Cyber Security Professionalism Cyber Security Becomes a Profession
Cyber Security Professionalism Cyber Security Becomes a Profession Navigating U. S. Sectoral Security S. 773 - the Current Impetus
Is “Cyber. Security” a Profession? What About “Risk Analysis? ” l Are these Trick/Gotcha Questions? l l Maybe Why…What is the Dilemma? Long tradition of fields, disciplines, callings actively seek legitimacy of professional status Vs. l Once you’re a Professional, Public Expectations Hold you Feet to the Fire l l What is the Role of S. 773 & S. 778 in Cyber. Security Professionalism?
What is a Profession? l l l Traditionally only 3 professions: l Divinity, Medicine, Law Persons/firms who supply specialized knowledge (subject, field, science) to fee-paying clients l Also the body of qualified professional persons l Derived from Latin professiō - to swear (an oath), avowal, public declaration l Professional (adj) - behaves properly, not amateurish l The oath dictates ethical standards, usually include confidentiality, truthfulness, expertise, all for client’s benefit; also upholding profession’s good name EX: l Architects, Accountants, Actuaries, Chiropractors, Clergy, Dentists, Engineers, Lawyers, Librarians, Nurses, Occupational/ Physical Therapists, Pharmacists, Physicians, Professors/Teachers, Psychiatrists, Veterinarians l (Cyber-)Security “Professionals” too? !?
Milestones towards Profession l l l Full-Time Occupation Training & University Instruction Accreditation of Instruction & Qualifications Associations: local, national, int’l Codes of Conduct (govt & self-) l l ethics, professional responsibility, self-discipline Law/Regulation Compels Professional Status l Licensure, Certification
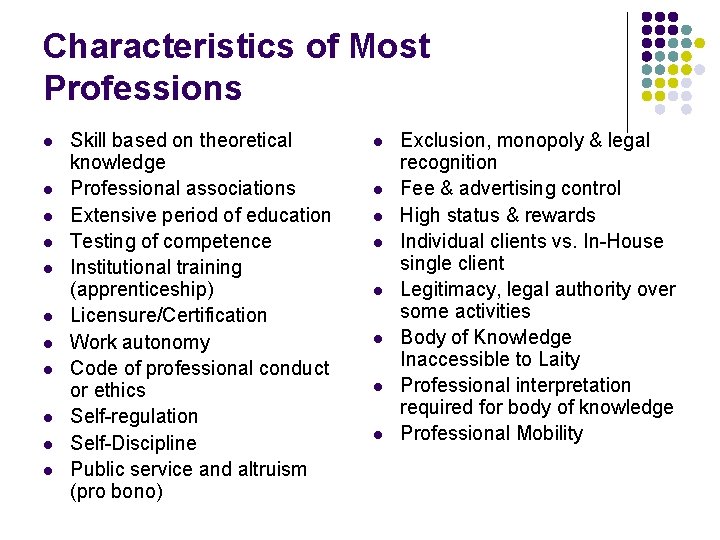
Characteristics of Most Professions l l l Skill based on theoretical knowledge Professional associations Extensive period of education Testing of competence Institutional training (apprenticeship) Licensure/Certification Work autonomy Code of professional conduct or ethics Self-regulation Self-Discipline Public service and altruism (pro bono) l l l l Exclusion, monopoly & legal recognition Fee & advertising control High status & rewards Individual clients vs. In-House single client Legitimacy, legal authority over some activities Body of Knowledge Inaccessible to Laity Professional interpretation required for body of knowledge Professional Mobility
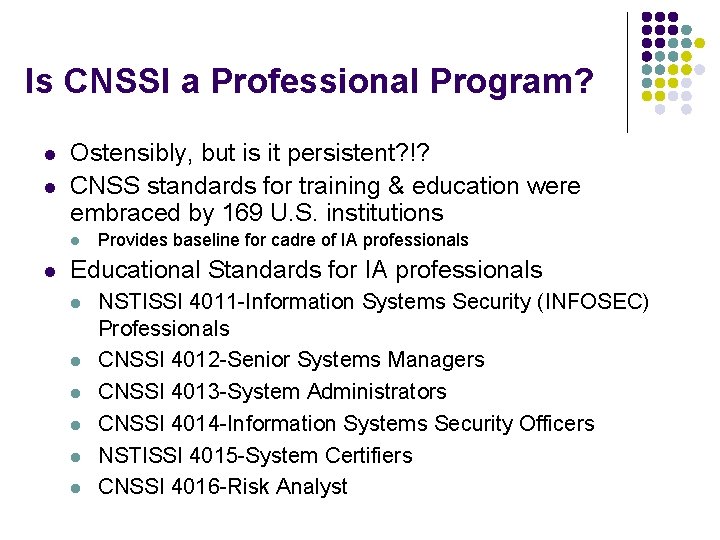
Is CNSSI a Professional Program? l l Ostensibly, but is it persistent? !? CNSS standards for training & education were embraced by 169 U. S. institutions l l Provides baseline for cadre of IA professionals Educational Standards for IA professionals l l l NSTISSI 4011 -Information Systems Security (INFOSEC) Professionals CNSSI 4012 -Senior Systems Managers CNSSI 4013 -System Administrators CNSSI 4014 -Information Systems Security Officers NSTISSI 4015 -System Certifiers CNSSI 4016 -Risk Analyst
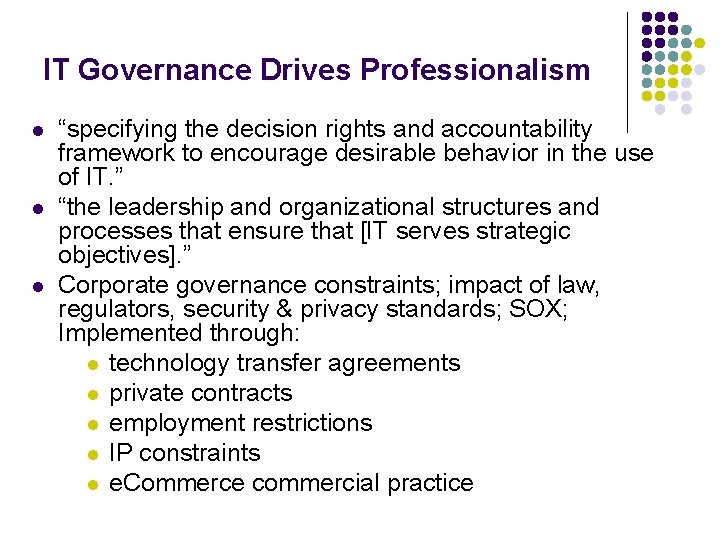
IT Governance Drives Professionalism l l l “specifying the decision rights and accountability framework to encourage desirable behavior in the use of IT. ” “the leadership and organizational structures and processes that ensure that [IT serves strategic objectives]. ” Corporate governance constraints; impact of law, regulators, security & privacy standards; SOX; Implemented through: l technology transfer agreements l private contracts l employment restrictions l IP constraints l e. Commerce commercial practice
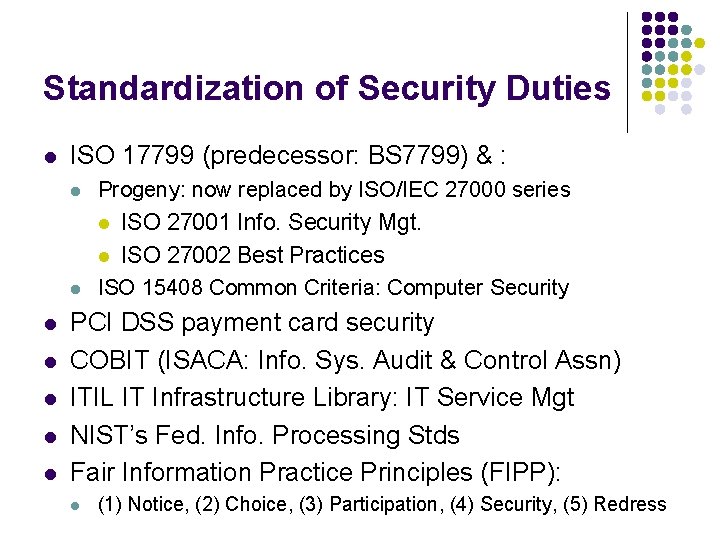
Standardization of Security Duties l ISO 17799 (predecessor: BS 7799) & : l Progeny: now replaced by ISO/IEC 27000 series l ISO 27001 Info. Security Mgt. ISO 27002 Best Practices ISO 15408 Common Criteria: Computer Security l l l l PCI DSS payment card security COBIT (ISACA: Info. Sys. Audit & Control Assn) ITIL IT Infrastructure Library: IT Service Mgt NIST’s Fed. Info. Processing Stds Fair Information Practice Principles (FIPP): l (1) Notice, (2) Choice, (3) Participation, (4) Security, (5) Redress

Why are Standards Important? l l l Stds are emerging from obscurity More widely understood to impact most economic activity Increasingly viewed less as technically objective matters; more as arbitrary choices from among near infinite alternatives Increasingly perceived to favor particular nations, industries, identifiable groups or individual firms who participate most effectively Increasingly have behavioral component
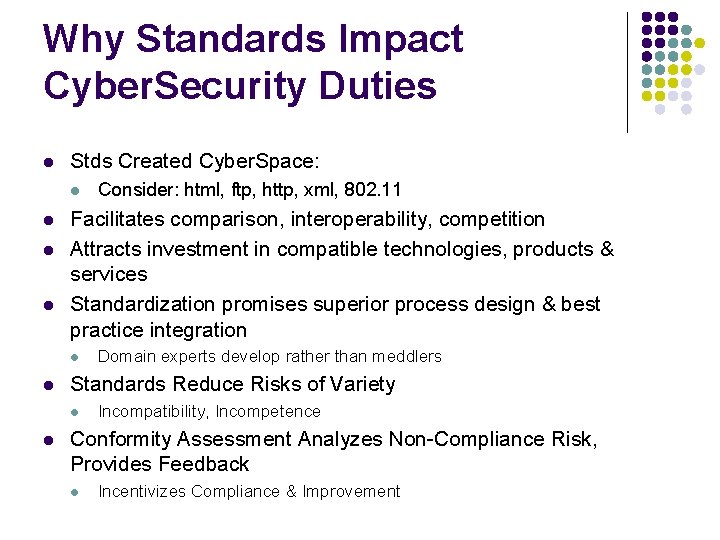
Why Standards Impact Cyber. Security Duties l Stds Created Cyber. Space: l l Facilitates comparison, interoperability, competition Attracts investment in compatible technologies, products & services Standardization promises superior process design & best practice integration l l Domain experts develop rather than meddlers Standards Reduce Risks of Variety l l Consider: html, ftp, http, xml, 802. 11 Incompatibility, Incompetence Conformity Assessment Analyzes Non-Compliance Risk, Provides Feedback l Incentivizes Compliance & Improvement
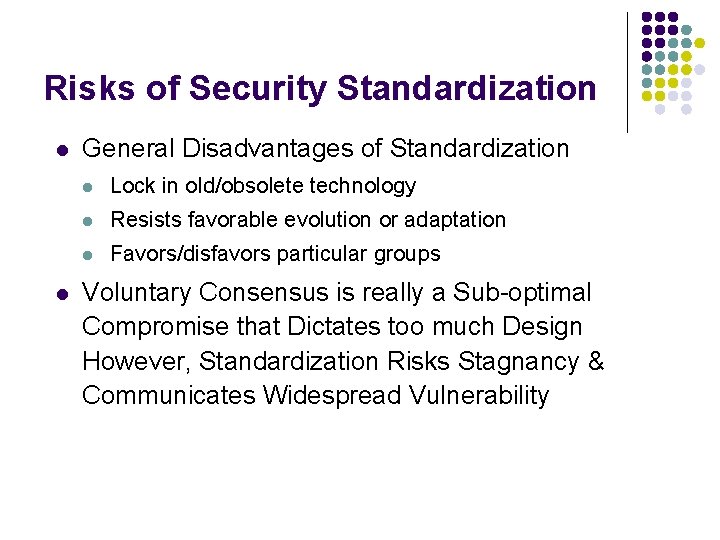
Risks of Security Standardization l l General Disadvantages of Standardization l Lock in old/obsolete technology l Resists favorable evolution or adaptation l Favors/disfavors particular groups Voluntary Consensus is really a Sub-optimal Compromise that Dictates too much Design However, Standardization Risks Stagnancy & Communicates Widespread Vulnerability
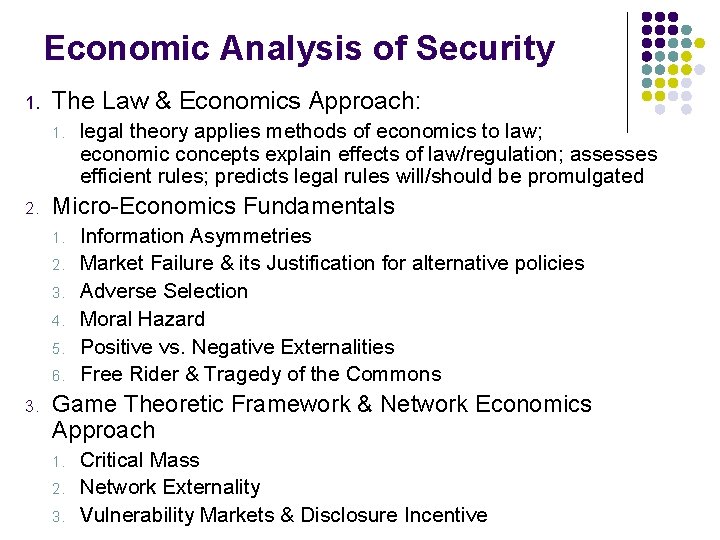
Economic Analysis of Security 1. The Law & Economics Approach: 1. 2. Micro-Economics Fundamentals 1. 2. 3. 4. 5. 6. 3. legal theory applies methods of economics to law; economic concepts explain effects of law/regulation; assesses efficient rules; predicts legal rules will/should be promulgated Information Asymmetries Market Failure & its Justification for alternative policies Adverse Selection Moral Hazard Positive vs. Negative Externalities Free Rider & Tragedy of the Commons Game Theoretic Framework & Network Economics Approach 1. 2. 3. Critical Mass Network Externality Vulnerability Markets & Disclosure Incentive

Some Public Policies Pressing Security Duties l Privacy Law Requires Cyber. Security l G/L/B, Sour. Box (a/k/a SOX), FCPA l l The Primary Federal Privacy Regulator: FTC l l l CA state Privacy Czar Breach Notification, see: Privacyrights. org Mass, Nev. Comprehensive Regulations Tort Liability for Privacy Violations HIPAA now HITECH PHI std IA laws Impact Security Duties l l Outsourcing (SAS 70) Trade Secrecy (IP) & National Security l l Enforcement Caselaw, deceptive trade practices State Privacy & Info Security Laws l l Internal Control USA PATRIOT Act FTC Privacy Enforcement Common Law History l l Red Flags (best/worst practices), Disposal Rule, Exposing then Stamping Out Deception
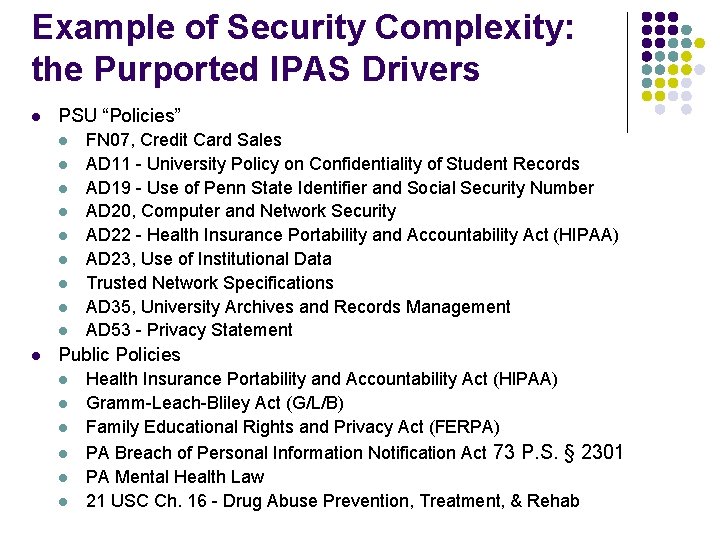
Example of Security Complexity: the Purported IPAS Drivers l PSU “Policies” l l l l l FN 07, Credit Card Sales AD 11 - University Policy on Confidentiality of Student Records AD 19 - Use of Penn State Identifier and Social Security Number AD 20, Computer and Network Security AD 22 - Health Insurance Portability and Accountability Act (HIPAA) AD 23, Use of Institutional Data Trusted Network Specifications AD 35, University Archives and Records Management AD 53 - Privacy Statement Public Policies l l l Health Insurance Portability and Accountability Act (HIPAA) Gramm-Leach-Bliley Act (G/L/B) Family Educational Rights and Privacy Act (FERPA) PA Breach of Personal Information Notification Act 73 P. S. § 2301 PA Mental Health Law 21 USC Ch. 16 - Drug Abuse Prevention, Treatment, & Rehab
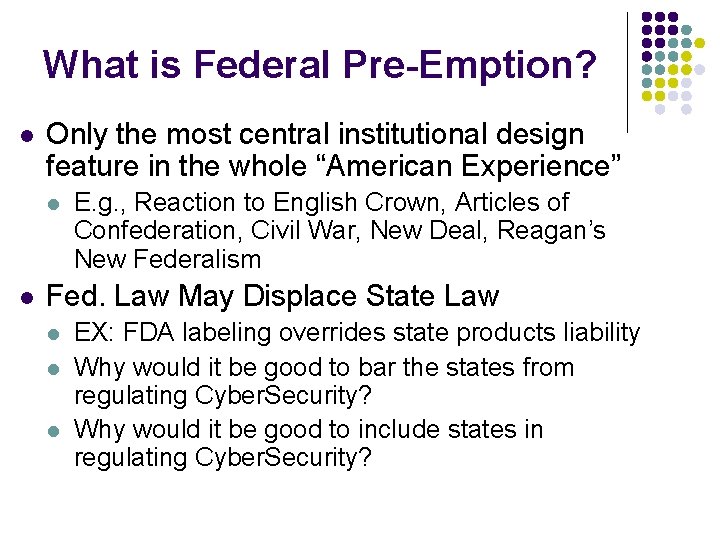
What is Federal Pre-Emption? l Only the most central institutional design feature in the whole “American Experience” l l E. g. , Reaction to English Crown, Articles of Confederation, Civil War, New Deal, Reagan’s New Federalism Fed. Law May Displace State Law l l l EX: FDA labeling overrides state products liability Why would it be good to bar the states from regulating Cyber. Security? Why would it be good to include states in regulating Cyber. Security?
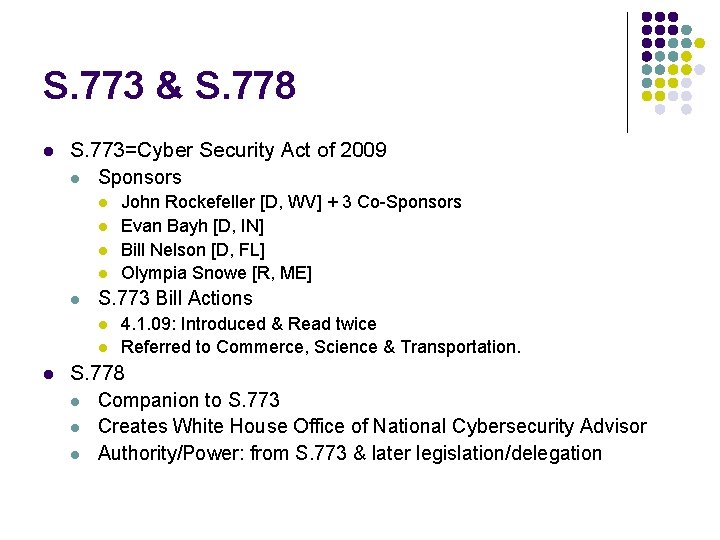
S. 773 & S. 778 l S. 773=Cyber Security Act of 2009 l Sponsors l l l S. 773 Bill Actions l l l John Rockefeller [D, WV] + 3 Co-Sponsors Evan Bayh [D, IN] Bill Nelson [D, FL] Olympia Snowe [R, ME] 4. 1. 09: Introduced & Read twice Referred to Commerce, Science & Transportation. S. 778 l Companion to S. 773 l Creates White House Office of National Cybersecurity Advisor l Authority/Power: from S. 773 & later legislation/delegation

Some S. 773 & S. 778 Provisions l l l l l Raise Cyber. Security profile within Fed. Govt. Streamline cyber-related govt functions & authorities Establish: Office of the National Cyber. Security Advisor Develop Cyber. Security national strategy Quadrennial Cybersecurity Review l modeled after the Do. D Quadrennial Defense Review l to examine cyber strategy, budget, plans & policies Require a threat & vulnerability assessment Promote public awareness Protect civil liberties Require comprehensive legal review
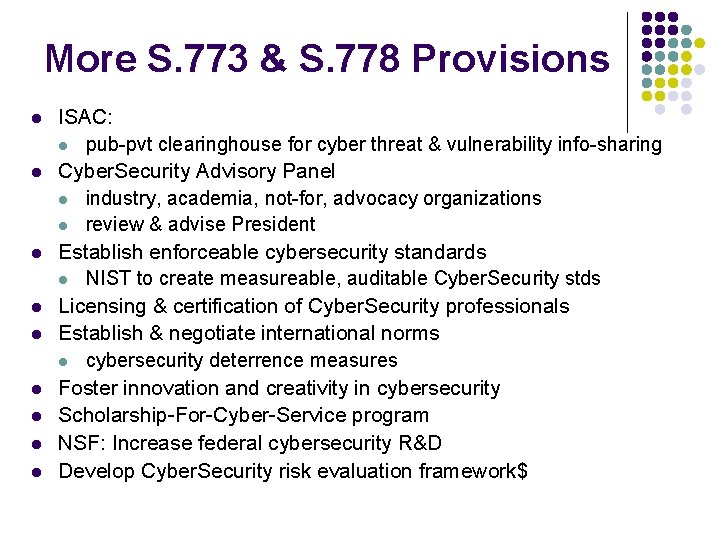
More S. 773 & S. 778 Provisions l l l l l ISAC: l pub-pvt clearinghouse for cyber threat & vulnerability info-sharing Cyber. Security Advisory Panel l industry, academia, not-for, advocacy organizations l review & advise President Establish enforceable cybersecurity standards l NIST to create measureable, auditable Cyber. Security stds Licensing & certification of Cyber. Security professionals Establish & negotiate international norms l cybersecurity deterrence measures Foster innovation and creativity in cybersecurity Scholarship-For-Cyber-Service program NSF: Increase federal cybersecurity R&D Develop Cyber. Security risk evaluation framework$
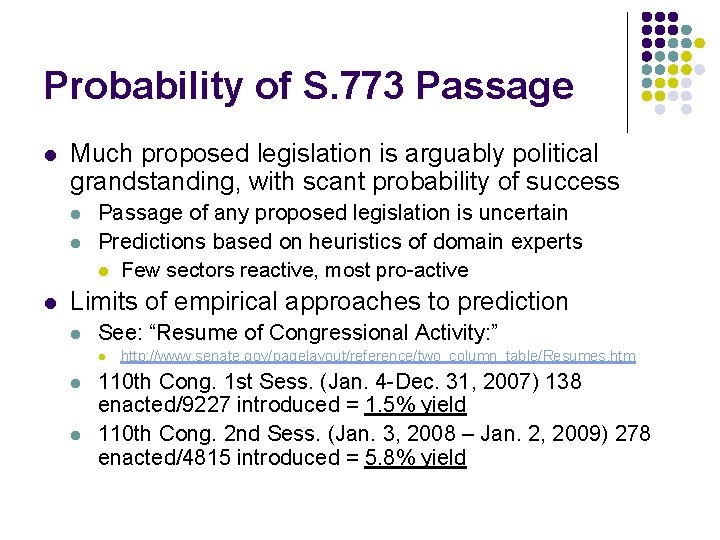
Probability of S. 773 Passage l Much proposed legislation is arguably political grandstanding, with scant probability of success l l l Passage of any proposed legislation is uncertain Predictions based on heuristics of domain experts l Few sectors reactive, most pro-active Limits of empirical approaches to prediction l See: “Resume of Congressional Activity: ” l l l http: //www. senate. gov/pagelayout/reference/two_column_table/Resumes. htm 110 th Cong. 1 st Sess. (Jan. 4 -Dec. 31, 2007) 138 enacted/9227 introduced = 1. 5% yield 110 th Cong. 2 nd Sess. (Jan. 3, 2008 – Jan. 2, 2009) 278 enacted/4815 introduced = 5. 8% yield
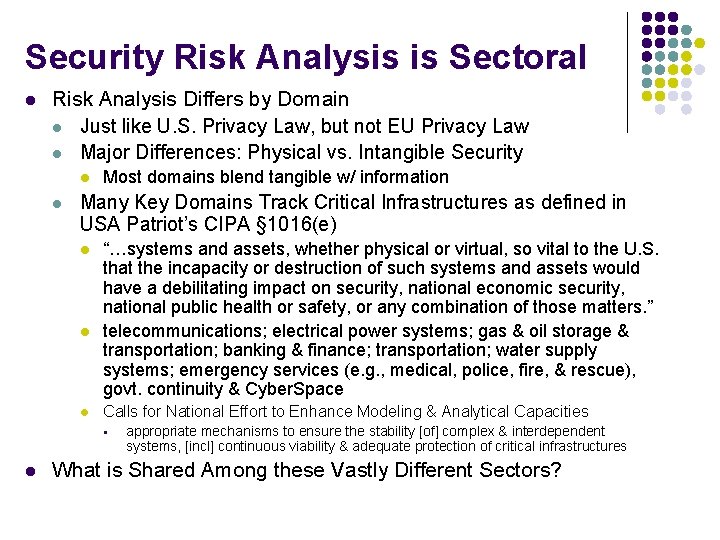
Security Risk Analysis is Sectoral l Risk Analysis Differs by Domain l Just like U. S. Privacy Law, but not EU Privacy Law l Major Differences: Physical vs. Intangible Security l l Most domains blend tangible w/ information Many Key Domains Track Critical Infrastructures as defined in USA Patriot’s CIPA § 1016(e) l l l “…systems and assets, whether physical or virtual, so vital to the U. S. that the incapacity or destruction of such systems and assets would have a debilitating impact on security, national economic security, national public health or safety, or any combination of those matters. ” telecommunications; electrical power systems; gas & oil storage & transportation; banking & finance; transportation; water supply systems; emergency services (e. g. , medical, police, fire, & rescue), govt. continuity & Cyber. Space Calls for National Effort to Enhance Modeling & Analytical Capacities § l appropriate mechanisms to ensure the stability [of] complex & interdependent systems, [incl] continuous viability & adequate protection of critical infrastructures What is Shared Among these Vastly Different Sectors?
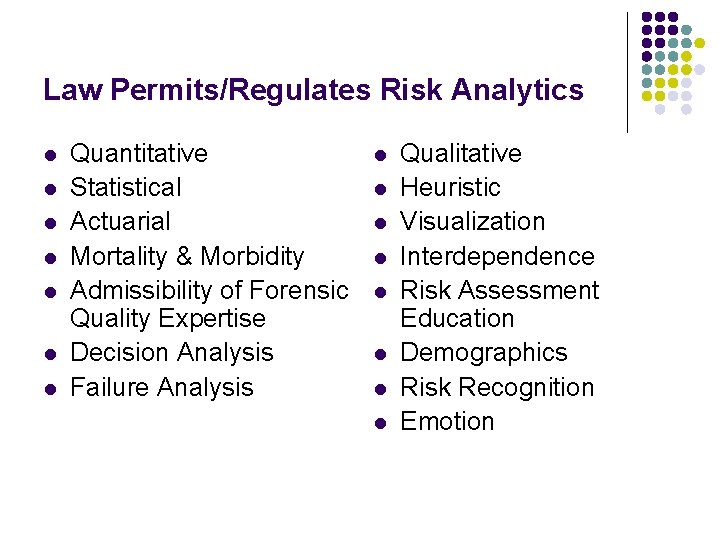
Law Permits/Regulates Risk Analytics l l l l Quantitative Statistical Actuarial Mortality & Morbidity Admissibility of Forensic Quality Expertise Decision Analysis Failure Analysis l l l l Qualitative Heuristic Visualization Interdependence Risk Assessment Education Demographics Risk Recognition Emotion
Epilogue l l There is far more here than meets the eye! A website devoted to the developing public policy of cyber security professionalism l l http: //faculty. ist. psu. edu/bagby/Security. Profession alism/ This IS interdisciplinary! l Good luck w/o interdisciplinarity…
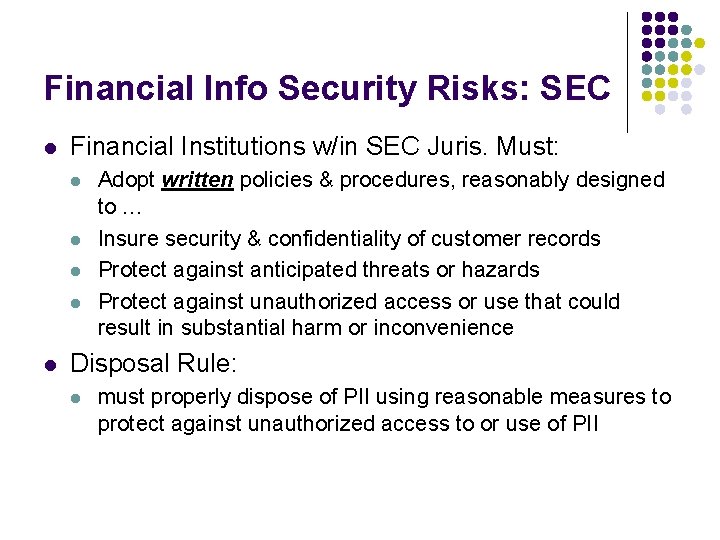
Financial Info Security Risks: SEC l Financial Institutions w/in SEC Juris. Must: l l l Adopt written policies & procedures, reasonably designed to … Insure security & confidentiality of customer records Protect against anticipated threats or hazards Protect against unauthorized access or use that could result in substantial harm or inconvenience Disposal Rule: l must properly dispose of PII using reasonable measures to protect against unauthorized access to or use of PII
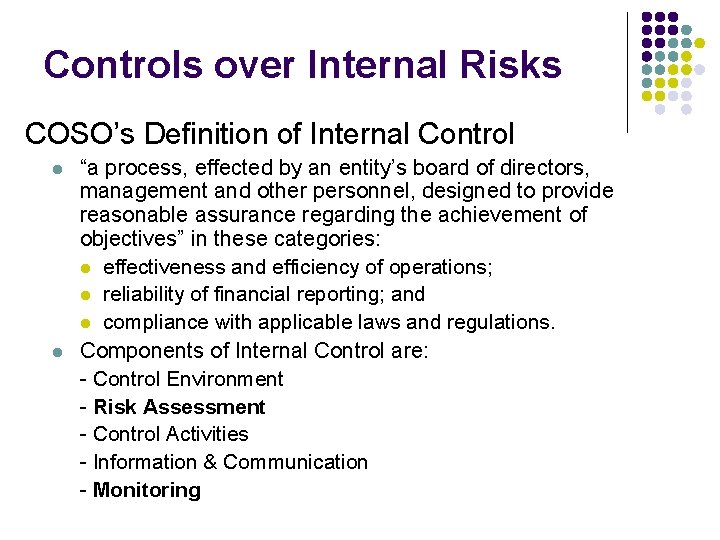
Controls over Internal Risks COSO’s Definition of Internal Control l l “a process, effected by an entity’s board of directors, management and other personnel, designed to provide reasonable assurance regarding the achievement of objectives” in these categories: l effectiveness and efficiency of operations; l reliability of financial reporting; and l compliance with applicable laws and regulations. Components of Internal Control are: - Control Environment - Risk Assessment - Control Activities - Information & Communication - Monitoring
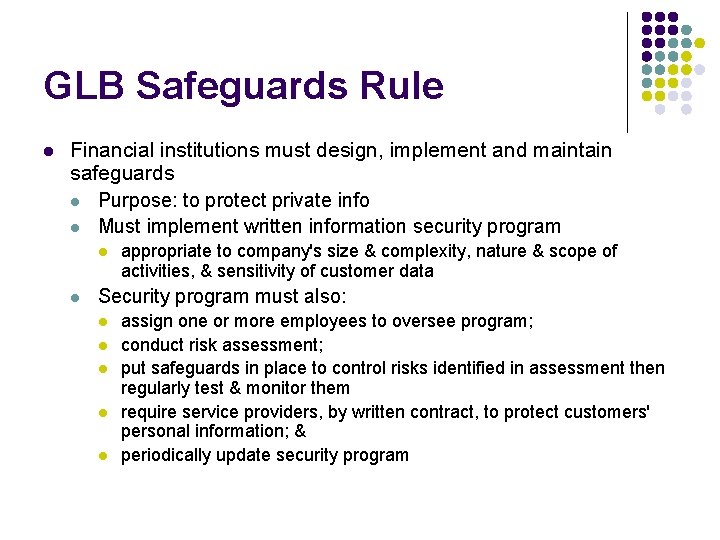
GLB Safeguards Rule l Financial institutions must design, implement and maintain safeguards l Purpose: to protect private info l Must implement written information security program l l appropriate to company's size & complexity, nature & scope of activities, & sensitivity of customer data Security program must also: l l l assign one or more employees to oversee program; conduct risk assessment; put safeguards in place to control risks identified in assessment then regularly test & monitor them require service providers, by written contract, to protect customers' personal information; & periodically update security program
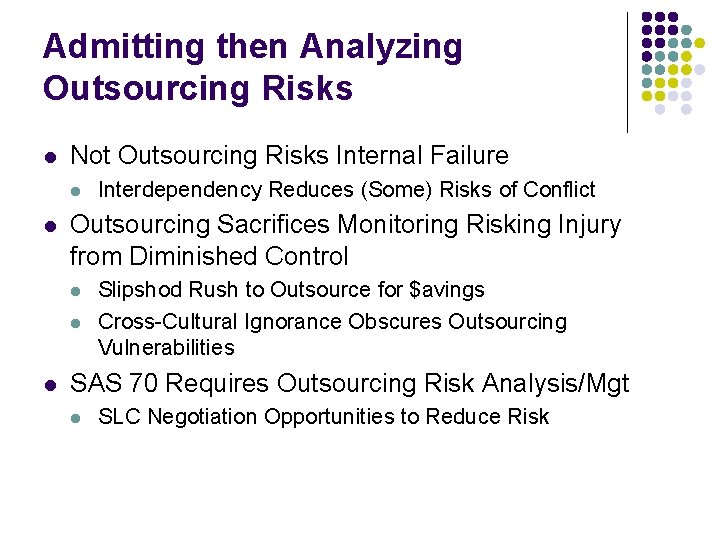
Admitting then Analyzing Outsourcing Risks l Not Outsourcing Risks Internal Failure l l Outsourcing Sacrifices Monitoring Risking Injury from Diminished Control l Interdependency Reduces (Some) Risks of Conflict Slipshod Rush to Outsource for $avings Cross-Cultural Ignorance Obscures Outsourcing Vulnerabilities SAS 70 Requires Outsourcing Risk Analysis/Mgt l SLC Negotiation Opportunities to Reduce Risk
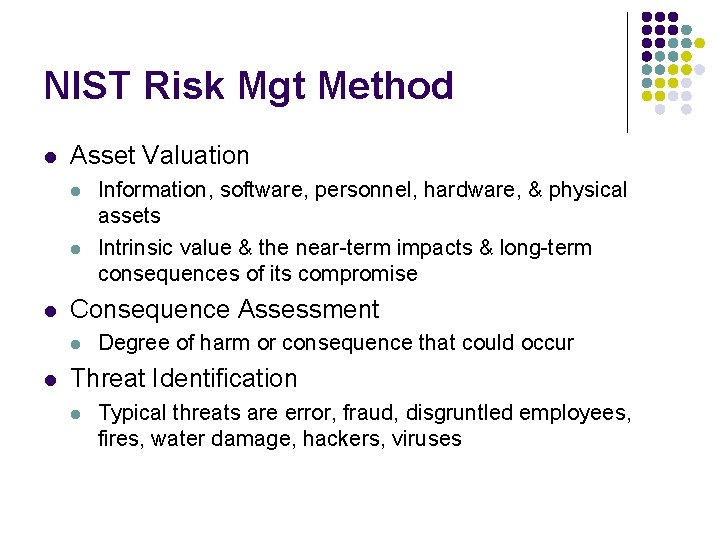
NIST Risk Mgt Method l Asset Valuation l l l Consequence Assessment l l Information, software, personnel, hardware, & physical assets Intrinsic value & the near-term impacts & long-term consequences of its compromise Degree of harm or consequence that could occur Threat Identification l Typical threats are error, fraud, disgruntled employees, fires, water damage, hackers, viruses
NIST Risk Mgt Method l l Vulnerability Analysis Safeguard Analysis l l l Any action that reduces an entity’s vulnerability to a threat Includes the examination of existing security measures & the identification of new safeguards Risk Management Requires Risk Analysis l Analyzed in terms of missing safeguards“The Process of Identifying, Controlling and Minimizing the Impact of Uncertain Events” (NIST, 1995 @59) Source: NIST Handbook
Roles of Law/Reg/Policy in Risk Analysis & Risk Management l Law Resolves Disputes, Shifts Risk of Loss l l l Law Defines Risks & Duties of Care l l l l Law Compensates Injuries Derived from Law Defines/Constrains Damage Computation Law Encourages Risk Mgt l l Crimes, Torts, Contracts, Standards, Determination of Injury Law Dis-Incentivizes Risky Deeds (DD&t. DDC) Law Defines Risk Management Duties l l Risk Analysis Failure Shifts Liability Risks to Creator Actual Injuries Trigger Disputes over Risk Duties Law Defines Risk Mgt Professionalism Law Enforces Risk Shifting Contracts Law Requires Risk Analysis & Impacts Methods But Law may Disincentivize Introspection w/o Self-Eval Privilege Law Regulates Risk Management Industry Law Enforces Risk Mgt Profession’s Arrangements
- Slides: 29