Worm Wars The Warrior Worm by Rob Iverson
Worm Wars: The Warrior Worm by Rob Iverson and Tevfik Kosar Worm Wars: The Warrior Worm
Outline Ø Introduction Ø Design Strategies Ø Evaluation Ø Problems & Optimizations Ø Conclusion Worm Wars: The Warrior Worm 2
Worm ? ? Ø First described by John Brunner in 1975 in the science fiction novel “the shockwave rider”. Ø Brunner called these programs tapeworms that lived inside the computers and spread themselves to other machines. Worm Wars: The Warrior Worm 3
The Internet Worm Ø Released by Robert Morris Jr. on November 2, 1988, from a machine at MIT Ø Used sendmail and fingerd bugs in BSD 4 Ø Caused thousands of computers on the internet to shut down Ø After 2 days, the worm was removed from most sites Worm Wars: The Warrior Worm 4
The Warrior Worm Project Ø All worms will be running with the same userid Ø Only one process of each worm running at the same time on any host Ø All worms will start after 1 minute initialization time Ø Contest will end if one of the worms gets completely cleaned from the cluster or if the contest time ends Worm Wars: The Warrior Worm 5
Main Strategies Ø Attack Ø Defense Ø Replication Ø Training Worm Wars: The Warrior Worm 6
Attack Ø Destroy enemy Processes Ø Remove enemy files Ø ? ? Worm Wars: The Warrior Worm 7
Destroy Enemy Processes Ø Locate enemy processes – Get list of all processes with same UID • ps command • /proc filesystem – All processes but our own are possibly ENEMY ! Ø Destroy enemy process – kill(enemy_pid, SIGKILL); Worm Wars: The Warrior Worm 8
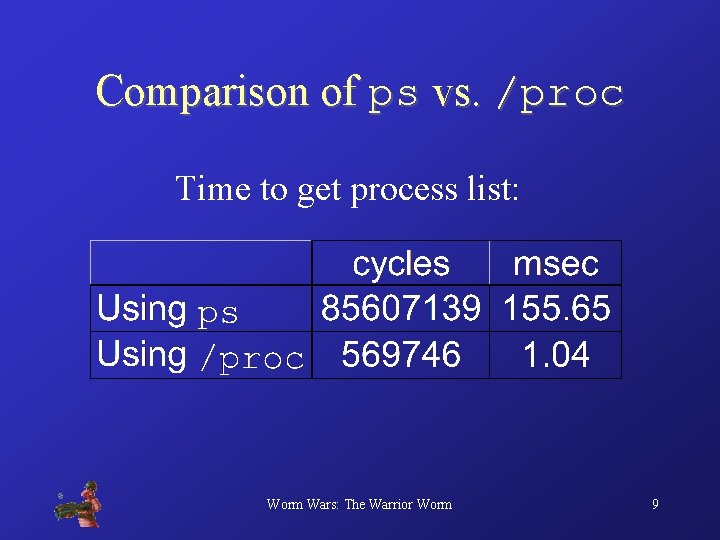
Comparison of ps vs. /proc Time to get process list: Worm Wars: The Warrior Worm 9
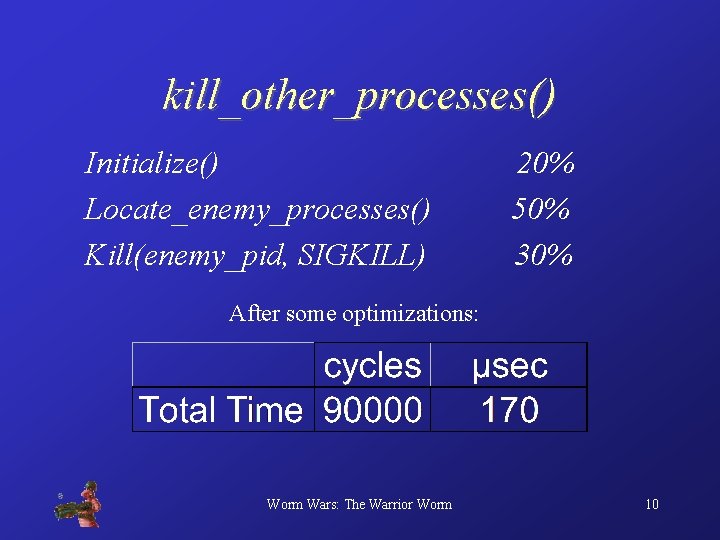
kill_other_processes() Initialize() Locate_enemy_processes() Kill(enemy_pid, SIGKILL) 20% 50% 30% After some optimizations: Worm Wars: The Warrior Worm 10
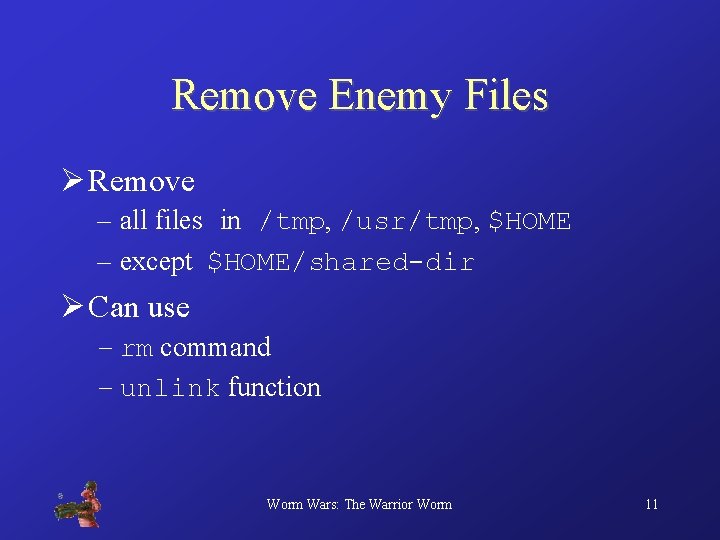
Remove Enemy Files Ø Remove – all files in /tmp, /usr/tmp, $HOME – except $HOME/shared-dir Ø Can use – rm command – unlink function Worm Wars: The Warrior Worm 11
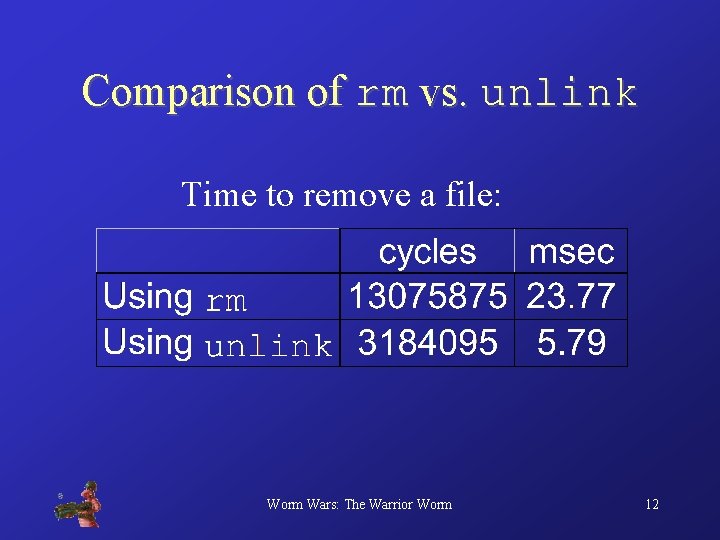
Comparison of rm vs. unlink Time to remove a file: Worm Wars: The Warrior Worm 12
Defense Ø Hide From Enemy Processes Ø Survive Attacks Worm Wars: The Warrior Worm 13
Hide From Enemy Processes Ø Change process id – fork() and let the parent die … Ø Change process name – overwrite argv[0] with a combination of X and Y (also used for authentication) Worm Wars: The Warrior Worm 14
Surviving Attacks Ø Load binary into memory to survive file removal and dump it when necessary Ø After a failed defense, re-infect the machine quickly Worm Wars: The Warrior Worm 15
Replication Ø Decision Ø Infection Ø Synchronization Worm Wars: The Warrior Worm 16
Decision Ø When is a worm "dead" to its peers? – Hello/keepalive messages – timeout to pronounce them dead Ø Who should revive the dead worm? – RRR (Round Robin Resurrection) • reduces repetition • provides for parallelism Worm Wars: The Warrior Worm 17
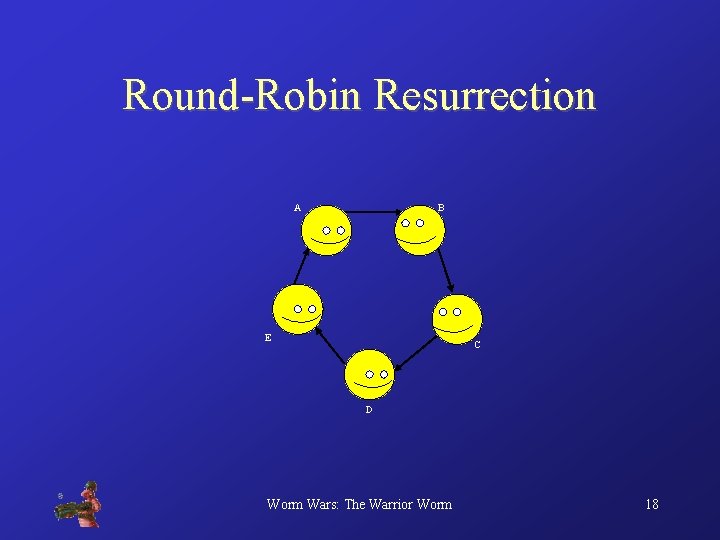
Round-Robin Resurrection A B E C D Worm Wars: The Warrior Worm 18
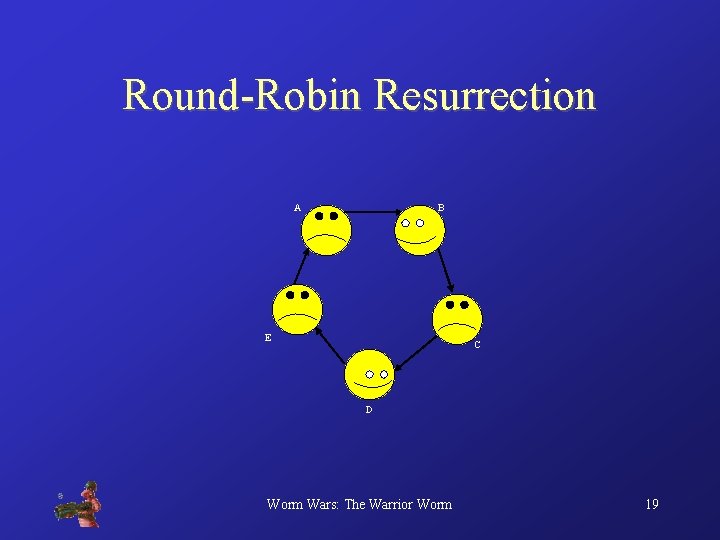
Round-Robin Resurrection A B E C D Worm Wars: The Warrior Worm 19
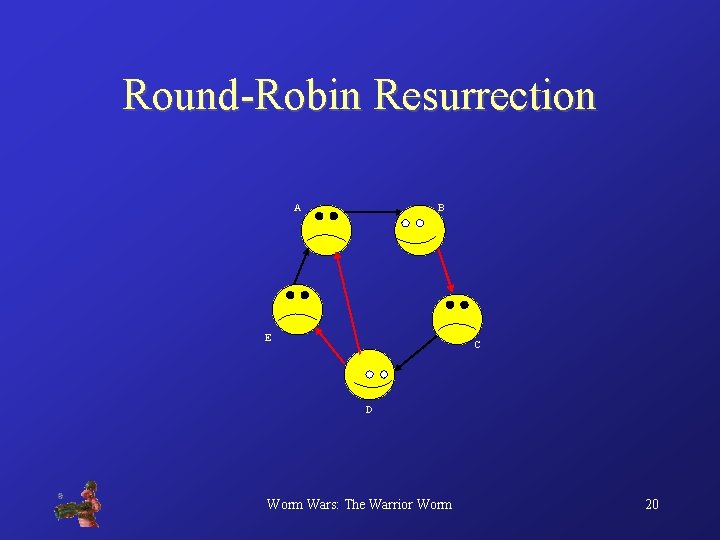
Round-Robin Resurrection A B E C D Worm Wars: The Warrior Worm 20
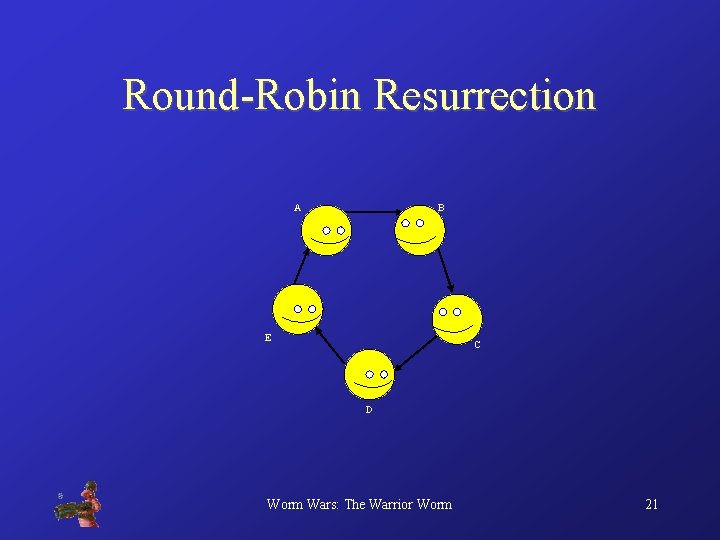
Round-Robin Resurrection A B E C D Worm Wars: The Warrior Worm 21
Messaging System Ø Fixed-size messages – simple handling Ø fields: – message type, sequence, host ID, worm ID – signature – specific data (port/host ID combo) Ø Format: ? ? ? Worm Wars: The Warrior Worm ? ? ? 22
Infection Ø save executable – some shared space like AFS, NFS – rcp/scp another possibility Ø execute ssh – fork/exec to get control back immediately Worm Wars: The Warrior Worm 23
Synchronization Ø NEW CHILD messages – sent to parent of new worm – includes all info necessary to communicate with new worm Ø NEW PEER messages – sent to peers when a new child is created – all communication info Worm Wars: The Warrior Worm 24
Training Ø Worm ID – like a “team” - constant within one worm group, unique to that group Ø Different Parameters – enables comparison and real-life evaluation • which worm won? – optimizing worms for different situations Worm Wars: The Warrior Worm 25
Evaluation Ø Methods – RDTSC - cycle counter on Pentium machines – low overhead, high degree of precision – multiple executions, averaged elapsed time Ø Observations – “Worm Watcher” program – protected pids for observers Worm Wars: The Warrior Worm 26
The Numbers Worm Wars: The Warrior Worm 27
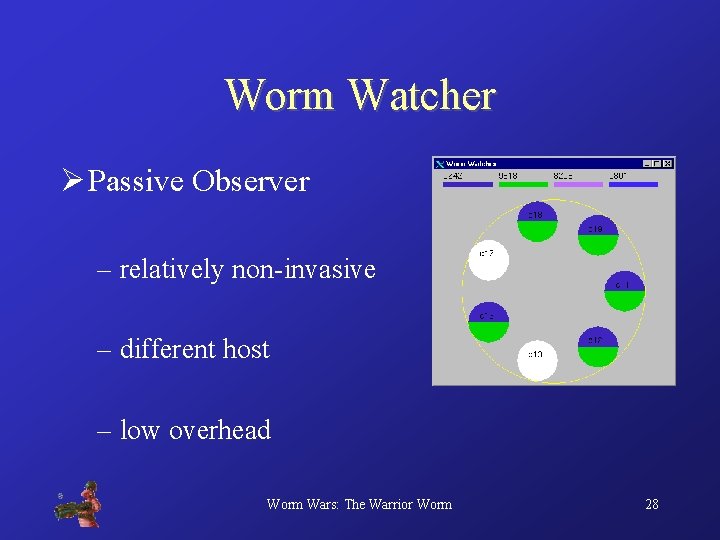
Worm Watcher Ø Passive Observer – relatively non-invasive – different host – low overhead Worm Wars: The Warrior Worm 28
Problems Ø ssh – long wait time – no way to disable encryption – no alternatives (cluster/CSL policy) – possible workarounds Worm Wars: The Warrior Worm 29
Optimizations Ø extra /proc files Ø gethostbyaddr Ø speed up kill_procs() as much as possible Ø other techniques T E R C E S P – kernel-based shit: kill -SEGV – technique #2, use file descriptors TO Worm Wars: The Warrior Worm 30
Conclusions Ø speed is everything – slow worm = dead worm Ø complicated techniques can backfire – no full-featured message-passing system! Worm Wars: The Warrior Worm 31
- Slides: 31