EndtoEnd Cyber Security David Francis European Cyber Security
End-to-End Cyber Security David Francis European Cyber Security Officer www. huawei. com
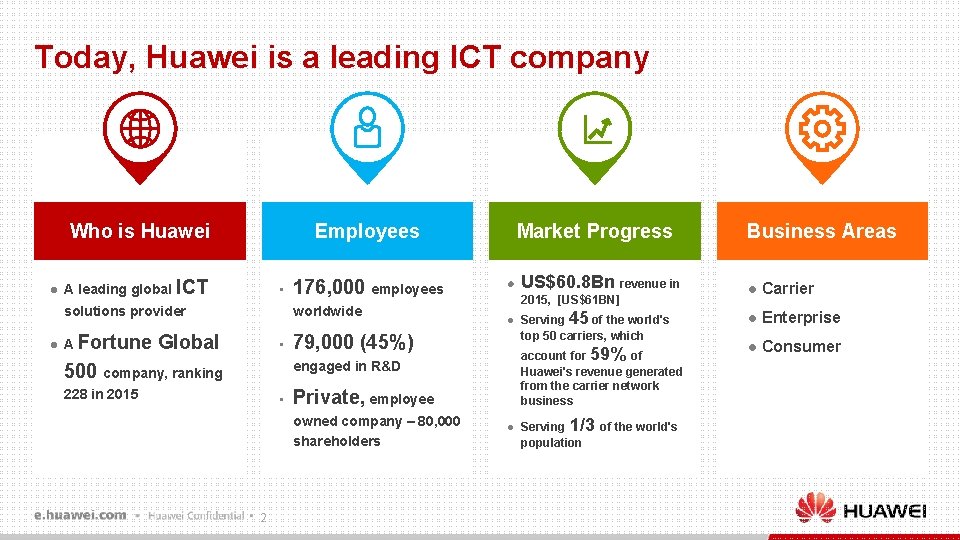
Today, Huawei is a leading ICT company Employees Who is Huawei l A leading global ICT • solutions provider l 176, 000 employees worldwide A Fortune Global • Market Progress l 2015, [US$61 BN] l 79, 000 (45%) 228 in 2015 • Private, employee owned company – 80, 000 shareholders 2 Serving 45 of the world's top 50 carriers, which account for 59% of Huawei's revenue generated from the carrier network business engaged in R&D 500 company, ranking US$60. 8 Bn revenue in l Serving 1/3 of the world's population Business Areas l Carrier l Enterprise l Consumer
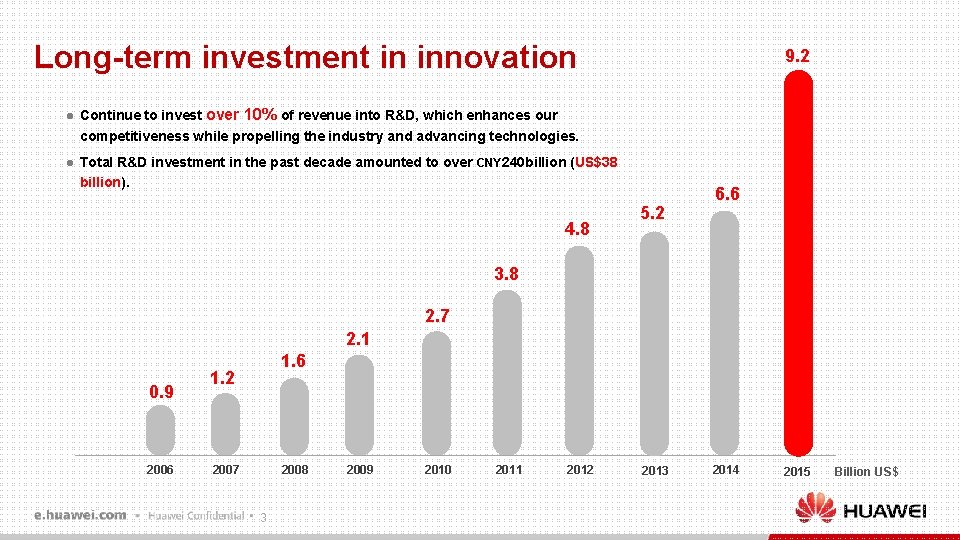
Long-term investment in innovation l l 9. 2 Continue to invest over 10% of revenue into R&D, which enhances our competitiveness while propelling the industry and advancing technologies. Total R&D investment in the past decade amounted to over CNY 240 billion (US$38 billion). 4. 8 5. 2 6. 6 3. 8 2. 7 2. 1 0. 9 2006 1. 2 2007 2008 3 2009 2010 2011 2012 2013 2014 2015 Billion US$
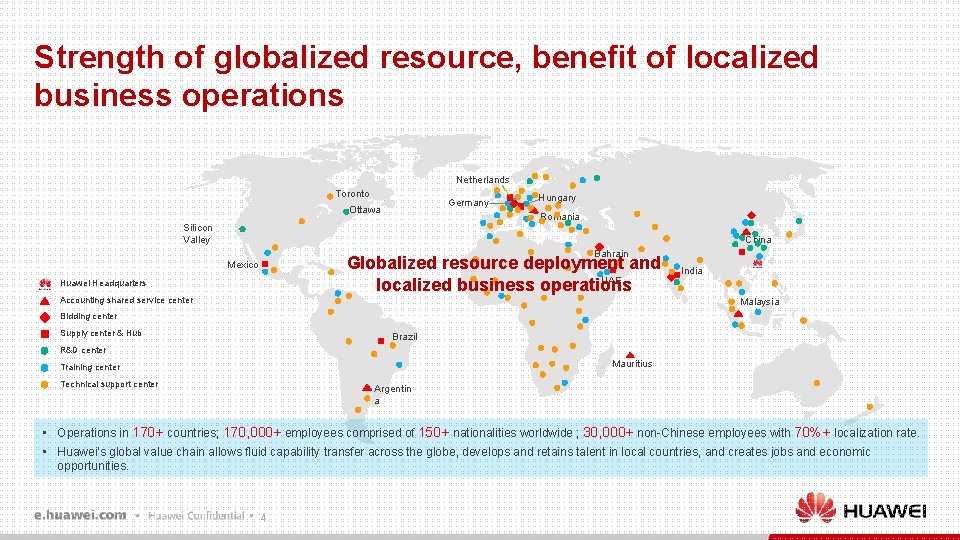
Strength of globalized resource, benefit of localized business operations Netherlands Toronto Germany Ottawa Hungary Romania Silicon Valley China Bahrain Globalized resource deployment and UAE localized business operations Mexico Huawei Headquarters Accounting shared service center India Malaysia Bidding center Supply center & Hub Brazil R&D center Mauritius Training center Technical support center Argentin a • Operations in 170+ countries; 170, 000+ employees comprised of 150+ nationalities worldwide ; 30, 000+ non-Chinese employees with 70%+ localization rate. • Huawei's global value chain allows fluid capability transfer across the globe, develops and retains talent in local countries, and creates jobs and economic opportunities. 4

Open networks connect the world, facilitate economic exchanges across regions, and promote global trade 7 Billion People In-vehicle Communication & Smart Traffic Vehicle communication, navigation, tracing, security and maintenance Remote monitoring & Healthy Remote Homecaring, Healthy, Safety mgmt 5 50 Billion Machine Auto Meter Reading Remote meter reading is safer and easier. Benefit for Green City construction Vending, cargos magt, E-wallet mgmt Merchandise Distribution RFID is used for merchandise trade and garbage sorting mgmt Electronic Consumer Info Sharing, on-line game, media download, communication and etc.
Technology and its use is advancing at an amazing rate and brings substantial benefits to all, but so are threats to the users of technology advancing l l 6 It is hard to stop the tide of progress and technology innovation. Threats are increasing every day. The bad guys are getting significantly more sophisticated. And international law provides its own security twists and turns. And finally it is impacting on almost all hardware and software – even air-gapped systems are being breached.
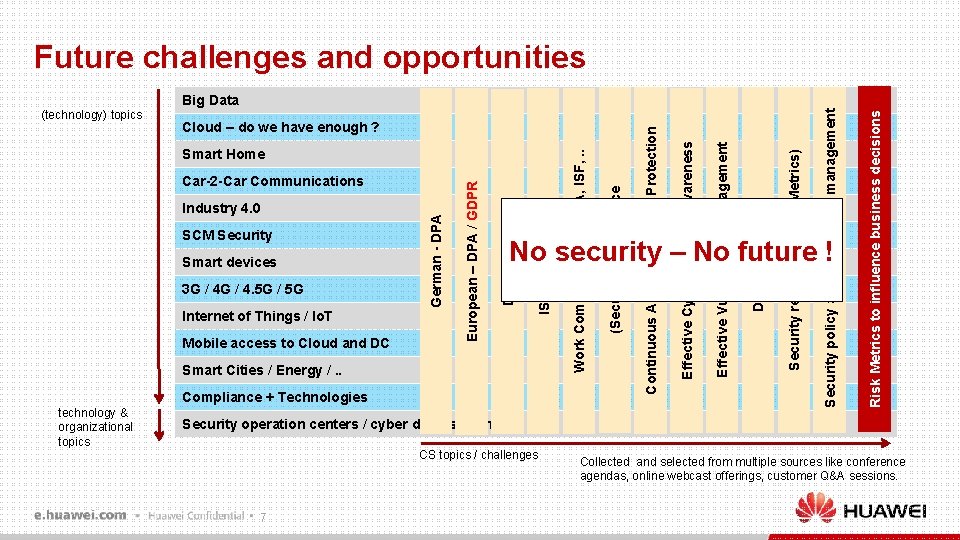
Future challenges and opportunities Compliance + Technologies Risk Metrics to influence business decisions Security policy and complaince management No security – No future ! Smart Cities / Energy /. . technology & organizational topics Security reporting (KPIs, Metrics) Mobile access to Cloud and DC Data Residency Internet of Things / Io. T Effective Vulnerability Management 3 G / 4. 5 G / 5 G Effective Cyber Security Awareness Smart devices ISO 27000 topics SCM Security Data Security Industry 4. 0 German - DPA Car-2 -Car Communications European – DPA / GDPR Smart Home (Security) Compliance Cloud – do we have enough ? Continuous Advanced Threat Protection Big Data Work Community @ GSMA, ISF, . . (technology) topics Security operation centers / cyber defense centers CS topics / challenges 7 Collected and selected from multiple sources like conference agendas, online webcast offerings, customer Q&A sessions.
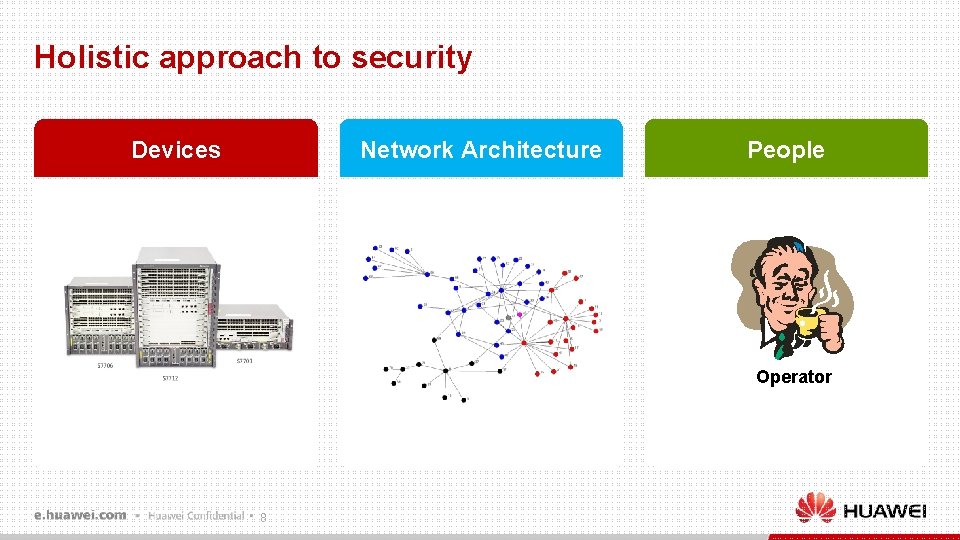
Holistic approach to security Network Architecture Devices People Operator 8
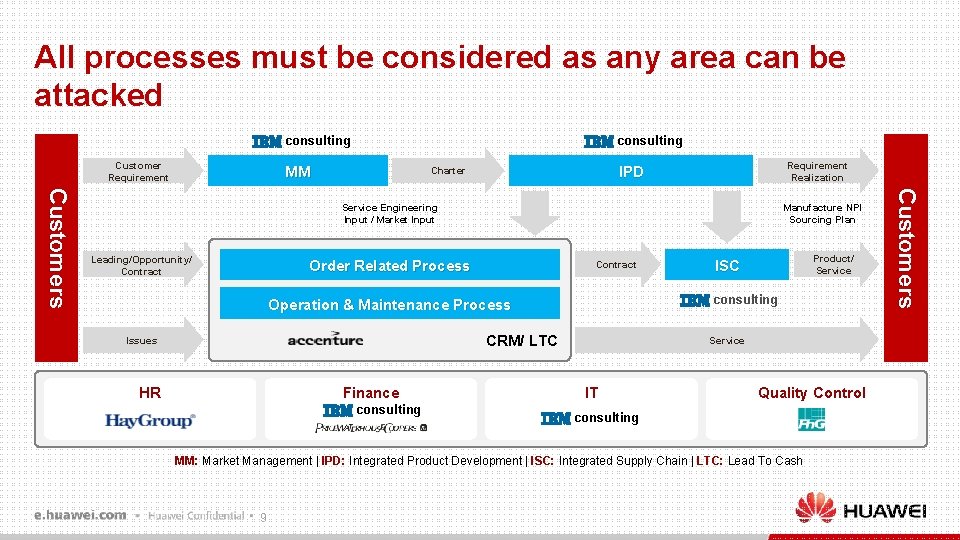
All processes must be considered as any area can be attacked consulting Customer Requirement consulting MM Requirement Realization IPD Charter Leading/Opportunity/ Contract Manufacture NPI Sourcing Plan Order Related Process Contract consulting Operation & Maintenance Process CRM/ LTC Issues HR Finance consulting Product/ Service ISC Service IT Quality Control consulting MM: Market Management | IPD: Integrated Product Development | ISC: Integrated Supply Chain | LTC: Lead To Cash 9 C u s to m e r s Service Engineering Input / Market Input
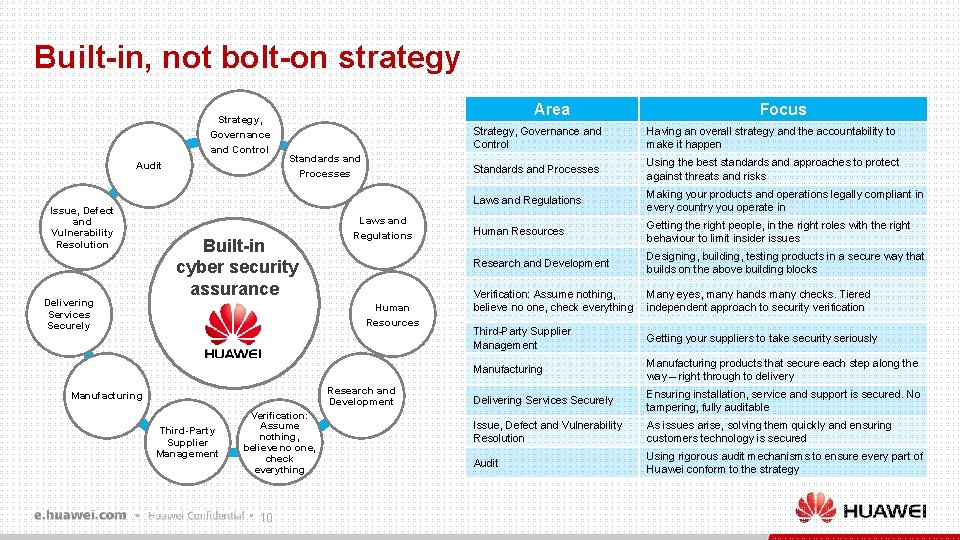
Built-in, not bolt-on strategy Strategy, Governance and Control Audit Issue, Defect and Vulnerability Resolution Delivering Services Securely Area Standards and Processes Built-in cyber security assurance Laws and Regulations Human Resources Research and Development Manufacturing Third-Party Supplier Management Verification: Assume nothing, believe no one, check everything 10 Focus Strategy, Governance and Control Having an overall strategy and the accountability to make it happen Standards and Processes Using the best standards and approaches to protect against threats and risks Laws and Regulations Making your products and operations legally compliant in every country you operate in Human Resources Getting the right people, in the right roles with the right behaviour to limit insider issues Research and Development Designing, building, testing products in a secure way that builds on the above building blocks Verification: Assume nothing, believe no one, check everything Many eyes, many hands many checks. Tiered independent approach to security verification Third-Party Supplier Management Getting your suppliers to take security seriously Manufacturing products that secure each step along the way – right through to delivery Delivering Services Securely Ensuring installation, service and support is secured. No tampering, fully auditable Issue, Defect and Vulnerability Resolution As issues arise, solving them quickly and ensuring customers technology is secured Audit Using rigorous audit mechanisms to ensure every part of Huawei conform to the strategy
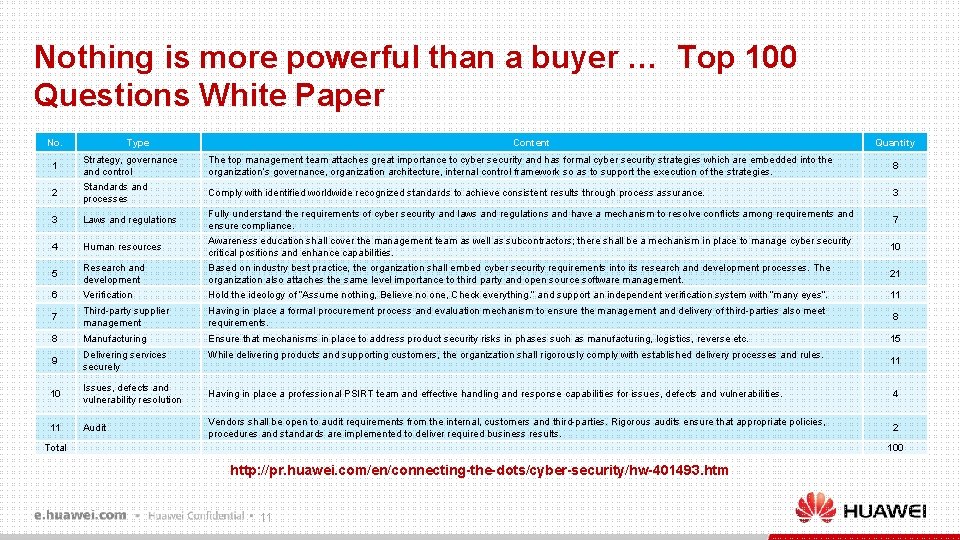
Nothing is more powerful than a buyer … Top 100 Questions White Paper No. 1 2 Type Strategy, governance and control Standards and processes Content Quantity The top management team attaches great importance to cyber security and has formal cyber security strategies which are embedded into the organization’s governance, organization architecture, internal control framework so as to support the execution of the strategies. 8 Comply with identified worldwide recognized standards to achieve consistent results through process assurance. 3 10 Research and development Fully understand the requirements of cyber security and laws and regulations and have a mechanism to resolve conflicts among requirements and ensure compliance. Awareness education shall cover the management team as well as subcontractors; there shall be a mechanism in place to manage cyber security critical positions and enhance capabilities. Based on industry best practice, the organization shall embed cyber security requirements into its research and development processes. The organization also attaches the same level importance to third party and open source software management. 6 Verification Hold the ideology of “Assume nothing, Believe no one, Check everything. ” and support an independent verification system with “many eyes”. 11 7 Third-party supplier management Having in place a formal procurement process and evaluation mechanism to ensure the management and delivery of third-parties also meet requirements. 8 8 Manufacturing Ensure that mechanisms in place to address product security risks in phases such as manufacturing, logistics, reverse etc. 15 9 Delivering services securely While delivering products and supporting customers, the organization shall rigorously comply with established delivery processes and rules. 10 Issues, defects and vulnerability resolution Having in place a professional PSIRT team and effective handling and response capabilities for issues, defects and vulnerabilities. 4 11 Audit Vendors shall be open to audit requirements from the internal, customers and third-parties. Rigorous audits ensure that appropriate policies, procedures and standards are implemented to deliver required business results. 2 3 Laws and regulations 4 Human resources 5 Total 7 21 11 100 http: //pr. huawei. com/en/connecting-the-dots/cyber-security/hw-401493. htm 11
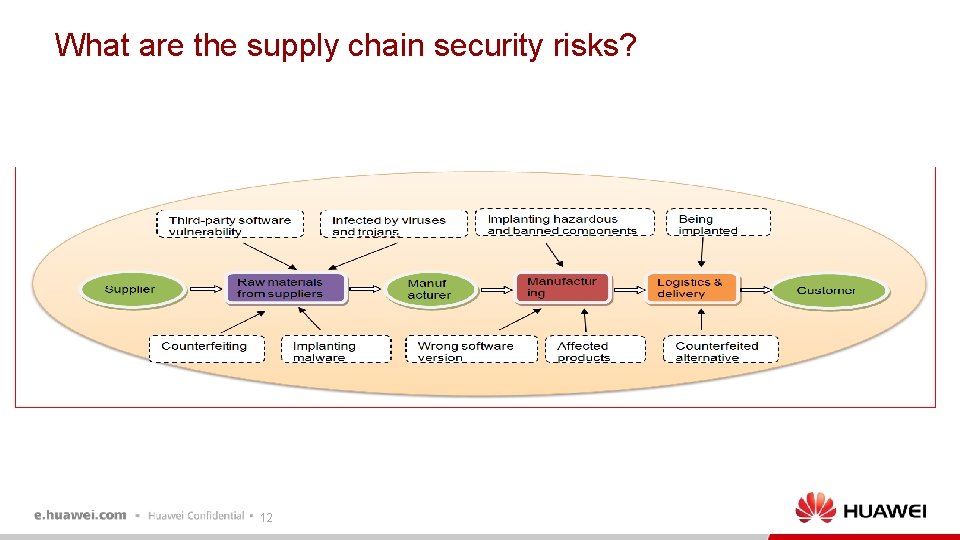
What are the supply chain security risks? 12
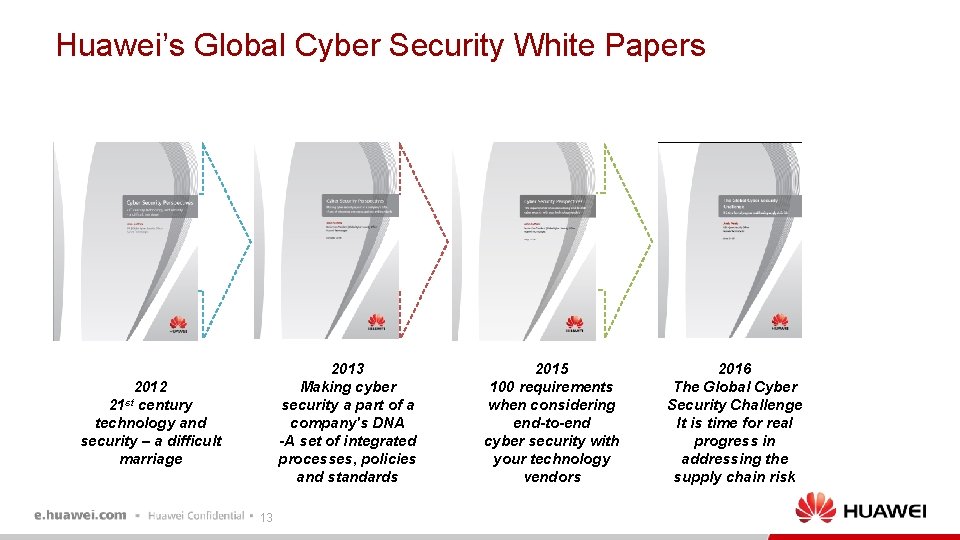
Huawei’s Global Cyber Security White Papers ves 2013 Making cyber security a part of a company's DNA -A set of integrated processes, policies and standards 2012 century technology and security – a difficult marriage 21 st 13 2015 100 requirements when considering end-to-end cyber security with your technology vendors 2016 The Global Cyber Security Challenge It is time for real progress in addressing the supply chain risk

Collaboration for a shared, interconnected future 14 l Huge benefits for society l Threats must be confronted , not ignored l None of us can be successful in isolation l Positive engagement with all stakeholders l Holistic approach l No monopoly on good ideas l Open, transparent, humble l Shared Assurance

Thank you www. huawei. com Copyright© 2016 Huawei Technologies Co. , Ltd. All Rights Reserved. The information in this document may contain predictive statements including, without limitation, statements regarding the future financial and operating results, future product portfolio, new technology, etc. There a number of factors that could cause actual results and developments to differ materially from those expressed or implied in the predictive statements. Therefore, such information is provided for reference purpose only and constitutes neither an offer nor an acceptance. Huawei may change the information at any time without notice.
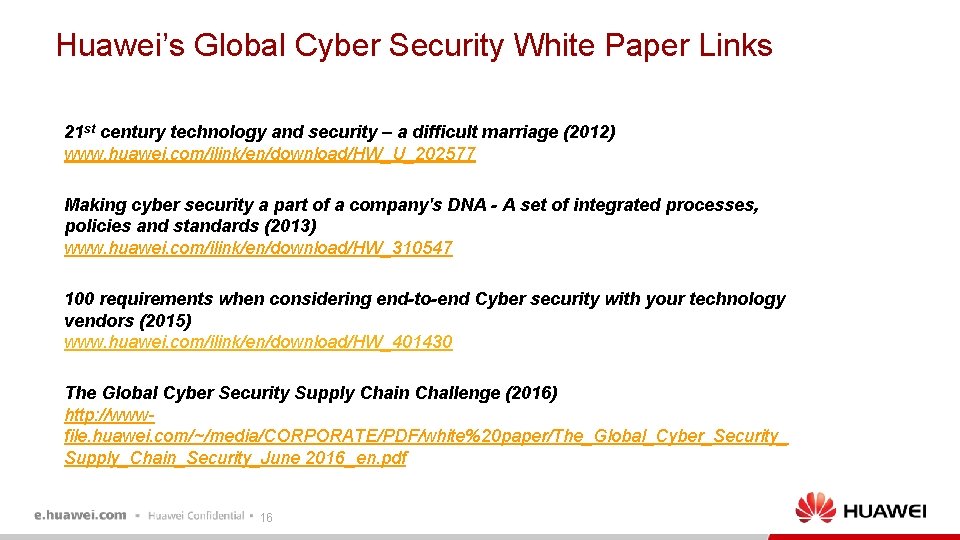
Huawei’s Global Cyber Security White Paper Links 21 st century technology and security – a difficult marriage (2012) www. huawei. com/ilink/en/download/HW_U_202577 Making cyber security a part of a company's DNA - A set of integrated processes, policies and standards (2013) www. huawei. com/ilink/en/download/HW_310547 100 requirements when considering end-to-end Cyber security with your technology vendors (2015) www. huawei. com/ilink/en/download/HW_401430 The Global Cyber Security Supply Chain Challenge (2016) http: //wwwfile. huawei. com/~/media/CORPORATE/PDF/white%20 paper/The_Global_Cyber_Security_ Supply_Chain_Security_June 2016_en. pdf 16
- Slides: 16