HTTPS Inspection Best Practices Focus Outbound HTTPS inspection
HTTPS Inspection - Best Practices Focus: Outbound HTTPS inspection Peter Elmer | Security Expert, EMEA | Office of the CTO December 2019 © 2019 Check Point Software Technologies Ltd. [Protected] Distribution or modification is subject to approval 1
Agenda • The Need • Fundamentals • Survival Package • Performance • Life Demo R 80. 40 EA © 2019 Check Point Software Technologies Ltd. [Protected] Distribution or modification is subject to approval 2
![The Need For HTTPS Inspection © 2019 Check Point Software Technologies Ltd. [Protected] Distribution The Need For HTTPS Inspection © 2019 Check Point Software Technologies Ltd. [Protected] Distribution](http://slidetodoc.com/presentation_image/2480714a178bdf09ee3340eeb076ba5d/image-3.jpg)
The Need For HTTPS Inspection © 2019 Check Point Software Technologies Ltd. [Protected] Distribution or modification is subject to approval 3
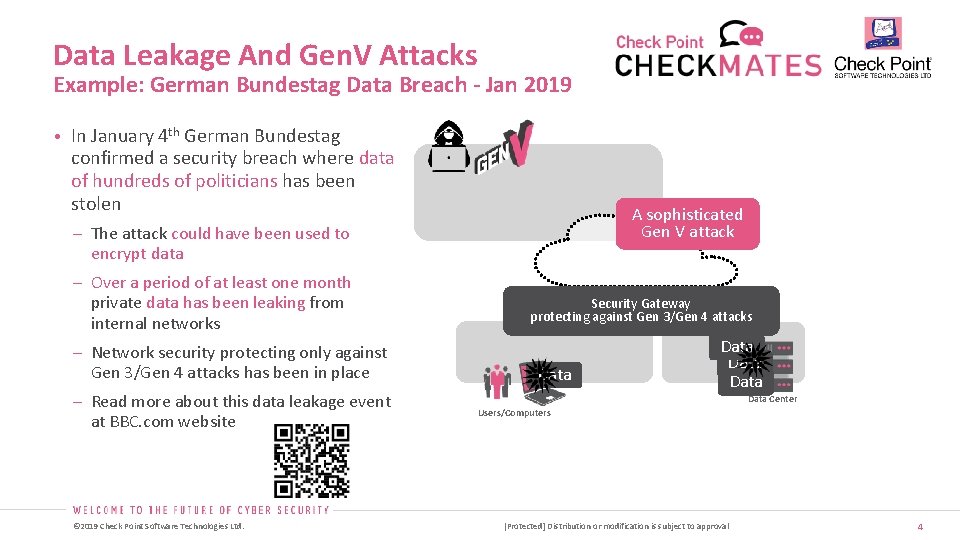
Data Leakage And Gen. V Attacks Example: German Bundestag Data Breach - Jan 2019 • In January 4 th German Bundestag confirmed a security breach where data of hundreds of politicians has been stolen A sophisticated Gen V attack – The attack could have been used to encrypt data – Over a period of at least one month private data has been leaking from internal networks – Network security protecting only against Gen 3/Gen 4 attacks has been in place – Read more about this data leakage event at BBC. com website © 2019 Check Point Software Technologies Ltd. Security Gateway protecting against Gen 3/Gen 4 attacks Data Data Center Users/Computers [Protected] Distribution or modification is subject to approval 4
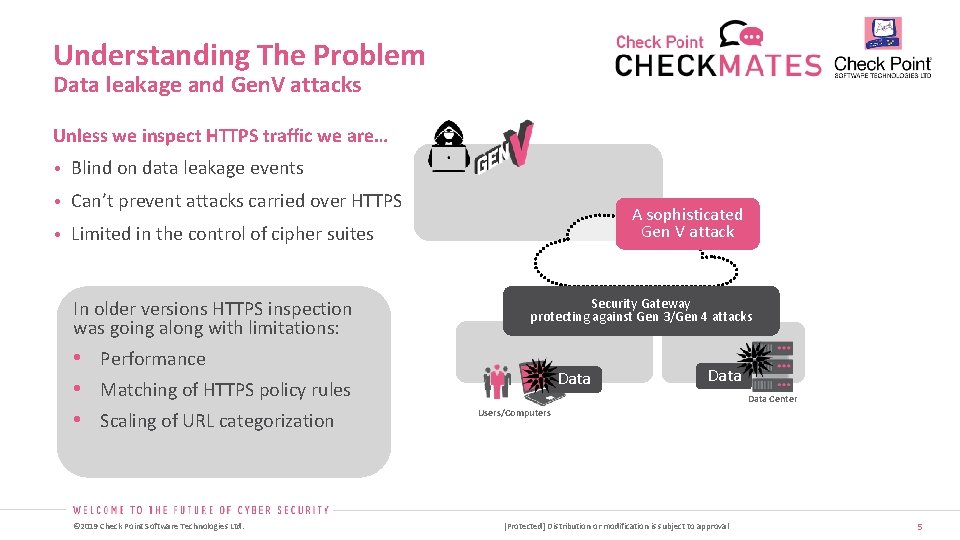
Understanding The Problem Data leakage and Gen. V attacks Unless we inspect HTTPS traffic we are… • Blind on data leakage events • Can’t prevent attacks carried over HTTPS A sophisticated Gen V attack • Limited in the control of cipher suites In older versions HTTPS inspection was going along with limitations: • Performance • Matching of HTTPS policy rules • Scaling of URL categorization © 2019 Check Point Software Technologies Ltd. Security Gateway protecting against Gen 3/Gen 4 attacks Data Center Users/Computers [Protected] Distribution or modification is subject to approval 5
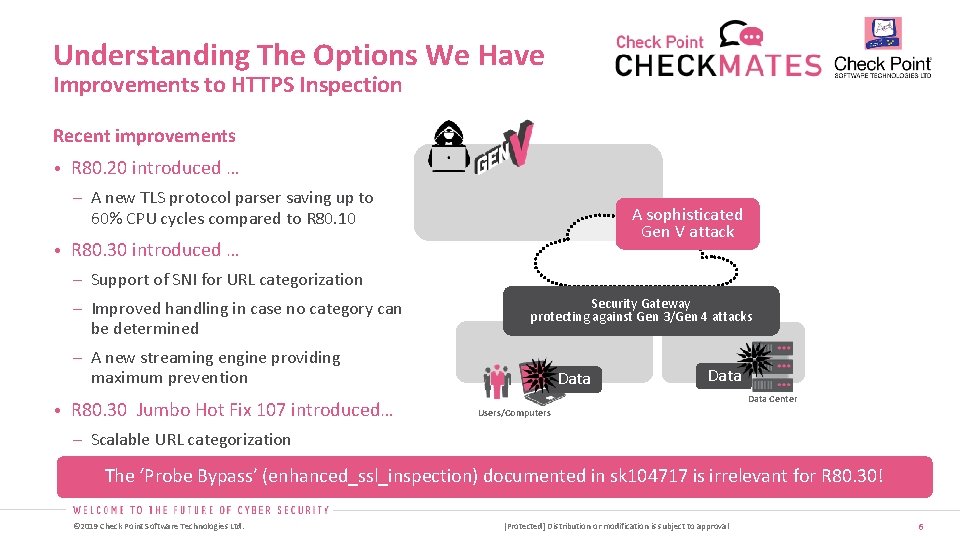
Understanding The Options We Have Improvements to HTTPS Inspection Recent improvements • R 80. 20 introduced … – A new TLS protocol parser saving up to 60% CPU cycles compared to R 80. 10 A sophisticated Gen V attack • R 80. 30 introduced … – Support of SNI for URL categorization – Improved handling in case no category can be determined Security Gateway protecting against Gen 3/Gen 4 attacks – A new streaming engine providing maximum prevention • R 80. 30 Jumbo Hot Fix 107 introduced… Data Center Users/Computers – Scalable URL categorization The ‘Probe Bypass’ (enhanced_ssl_inspection) documented in sk 104717 is irrelevant for R 80. 30! © 2019 Check Point Software Technologies Ltd. [Protected] Distribution or modification is subject to approval 6
![HTTPS Inspection Fundamentals © 2019 Check Point Software Technologies Ltd. [Protected] Distribution or modification HTTPS Inspection Fundamentals © 2019 Check Point Software Technologies Ltd. [Protected] Distribution or modification](http://slidetodoc.com/presentation_image/2480714a178bdf09ee3340eeb076ba5d/image-7.jpg)
HTTPS Inspection Fundamentals © 2019 Check Point Software Technologies Ltd. [Protected] Distribution or modification is subject to approval 7
![Understanding Policies Matching Gateway Topology © 2019 Check Point Software Technologies Ltd. [Protected] Distribution Understanding Policies Matching Gateway Topology © 2019 Check Point Software Technologies Ltd. [Protected] Distribution](http://slidetodoc.com/presentation_image/2480714a178bdf09ee3340eeb076ba5d/image-8.jpg)
Understanding Policies Matching Gateway Topology © 2019 Check Point Software Technologies Ltd. [Protected] Distribution or modification is subject to approval 8
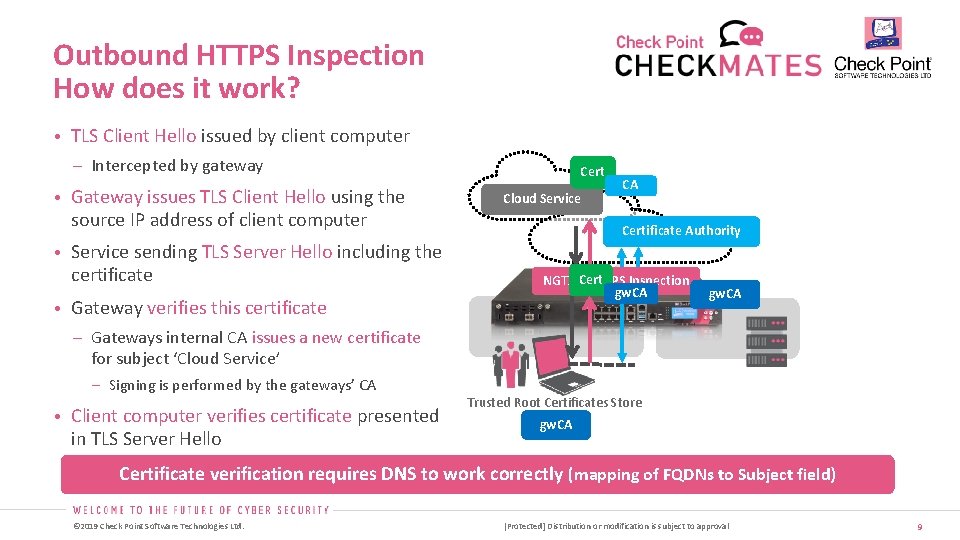
Outbound HTTPS Inspection How does it work? • TLS Client Hello issued by client computer – Intercepted by gateway • Gateway issues TLS Client Hello using the source IP address of client computer Cert Cloud Service CA CA Certificate Authority • Service sending TLS Server Hello including the certificate • Gateway verifies this certificate NGTX +Cert HTTPS Inspection gw. CA – Gateways internal CA issues a new certificate for subject ‘Cloud Service’ Signing is performed by the gateways’ CA • Client computer verifies certificate presented in TLS Server Hello Trusted Root Certificates Store gw. CA Certificate verification requires DNS to work correctly (mapping of FQDNs to Subject field) © 2019 Check Point Software Technologies Ltd. [Protected] Distribution or modification is subject to approval 9
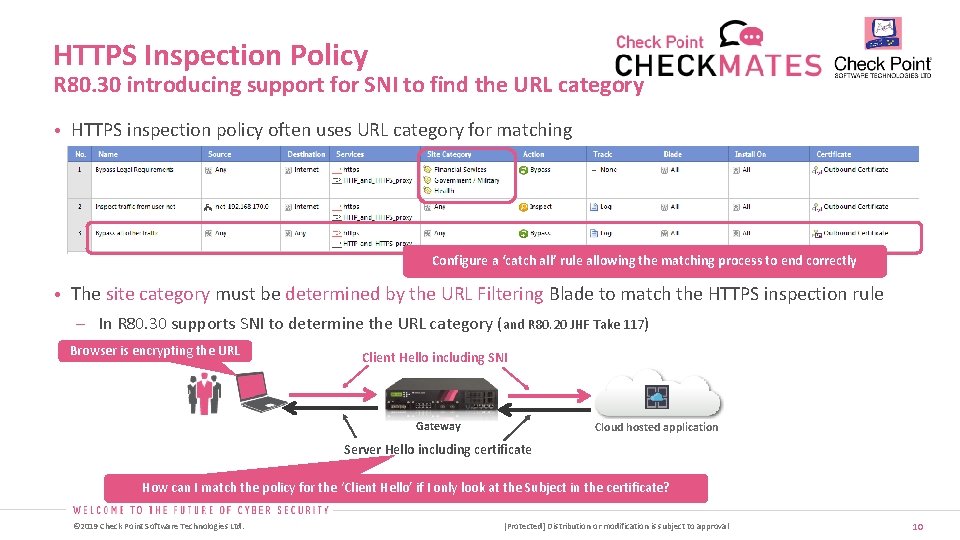
HTTPS Inspection Policy R 80. 30 introducing support for SNI to find the URL category • HTTPS inspection policy often uses URL category for matching Configure a ‘catch all’ rule allowing the matching process to end correctly • The site category must be determined by the URL Filtering Blade to match the HTTPS inspection rule In R 80. 30 supports SNI to determine the URL category (and R 80. 20 JHF Take 117) Browser is encrypting the URL Client Hello including SNI Gateway Cloud hosted application Server Hello including certificate How can I match the policy for the ‘Client Hello’ if I only look at the Subject in the certificate? © 2019 Check Point Software Technologies Ltd. [Protected] Distribution or modification is subject to approval 10
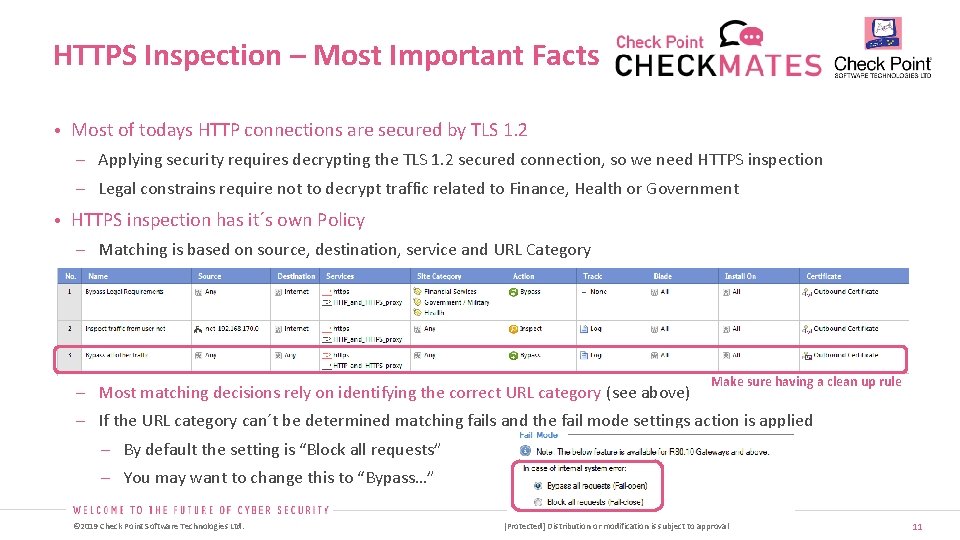
HTTPS Inspection – Most Important Facts • Most of todays HTTP connections are secured by TLS 1. 2 Applying security requires decrypting the TLS 1. 2 secured connection, so we need HTTPS inspection Legal constrains require not to decrypt traffic related to Finance, Health or Government • HTTPS inspection has it´s own Policy Matching is based on source, destination, service and URL Category Most matching decisions rely on identifying the correct URL category (see above) Make sure having a clean up rule If the URL category can´t be determined matching fails and the fail mode settings action is applied By default the setting is “Block all requests” You may want to change this to “Bypass…” © 2019 Check Point Software Technologies Ltd. [Protected] Distribution or modification is subject to approval 11
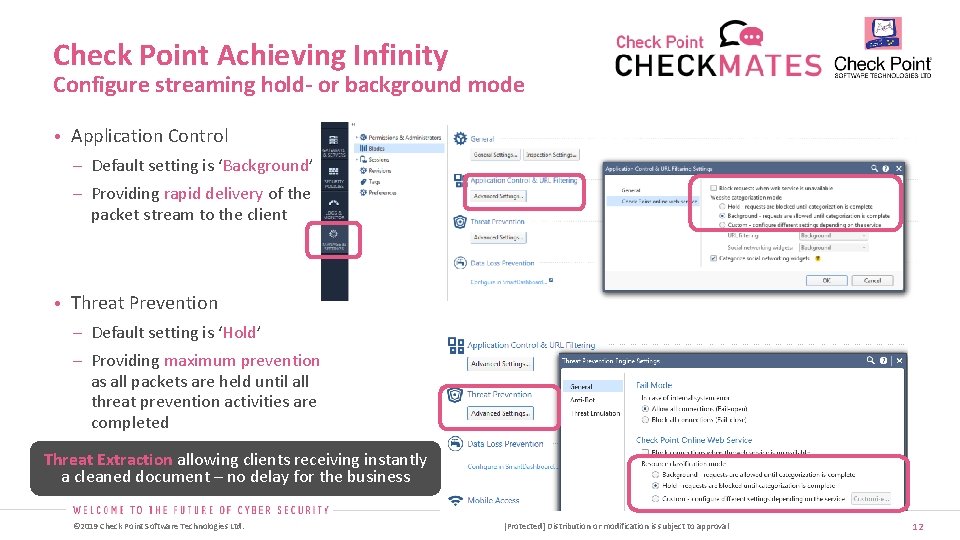
Check Point Achieving Infinity Configure streaming hold- or background mode • Application Control – Default setting is ‘Background’ – Providing rapid delivery of the packet stream to the client • Threat Prevention – Default setting is ‘Hold’ – Providing maximum prevention as all packets are held until all threat prevention activities are completed Threat Extraction allowing clients receiving instantly a cleaned document – no delay for the business © 2019 Check Point Software Technologies Ltd. [Protected] Distribution or modification is subject to approval 12
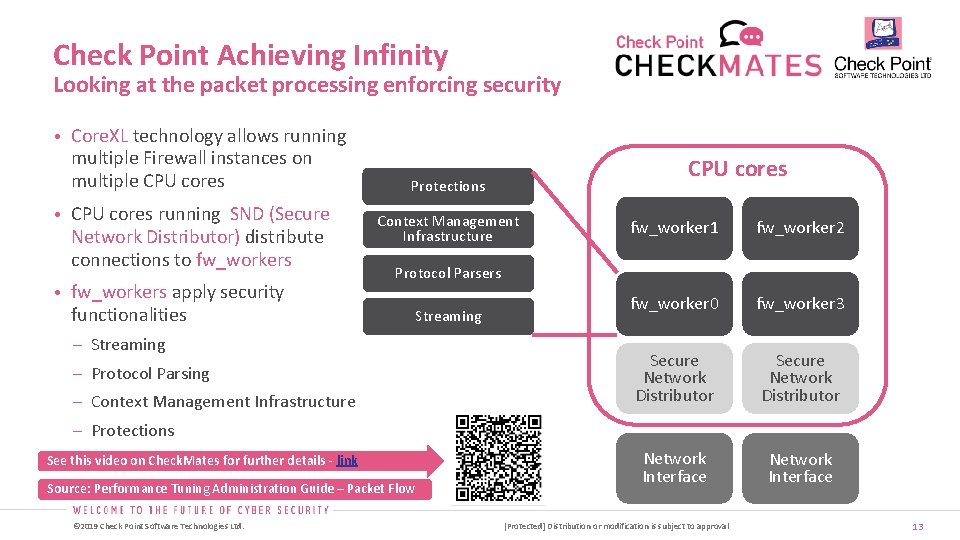
Check Point Achieving Infinity Looking at the packet processing enforcing security • Core. XL technology allows running multiple Firewall instances on multiple CPU cores • CPU cores running SND (Secure Network Distributor) distribute connections to fw_workers • fw_workers apply security CPU cores Protections Context Management Infrastructure fw_worker 1 fw_worker 2 fw_worker 0 fw_worker 3 Secure Network Distributor Network Interface Protocol Parsers functionalities – Streaming – Protocol Parsing – Context Management Infrastructure Streaming – Protections See this video on Check. Mates for further details - link Source: Performance Tuning Administration Guide – Packet Flow © 2019 Check Point Software Technologies Ltd. [Protected] Distribution or modification is subject to approval 13
![HTTPS Inspection Survival Package © 2019 Check Point Software Technologies Ltd. [Protected] Distribution or HTTPS Inspection Survival Package © 2019 Check Point Software Technologies Ltd. [Protected] Distribution or](http://slidetodoc.com/presentation_image/2480714a178bdf09ee3340eeb076ba5d/image-14.jpg)
HTTPS Inspection Survival Package © 2019 Check Point Software Technologies Ltd. [Protected] Distribution or modification is subject to approval 14
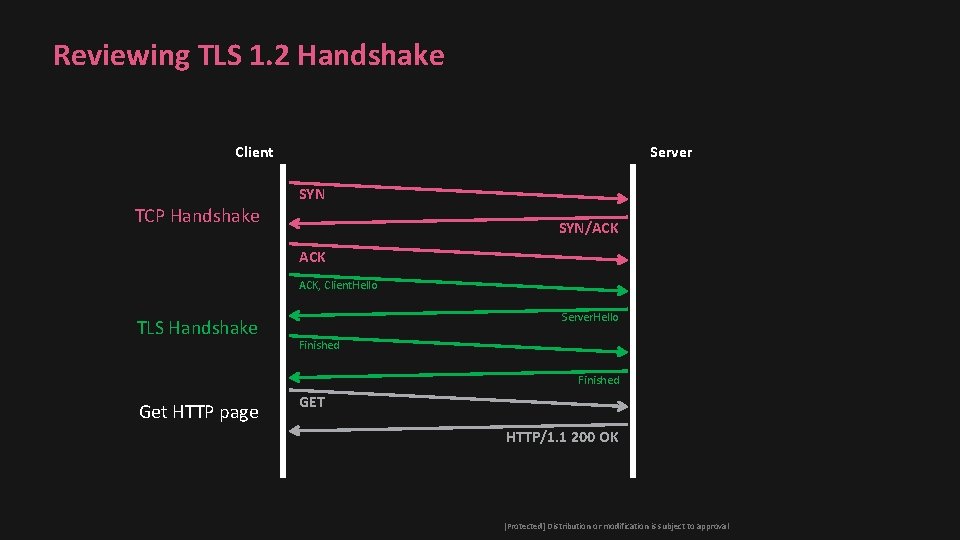
Reviewing TLS 1. 2 Handshake Client TCP Handshake Server SYN/ACK ACK, Client. Hello TLS Handshake Server. Hello Finished Get HTTP page GET HTTP/1. 1 200 OK © 2019 Check Point Software Technologies Ltd. [Protected] Distribution or modification is subject to approval 15
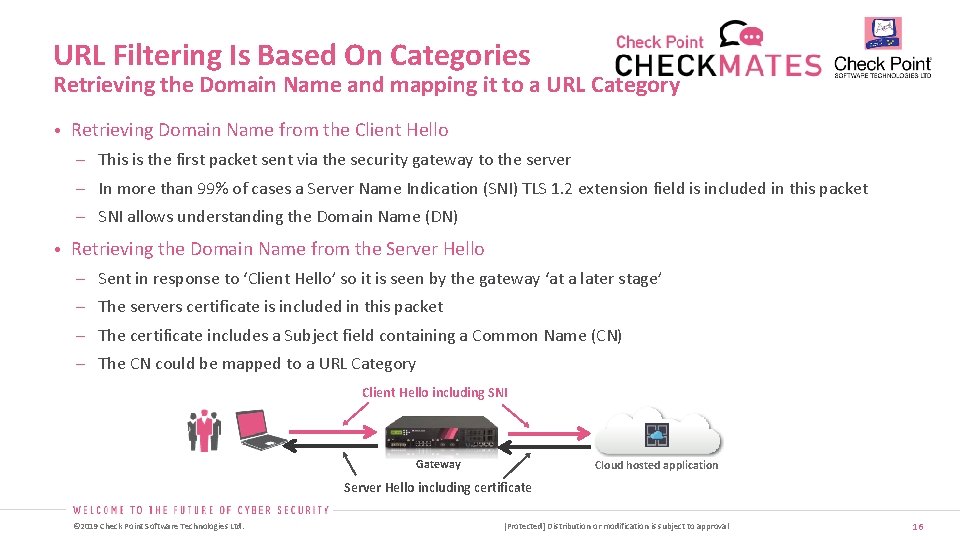
URL Filtering Is Based On Categories Retrieving the Domain Name and mapping it to a URL Category • Retrieving Domain Name from the Client Hello This is the first packet sent via the security gateway to the server In more than 99% of cases a Server Name Indication (SNI) TLS 1. 2 extension field is included in this packet SNI allows understanding the Domain Name (DN) • Retrieving the Domain Name from the Server Hello Sent in response to ‘Client Hello’ so it is seen by the gateway ‘at a later stage’ The servers certificate is included in this packet The certificate includes a Subject field containing a Common Name (CN) The CN could be mapped to a URL Category Client Hello including SNI Gateway Cloud hosted application Server Hello including certificate © 2019 Check Point Software Technologies Ltd. [Protected] Distribution or modification is subject to approval 16
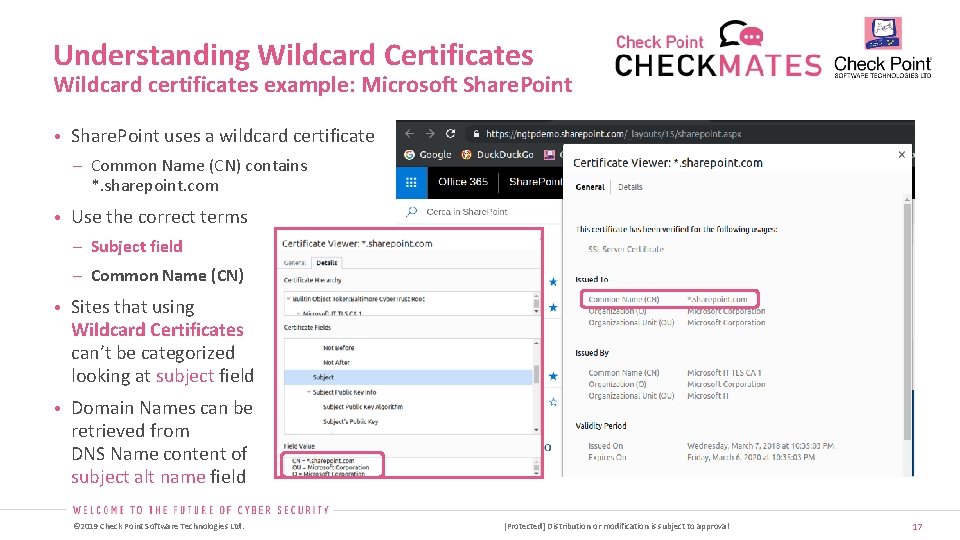
Understanding Wildcard Certificates Wildcard certificates example: Microsoft Share. Point • Share. Point uses a wildcard certificate – Common Name (CN) contains *. sharepoint. com • Use the correct terms – Subject field – Common Name (CN) • Sites that using Wildcard Certificates can’t be categorized looking at subject field • Domain Names can be retrieved from DNS Name content of subject alt name field © 2019 Check Point Software Technologies Ltd. [Protected] Distribution or modification is subject to approval 17
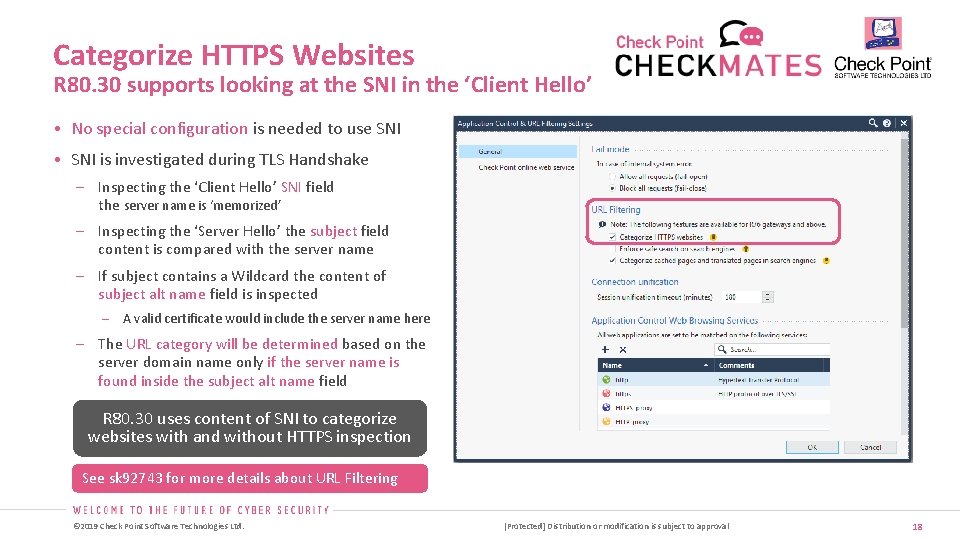
Categorize HTTPS Websites R 80. 30 supports looking at the SNI in the ‘Client Hello’ • No special configuration is needed to use SNI • SNI is investigated during TLS Handshake Inspecting the ‘Client Hello’ SNI field the server name is ‘memorized’ Inspecting the ‘Server Hello’ the subject field content is compared with the server name If subject contains a Wildcard the content of subject alt name field is inspected A valid certificate would include the server name here The URL category will be determined based on the server domain name only if the server name is found inside the subject alt name field R 80. 30 uses content of SNI to categorize websites with and without HTTPS inspection See sk 92743 for more details about URL Filtering © 2019 Check Point Software Technologies Ltd. [Protected] Distribution or modification is subject to approval 18
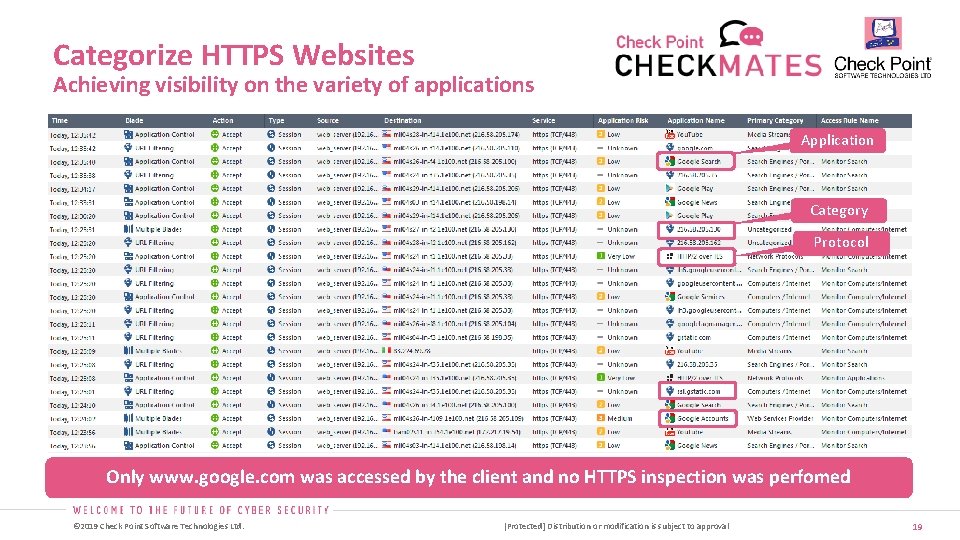
Categorize HTTPS Websites Achieving visibility on the variety of applications Application Category Protocol Only www. google. com was accessed by the client and no HTTPS inspection was perfomed © 2019 Check Point Software Technologies Ltd. [Protected] Distribution or modification is subject to approval 19
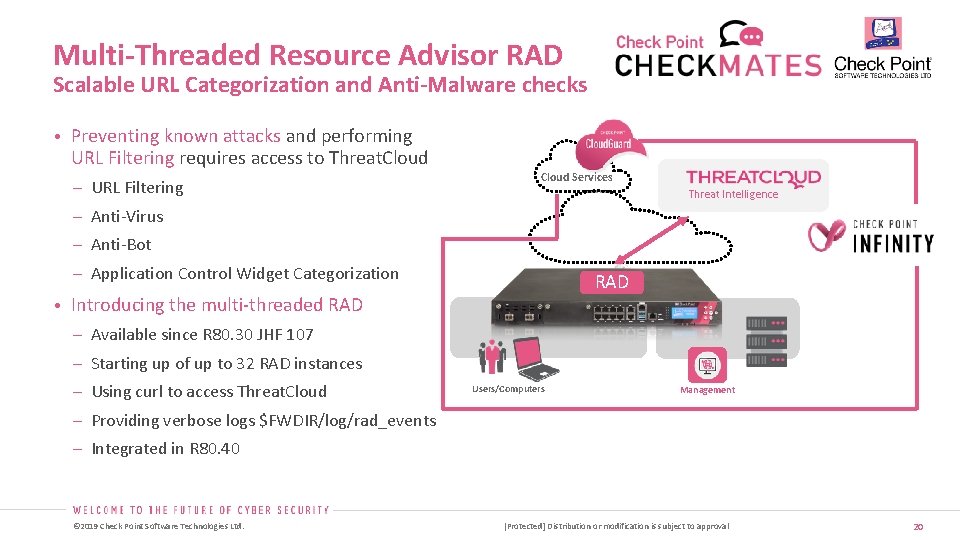
Multi-Threaded Resource Advisor RAD Scalable URL Categorization and Anti-Malware checks • Preventing known attacks and performing URL Filtering requires access to Threat. Cloud – URL Filtering Cloud Services Threat Intelligence – Anti-Virus – Anti-Bot – Application Control Widget Categorization RAD • Introducing the multi-threaded RAD – Available since R 80. 30 JHF 107 – Starting up of up to 32 RAD instances – Using curl to access Threat. Cloud Users/Computers Management – Providing verbose logs $FWDIR/log/rad_events – Integrated in R 80. 40 © 2019 Check Point Software Technologies Ltd. [Protected] Distribution or modification is subject to approval 20
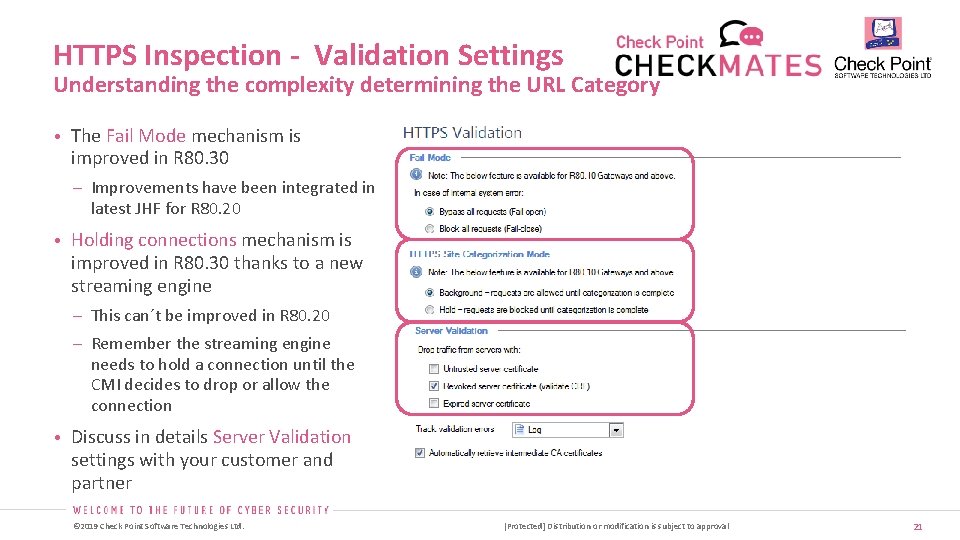
HTTPS Inspection - Validation Settings Understanding the complexity determining the URL Category • The Fail Mode mechanism is improved in R 80. 30 – Improvements have been integrated in latest JHF for R 80. 20 • Holding connections mechanism is improved in R 80. 30 thanks to a new streaming engine – This can´t be improved in R 80. 20 – Remember the streaming engine needs to hold a connection until the CMI decides to drop or allow the connection • Discuss in details Server Validation settings with your customer and partner © 2019 Check Point Software Technologies Ltd. [Protected] Distribution or modification is subject to approval 21
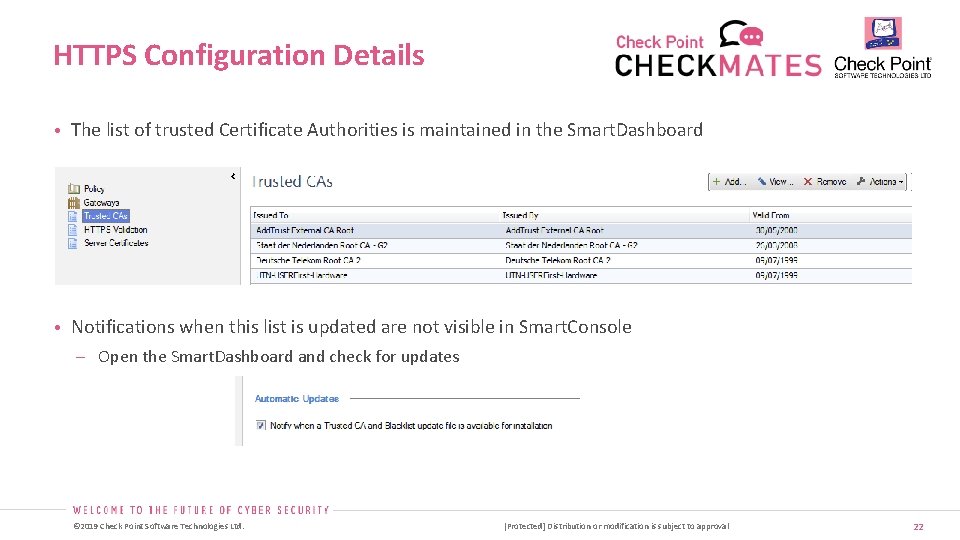
HTTPS Configuration Details • The list of trusted Certificate Authorities is maintained in the Smart. Dashboard • Notifications when this list is updated are not visible in Smart. Console Open the Smart. Dashboard and check for updates © 2019 Check Point Software Technologies Ltd. [Protected] Distribution or modification is subject to approval 22
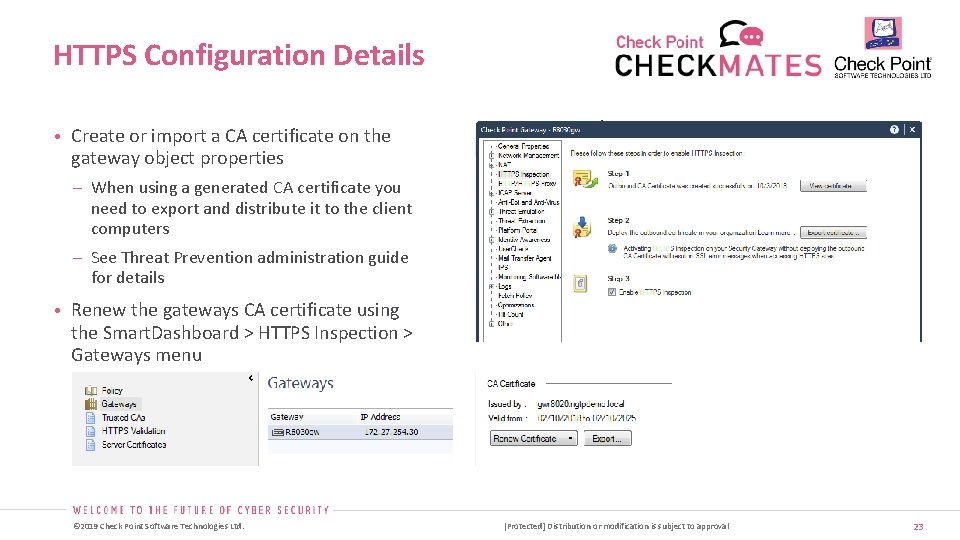
HTTPS Configuration Details • Create or import a CA certificate on the gateway object properties – When using a generated CA certificate you need to export and distribute it to the client computers – See Threat Prevention administration guide for details • Renew the gateways CA certificate using the Smart. Dashboard > HTTPS Inspection > Gateways menu © 2019 Check Point Software Technologies Ltd. [Protected] Distribution or modification is subject to approval 23
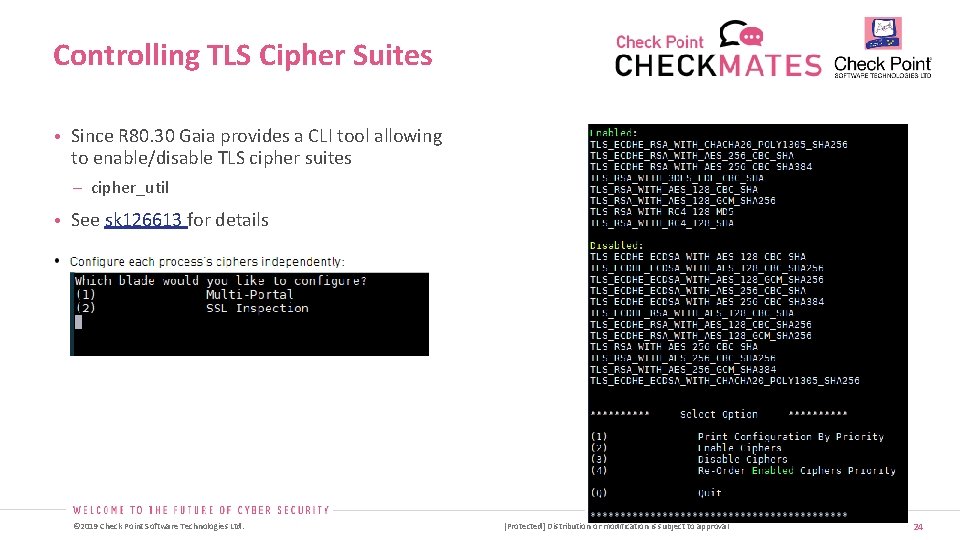
Controlling TLS Cipher Suites • Since R 80. 30 Gaia provides a CLI tool allowing to enable/disable TLS cipher suites – cipher_util • See sk 126613 for details © 2019 Check Point Software Technologies Ltd. [Protected] Distribution or modification is subject to approval 24
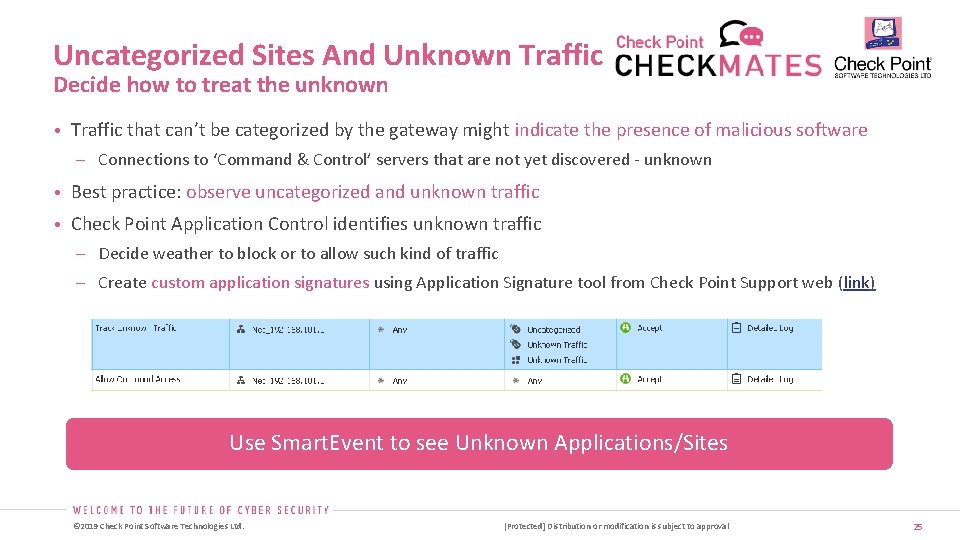
Uncategorized Sites And Unknown Traffic Decide how to treat the unknown • Traffic that can’t be categorized by the gateway might indicate the presence of malicious software Connections to ‘Command & Control’ servers that are not yet discovered - unknown • Best practice: observe uncategorized and unknown traffic • Check Point Application Control identifies unknown traffic Decide weather to block or to allow such kind of traffic Create custom application signatures using Application Signature tool from Check Point Support web (link) Use Smart. Event to see Unknown Applications/Sites © 2019 Check Point Software Technologies Ltd. [Protected] Distribution or modification is subject to approval 25
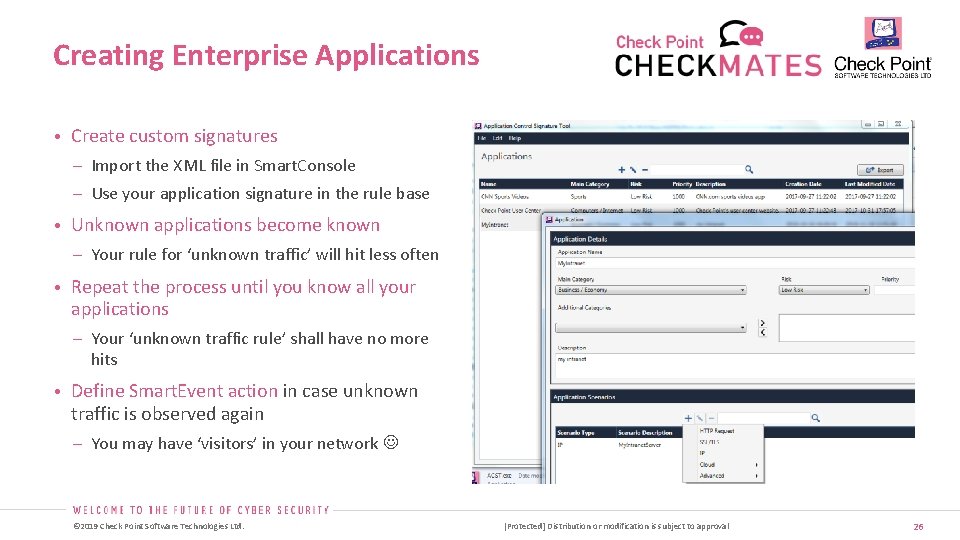
Creating Enterprise Applications • Create custom signatures – Import the XML file in Smart. Console – Use your application signature in the rule base • Unknown applications become known – Your rule for ‘unknown traffic’ will hit less often • Repeat the process until you know all your applications – Your ‘unknown traffic rule’ shall have no more hits • Define Smart. Event action in case unknown traffic is observed again – You may have ‘visitors’ in your network © 2019 Check Point Software Technologies Ltd. [Protected] Distribution or modification is subject to approval 26
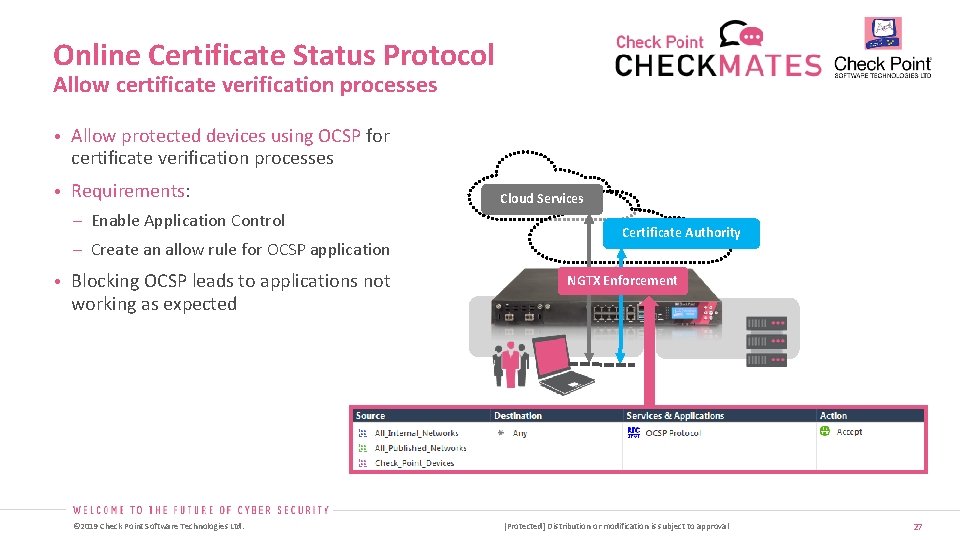
Online Certificate Status Protocol Allow certificate verification processes • Allow protected devices using OCSP for certificate verification processes • Requirements: – Enable Application Control – Create an allow rule for OCSP application • Blocking OCSP leads to applications not Cloud Services Certificate Authority NGTX Enforcement working as expected © 2019 Check Point Software Technologies Ltd. [Protected] Distribution or modification is subject to approval 27
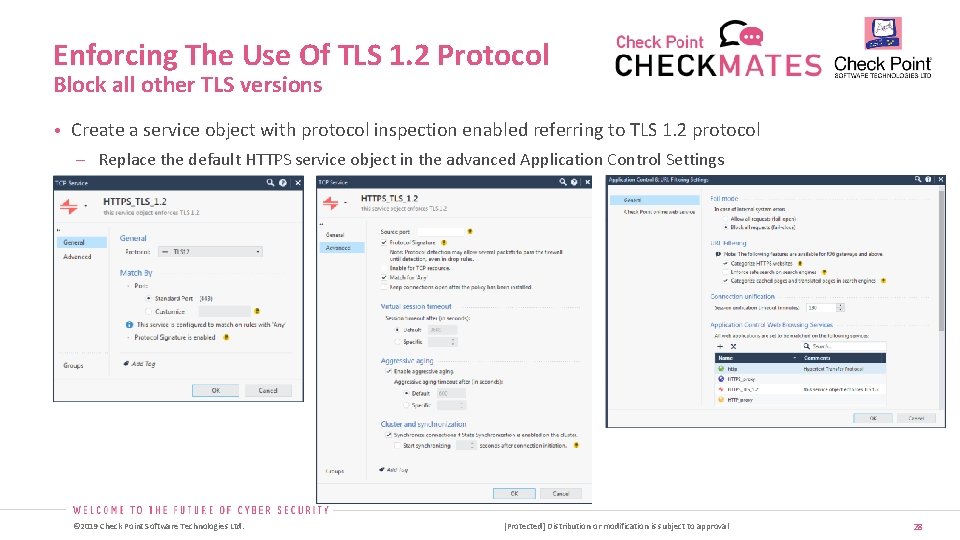
Enforcing The Use Of TLS 1. 2 Protocol Block all other TLS versions • Create a service object with protocol inspection enabled referring to TLS 1. 2 protocol Replace the default HTTPS service object in the advanced Application Control Settings © 2019 Check Point Software Technologies Ltd. [Protected] Distribution or modification is subject to approval 28
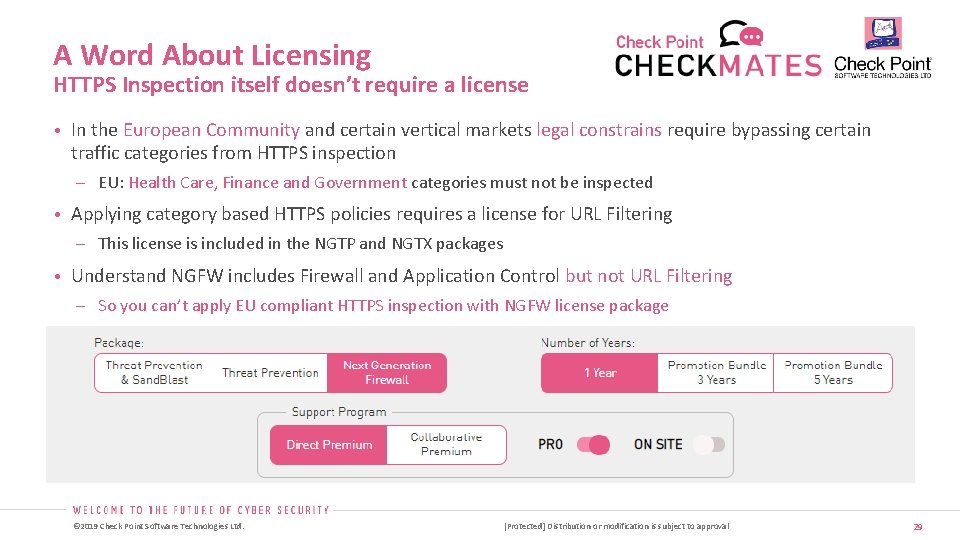
A Word About Licensing HTTPS Inspection itself doesn’t require a license • In the European Community and certain vertical markets legal constrains require bypassing certain traffic categories from HTTPS inspection EU: Health Care, Finance and Government categories must not be inspected • Applying category based HTTPS policies requires a license for URL Filtering This license is included in the NGTP and NGTX packages • Understand NGFW includes Firewall and Application Control but not URL Filtering So you can’t apply EU compliant HTTPS inspection with NGFW license package © 2019 Check Point Software Technologies Ltd. [Protected] Distribution or modification is subject to approval 29
![Performance © 2019 Check Point Software Technologies Ltd. [Protected] Distribution or modification is subject Performance © 2019 Check Point Software Technologies Ltd. [Protected] Distribution or modification is subject](http://slidetodoc.com/presentation_image/2480714a178bdf09ee3340eeb076ba5d/image-30.jpg)
Performance © 2019 Check Point Software Technologies Ltd. [Protected] Distribution or modification is subject to approval 30

Test Results For Content Aware Security Inspecting HTTPS Traffic And Preventing Gen V Attacks Objectives and results • Achieving a balance of throughput and connections per seconds – A Throughput of about 5 Gbps was achieved while maintaining 3000 connections/second Check Point 16000 Turbo • Appliance CPUs had still free cycles – The traffic was loading the appliance around 80% • Application transactions have been successful – 420 000 application transactions and only 0, 08% required retransmission A video about the performance results is posted on Check. Mates here © 2019 Check Point Software Technologies Ltd. 5 Gbps @3000 conns/sec 420 000 application transactions [Protected] Distribution or modification is subject to approval 31
Live Demo of R 80. 40 EA © 2019 Check Point Software Technologies Ltd. [Protected] Distribution or modification is subject to approval 32
![Closing © 2019 Check Point Software Technologies Ltd. [Protected] Distribution or modification is subject Closing © 2019 Check Point Software Technologies Ltd. [Protected] Distribution or modification is subject](http://slidetodoc.com/presentation_image/2480714a178bdf09ee3340eeb076ba5d/image-33.jpg)
Closing © 2019 Check Point Software Technologies Ltd. [Protected] Distribution or modification is subject to approval 33
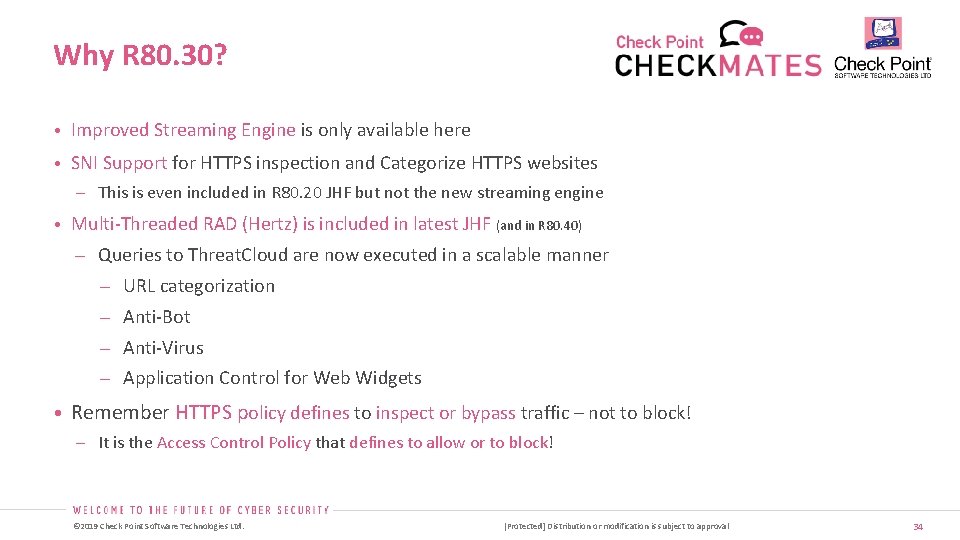
Why R 80. 30? • Improved Streaming Engine is only available here • SNI Support for HTTPS inspection and Categorize HTTPS websites This is even included in R 80. 20 JHF but not the new streaming engine • Multi-Threaded RAD (Hertz) is included in latest JHF (and in R 80. 40) Queries to Threat. Cloud are now executed in a scalable manner URL categorization Anti-Bot Anti-Virus Application Control for Web Widgets • Remember HTTPS policy defines to inspect or bypass traffic – not to block! It is the Access Control Policy that defines to allow or to block! © 2019 Check Point Software Technologies Ltd. [Protected] Distribution or modification is subject to approval 34
![Questions © 2019 Check Point Software Technologies Ltd. [Protected] Distribution or modification is subject Questions © 2019 Check Point Software Technologies Ltd. [Protected] Distribution or modification is subject](http://slidetodoc.com/presentation_image/2480714a178bdf09ee3340eeb076ba5d/image-35.jpg)
Questions © 2019 Check Point Software Technologies Ltd. [Protected] Distribution or modification is subject to approval 35
Thank You – Grazie Many thanks to Nadav, Dor and Danny from R&D for reviewing and tips given from Christian! Peter Elmer | Security Expert, EMEA | Office of the CTO December 2019 © 2019 Check Point Software Technologies Ltd. [Protected] Distribution or modification is subject to approval 36
- Slides: 36