Cyber Security Assessment Management CSAM Five Services One
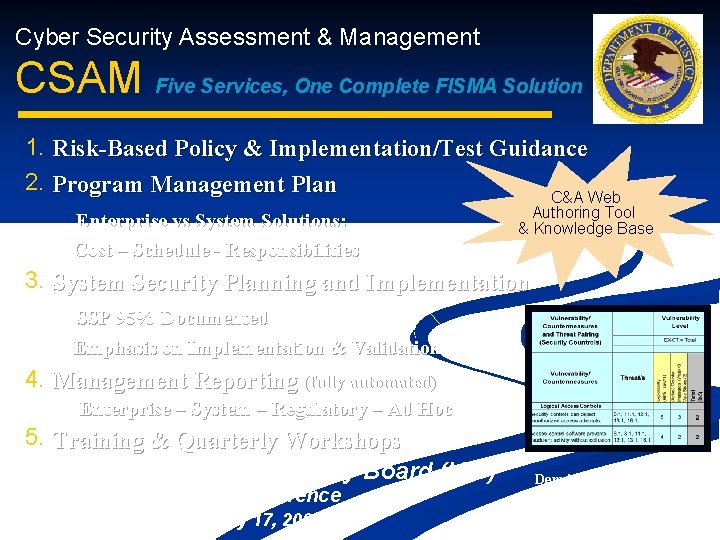
Cyber Security Assessment & Management CSAM Five Services, One Complete FISMA Solution 1. 2. Risk-Based Policy & Implementation/Test Guidance Program Management Plan C&A Web Enterprise vs System Solutions: Cost – Schedule - Responsibilities Authoring Tool & Knowledge Base 3. System Security Planning and Implementation SSP 95% Documented Emphasis on Implementation & Validation 4. Management Reporting (fully automated) Enterprise – System – Regulatory – Ad Hoc 5. Training & Quarterly Workshops Intergovernmental Advisory Board (IAB) Teleconference May 17, 2007 Dennis Heretick Deputy CIO, IT Security Department of Justice 1 Dennis. heretick@usdoj. gov
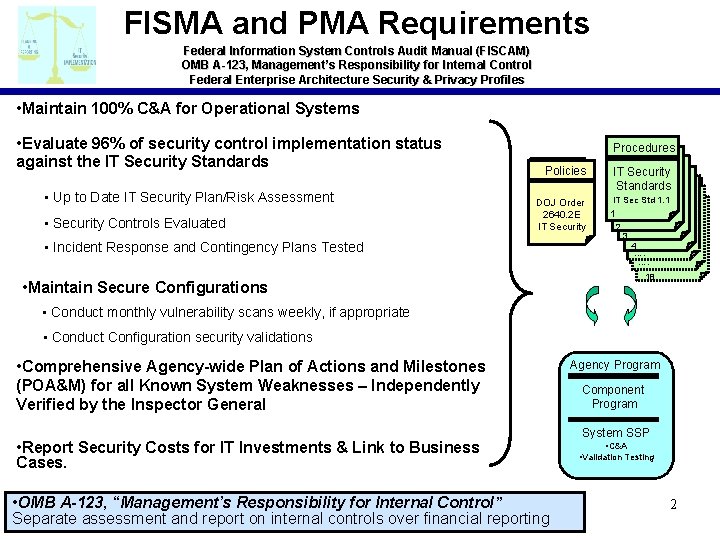
FISMA and PMA Requirements Federal Information System Controls Audit Manual (FISCAM) OMB A-123, Management’s Responsibility for Internal Control Federal Enterprise Architecture Security & Privacy Profiles • Maintain 100% C&A for Operational Systems • Evaluate 96% of security control implementation status against the IT Security Standards • Up to Date IT Security Plan/Risk Assessment • Security Controls Evaluated Procedures Policies IT Security Standards DOJ Order 2640. 2 E IT Security IT Sec Std 1. 1 • Incident Response and Contingency Plans Tested 1 2 3 4 …. …. 18 • Maintain Secure Configurations • Conduct monthly vulnerability scans weekly, if appropriate • Conduct Configuration security validations • Comprehensive Agency-wide Plan of Actions and Milestones (POA&M) for all Known System Weaknesses – Independently Verified by the Inspector General • Report Security Costs for IT Investments & Link to Business Cases. • OMB A-123, “Management’s Responsibility for Internal Control” Separate assessment and report on internal controls over financial reporting Agency Program Component Program System SSP • C&A • Validation Testing 2
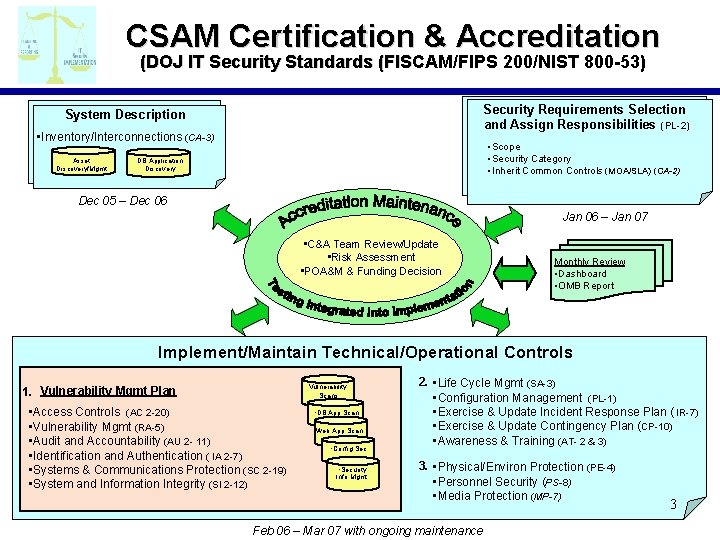
CSAM Certification & Accreditation (DOJ IT Security Standards (FISCAM/FIPS 200/NIST 800 -53) Security Requirements Selection and Assign Responsibilities (PL-2) System Description • Inventory/Interconnections (CA-3) Asset Discovery/Mgmt • Scope • Security Category • Inherit Common Controls (MOA/SLA) (CA-2) DB Application Discovery Dec 05 – Dec 06 Jan 06 – Jan 07 • C&A Team Review/Update • Risk Assessment • POA&M & Funding Decision Monthly Review • Dashboard • OMB Report Implement/Maintain Technical/Operational Controls Vulnerability Scans 1. Vulnerability Mgmt Plan • Access Controls (AC 2 -20) • Vulnerability Mgmt (RA-5) • Audit and Accountability (AU 2 - 11) • Identification and Authentication ( IA 2 -7) • Systems & Communications Protection (SC 2 -19) • System and Information Integrity (SI 2 -12) • DB App Scan • Web App Scan • Config Sec • Security Info Mgmt 2. • Life Cycle Mgmt (SA-3) • Configuration Management (PL-1) • Exercise & Update Incident Response Plan ( IR-7) • Exercise & Update Contingency Plan (CP-10) • Awareness & Training (AT- 2 & 3) 3. • Physical/Environ Protection (PE-4) • Personnel Security (PS-8) • Media Protection (MP-7) Feb 06 – Mar 07 with ongoing maintenance 3
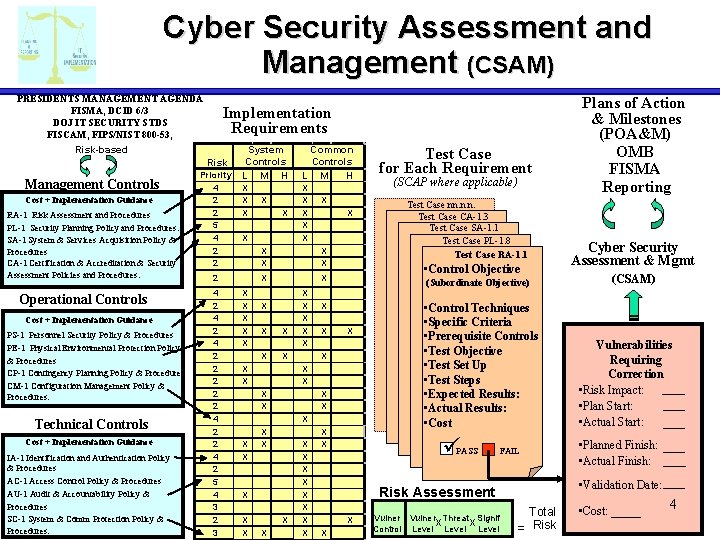
Cyber Security Assessment and Management (CSAM) PRESIDENTS MANAGEMENT AGENDA FISMA, DCID 6/3 DOJ IT SECURITY STDS FISCAM, FIPS/NIST 800 -53, Risk-based Implementation Requirements Risk Management Controls Cost + Implementation Guidance RA-1 Risk Assessment and Procedures PL-1 Security Planning Policy and Procedures. SA-1 System & Services Acquisition Policy & Procedures CA-1 Certification & Accreditation & Security Assessment Policies and Procedures. Operational Controls Cost + Implementation Guidance PS-1 Personnel Security Policy & Procedures PE-1 Physical Environmental Protection Policy & Procedures CP-1 Contingency Planning Policy & Procedures CM-1 Configuration Management Policy & Procedures. Technical Controls Cost + Implementation Guidance IA-1 Identification and Authentication Policy & Procedures AC-1 Access Control Policy & Procedures AU-1 Audit & Accountability Policy & Procedures SC-1 System & Comm Protection Policy & Procedures. Priority 4 2 2 5 4 2 2 System Controls L M H Common Controls L M H X X X X X 2 4 2 4 2 2 2 4 2 5 4 3 2 3 X X X X X X X X X X X X X Test Case nn. n. n. Test Case CA-1. 3 Test Case SA-1. 1 Test Case PL-1. 8 Test Case RA-1. 1 (Subordinate Objective) X X X (SCAP where applicable) • Control Objective X X Test Case for Each Requirement X X • Control Techniques • Specific Criteria • Prerequisite Controls • Test Objective • Test Set Up • Test Steps • Expected Results: • Actual Results: • Cost ü PASS FAIL X Vulner Threat Signif X X Control Level Cyber Security Assessment & Mgmt (CSAM) Vulnerabilities Requiring Correction • Risk Impact: • Plan Start: • Actual Start: • Planned Finish: • Actual Finish: • Validation Date: Risk Assessment X Plans of Action & Milestones (POA&M) OMB FISMA Reporting Total = Risk • Cost: _____ 4
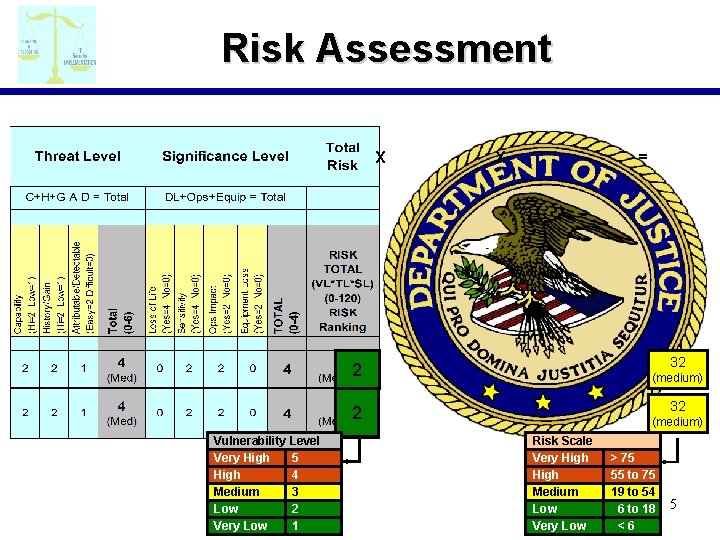
Risk Assessment X X = 32 2 (medium) 32 2 Vulnerability Level Very High 5 High 4 Medium 3 Low 2 Very Low 1 (medium) Risk Scale Very High Medium Low Very Low > 75 55 to 75 19 to 54 6 to 18 <6 5
Identifies Moderate and High Risk Weaknesses Provides impacts and costs to correct Identified weaknesses Documents POA&M to correct weaknesses 6
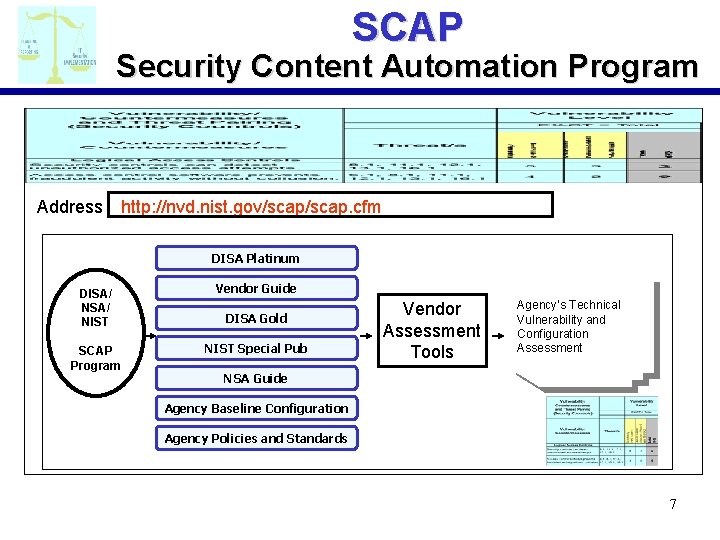
SCAP Security Content Automation Program Address http: //nvd. nist. gov/scap. cfm DISA Platinum DISA/ NIST SCAP Program Vendor Guide DISA Gold NIST Special Pub Vendor Assessment Tools Agency’s Technical Vulnerability and Configuration Assessment NSA Guide Agency Baseline Configuration Agency Policies and Standards 7
My Schedule – Tasking Synopsis System user Drill-down links you directly to the point of interest. 8
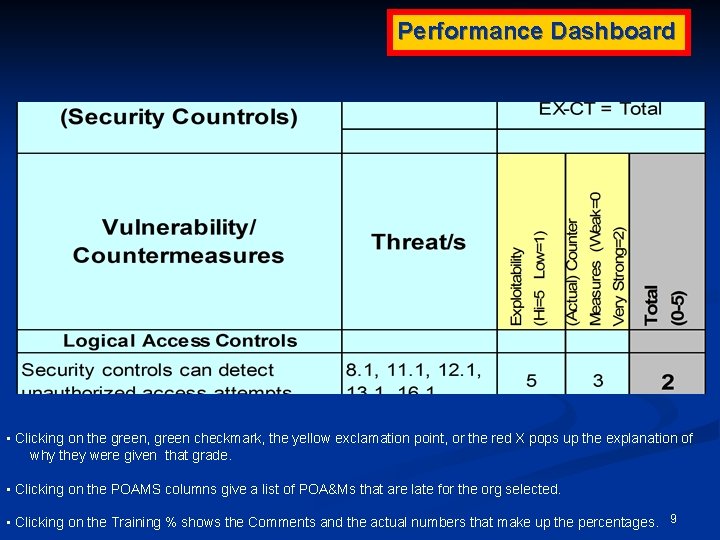
Performance Dashboard • Clicking on the green, green checkmark, the yellow exclamation point, or the red X pops up the explanation of why they were given that grade. • Clicking on the POAMS columns give a list of POA&Ms that are late for the org selected. • Clicking on the Training % shows the Comments and the actual numbers that make up the percentages. 9
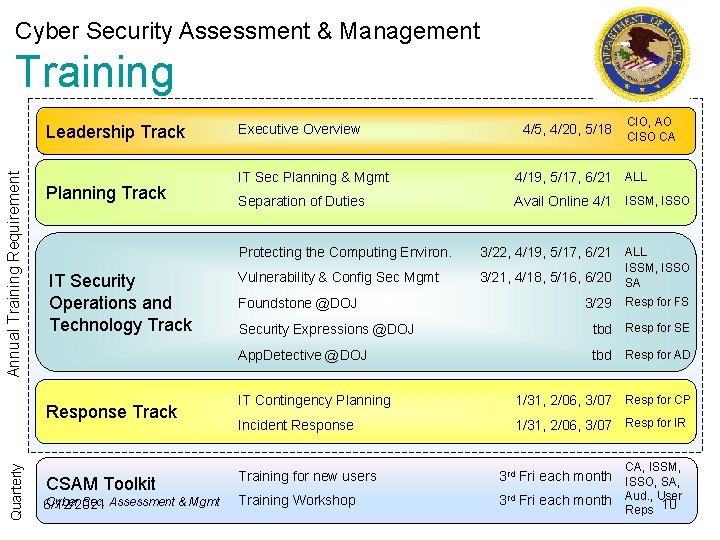
Cyber Security Assessment & Management Training Annual Training Requirement Leadership Track Planning Track IT Security Operations and Technology Track Quarterly Response Track CSAM Toolkit Cyber Sec. Assessment & Mgmt 6/12/2021 Executive Overview 4/5, 4/20, 5/18 CIO, AO CISO CA IT Sec Planning & Mgmt 4/19, 5/17, 6/21 ALL Separation of Duties Avail Online 4/1 ISSM, ISSO Protecting the Computing Environ. 3/22, 4/19, 5/17, 6/21 ALL Vulnerability & Config Sec Mgmt 3/21, 4/18, 5/16, 6/20 SA Foundstone @DOJ ISSM, ISSO 3/29 Resp for FS Security Expressions @DOJ tbd Resp for SE App. Detective @DOJ tbd Resp for AD IT Contingency Planning 1/31, 2/06, 3/07 Resp for CP Incident Response 1/31, 2/06, 3/07 Resp for IR Training for new users Training Workshop CA, ISSM, 3 rd Fri each month ISSO, SA, 3 rd Fri each month Aud. , User 10 Reps
- Slides: 10