Routing Worm A Fast Selective Attack Worm based
Routing Worm: A Fast, Selective Attack Worm based on IP Address Information Cliff C. Zou, Don Towsley, Weibo Gong, Songlin Cai Univ. Massachusetts, Amherst 1
Routing Worm Summary n n Routing worm: contains information of BGP routing prefixes in the worm code. A faster spreading worm u u u n Internet routable IP space < 30% of entire IPv 4 space. Scanning routable space instead of entire IPv 4 space. Increasing propagation speed by 2 ~ 3. 5 times. A selective attack worm u IP address routing prefix AS ISP, country Ø u Pinpoint attacking vulnerable hosts in a specific target Selective attack based on any information derived from compromised hosts. 2
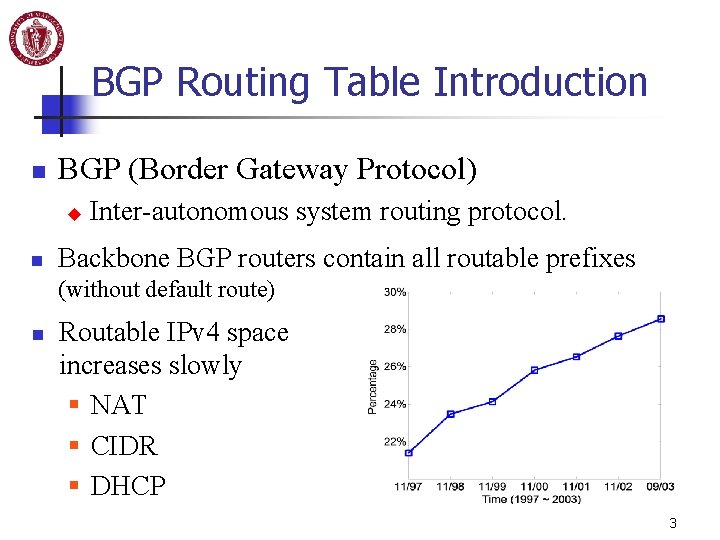
BGP Routing Table Introduction n BGP (Border Gateway Protocol) u n Inter-autonomous system routing protocol. Backbone BGP routers contain all routable prefixes (without default route) n Routable IPv 4 space increases slowly § NAT § CIDR § DHCP 3
BGP Routing Worm n Contains BGP non-overlapping prefixes: u Non-overlapping prefixes: Ø u n 140602 prefixes 62053 prefixes (Sept. 22, 2003) Payload requirement: 175 KB u n Remove “ 128. 119. 85/24” if BGP contains “ 128. 119/16”. Big payload for Internet-scale worm propagation. Increasing worm’s speed by 3. 5 times. u Scanning space is 28. 6% of entire IPv 4 space. 4
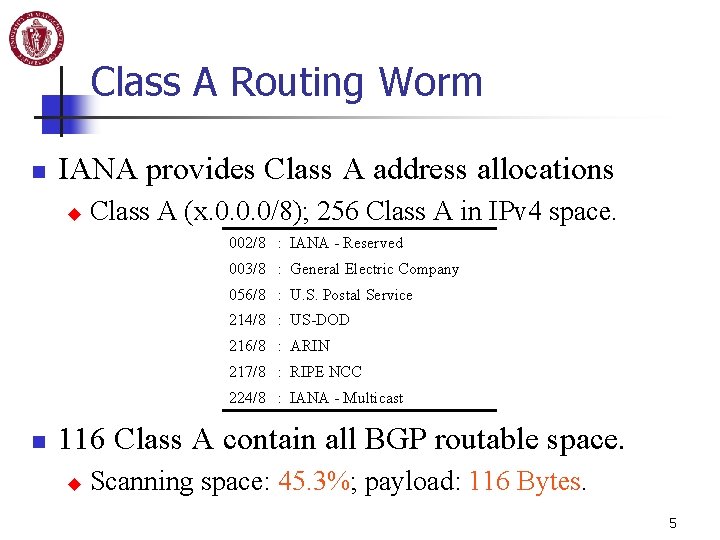
Class A Routing Worm n IANA provides Class A address allocations u Class A (x. 0. 0. 0/8); 256 Class A in IPv 4 space. 002/8 : IANA - Reserved 003/8 : General Electric Company 056/8 : U. S. Postal Service 214/8 : US-DOD 216/8 : ARIN 217/8 : RIPE NCC 224/8 : IANA - Multicast n 116 Class A contain all BGP routable space. u Scanning space: 45. 3%; payload: 116 Bytes. 5

Routing Worm based on Aggregated BGP Prefixes n Two extreme cases of routing worms: u u n BGP routing worm: all prefixes in BGP Class A routing worm: only “/8” prefixes Routing worm based on aggregated prefixes u “/n” aggregation: combine several longer prefixes into a shorter “/n” prefix. Ø “ 128. 119. 5/24” + “ 128. 119. 2/24” “ 128. 119/16” or “ 128. 119. 0/19” Ø Class A prefixes are results of “/8” aggregation. 6
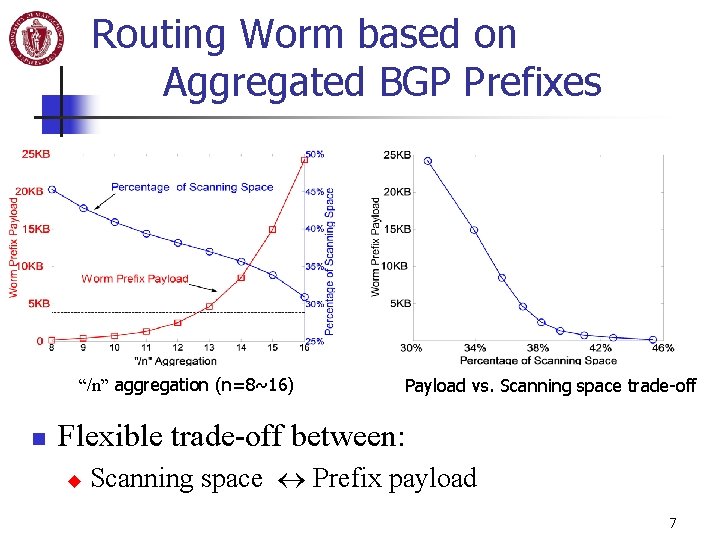
Routing Worm based on Aggregated BGP Prefixes “/n” aggregation (n=8~16) n Payload vs. Scanning space trade-off Flexible trade-off between: u Scanning space Prefix payload 7
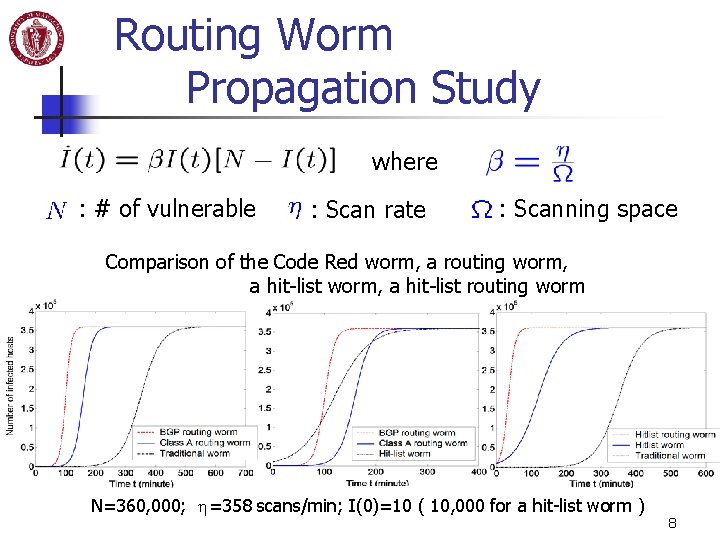
Routing Worm Propagation Study where : # of vulnerable : Scan rate : Scanning space Comparison of the Code Red worm, a routing worm, a hit-list routing worm N=360, 000; h=358 scans/min; I(0)=10 ( 10, 000 for a hit-list worm ) 8
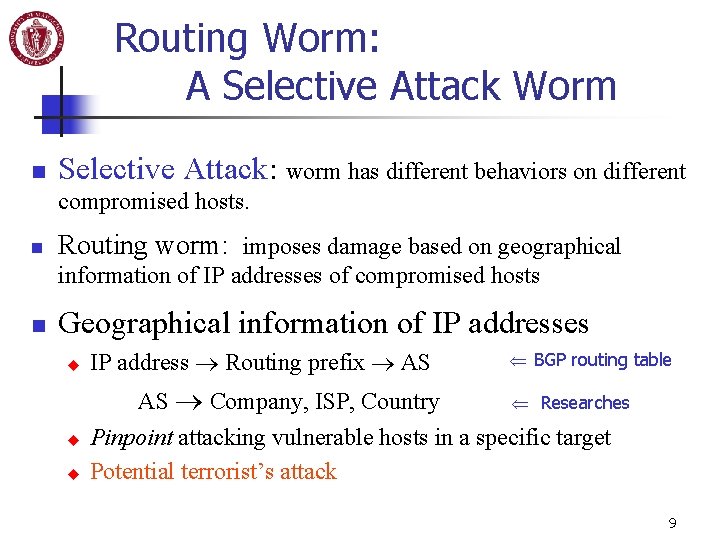
Routing Worm: A Selective Attack Worm n Selective Attack: worm has different behaviors on different compromised hosts. n Routing worm: imposes damage based on geographical information of IP addresses of compromised hosts n Geographical information of IP addresses u u u IP address Routing prefix AS BGP routing table Researches AS Company, ISP, Country Pinpoint attacking vulnerable hosts in a specific target Potential terrorist’s attack 9
Selective Attack: a Generic Attacking Technique n Selective attack: imposes damage based on any information a worm can get from compromised hosts u u u n OS (e. g. : illegal OS, language, time zone ) Software (e. g. : installed a specific program) Hardware ( e. g. : CPU, memory, network card) Selective attack: improving propagation speed u Maximize infectious power of each compromised host. Ø Multi-thread worm: generates different numbers of threads on different computers based on CPU, memory, and connection speed. 10
Defense: Upgrading IPv 4 to IPv 6 n Routing worm: Reducing worm scanning space Effective, easier than hit-list worm to implement u Difficult to prevent: u Ø n public BGP tables and IP geographical information Defense: Increasing worm scanning space Upgrading IPv 4 to IPv 6 u u u The smallest network in IPv 6 has 264 IP address space. A worm needs 40 years to infect 50% of vulnerable hosts in a network when N=1, 000, h=100, 000/sec, I(0)=1000 Limitation: for scan-based worms only 11
Summary n Routing worm: contains information of BGP routing prefixes in the worm code. n Routing worm: a faster spreading worm u u n Scans routable space (< 30%) instead of entire IPv 4 space. Increasing propagation speed by 2 ~ 3. 5 times. Routing worm: a selective attack worm u IP address routing prefix AS Ø u n ISP, Country Pinpoint attacking vulnerable hosts in a specific target Selective attack based on any information a worm can get from compromised hosts. Defense: Increase a worm’s scanning space IPv 4 upgrade to IPv 6 12
- Slides: 12