Introduction CPSC 363 Computer Networks Ellen Walker Hiram
- Slides: 46
Introduction CPSC 363 Computer Networks Ellen Walker Hiram College (Includes figures from Computer Networking by Kurose & Ross, © Addison Wesley 2002)
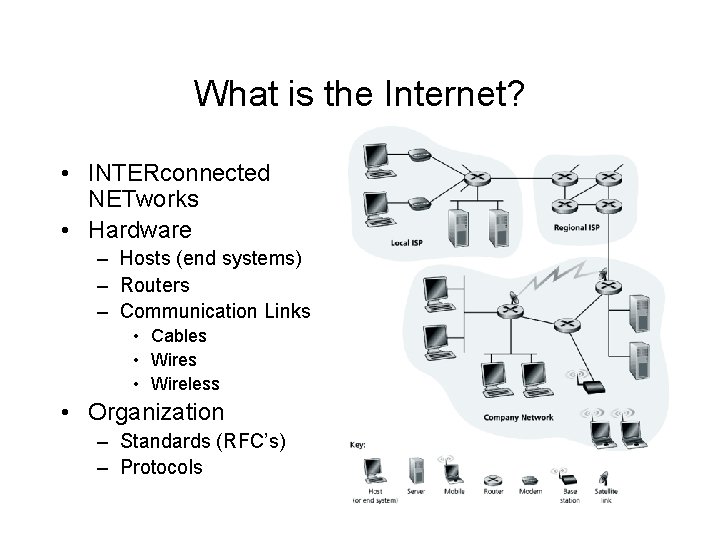
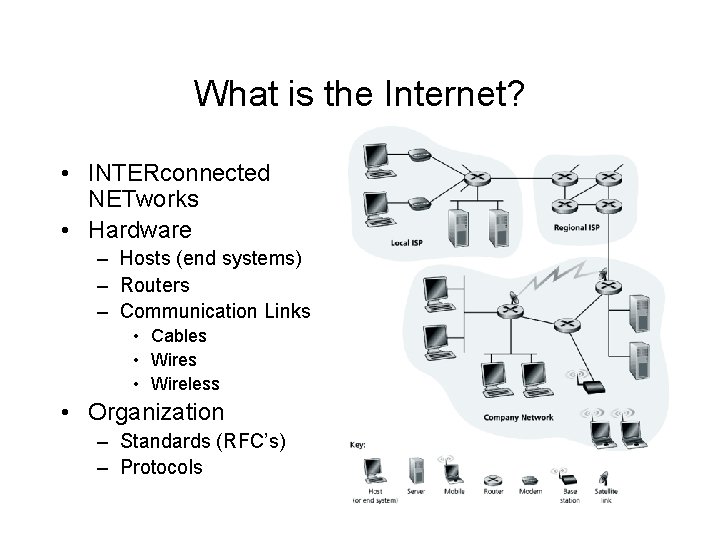
What is the Internet? • INTERconnected NETworks • Hardware – Hosts (end systems) – Routers – Communication Links • Cables • Wireless • Organization – Standards (RFC’s) – Protocols
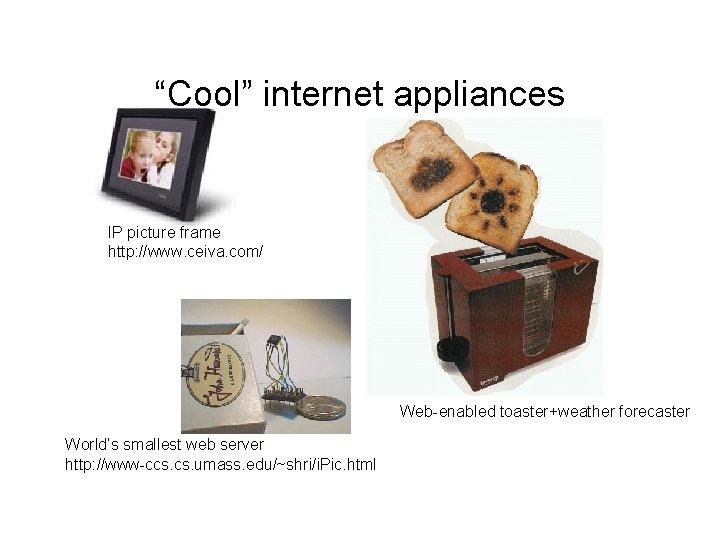
“Cool” internet appliances IP picture frame http: //www. ceiva. com/ Web-enabled toaster+weather forecaster World’s smallest web server http: //www-ccs. umass. edu/~shri/i. Pic. html
Message Transmission across the Internet • Source host creates the message to send • Message is transmitted via the local network to the local router (gateway) • Message travels from router to router until the destination’s gateway is reached • Message is transmitted across the destination’s LAN to the destination host. • Destination host receives and acts upon the message.
What is Provided? • Communication services for distributed applications – – – Remote file transfer and login WWW Peer to Peer (e. g. Gnutella, Kazaa) Multimedia applications IM, chat New applications all the time… • Types of services – Connection-oriented & reliable (TCP) – Connectionless unreliable (UDP) – No guarantee of how quickly the message is delivered
TCP vs UDP: An analogy • TCP is like a conversation – Each party makes sure the other party received and understood each message. – If you don’t understand, I repeat … • UDP is like shouting from a rooftop – I keep yelling (transmitting info) with no idea of whether you can hear and understand me
What is a Protocol? • Set of conventions surrounding a conversation, e. g. – – – – – Dial phone, hear ring Hear ring, pick up phone, “Hello” “Hello, may I speak to…” “Just a minute…” [New person] “Hello” [conversation here] “Goodbye”, hang up phone Hang up phone • Conversation is aborted if appropriate response is missing!
Examples of Computer Network Protocols • Application protocols – HTTP (Hypertext transfer protocol) – FTP (File transfer protocol) – SMTP (Simple mail transfer protocol) • Router and Network protocols – TCP (Transmission Control Protocol) – IP (Internet Protocol)
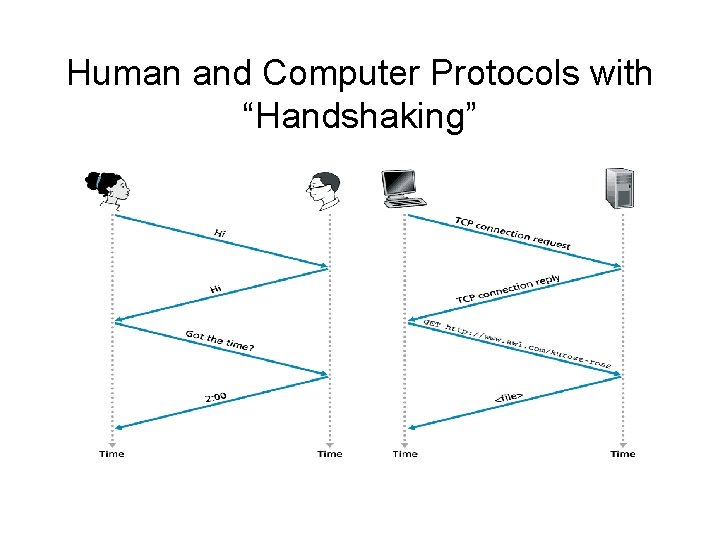
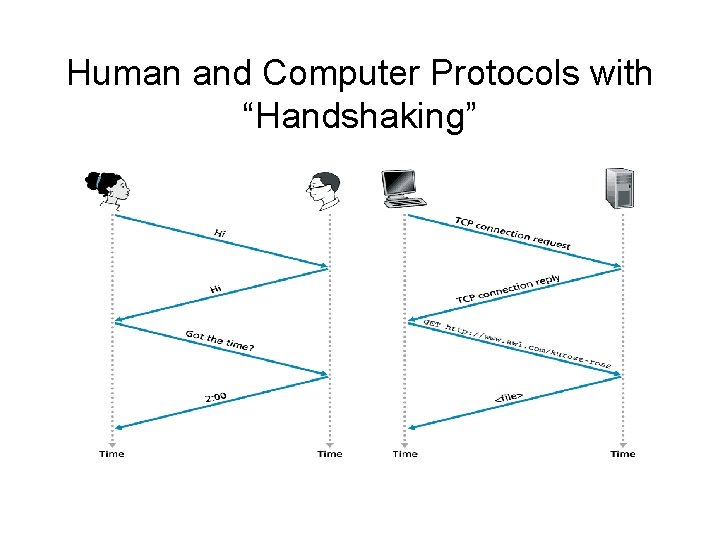
Human and Computer Protocols with “Handshaking”
End Systems • Servers – Provide a “service” to others on the network • Web server • Email server • Database Management System • Clients – Request “services” from others • Web browser • Email or DB client program • Both – Peer to Peer (P 2 P) hosts act as both client and server.
Network Core • How is information passed through the network? • Goal: fast, accurate, avoid “idleness” • Terms from telephony, information theory – Circuit Switching vs. Packet Switching – Multiplexing (Frequency vs. time) – Bandwidth, Latency, Throughput
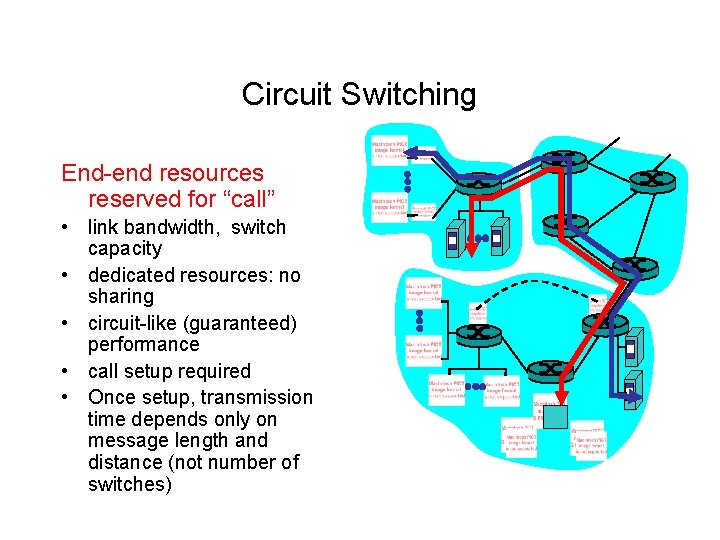
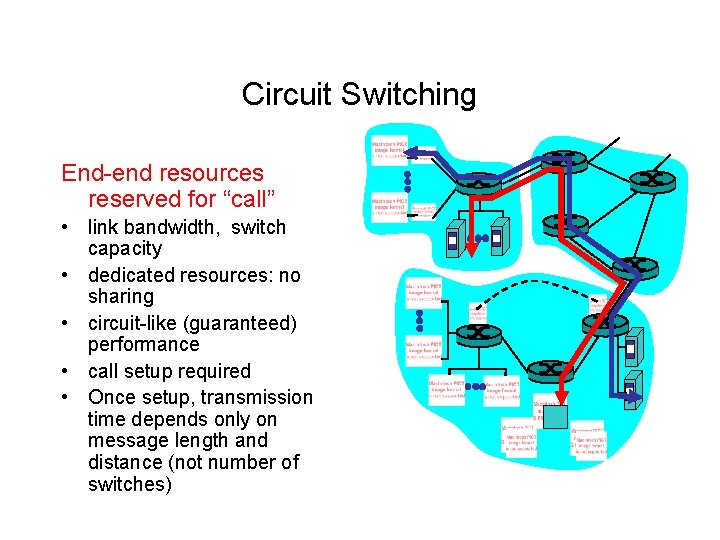
Circuit Switching End-end resources reserved for “call” • link bandwidth, switch capacity • dedicated resources: no sharing • circuit-like (guaranteed) performance • call setup required • Once setup, transmission time depends only on message length and distance (not number of switches)
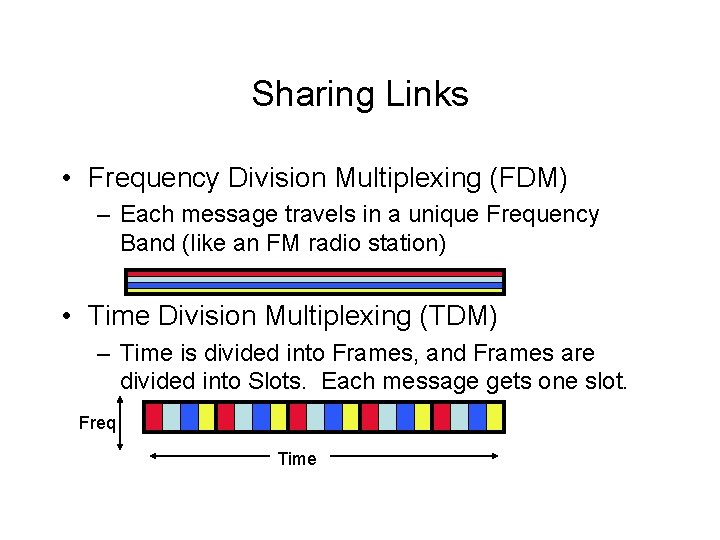
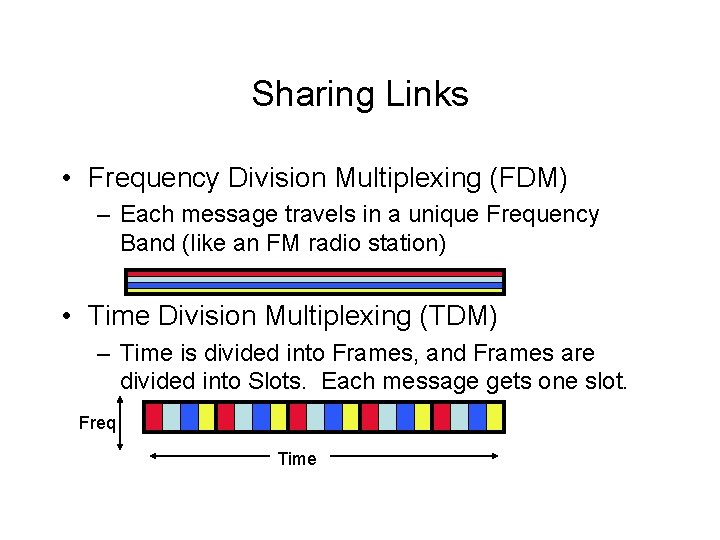
Sharing Links • Frequency Division Multiplexing (FDM) – Each message travels in a unique Frequency Band (like an FM radio station) • Time Division Multiplexing (TDM) – Time is divided into Frames, and Frames are divided into Slots. Each message gets one slot. Freq Time
Disadvantages of Circuit Switching • Time to set up the circuit • Once the circuit is connected, bandwidth is reserved -- even if no message is being sent – Telephone “silence” – Reading the message before responding… • … but it worked pretty well for telephones for years! (Mostly because people aren’t silent much)
Packet Switching • Divide messages into fixed-size packets • Each packet uses full bandwidth • Each packet travels its own path (message is reassembled and reordered at the end) • Switches (now called routers) collect and pass packets along paths toward their final destination
Store and Forward Transmission • Router has several links • When a packet is received: – Router waits until the entire packet has been received before doing anything (store-and-forward delay) – Packet is stored in the output buffer until the outgoing link is available (queuing delay) – If the buffer is full, the packet is dropped (packet loss) – Packet is sent on the outgoing link (to the next router)
How Long Does it Take? • Assume we want to send a packet of L=1000 bits from one host to another across the network • The packet must pass through Q=4 links to get there. • Each link can transmit R= 10, 000 bps (bits per second) • From one router to the next will take (1000 bits) / (10, 000 bits / second) = 0. 1 seconds • After 0. 1 seconds, the full packet is available to send out. Assuming no delays, we can do this 4 times in 0. 4 seconds, which is the total time to send the message.
Unit Math • If you forget the formulas for computing times and distances, remember you can always do the “unit math” for example: Bits / (Bits / Second) = Bits * (Seconds / Bits) = (Bits * Seconds) / Bits = (Seconds * Bits) / Bits = Seconds * (Bits / Bits) = Seconds
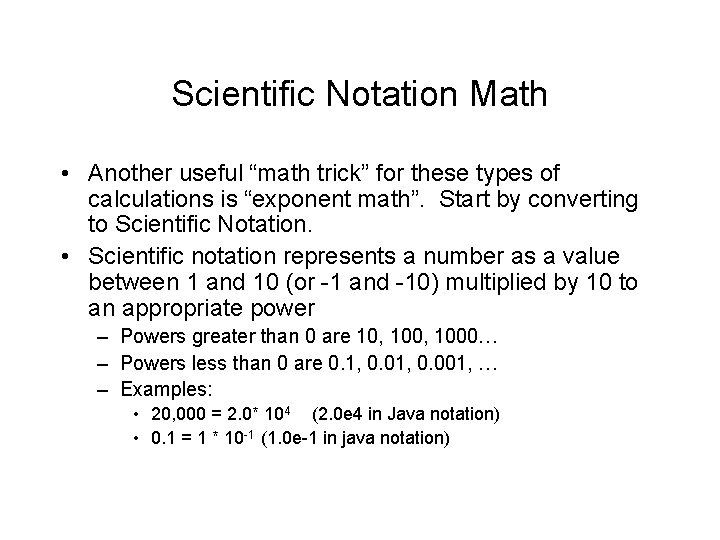
Scientific Notation Math • Another useful “math trick” for these types of calculations is “exponent math”. Start by converting to Scientific Notation. • Scientific notation represents a number as a value between 1 and 10 (or -1 and -10) multiplied by 10 to an appropriate power – Powers greater than 0 are 10, 1000… – Powers less than 0 are 0. 1, 0. 001, … – Examples: • 20, 000 = 2. 0* 104 (2. 0 e 4 in Java notation) • 0. 1 = 1 * 10 -1 (1. 0 e-1 in java notation)
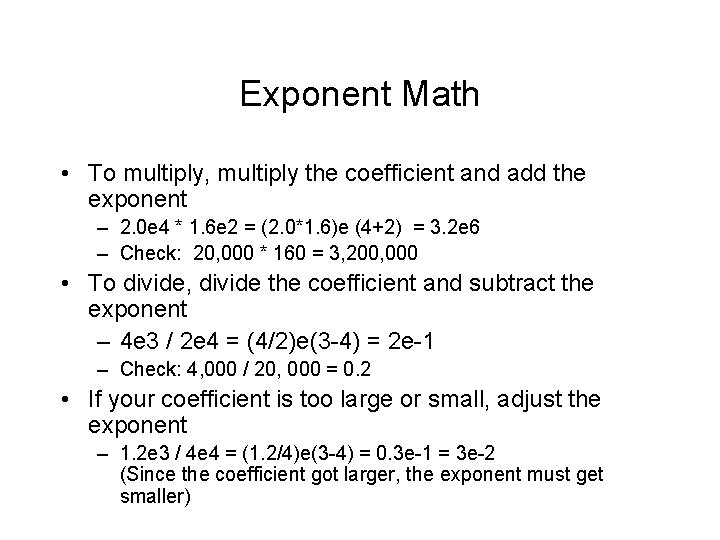
Exponent Math • To multiply, multiply the coefficient and add the exponent – 2. 0 e 4 * 1. 6 e 2 = (2. 0*1. 6)e (4+2) = 3. 2 e 6 – Check: 20, 000 * 160 = 3, 200, 000 • To divide, divide the coefficient and subtract the exponent – 4 e 3 / 2 e 4 = (4/2)e(3 -4) = 2 e-1 – Check: 4, 000 / 20, 000 = 0. 2 • If your coefficient is too large or small, adjust the exponent – 1. 2 e 3 / 4 e 4 = (1. 2/4)e(3 -4) = 0. 3 e-1 = 3 e-2 (Since the coefficient got larger, the exponent must get smaller)
Another Example • Link bandwidth is 2400 bits / second • Message is 120, 000 bits long • Message must pass through 3 links • With no queueing delays or propagation delays, how long will the message take?
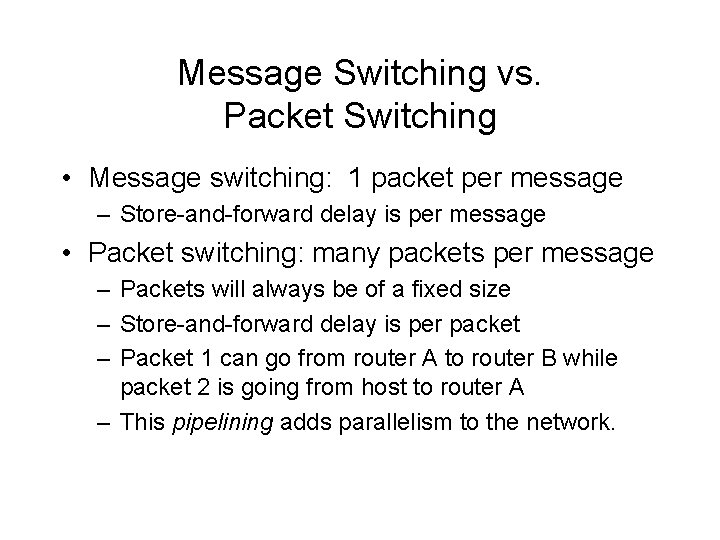
Message Switching vs. Packet Switching • Message switching: 1 packet per message – Store-and-forward delay is per message • Packet switching: many packets per message – Packets will always be of a fixed size – Store-and-forward delay is per packet – Packet 1 can go from router A to router B while packet 2 is going from host to router A – This pipelining adds parallelism to the network.
Packet Switching Example • Link bandwidth is 2400 bits / second • Message is 120, 000 bits long, divided into 4 packets of 30, 000 bits each • Message must pass through 3 links • With no queuing delays or propagation delays, how long will the message take?
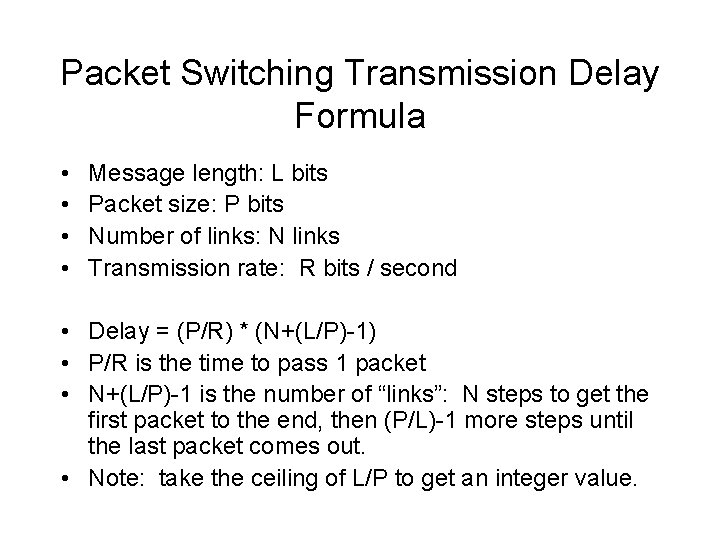
Packet Switching Transmission Delay Formula • • Message length: L bits Packet size: P bits Number of links: N links Transmission rate: R bits / second • Delay = (P/R) * (N+(L/P)-1) • P/R is the time to pass 1 packet • N+(L/P)-1 is the number of “links”: N steps to get the first packet to the end, then (P/L)-1 more steps until the last packet comes out. • Note: take the ceiling of L/P to get an integer value.
Considering Delay and Loss • Processing Delay (typically microseconds) – Time to examine header and determine where to store the packet • Queuing Delay (varies based on traffic) – Time waiting for outbound link to be available • Transmission Delay (packet length / transmission rate) – Time to push all bits of the packet onto the link • Propagation Delay (distance / speed) – Time for one bit to travel the length of the link • Packet Loss – When the queue is completely full, packets are dropped.
Tollbooth Analogy • Road has tollbooths every 100 km. • Messages are convoys; cars are packets • Transmission delay = time for one car to pass one toll barrier • Propagation delay = time for one car to travel 100 km to the next toll barrier
R and S in Tollbooth Analogy • R = transmission rate of the router (bits / second) – Corresponds to number of cars that can be served by a toll barrier in a fixed amount of time (say, cars / hour). – Increase by adding more toll collectors at the barrier • S = propagation speed of the link (e. g. speed of electrons in copper; speed of light) – Corresponds to car speed – Increase (legally) by raising the speed limit
Some Tradeoffs in Network Design • We have little control over propagation delay – Can’t move Europe (or Mars) closer – Can’t increase the speed of light! • Transmission delay is easier to control – Faster hardware, or more hardware in parallel increases transmission rate • Make sure transmission rate is at least as fast as average incoming bit rate (traffic intensity) – Otherwise, queues are guaranteed to fill and stay full
Javascript Applets • These can be found at the book’s website – Start at our site (http: //cs. hiram. edu/~walkerel/cs 363) – Or go direct to the textbook site (http: //www. awl. com/kurose-ross-3) – All 3 chapter 1 applets are very nice
Finding Real Delays • Application called “traceroute” – Sends a special message to the destination – Each host along the way replies back with timing information • To run in linux traceroute <address> , e. g. traceroute www. yahoo. com
How Are Packets Directed? • Virtual Circuit – All packets take the same path from source to destination – Packets contain virtual circuit number (VC#) changes at each hop – VC# tells router where to send the packet next – Each router has table of incoming interface# and VC#, and outgoing interface# and VC# – Special packets are used to establish and break virtual circuits
How are Packets Directed? • Datagram – Each packet has a header with an address – Address is hierarchically structured – Router looks at appropriate part of the address to select next destination • • • Paris -> plane to USA [USA] USA customs -> truck to Akron, OH post office [442] Akron -> truck to Hiram, OH post office [44234] Hiram post office -> Service Center [Hiram College] Service center -> my mailbox [Ellen Walker, CS Dept]
Virtual Circuit vs. Datagram • Virtual Circuit – All packets take the same path, arrive in order – Circuit, once established, subject to delays, etc. – Routers must keep connection state information • Datagram – Packets can take different paths, must be reassembled – Paths can vary to account for outages; delays – No connection state information maintained in routers
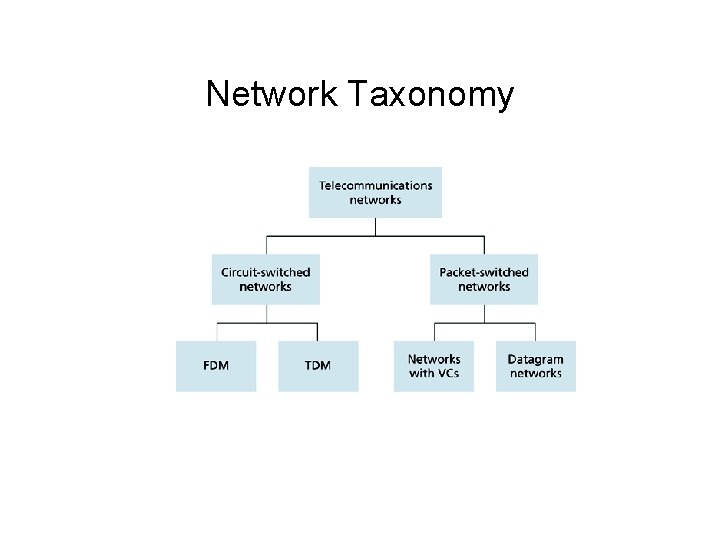
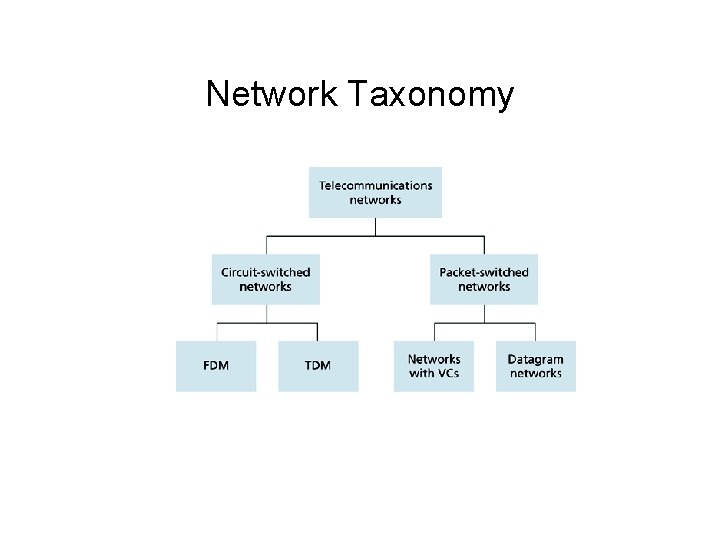
Network Taxonomy
Internet Service Providers (ISPs) • Tier 1 (“backbone”) – AT&T, Sprint, UUNet, etc. – National & international connections • Tier 2 – Provide regional connections, e. g. Oarnet (Ohio) – Purchase services from Tier 1 providers • Tier 3 and local – “Last mile” connections – Purchase services from Tier 2 – Sell services directly to individual & small business customers
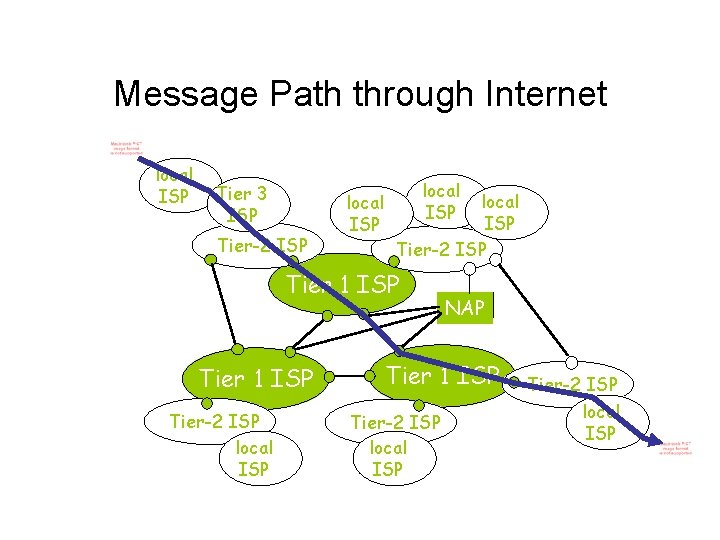
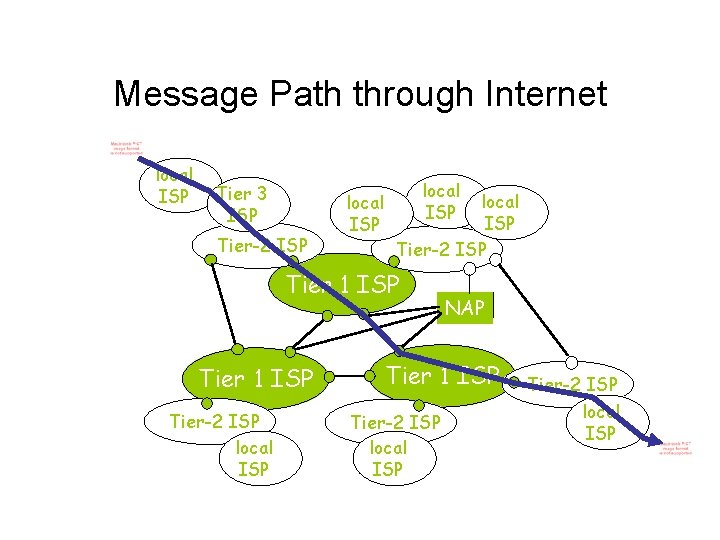
Message Path through Internet local ISP Tier 3 ISP Tier-2 ISP local ISP Tier-2 ISP Tier 1 ISP Tier-2 ISP local ISP NAP Tier 1 ISP Tier-2 ISP local ISP
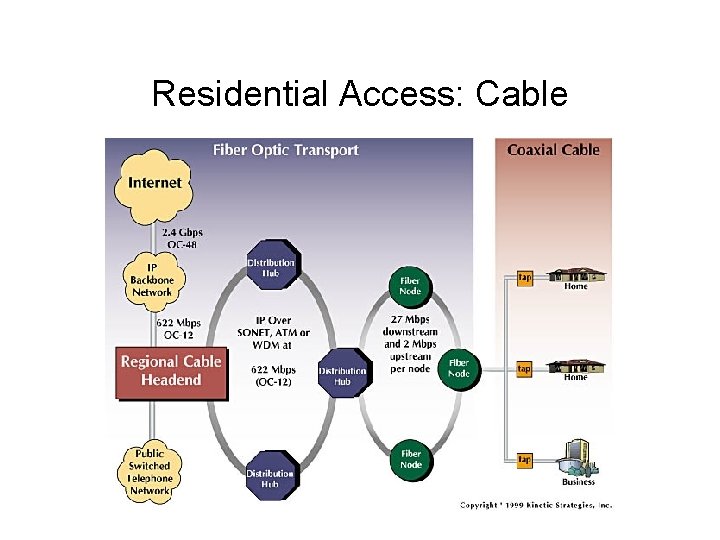
Residential “gateway” connections • Dialup modem – Standard analog telephone line – <= 56 Kbps • Digital subscriber line (DSL) – Standard phone lines, restricted distance to modem – 3 Frequency channels (downstream, upstream, voice) – 384 K– 1. 5 Mbps downstream, 128 K-256 Kbps upstream • Hybrid Fiber Coaxial Cable (HFC) – Fiber optic cable into neighborhood terminal, connected to coax cable to each house – 2 channels (downstream & upstream) – Shared medium (all messages to all connected modems)
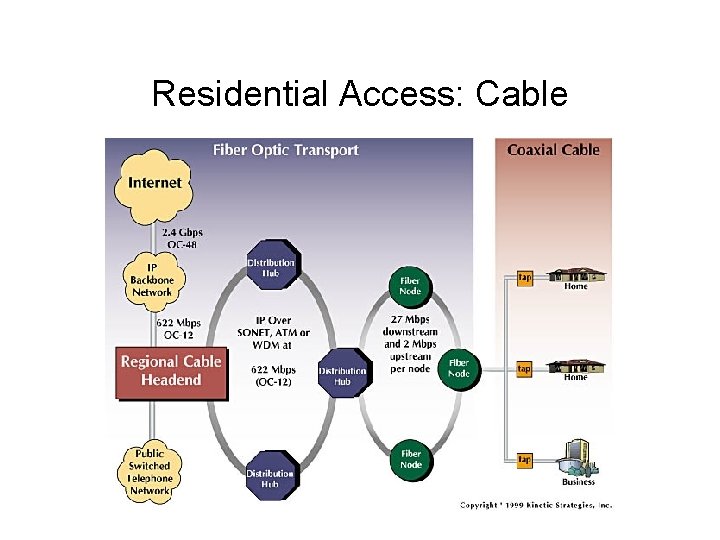
Residential Access: Cable
Local Area Networks • Ethernet (most common wired technology) – 10 Mbps , 100 Mbps, 1 Gbps even now 10 Gps – Twisted pair copper wire or coax cable • Wireless LAN – Base station (access point) connected to wired LAN – IEEE 802. 11 b is 11 Mbps (802. 11 g is faster) – Typically good for 10 s of meters • WAP (Europe, US) and I-mode (Japan) – Extend cell-phone network to Internet – Eg. Cingular GPRS, still fairly expensive
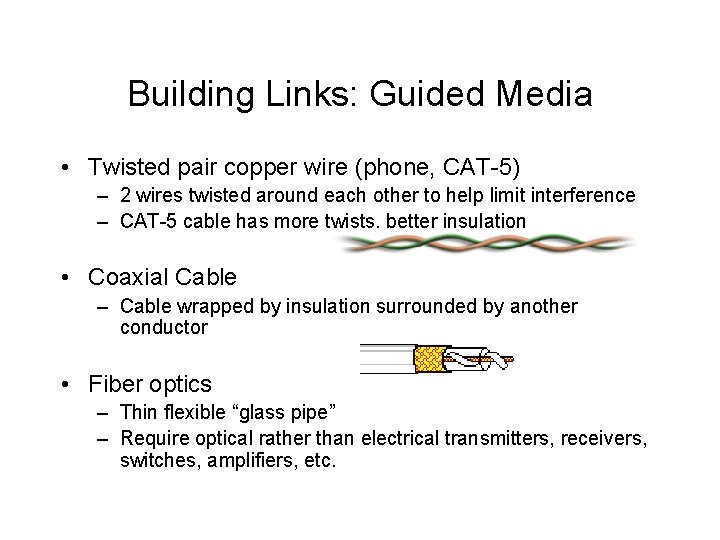
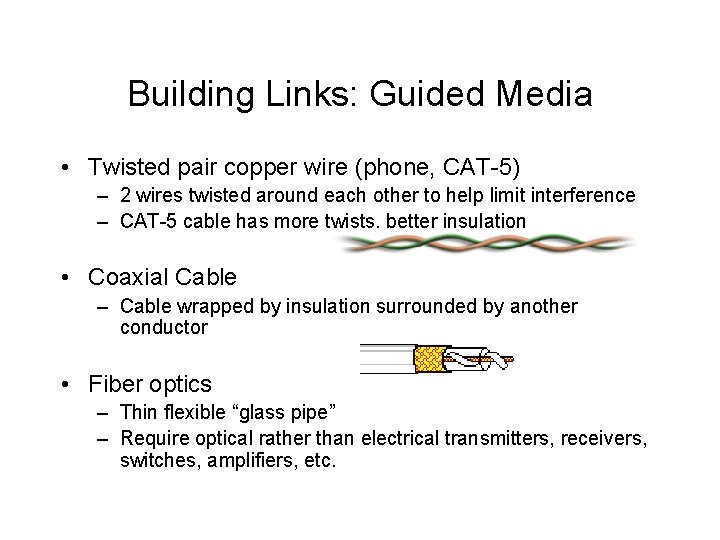
Building Links: Guided Media • Twisted pair copper wire (phone, CAT-5) – 2 wires twisted around each other to help limit interference – CAT-5 cable has more twists, better insulation • Coaxial Cable – Cable wrapped by insulation surrounded by another conductor • Fiber optics – Thin flexible “glass pipe” – Require optical rather than electrical transmitters, receivers, switches, amplifiers, etc.
Unguided Media • Terrestrial radio link – Bands allocated for wireless transmission – FCC regulated in US • Satellite radio channels – Geostationary satellites used for phone network & internet backbone
Dealing with Complexity • The path a message takes is complex; dealing with hosts, switches, packets, media, etc. • Therefore we use an abstract model to divide the transmission into layers • The sender at each layer uses the lower layers (as a black box) to send information directly to the recipient at that layer. • Each layer considers information from layers above to be “data bits”
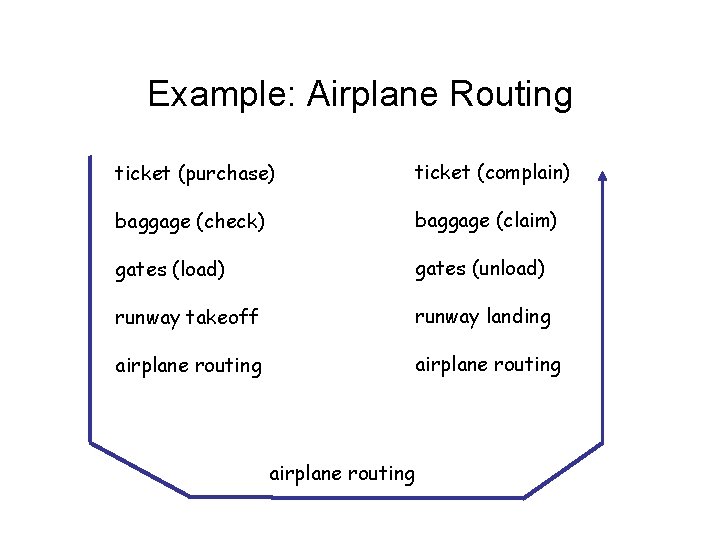
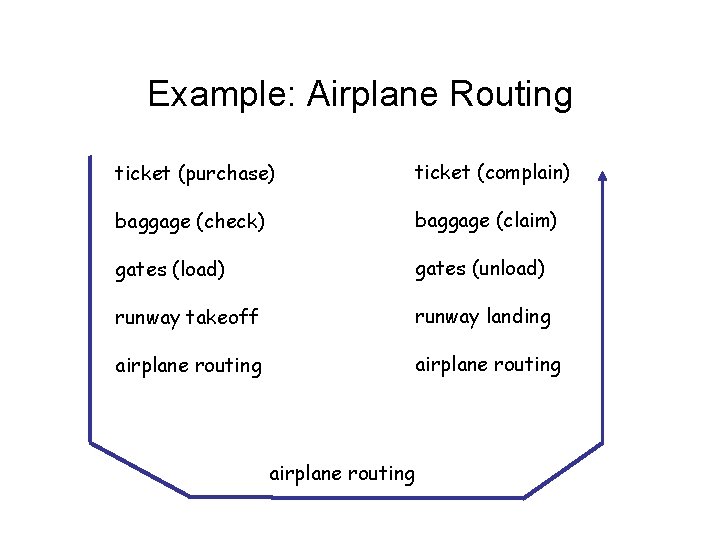
Example: Airplane Routing ticket (purchase) ticket (complain) baggage (check) baggage (claim) gates (load) gates (unload) runway takeoff runway landing airplane routing
Internet Protocol Stack • Application (web, email) • Transport (TCP, UDP, message transport) • Network (IP, datagram routing between endhosts) • Link (Ethernet, datagram transfer between neighboring switches) • Physical (bits on the “wire”)
Internet Hardware • End host (all 5 layers) • Intermediate switches (generally 3, sometimes 2 layers only)
Enveloping a Message • Each layer takes data from the above layer – Breaks it apart if necessary (e. g. packetizing) – Adds an “envelope” = header and/or footer bits – Passes it to the next layer below, which will treat envelope as part of the data