Security in Sensor Networks Overview of wireless sensor
- Slides: 37
Security in Sensor Networks Overview of wireless sensor network • Security in Sensor Network •
Sensor Node n n Consists of sensing, data processing and communicating component. Randomly deployed in inaccessible terrain. Processes sensed (raw) data and transmits it. Characteristics n n n Rapid deployment Self-organization Fault tolerance
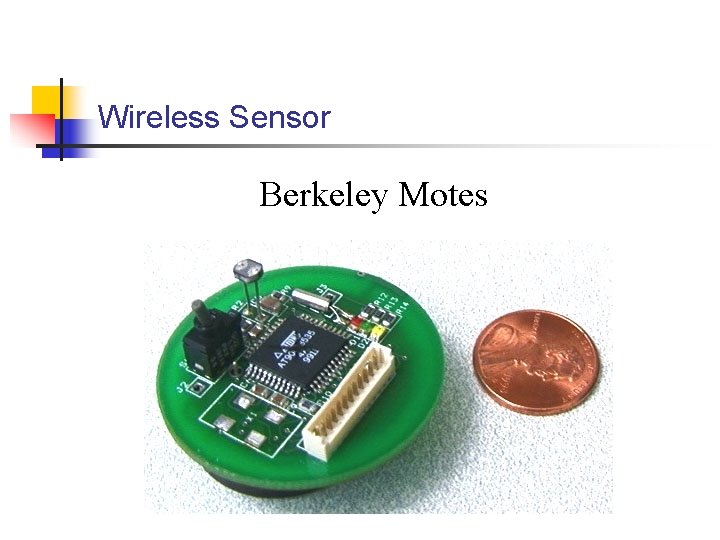
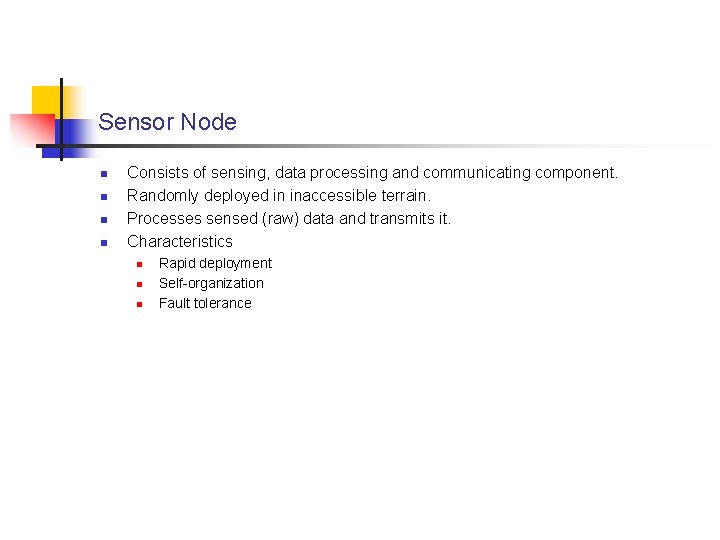
Wireless Sensor Berkeley Motes
Mica Motes n Prototype Sensor developed by UC Berkley n n n Processor 4 MHz Memory 128 Kb flash & 4 Kb RAM Radio 916 MHz and 40 Kbits/sec Transmission range 100 feet Tiny OS operating system: small, open source and energy efficient
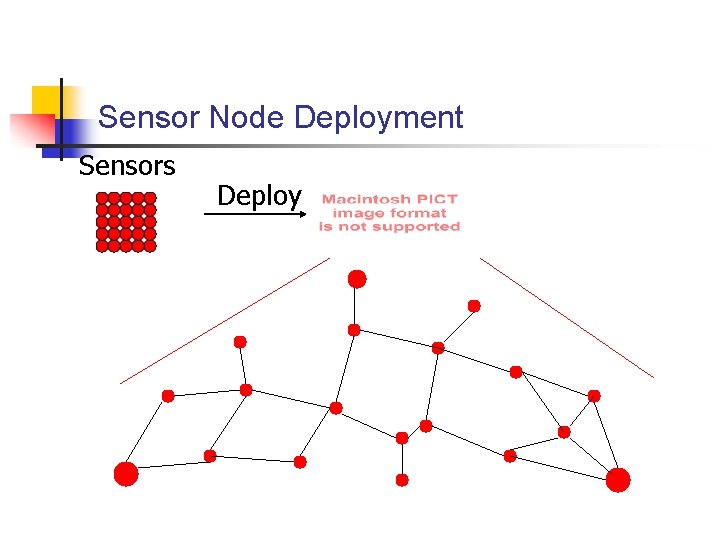
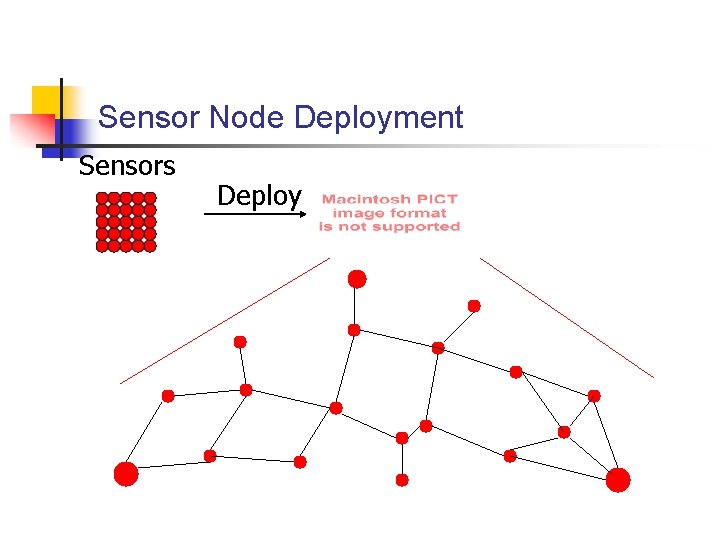
Sensor Node Deployment Sensors Deploy
Application of Sensor Network n Battle ground surveillance n n Environmental monitoring n n n Enemy movement Habitat monitoring Forrest fire monitoring Hospital Tracking system n Tracking patients, drug administration
Sensor Network vs. Wireless ad-hoc network n n n Number of sensor nodes is much higher than nodes in ad hoc network. Sensor nodes are densely deployed. Topology changes frequently. Sensor nodes mainly use broadcasts as opposed to point-to-point used by ad hoc network. Sensor nodes have limited power, computational capacities and memory. No global addressing scheme for sensor nodes
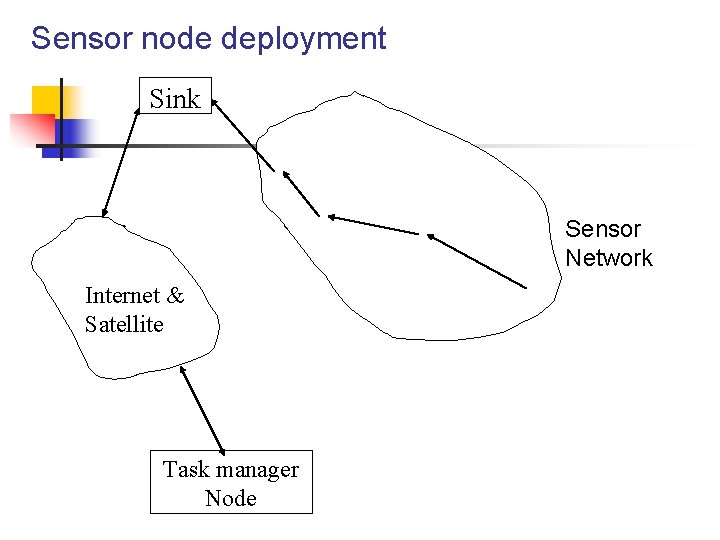
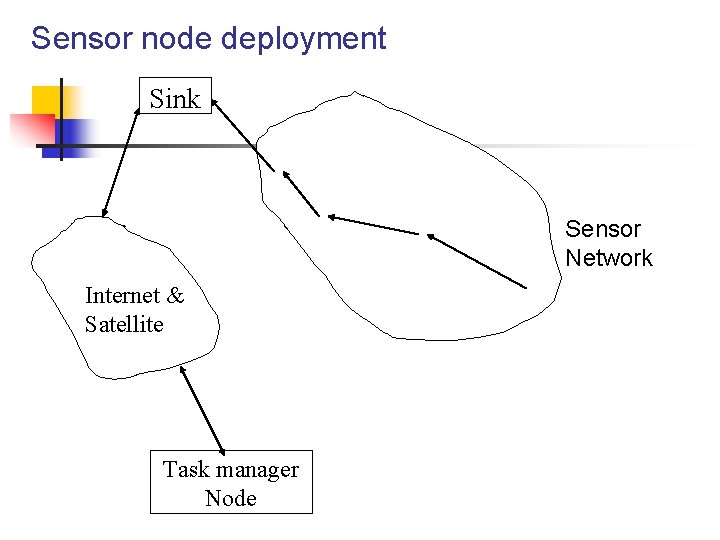
Sensor node deployment Sink Sensor Network Internet & Satellite Task manager Node
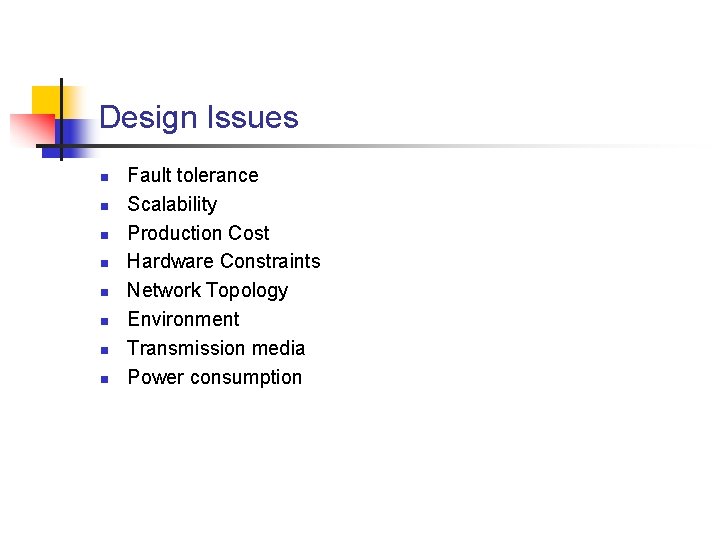
Design Issues n n n n Fault tolerance Scalability Production Cost Hardware Constraints Network Topology Environment Transmission media Power consumption
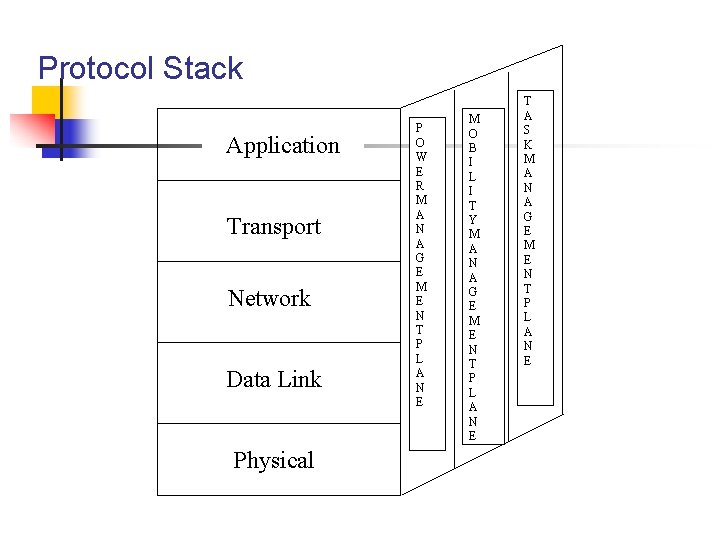
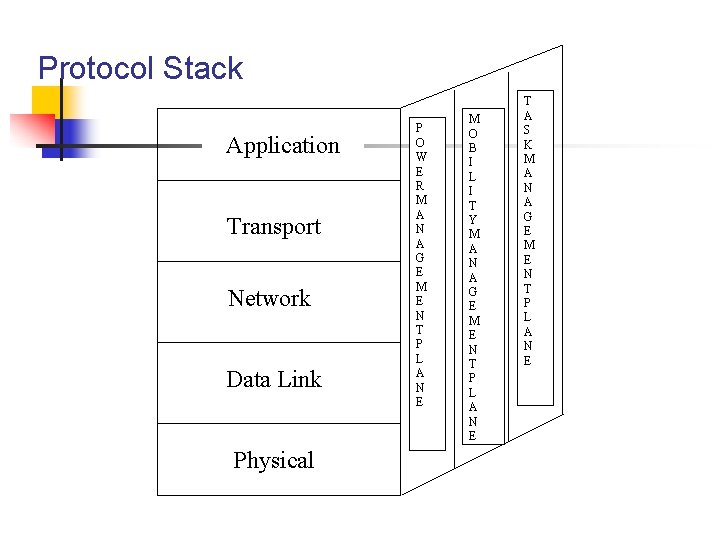
Protocol Stack Application Transport Network Data Link Physical P O W E R M A N A G E M E N T P L A N E M O B I L I T Y M A N A G E M E N T P L A N E T A S K M A N A G E M E N T P L A N E
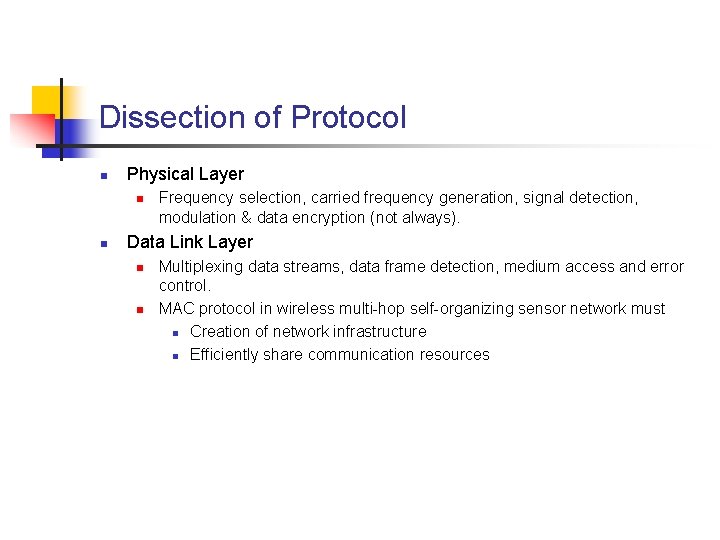
Dissection of Protocol n Physical Layer n n Frequency selection, carried frequency generation, signal detection, modulation & data encryption (not always). Data Link Layer n n Multiplexing data streams, data frame detection, medium access and error control. MAC protocol in wireless multi-hop self-organizing sensor network must n Creation of network infrastructure n Efficiently share communication resources
Existing MAC protocols n n n Cellular system n Nodes only single hop away from nearest base station. n MAC layer provides high Qo. S and bandwidth efficiency. n Power efficiency not an issue. Bluetooth & mobile ad hoc network ( MANET ) n Closest peer to sensor network. n MAC protocol forms the network and maintains mobility. n Primary goal is providing high Qo. S in face of mobility. Sensor network n Much larger nodes with transmission power ( ~0 d. Bm ) n Radio range is much less. n Topology changes more frequent. n Primary importance on power conservation renders cellular and MANET useless.
MAC for sensor n n n Self organizing medium access control for sensor networks (SMACS) and Eavesdrop-and. Register (EAR) algorithm n SMACS is a distributed protocol which achieves network startup by neighbor discovery and channel assignment. n EAR protocol attempts to offer continuous service to nodes under mobile and static conditions. CSMA based Medium Access n Traditional protocol is ineffective because of the assumption that traffic is stochastically distributed. n MAC protocol for sensor network should support periodic traffic. Hybrid TDMA/FDMA based n TDMA dedicates full bandwidth while FDMA allocates minimum n Optimum number of channels is calculated for lowest power consumption.
MAC for sensors (Cont…) n Error control n n n 2 different modes n Forward Error Control (FEC) n Automatic Repeat Request (ARQ) Both unsuitable for overhead (decoding complexity for FEC and retransmissions for ARQ) Simple error control with low complexity encoding/decoding is desirable.
Research issues n n SMACS and EAR are effective for static sensor networks. Improvement required for extensive mobility. Determination of lower bounds on energy required for sensor network self-organization. Error control coding schemes. Power saving modes of operation. n To prolong network activity nodes must enter into periods of reduced activity specially when running low on battery.
Network Layer n Mainly concerned with routing traffic n n n Power efficiency important consideration. Sensor network mainly data-centric. Ideal sensor network has attribute-based addressing and location awareness. Interconnecting with external network, command control system and Internet. Data aggregation n n Solves overlap problem in data-centric routing. Method for combining the data coming from multiple sensor nodes into meaningful information.
Routing protocols n Small Minimum Energy Communication Network n n n Flooding n n n Computes energy-efficient sub-network given a communication network. Maintains minimum energy property such that there is a minimum energy path in sub-graph for every pair of node. Each node broadcasts the data until maximum hops or destination reached. Not suitable because of implosion, overlap and resource blindness. Gossiping n n Here node randomly picks up a neighbor and forwards the packet. Avoids implosions but takes longer time to route the packet.
Routing Protocols (Cont…) n Sensor protocol for information via negotiation (SPIN) n n n Addresses deficiency of flooding by negotiation and resource adaptation. Based on data-centric routing where sensor nodes broadcast an advertisement for available data and waits for request from interested nodes. Sequential Assignment Routing (SAR) n n Creates multiple trees such that root is one hop away from sink. Each tree grows outwards avoiding nodes with low Qo. S and energy reserves. Nodes belong to multiple trees and selects one tree to relay information back to sink based on 2 parameters and priority level of the packet. Two parameters associated with each path n Energy resource n Additive Qo. S metric
Routing Protocols (Cont…) n Low-Energy Adaptive Clustering Hierarchy n n Minimizes energy dissipation Two phases: n Setup n n n Randomly selects clusterheads which communicates with sink. Clusterheads broadcast their address and sensor nodes pickup clusterheads based on signal strength of clusterheads. Steady n n n Begin sensing and transmitting data Clusterheads do data aggregation After sometime in this phase the network goes back in setup phase.
Routing Protocols (Cont…) n Directed Diffusion n n Sink sends out interest ( task description ) to all sensor. Node stores interest entry which contains timestamp and several gradient fields. As interest propagates in network the gradient from source to sink is setup. Sink must refresh and reinforce the interest when it starts to receive data from the source.
Research Issue n New improved protocol to address high topology changes and higher scalability.
Transport Layer n n Needed when the system is accessed through internet or external network. Clearly TCP is not suitable. Communication between user and sink can be done using TCP or UDP via internet or satellite Between sink and nodes can be done using UDP.
Research Issues n Development of transport layer protocol considering the hardware constraints such as limited power & memory.
Application Layer n Sensor Management Protocol n n n Sysadmin can interact using SMP. Nodes have no global addressing and so SMP needs to access them using attribute based naming. SMP can be used to carry out tasks such as n Introducing new rules to data aggregation. n Exchanging data n Moving sensors n Turning sensor on and off. n Authentication, key distribution and security in data communication. n Reconfiguring the sensor nodes.
Research Issues n Application layer protocol needs to be developed with basic functionalities of monitoring the sensor network and high level functions such as interest dissemination.
Dissection of Protocol (Cont…) n n n Power management plane efficiently manages the power usage of sensor nodes. Mobility planes detects and registers the movement. . so remembers the route back to a user and keep track of neighbors. Task management plane balances and schedules the sensing task given to a specific region.
Why security? n Protecting confidentiality, integrity and availability of communications. n n n Conventional view of security from cryptography community: cryptographically unbreakable design in practical sense Vulnerable to sniffing due to broadcast nature of communication. Physical threat.
How is Security Different? n Wireless Sensor networks have NO clear line of defense n n Each node is a host as well as a “router” Secure Network/service “infrastructure” has to be collaboratively established Wireless channel is easily accessible by both good citizens and attackers Resource Constraints - battery - cpu power - memory
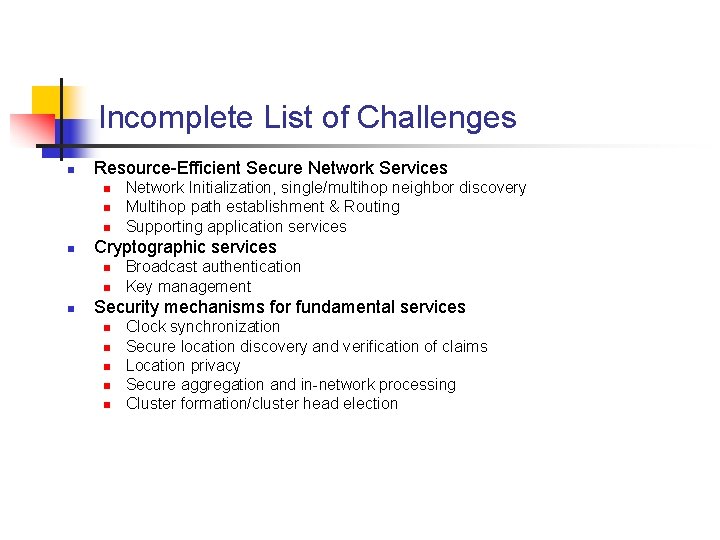
Incomplete List of Challenges n Resource-Efficient Secure Network Services n n Cryptographic services n n n Network Initialization, single/multihop neighbor discovery Multihop path establishment & Routing Supporting application services Broadcast authentication Key management Security mechanisms for fundamental services n n n Clock synchronization Secure location discovery and verification of claims Location privacy Secure aggregation and in-network processing Cluster formation/cluster head election
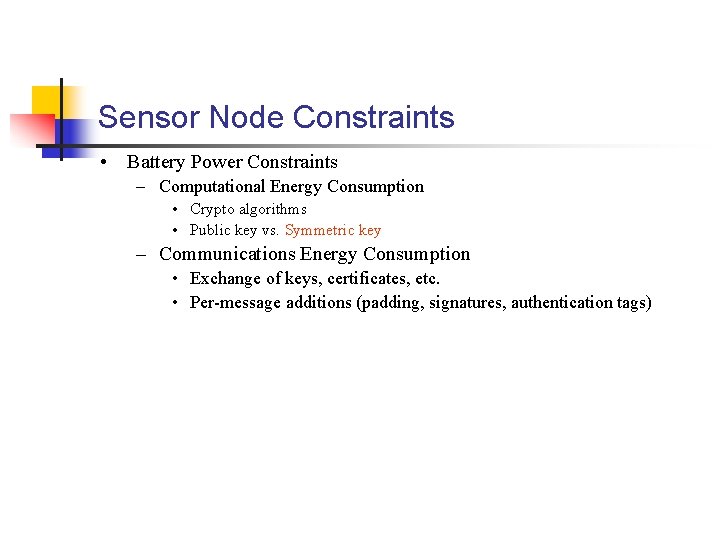
Sensor Node Constraints • Battery Power Constraints – Computational Energy Consumption • Crypto algorithms • Public key vs. Symmetric key – Communications Energy Consumption • Exchange of keys, certificates, etc. • Per-message additions (padding, signatures, authentication tags)
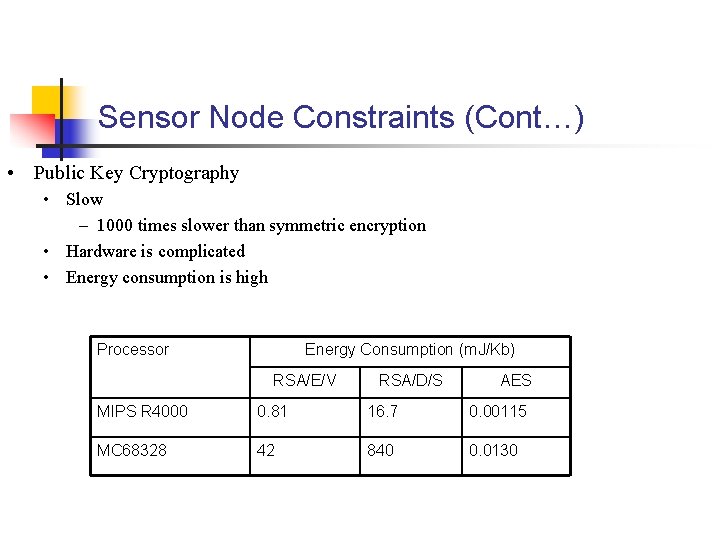
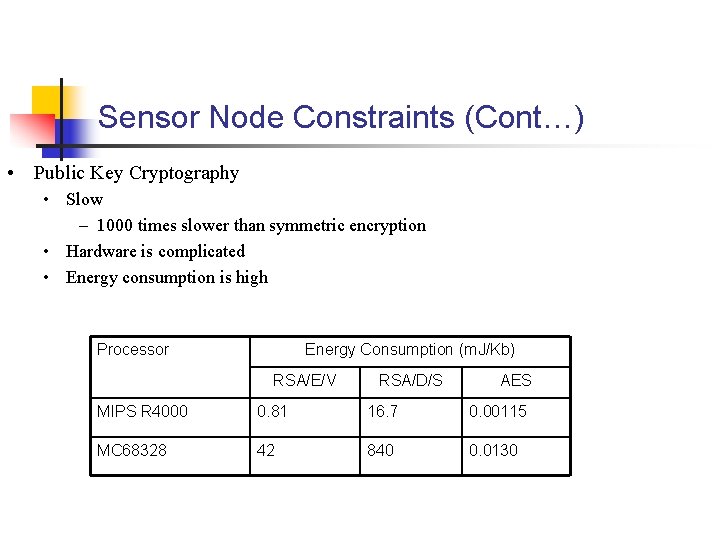
Sensor Node Constraints (Cont…) • Public Key Cryptography • Slow – 1000 times slower than symmetric encryption • Hardware is complicated • Energy consumption is high Processor Energy Consumption (m. J/Kb) RSA/E/V RSA/D/S AES MIPS R 4000 0. 81 16. 7 0. 00115 MC 68328 42 840 0. 0130
Related Work n Security Aware Ad hoc Routing (SAR) n n Uses trust values of nodes to do secure routing Employ route discovery protocol where nodes with security metric equivalent to sender receiver participate. Based on Bell-La Confidentiality model. SPINS n n n Comprises of SNEP & Mu-TESLA. SNEP provides confidentiality, integrity and freshness. Mu-TESLA provides authentication to data broadcasts. Each node shares a master key with base station and also a counter which is used as an input to RC 5 to get encryption key. Mu-TESLA uses symmetric mechanisms with a delayed disclosure of keys achieving asymmetry in digital signature.
Related Work (Cont…) n Key Management Problem n n n Trusted server scheme n Finding trusted server is difficult. Public key scheme n Expensive and infeasible for sensors Key Pre-distribution schemes n Loading keys into sensor prior to deployment. n Two nodes should find a common key after deployment.
Key Pre-Distribution scheme n Master key approach n n n Memory efficient but low security Requires tamper resistant hardware. Pair-wise key approach n n n (N-1) keys for each node Security perfect but memory is an issue. New nodes cannot be added.
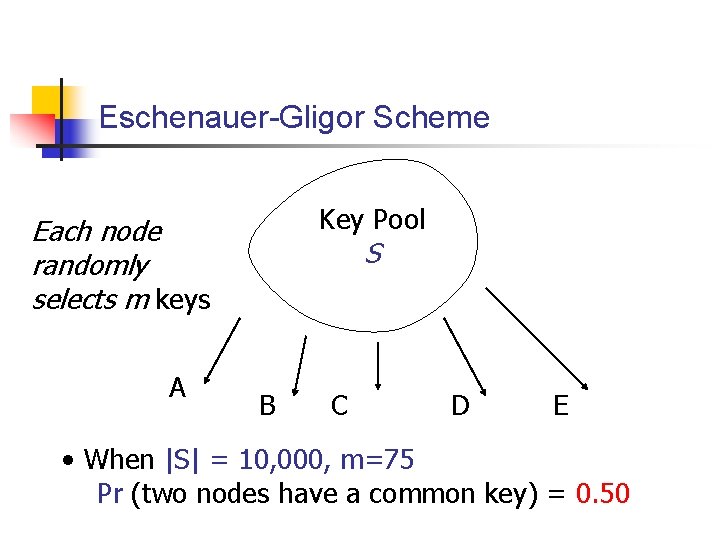
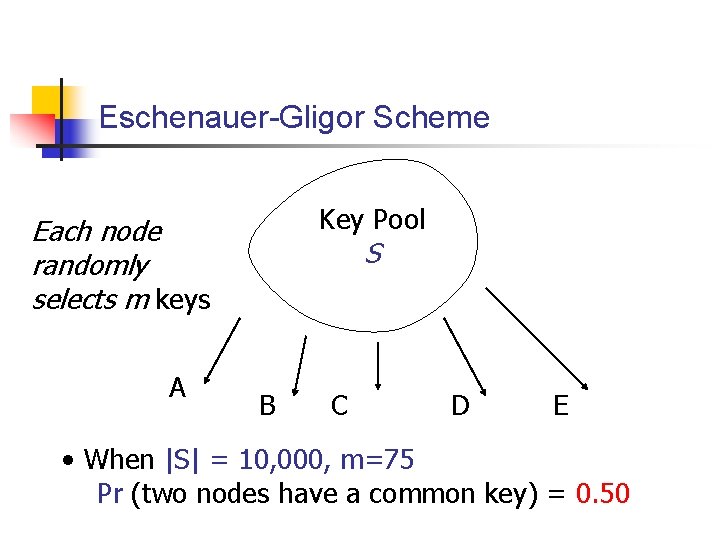
Eschenauer-Gligor Scheme Key Pool Each node randomly selects m keys A S B C D E • When |S| = 10, 000, m=75 Pr (two nodes have a common key) = 0. 50
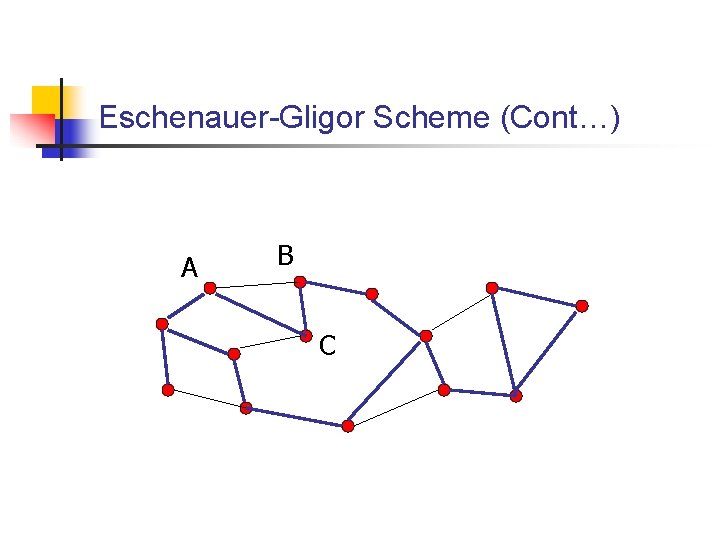
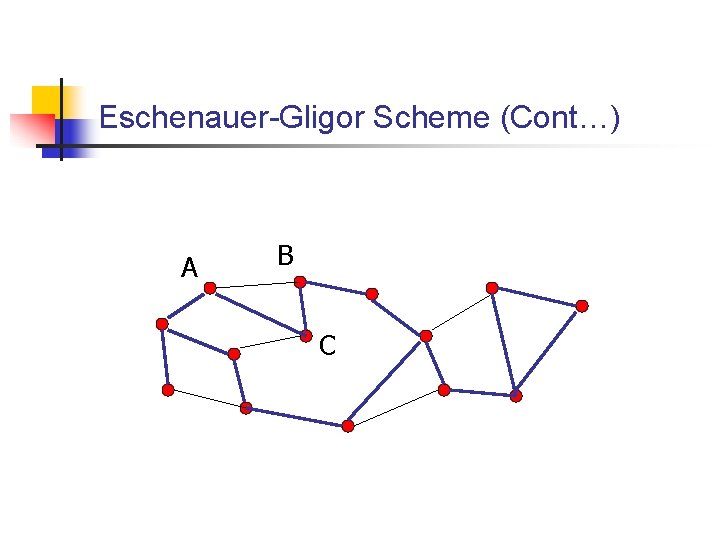
Eschenauer-Gligor Scheme (Cont…) A B C
Conclusion n The low cost, flexibility, fault tolerance, high sensing fidelity and rapid deployment makes way for new applications on remote sensing. Realization needs to satisfy the constraints such as scalability, topology changes, power consumption, environment etc. New wireless ad hoc networking techniques are required to overcome this contraints.