Image Selfrecovery with Watermark Selfembedding Source Signal Processing
Image Self-recovery with Watermark Self-embedding Source: Signal Processing: Image Communication, Vol. 65, pp. 11 -25, 2018 Author: Wei-Liang Tai and Zi-Jun Liao Speaker: Su Guodong Date: 2019/09/12 1
Outline • Introduction • Related works • Proposed scheme • Experiments • Conclusions 2

Introduction Original image Reconstruct image Similar Embedding watermark Watermarked image Detection and recovery Tampered image 3
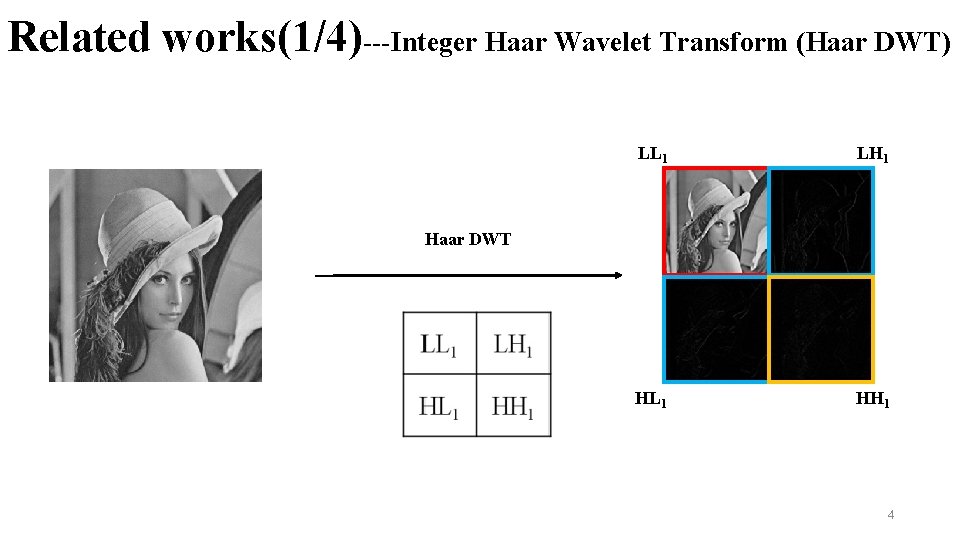
Related works(1/4)---Integer Haar Wavelet Transform (Haar DWT) LL 1 LH 1 HL 1 HH 1 Haar DWT 4
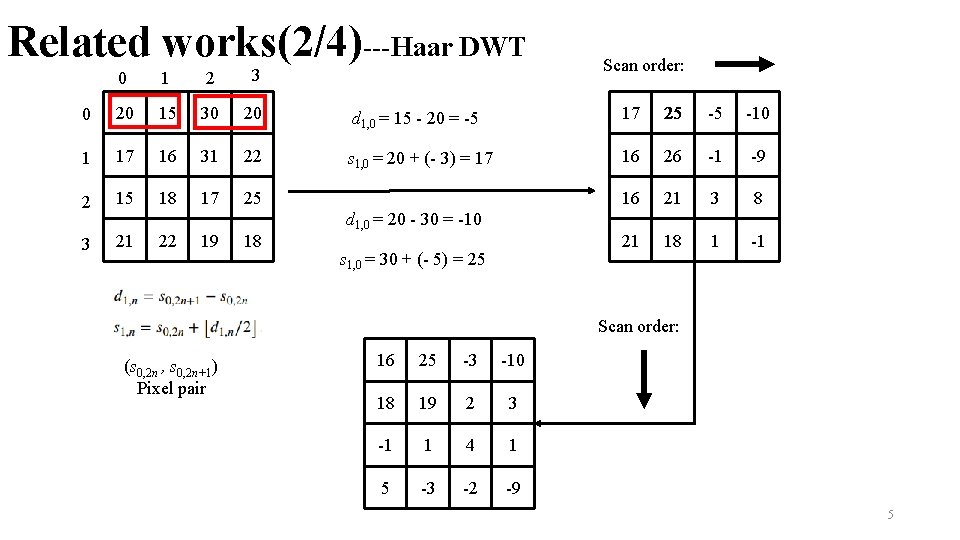
Related works(2/4)---Haar DWT Scan order: 1 2 3 20 15 30 20 d 1, 0 = 15 - 20 = -5 17 25 -5 -10 1 17 16 31 22 s 1, 0 = 20 + (- 3) = 17 16 26 -1 -9 2 15 18 17 25 16 21 3 8 3 21 21 18 1 -1 0 0 22 19 18 d 1, 0 = 20 - 30 = -10 s 1, 0 = 30 + (- 5) = 25 Scan order: (s 0, 2 n , s 0, 2 n+1) Pixel pair 16 25 -3 -10 18 19 2 3 -1 1 4 1 5 -3 -2 -9 5
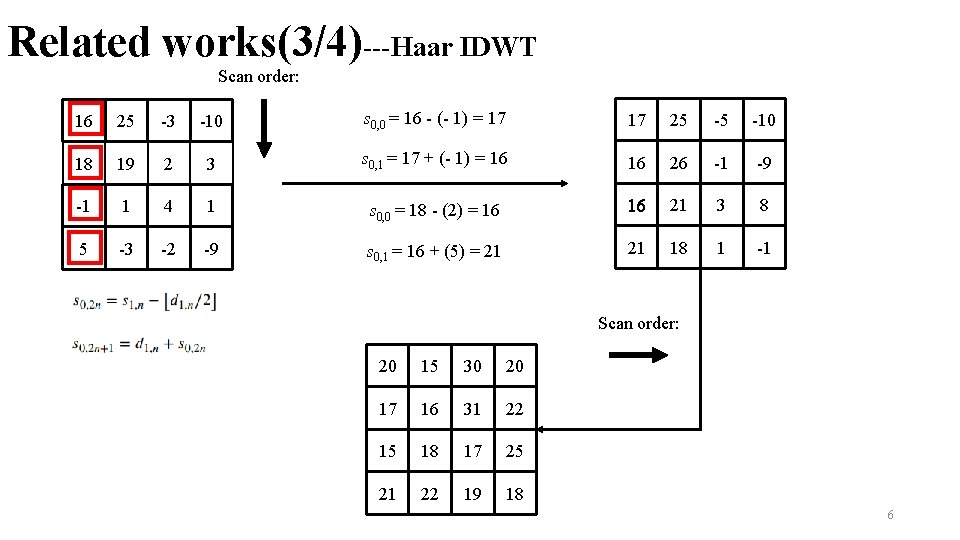
Related works(3/4)---Haar IDWT Scan order: 16 25 -3 -10 s 0, 0 = 16 - (- 1) = 17 17 25 -5 -10 18 19 2 3 s 0, 1 = 17 + (- 1) = 16 16 26 -1 -9 -1 1 4 1 s 0, 0 = 18 - (2) = 16 16 21 3 8 5 -3 -2 -9 s 0, 1 = 16 + (5) = 21 21 18 1 -1 Scan order: 20 15 30 20 17 16 31 22 15 18 17 25 21 22 19 18 6
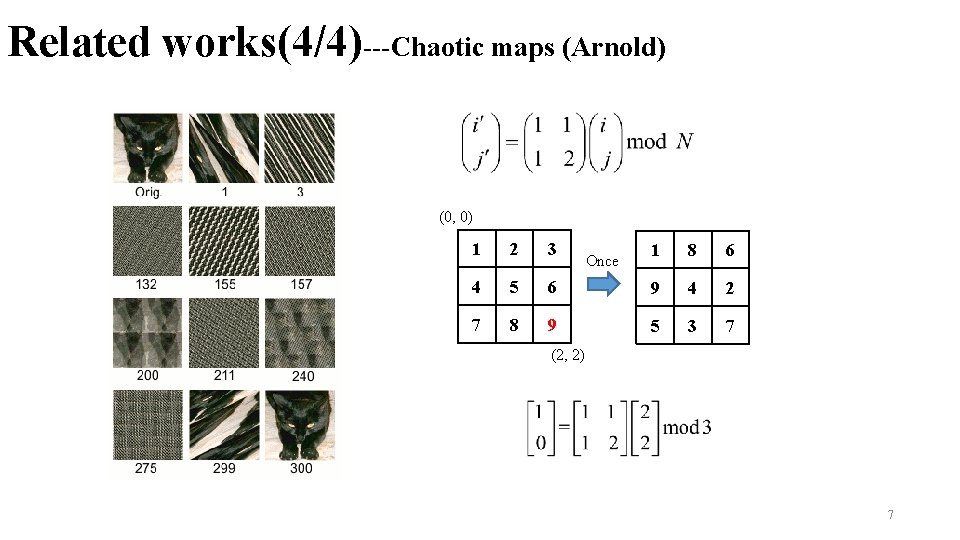
Related works(4/4)---Chaotic maps (Arnold) (0, 0) 1 2 3 4 5 7 8 1 8 6 6 9 4 2 9 5 3 7 Once (2, 2) 7
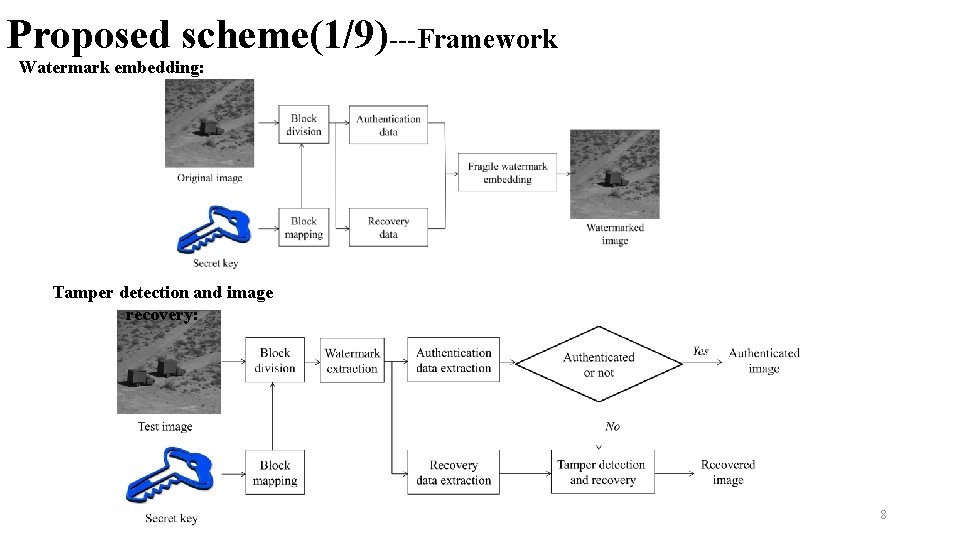
Proposed scheme(1/9)---Framework Watermark embedding: Tamper detection and image recovery: 8
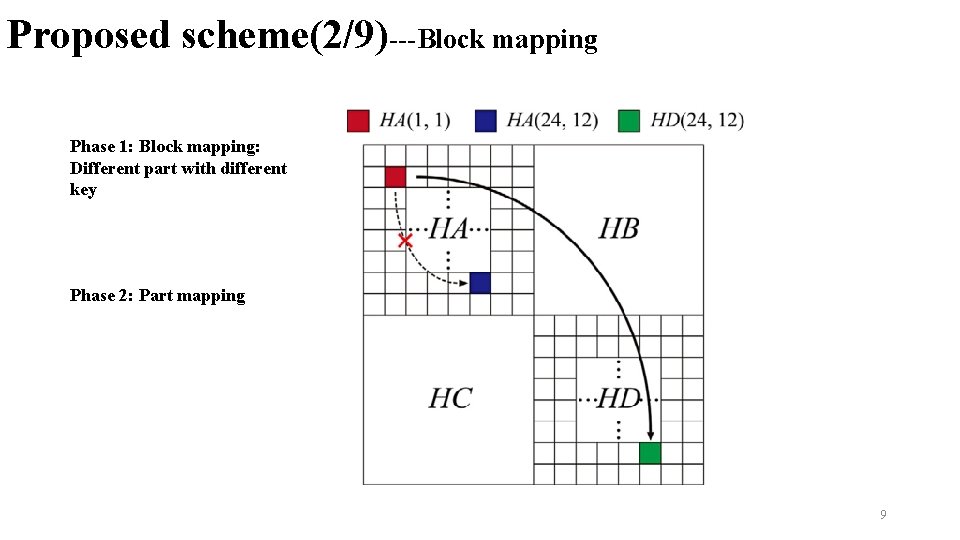
Proposed scheme(2/9)---Block mapping Phase 1: Block mapping: Different part with different key Phase 2: Part mapping 9
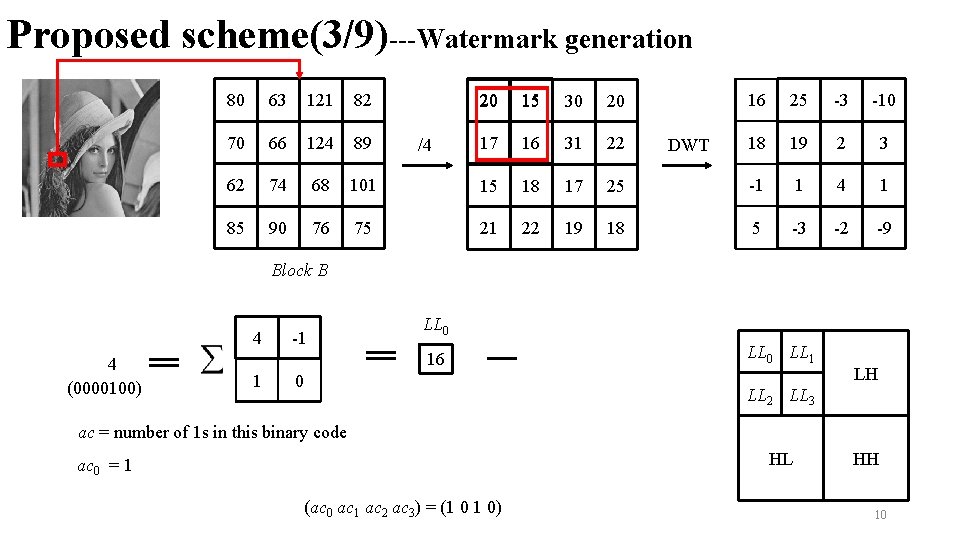
Proposed scheme(3/9)---Watermark generation 80 63 121 82 20 15 30 20 70 66 124 89 17 16 31 22 62 74 68 101 15 18 17 85 90 76 75 21 22 19 /4 16 25 -3 -10 18 19 2 3 25 -1 1 4 1 18 5 -3 -2 -9 DWT Block B 4 4 (0000100) -1 LL 0 16 1 0 LL 1 LH LL 2 LL 3 ac = number of 1 s in this binary code HL ac 0 = 1 (ac 0 ac 1 ac 2 ac 3) = (1 0 1 0) HH 10
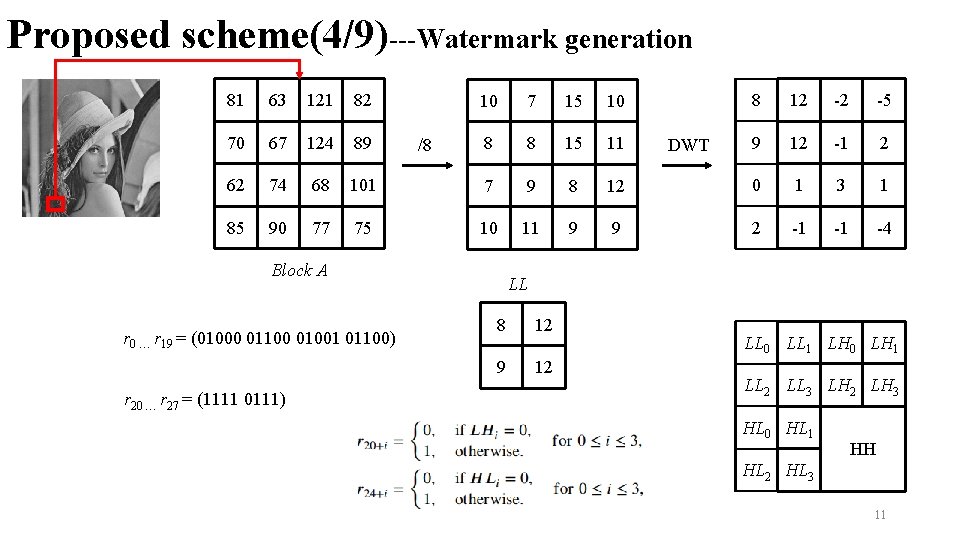
Proposed scheme(4/9)---Watermark generation 81 63 121 82 70 67 124 89 62 74 68 85 90 77 12 -2 -5 9 12 -1 2 12 0 1 3 1 9 2 -1 -1 -4 7 15 10 8 8 15 11 101 7 9 8 75 10 11 9 /8 Block A r 0 … r 19 = (01000 01100 01001 01100) r 20 … r 27 = (1111 0111) 8 10 DWT LL 8 12 9 12 LL 0 LL 1 LH 0 LH 1 LL 2 LL 3 LH 2 LH 3 HL 0 HL 1 HH HL 2 HL 3 11
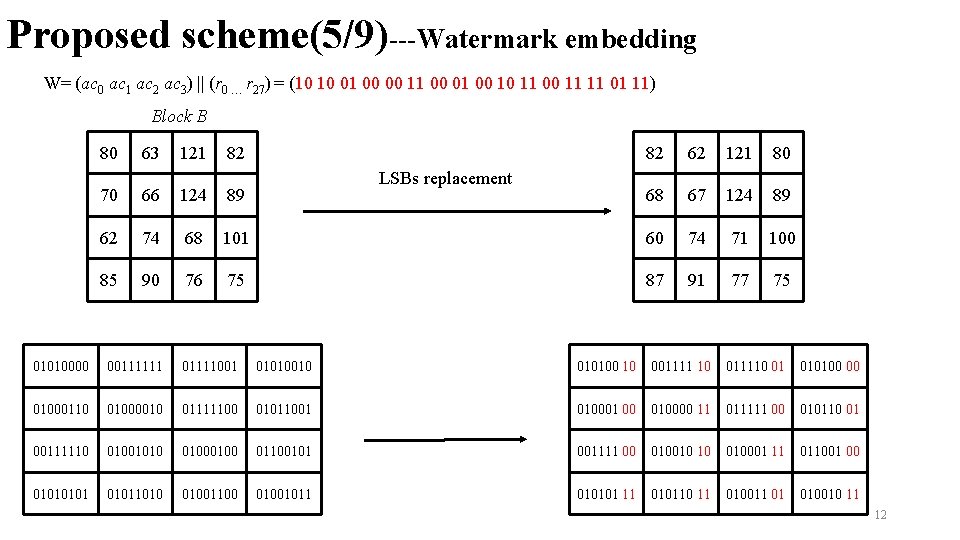
Proposed scheme(5/9)---Watermark embedding W= (ac 0 ac 1 ac 2 ac 3) || (r 0 … r 27) = (10 10 01 00 00 11 00 01 00 10 11 00 11 11 01 11) Block B 80 63 121 82 LSBs replacement 82 62 121 80 68 67 124 89 70 66 124 89 62 74 68 101 60 74 71 100 85 90 76 75 87 91 77 75 01010000 00111111 01111001 01010010 010100 10 001111 10 011110 01 010100 00 01000110 01000010 01111100 01011001 010001 00 010000 11 011111 00 010110 01 00111110 01001010 0100 01100101 001111 00 010010 10 010001 11 011001 00 01011010 01001100 01001011 010101 11 010110 11 010011 01 010010 11 12
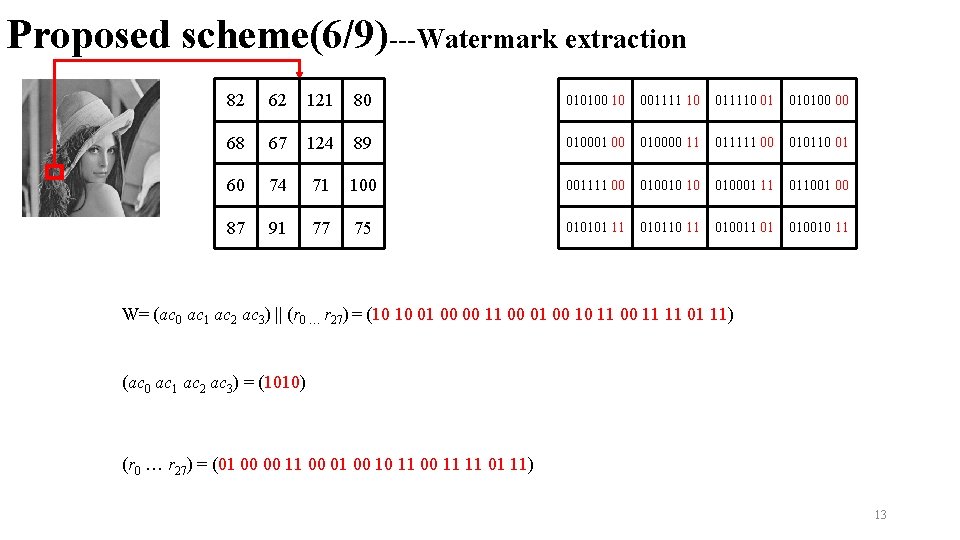
Proposed scheme(6/9)---Watermark extraction 82 62 121 80 010100 10 001111 10 011110 01 010100 00 68 67 124 89 010001 00 010000 11 011111 00 010110 01 60 74 71 100 001111 00 010010 10 010001 11 011001 00 87 91 77 75 010101 11 010110 11 010011 01 010010 11 W= (ac 0 ac 1 ac 2 ac 3) || (r 0 … r 27) = (10 10 01 00 00 11 00 01 00 10 11 00 11 11 01 11) (ac 0 ac 1 ac 2 ac 3) = (1010) (r 0 … r 27) = (01 00 00 11 00 01 00 10 11 00 11 11 01 11) 13
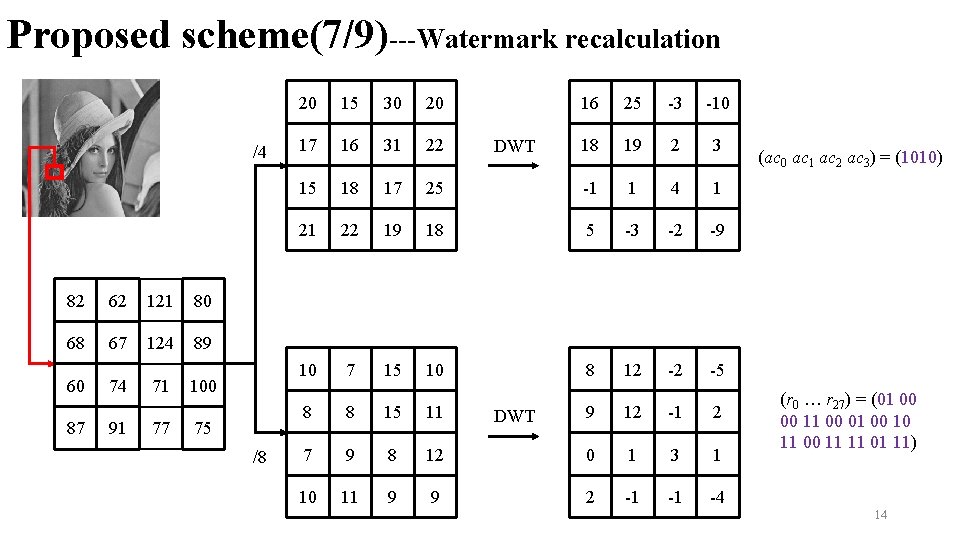
Proposed scheme(7/9)---Watermark recalculation /4 82 62 121 80 68 67 124 89 60 87 74 91 71 77 100 75 /8 20 15 30 20 16 25 -3 -10 17 16 31 22 18 19 2 3 15 18 17 25 -1 1 4 1 21 22 19 18 5 -3 -2 -9 10 7 15 10 8 12 -2 -5 8 8 15 11 9 12 -1 2 7 9 8 12 0 1 3 1 10 11 9 9 2 -1 -1 -4 DWT (ac 0 ac 1 ac 2 ac 3) = (1010) (r 0 … r 27) = (01 00 00 11 00 01 00 10 11 00 11 11 01 11) 14
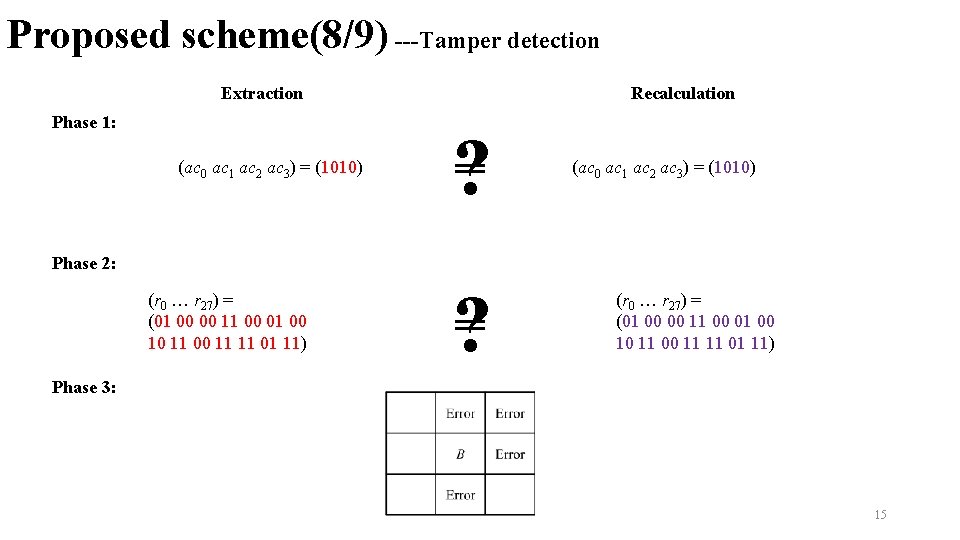
Proposed scheme(8/9) ---Tamper detection Extraction Phase 1: (ac 0 ac 1 ac 2 ac 3) = (1010) Recalculation ? (ac 0 ac 1 ac 2 ac 3) = (1010) Phase 2: (r 0 … r 27) = (01 00 00 11 00 01 00 10 11 00 11 11 01 11) ? (r 0 … r 27) = (01 00 00 11 00 01 00 10 11 00 11 11 01 11) Phase 3: 15
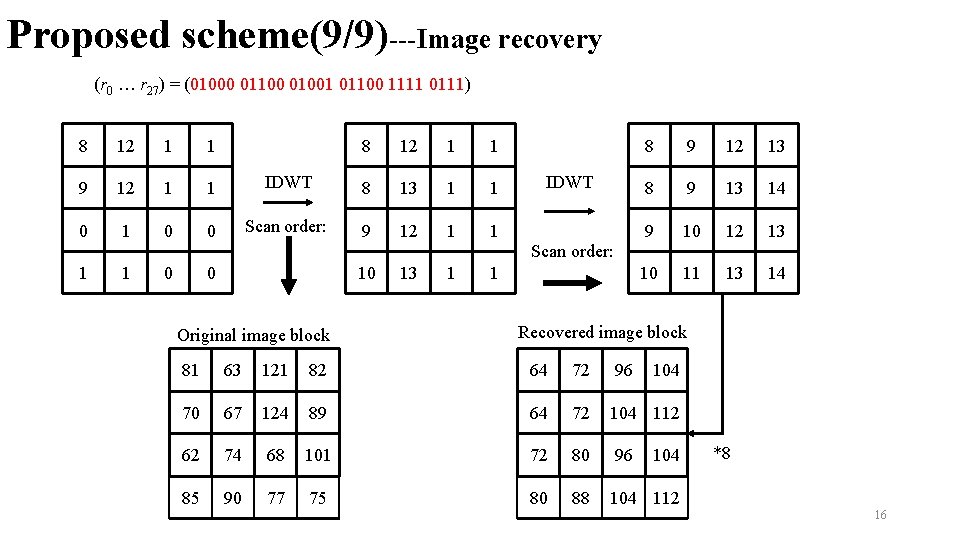
Proposed scheme(9/9)---Image recovery (r 0 … r 27) = (01000 01100 01001 01100 1111 0111) 8 12 1 1 9 12 1 1 0 0 8 12 1 1 IDWT 8 13 1 1 Scan order: 9 12 1 1 10 13 1 1 Original image block IDWT Scan order: 8 9 12 13 8 9 13 14 9 10 12 13 10 11 13 14 Recovered image block 81 63 121 82 64 72 96 104 70 67 124 89 64 72 104 112 62 74 68 101 72 80 96 85 90 77 75 80 88 104 112 104 *8 16
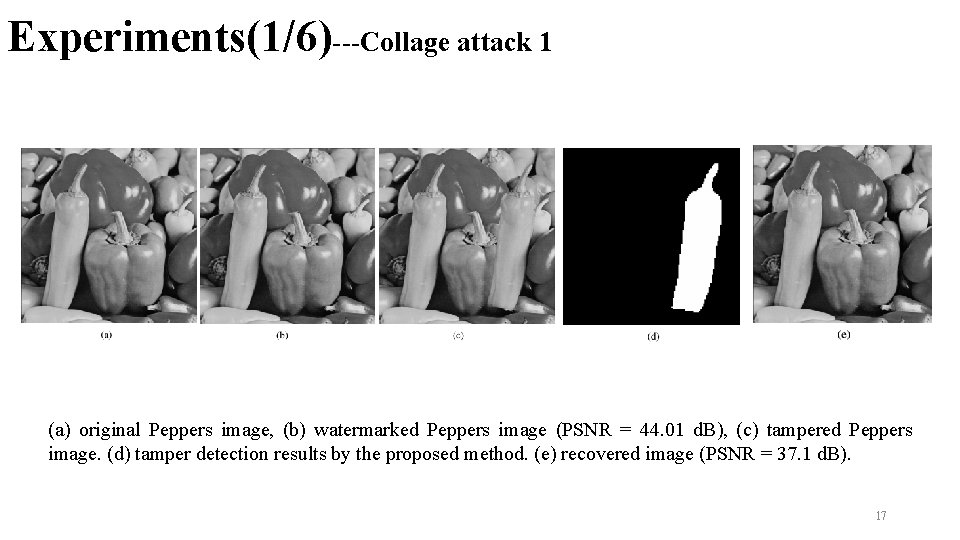
Experiments(1/6)---Collage attack 1 (a) original Peppers image, (b) watermarked Peppers image (PSNR = 44. 01 d. B), (c) tampered Peppers image. (d) tamper detection results by the proposed method. (e) recovered image (PSNR = 37. 1 d. B). 17
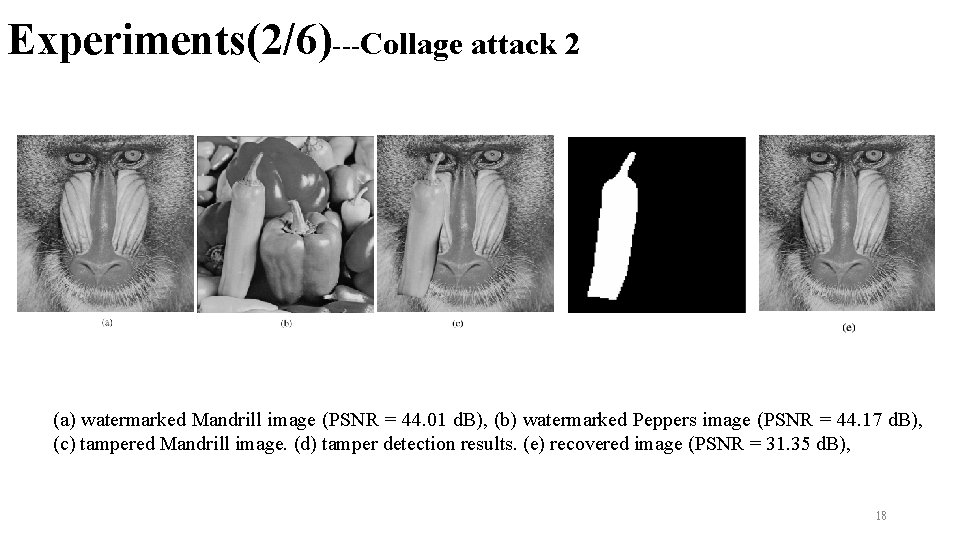
Experiments(2/6)---Collage attack 2 (a) watermarked Mandrill image (PSNR = 44. 01 d. B), (b) watermarked Peppers image (PSNR = 44. 17 d. B), (c) tampered Mandrill image. (d) tamper detection results. (e) recovered image (PSNR = 31. 35 d. B), 18
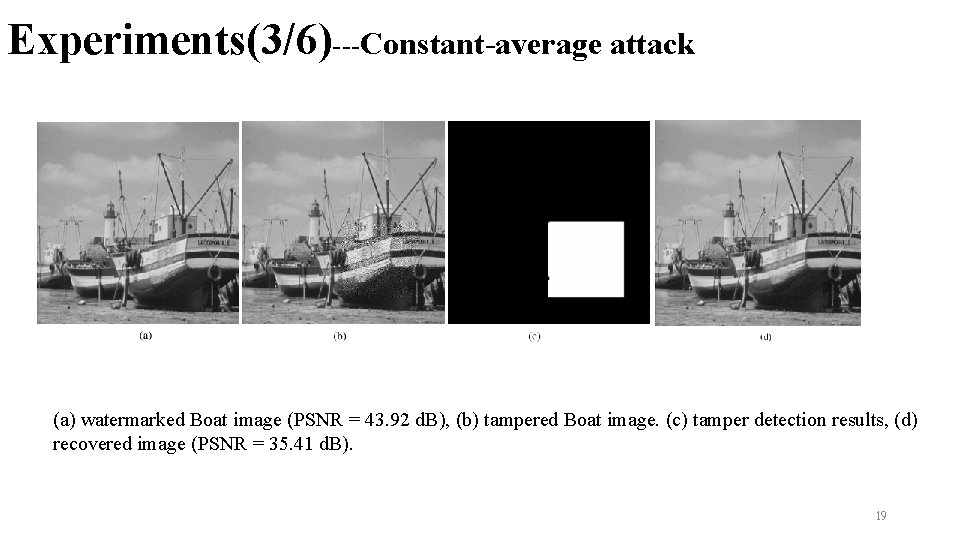
Experiments(3/6)---Constant-average attack (a) watermarked Boat image (PSNR = 43. 92 d. B), (b) tampered Boat image. (c) tamper detection results, (d) recovered image (PSNR = 35. 41 d. B). 19
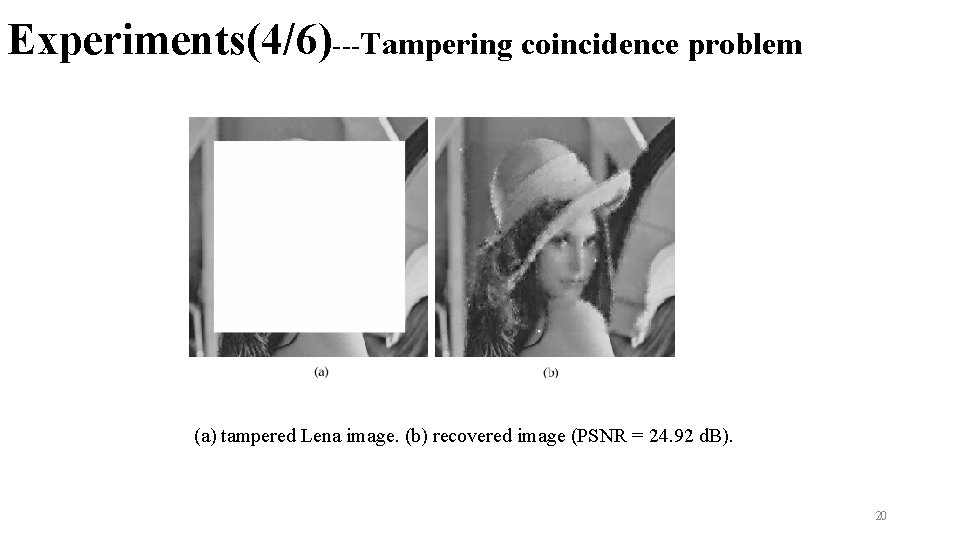
Experiments(4/6)---Tampering coincidence problem (a) tampered Lena image. (b) recovered image (PSNR = 24. 92 d. B). 20
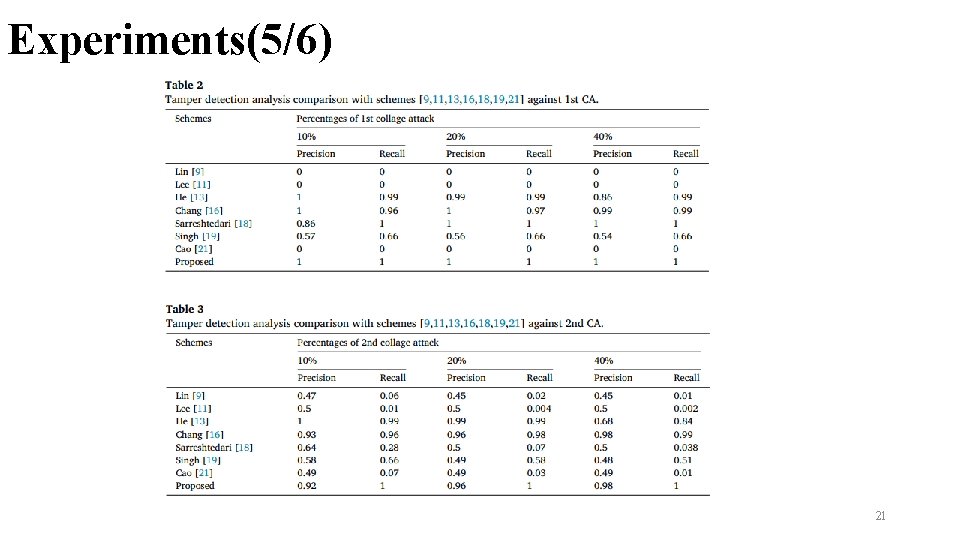
Experiments(5/6) 21

Experiments(6/6) 22
Conclusions ØPropose an hierarchical tamper detection algorithm enables the proposed scheme to effectively detect the tampered regions manipulated by collage attack and constant-average attack. ØUse the wavelet transform rather than the average is used as recovery data to reduce the smoothing blocking effect of recovered image ØAchieve high recovered image quality 23
Thanks! 24
- Slides: 24