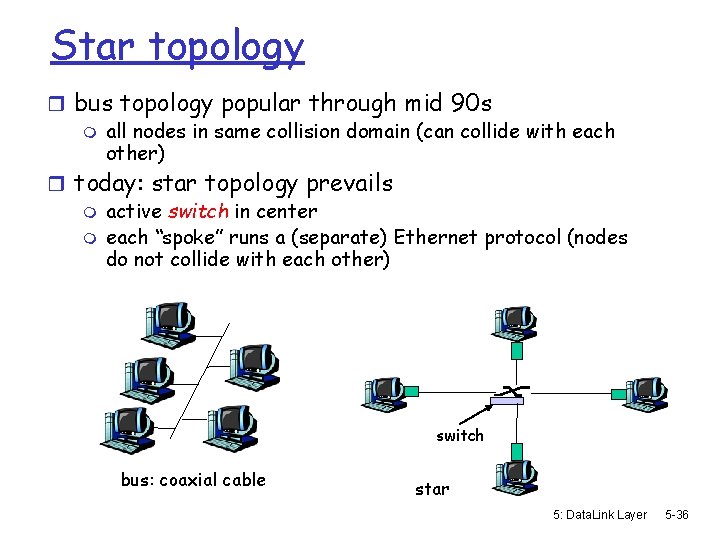
Star topology r bus topology popular through mid 90 s m all nodes in same collision domain (can collide with each other) r today: star topology prevails m active switch in center m each “spoke” runs a (separate) Ethernet protocol (nodes do not collide with each other) switch bus: coaxial cable star 5: Data. Link Layer 5 -36
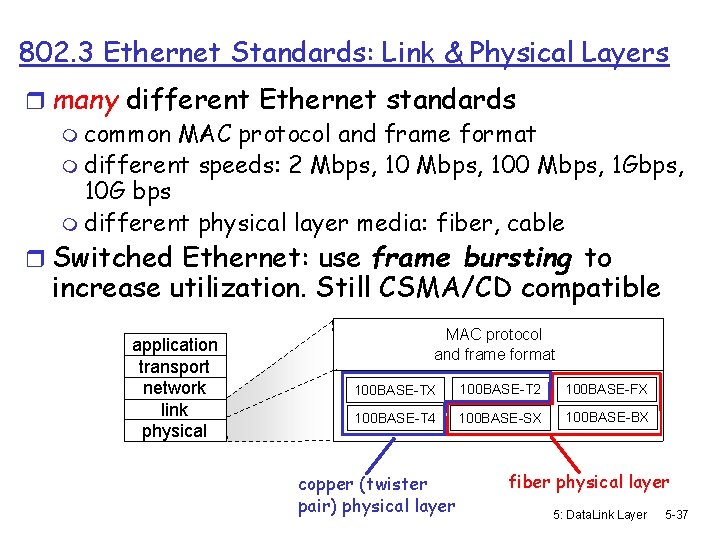
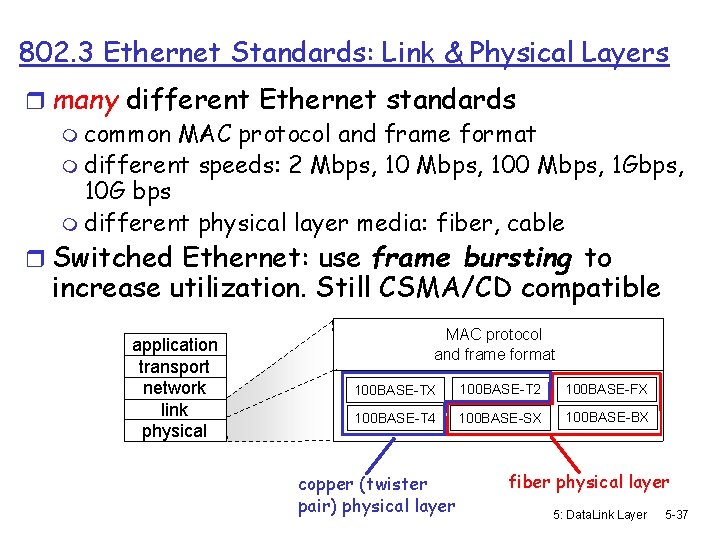
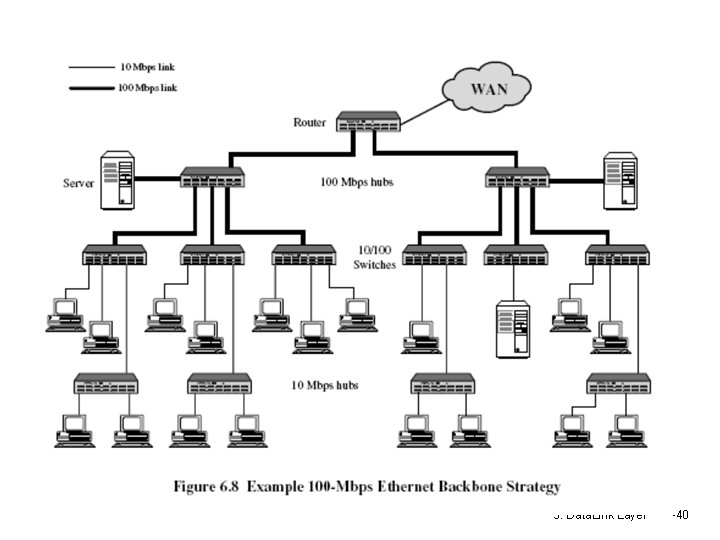
802. 3 Ethernet Standards: Link & Physical Layers r many different Ethernet standards m common MAC protocol and frame format m different speeds: 2 Mbps, 100 Mbps, 1 Gbps, 10 G bps m different physical layer media: fiber, cable r Switched Ethernet: use frame bursting to increase utilization. Still CSMA/CD compatible application transport network link physical MAC protocol and frame format 100 BASE-TX 100 BASE-T 2 100 BASE-FX 100 BASE-T 4 100 BASE-SX 100 BASE-BX copper (twister pair) physical layer fiber physical layer 5: Data. Link Layer 5 -37
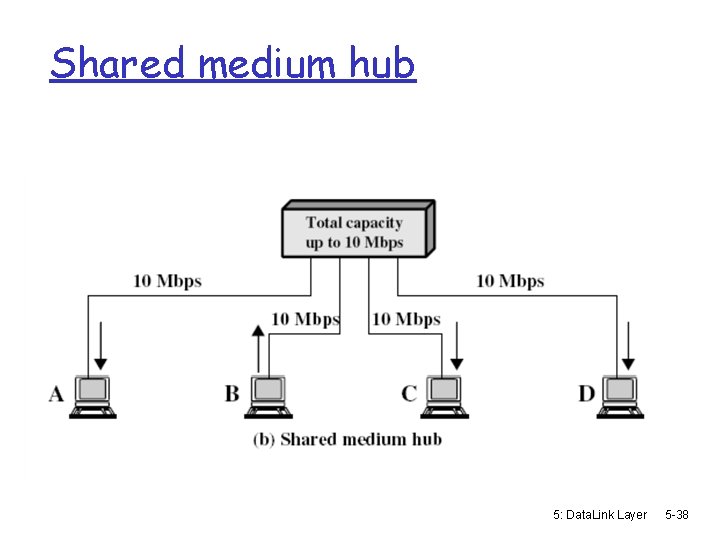
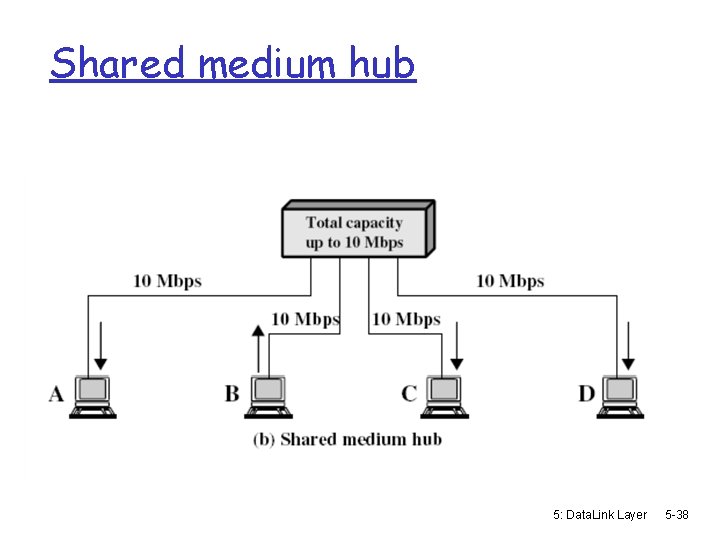
Shared medium hub 5: Data. Link Layer 5 -38
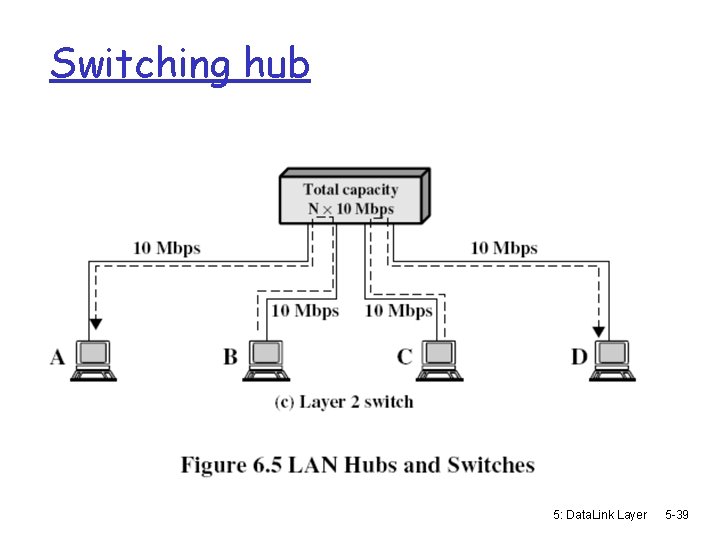
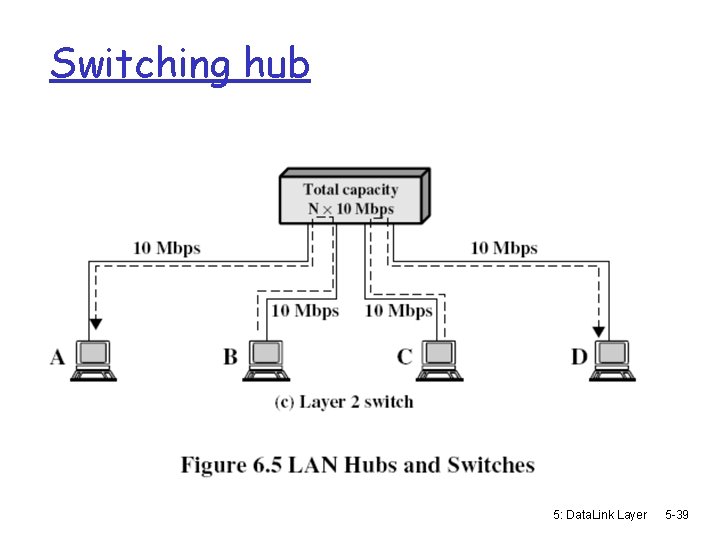
Switching hub 5: Data. Link Layer 5 -39
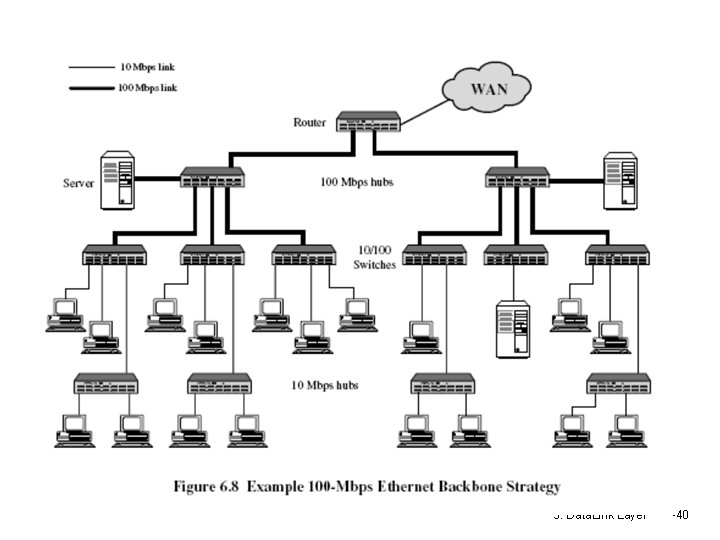
5: Data. Link Layer 5 -40

5: Data. Link Layer 5 -41
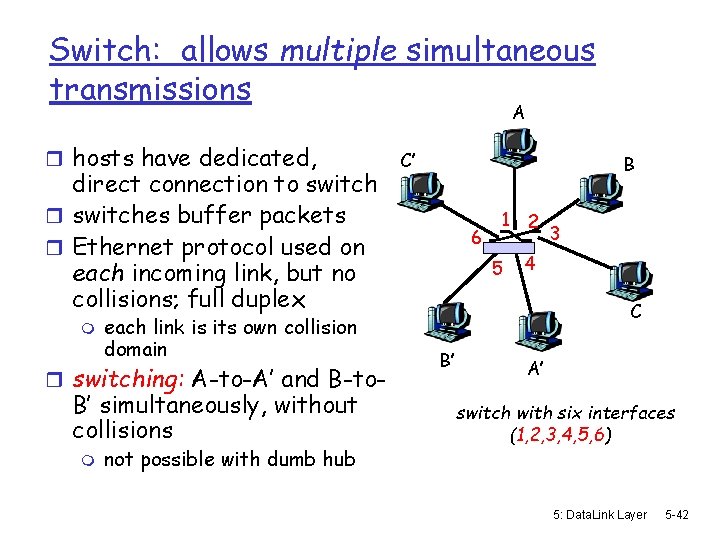
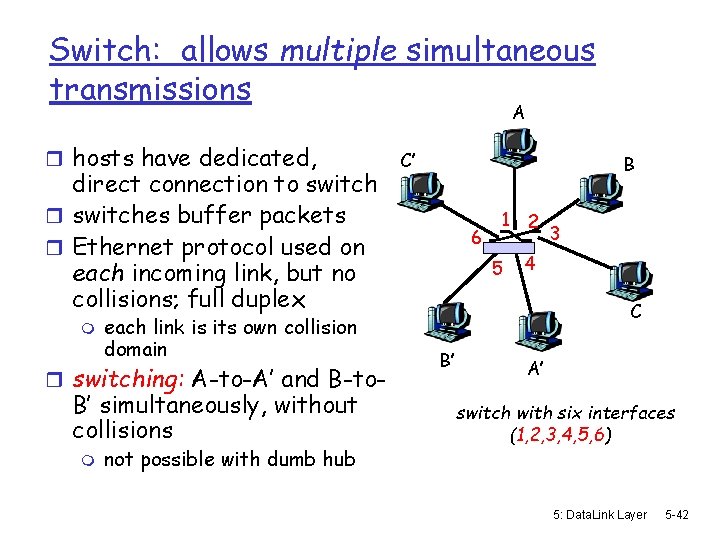
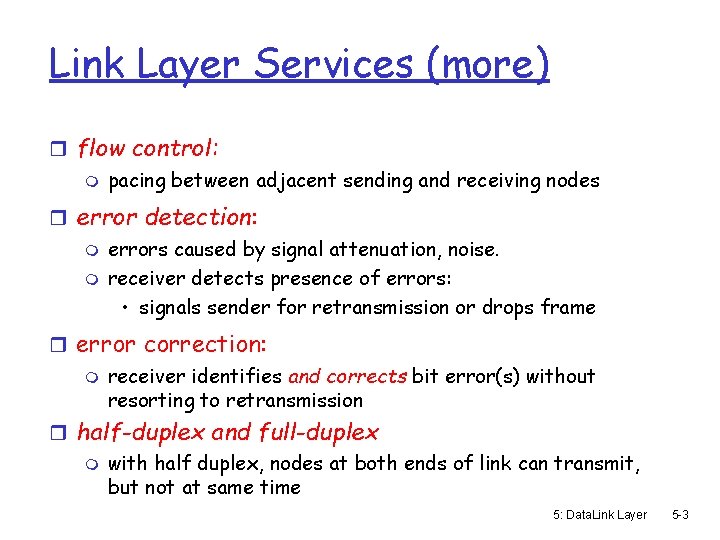
Switch: allows multiple simultaneous transmissions A r hosts have dedicated, direct connection to switch r switches buffer packets r Ethernet protocol used on each incoming link, but no collisions; full duplex m each link is its own collision domain r switching: A-to-A’ and B-to- B’ simultaneously, without collisions m not possible with dumb hub C’ B 6 1 5 2 3 4 C B’ A’ switch with six interfaces (1, 2, 3, 4, 5, 6) 5: Data. Link Layer 5 -42
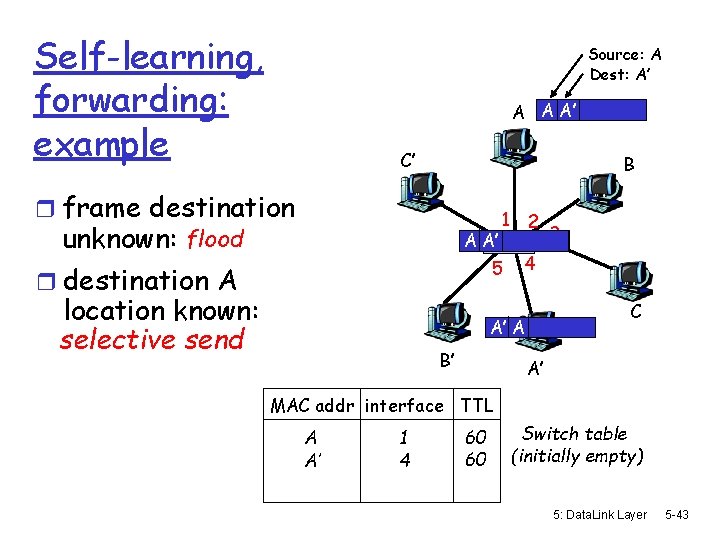
Self-learning, forwarding: example Source: A Dest: A’ A A A’ C’ B r frame destination unknown: flood A 6 A’ 1 2 4 5 r destination A location known: selective send C A’ A B’ 3 A’ MAC addr interface TTL A A’ 1 4 60 60 Switch table (initially empty) 5: Data. Link Layer 5 -43