Cyber Security Summit Addressing Cyber Security Risk May
Cyber Security Summit: Addressing Cyber Security Risk May 31, 2017 National Rural Electric Cooperative Association (NRECA) & Information Trust Institute (ITI) Dr. Cynthia Hsu Cyber Security Program Manager NRECA
https: //www. cooperative. com/interest-areas/CRN/productsservices/Tech. Surveillance. Magazine/Documents/tsransomwaresept 2016. pdf
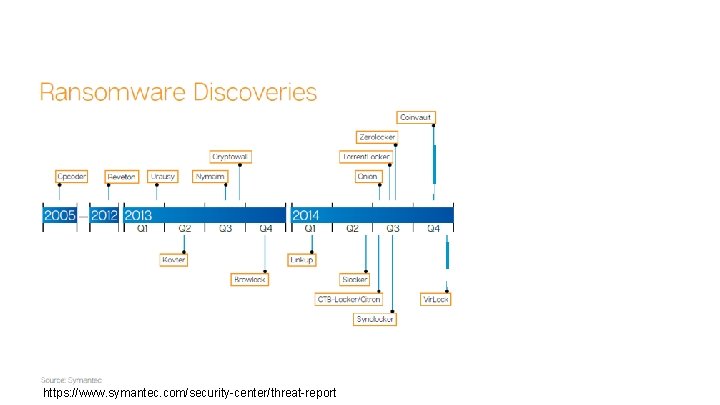
https: //www. symantec. com/security-center/threat-report
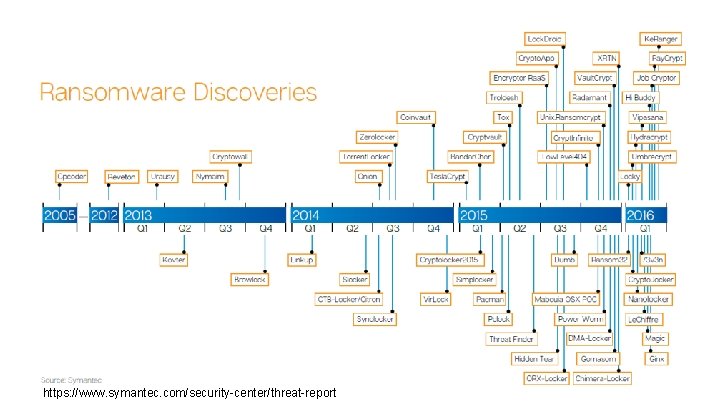
https: //www. symantec. com/security-center/threat-report
$7, 500 The average cost of a ransomware event: • hiring IT specialists to restore files • beefing up security • having experts conduct penetration tests • putting together an incident-response plan Bill West, Vice President of Underwriting Federated Rural Electric Insurance Exchange
97. 25 % • The percentage of phishing emails that contained ransomware in Q 3 2016 (Phish. Me 2016 Q 3 Malware Review) • “Remaining at the forefront is the Locky encryption ransomware, which has introduced a number of techniques to resist detection during the infection process. ” https: //phishme. com/ransomware-delivered-97 -phishing-emails-end-q 3 -2016 -supporting-booming -cybercrime-industry//
MOBILE DEVICES … More than 70% of IT leaders admit they are at risk from an inability to control employees’ apps and devices. Citrix/Ponemon Institute survey January 2017
INSECURE SOFTWARE DEVELOPMENT 1) Poor software design 2) Reliance on open source software as a base, vulnerabilities multiply into hundreds or thousands of software products built on that base and persist over time 3) Commercial Off The Shelf (COTS) products that rely on foreign and non-vetted domestic suppliers
INSECURE SOFTWARE DEVELOPMENT 1) Poor software design 2) Reliance on open source software as a base, vulnerabilities multiply into hundreds or thousands of software products built on that base and persist over time 3) Commercial Off The Shelf (COTS) products that rely on foreign and non-vetted domestic suppliers
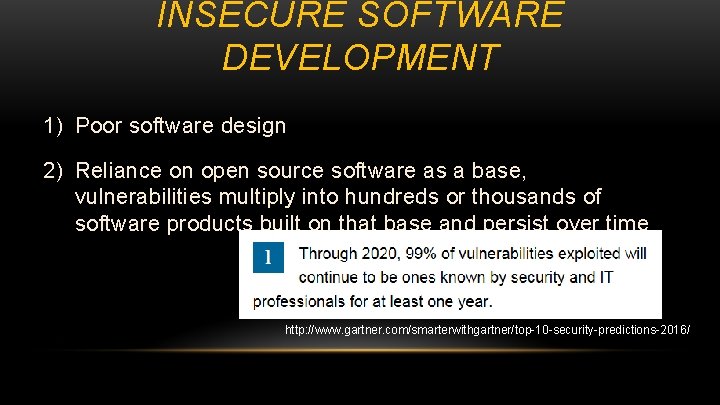
INSECURE SOFTWARE DEVELOPMENT 1) Poor software design 2) Reliance on open source software as a base, vulnerabilities multiply into hundreds or thousands of software products built on that base and persist over time 3) Commercial Off The Shelf (COTS) products that rely on foreign and non-vetted domestic suppliers http: //www. gartner. com/smarterwithgartner/top-10 -security-predictions-2016/
WANNACRY Infected over tens of thousands of businesses, hospitals and agencies across 153 countries
INSECURE SOFTWARE DEVELOPMENT 1) Poor software design 2) Reliance on open source software as a base, vulnerabilities multiply into hundreds or thousands of software products built on that base and persist over time 3) Commercial Off The Shelf (COTS) products that rely on foreign and non-vetted domestic suppliers
AQUIR E https: //www. us-cert. gov/bsi/articles/bestpractices/acquisition/a-systemic-approach-assessing-
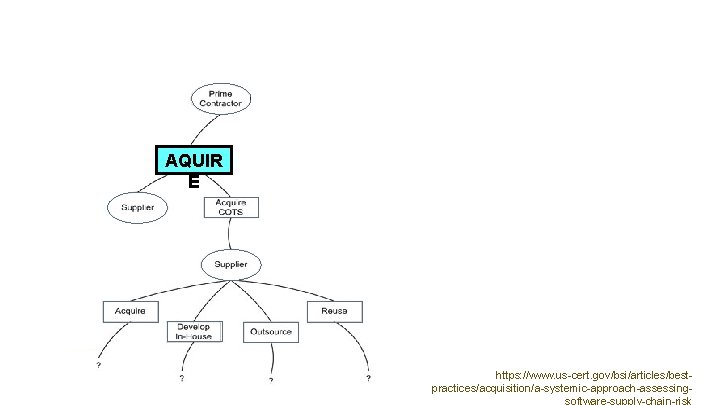
AQUIR E https: //www. us-cert. gov/bsi/articles/bestpractices/acquisition/a-systemic-approach-assessing-
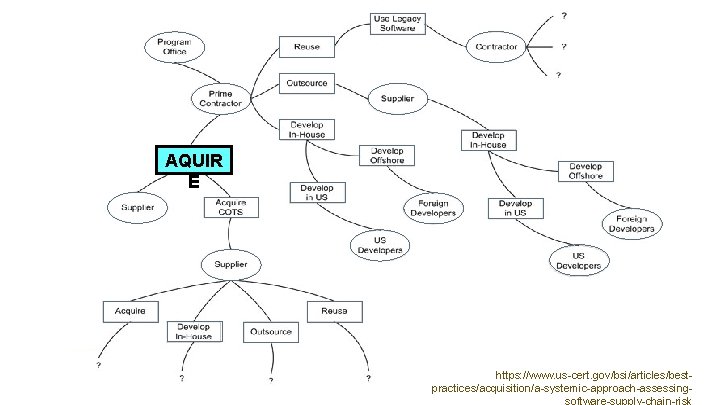
AQUIR E https: //www. us-cert. gov/bsi/articles/bestpractices/acquisition/a-systemic-approach-assessing-

SUPPLY CHAIN THREATS …. counterfeiting piracy subversion social engineering pseudo-insider threat Goertzel, Karen M. , et al. State of the Art Report on Supply Chain Risk Management for the Off-the-Shelf (OTS) Information and Communications Technology (ICT) Supply Chain, U. S. Department of Defense, Information Assurance Technology Analysis Center (IATAC), (2010), p. 40. https: //www. csiac. org/content/state-art-report-soar-security-risk-management-shelf-ots-information-and-communications-tech

SUPPLY CHAIN THREATS …. counterfeiting piracy destruction disruption tampering subversion social engineering pseudo-insider threat exfiltration insider threat theft Goertzel, Karen M. , et al. State of the Art Report on Supply Chain Risk Management for the Off-the-Shelf (OTS) Information and Communications Technology (ICT) Supply Chain, U. S. Department of Defense, Information Assurance Technology Analysis Center (IATAC), (2010), p. 40. https: //www. csiac. org/content/state-art-report-soar-security-risk-management-shelf-ots-information-and-communications-tech

SUPPLY CHAIN THREATS …. counterfeiting piracy destruction disruption tampering infiltration subversion social engineering pseudo-insider threat exfiltration insider threat theft sabotage diversion Goertzel, Karen M. , et al. State of the Art Report on Supply Chain Risk Management for the Off-the-Shelf (OTS) Information and Communications Technology (ICT) Supply Chain, U. S. Department of Defense, Information Assurance Technology Analysis Center (IATAC), (2010), p. 40. https: //www. csiac. org/content/state-art-report-soar-security-risk-management-shelf-ots-information-and-communications-tech

SUPPLY CHAIN THREATS …. subversion social engineering pseudo-insider threat counterfeiting piracy destruction disruption tampering corruption infiltration exfiltration insider threat theft sabotage diversion export control violationsforeign ownership Goertzel, Karen M. , et al. State of the Art Report on Supply Chain Risk Management for the Off-the-Shelf (OTS) Information and Communications Technology (ICT) Supply Chain, U. S. Department of Defense, Information Assurance Technology Analysis Center (IATAC), (2010), p. 40. https: //www. csiac. org/content/state-art-report-soar-security-risk-management-shelf-ots-information-and-communications-tech


MANAGING THIRD PARTY RISKS • Subcontractors and members of the vendor ecosystem • Software code • Supply chain • People http: //www. ciodive. com/news/why-third-party-risk-is-worth-the-reward/436918/
IMPROVING THE CYBER AND PHYSICAL SECURITY POSTURE OF THE ELECTRIC SECTOR
Rural Cooperative Cyber Security Capabilities Program July 1, 2016 – June 30, 2017
GUIDING PRINCIPLES: 1. Funding is limited – solutions must be sustainable beyond the 3 years 2. Voluntary participation 3. Ongoing member engagement in program development and implementation
Rural Cooperative Cyber Security Capabilities Program (RC 3) SELF ASSESSMENT
SELF ASSESSMENT ACTION PLAN
SELF ASSESSMENT ACTION PLAN IMPLEMENTATION

Training IMPLEMENTATION Increasing Access to Existing Cyber Security Courses:

Creating New Curricula: 1. Purchasing a. Hardware & Software b. Security Assessment Services Training IMPLEMENTATION 2. 3. 4. 5. 6. Communicators Administration Staff Legal CEOs/GMs Engineers/Operators

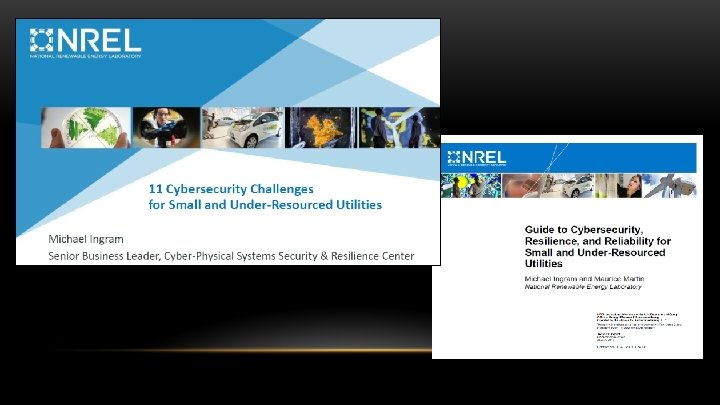
Cyber Security Summits: Opportunities for Peer-to-Peer Learning Training 1. January 2017 – National Renewable Energy Laboratory (NREL), Golden, CO IMPLEMENTATION 2. April 2017 – Cybersecurity Center for Secure Evolvable Energy Delivery Systems (SEEDS), University of Arkansas 3. May 2017 – Information Trust Institute (ITI), University of Illinois 4. June 2017 – 5. July 2017 – Electric Power Research Institute (EPRI), Knoxville, TN Pacific Northwest National Laboratory, Richland, WA
Cyber Security Competition Training Engineering & Operations + IMPLEMENTATION Information Technology = Solution
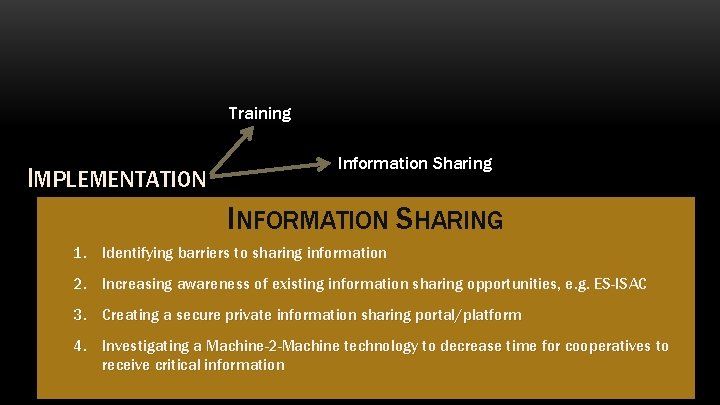
Training IMPLEMENTATION Information Sharing INFORMATION SHARING 1. Identifying barriers to sharing information 2. Increasing awareness of existing information sharing opportunities, e. g. ES-ISAC 3. Creating a secure private information sharing portal/platform 4. Investigating a Machine-2 -Machine technology to decrease time for cooperatives to receive critical information
Training IMPLEMENTATION Information Sharing Hire
Training IMPLEMENTATION Information Sharing Hire Buy
Training Information Sharing IMPLEMENTATION Hire Buy Build
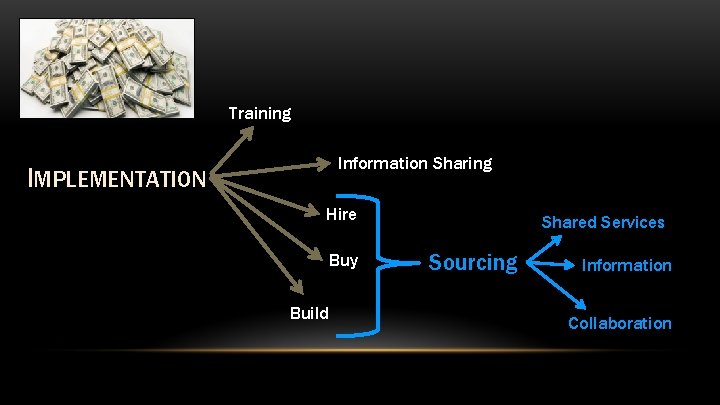
Training Information Sharing IMPLEMENTATION Hire Buy Build Shared Services Sourcing Information Collaboration
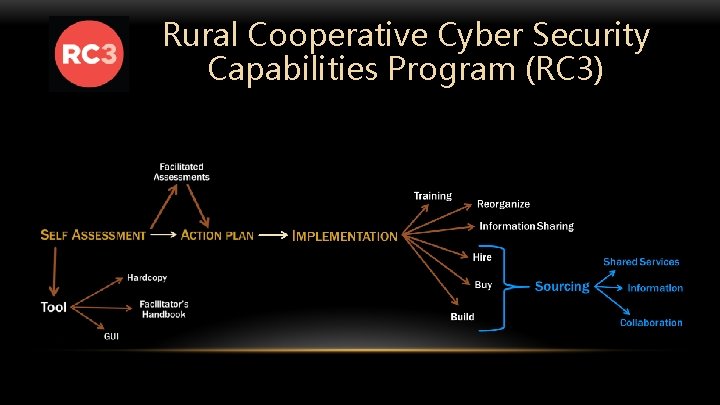
Rural Cooperative Cyber Security Capabilities Program (RC 3)

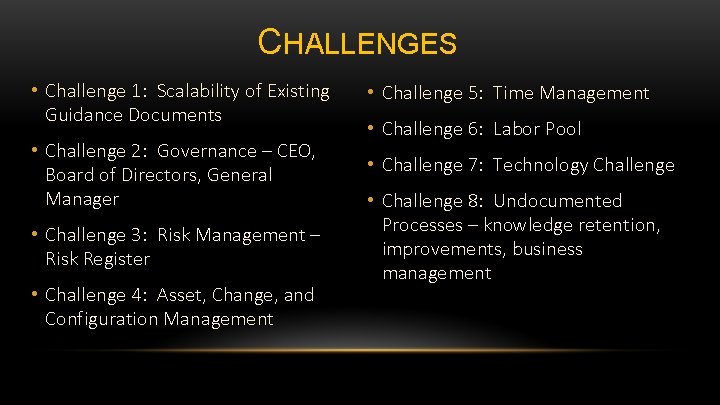
CHALLENGES • Challenge 1: Scalability of Existing Guidance Documents • Challenge 5: Time Management • Challenge 2: Governance – CEO, Board of Directors, General Manager • Challenge 7: Technology Challenge • Challenge 3: Risk Management – Risk Register • Challenge 4: Asset, Change, and Configuration Management • Challenge 6: Labor Pool • Challenge 8: Undocumented Processes – knowledge retention, improvements, business management
CHALLENGE 1: SCALABILITY OF EXISTING GUIDANCE DOCUMENTS
CHALLENGE 1: SCALABILITY OF EXISTING GUIDANCE DOCUMENTS 1. Few existing documents or for larger organizations 2. Written in legalese or theoretical – limited staff (time and budget constraints) to spend on understanding complex documents 3. Need actionable information
CHALLENGE 2: GOVERNANCE – CEO, BOARD OF DIRECTORS, GENERAL MANAGER
CHALLENGE 2: GOVERNANCE – CEO, BOARD OF DIRECTORS, GENERAL MANAGER 1. Materials/messaging for CEO and Board audiences to convey importance, risks, and exposure 2. Importance of CEO and Board leadership on this topic 3. Boards want guaranteed results for investment, and IT is trying to secure necessary resources and funding for preventative measures

CHALLENGE 3: RISK MANAGEMENT
CHALLENGE 3: RISK MANAGEMENT 1. Need ways to identify, understand, and prioritize cyber security risks – tools for risk assessment, tracking, and monitoring 2. Assistance in how to communicate risks to management and Board to gain understanding and support for resources 3. Best practices training, general education, and actual co-op examples (not theory) 4. Risk register – who decides on risk level that is acceptable?
WANNACRY 2. Review decision authority. “IT employees likely knew about the update but chose not to do so as per the guidance from senior leaders. The question is, what was the criteria those senior leaders [used] for their decisions? Sure, updating tens of thousands of computers comes with a price, but so too does the cost of not. ” The Wanna. Cry Cyber Attack Makes You Want To Cry: How To Turn Chaos Into An Advantage, Forbes, Jeff Boss, May 16, 2017. forbes. com/sites/jeffboss/2017/05/16/the-wannacry-cyberattack-makes-you-want-to-cry-how-to-turn-chaos-into-an-advantage/#870 e 63 e 3 c 116
CHALLENGE 4: ASSET, CHANGE, AND CONFIGURATION MANAGEMENT

CHALLENGE 4: ASSET, CHANGE, AND CONFIGURATION MANAGEMENT 1. Decentralized business systems and disconnected systems that don’t communicate with tracking tools make tracking difficult 2. Guidance on what to track using policies and education 3. Easy-to-use tools/checklists to help track 4. Automated tracking tools

CHALLENGE 5: TIME MANAGEMENT
CHALLENGE 5: TIME MANAGEMENT 1. Who within the organization is responsible for what? Goal cyber security is everyone’s responsibility 2. Time learning new technologies, researching existing technologies, vetting vendors – need tools to give quick information on technologies, vendors, etc. 3. Tools to help simplify requirements 4. New responsibilities add workload to existing staff

CHALLENGE 6: LABOR POOL
CHALLENGE 6: LABOR POOL 1. Difficult to attract and retain good talent into rural areas at an affordable price – need conduit to appropriate talent – job descriptions, connections, qualified talent pools, etc. 2. Coordinate shared services 3. Guidance on how to implement effective knowledge retention practices 4. Vetted list of 3 rd party IT providers

CHALLENGE 7: TECHNOLOGY
CHALLENGE 7: TECHNOLOGY 1. Difficulty in demonstrating the needs of the IT department for technology to CEO and Board 2. Guidance on how to build consensus across departments – challenges in coordinating technology changes by various departments 3. Many solutions and little time to sort and understand them – need assistance in what fits co-ops

CHALLENGE 8: UNDOCUMENTED PROCESSES KNOWLEDGE RETENTION , IMPROVEMENTS, BUSINESS MANAGEMENT
CHALLENGE 8: UNDOCUMENTED PROCESSES KNOWLEDGE RETENTION , IMPROVEMENTS, BUSINESS MANAGEMENT 1. People who know the processes are too busy implementing to document 2. Guidance on what and how to document 3. No technology standard – documenting not useful for everyone 4. Cross-training needed to ensure information sharing, knowledge retention, succession planning
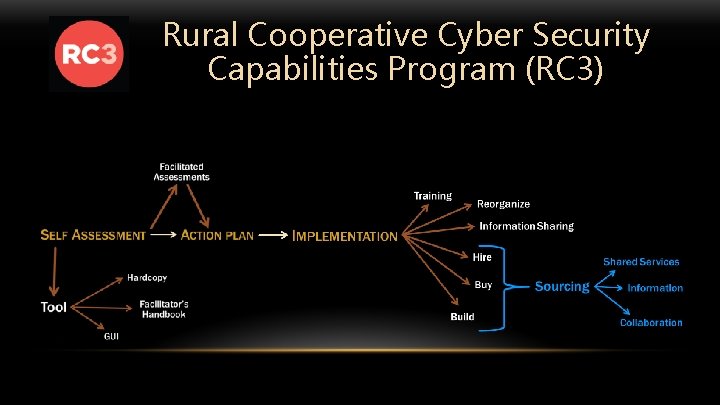
Rural Cooperative Cyber Security Capabilities Program (RC 3)

YOU DESIGN THE RESEARCH • Challenge 1: Scalability of Existing Guidance Documents • Challenge 5: Time Management • Challenge 2: Governance – CEO, Board of Directors, General Manager • Challenge 7: Technology Challenge • Challenge 3: Risk Management – Risk Register • Challenge 4: Asset, Change, and Configuration Management • Challenge 6: Labor Pool • Challenge 8: Undocumented Processes – knowledge retention, improvements, business management
WHAT WILL HAPPEN TO THE INFORMATION COLLECTED TODAY? • Raw data not shared • Aggregated, anonymized summaries will be used to inform: • Other co-ops • Future RC 3 Program directions • DOE

YOU DESIGN THE RESEARCH • Challenge 1: Scalability of Existing Guidance Documents • Challenge 5: Time Management • Challenge 2: Governance – CEO, Board of Directors, General Manager • Challenge 7: Technology Challenge • Challenge 3: Risk Management – Risk Register • Challenge 4: Asset, Change, and Configuration Management • Challenge 6: Labor Pool • Challenge 8: Undocumented Processes – knowledge retention, improvements, business management
- Slides: 64