Optimal Termination Detection for Rings Murat Demirbas OSU
Optimal Termination Detection for Rings Murat Demirbas OSU
Termination Detection in D. S. n n n Message passing, Asynchronous execution A process is either active or passive Active processes: – send and receive messages, – can become passive spontaneously n Passive processes: – can only receive messages, – can become active only by receiving a message.
Termination detection problem n The system is terminated iff – all processes are passive – no messages in transit n The problem is to detect termination as and when the system terminated.
Related work n Chandy & Lamport snapshot alg. – O(N 2) time n Dijkstra & Safra token-based alg. – O(N) time, 2 N -- 3 N n Chandy alg. – 2 N integers per process, and message – 2 N 2 integers at the detector – Sivilotti improved the space complexity
Our algorithm n n Based on Dijkstra&Safra alg. Detection in 0 -- N time each process maintains 1 int. + N bits token stores N int. + N bits
Outline n n Dijkstra & Safra alg Optimal alg – Enhancement 1 – Enhancement 2 n Proof
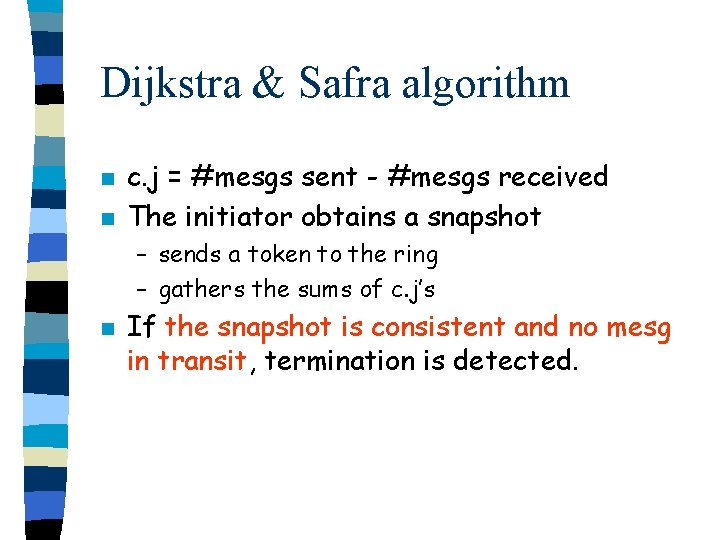
Dijkstra & Safra algorithm n n c. j = #mesgs sent - #mesgs received The initiator obtains a snapshot – sends a token to the ring – gathers the sums of c. j’s n If the snapshot is consistent and no mesg in transit, termination is detected.
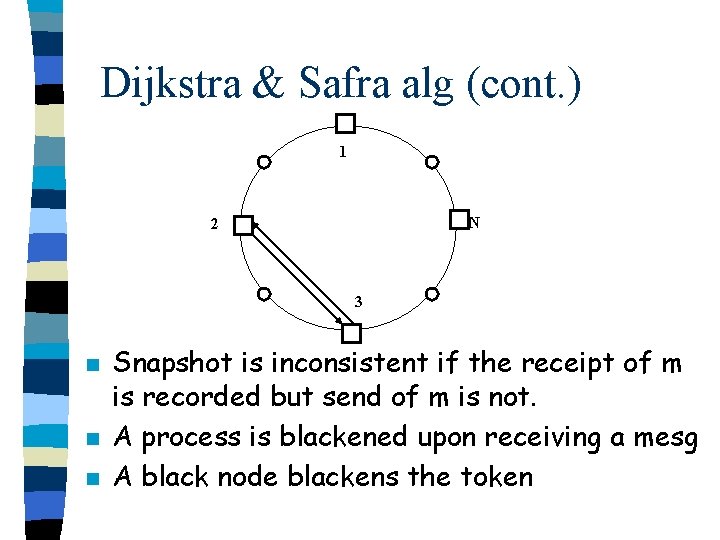
Dijkstra & Safra alg (cont. ) 1 N 2 3 n n n Snapshot is inconsistent if the receipt of m is recorded but send of m is not. A process is blackened upon receiving a mesg A black node blackens the token
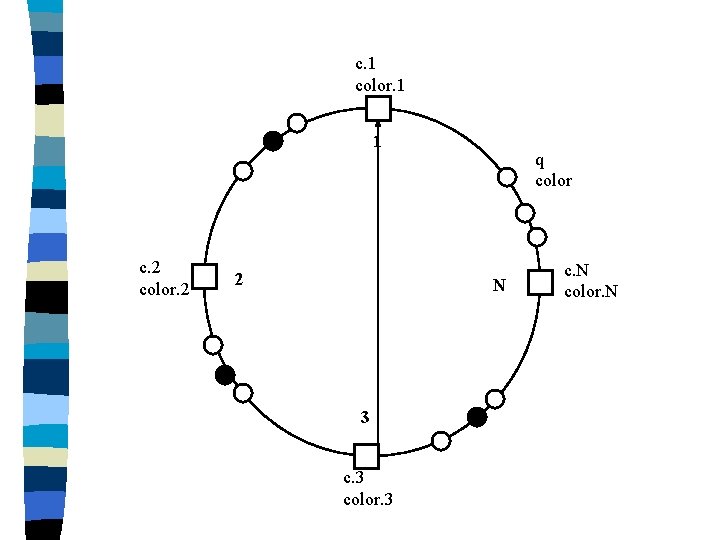
c. 1 color. 1 1 c. 2 color. 2 2 q color N 3 color. 3 c. N color. N
An optimal algorithm for Termination Detection on Rings n n n First enhancement (Enumeration bits) Second enhancement (Multiple initiators) Optimal algorithm = 1 st & 2 nd enh. combined
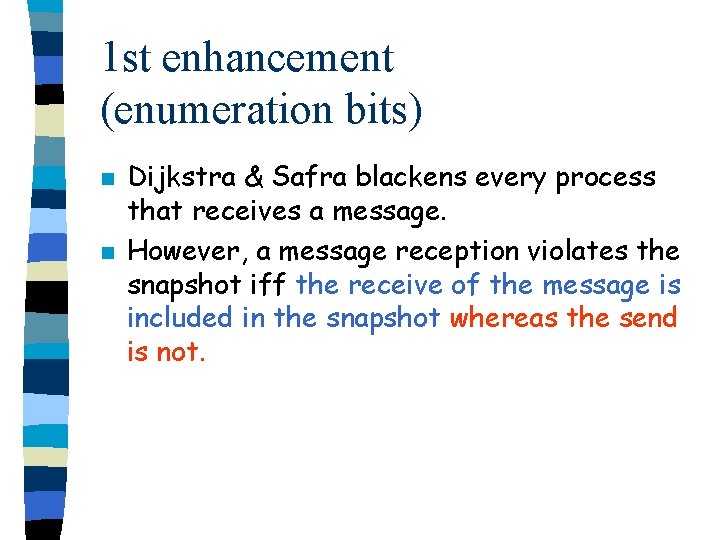
1 st enhancement (enumeration bits) n n Dijkstra & Safra blackens every process that receives a message. However, a message reception violates the snapshot iff the receive of the message is included in the snapshot whereas the send is not.
1 2 3 5 4
1 st enhancement (enumeration bits) n n n The messages that violate the consistency are those sent by a process in the visited region to another process in the unvisited region. A process sending a mesg piggybacks its enumeration bit + its process id. j upon receiving “m” blackens itself iff: – enum. j enum. m – j > sender_id. m
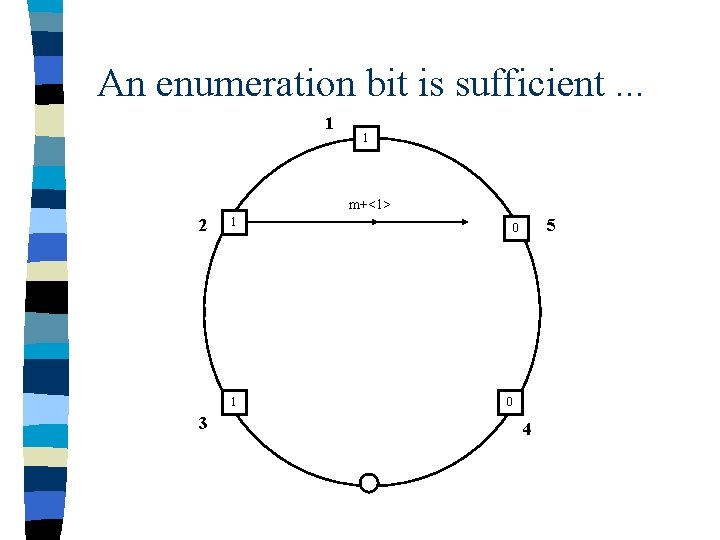
An enumeration bit is sufficient. . . 1 1 m+<1> 2 1 1 3 5 0 0 4
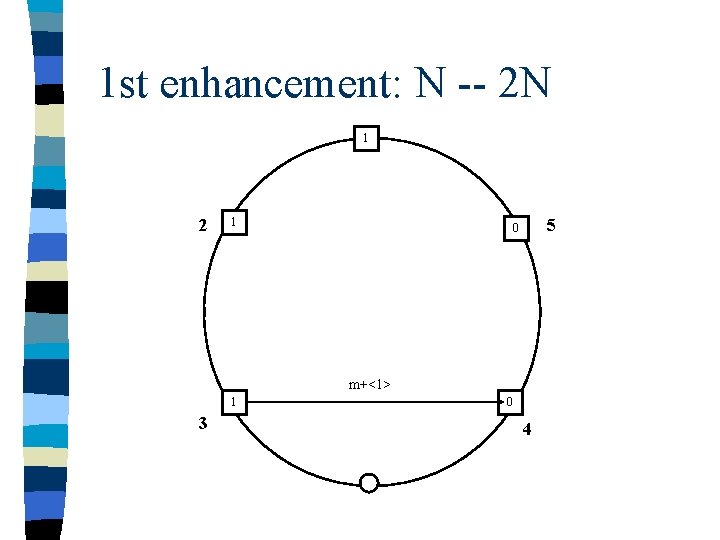
1 st enhancement: N -- 2 N 1 2 1 5 0 m+<1> 1 3 0 4
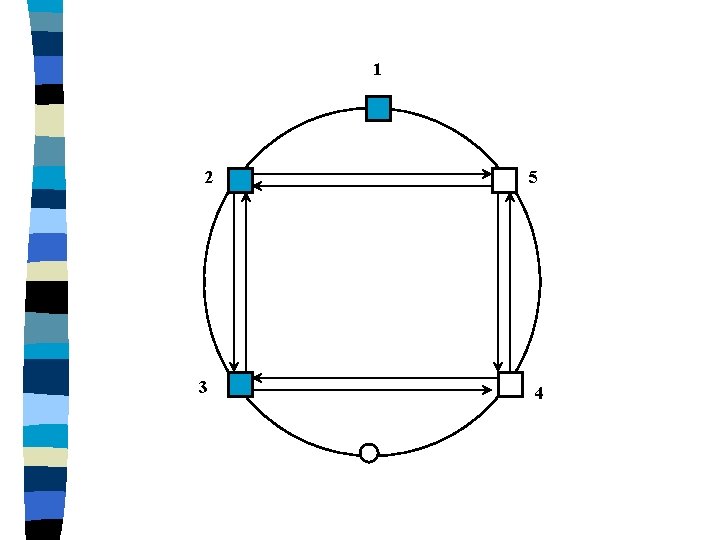
2 nd Enhancement (Multiple initiators) n n n D&S alg has a fixed initiator: N A vector [q 1, q 2, …, q. N] maintains the sum, q, w. r. t. multiple initiators. N -- 2 N time to detect termination
![1 [0, q 2, q 3, q 4, q 5] [0, 0, 0] [B, 1 [0, q 2, q 3, q 4, q 5] [0, 0, 0] [B,](http://slidetodoc.com/presentation_image_h/198b83d7619062daca365b751f2df1e5/image-17.jpg)
1 [0, q 2, q 3, q 4, q 5] [0, 0, 0] [B, q 2, q 3, q 4, 0] [q 1, 0, 0] 2 5 [B, q 2, q 3, 0, B] [B, 0, B, B, B] 3 4 [B, q 2, 0, B, B]
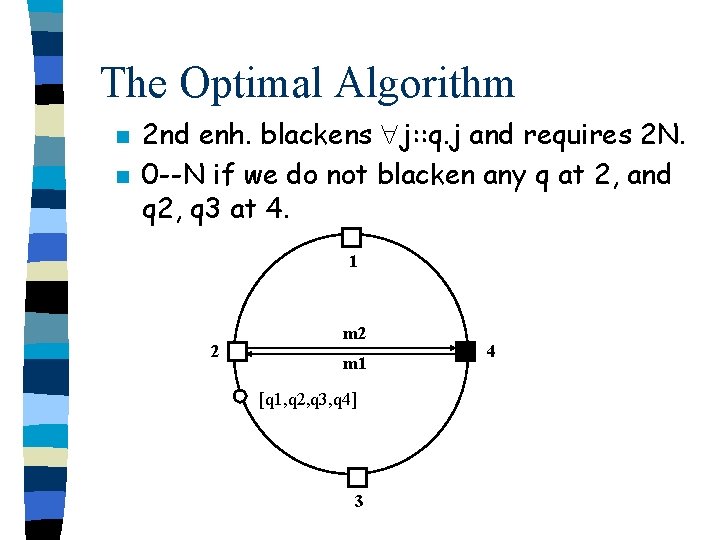
The Optimal Algorithm n n 2 nd enh. blackens j: : q. j and requires 2 N. 0 --N if we do not blacken any q at 2, and q 2, q 3 at 4. 1 2 m 1 [q 1, q 2, q 3, q 4] 3 4
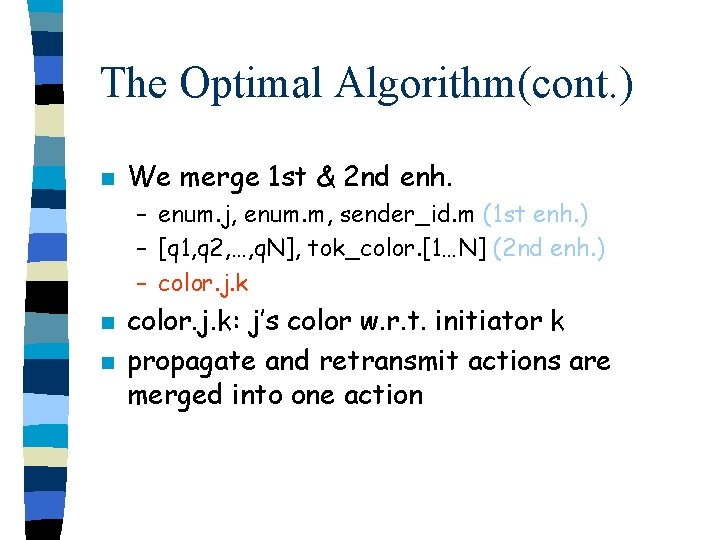
The Optimal Algorithm(cont. ) n We merge 1 st & 2 nd enh. – enum. j, enum. m, sender_id. m (1 st enh. ) – [q 1, q 2, …, q. N], tok_color. [1…N] (2 nd enh. ) – color. j. k n n color. j. k: j’s color w. r. t. initiator k propagate and retransmit actions are merged into one action
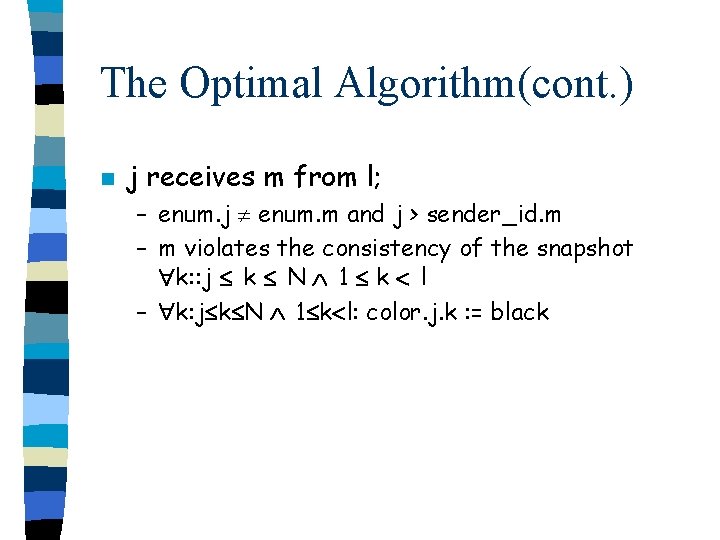
The Optimal Algorithm(cont. ) n j receives m from l; – enum. j enum. m and j > sender_id. m – m violates the consistency of the snapshot k: : j k N 1 k l – k: j k N 1 k l: color. j. k : = black
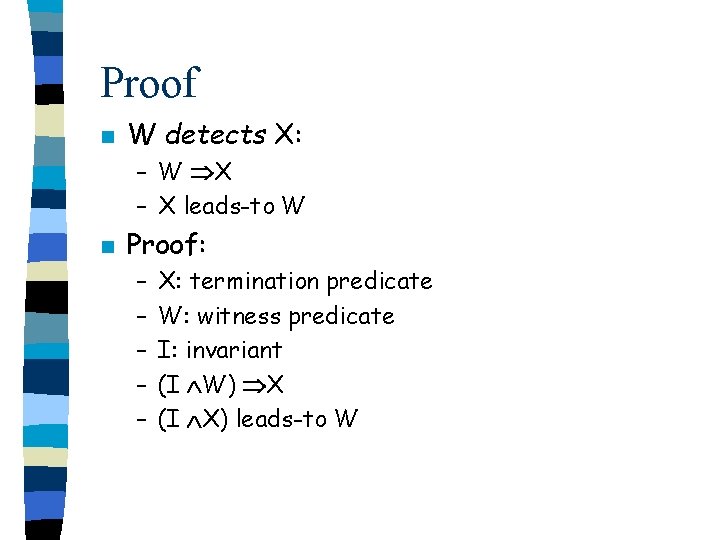
Proof n W detects X: – W X – X leads-to W n Proof: – – – X: termination predicate W: witness predicate I: invariant (I W) X (I X) leads-to W
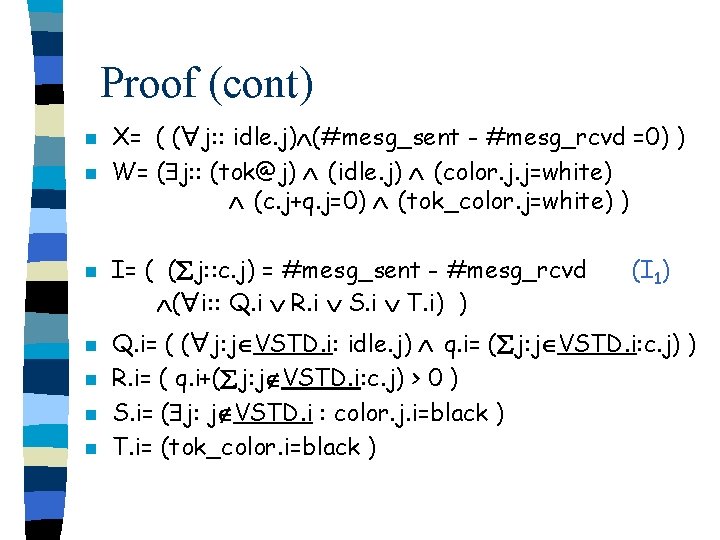
Proof (cont) n n n n X= ( ( j: : idle. j) (#mesg_sent - #mesg_rcvd =0) ) W= ( j: : (tok@j) (idle. j) (color. j. j=white) (c. j+q. j=0) (tok_color. j=white) ) I= ( ( j: : c. j) = #mesg_sent - #mesg_rcvd ( i: : Q. i R. i S. i T. i) ) (I 1) Q. i= ( ( j: j VSTD. i: idle. j) q. i= ( j: j VSTD. i: c. j) ) R. i= ( q. i+( j: j VSTD. i: c. j) > 0 ) S. i= ( j: j VSTD. i : color. j. i=black ) T. i= (tok_color. i=black )
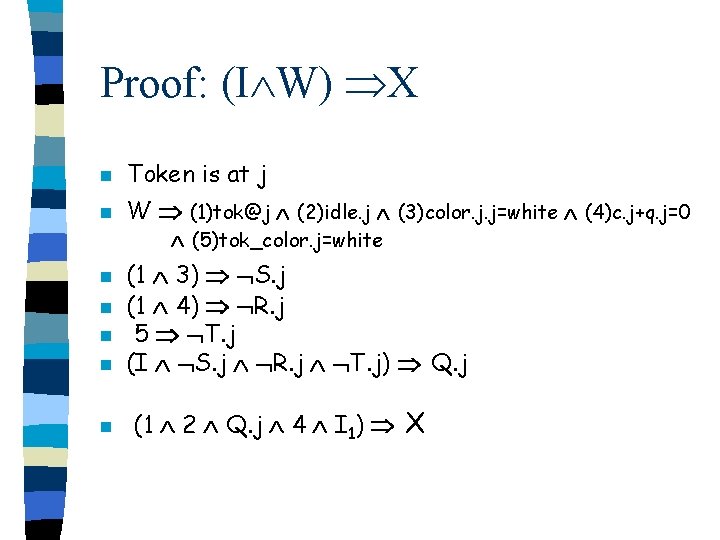
Proof: (I W) X n Token is at j n W (1)tok@j (2)idle. j (3)color. j. j=white (4)c. j+q. j=0 (5)tok_color. j=white n n n (1 3) S. j (1 4) R. j 5 T. j (I S. j R. j T. j) Q. j (1 2 Q. j 4 I 1) X
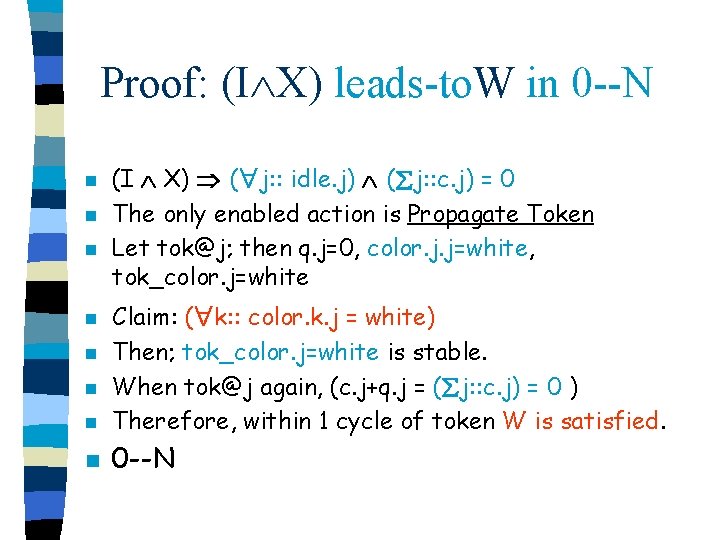
Proof: (I X) leads-to. W in 0 --N n n n (I X) ( j: : idle. j) ( j: : c. j) = 0 The only enabled action is Propagate Token Let tok@j; then q. j=0, color. j. j=white, tok_color. j=white n Claim: ( k: : color. k. j = white) Then; tok_color. j=white is stable. When tok@j again, (c. j+q. j = ( j: : c. j) = 0 ) Therefore, within 1 cycle of token W is satisfied. n 0 --N n n n
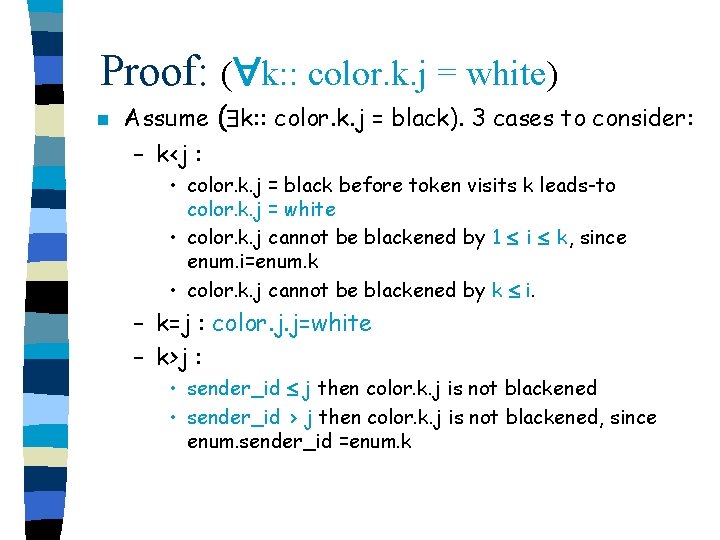
Proof: ( k: : color. k. j = white) n Assume ( k: : color. k. j = black). 3 cases to consider: – k<j : • color. k. j = black before token visits k leads-to color. k. j = white • color. k. j cannot be blackened by 1 i k, since enum. i=enum. k • color. k. j cannot be blackened by k i. – k=j : color. j. j=white – k>j : • sender_id j then color. k. j is not blackened • sender_id > j then color. k. j is not blackened, since enum. sender_id =enum. k
Conclusion n An optimal termination detection algorithm on rings 0 --N
New Results T. D. in Trees & Chandy’s model: n n n 2 h--3 h detection in trees Efficient T. D. in Chandy’s model: – 1 --2 rounds to detect termination – requires just 1 integer + 1 bit in each process including DET. – Chandy: 2 N integers in each process, 2 N 2 integers in DET.
- Slides: 27