National Cyber Security Policy 2013 Cyber Security Conference
National Cyber Security Policy 2013 Cyber Security Conference, Raipur CYBER SECURITY CONFERENCE, RAIPUR (CHHATTISGARH) (Chhattisgarh) 19 July 2018 Changes, Amendments Recommendations
Dinesh O Bareja CISA, CISM, ITIL, ISMS, Cert ERM, Cert IPR ABOUT ME • Researcher – India. Watch & Open Security Alliance • Advisor – Pyramid Cyber Security & Forensic Pvt Ltd Cyber Peace Foundation • Co-Founder – Indian Honeynet Project Enterprise & Government Policy Development; Cyber Security Strategy, Design, Architecture; Threat Modelling; Security Audit; Governance & Risk CYBER SECURITY CONFERENCE, RAIPUR (CHHATTISGARH) 19 July 2018
Introduction • Before we look at the NCSP from my point of view • We will spend a few minutes setting the context of this talk • 1 st Concept of time • 2 nd Cyber attack surface (global or local is no different) • 3 rd a little bit of theory of policy development CYBER SECURITY CONFERENCE, RAIPUR (CHHATTISGARH) 19 July 2018
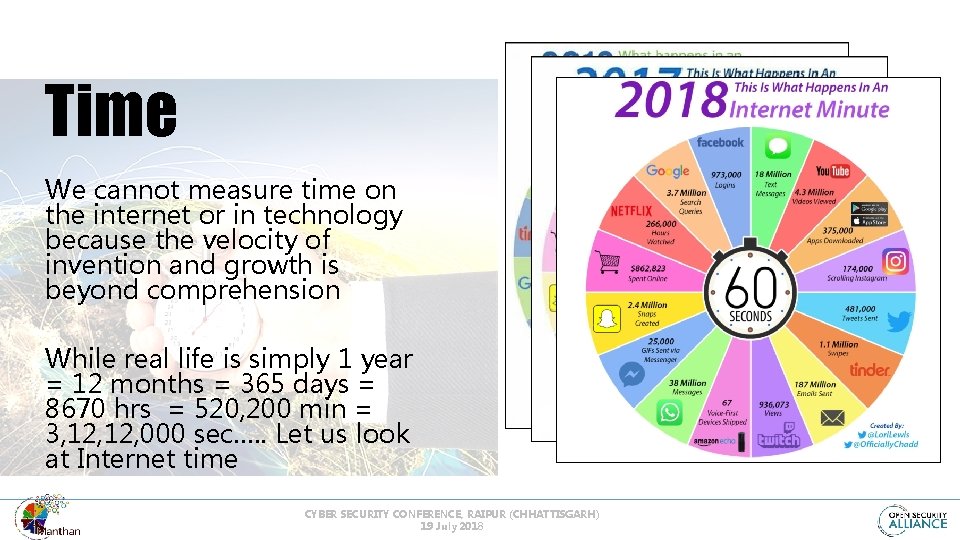
Time We cannot measure time on the internet or in technology because the velocity of invention and growth is beyond comprehension While real life is simply 1 year = 12 months = 365 days = 8670 hrs = 520, 200 min = 3, 12, 000 sec…. . Let us look at Internet time CYBER SECURITY CONFERENCE, RAIPUR (CHHATTISGARH) 19 July 2018
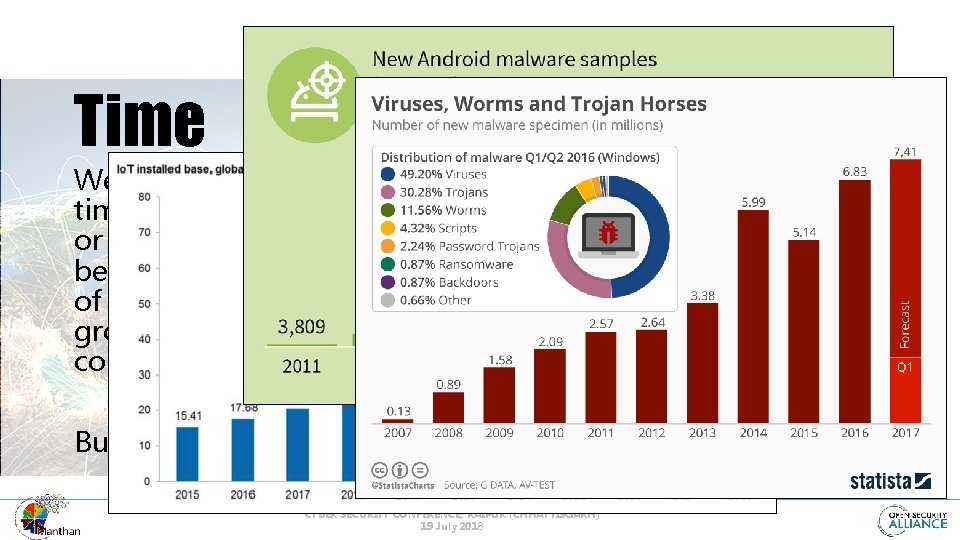
Time We cannot measure time on the internet or in technology because the velocity of invention and growth is beyond comprehension But still… in trying… CYBER SECURITY CONFERENCE, RAIPUR (CHHATTISGARH) 19 July 2018
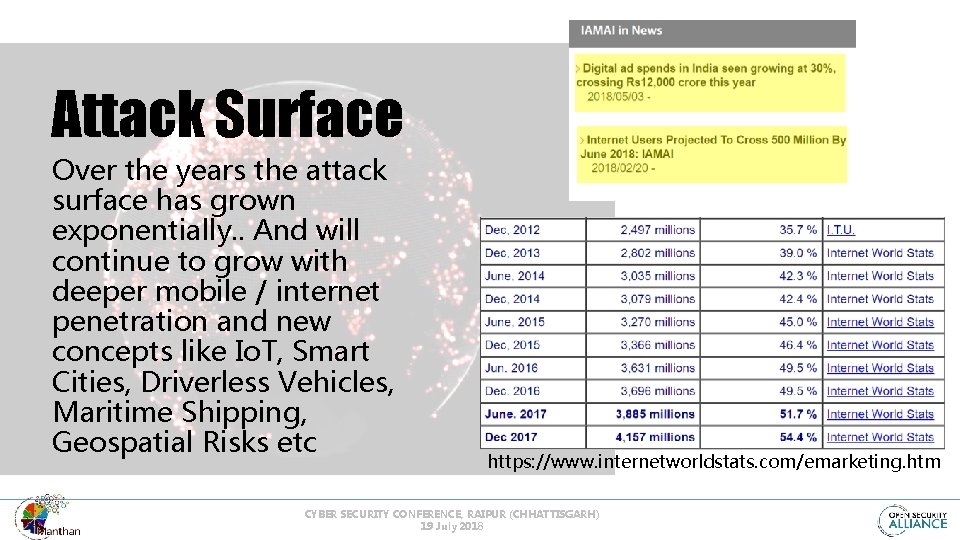
Attack Surface Over the years the attack surface has grown exponentially. . And will continue to grow with deeper mobile / internet penetration and new concepts like Io. T, Smart Cities, Driverless Vehicles, Maritime Shipping, Geospatial Risks etc https: //www. internetworldstats. com/emarketing. htm CYBER SECURITY CONFERENCE, RAIPUR (CHHATTISGARH) 19 July 2018
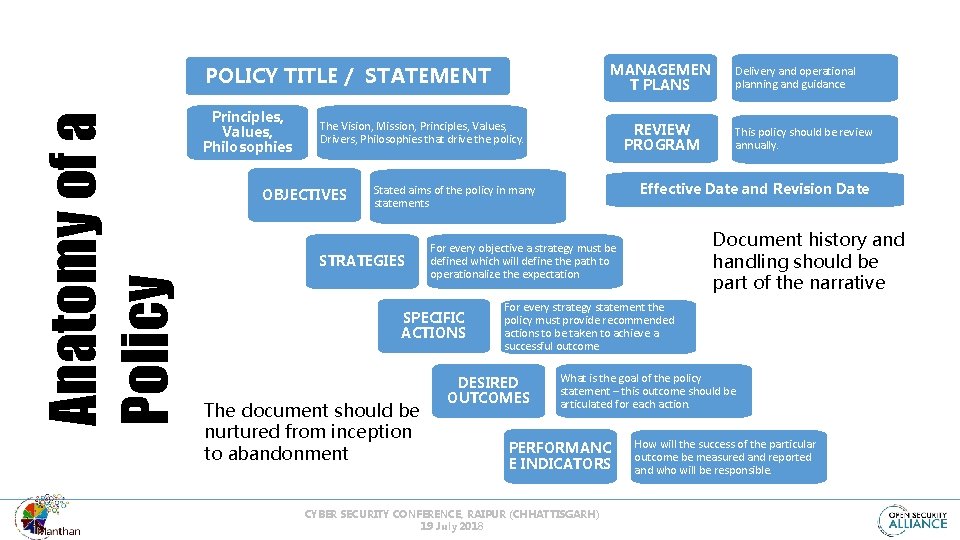
MANAGEMEN T PLANS Anatomy of a Policy POLICY TITLE / STATEMENT Principles, Values, Philosophies The Vision, Mission, Principles, Values, Drivers, Philosophies that drive the policy. OBJECTIVES REVIEW PROGRAM The document should be nurtured from inception to abandonment Document history and handling should be part of the narrative For every objective a strategy must be defined which will define the path to operationalize the expectation SPECIFIC ACTIONS This policy should be review annually. Effective Date and Revision Date Stated aims of the policy in many statements STRATEGIES Delivery and operational planning and guidance For every strategy statement the policy must provide recommended actions to be taken to achieve a successful outcome DESIRED OUTCOMES What is the goal of the policy statement – this outcome should be articulated for each action. PERFORMANC E INDICATORS CYBER SECURITY CONFERENCE, RAIPUR (CHHATTISGARH) 19 July 2018 How will the success of the particular outcome be measured and reported and who will be responsible.
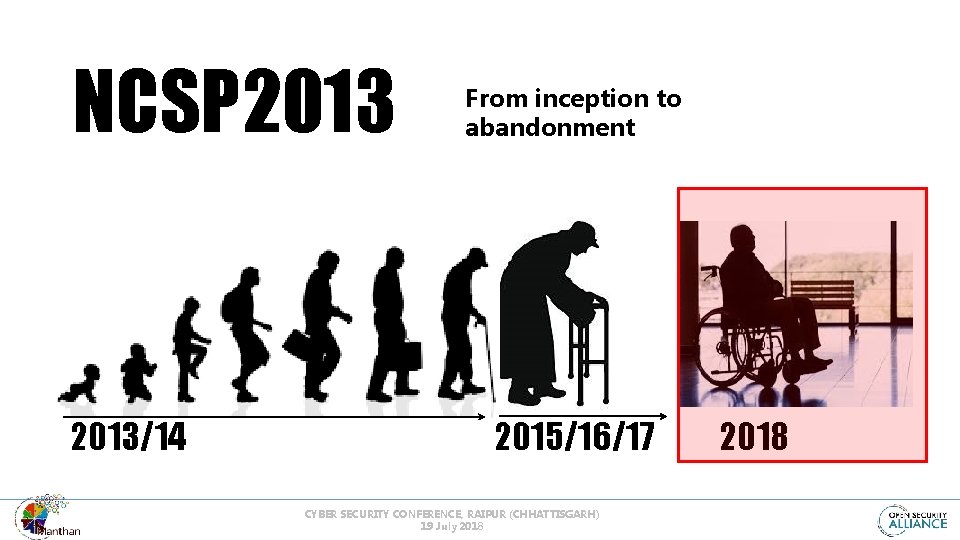
NCSP 2013/14 From inception to abandonment 2015/16/17 CYBER SECURITY CONFERENCE, RAIPUR (CHHATTISGARH) 19 July 2018

We have HOPE CYBER SECURITY CONFERENCE, RAIPUR (CHHATTISGARH) 19 July 2018
�� ���� National Cyber Security Policy 2013 CYBER SECURITY CONFERENCE, RAIPUR (CHHATTISGARH) 19 July 2018 � �
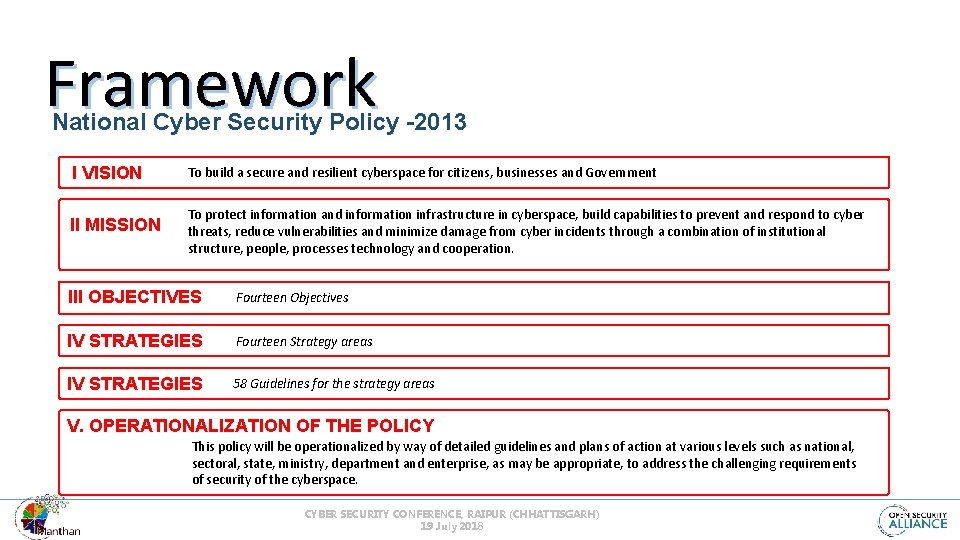
Framework National Cyber Security Policy -2013 I VISION To build a secure and resilient cyberspace for citizens, businesses and Government II MISSION To protect information and information infrastructure in cyberspace, build capabilities to prevent and respond to cyber threats, reduce vulnerabilities and minimize damage from cyber incidents through a combination of institutional structure, people, processes technology and cooperation. III OBJECTIVES Fourteen Objectives IV STRATEGIES Fourteen Strategy areas IV STRATEGIES 58 Guidelines for the strategy areas V. OPERATIONALIZATION OF THE POLICY This policy will be operationalized by way of detailed guidelines and plans of action at various levels such as national, sectoral, state, ministry, department and enterprise, as may be appropriate, to address the challenging requirements of security of the cyberspace. CYBER SECURITY CONFERENCE, RAIPUR (CHHATTISGARH) 19 July 2018
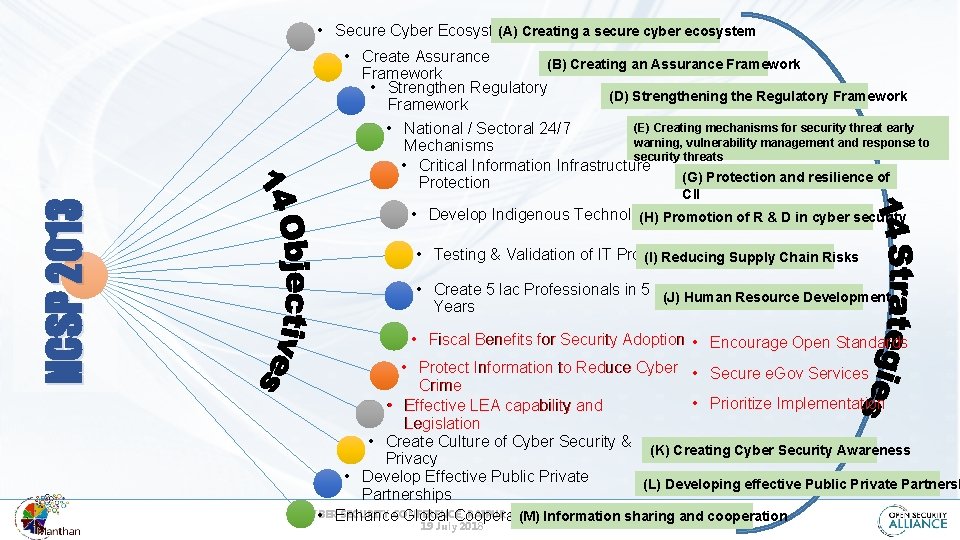
(A) Creating a secure cyber ecosystem • Secure Cyber Ecosystem NCSP 2013 • Create Assurance (B) Creating an Assurance Framework • Strengthen Regulatory (D) Strengthening the Regulatory Framework (E) Creating mechanisms for security threat early • National / Sectoral 24/7 warning, vulnerability management and response to Mechanisms security threats • Critical Information Infrastructure (G) Protection and resilience of Protection CII • Develop Indigenous Technologies (H) Promotion of R & D in cyber security • Testing & Validation of IT Products (I) Reducing Supply Chain Risks • Create 5 lac Professionals in 5 (J) Human Resource Development Years • Fiscal Benefits for Security Adoption • Encourage Open Standards • Protect Information to Reduce Cyber • Secure e. Gov Services Crime • Prioritize Implementation • Effective LEA capability and Legislation • Create Culture of Cyber Security & (K) Creating Cyber Security Awareness Privacy • Develop Effective Public Private (L) Developing effective Public Private Partnerships CYBER SECURITY CONFERENCE, RAIPUR (CHHATTISGARH) • Enhance Global Cooperation (M) Information sharing and cooperation 19 July 2018
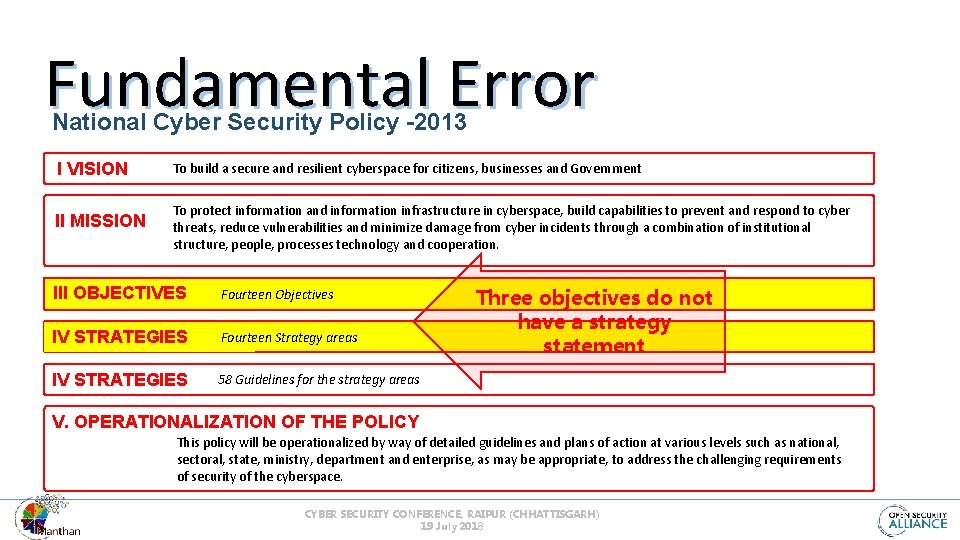
Fundamental Error National Cyber Security Policy -2013 I VISION To build a secure and resilient cyberspace for citizens, businesses and Government II MISSION To protect information and information infrastructure in cyberspace, build capabilities to prevent and respond to cyber threats, reduce vulnerabilities and minimize damage from cyber incidents through a combination of institutional structure, people, processes technology and cooperation. III OBJECTIVES Fourteen Objectives IV STRATEGIES Fourteen Strategy areas IV STRATEGIES 58 Guidelines for the strategy areas Three objectives do not have a strategy statement V. OPERATIONALIZATION OF THE POLICY This policy will be operationalized by way of detailed guidelines and plans of action at various levels such as national, sectoral, state, ministry, department and enterprise, as may be appropriate, to address the challenging requirements of security of the cyberspace. CYBER SECURITY CONFERENCE, RAIPUR (CHHATTISGARH) 19 July 2018
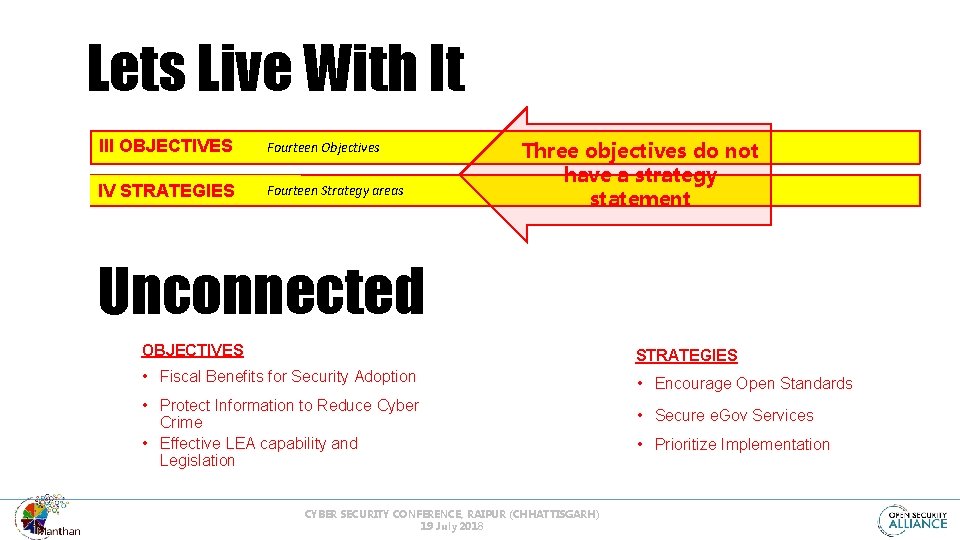
Lets Live With It III OBJECTIVES Fourteen Objectives IV STRATEGIES Fourteen Strategy areas Three objectives do not have a strategy statement Unconnected OBJECTIVES STRATEGIES • Fiscal Benefits for Security Adoption • Encourage Open Standards • Protect Information to Reduce Cyber Crime • Effective LEA capability and Legislation CYBER SECURITY CONFERENCE, RAIPUR (CHHATTISGARH) 19 July 2018 • Secure e. Gov Services • Prioritize Implementation
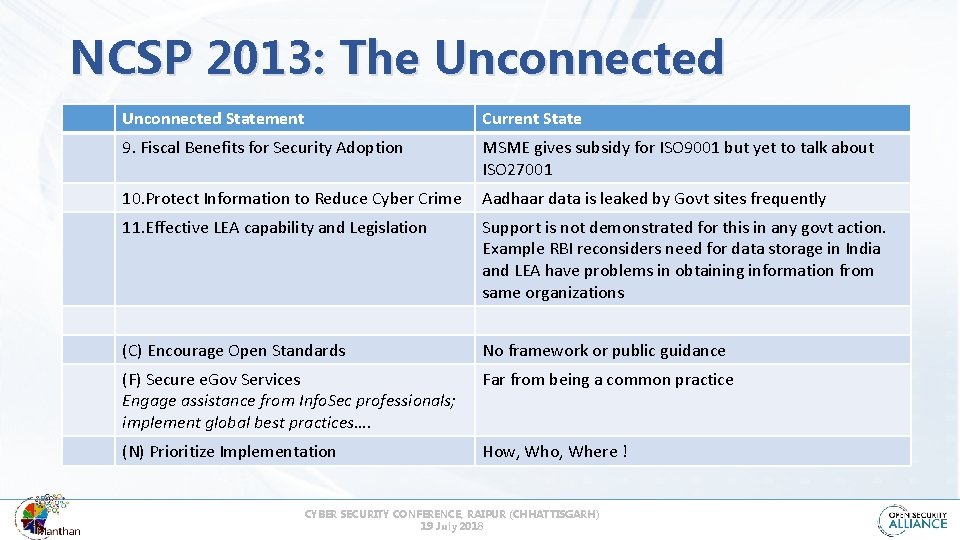
NCSP 2013: The Unconnected Statement Current State 9. Fiscal Benefits for Security Adoption MSME gives subsidy for ISO 9001 but yet to talk about ISO 27001 10. Protect Information to Reduce Cyber Crime Aadhaar data is leaked by Govt sites frequently 11. Effective LEA capability and Legislation Support is not demonstrated for this in any govt action. Example RBI reconsiders need for data storage in India and LEA have problems in obtaining information from same organizations (C) Encourage Open Standards No framework or public guidance (F) Secure e. Gov Services Engage assistance from Info. Sec professionals; implement global best practices…. Far from being a common practice (N) Prioritize Implementation How, Who, Where ! CYBER SECURITY CONFERENCE, RAIPUR (CHHATTISGARH) 19 July 2018
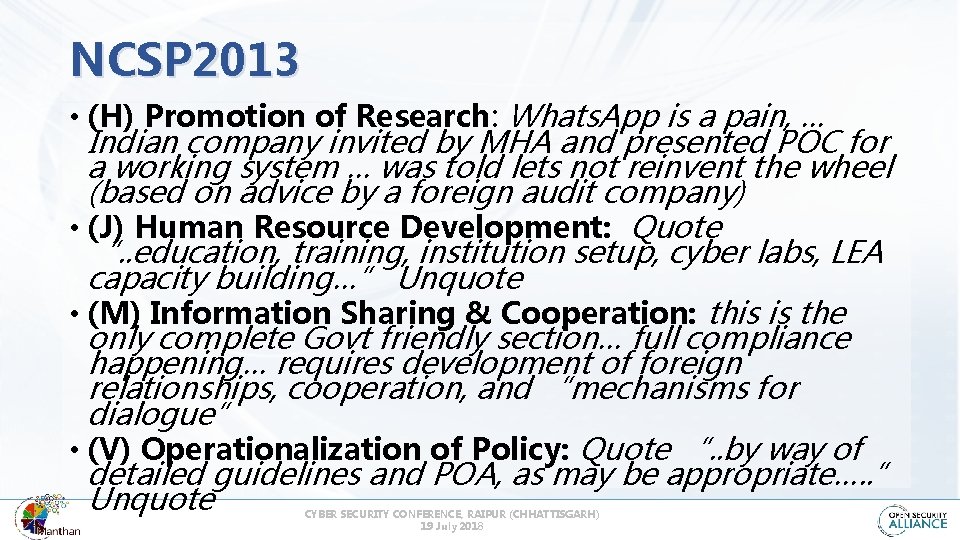
NCSP 2013 • (H) Promotion of Research: Whats. App is a pain, … Indian company invited by MHA and presented POC for a working system … was told lets not reinvent the wheel (based on advice by a foreign audit company) • (J) Human Resource Development: Quote “. . education, training, institution setup, cyber labs, LEA capacity building…” Unquote • (M) Information Sharing & Cooperation: this is the only complete Govt friendly section… full compliance happening… requires development of foreign relationships, cooperation, and “mechanisms for dialogue” • (V) Operationalization of Policy: Quote “. . by way of detailed guidelines and POA, as may be appropriate…. . ” Unquote CYBER SECURITY CONFERENCE, RAIPUR (CHHATTISGARH) 19 July 2018
National Cyber Security Policy 20 xx NCSP 2. 0 – Possibilities & Expectations CYBER SECURITY CONFERENCE, RAIPUR (CHHATTISGARH) 19 July 2018
NCSP is static should be dynamic • Policies are dynamic and not expected to be just static lists of goals or laws • Policy blueprints have to be implemented, to achieve defined objectives following planned actions by designated stakeholders • National policies are about what happens 'on the ground' when they are implemented • Transparency in reporting progress / challenges is essential to build public confidence CYBER SECURITY CONFERENCE, RAIPUR (CHHATTISGARH) 19 July 2018
NCSP 2. 0 • Responsible office that will own and implement the Policy • Policy MUST provide guidance via supplementary action plans • Empower the implementing body with defined milestones • Review and update Policy to remain relevant in changed technology ecosystem • Policy committee to meet quarterly / half-yearly for checkup CYBER SECURITY CONFERENCE, RAIPUR (CHHATTISGARH) 19 July 2018
NCSP 2. 0 • Designate a responsible office that will create, issue, own and implement the Policy • Policy MUST provide guidance via supplementary action plans (complete the anatomy) • Create and empower a body with implementation responsibility, necessary authority that will work with a defined plan and milestones • Review and update Policy to remain relevant in changed technology ecosystem • Policy committee to meet quarterly / half-yearly for check-up CYBER SECURITY CONFERENCE, RAIPUR (CHHATTISGARH) 19 July 2018
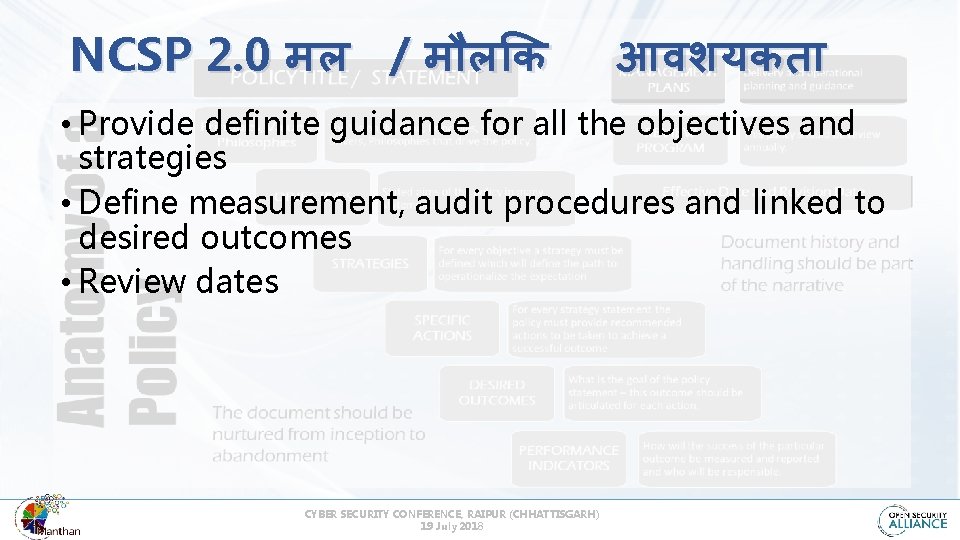
NCSP 2. 0 मल / म ल क आवशयकत • Provide definite guidance for all the objectives and strategies • Define measurement, audit procedures and linked to desired outcomes • Review dates CYBER SECURITY CONFERENCE, RAIPUR (CHHATTISGARH) 19 July 2018
NCSP 2. 0 Why Reinvent The Wheel NCSP 2. 0 in the year 20 xx CYBER SECURITY CONFERENCE, RAIPUR (CHHATTISGARH) 19 July 2018
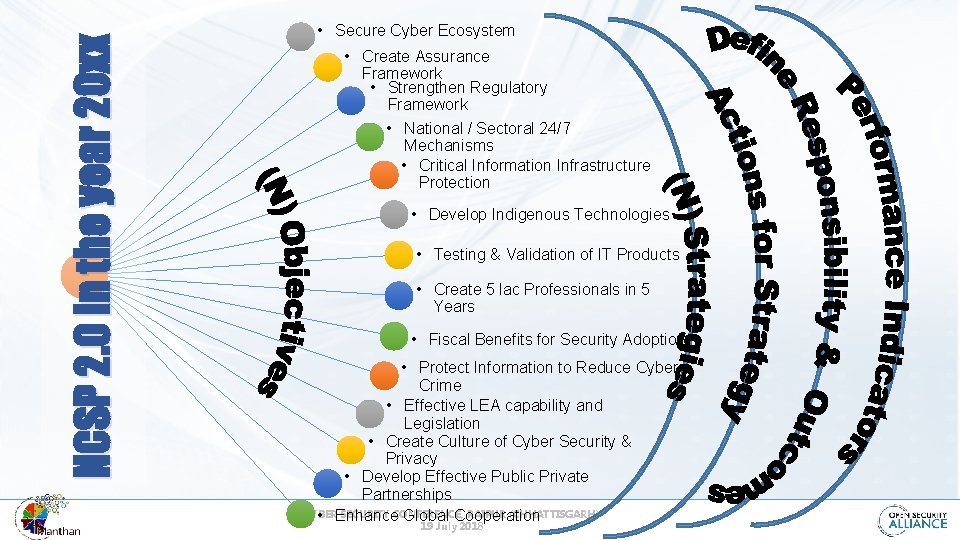
NCSP 2. 0 in the year 20 xx • Secure Cyber Ecosystem • Create Assurance Framework • Strengthen Regulatory Framework • National / Sectoral 24/7 Mechanisms • Critical Information Infrastructure Protection • Develop Indigenous Technologies • Testing & Validation of IT Products • Create 5 lac Professionals in 5 Years • Fiscal Benefits for Security Adoption • Protect Information to Reduce Cyber Crime • Effective LEA capability and Legislation • Create Culture of Cyber Security & Privacy • Develop Effective Public Private Partnerships CYBER SECURITY CONFERENCE, RAIPUR (CHHATTISGARH) • Enhance Global Cooperation 19 July 2018
Waiting for Divine Intervention CYBER SECURITY CONFERENCE, RAIPUR (CHHATTISGARH) 19 July 2018

ABOUT ME & Information Security professional working hard to be abreast of technology, risks, threats, opportunities and looks forward to the excitement of the future. . MY CONTACT INFORMATION CYBER SECURITY CONFERENCE, RAIPUR (CHHATTISGARH) 19 July 2018 dinesh@opensecurityalliance. org @bizsprite linkedin. com/in/dineshbareja +91. 9769890505 dineshobareja infosecgallery. blgspot. com securambling. blogspot. com
What professional infosec expertise and passion to demolish the hype and enable real-life balance in cybersecurity policy, strategy, training and operations at the national, enterprise or individual level – we bring the E Where Who ABOUT A Reality Check On The Past Present & Future of National Security & Cybersecurity dinesh@opensecurityalliance. org @bizsprite L: CYBER SECURITY CONFERENCE, RAIPUR (CHHATTISGARH) 19 July 2018 linkedin. com/in/dineshbareja +91. 9769890505 dineshobareja indiawatch. in dineshbareja. com
License and Copyright Released in the public domain under Creative Commons License (Attribution- Noncommercial 2. 5 India) http: //creativecommons. org/licenses/by-nc-sa/2. 5/in/ The information and practices listed in this document are provided as is and for guidance purposes only, and should not be construed to be a standard for practice or reference (unless mentioned otherwise). Readers are urged to make informed decisions before adopting the information given in this document. The author(s) may not be held responsible, or liable, in any event and for any issues arising out of the use of the information and / or guidelines included in this document. Further, we do not give any warranty on accuracy, completeness, functionality, usefulness or other assurances as to the content in the document. We disclaim all responsibility for any losses, damage caused or attributed, directly or indirectly, from reliance on and the use of such information. Readers are welcome to provide feedback to the authors using the contact information provided in this document. This document has been prepared for general public distribution so all animations have been converted to static images. Graphics and images are usually obtained from the internet and royalty free sources and are usually acknowledged by us. Errors may be expected in this practice and this is not intentional. -we resect creative rights and request owner(s) to inform us of any inadvertent omission. CYBER SECURITY CONFERENCE, RAIPUR (CHHATTISGARH) 19 July 2018
- Slides: 27