ECommerce RisksSecurity Ing Athanasios Podaras Ph D BSI

E-Commerce Risks/Security Ing. Athanasios Podaras, Ph. D
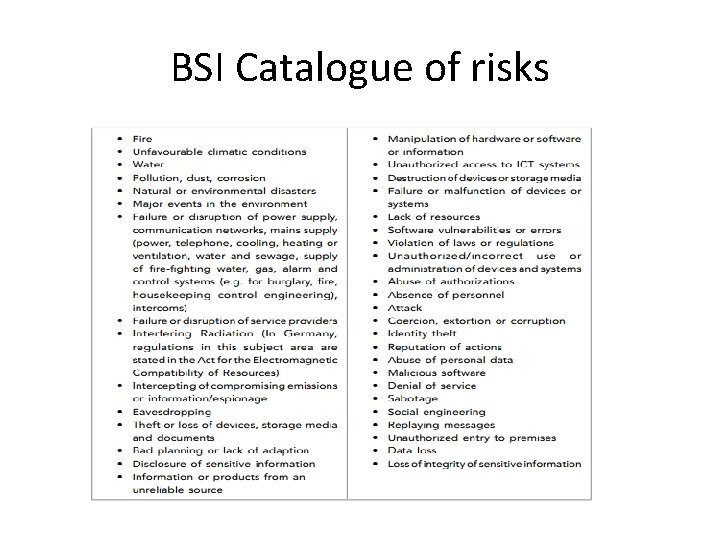
BSI Catalogue of risks
Basic Risk Management Strategies • Avoidance • Reduction • Transfer (i. e. to insurance companies) • Acceptance
Basic Risk Management Tasks • BE PREPARED TO DEAL WITH THE THREATS WHEN THEY OCCUR (BUSINESS CONTINUITY MANAGEMENT – SUPPLEMENT TO RM)
BASIC BCM PROCESSES • Prepare for emergency situation (Documentation /BIA- Business Impact Analysis, training of people, run emergency exercises) • Build emergency management team • Run the emergency management plan (when the disaster occurs) • Reinstall regular processes • Get back to normal • Termination of the emergency procedure

Security and E-commerce
What is computer security? ? • Computer security in general refers to the protection of data, networks, computer programs, computer power, and other elements of computerized information systems.
What is EC Security? ? EC Security involves: -prevention, or at least minimization of the web attacks -encryption of information -protection of users (customers, visitors, byers)
SECURITY Common protection goals • Authenticity: realness or crεdibility of a subject/object that can be verified • Integrity: data cannot be manipulated without proper authorization • Confidentiality • Availability • Obligation (not disclaiming an agreement later) • Authorization (power to conduct an activity)
Objectives of an overall IS Security Management • Fulfill organizational duties (clear instructions and assignments related to the duties) • Efficient and transparent organization • Professional security, risk and continuity management • Run a continual improvement process for minimizing risks and maximize economic efficiency • Good reputation to customers, stakeholders, authorities and the public sector
ISM Process Initializing: -Understanding IS requirements -build security policy by defining security objectives -establish representative Analyzing: -determine protection needs -risks and threats -deduction
Basic Security Terminology • • • Business continuity plan Cybercrime and Cybercriminal Exposure Fraud Malware (malicious software) Phishing Pharming Risk Spam Vulnerability
Unintentional Threats • Human errors i. e. in the design of HW or SW • Environmental Hazards (i. e. floods, earthquakes) • Malfunctions in Computer Systems due to i. e. poor manufacturing, badly maintained networks, lack of user experience or training
Intentional (by cybercriminals)Technical security attack methods Malware Unauthorized access Denial of Service Spam and spyware Hijacking servers Botnets (malicious SW to hijack number of different computers) • Maladvertising • • •
Non-technical threats • Phishing is a fraudulent process of acquiring confi dential information, such as credit card or banking details, from unsuspecting computer users. • Pharming. Similarly to phishing, pharming is a scam where malicious code is installed on a computer and used to redirect victims to a bogus (fake) websites without their knowledge or consent
Security risks 2014 and 2015 (IBM, 2014) • • • Cyberespionage and cyberwars are growing threats. Attacks are now also against mobile assets, including on smartphones, tablets, and other mobile devices. Enterprise mobile devices are a particular target. Attacks on social networks and social software tools. User-generated content is a major source of malware. Attacks on BYOD (“Bring Your Own Device”). Identity theft is exploding, increasing the criminal use of the stolen identities. Profit motive – as long as cybercriminals can make money, security threats and phishing attacks, will continue to grow. Social engineering tools such as phishing via e-mail are growing rapidly. Cybergang consolidation – underground groups are multiplying and getting bigger, especially in Internet fraud and cyberwars. Business-oriented spam (including imagebased spam). Attacks using spyware (e. g. , using Denial-of- Service method). Attacks on new technologies such as cloud computing and virtualization. Attacks on Web and mobile applications (apps).
TYPES OF ATTACKS Cyber attacks can be classified into two major interrelated categories: • Corporate espionage. Many attacks target energyrelated companies because their inside information is valuable (Mc. Afee 2011 ) • Political espionage and warfare. Political espionage and cyberwars are increasing in magnitude.
EC Security Requirements • Authentication is a process used to verify (assure) the real identity of an EC entity, which could be an individual, software agent, computer program, or EC website. • Authorization is the provision of permission to an authenticated person to access systems and perform certain operations in those specific systems. • Auditing. When a person or program accesses a website or queries a database, various pieces of information are recorded or logged into a file. The process of maintaining or revisiting the sequence of events during the transaction, when, and by whom, is known as auditing.
• Availability. Assuring that systems and information are available to the user when needed • Nonrepudiation. Closely associated with authentication is nonrepudiation , which is the assurance that online customers or trading partners will not be able to falsely deny (repudiate) their purchase, transaction, sale,
Factors that convert consumers who browse online into consumers who buy online: • • security price comparative information searchability ease of ordering delivery time product presentation
Possible threats • hacking • viruses • denial of service
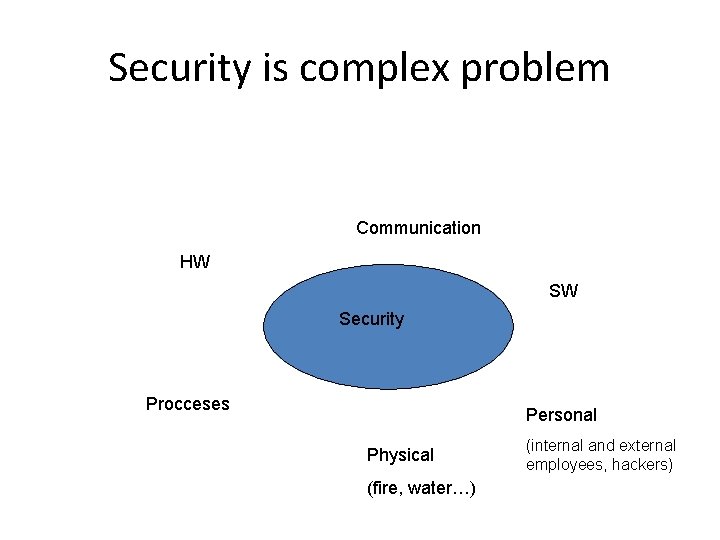
Security is complex problem Communication HW SW Security Procceses Personal Physical (fire, water…) (internal and external employees, hackers)
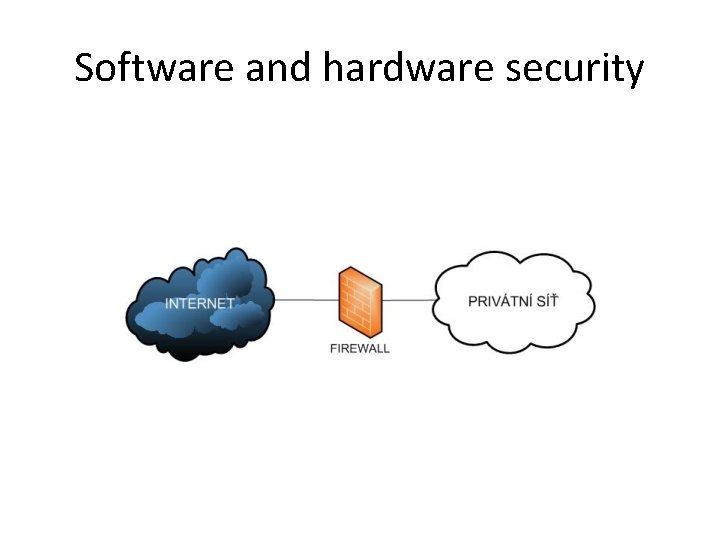
Software and hardware security
The methods by which a human can authenticate • Something the user is (e. g. , fingerprint or retinal pattern, DNA sequence (there assorted definitions of what is sufficient), voice pattern (again several definitions), signature recognition or other biometric identifier) • Something the user has (e. g. , ID card, security token) • Something the user knows (e. g. , a password, a pass phrase or a personal identification number (PIN))
Technologies
Methods • Cryptography or cryptology is a field of mathematics and computer science concerned with information security and related issues, particularly encryption and authentication.
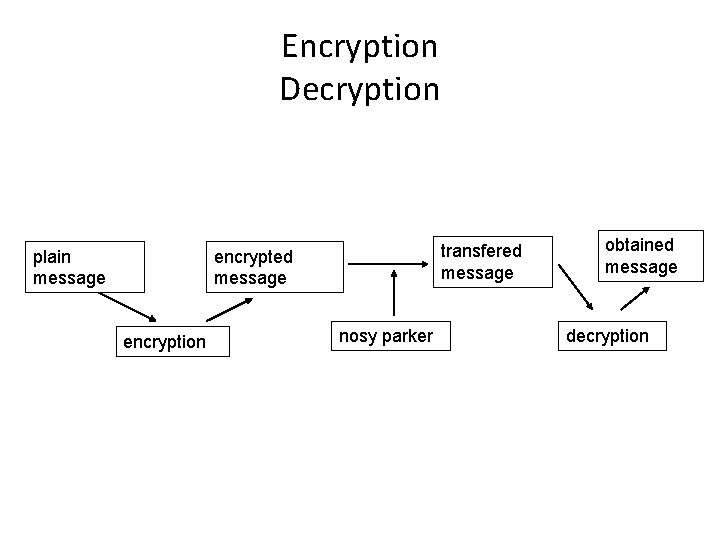
Encryption Decryption plain message transfered message encryption nosy parker obtained message decryption
Modern cryptography • Symmetric-key cryptography • Public-key cryptography
Symmetric-key cryptography Symmetric-key algorithms are a class of algorithms for cryptography that use trivially related cryptographic keys for both decryption and encryption
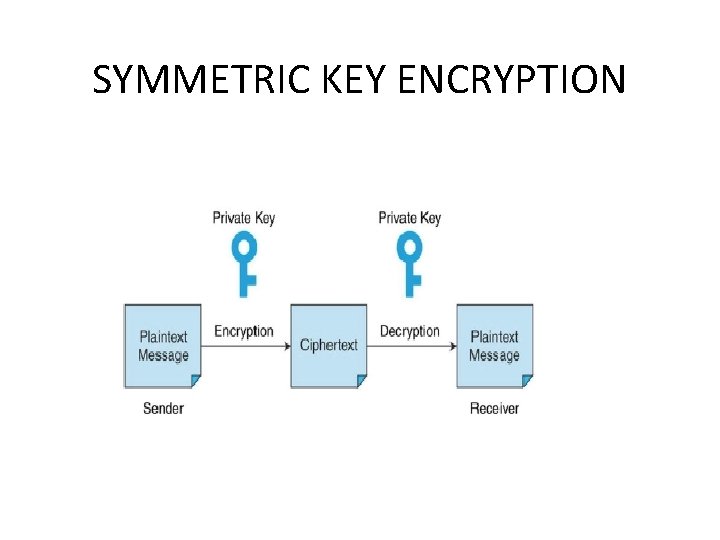
SYMMETRIC KEY ENCRYPTION
Public-key cryptography Public key cryptography is a form of cryptography which generally allows users to communicate securely without having prior access to a shared secret key. This is done by using a pair of cryptographic keys, designated as public key and private key, which are related mathematically
In cryptography, a certificate authority or certification authority (CA) is an entity which issues digital certificates for use by other parties. It is an example of a trusted third party. CA's are characteristic of many public key infrastructure (PKI) schemes
• Smart Cards • Digital signatures
Digital signatures • Digital signatures are the electronic equivalent of personal signatures on paper. They are difficult to forge since they authenticate the identity of the sender that uses the public key.
Example of contract process • The sender creates the e-mail message that includes the contract in plain language • Using special software, a secured mathematical algorithm called a hash function is applied to the message, which results in a special summary of the message converted into a string of digits that is called a message digest
• The sender uses his or her private key to encrypt the hash. This is the sender’s digital signature. No one else can replicate the sender’s digital signature because it is based on the sender’s private key, which no one else knows. • The sender encrypts with the recipients’ public key, both the original message and the digital signature. This pair together form a digital envelope. • The sender e-mails the digital envelope to the vendor • the vendor uses his or her private key to decrypt the contents •
• The vendor uses the sender’s public key for decrypting the content of the digital signature, resulting in a copy of the original message digest. • Using the same hash function employed in step 2, the vendor then creates a message digest from the decrypted message. • The vendor then compares this digest with the original message digest. • If the two digests match, then the vendor can conclude that the message is authentic.
- Slides: 37