Public Key Infrastructure Introduction to Cyber Security Public

Public Key Infrastructure Introduction to Cyber Security
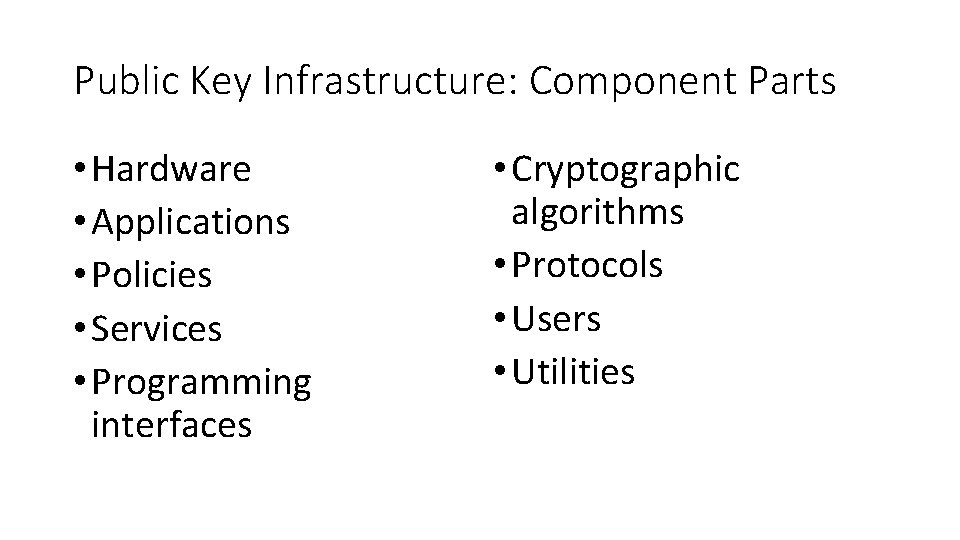
Public Key Infrastructure: Component Parts • Hardware • Applications • Policies • Services • Programming interfaces • Cryptographic algorithms • Protocols • Users • Utilities
What PKI boils down to… Establishing a level of trust
Without PKIs… Individuals could spoof others’ identities
Man-in-the-Middle Attack Example (using e-mail surveillance): 1. Katie replaces John’s public key with her key in the publicly accessible directory 2. Diane extracts what she thinks is John’s key, but it is in fact Katie’s key 3. Katie can now read messages Diane encrypts and sends to John 4. After Katie decrypts and reads Diane’s message, she encrypts it with John’s public key and sends it on to him so he will not be the wiser
With PKIs Registration Authorities (RAs) and Certificate Authorities (CAs) will verify the identity of parties wishing to send messages to each other as a trusted third party
Registration Authority Example • John wishes to register for a driver’s license • Must provide one or more of the following for proof of identity: • Passport • Birth Certificate • Social Security Card • If the DMV is satisfied with the proof provided, and he passes the road test, the DMV will create a driver’s license that can then be used by John to prove his identity
Registration Authority Example The trust does not lie with John in proving his identity, but since his identity was verified by the DMV, he can use his new license to prove his identity because people trust the DMV
How the RA and CA work together 1. The RA requires the proof of identity from the individual requesting the certificate and will validate the information 2. The RA will then advise the CA to generate a certificate, similar to the driver’s license 3. The CA will digitally sign the certificate using its private key 4. The use of the private key ensures to the recipient that the certificate came from the CA
Digital Certificate • Establishes the association between the subject’s identity and a public key • The private key that is paired with the public key in the certificate is stored separately
Certification Practices Statement • Outlines how identities are verified • Steps the CA follows to generate, maintain, and transmit certificates • Why the CA can be trusted to fulfill its responsibilities
Certificate Server • Actual service that issues certificates based on the data provided during the initial registration process • Constructs and populates the digital certificate with the necessary information • Combines the user’s public key with the resulting certificate • Digitally signs with the CA’s private key
Certificate Classes • Class 1: Name, e-mail address, physical address • Class 2: Driver’s license, passport, company information • Class 3: Provide more information, likely to go to RA’s office for face-to-face meeting
Certificate Revocation List (CRL) • List of serial numbers of certificates that have been revoked • Statements indicating why the individual certificate was revoked • Date when it was revoked • Certificates that are expired are not the same as those that have been revoked
Certificate Revocation List (CRL) The CA is responsible for maintaining the CRL and posting it in a publicly available directory
Public CAs • Specialize in verifying individuals identities and creating and maintaining their certificates • Not bound to specific companies or intracompany departments • Companies pay public CAs for the certificates as well as the service of maintaining the certificates
In-house CAs • Implemented, maintained, and controlled by the company that implemented it • Creates certificates for internal employees, devices, applications, partners, and customers
In-house CAs Gives companies complete control over • How individuals are identified • What certification classes are created • Who can and cannot have access to the CA • How certifications can be used
Outsourced CAs • Provide dedicated services and possibly equipment to an individual company • Different from public CAs since public CAs do not offer specific servers and infrastructures for individual companies • More complex parts are outsourced • CA • RA • CRL • Key recovery mechanisms
FACT Setting up your own PKI takes significant resources, especially skilled personnel
FACT Public CAs already have the necessary equipment, skills, and technologies
FACT Some companies do NOT believe they can trust an outside authority to generate and maintain their users’ and company’s certificates
Trust Models • Describe and outline the trust relationships between the different CAs and different environments, which will indicate where the trust paths reside • Goal is to have as few trust paths as possible
Intermediate Certificates • Sit between the presented certificate and the root certificate
Root Certificates • All certificates in the chain must be verified up to the root certificate • The root certificate is always signed by the CA itself
Leaf Certificates • Used in the hierarchical trust model • Model configuration is that of an inverted tree • Leaf CAs generate certificates for the end users (users, network devices, applications)
Trust Models • Hierarchical (Root CA, Intermediate CAs, and Leaf CAs) • Peer-to-Peer • Hybrid (using both models)
Digital Certificates Binds an individual’s identity to a public key
How does the CA know what type of data to insert into the certificate? Certificates are created and formatted based on the X. 509 standard
The X. 509 Standard • Outlines necessary fields of the certificate • Possible values that can be inserted into the fields • Version 3 is the most current version of the standard
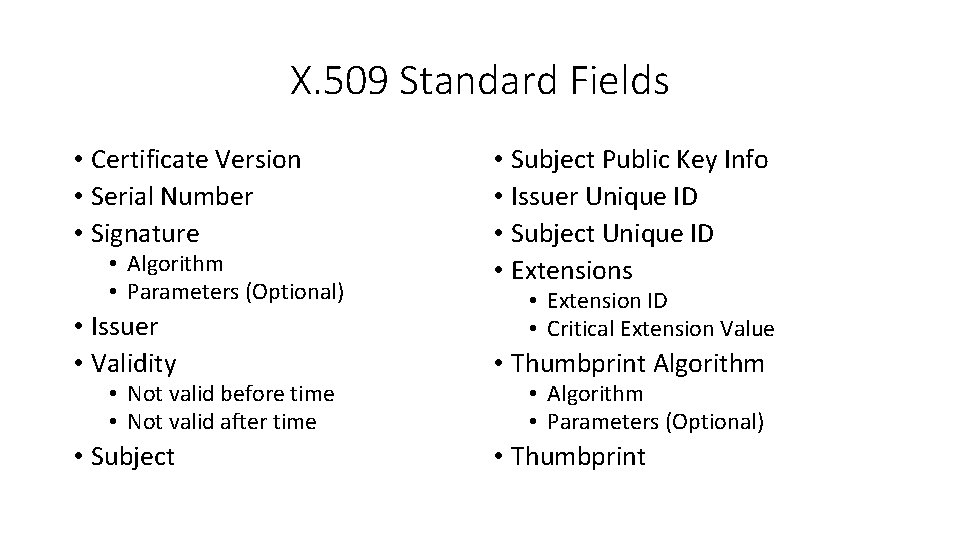
X. 509 Standard Fields • Certificate Version • Serial Number • Signature • Algorithm • Parameters (Optional) • Subject Public Key Info • Issuer Unique ID • Subject Unique ID • Extensions • Extension ID • Critical Extension Value • Issuer • Validity • Thumbprint Algorithm • Subject • Thumbprint • Not valid before time • Not valid after time • Algorithm • Parameters (Optional)
Certificate Lifecycles • Registration and Generation • Registration Authority (RA)
Certificate Lifecycles • Certificate Signing Request (CSR) • Actual request to a CA containing a public key and the requisite information needed to generate the certificate
Certificate Lifecycles • Renewal • Specified by the validity dates inserted into the digital certificate • Cannot be used before the start date and a new certificate needs to be issued by the end date
Certificate Lifecycles • Suspension • Certificate is temporarily put on hold before its expiration date • Example: Private key may be compromised • Example: Extended vacation or lapse in certificate subject maintenance
Certificate Lifecycles • Revocation • Examples of Reasons for Revocation • Stolen laptop with private key • Improper software installation that directly affects private key • Social engineering attack • Certificate no longer applies to subject • Employee left company that has knowledge of the private key • In any of these events, the user’s private key should no longer be mapped to the owner’s identity
Certificate Lifecycles • Certificate Revocation List (CRL) • List of serial numbers of certificates that have been revoked • Statement indicating why the certificate was revoked • Date when it was revoked • All revocations on list have occurred within the lifetime of the CA
Certificate Lifecycles • CRL Distribution • User’s PKI software needs to know where to look for the posted CRL that relates to the certificate it is trying to validate • Online Certificate Status Protocol • Database of the available CRLs within the environment • Searches for one subject on list instead of all subjects
Certificate Lifecycles • Key Destruction • Certificates and keys are properly destroyed when the time comes and wherever the keys are stored • User workstations • Centralized key servers • USB token devices • Smart cards
Certificate Repositories • Centralized directory that can be accessed by a subset of individuals • Usually uses Lightweight Directory Access Protocol (active directory similar to our school network)
Validating a Certificate 1. Compare the CA that digitally signed the certificate to a list of CAs that have already been loaded into the receiver’s computer 2. Calculate a message digest (MD) for the certificate 3. Use the CA’s public key to decrypt the digital signature and recover what is claimed to be the original message digest embedded within the certificate (validating the digital signature) 4. Compare the two resulting message digest values to ensure the integrity of the certificate
Validating a certificate 5. Review the identification information within the certificate, such as the e-mail address 6. Review the validity dates 7. Check a revocation list to see if the certificate has been revoked
Centralized PKIs • Keys are generated and stored on a central server • Keys are transmitted to the individual systems as needed
Decentralized PKIs • Software on individual computers generates and stores cryptographic keys local to the systems themselves
Key Archiving • Backing up keys and securely storing them in a repository
Key Recovery • Process of restoring lost keys to the users or the company
Dual Control Recovery • Two people must be present to carry out the task
Key Escrow • Process of giving keys to a third party so that they can decrypt and read sensitive information if the need arises • Almost always pertains to handing over encryption keys to the government
- Slides: 48