Security in Ad hoc Networks MOBILEMAN Meeting Cambridge
Security in Ad hoc Networks MOBILEMAN Meeting Cambridge July 2 -4, 2003 Pietro Michiardi – Refik Molva Institut Eurecom
• Secure routing Outline – State of the art – Mobile. Man proposal • Cooperation enforcement – State of the art – Mobile. Man proposal • Key management – State of the art • Layer 2 security R. Molva, P. Michiardi, “Ad hoc networks Security”, In Proc. of PWC 2003, September 2003 P. Michiardi, R. Molva, “Ad hoc networks Security”, Chapter in IEEE/Wiley Press. Handbook of Mobile Ad hoc Networks
Secure Routing
Secure Routing - Attacks • • • Threats using modification Threats using impersonation Threats using fabrication Wormhole attack Lack of cooperation
Secure Routing - Objectives • Data origin authentication • Integrity on routing information • Entity authentication – Source – Destination – Intermediate node • Correct behavior (routing algorithm)
Secure Routing – State of the art • Assumption: reliance on existing key set-up • Asymmetric vs. Symmetric Crypto • Pro-active vs. Reactive routing protocols
Secure Routing - Example • Ariadne: 1. The target node can authenticate the initiator (using a MAC with a key shared between the initiator and the target) 2. The initiator can authenticate each entry of the path in the ROUTE REPLY (each intermediate node appends a MAC with its TESLA key) 3. No intermediate node can remove a previous node in the node list in the REQUEST or REPLY (a one wayfunction prevents a compromised node from removing a node from the node list).
Secure Routing • Limitations of current solutions – Mandatory key set-up – Contradiction: long-lived security associations in self-organized MANET – No incentive for cooperation
Eurecom’s Proposal for Secure Routing • Secure routing combined with cooperation enforcement mechanism (CORE) • Self-organized: no need for key set-up • Symmetric cryptography Work in progress !
Cooperation enforcement
Cooperation in MANET • Participation to Routing and Packet Forwarding (PF) costs energy. • Selfish node: priority is to use available energy for oneself, no intentional damage to other nodes. • CLAIM: without appropriate Cooperation Enforcement Mechanism, MANET cannot work.
Cooperation enforcement - Objectives • Detect misbehaving (selfish) nodes • Isolate misbehaving nodes • Stimulate/Enforce cooperation
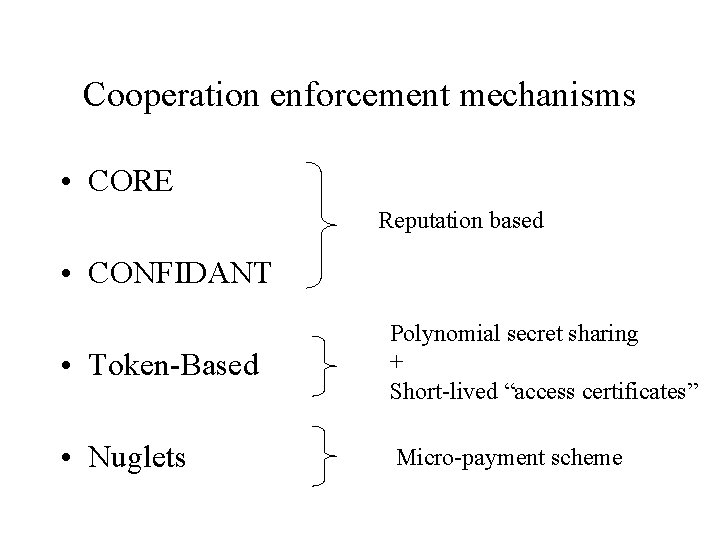
Cooperation enforcement mechanisms • CORE Reputation based • CONFIDANT • Token-Based Polynomial secret sharing + Short-lived “access certificates” • Nuglets Micro-payment scheme
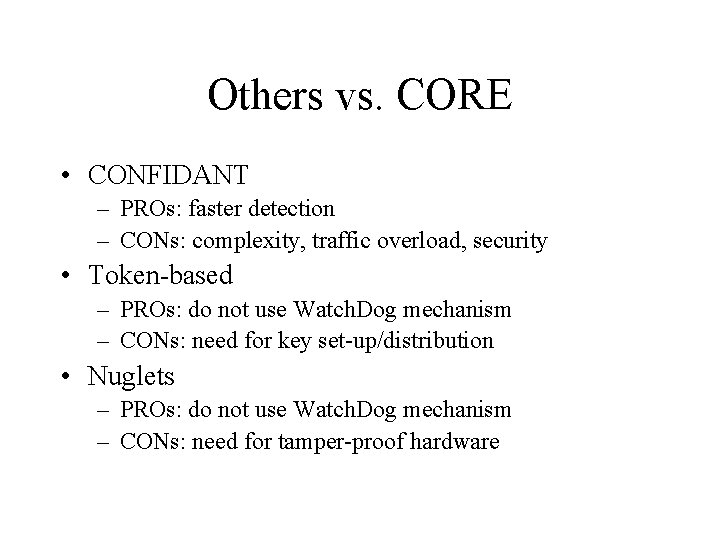
Others vs. CORE • CONFIDANT – PROs: faster detection – CONs: complexity, traffic overload, security • Token-based – PROs: do not use Watch. Dog mechanism – CONs: need for key set-up/distribution • Nuglets – PROs: do not use Watch. Dog mechanism – CONs: need for tamper-proof hardware
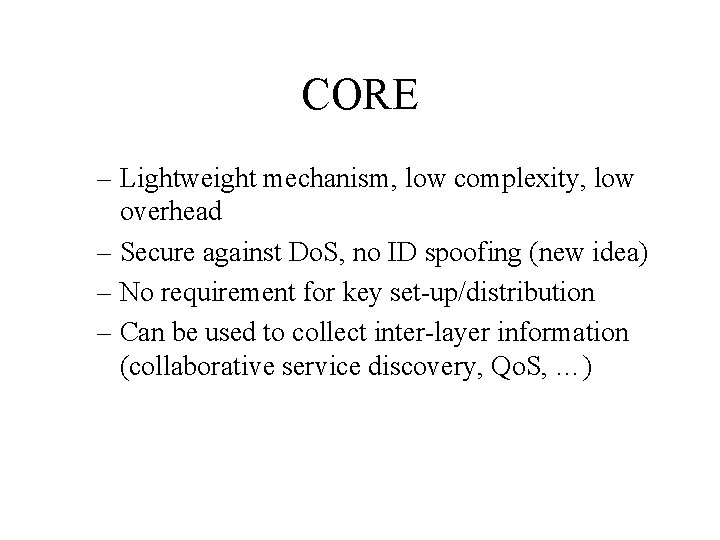
CORE – Lightweight mechanism, low complexity, low overhead – Secure against Do. S, no ID spoofing (new idea) – No requirement for key set-up/distribution – Can be used to collect inter-layer information (collaborative service discovery, Qo. S, …)
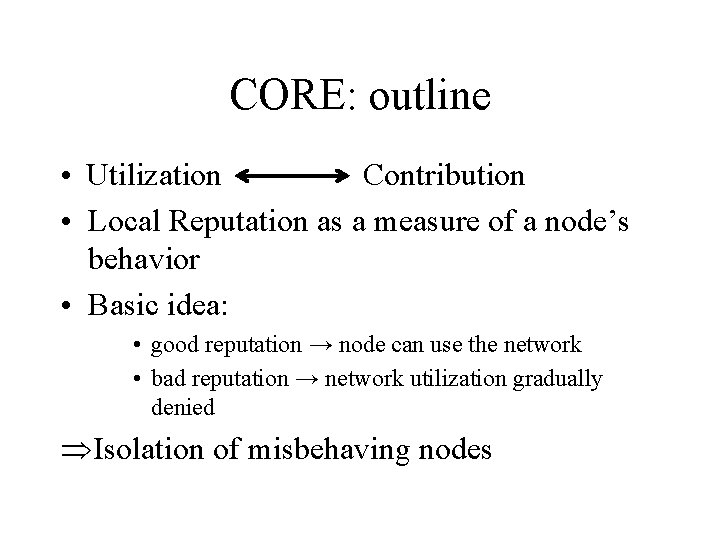
CORE: outline • Utilization Contribution • Local Reputation as a measure of a node’s behavior • Basic idea: • good reputation → node can use the network • bad reputation → network utilization gradually denied ÞIsolation of misbehaving nodes
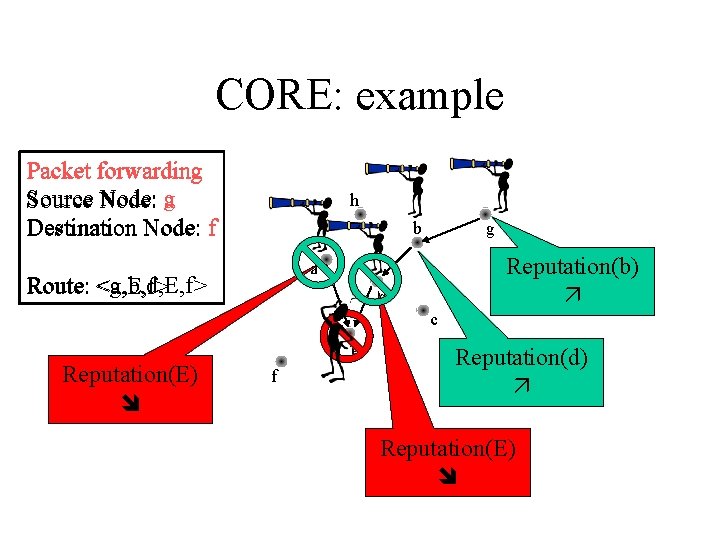
CORE: example Packet forwarding Source Node: ag Destination Node: f h b g Reputation(b) a <g, b, d, E, f> Route: <a, E, f> d c Reputation(E) E f Reputation(d) Reputation(E)
Problem: how to analyze CORE? • By simulation OR • Game Theory (GT) as a tool to model node’s behavior wrt. Routing & PF • Introduce CORE in the GT model and study the effects it has on node’s behavior Original approach, presented first in Michiardi, Molva RR-02 -069 “Making greed work in MANET”
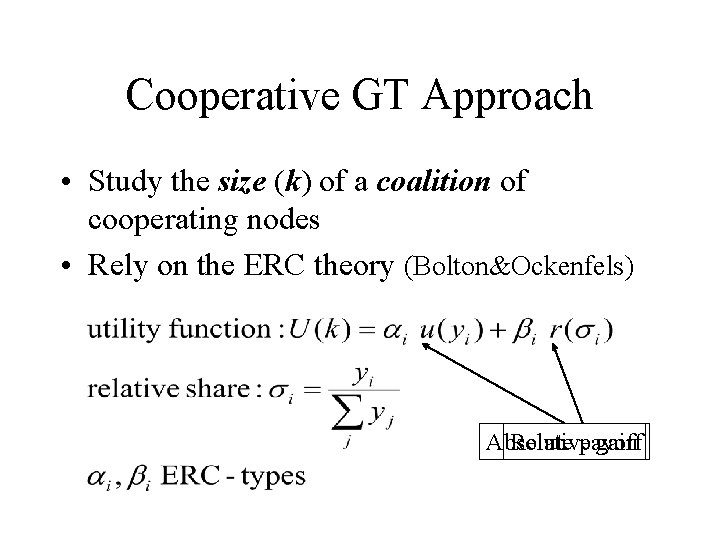
Cooperative GT Approach • Study the size (k) of a coalition of cooperating nodes • Rely on the ERC theory (Bolton&Ockenfels) Absolute Relativepayoff gain
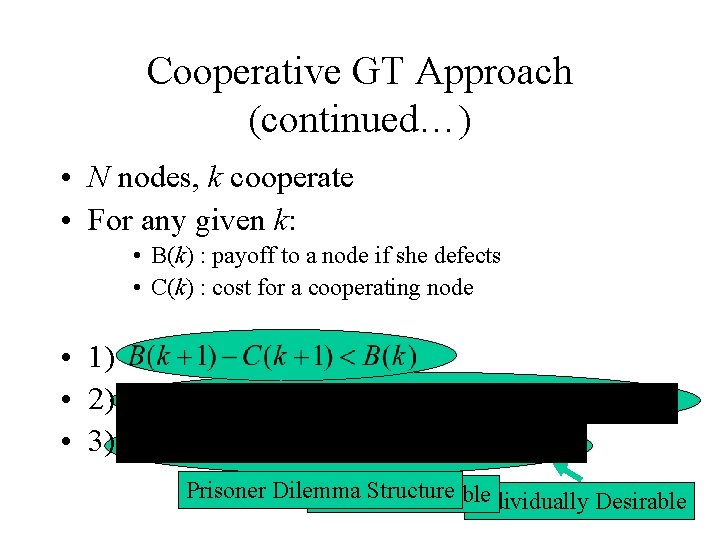
Cooperative GT Approach (continued…) • N nodes, k cooperate • For any given k: • B(k) : payoff to a node if she defects • C(k) : cost for a cooperating node • 1) • 2) • 3) Prisoner Dilemma Structure Socially Desirable Individually Desirable
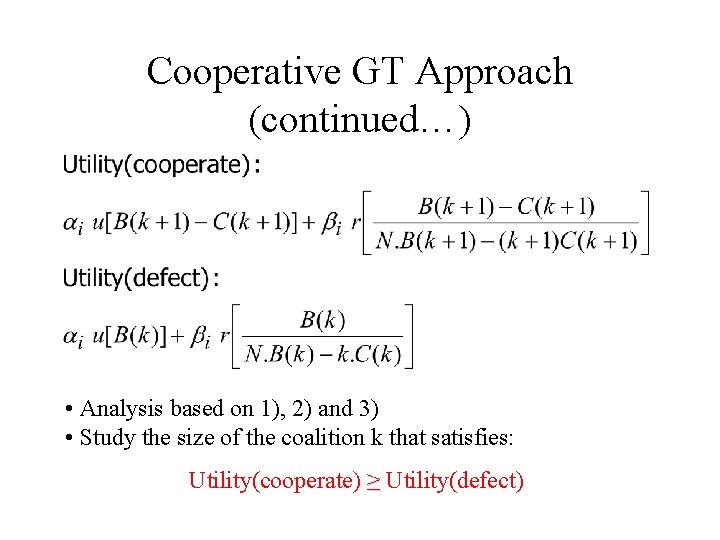
Cooperative GT Approach (continued…) • Analysis based on 1), 2) and 3) • Study the size of the coalition k that satisfies: Utility(cooperate) ≥ Utility(defect)
Cooperative GT Approach: Results • Depending on the distribution of ERCtypes, there can be a Nash Equilibrium in which at least N/2 nodes cooperate N/2 is the lower bound of the coalition size
Cooperative GT Approach: Limits • Define B(k) and C(k) to take into account topology and connectivity • CORE reputation mechanism not objectively modeled • IDEA: express ERC-types as a function of reputation Addressed in IEEE Journal of Performance Evaluation
Non-cooperative GT approach • Study the strategy adopted by a selfish node • Define utility as function of available energy of a node • Introduce the CORE mechanism as a pricing factor to induce a cooperative behavior
Non-cooperative GT approach (continued…) • Utility function, no pricing: • bi: strategy selected by node ni • bj: common strategy selected by neighbors of node ni n 1 nj ni n 2 nt
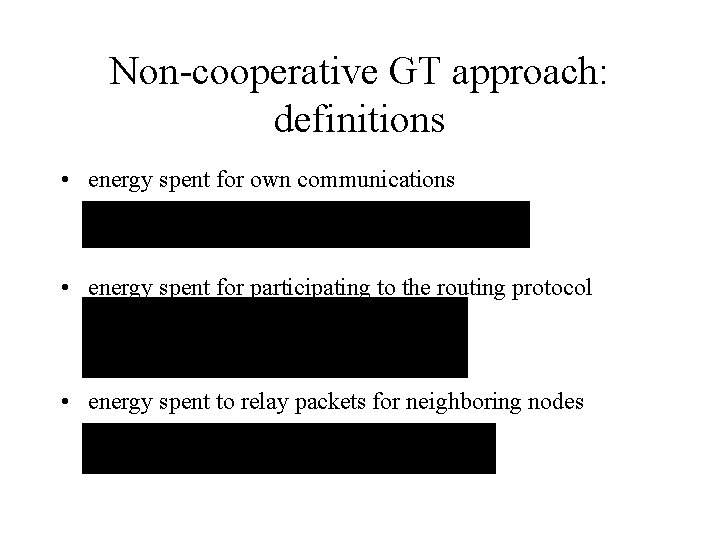
Non-cooperative GT approach: definitions • energy spent for own communications • energy spent for participating to the routing protocol • energy spent to relay packets for neighboring nodes
Non-cooperative GT approach (continued…) No pricing, i. e. no CEM Best strategy: defect Nodes choose strategy by maximizing utility function
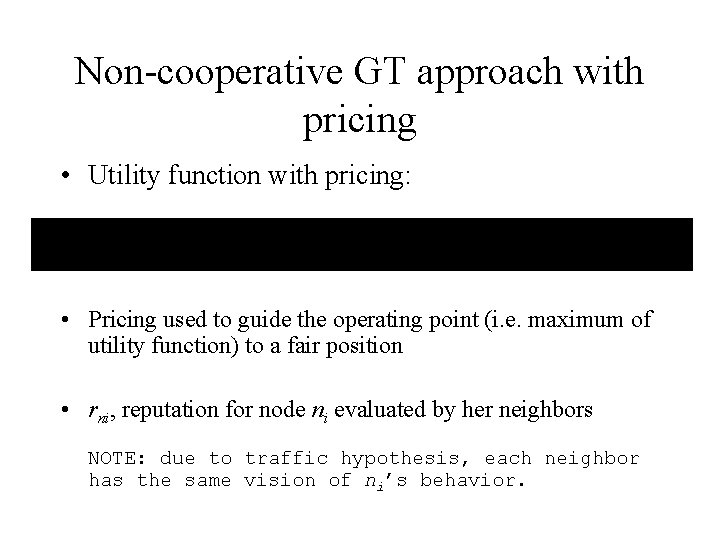
Non-cooperative GT approach with pricing • Utility function with pricing: • Pricing used to guide the operating point (i. e. maximum of utility function) to a fair position • rni, reputation for node ni evaluated by her neighbors NOTE: due to traffic hypothesis, each neighbor has the same vision of ni’s behavior.
Non-cooperative GT approach with pricing • rni, evaluated based on past strategies selected by node ni • rni, influence on future neighbor’ strategy Dynamic game • MATLAB simulation using the SAME definition of reputation in [Michiardi, Molva, CORE, CMS’ 02]
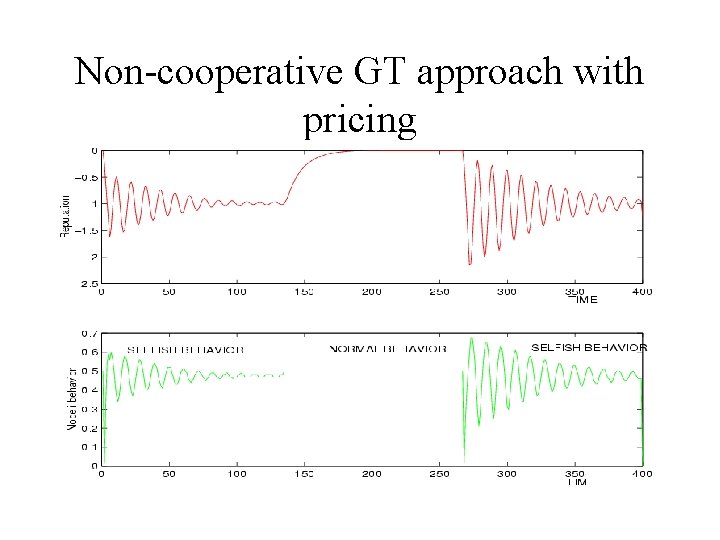
Non-cooperative GT approach with pricing
Non-cooperative GT approach with pricing: results • Analytical proof that MANET without Cooperation Enforcement cannot work • Numerical proof that CORE asymptotically enforces cooperation • GT allows the fine-tuning of CORE parameters to obtain FAST convergence
Non-cooperative GT approach with pricing: limits • Indirect reputation defined in CORE • Analytical solution of dynamic game • Future work: – Evaluate sampling frequency of watchdog mechanism
Key Management
Key Management - Challenges • • No infrastructure No trusted third parties (TTPs) Broadcast nature of communications Fully distributed system
Key Management - Objectives • Secure routing • Basic security services – – Authentication Confidentiality Integrity Non-repudiation • Symmetric or Asymmetric Keys
![Key Management Fully Distributed Certificate Authority [Luo, Lu] • Based on threshold cryptography [cert(PKi)]SK Key Management Fully Distributed Certificate Authority [Luo, Lu] • Based on threshold cryptography [cert(PKi)]SK](http://slidetodoc.com/presentation_image_h2/d25b14f1c8a02e63f2b303ac3bf2f03f/image-36.jpg)
Key Management Fully Distributed Certificate Authority [Luo, Lu] • Based on threshold cryptography [cert(PKi)]SK 1 PKi [cert(PKi)]SKi CERT(PKi)SK [cert(PKi)]SK 1 [cert(PKi)]SK 2 … [cert(PKi)]SK 2 [cert(PKi)]Ski … Verification of CERT(PKi)SK by any node using well known PK • PROs: distributed approach • CONs: bootstrap phase, requirement for dense network
![Key Management Self issued Certificates (PGP) [Chapkun, Hubaux] • Based on Web-of-trust • PROs: Key Management Self issued Certificates (PGP) [Chapkun, Hubaux] • Based on Web-of-trust • PROs:](http://slidetodoc.com/presentation_image_h2/d25b14f1c8a02e63f2b303ac3bf2f03f/image-37.jpg)
Key Management Self issued Certificates (PGP) [Chapkun, Hubaux] • Based on Web-of-trust • PROs: no centralized key management • CONs: initialization phase, storage requirements
![Key Management Secure Pebblenets [Basagni et al. ] • Based on symmetric cryptography, and Key Management Secure Pebblenets [Basagni et al. ] • Based on symmetric cryptography, and](http://slidetodoc.com/presentation_image_h2/d25b14f1c8a02e63f2b303ac3bf2f03f/image-38.jpg)
Key Management Secure Pebblenets [Basagni et al. ] • Based on symmetric cryptography, and cluster formation algorithm Cluster Head Cluster Member KH KTEK KB KTEK KG= group key, well known KH= hello key (derived from K G), used for cluster head selection KB= inter cluster key, used for traffic encryption key generation KTEK= used for traffic confidentiality Assumption: no malicious nodes
![Key Management Key Agreement in Ad Hoc Networks [Asokan, Ginzborg] Hyper. Cube Protocol (Diffie-Hellman) Key Management Key Agreement in Ad Hoc Networks [Asokan, Ginzborg] Hyper. Cube Protocol (Diffie-Hellman)](http://slidetodoc.com/presentation_image_h2/d25b14f1c8a02e63f2b303ac3bf2f03f/image-39.jpg)
Key Management Key Agreement in Ad Hoc Networks [Asokan, Ginzborg] Hyper. Cube Protocol (Diffie-Hellman)
Layer 2 security
Layer 2 vs MANET Security • IEEE 802. 11 and Bluetooth – weaknesses – secure extensions to wireline networks • Layer 2 mechanisms in MANET – managed environments: L 2 sufficient if node integrity is guaranteed (tamper-proof HW) – open environments (no a priori trust): L 2 cannot cover higher layer (3, 4, . . ) security
Summary • Cooperation enforcement mechanism – Design – Simulation – Qualnet – Validation using GT • Secure Routing (in progress)
Summary • Collaboration • French research grant (ACI Sécurité) on MANET Security – collaboration with INRIA Rhône Alpes • Witness IST FP 5 project on Ubiquitous Computing Security • Research engineer expected on board Sept. 2003
Publications – P. Michiardi, R. Molva, Chapter on “ Ad hoc networks security ” IEEE Press / Wiley Ed. Book on Ad hoc Networking. – P. Michiardi, R. Molva, “ Stimulating Cooperation in Mobile Ad hoc Networks”, EUROPEAN SCIENCE FOUNDATION (PESC): Exploratory Workshop – Is Mobile Ad hoc Networking Part of the Future of Mobile Networking in Europe? , Monterosso al mare, La Spezia, Italy, 10 12 October 2002. – P. Michiardi, R. Molva, “ A Game Theoretical Approach to Evaluate Cooperation Enforcement Mechanisms in Mobile Ad Hoc Networks ”, Wi. Opt 2003: Modeling and Optimization in Mobile, Ad Hoc and Wireless Networks, INRIA Sophia Antipolis, France, March 3 5, 2003. ( Best student paper award ) – P. Michiardi, R. Molva, “ Ad hoc Network Security”, to appear in ST Microelectronics Journal of System Research, 2003. – P. Michiardi, R. Molva, “ A Game Theoretical Approach to Evaluate Cooperation Enforcement Mechanisms in Mobile Ad Hoc Networks ”, Submitted to IEEE Journal of Performance Evaluation. – R. Molva, P. Michiardi, “ Ad hoc Network Security”, Invited paper to appear in Proceedings of PWC 2003, Venice, Italy, September 23 25, 2003.
- Slides: 44