Spatial Domain Image Watermarking Robust against Compression Filtering
Spatial Domain Image Watermarking Robust against Compression, Filtering, Cropping and Scaling By Sebé, Domingo-Ferrer, Herrera Information Security Dec 2000 Wollongong Austr. Electronic copyright protection schemes… have proven ineffective or insufficient in the last years. The recent failure of the DVD copy prevention is just another argument supporting the idea that electronic copyright protection should rather rely on copy detection techniques. Presented by Gene Rugg
Measure of a Watermark • Robustness * – Ability to resist image modification from typical image processing applications, difficult or impossible to remove without visiably degrading the original image • Capacity * – The amount of information embedded and later detectible by the proper authorities • Imperceptibility – The degree with which the original image is left unchanged.

Achievements of Watermarking • Difficult to remove – Fairly easy to do • Robust – Not easily done with current watermarks. Very fragile to many graphic attacks • Imperceptible • Readily detectible – Fairly easy to do
Robustness Sebe, Domingo and Herrera developed two algorithms that was more robust than most other watermarking techniques, based off ideas from “Didital watermarking robust against JPEG compression”, Lee Park and Zheng, 1999.
1: Crop-Proof Watermarking From the original take a JPEG copy, compressed to greater than the required resistance level eg 10%
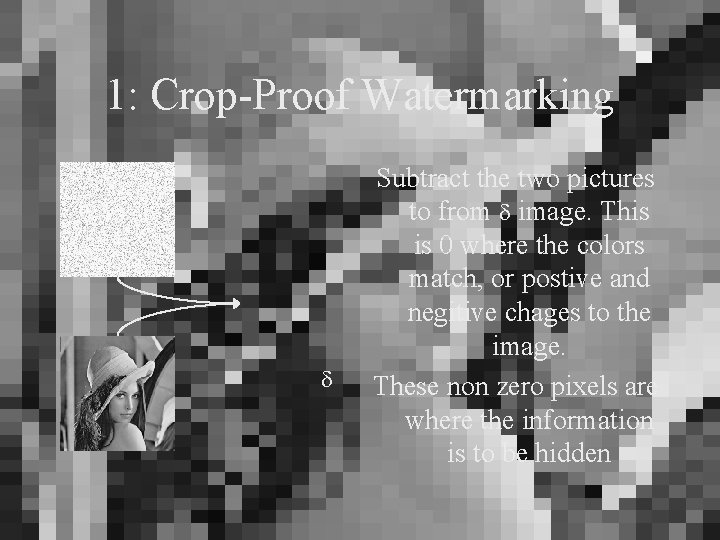
1: Crop-Proof Watermarking Subtract the two pictures to from image. This is 0 where the colors match, or postive and negitive chages to the image. These non zero pixels are where the information is to be hidden
1: Crop-Proof Watermarking • Take the binary watermark you wish to embed 10010110

1: Crop-Proof Watermarking • Encode with an Error Correcting Code (ECC) 100100111010
1: Crop-Proof Watermarking • Take a pseudo-random number, generated by a key only we know; k 100100111010 100101111101010010001010…
1: Crop-Proof Watermarking • Repeat watermark up to the number of bits in the image, ie w h pixels (3 w h colour) 100100111010100100111… 100101111101010010001010…
1: Crop-Proof Watermarking • XOR the bit strings. These represent when add or subtract the difference, the embedded string 100100111010100100111… 100101111101010010001010… S=0000010111100111101101…
1: Crop-Proof Watermarking • Use the string s to encode into the image Original Image

1: Crop-Proof Watermarking • Use the string s to encode into the image JPEG Approximation

1: Crop-Proof Watermarking • Use the string s to encode into the image • 0 subtract, 1 adds 0 1 0 0 0 1 Encoded Image
1: Crop-Proof Watermarking • If there is too much noise in the image, randomly choose pixels and shift the values towards the original image until the noise level is reduced.
1: Crop-Proof Retrieval • Restore test image to BMP form, and compress to original JPEG level, and recalculate the non zero pixel locations • Cycling the length of the watermark, compare the levels, and return 1: higher or 0: lower or #: undefined • XOR this result with the pseudorandom string. Recall the result at the position in the watermark, then ECC retrieve the message
1: Robustness Assessment Natively Robust Against: • Color quantization • All Low pass filtering • • – – Gaussian blur Median filter (2 x 2 3 x 3 4 x 4) Simple sharpening Laplacian removal, frequency mode JPEG compression higher than q Rotations of ±. 25 degrees Shearing of 1% Cropping attacks/removal of rows or columns, by shifting the image until relative position is correct

1: Robustness Re. Assessment Crop-Proof is better, as multiple watermarks can be applied, and still all can be detected, and recovered. Crop-Proof is worse against: • Scale attacks of a small degree or more • Minor rotations • Random transformations and filters

2: Scale-Proof Watermarking d From the original, calculate its ‘darkness’ if its color is <70, and also by averaging the pixels around it, giving a maximised normalized number in a range of 1 to 4. This is Vj
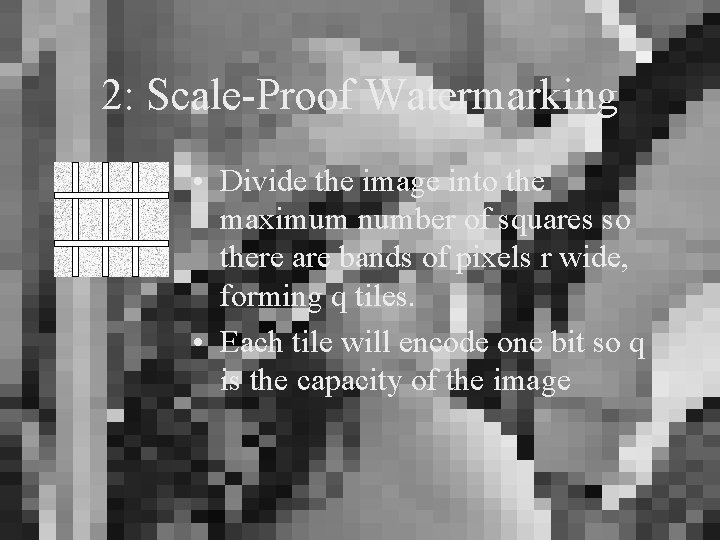
2: Scale-Proof Watermarking • Divide the image into the maximum number of squares so there are bands of pixels r wide, forming q tiles. • Each tile will encode one bit so q is the capacity of the image
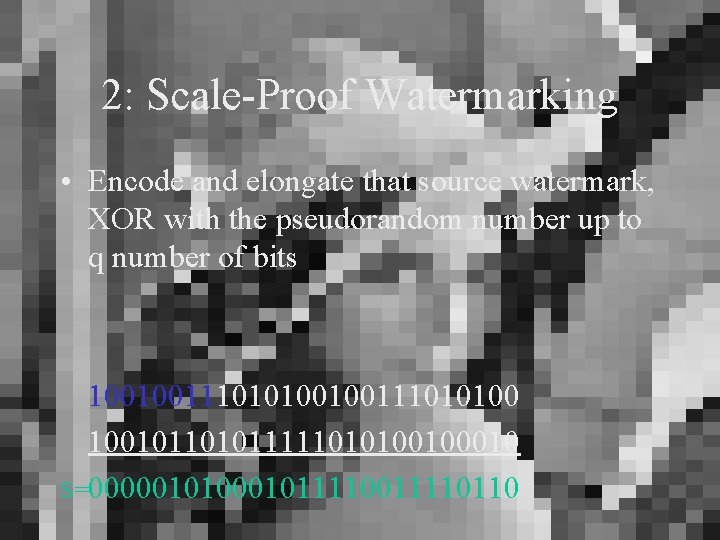
2: Scale-Proof Watermarking • Encode and elongate that source watermark, XOR with the pseudorandom number up to q number of bits 100100111010100 100101111101010010 S=000001011110011110110

2: Scale-Proof Watermarking • For all embeddable pixels in each tile, apply Vj to each difference as before • 0; new pixel is old color minus Vj • 1; new pixel is old color plus Vj
2: Scale-Proof Retrieval • From the given image, estimate the tile spacing, and number of tiles • Within each tile, locate and compare each pixel relative with the original. If the difference is greater, record a 1 for that tile, or if less, a 0. XOR with the pseudorandom number • Tally on each tile to see if there are more 1 s or 0 s • Decode via ECC
2: Robustness Assessment Natively Robust Against: • Color quantization • Most Low pass filtering • • • – – Gaussian blur Median filter (2 x 2 3 x 3) Simple sharpening Laplacian removal, frequency mode JPEG compression Rotations (with/without scaling) of ±. 25 degrees Shearing of 1% Removal of rows or columns Scaling Attacks
2: Robustness Re. Assessment Scale-Proof is better handling large compression and scaling attacks Scale-Proof is worse against: • Crop attacks of a small degree or more • Minor rotations

Conclusions • More work is needed in the field of spatialdomain image watermarking • Suggested a combination of the two techniques • Obvious that image manipulation to scale and rotate back to ‘normal’ possible and helps algorithms.
Thoughts • Is 0. 25° enough for most image manipulators? • Is computation time as important as a concise algorithm? • Did you understand, and is it useful? Acknowledgments: Sebé, Domingo-Ferrer, Herrera * Alecander Huber, informatik. tu-meunchen. de/~hubera/watermarking
- Slides: 27