Internet Cache Pollution Attacks and Countermeasures Yan Gao
- Slides: 23
Internet Cache Pollution Attacks and Countermeasures Yan Gao, Leiwen Deng, Aleksandar Kuzmanovic, and Yan Chen Electrical Engineering and Computer Science Department Northwestern University 1
Outline • • Motivation Pollution Attacks Evaluation of Pollution Effects Counter-Pollution Techniques & Evaluation • Conclusion 2
Motivation • Caching has been widely applied in the Internet – Decrease the amount of requests in server side – Reduce the amount of traffic in the network – Improve the client-perceived latency • Open proxy caches are used for various abuse-related activities • Proxy caches themselves become victims – Little attention given to such attacks – Existing pollution attacks mostly on content pollutions on P 2 P systems 3
Contributions • Propose a class of pollution attacks targeted against Internet proxy caches – Locality-disruption (LD) attacks – False-locality (FL) attacks • Analyze the resilience of the current cache replacement algorithms to pollution attacks • Propose two cache pollution detection mechanisms – Detect LD, FL attacks, and their combination – Leverage data streaming computation techniques 4
Outline • • Motivation Pollution Attacks Evaluation of Pollution Effects Counter-Pollution Techniques & Evaluation • Conclusion 5
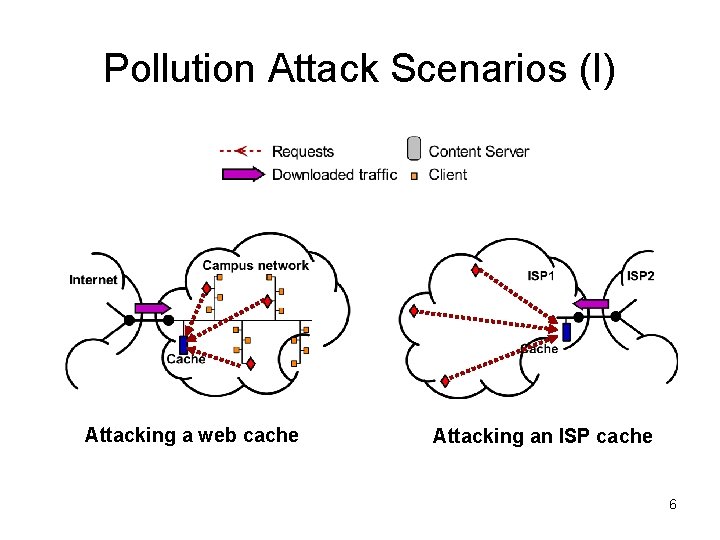
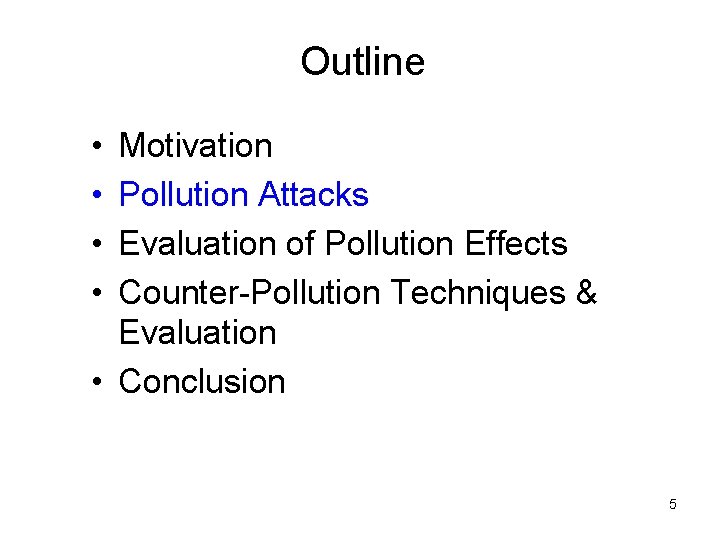
Pollution Attack Scenarios (I) Attacking a web cache Attacking an ISP cache 6
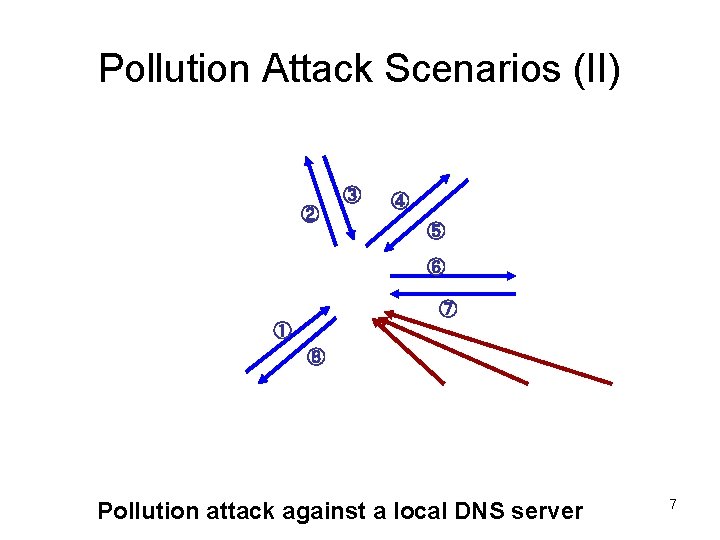
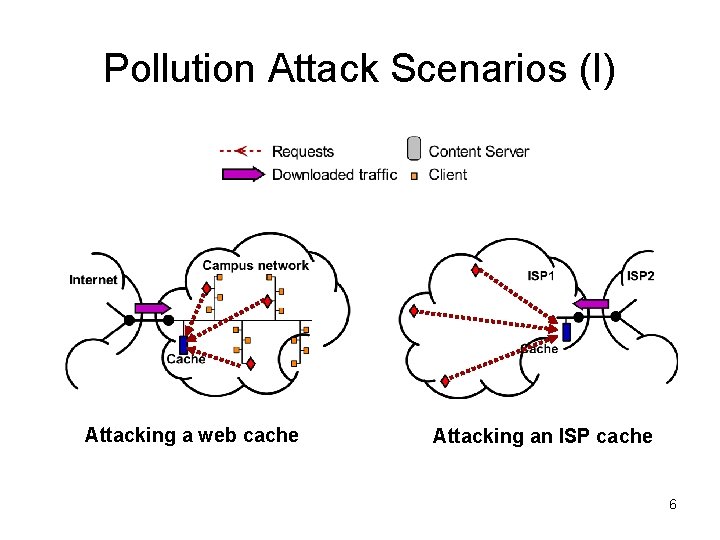
Pollution Attack Scenarios (II) ③ ② ④ ⑤ ⑥ ⑦ ① ⑧ Pollution attack against a local DNS server 7
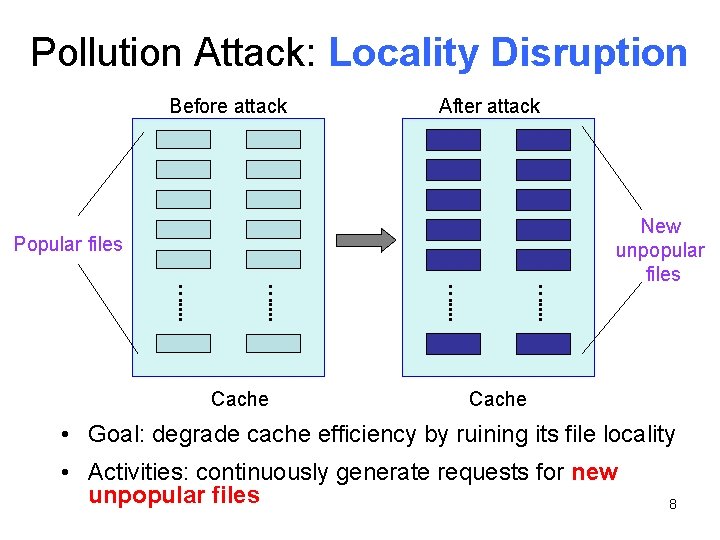
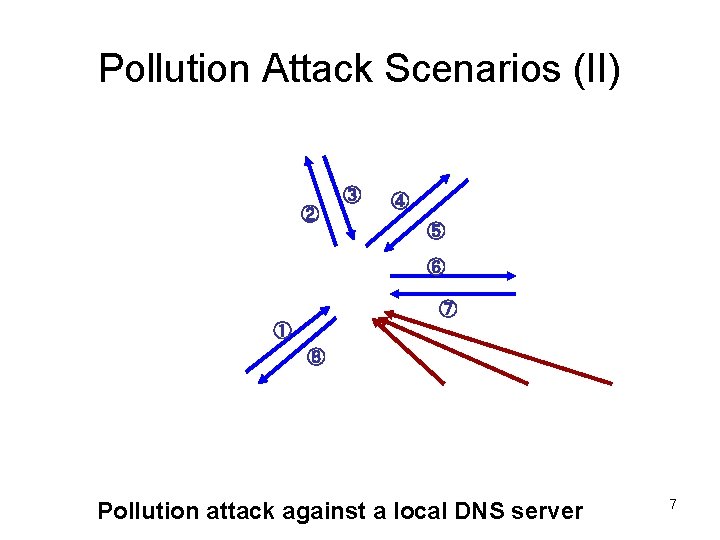
Pollution Attack: Locality Disruption Before attack After attack Popular files …. . . . Cache New unpopular files Cache • Goal: degrade cache efficiency by ruining its file locality • Activities: continuously generate requests for new unpopular files 8
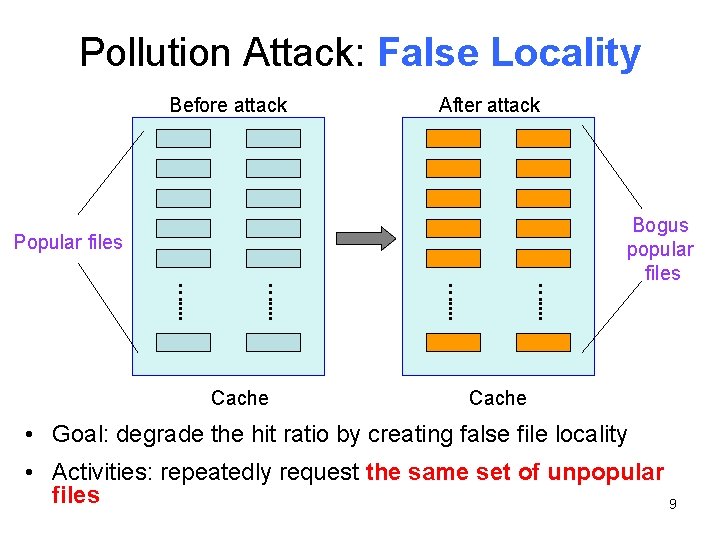
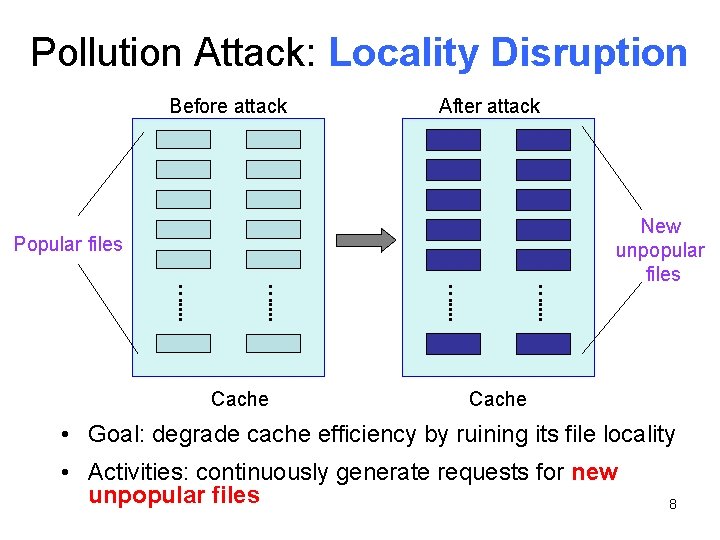
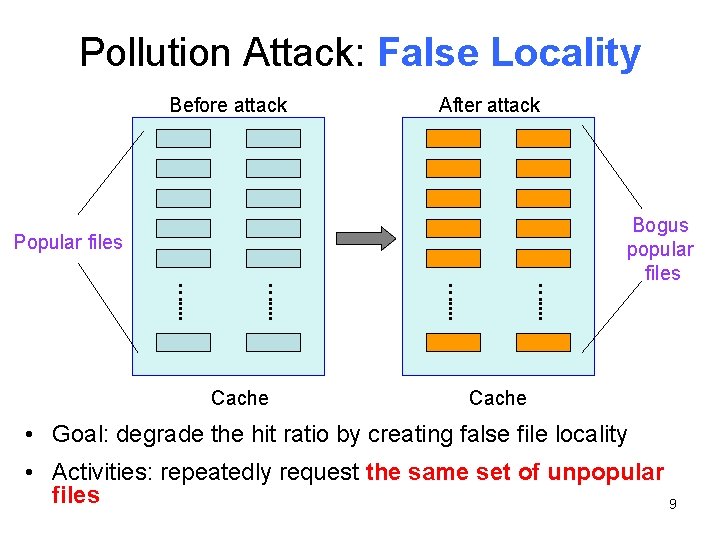
Pollution Attack: False Locality Before attack After attack Popular files …. . . . Cache Bogus popular files Cache • Goal: degrade the hit ratio by creating false file locality • Activities: repeatedly request the same set of unpopular files 9
Outline • • Motivation Pollution Attacks Evaluation of Pollution Effects Counter-Pollution Techniques & Evaluation • Conclusion 10
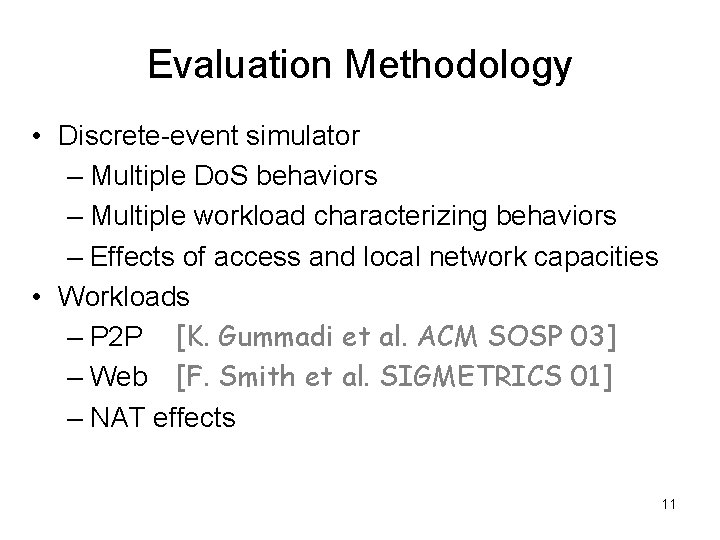
Evaluation Methodology • Discrete-event simulator – Multiple Do. S behaviors – Multiple workload characterizing behaviors – Effects of access and local network capacities • Workloads – P 2 P [K. Gummadi et al. ACM SOSP 03] – Web [F. Smith et al. SIGMETRICS 01] – NAT effects 11
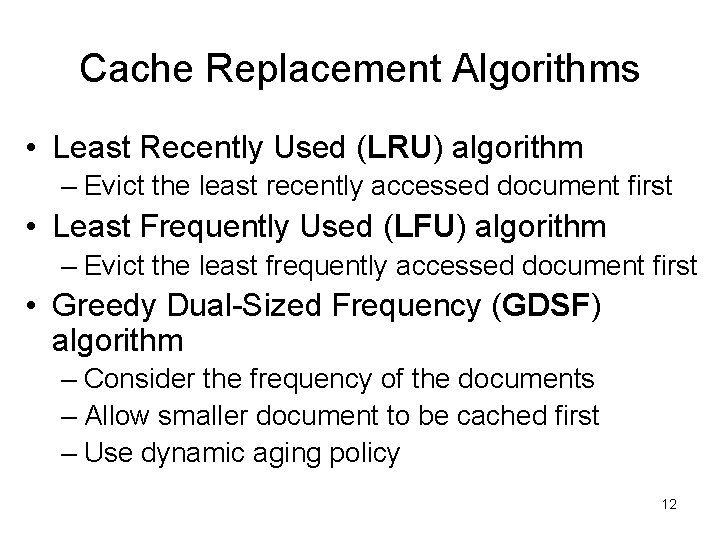
Cache Replacement Algorithms • Least Recently Used (LRU) algorithm – Evict the least recently accessed document first • Least Frequently Used (LFU) algorithm – Evict the least frequently accessed document first • Greedy Dual-Sized Frequency (GDSF) algorithm – Consider the frequency of the documents – Allow smaller document to be cached first – Use dynamic aging policy 12
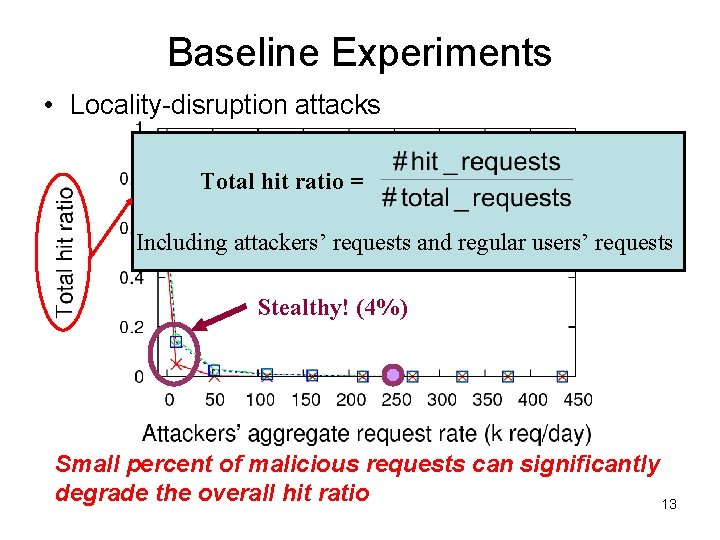
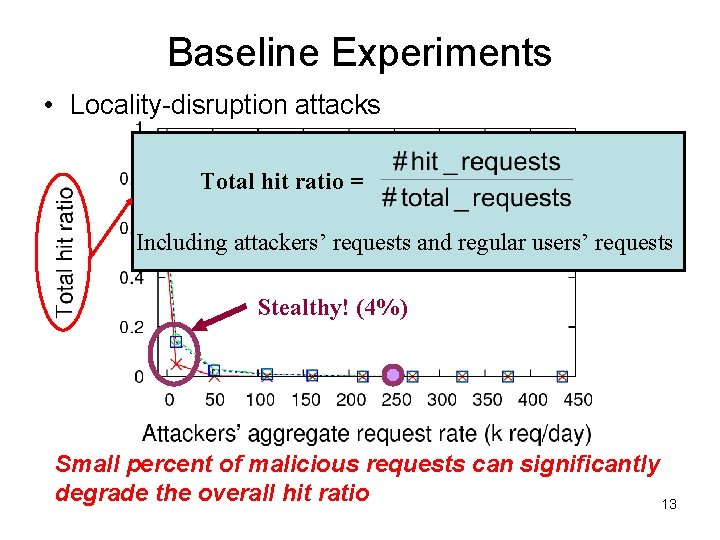
Baseline Experiments • Locality-disruption attacks Total hit ratio = Including attackers’ requests and regular users’ requests Stealthy! (4%) Small percent of malicious requests can significantly degrade the overall hit ratio 13
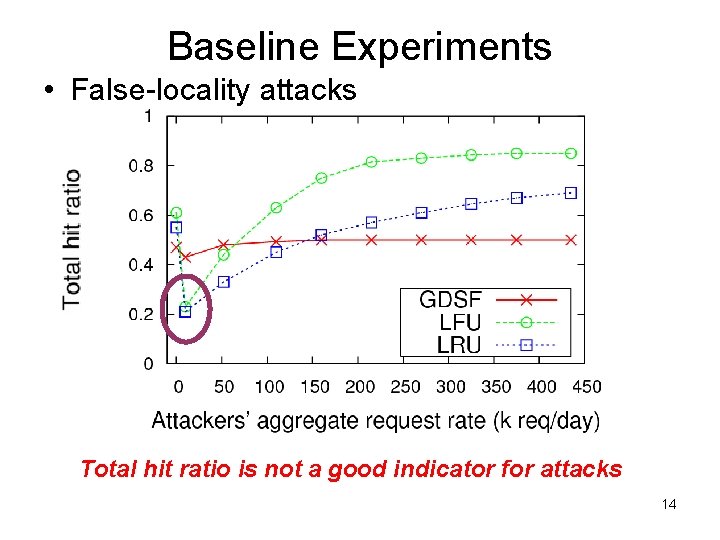
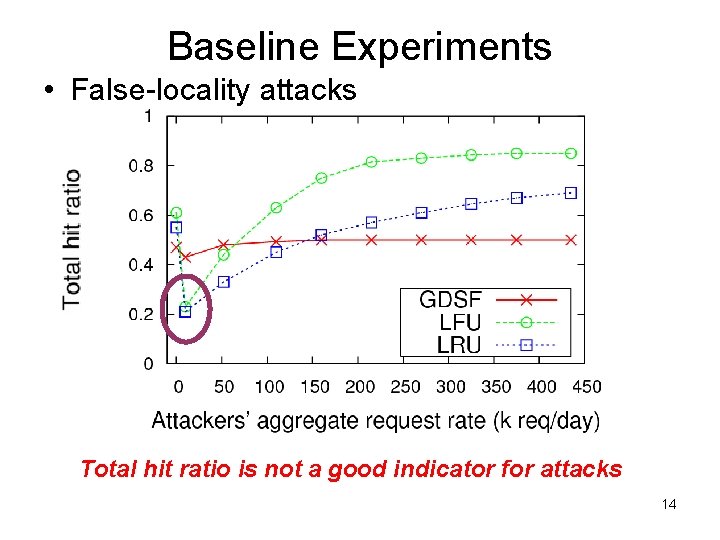
Baseline Experiments • False-locality attacks Total hit ratio is not a good indicator for attacks 14
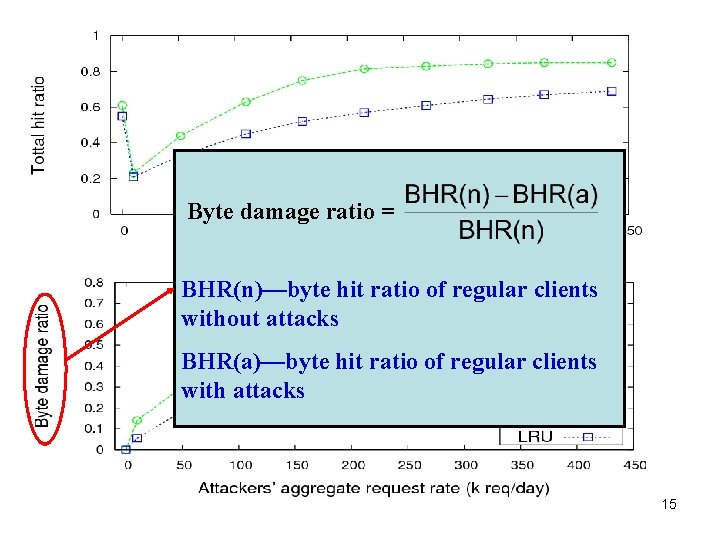
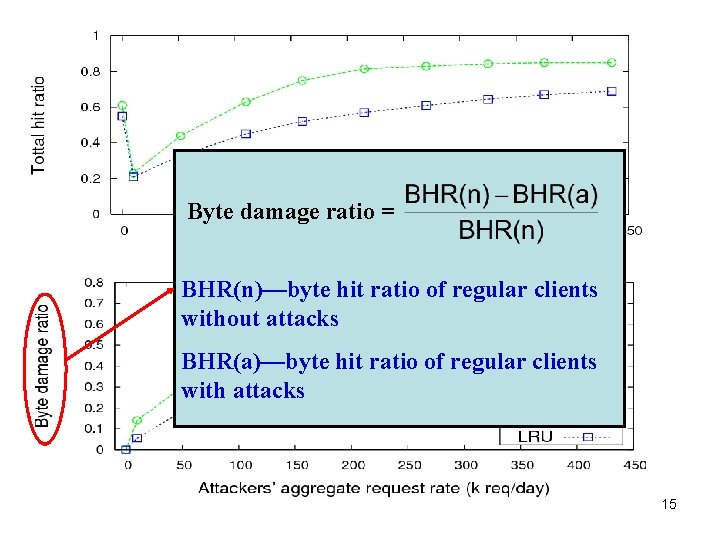
Byte damage ratio = BHR(n)—byte hit ratio of regular clients without attacks BHR(a)—byte hit ratio of regular clients with attacks 15
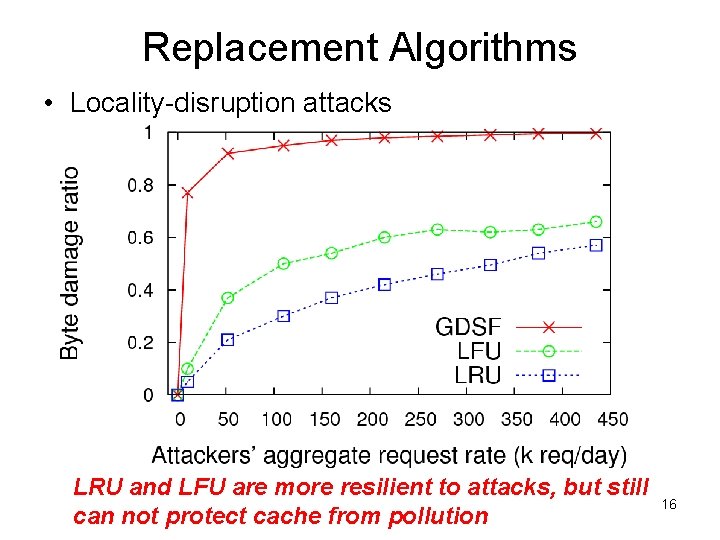
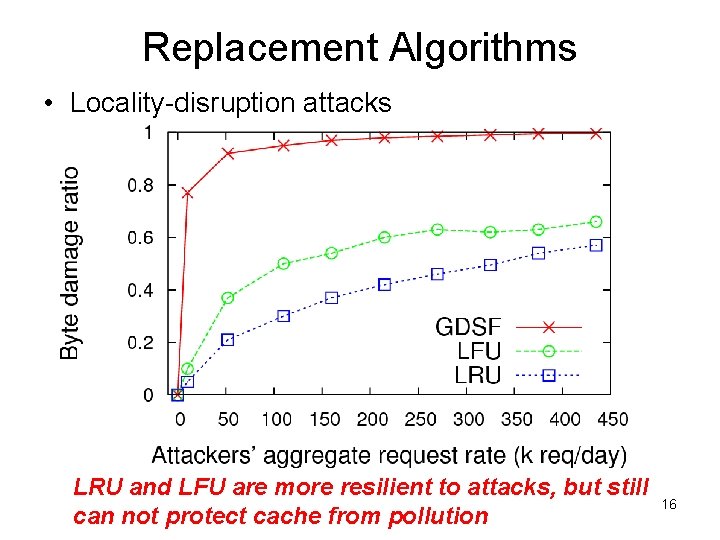
Replacement Algorithms • Locality-disruption attacks LRU and LFU are more resilient to attacks, but still can not protect cache from pollution 16
Outline • • Motivation Pollution Attacks Evaluation of Pollution Effects Counter-Pollution Techniques & Evaluation • Conclusion 17
Detecting Locality Disruption Attacks • Observations: – Low total hit ratio – Short average life-time of all cached files • Design: – Detection: compute the average durations for all files in the cache – Mitigation: recognize the attackers 18
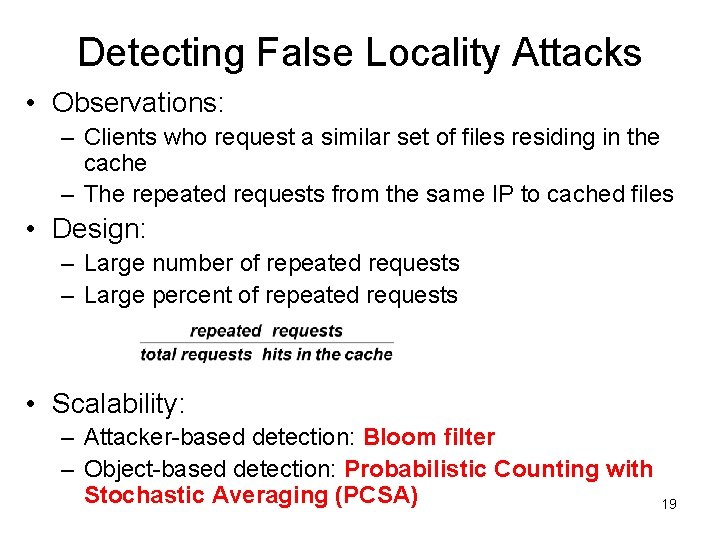
Detecting False Locality Attacks • Observations: – Clients who request a similar set of files residing in the cache – The repeated requests from the same IP to cached files • Design: – Large number of repeated requests – Large percent of repeated requests • Scalability: – Attacker-based detection: Bloom filter – Object-based detection: Probabilistic Counting with Stochastic Averaging (PCSA) 19
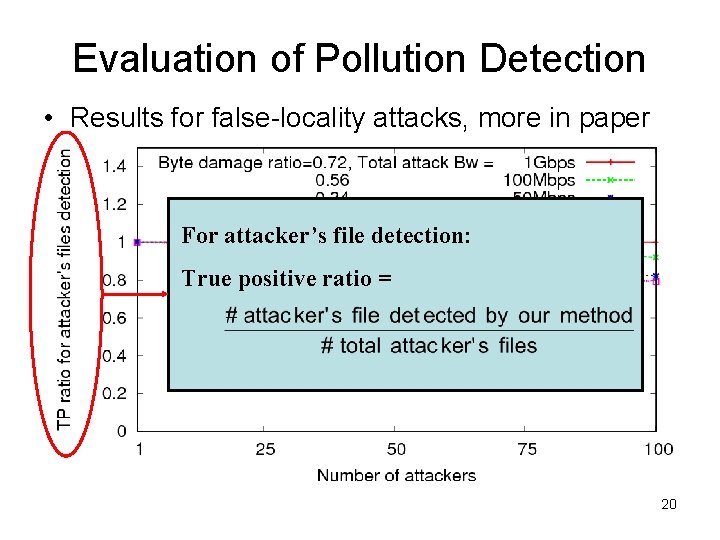
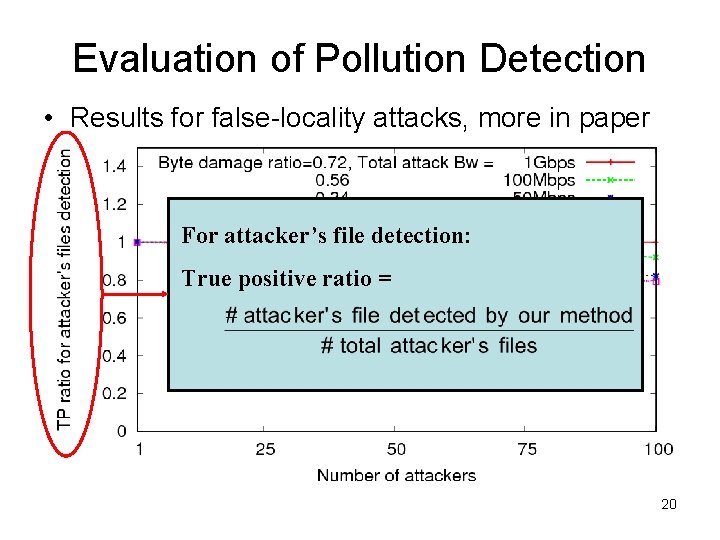
Evaluation of Pollution Detection • Results for false-locality attacks, more in paper For attacker’s file detection: True positive ratio = 20
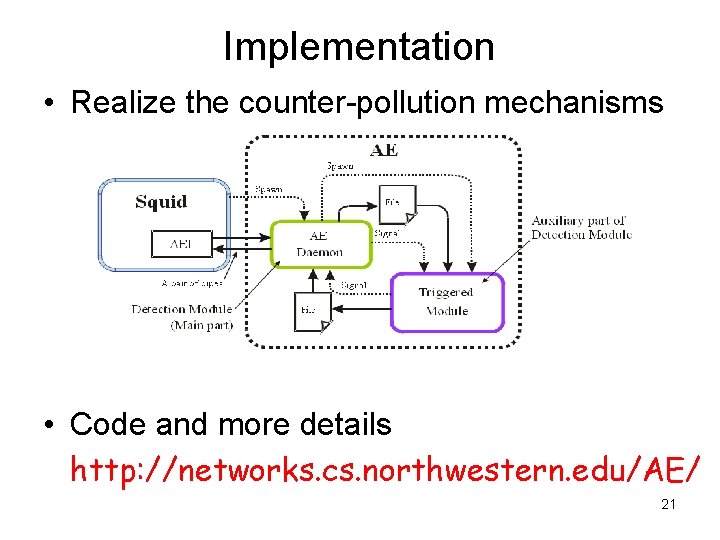
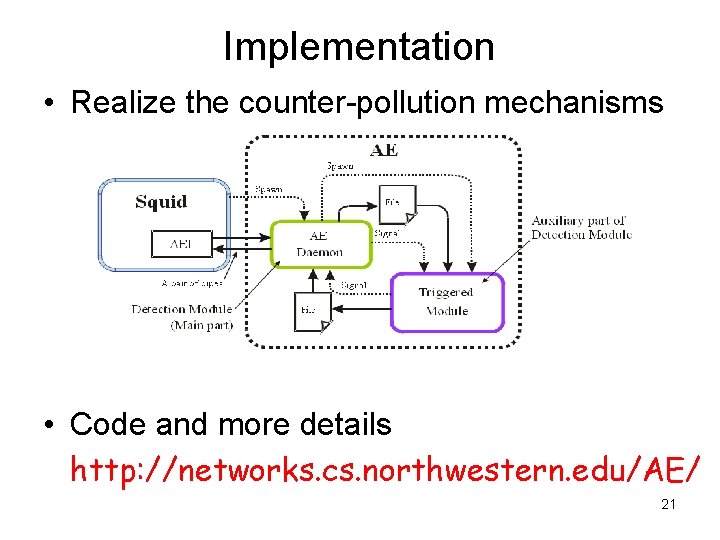
Implementation • Realize the counter-pollution mechanisms • Code and more details http: //networks. cs. northwestern. edu/AE/ 21
Conclusions • Propose and evaluate two classes of attacks: locality-disruption and falselocality attacks • Show that pollution attacks are stealthy, but powerful, and different replacement algorithms have different resiliency • Propose and evaluate a set of scalable and effective counter-pollution mechanisms 22
Thank You ! Questions? 23