Tech UK Cyber Security Group Transatlantic Cyber Security

Tech UK Cyber Security Group Transatlantic Cyber Security Business Opportunities Seminar 6 June 2016 Mark Howard Mark Bailey Partners Charles Russell Speechlys LLP The rapidly evolving European Regulatory environment what UK and US cyber security vendors need to know charlesrussellspeechlys. com

Doing business in the UK • The 2 most common vehicles/methods are: • Incorporate a UK subsidiary company • Create a UK branch/representative office of an existing overseas company • Common alternative approaches are to enter a JV or to create a UK sales channel through e. g. , a reseller/VAR • Are other vehicles (e. g. , Limited Liability Partnership, General partnership, European company) but these are unlikely to be the best fit 2
Doing business in the UK (cont. ) • Main advantages of a subsidiary are: • legal ring fence between overseas company and UK debts and obligations • Local businesses and lenders are familiar with the business format • Main perceived advantage of a branch is administrative ease. However, the overseas company must file annual accounts that comply with UK requirements for the entire overseas company and not just the UK establishment • Get bespoke tax advice and beware “Diverted Profits Tax” introduced in 2015 3
Doing business in the UK (cont. ) • Generally no licensing requirements to trade in the UK • Generally no statutory restrictions on foreign shareholders • No nationality or residence requirement for directors • Data Protection registration • New General Data Protection Regulation from early 2018 • Will be one DP authority based on where businesses have their “main establishment” • Public filing of annual financial accounts • Note new transparency regime for “persons with significant control” which came into force on 6 April 2016 4
Doing business in the UK (cont. ) • No “employment at will” in the UK, minimum statutory notice periods • Unfair dismissal protection after two years’ service • Workplace pension obligations with prescribed minimum contribution. 1% of qualifying earnings, but set to rise to 3% from 1 October 2018 • National Minimum Wage and new National Living Wage for employees aged over 25 • Working time and holidays are regulated, plus specific “family-friendly” employments rights e. g. paternity and maternity leave 5
Cyber – Current Landscape • Cyber is a Board level responsibility • Cyber Essentials / Cyber Essentials Plus. • CE needed for public sector contracting but practice what you preach? • Certifications: • ISO 27001 • Information Security Forum Standard of Good Practice for Information Security (ISF Standard) • Information Assurance for Small and Medium Enterprises (IASME) 6

Digital Single Market charlesrussellspeechlys. com

"I believe that we must make much better use of the great opportunities offered by digital technologies, which know no borders. To do so, we will need to have the courage to break down national silos in telecoms regulation, in copyright and data protection legislation, in the management of radio waves and in the application of competition law. ” Jean-Claude Juncker (President of the European Commission) 8
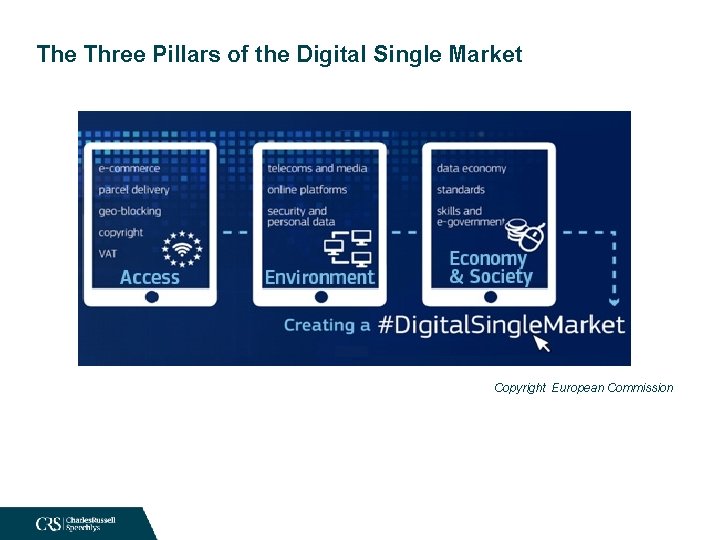
The Three Pillars of the Digital Single Market Copyright European Commission

The Three Pillars of the Digital Single Market The Digital Single Market Strategy is built on three pillars: • Access: better access for consumers and businesses to digital goods and services across Europe, helping to make the EU’s digital world a seamless and level marketplace to buy and sell; • Environment: creating the right conditions and a level playing field for digital networks and innovative services to flourish designing rules which match the pace of technology and support infrastructure development; • Economy & Society: maximising the growth potential of the digital economy, ensuring that Europe’s economy, industry and employment take full advantage of what digitalisation offers. Copyright European Commission
Diagram - Roadmap of initiatives Copyright European Commission

Trade Secrets Directive charlesrussellspeechlys. com
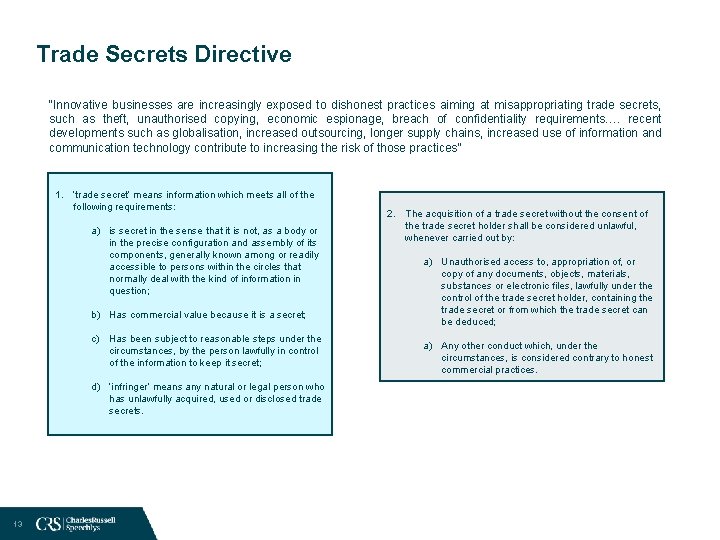
Trade Secrets Directive “Innovative businesses are increasingly exposed to dishonest practices aiming at misappropriating trade secrets, such as theft, unauthorised copying, economic espionage, breach of confidentiality requirements…. recent developments such as globalisation, increased outsourcing, longer supply chains, increased use of information and communication technology contribute to increasing the risk of those practices” 1. ‘trade secret’ means information which meets all of the following requirements: a) is secret in the sense that it is not, as a body or in the precise configuration and assembly of its components, generally known among or readily accessible to persons within the circles that normally deal with the kind of information in question; b) Has commercial value because it is a secret; c) Has been subject to reasonable steps under the circumstances, by the person lawfully in control of the information to keep it secret; d) ‘infringer’ means any natural or legal person who has unlawfully acquired, used or disclosed trade secrets. 13 2. The acquisition of a trade secret without the consent of the trade secret holder shall be considered unlawful, whenever carried out by: a) Unauthorised access to, appropriation of, or copy of any documents, objects, materials, substances or electronic files, lawfully under the control of the trade secret holder, containing the trade secret or from which the trade secret can be deduced; a) Any other conduct which, under the circumstances, is considered contrary to honest commercial practices.

General Data Protection Regulation charlesrussellspeechlys. com
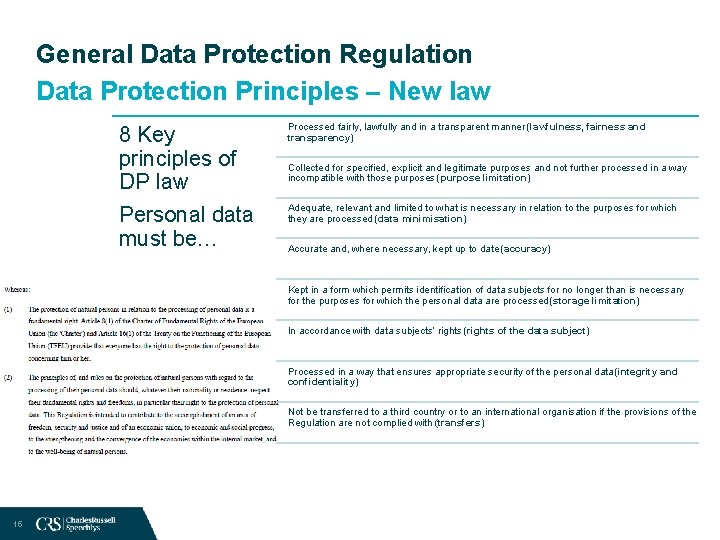
General Data Protection Regulation Data Protection Principles – New law 8 Key principles of DP law Personal data must be… Processed fairly, lawfully and in a transparent manner (lawfulness, fairness and transparency) Collected for specified, explicit and legitimate purposes and not further processed in a way incompatible with those purposes (purpose limitation) Adequate, relevant and limited to what is necessary in relation to the purposes for which they are processed (data minimisation) Accurate and, where necessary, kept up to date (accuracy) Kept in a form which permits identification of data subjects for no longer than is necessary for the purposes for which the personal data are processed (storage limitation) In accordance with data subjects’ rights (rights of the data subject) Processed in a way that ensures appropriate security of the personal data (integrity and confidentiality) Not be transferred to a third country or to an international organisation if the provisions of the Regulation are not complied with (transfers) 15
General Data Protection Regulation Article 24 – Responsibility of controller 16
General Data Protection Regulation Data protection by design and by default 17
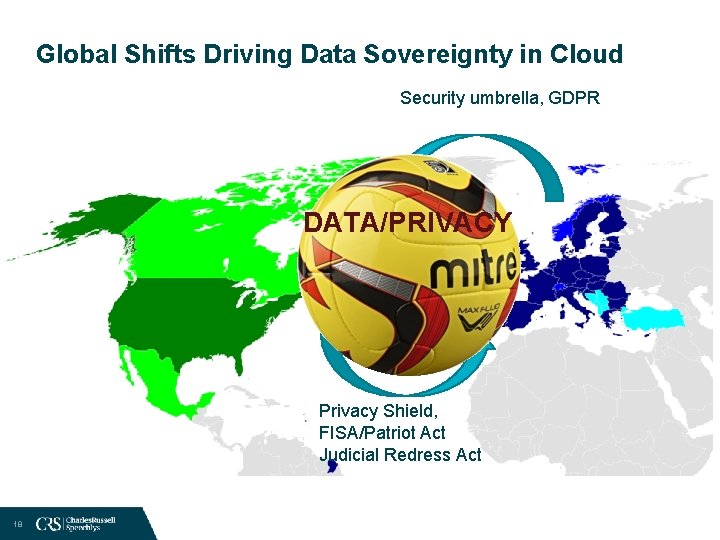
Global Shifts Driving Data Sovereignty in Cloud Security umbrella, GDPR DATA/PRIVACY Privacy Shield, FISA/Patriot Act Judicial Redress Act 18
Investigatory Powers Bill charlesrussellspeechlys. com
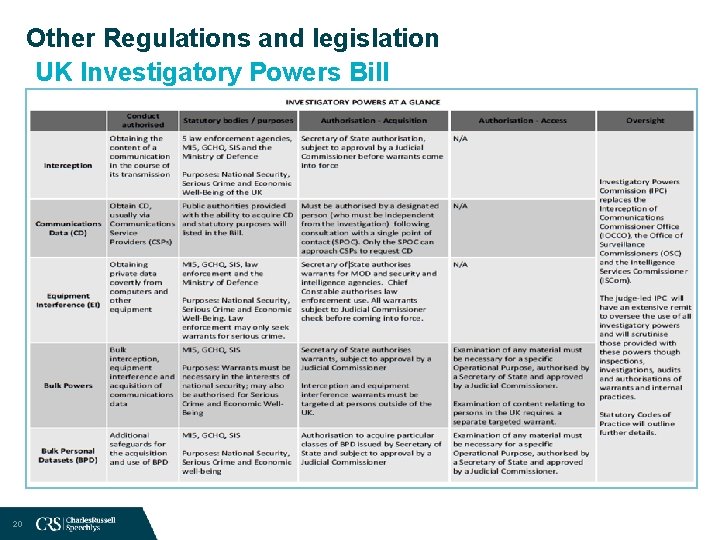
Other Regulations and legislation UK Investigatory Powers Bill 20
Other Regulations and legislation UK Investigatory Powers Bill 21

NIS Directive and other EU initiatives charlesrussellspeechlys. com
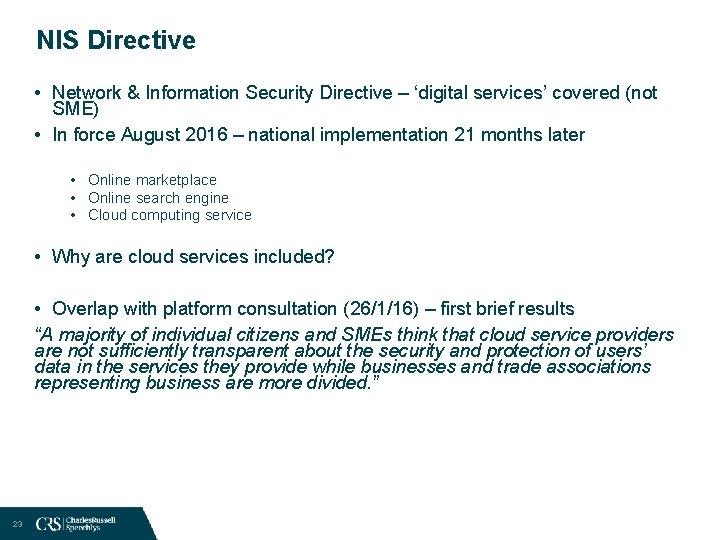
NIS Directive • Network & Information Security Directive – ‘digital services’ covered (not SME) • In force August 2016 – national implementation 21 months later • Online marketplace • Online search engine • Cloud computing service • Why are cloud services included? • Overlap with platform consultation (26/1/16) – first brief results “A majority of individual citizens and SMEs think that cloud service providers are not sufficiently transparent about the security and protection of users’ data in the services they provide while businesses and trade associations representing business are more divided. ” 23
- Slides: 23