THREAT ASSESSMENT THREAT MANAGEMENT Employee Assistance Professional Association
- Slides: 39
THREAT ASSESSMENT THREAT MANAGEMENT Employee Assistance Professional Association DORIAN VAN HORN MAY 19, 2016
DORIAN VAN HORN • Senior Consultant with SIGMA Threat Management Associates • President, ATAP Washington DC Chapter • Instructor for the National Center for Campus Public Safety (NCCPS) as an Educational Instructor/Trauma-Informed Sexual Assault Investigation and Adjudication Educational Program under the Department of Justice. • Retired Naval Criminal Investigative Service (NCIS) Special Agent. Division Chief overseeing Threat Management Unit/Insider Threat, Family & Sexual Violence; Supervisory Special Agent; Death, Violent Crime & Cold Case Homicide.
OBJECTIVES 1. What is Threat Assessment? 2. Current Best Practices in Threat Assessment 3. Management 4. Legal 5. Closing and Questions
Purpose of the Threat Assessment • To assist the governments, companies and commands with complex and potentially dangerous investigations. The risk assessment places the communication and/or threatening behavior on a continuum of potential violence and provides recommendations regarding investigative strategies and securityrelated solutions.
PURPOSE OF THREAT ASSESSMENT Threat Assessment can assist with: – Work Place Violence (WPV)/Insider Threat – Sexual Assault – Stalking – Wrongful Destruction – School Violence – Threatening Communications – Murder for Hire – Serial Crimes such as Rape, Child Abuse, Bomb Threats – High Risk Domestic Violence – Espionage
WORKPLACE VIOLENCE: WHAT DO WE FEAR? Fort Hood Navy Yard Shooting Wiki. Leaks Snowden San Bernardino
INSIDER THREAT • WPV – Will not know if the disgruntled employ will try to sell secrets, will come into the work place and kill co-workers, will go home and beat up his wife – Need to look at motivation (religious or political extremism; angry with the system; financial, etc) – Need to determine how to best stop the behavior
INSIDER THREAT • Can’t profile a terrorist • Look for the CRIMINAL activity • Example: FT Hood/WIKILEAKS—they were not impulsive or reactive—they were was planned and purposeful • Domestic Violence – Restraining Orders
Beyond Mass Shootings: A broad range of issues impact the safety & well-being workplace: Harassment & Bullying Bias-related incidents Stalking Domestic abuse Sexual assault Substance abuse Suicide
• • Results of Workplace Violence Psychological impairment Property damage and theft Reduced productivity Diversion of management resources Increased security costs Increased personnel costs Increased worker’s compensation costs Employer liability
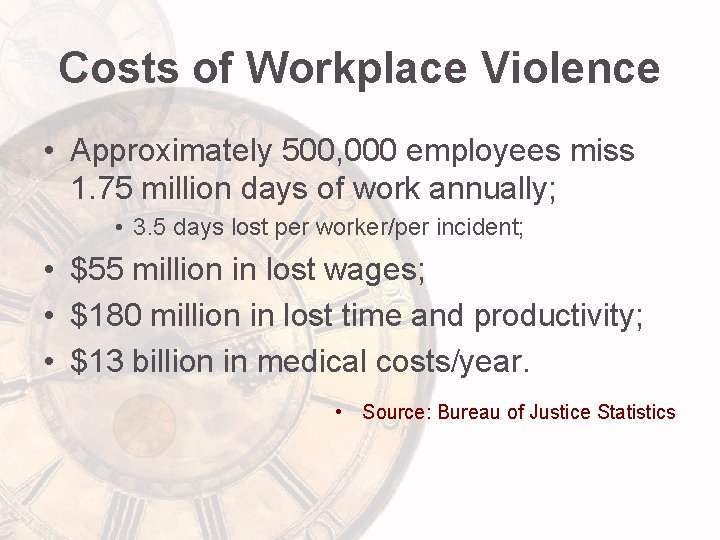
Costs of Workplace Violence • Approximately 500, 000 employees miss 1. 75 million days of work annually; • 3. 5 days lost per worker/per incident; • $55 million in lost wages; • $180 million in lost time and productivity; • $13 billion in medical costs/year. • Source: Bureau of Justice Statistics
GOAL OF THREAT ASSESSMENT & MANAGEMENT • PREVENT VIOLENCE • RESOLVE the PERCIEVED CONFLICT
BEHAVIORAL BASED THREAT/RISK ASSESSMENT • Does there have to be a crime? NO
“…there is no such thing as a psycho” All behavior is understandable, goal oriented, tension reducing, and problem solving Harvey Schlossberg-NYPD
Keys to Threat Assessment • Identify potential attackers • Assess verbal, written and unstated threats/concerns • Know the pre-attack behaviors • Understand the continuum of idea to action • Interrupt forward motion
Keys to Threat Assessment • Goal is to assess behaviors associated with targeted violence to help identify and understand the subject’s motivation and future behavior • Open ended assessment of behavioral patterns & motivations • Identify targets & potential attackers • Assess verbal, written, and unstated threats • Identify patterns of behavior & pre-attack behaviors • Assess frequency, recency, & severity of contacts • Assess location on idea-to-action continuum • Interrupt forward motion
Threat Assessment Threat assessment offers consultation services in the following areas: – Risk assessment: indicators and patterns of escalation toward targeted violence – Evaluation of threatening, intimidating and harassing statements/behaviors – Analysis of stalking/surveillance behaviors – Use of boundary probes as monitors of escalating violence
Implications for Prevention § Many targeted attacks can be prevented. § A person’s ideas and plans for violence may be detectable before harm can occur. § Information is likely to be scattered and fragmented. § Team should act quickly upon initial report, gather information and pieces of the puzzle, and assemble the information to see is person is on pathway to violence. – Threat assessment and case management is not an adversarial process. Engagement with a person of concern can be critical to preventing violence or harm.
Why Threat Assessment? Recommended by: – Defense Science Board Task Force on Predicting Violent Behavior (2012) – ASIS / SHRM Workplace Violence Prevention and Intervention (ANSI-approved National Standard) – FBI Task Force Report – Other Sectors: • • Protective agencies (USSS, USCP, State Dept) Judicial Security (US DOJ/OIG) Higher Education (ANSI-approved national standard) K 12 Schools (USSS/ED model)
SUICIDE • Suicide? Homicide? – Threat Assessment Professionals know all too well that it is never a good thing when perpetrators think too much about death – What starts out as suicidal ideation or intent can rapidly switch to homicidal or homicide/suicide
LEGAL ISSUES IN THREAT ASSESSMENT
Legal Duties • Duties to employees • Duty to control employees • Special relationships • Duties to customers, clients, students & other third parties on premises • Theories of liability – Negligent hiring, supervision, training or retention – Breach of contract
LEGAL CONSIDERATIONS • Federal American with Disability Act and Section 504 of the Rehabilitation Act • State Public Accommodation Laws/Disability Related Employment Laws • HIPPA • CHECK WITH LEGAL
Standards of Care: • ANSI-approved national standard (ASIS / SHRM) • Common practice (e. g. , USSS, USCP, DPS, USMS, USPS) • Post-incident investigative guidance (OSHA)
• GUIDING PRINCIPLES • & • BEST PRACTICES
Threat Assessment Principles Violence is a dynamic process – Not asking whether this is a “violent person. ” – Looking at changes in circumstances, situation, and its impact on the person in question.
Threat Assessment Principles Threat assessment is about behavior, not profiles – There is no accurate or useful profile of a “campus shooter” or “workplace shooter. ” – Focus is on behavior that suggests a potential for harm OR some need for assistance.
Threat Assessment Principles Determine if situation poses a threat – Critical question is about behavior along a pathway toward harm. – Focus is not solely on whether the person made a threat. – Expressed threats (or the lack thereof) are not reliable indicators.
Threat Assessment Principles Safety is a primary focus – Safety is guiding mission of all threat assessment and management efforts. – Assessment and management steps are all tools toward the goal of safety.
CASE MANAGEMENT PLANNING AND IMPLEMENTATION
Case Management Develop an individualized plan based on information gathered in the investigation and other facts known about the person – Case management is more art than science. – Plan must be fact-based and person-specific. – Engagement can be critical, even when dealing with someone who is very angry. – Distancing makes monitoring and intervention more difficult. – Personalities matter.
COMMON PROBLEMS AND SOLUTIONS
Common Problems – Do you have a team? Solutions – Lack of training for team: • Formal training in threat assessment and management • Trainer(s) not qualified / vetted – Team and / or workplace misunderstanding of HIPAA, ADA: – Insufficient investigation, communication • Solution: Follow best practices procedures, be sure to also consider victim management and witness follow-up
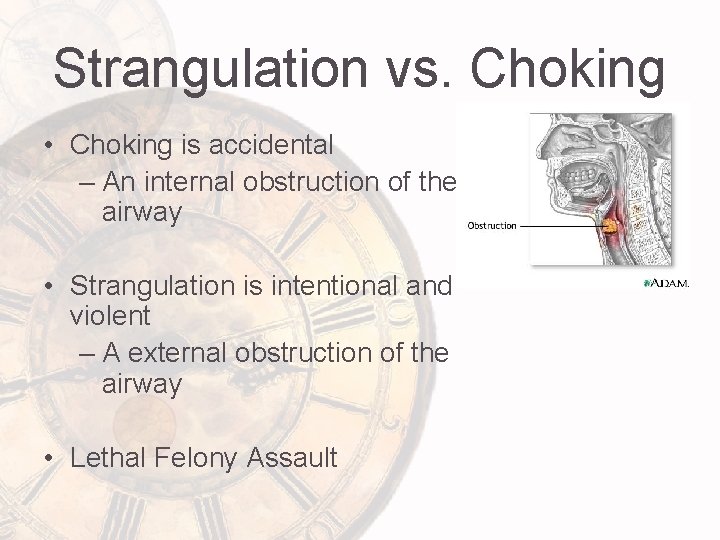
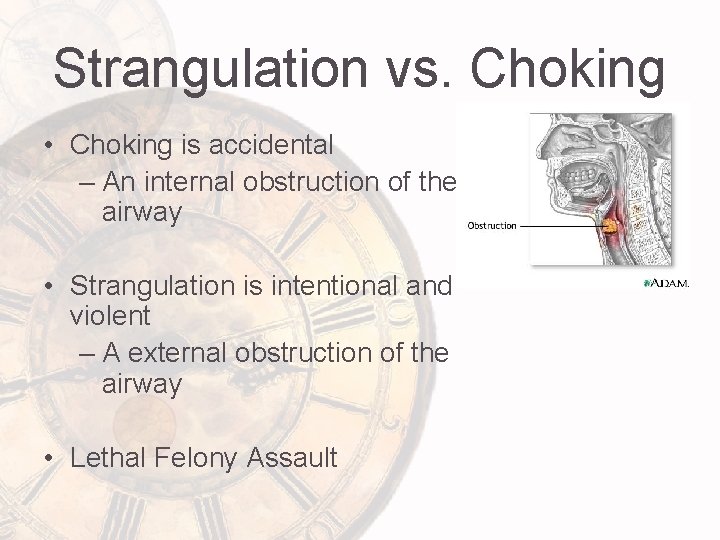
Strangulation vs. Choking • Choking is accidental – An internal obstruction of the airway • Strangulation is intentional and violent – A external obstruction of the airway • Lethal Felony Assault
Strangulation • Strangulation commonly seen in: – domestic violence cases – serial murder • In strangulation cases, the S/ exercises power and control over a V/.
SUMMARY / Q&A
Summary § Prevention is possible; using a team helps. § Current best practices recommend standard procedures and supporting resources, in addition to a team. § Threat assessment procedures involve seeking out information, answering standard investigative questions, and making an informed assessment. § Effective case management requires implementation and monitoring, as well as planning and creative use of resources.
“In the End, we will remember not the words of our enemies, but the silence of our friends. ” Martin Luther King
DORIAN VAN HORN 703 -314 -0566