Cyberoam Unified Threat Management Identitybased Unified Threat Management
Cyberoam - Unified Threat Management Identity-based Unified Threat Management One Identity – One Security

Cyberoam - Unified Threat Management Agenda • • • Evolution of IT Security Challenges of Unified Threat Management Introduction to Cyberoam UTM Cyberoam Product Walk-thru Cyberoam Credentials Awards & Accreditations
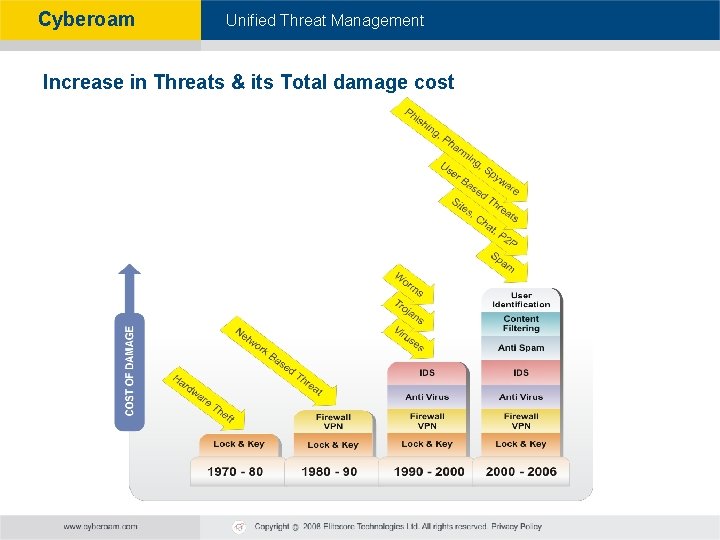
Cyberoam - Unified Threat Management Increase in Threats & its Total damage cost
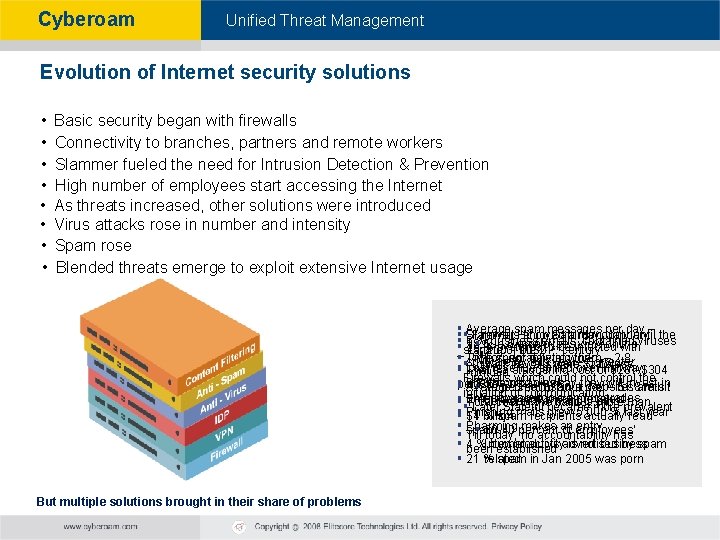
Cyberoam - Unified Threat Management Evolution of Internet security solutions • • Basic security began with firewalls Connectivity to branches, partners and remote workers Slammer fueled the need for Intrusion Detection & Prevention High number of employees start accessing the Internet As threats increased, other solutions were introduced Virus attacks rose in number and intensity Spam rose Blended threats emerge to exploit extensive Internet usage §§§Slammer Hit on Saturday, January Average spam messages per day – Firewalls enjoyed a monopoly until the §§ 6 % business emails contained viruses 18. 5 § 1 in 5 employees view online st century 25 % systems to be infected with starting of the 21 25, 2003, 0030 – IBM §§Time spent deleting them – 2. 8 pornography at work spyware by this year– Forrester Initial Firewalls were Stateless § That’s a staggering cost of $281 -$304 Lost revenue spilled over halfway mintues. Firewalls which could not control the into the next week §§per PC 65 % companies say they will invest in Average time lost in a day – 51. 8 mts § 70 percent of adult websites are hit initiation of communication anti-spyware tools and upgrades §§ Email became more prevalent between 9 am and 5 pm Total cost of the bailout: more than Later Stateful became more prevalent §§§$1 billion Phishing mails grew 5, 000 % last year 14 % spam recipients actually read § Pharming makes an entry spam § 30 -40 percent of employees' § Till today, no accountability has § been established 4 % buy products advertised by spam Internet activity is not business § 21 % spam in Jan 2005 was porn related But multiple solutions brought in their share of problems
Cyberoam - Unified Threat Management Current Challenges due to Multiple Internet Security Solutions • • • Higher purchase cost of Individual Appliances Problems in handling multiple Maintenance & Subscription Contracts Requirement of highly Technical man power to maintain Multiple Appliances & Solutions Difficult for a single network admin to handle increasing complexity of LAN Networks Excessive time taken to understand threat patterns with Individual Reports by Appliances Inadequacy in handling new blended attacks Need For Single Unified Appliance for all Internet Security Problems
Cyberoam - Unified Threat Management UTM : Unified Threat Management A solution to fight against multiple attacks and threats
Cyberoam - Unified Threat Management UTM Unified threat management (UTM) refers to a comprehensive security product which integrates a range of security features into a single appliance. A true UTM Appliance should have following features in single solution: 1. Firewall 2. VPN 3. Intrusion Prevention System 4. Gateway Level Anti-virus for Mails, Website, File Transfers 5. Gateway level Anti-spam 6. Content Identification & Filtering 7. Bandwidth Management for Applications & Services 8. Load Balancing & Failover Facilities UTM
Cyberoam - Unified Threat Management Benefits of UTM Appliances Reduced complexity All-in-one approach simplifies product selection, integration and support Easy to deploy Customers, VARs, VADs, MSSPs can easily install and maintain the products Remote Management Remote sites may not have security professionals – requires plug-&-play appliance for easy installation and management Better Man Power Management Reduction in dependency and number of high-end skilled Human resources Managed Services Security requirements & day to day operations can be outsourced to MSSPs
Cyberoam - Unified Threat Management Challenges with Current UTM Products Lack of user Identity recognition and control § Inadequate in handling threats that target the user – Phishing, Pharming Unable to Identify source of Internal Threats § Employee with malicious intent posed a serious internal threat § Indiscriminate surfing exposes network to external threats § 50 % of security problems originate from internal threats – Yankee Group § Source of potentially dangerous internal threats remain anonymous Unable to Handle Dynamic Environments § Wi-Fi § DHCP Unable to Handle Blended Threats § Threats arising out of internet activity done by internal members of organization § External threats that use multiple methods to attack - Slammer Lack of In-depth Features § Sacrificed flexibility as UTM tried to fit in many features in single appliance. § Inadequate Logging, reporting, lack of granular features in individual solutions Need for Identity based UTM…
Cyberoam - Unified Threat Management Patent pending: Identity-based technology User
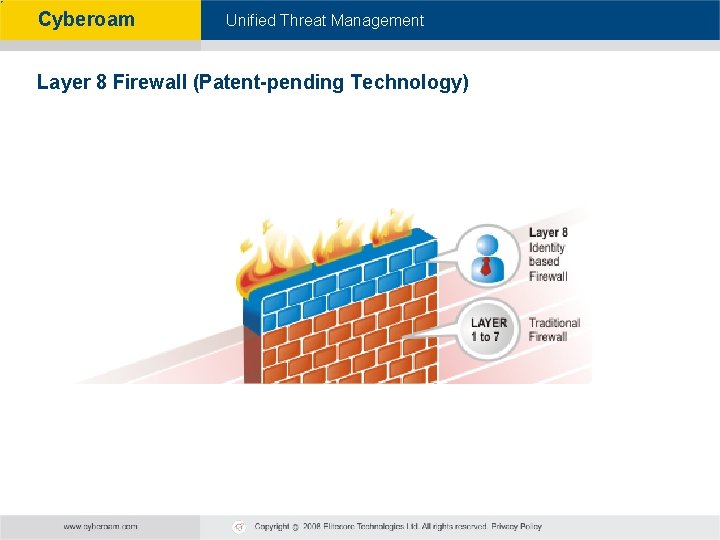
Cyberoam - Unified Threat Management Layer 8 Firewall (Patent-pending Technology)

Cyberoam - Unified Threat Management Cyberoam – Identity Based Security Cyberoam is the only Identity-based Unified Threat Management appliance that provides integrated Internet security to enterprises and educational institutions through its unique granular user-based controls.
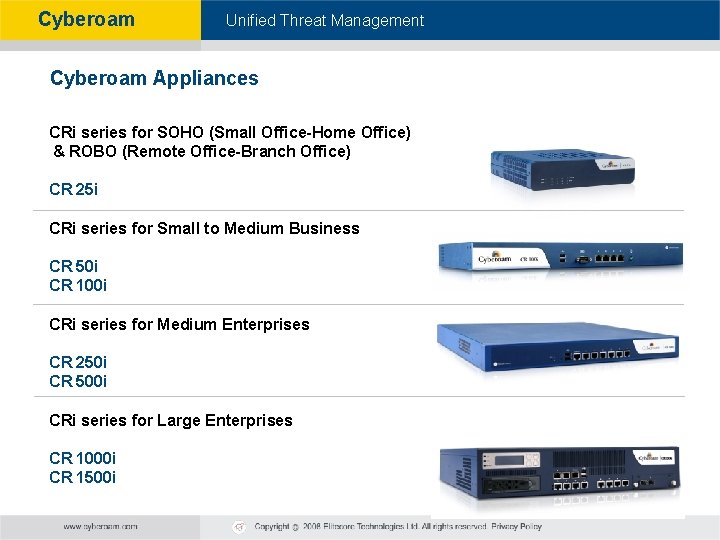
Cyberoam - Unified Threat Management Cyberoam Appliances CRi series for SOHO (Small Office-Home Office) & ROBO (Remote Office-Branch Office) CR 25 i CRi series for Small to Medium Business CR 50 i CR 100 i CRi series for Medium Enterprises CR 250 i CR 500 i CRi series for Large Enterprises CR 1000 i CR 1500 i
Cyberoam - Unified Threat Management Identity - based UTM
Cyberoam - Unified Threat Management Cyberoam Product walk thru
Cyberoam - Unified Threat Management Cyberoam Unified Threat Management Features Cyberoam offers comprehensive threat protection with: • • • Identity-based Firewall VPN Gateway Anti-Virus Gateway Anti-Spam Intrusion Prevention System Content Filtering Bandwidth Management Multiple Link Management On-Appliance Reporting
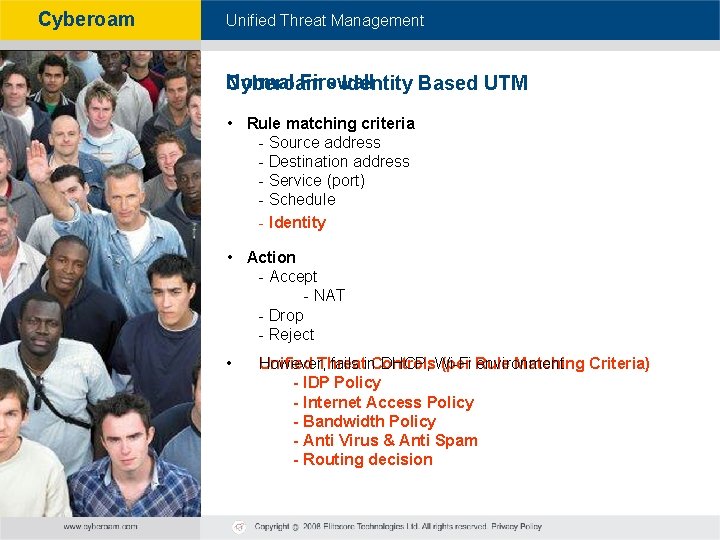
Cyberoam - Unified Threat Management Normal Firewall Cyberoam - Identity Based UTM • Rule matching criteria - Source address - Destination address - Service (port) - Schedule - Identity • Action - Accept - NAT - Drop - Reject • However, fails in DHCP, Wi-Fi environment Unified Threat Controls (per Rule Matching Criteria) - IDP Policy - Internet Access Policy - Bandwidth Policy - Anti Virus & Anti Spam - Routing decision
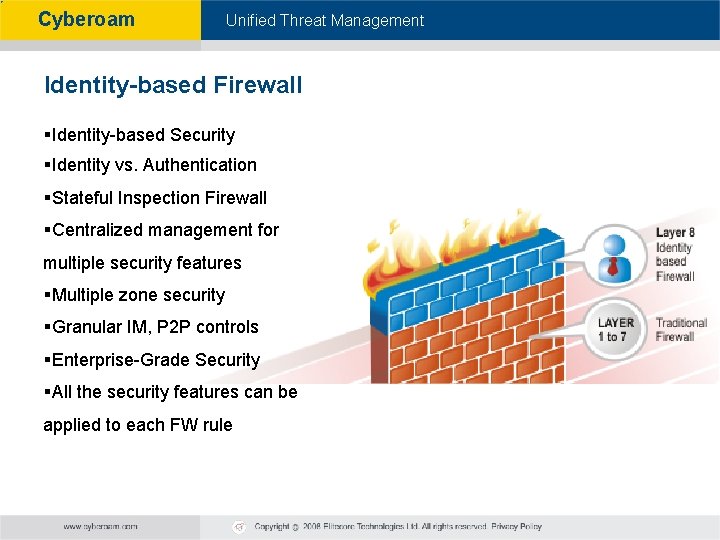
Cyberoam - Unified Threat Management Identity-based Firewall §Identity-based Security §Identity vs. Authentication §Stateful Inspection Firewall §Centralized management for multiple security features §Multiple zone security §Granular IM, P 2 P controls §Enterprise-Grade Security §All the security features can be applied to each FW rule
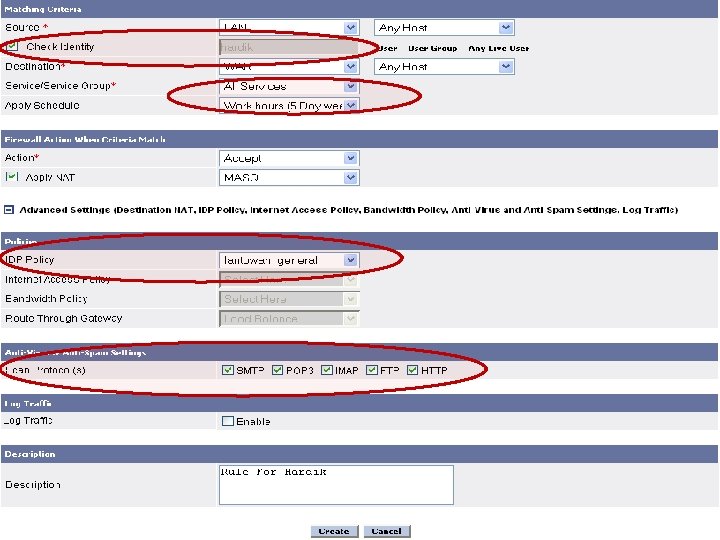
Cyberoam - Unified Threat Management
Cyberoam - Unified Threat Management Gateway Anti-Virus
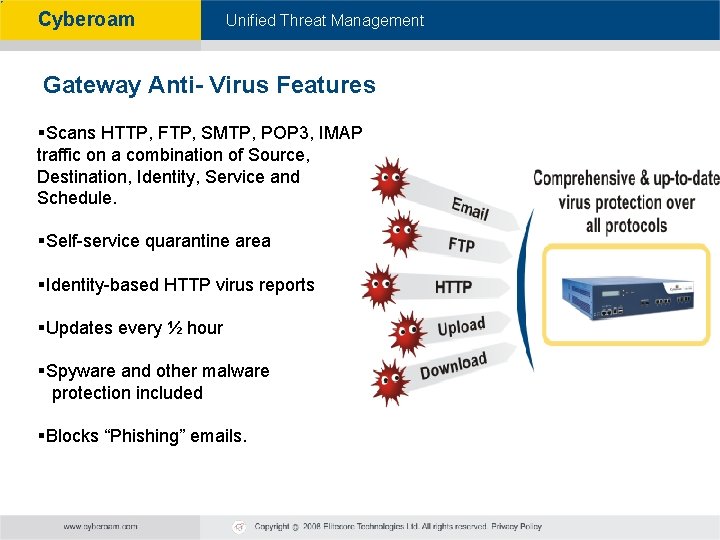
Cyberoam - Unified Threat Management Gateway Anti- Virus Features §Scans HTTP, FTP, SMTP, POP 3, IMAP traffic on a combination of Source, Destination, Identity, Service and Schedule. §Self-service quarantine area §Identity-based HTTP virus reports §Updates every ½ hour §Spyware and other malware protection included §Blocks “Phishing” emails.
Cyberoam - Unified Threat Management Gateway Anti-Spam
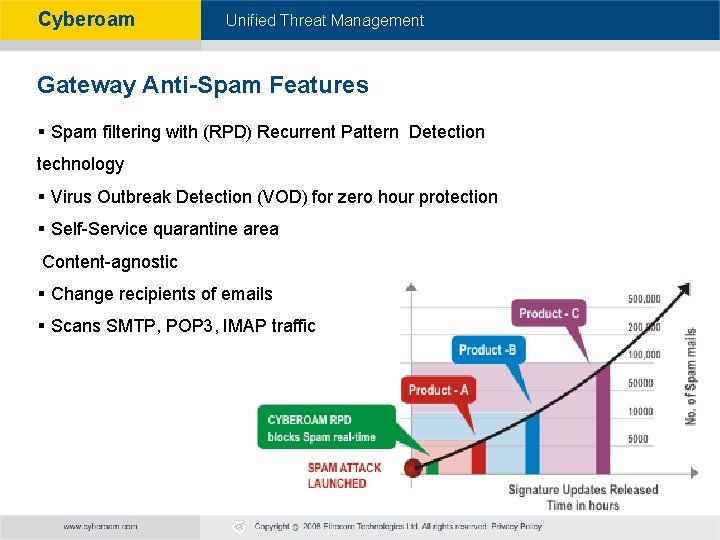
Cyberoam - Unified Threat Management Gateway Anti-Spam Features § Spam filtering with (RPD) Recurrent Pattern Detection technology § Virus Outbreak Detection (VOD) for zero hour protection § Self-Service quarantine area Content-agnostic § Change recipients of emails § Scans SMTP, POP 3, IMAP traffic
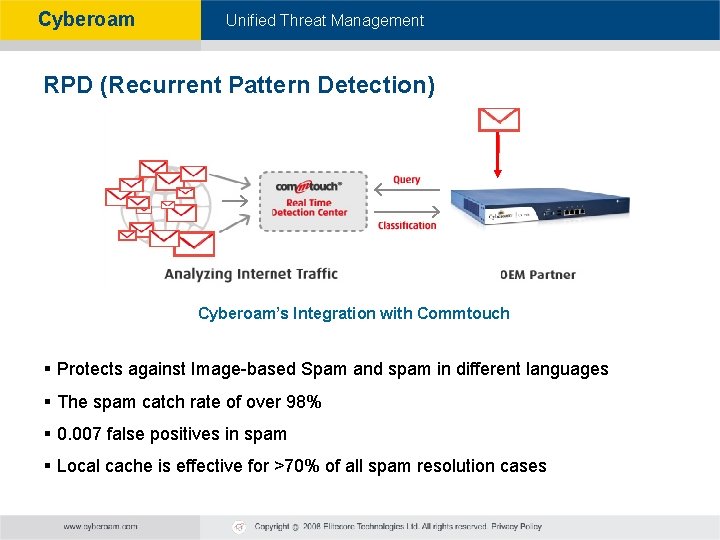
Cyberoam - Unified Threat Management RPD (Recurrent Pattern Detection) Cyberoam’s Integration with Commtouch § Protects against Image-based Spam and spam in different languages § The spam catch rate of over 98% § 0. 007 false positives in spam § Local cache is effective for >70% of all spam resolution cases
Cyberoam - Unified Threat Management Intrusion Prevention System (IPS)
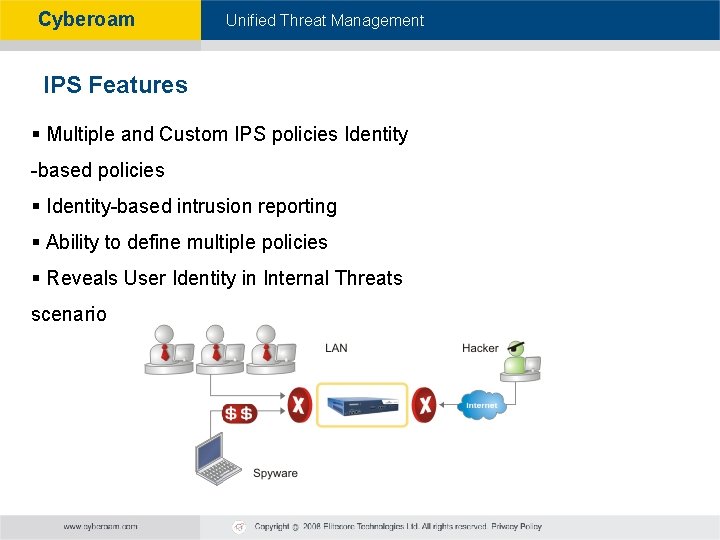
Cyberoam - Unified Threat Management IPS Features § Multiple and Custom IPS policies Identity -based policies § Identity-based intrusion reporting § Ability to define multiple policies § Reveals User Identity in Internal Threats scenario
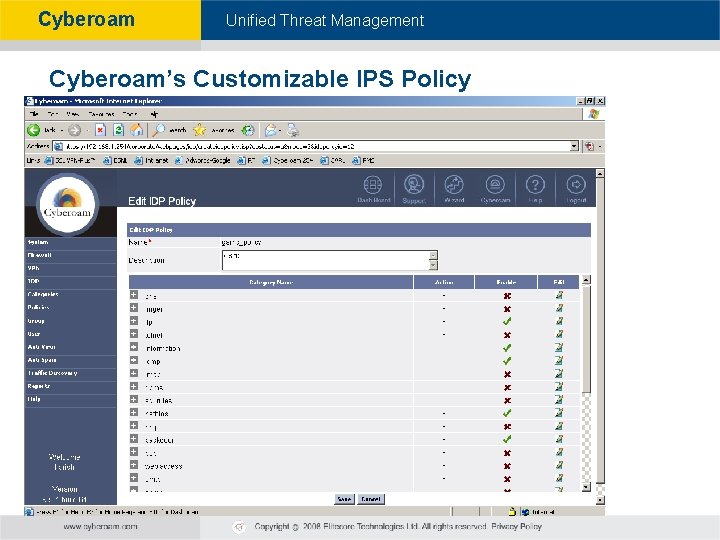
Cyberoam - Unified Threat Management Cyberoam’s Customizable IPS Policy
Cyberoam - Unified Threat Management Identity-Based Content Filtering

Cyberoam - Unified Threat Management Web and Application Filtering Features §Database of millions of sites in 82+ categories Blocks phishing, pharming, spyware URLs §HTTP upload control §Ability to control & Block Applications such as P 2 P, Streaming, Videos/Flash §Local Database for the content filter reduces latency and dependence on network connectivity. §Customized blocked message to educate users about organizational policies and reduce support calls
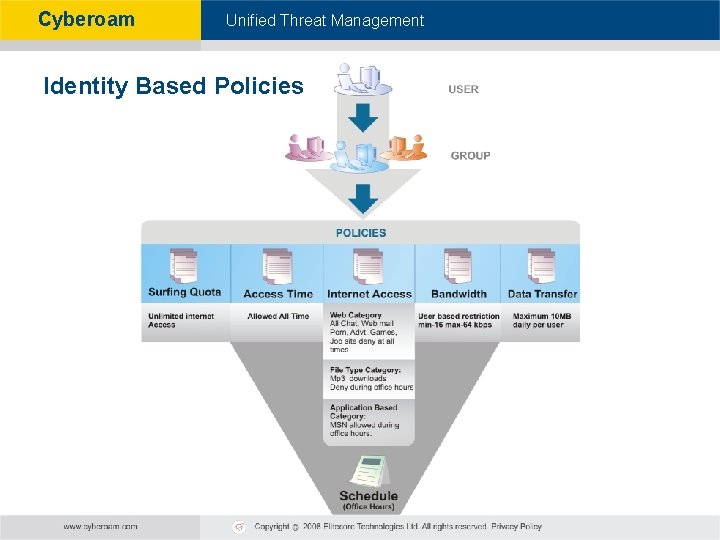
Cyberoam - Unified Threat Management Identity Based Policies
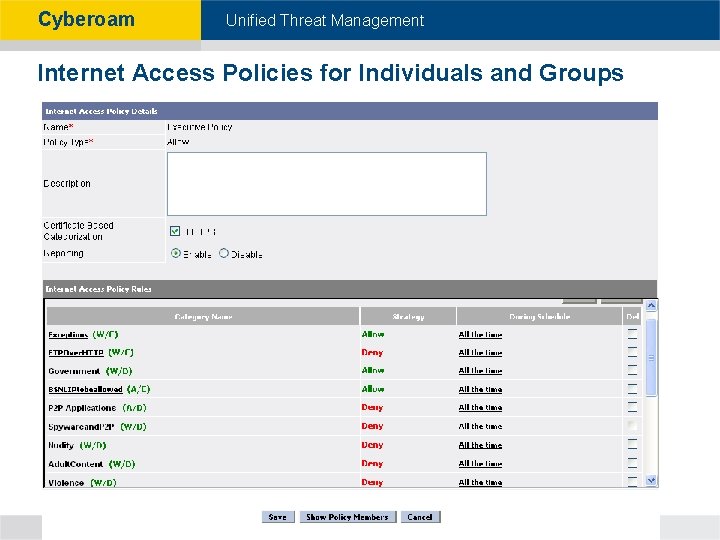
Cyberoam - Unified Threat Management Internet Access Policies for Individuals and Groups
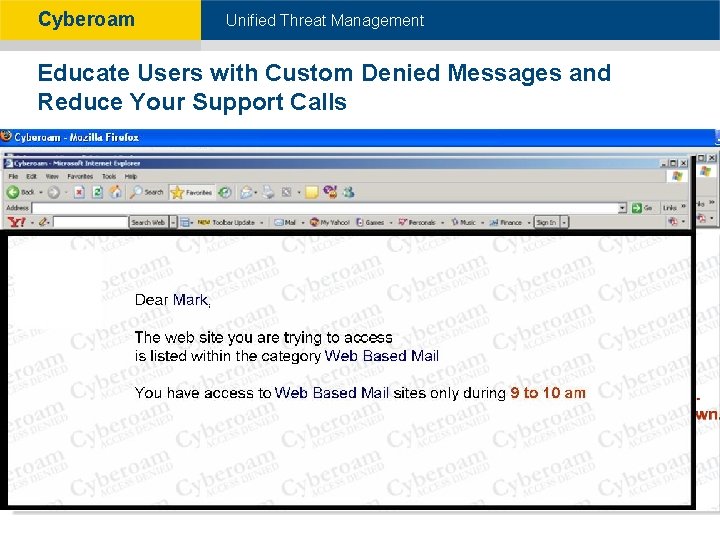
Cyberoam - Unified Threat Management Educate Users with Custom Denied Messages and Reduce Your Support Calls James
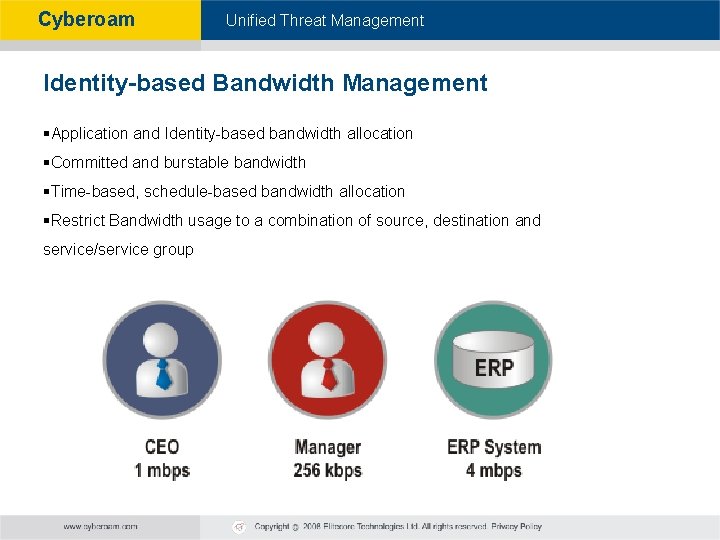
Cyberoam - Unified Threat Management Identity-based Bandwidth Management §Application and Identity-based bandwidth allocation §Committed and burstable bandwidth §Time-based, schedule-based bandwidth allocation §Restrict Bandwidth usage to a combination of source, destination and service/service group
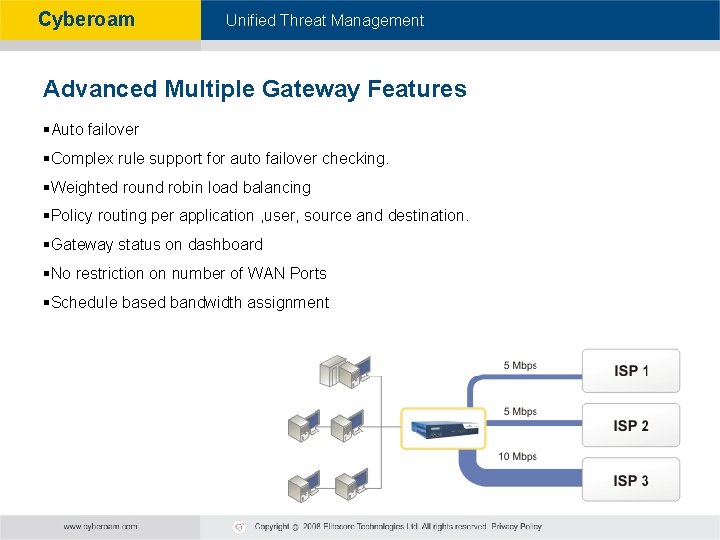
Cyberoam - Unified Threat Management Advanced Multiple Gateway Features §Auto failover §Complex rule support for auto failover checking. §Weighted round robin load balancing §Policy routing per application , user, source and destination. §Gateway status on dashboard §No restriction on number of WAN Ports §Schedule based bandwidth assignment
Cyberoam - Unified Threat Management External Authentication
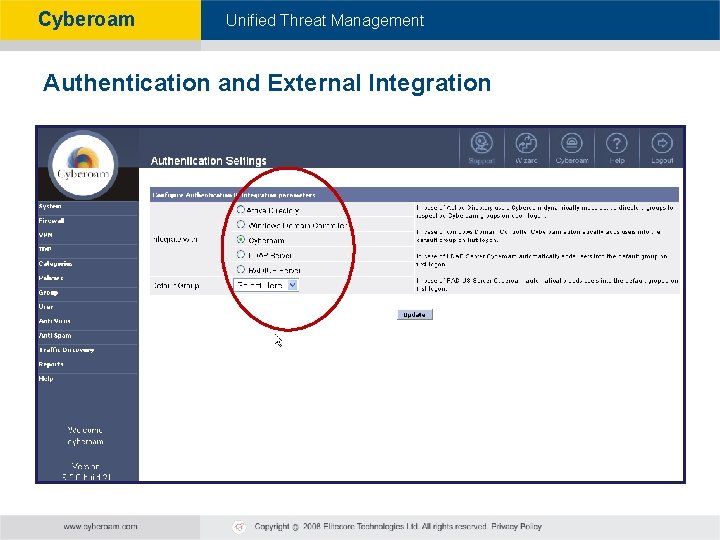
Cyberoam - Unified Threat Management Authentication and External Integration
Cyberoam - Unified Threat Management Traffic Discovery
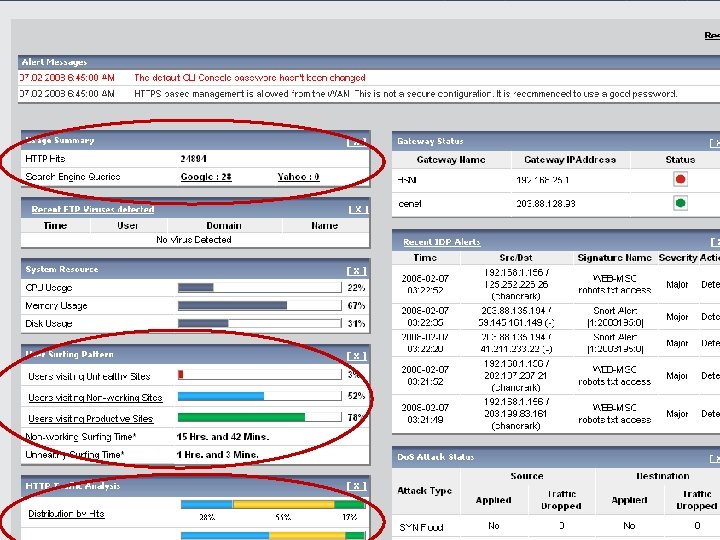
Cyberoam - Unified Threat Management Identity Based “On Appliance” Reporting
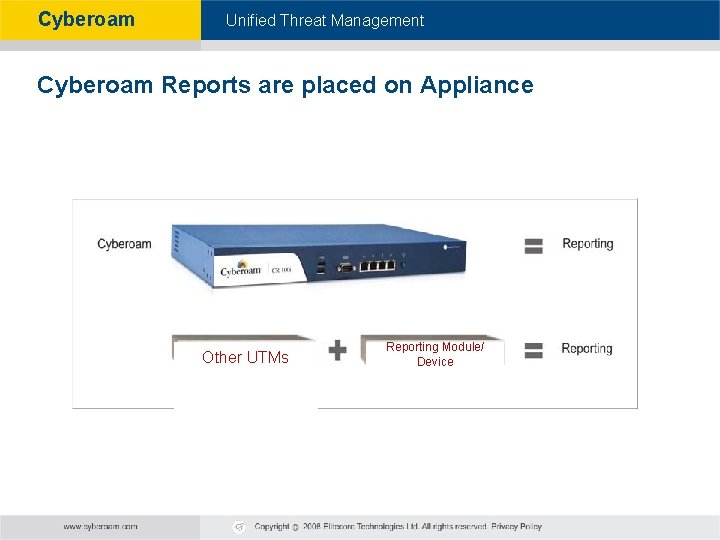
Cyberoam - Unified Threat Management Cyberoam Reports are placed on Appliance Other UTMs Reporting Module/ Device
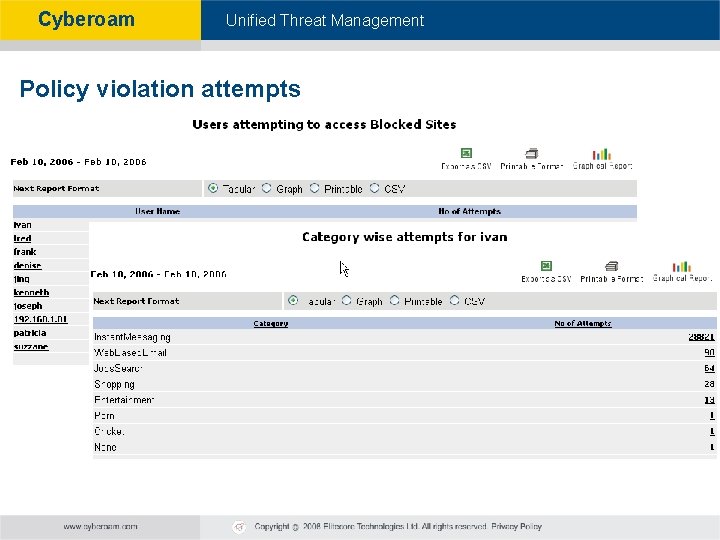
Cyberoam - Unified Threat Management Policy violation attempts
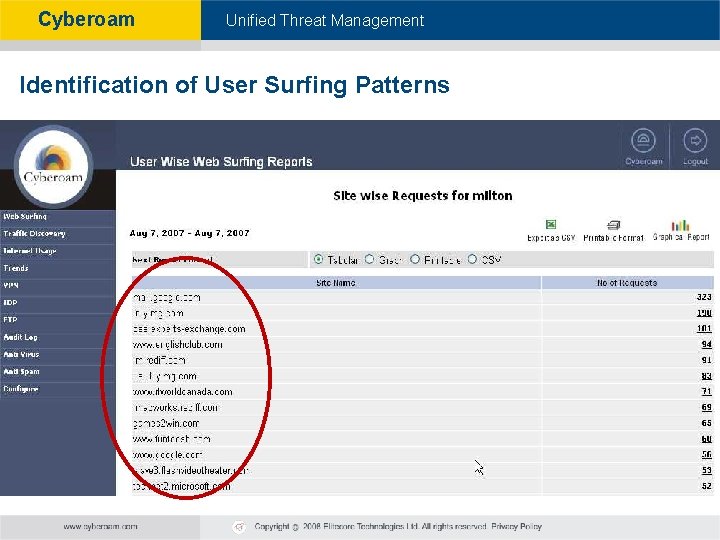
Cyberoam - Unified Threat Management Identification of User Surfing Patterns
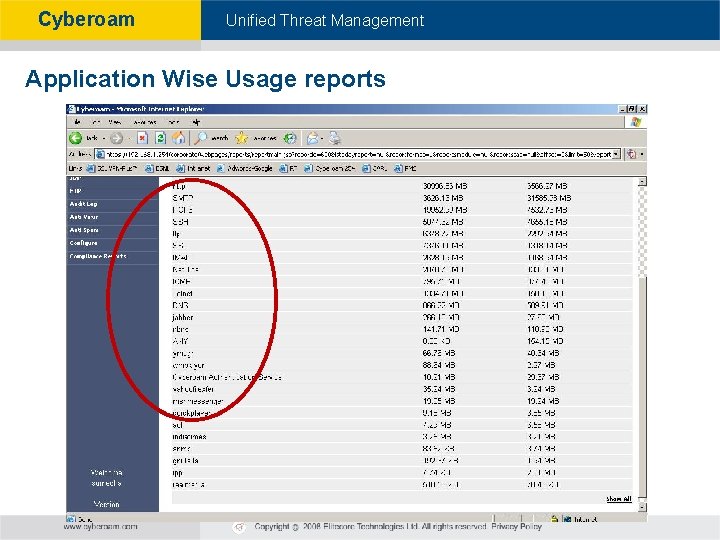
Cyberoam - Unified Threat Management Application Wise Usage reports
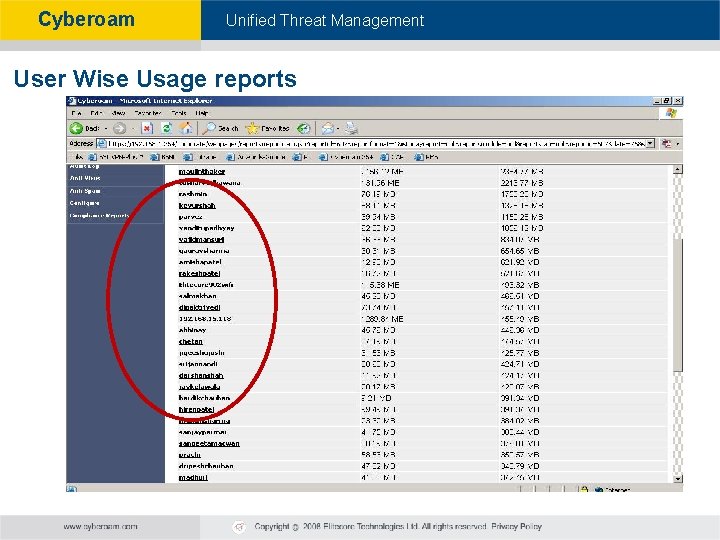
Cyberoam - Unified Threat Management User Wise Usage reports
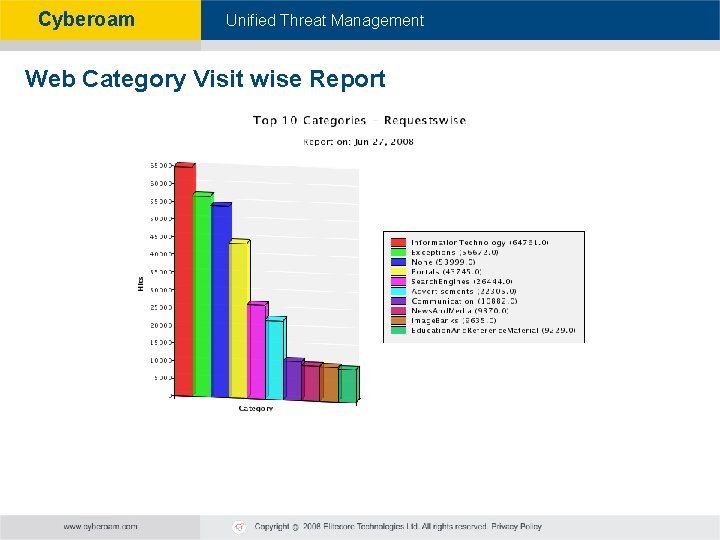
Cyberoam - Unified Threat Management Web Category Visit wise Report
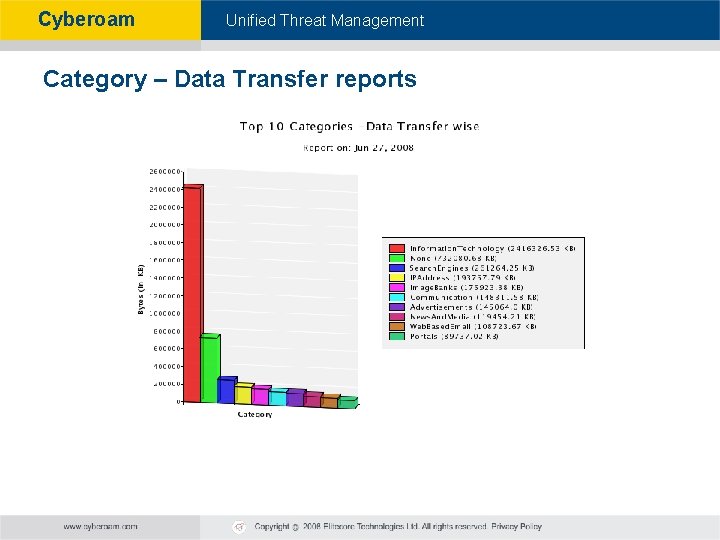
Cyberoam - Unified Threat Management Category – Data Transfer reports
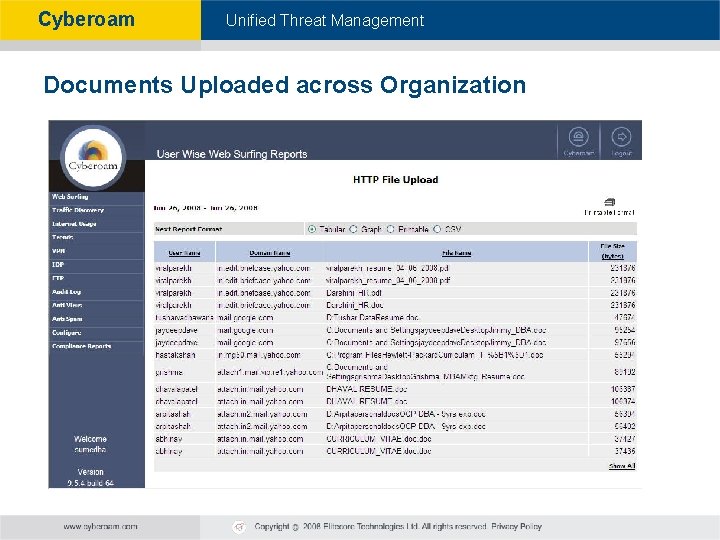
Cyberoam - Unified Threat Management Documents Uploaded across Organization
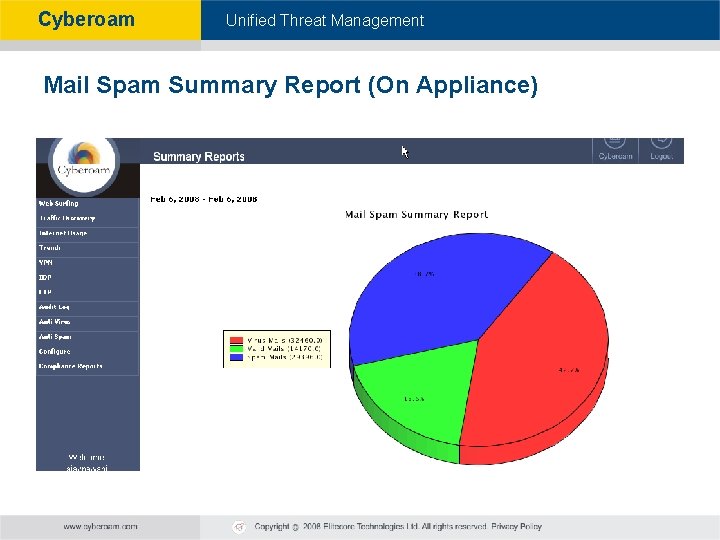
Cyberoam - Unified Threat Management Mail Spam Summary Report (On Appliance)
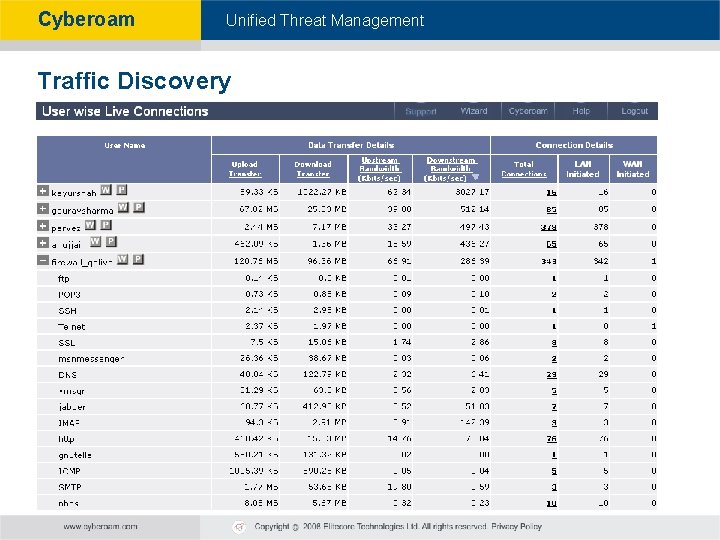
Cyberoam - Unified Threat Management Traffic Discovery
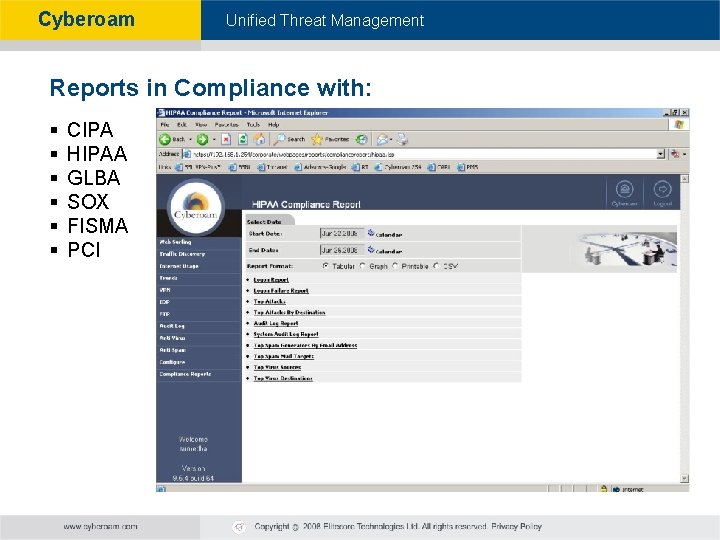
Cyberoam - Unified Threat Management Reports in Compliance with: § § § CIPA HIPAA GLBA SOX FISMA PCI
Cyberoam - Unified Threat Management
Cyberoam - Unified Threat Management Networking Features • Active- Passive High Availability • Stateful Failover • VPN Failover • Dynamic Routing (RIP, OSPF, BGP)
Cyberoam - Unified Threat Management ASIC Vs. Multi-core Architecture
Cyberoam - Unified Threat Management ASICs (Application Specific Integrated Circuits) - Closed Systems What is ASIC: § Built to handle certain tasks faster than general purpose processors §For e. g: Packet Filtering Drawbacks: §Serial Processing §ASICs cannot be reprogrammed to address new attacks § ASICs accelerate traffic, but for complex tasks (VOIP, email, web traffic), tasks are sent to secondary processor - thus depending on processor performance § With each attack (not programmed) closed Systems become slower & Slower
Cyberoam - Unified Threat Management Multicore Processor-based Cyberoam What is Multi-core: More than one processors working together to achieve high processing power. Benefits: §Purpose-built Hardware §True Parallel Processing §Each processor is programmed to run tasks parallel §In case of a new attack, Cyberoam appliances do not suffer from performance degradation associated with switching from ASICbased acceleration to general-purpose processors.
Cyberoam - Unified Threat Management Cyberoam – Appliance Details
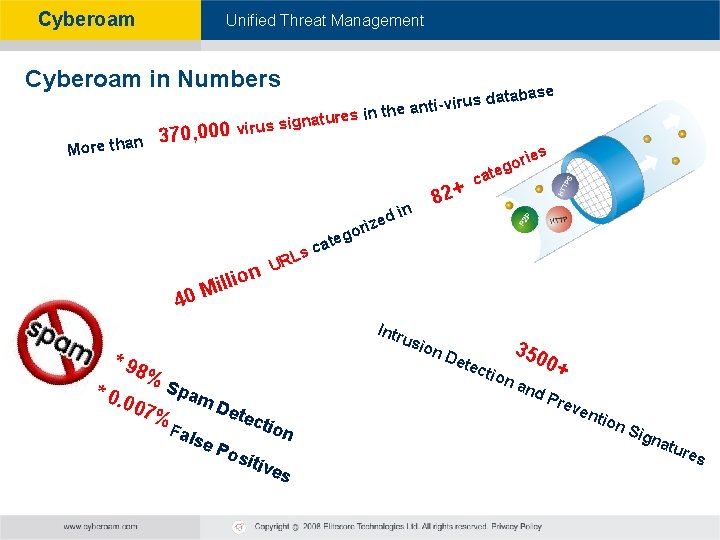
Cyberoam - Unified Threat Management Cyberoam in Numbers 370, 000 n More tha res i natu virus sig s n 40 atabase i-virus d n the ant io Mill UR at sc ed z i r o in L sio n * 98 % 007 Spa % se 350 Det ect io 0+ na m. D Fal ca eg Intr u * 0. 82+ rie o g te ete Pos ctio n itiv es nd Pre ven tion Sig nat ure s
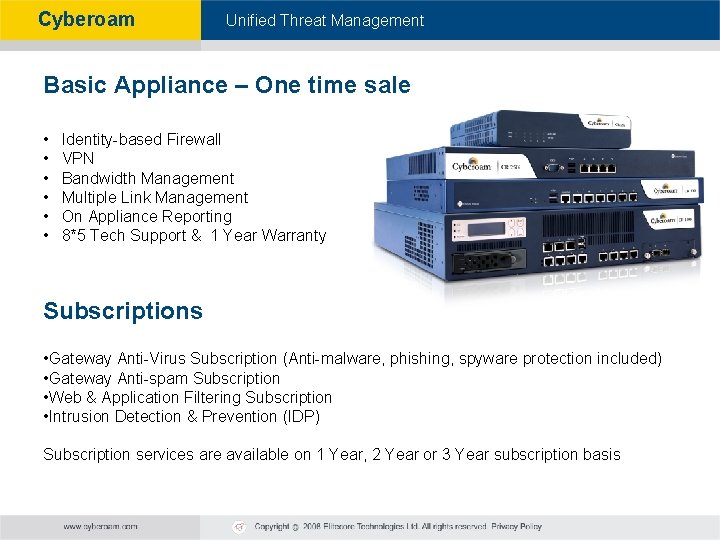
Cyberoam - Unified Threat Management Basic Appliance – One time sale • • • Identity-based Firewall VPN Bandwidth Management Multiple Link Management On Appliance Reporting 8*5 Tech Support & 1 Year Warranty Subscriptions • Gateway Anti-Virus Subscription (Anti-malware, phishing, spyware protection included) • Gateway Anti-spam Subscription • Web & Application Filtering Subscription • Intrusion Detection & Prevention (IDP) Subscription services are available on 1 Year, 2 Year or 3 Year subscription basis
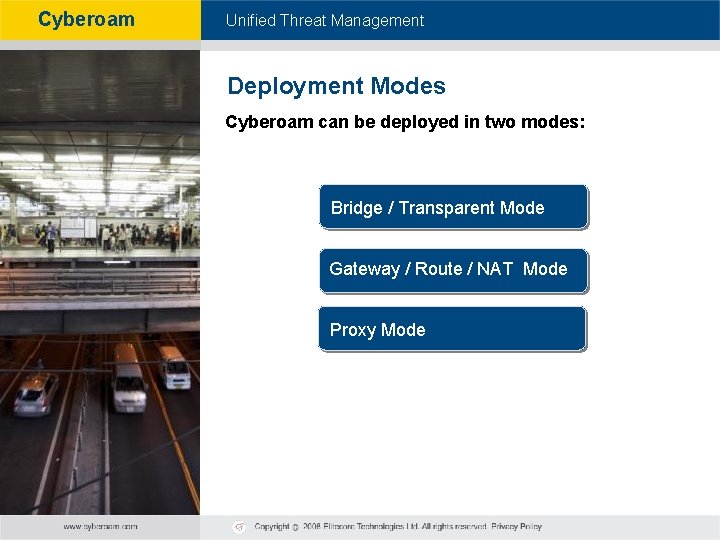
Cyberoam - Unified Threat Management Deployment Modes Cyberoam can be deployed in two modes: Bridge / Transparent Mode Gateway / Route / NAT Mode Proxy Mode
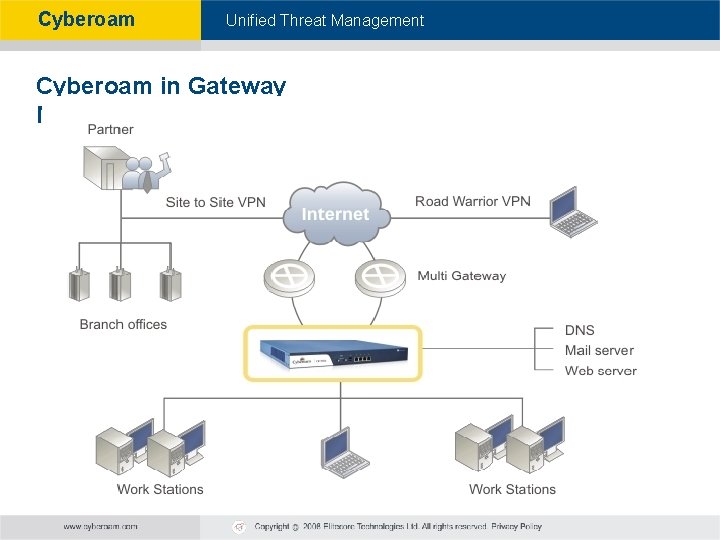
Cyberoam - Unified Threat Management Cyberoam in Gateway Mode
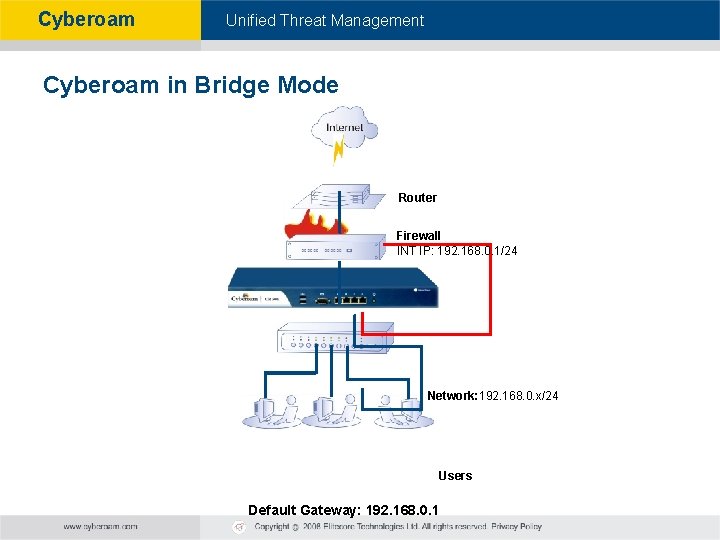
Cyberoam - Unified Threat Management Cyberoam in Bridge Mode Router Firewall INT IP: 192. 168. 0. 1/24 Network: 192. 168. 0. x/24 Users Default Gateway: 192. 168. 0. 1
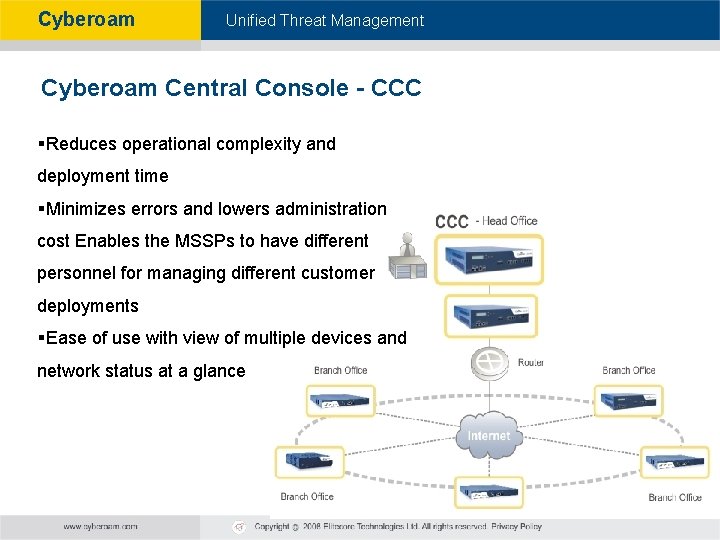
Cyberoam - Unified Threat Management Cyberoam Central Console - CCC §Reduces operational complexity and deployment time §Minimizes errors and lowers administration cost Enables the MSSPs to have different personnel for managing different customer deployments §Ease of use with view of multiple devices and network status at a glance
Cyberoam - Unified Threat Management Cyberoam: Identity-based Security Overview of Cyberoam’s Security Approach: § Who do you give access to: An IP Address or a User? § Whom do you wish to assign security policies: Username or IP Addresses? § In case of an insider attempted breach, whom do you wish to see: User Name or IP Address? § How do you create network address based policies in a DHCP and a Wi-Fi network? § How do you create network address based policies for shared desktops?
Cyberoam - Unified Threat Management Cyberoam Credentials

Cyberoam - Unified Threat Management “IDC believes that identity-based UTM represents the next generation in the burgeoning UTM marketplace. When enterprises realize the value of having identity as a full component of their UTM solution the increased internal security, protection against insidious and complex attacks, understanding individual network usage patterns, and compliance reporting - Cyberoam will benefit as the innovator. ” Source: Unified Threat Management Appliances and Identity-Based Security: The Next Level in Network Security, IDC Vendor Spotlight (2007)
Cyberoam - Unified Threat Management 2008 - Emerging Vendor of the Year
Cyberoam - Unified Threat Management Certifications Premium Anti-Virus Anti-Spyware Anti-Spam URL Filtering Firewall Cyberoam holds a unique & complete UTM Level 5 VPN IPS/IDP UTM certification Certifications Applied ICSA Certified Firewall VPNC Certified for Basic VPN & AES Interoperability ICSA Certification for High Availability
Cyberoam - Unified Threat Management Five Star Rated – Two Years Running se ri rp March 2008 – UTM Roundup te n Cyberoam CR 1000 i E July 2007 – UTM Roundup B SM Cyberoam CR 250 i § § § “console is well organized and intuitive to navigate” “flexible and very powerful” § “this appliance is a good value for almost any size environment”. § § “Fully loaded, with many great features” “packs a more serious punch” “can restrict or open internet access by bandwidth usage, surf time or data transfer”.
Cyberoam - Unified Threat Management “deserves credit for its flexible configuration options, extensive security, content filtering, and bandwidth management features. “
Cyberoam - Unified Threat Management LORD OF THE NETWORKS If there is no network security and discipline in small or large networks, the chaos may result with serious work and data loss. Cyberoam CR 25 i, which was sent to our test center, is a good solution for networks. This UTM (unified threat management) appliance has 100% control over the users in your network in addition to its firewall, package inspection and other similar features. It prevents you from the threats of anti-viruses and other harmful softwares with built in Kaspersky solution. It also provides you antispam feature. In addition to its advanced security features, you can manage your network in terms of identity based bandwith management, application control, site visiting logs. Normally you need a separate PC or similar device so as to record logs. But there is a hard disk of 80 GB in this appliance for this feature. (It was written 160 GB on original copy of the magazine by mistake. ) You can also visit the website www. cyberoam. com and inspect the online demo before buying the product. RESULT Cyberoam CR 25 i is a successful solution for security and network management especially for small business companies. Other advantages: - Advanced features - Flexible licensing options - Free of charge service
Cyberoam - Unified Threat Management Awards § § § Product Excellence Award in the 3 categories: (2007) Integrated Security Appliance Security Solution for Education Unified Security § 2007 Finalist Network Middle East Award Best Security Product Best SMB Networking Vendor § § § Finalist - 2008 Global Excellence in Network Security Solution Tomorrow’s Technology Today 2007 § CRN – Emerging Tech Vendors 2007 § 2007 Finalist American Business Awards § VAR Editor’s Choice for Best UTM (2007)

Cyberoam - Unified Threat Management GLOBAL PRESENCE (Over 55 Countries)

Cyberoam Partial Clientele Cyberoam - Unified Threat Management
Cyberoam - Unified Threat Management Business alliances
Cyberoam - Unified Threat Management Thank you!
- Slides: 74