Identity Based Encryption Debdeep Mukhopadhyay Associate Professor Dept
Identity Based Encryption Debdeep Mukhopadhyay Associate Professor Dept of Computer Sc and Engg, IIT Kharagpur
Public Key Setting • Alice and Bob might not have a prior shared secret. • Each participant has a pair of public and private key for certain pre-specified cryptosystem or signature scheme. • It is always necessary to authenticate the public keys of other people in the network. • This requires some kind of Public Key Infrastructure (PKI) • We assume there is a Trusted Authoruty (TA) or Certification Authority (CA) who signs the public keys of all people in the network. • The public verification key, ver. TA of the TA is known to all.
Certificates • A certificate for someone in the network will consist of: • some identifying information for a person (eg, name, email address, etc. ), • their public keys, and • the signature of the TA on that information. • The certificate allows network users to verify the authenticity of each other’s keys. • How does Alice obtain a certificate from the TA which contains a copy of Alice’s public verification key for a signature scheme?
A Protocol to Issue a Certificate to Alice • The TA establishes Alice’s identity by means of conventional forms of identification like birth certificate, passport etc. Then the TA forms a string ID(Alice), which contains Alice’s identification. • A private signing key for Alice, sign. Alice, and a corresponding public verification key ver. Alice are determined. • The TA determines its signature: • s=sig. TA(ID(Alice)||ver. Alice) on Alice’s identity string and verification key. The certificate Cert(Alice)=(ID(Alice)||ver. Alice||s) is given to Alice, along with Alice’s private key, sig. Alice.
Verification of the Public Key • Any one who has the TA’s verification key, ver. TA can verify anyone else’s certificate. • Suppose, Bob wants to be sure that Alice’s public key is authentic: • Alice gives her certificate to Bob. • Bob can then verify the signature of the TA by checking: ver. TA(ID(Alice)||ver. Alice||s)=true Note: • The purpose of verifying a certificate is to authenticate the public key. • Verifying the signature allows someone to verify that the certificate was issued by the CA. • Having verified the signature, a user would then believe the information provided the CA can be trusted of verifying the information before signing.
X. 509 v 3 • Version number • Serial number • Signature algorithm ID • Issuer name • Validity period • Subject name (ie. Signature owner) • Public key of owner • Signature of CA on all the fields
Problems of PKI • Many difficulties associated with practical large scale deployments of PKI • Who is responsible for its deployment, maintenance, and regulations? • Govt or Industry? • What standards should be used? : certificate formats, cryptographic algorithms, revocation, etc. • Lack of PKI compatible applications has slowed down its deployment.
Alternative to PKI • Identity Based Encryption (IBE): • Refers to Public Key Cryptography where the values of the public key are computed from the identity of the owners. • Renders certificates unnecessary, and hence the need for an infrastructure to verify public keys is avoided.
ID-based Encryption • Public Key for a user U is obtained by applying a public hash function h to the user’s identity string, ID(U). • The corresponding private key would be generated by a central trusted authority (denoted by TA). • The private key would then be supplied to the user U after that user proves his or her identity to the TA. • Issuance of private key by the TA replaces the issuing of a certificate. • The resulting private and public keys are used in an encryption scheme, signature scheme, or other scheme. • The scheme uses some fixed public parameters, incluiding a certain master key.
IBE and PKI • IBE removes the need for certificates. • However, still need a convenient and reliable method for associating an identity string with a person. • However IBE alleviates many of the problems of PKI. • Note that unlike PKI, in IBE any user, say Bob, can encrypt a message for Alice (using the IDA and the public key of the TA) before Alice has received her private key from the TA. • Also Bob could include in the IDA any set of conditions that should be met before the TA issues the private key. • Could include credit ratings, employment status, minimum age requirement, etc. • Date in the IDA to solve the key revocation problem (ie. Private key will be issued only if it has not been revoked).
Designing an IBE • Can a Public Key Cryptosystem be converted to an IBE? • Let us try with RSA. • The TA chooses the RSA modulus n=pq, as the public master key. • The factors p and q are known only to the TA, and work as the master private key. • How does a user U obtain its key pair?
RSA converted to IBE? • Public Key of a user U is an encryption exponent and a private key is a decryption exponent. • However, once U has a public key and private key pair, it can factor n. • Once U knows the private master key, it can impersonate the TA. • Can compute any one else’s private key. • The IBE fails! • Thus IBE necessitates that a user’s public key and private key cannot be used to determine the private master key of the TA.
Components of an IBE • System Parameters: • Master key generation: The TA generates the master public key Mpub and a corresponding master private key Mpriv. Master key, M=(Mpub, Mpriv). • A hash function h is also public.
User Key Generation • When a user U identifies himself to the TA, the TA uses a function extract to compute U’s private key Kupriv: Kupriv=extract(M, Kupub), where U’s public key is Kupub=h(ID(U)). User U’s key is KU=(Kupub, Kupriv).
Encryption and Decryption • Encryption: • User U’s public key Kupub defines a public encryption rule, e. KU, that can be used by anyone to encrypt messages sent to U. • Decryption: • U’s private key Kupriv defines a private decryption rule d. KU, that U will use to decrypt messages he receives.
The Cocks IBE • Based on certain properties of the Jacobi symbols. • It uses certain number theoretic properties of quadratic residues.
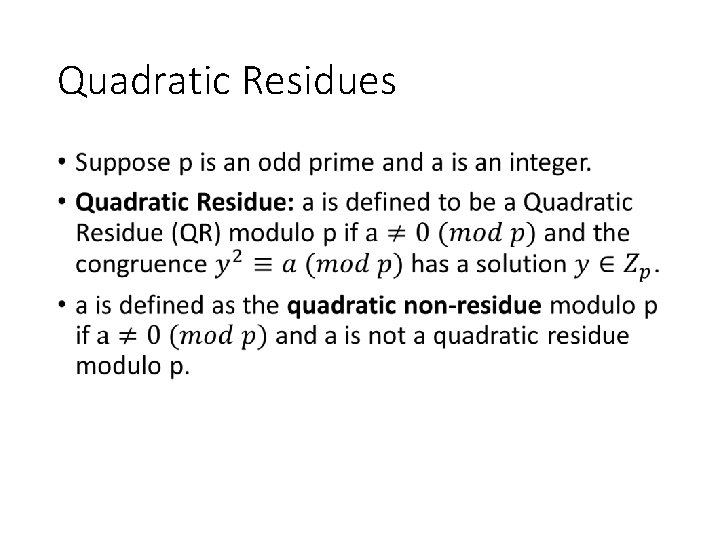
Quadratic Residues •
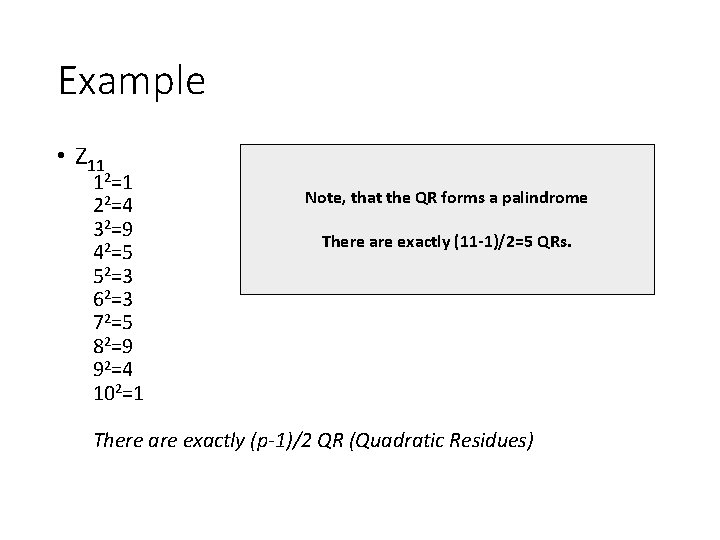
Example • Z 11 12=1 22=4 32=9 42=5 52=3 62=3 72=5 82=9 92=4 102=1 Note, that the QR forms a palindrome There are exactly (11 -1)/2=5 QRs. There are exactly (p-1)/2 QR (Quadratic Residues)
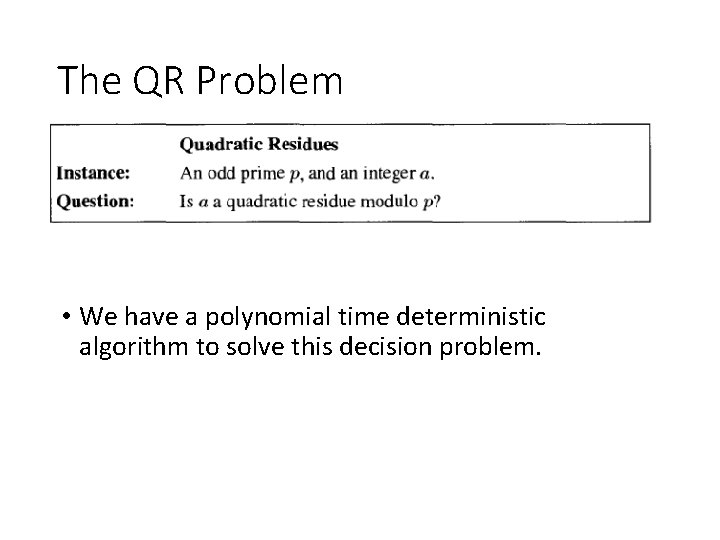
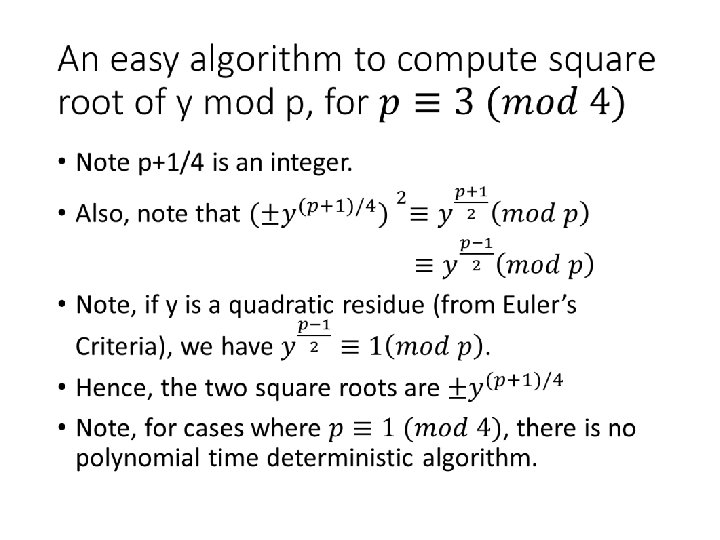
The QR Problem • We have a polynomial time deterministic algorithm to solve this decision problem.
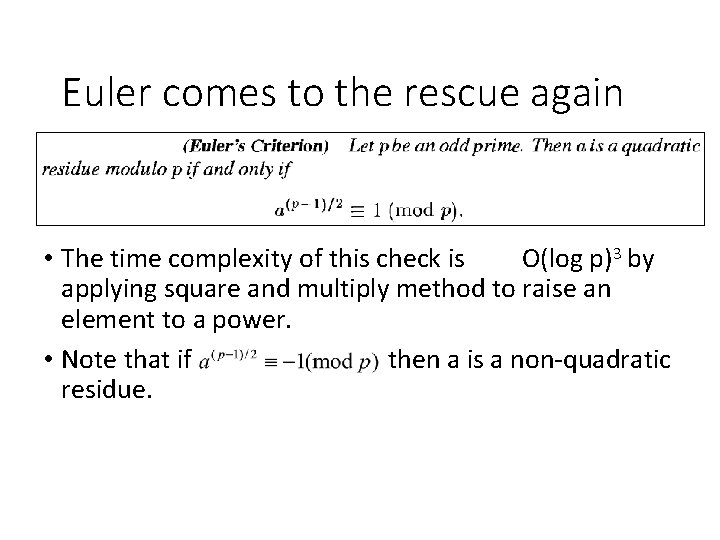
Euler comes to the rescue again • The time complexity of this check is O(log p)3 by applying square and multiply method to raise an element to a power. • Note that if then a is a non-quadratic residue.
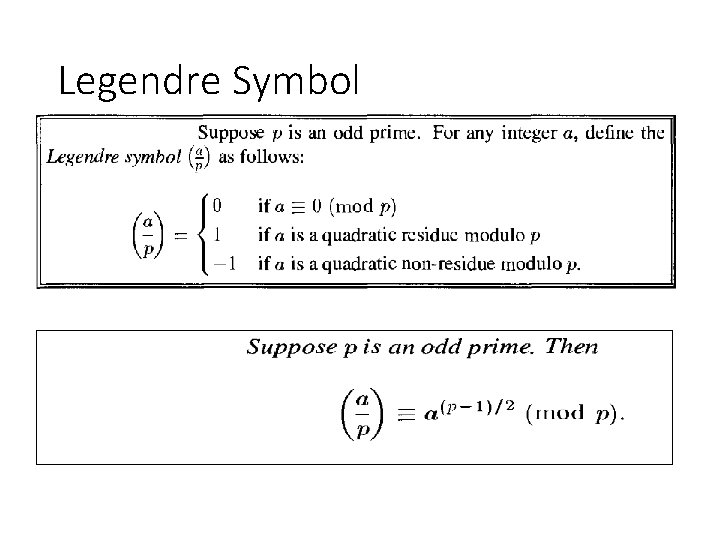
Legendre Symbol
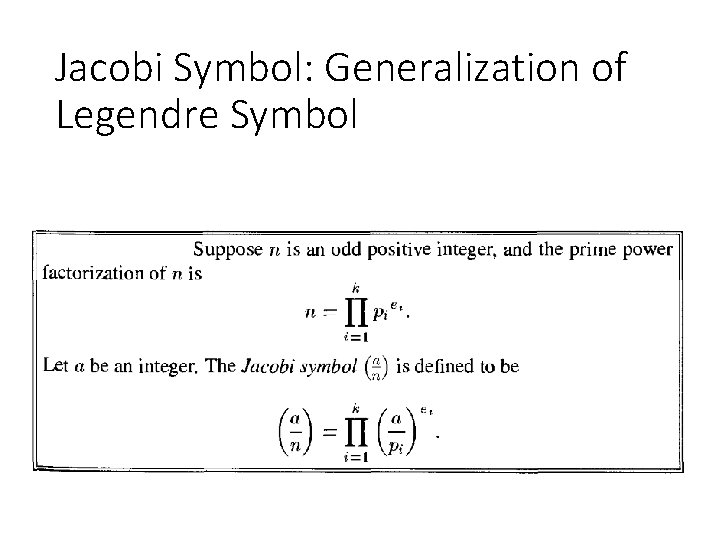
Jacobi Symbol: Generalization of Legendre Symbol
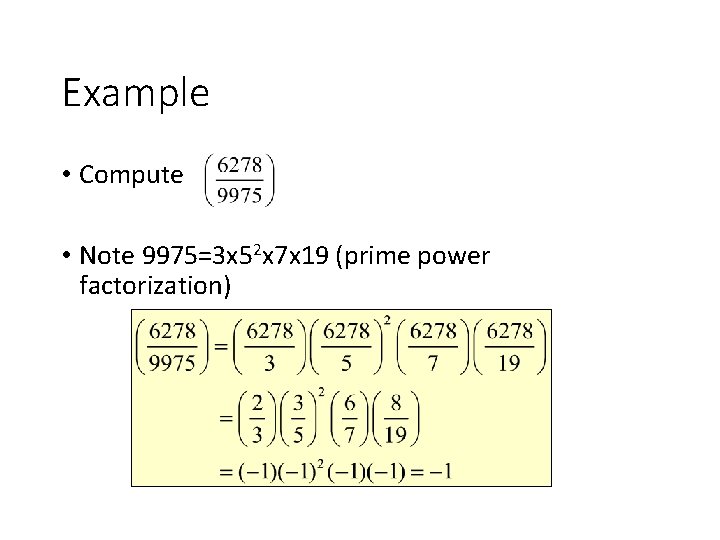
Example • Compute • Note 9975=3 x 52 x 7 x 19 (prime power factorization)
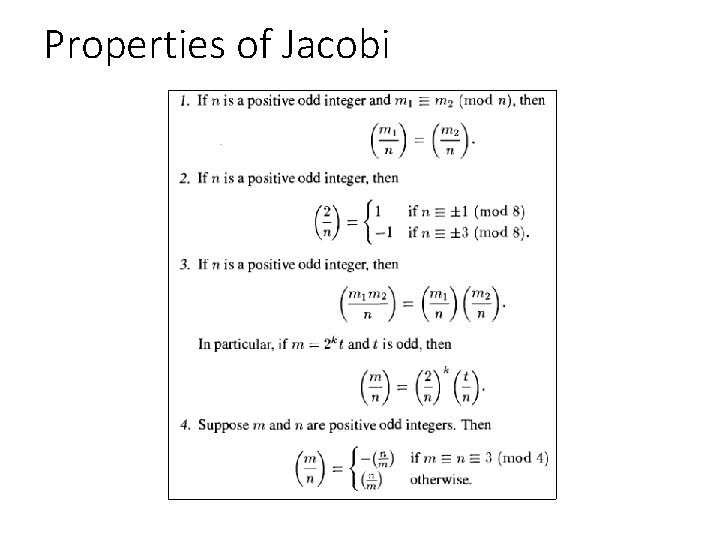
Properties of Jacobi
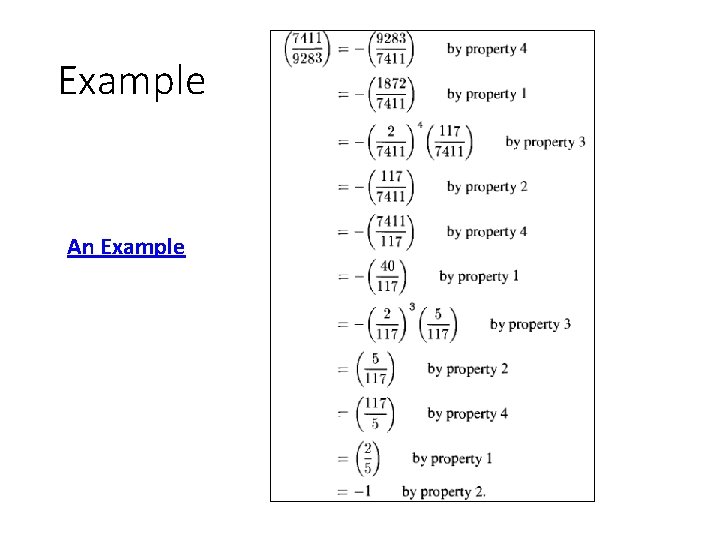
Example An Example
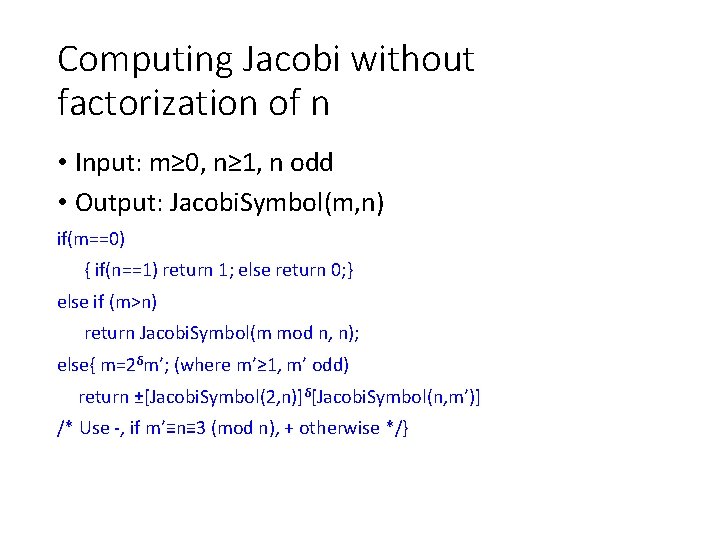
Computing Jacobi without factorization of n • Input: m≥ 0, n≥ 1, n odd • Output: Jacobi. Symbol(m, n) if(m==0) { if(n==1) return 1; else return 0; } else if (m>n) return Jacobi. Symbol(m mod n, n); else{ m=2δm’; (where m’≥ 1, m’ odd) return ±[Jacobi. Symbol(2, n)]δ[Jacobi. Symbol(n, m’)] /* Use -, if m’≡n≡ 3 (mod n), + otherwise */}
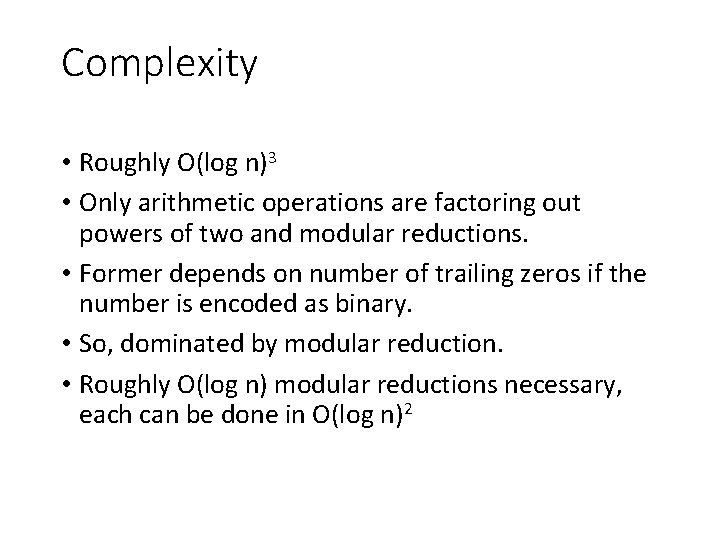
Complexity • Roughly O(log n)3 • Only arithmetic operations are factoring out powers of two and modular reductions. • Former depends on number of trailing zeros if the number is encoded as binary. • So, dominated by modular reduction. • Roughly O(log n) modular reductions necessary, each can be done in O(log n)2
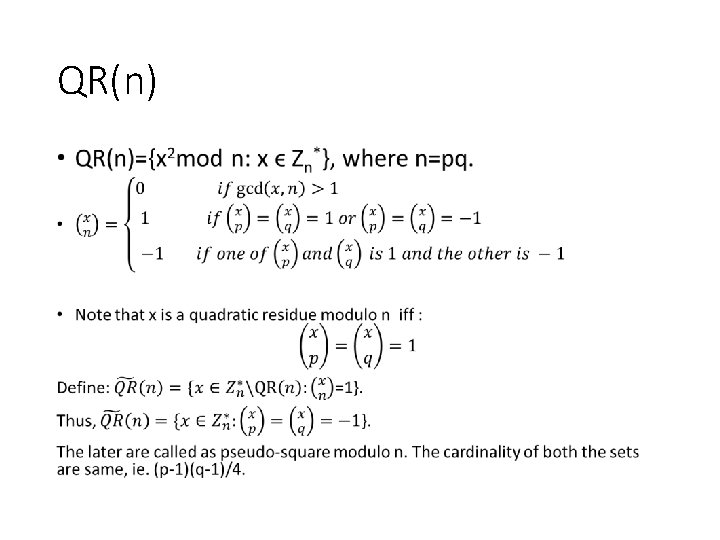
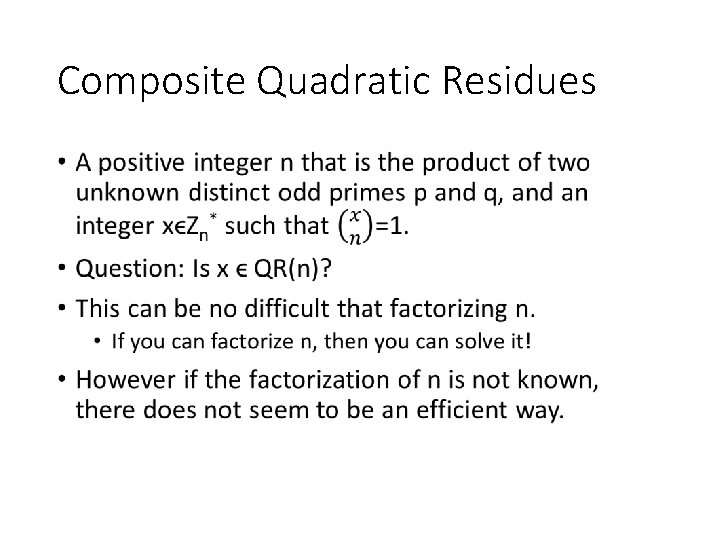
Composite Quadratic Residues •
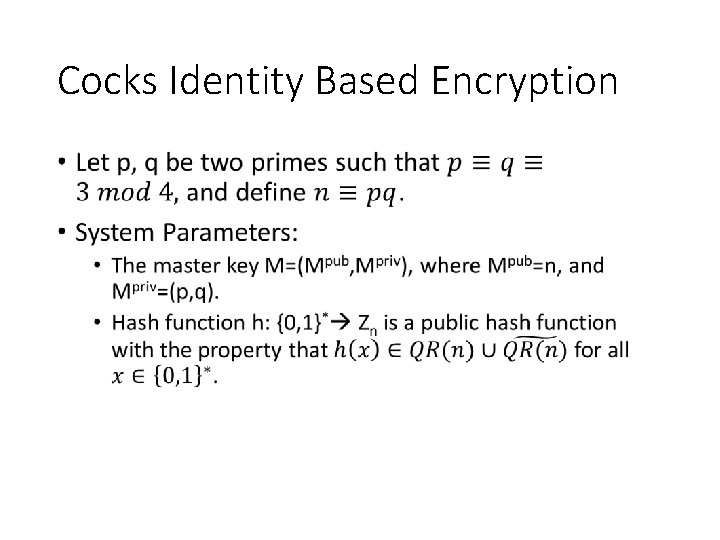
Cocks Identity Based Encryption •
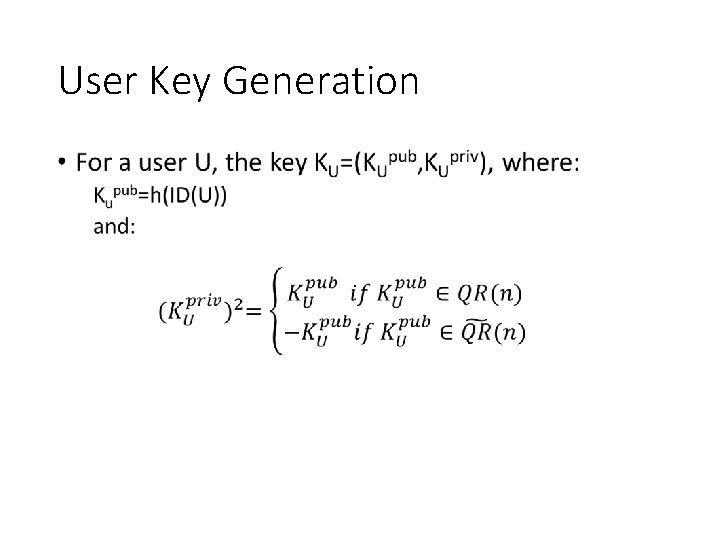
User Key Generation •
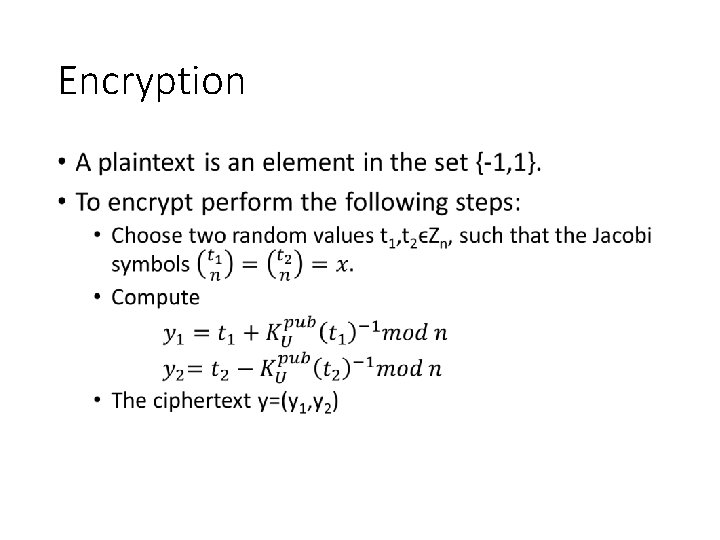
Encryption •
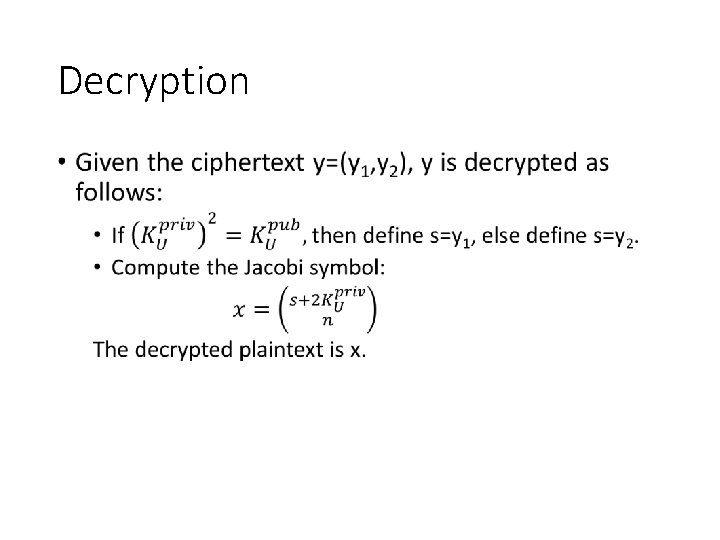
Decryption •
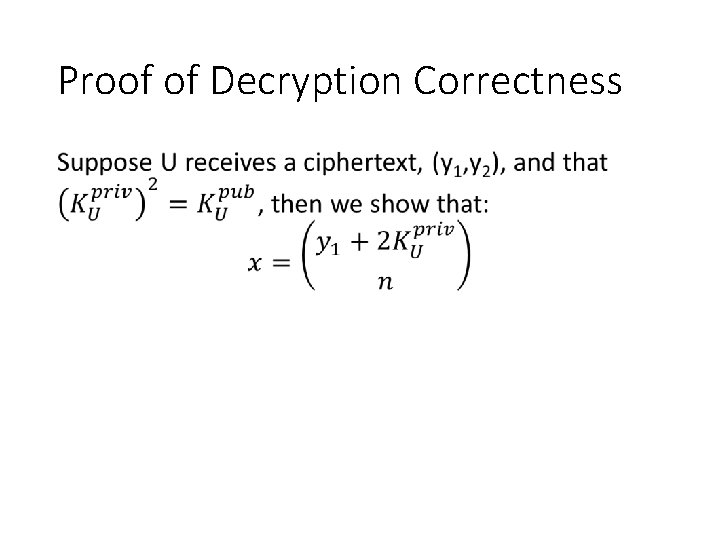
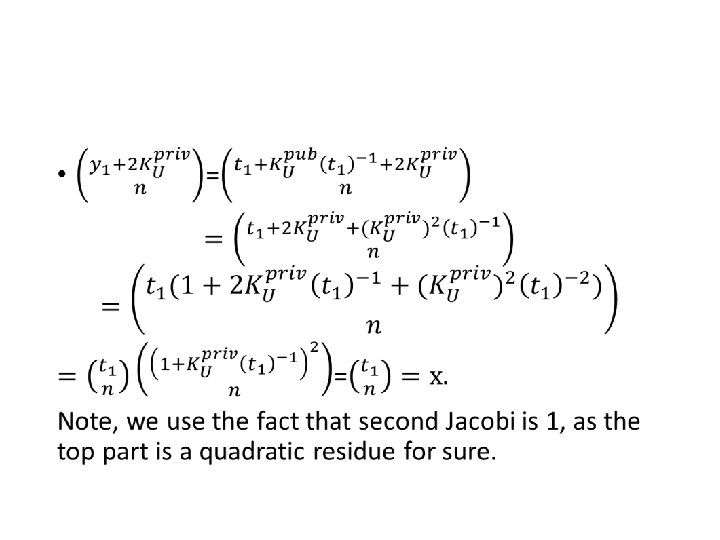
Proof of Decryption Correctness •
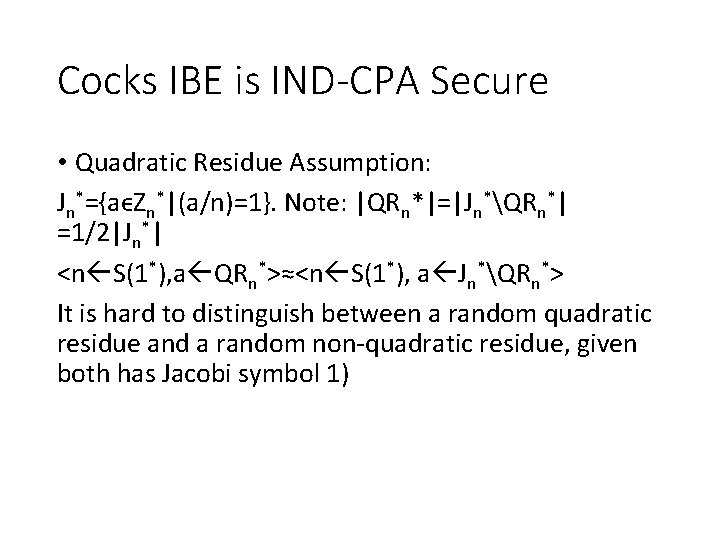
Cocks IBE is IND-CPA Secure • Quadratic Residue Assumption: Jn*={aϵZn*|(a/n)=1}. Note: |QRn*|=|Jn*QRn*| =1/2|Jn*| <n S(1*), a QRn*>≈<n S(1*), a Jn*QRn*> It is hard to distinguish between a random quadratic residue and a random non-quadratic residue, given both has Jacobi symbol 1)
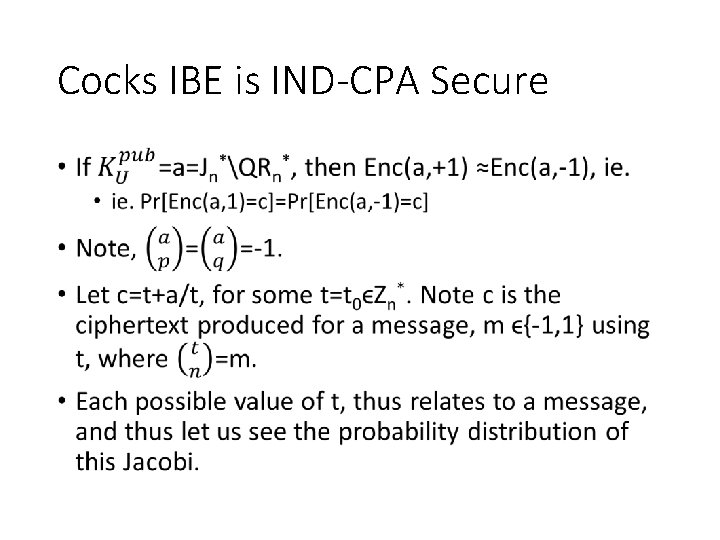
Cocks IBE is IND-CPA Secure •
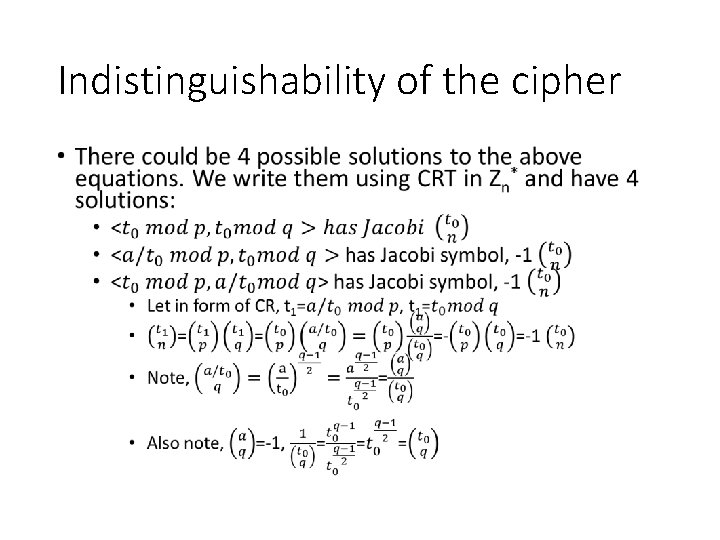
Indistinguishability of the cipher •
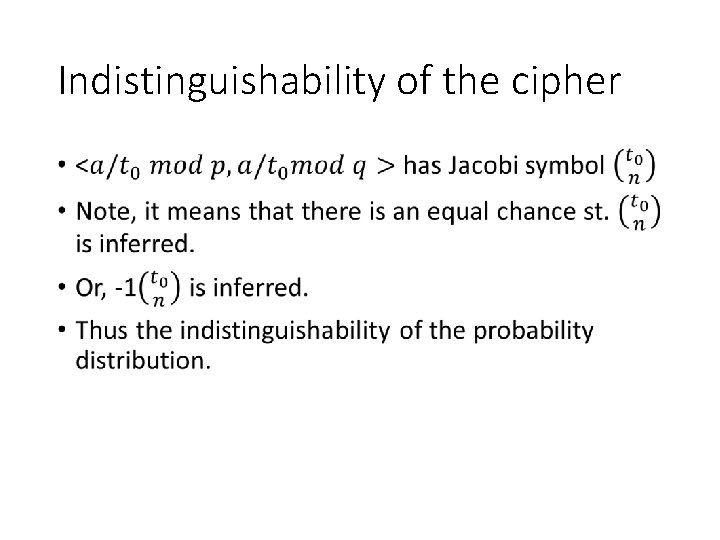
Indistinguishability of the cipher •
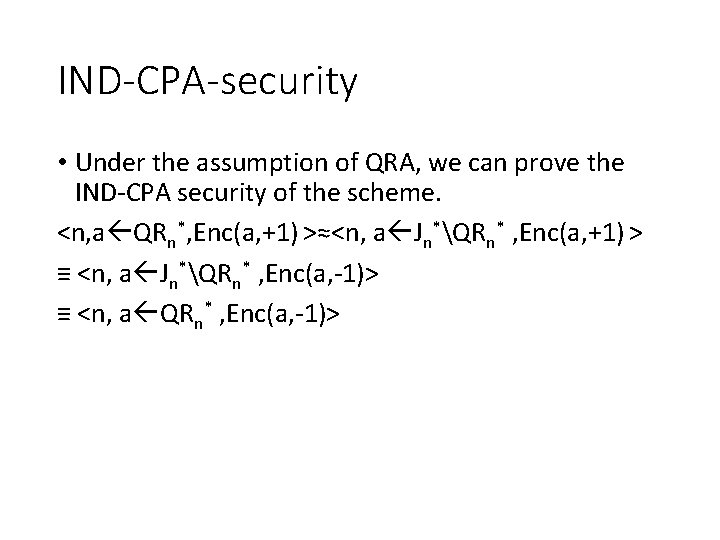
IND-CPA-security • Under the assumption of QRA, we can prove the IND-CPA security of the scheme. <n, a QRn*, Enc(a, +1) >≈<n, a Jn*QRn* , Enc(a, +1) > ≡ <n, a Jn*QRn* , Enc(a, -1)> ≡ <n, a QRn* , Enc(a, -1)>
- Slides: 41