DIFC Programs by Automatic Instrumentation William Harris Somesh
DIFC Programs by Automatic Instrumentation William Harris, Somesh Jha, and Thomas Reps 1
Decentralized Information Flow Control Operating System (DIFC OS) Allows programs to control flow of their data throughout the entire system. 2
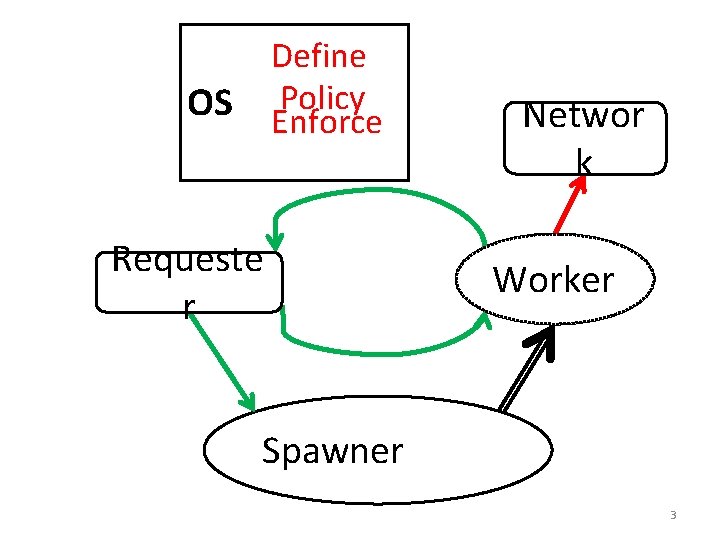
Define Policy Enforce OS Requeste r Networ k Worker Spawner 3
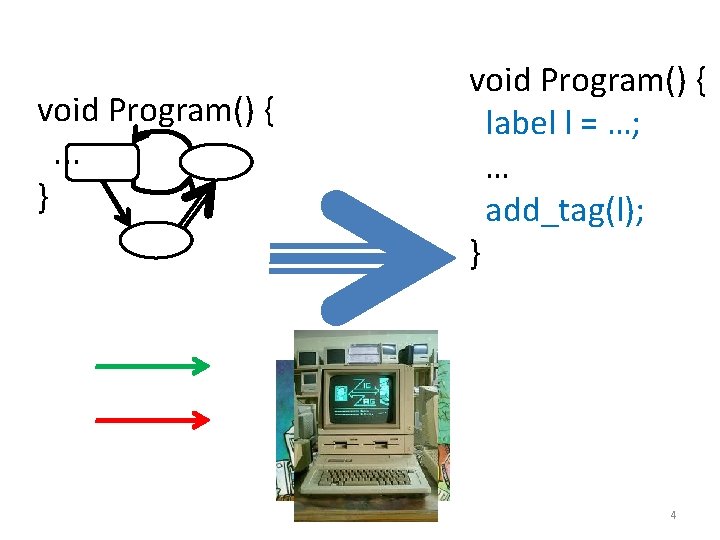
void Program() {. . . } void Program() { label l = …; … add_tag(l); } 4
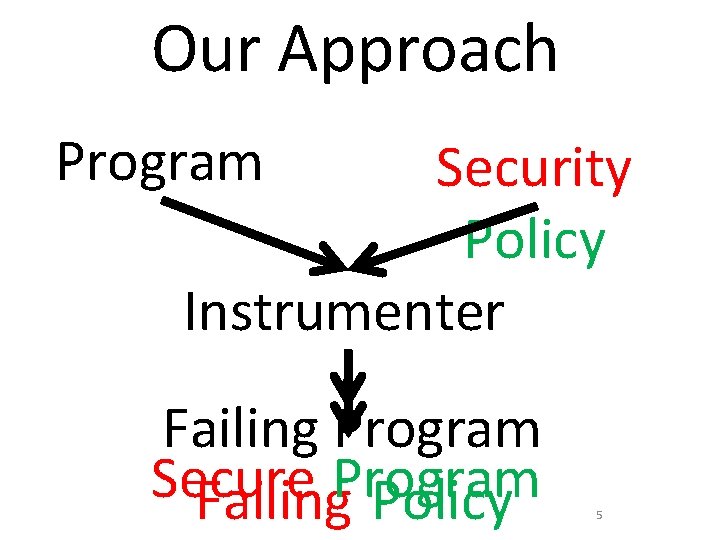
Our Approach Program Security Policy Instrumenter Failing Program Secure Program Failing Policy 5
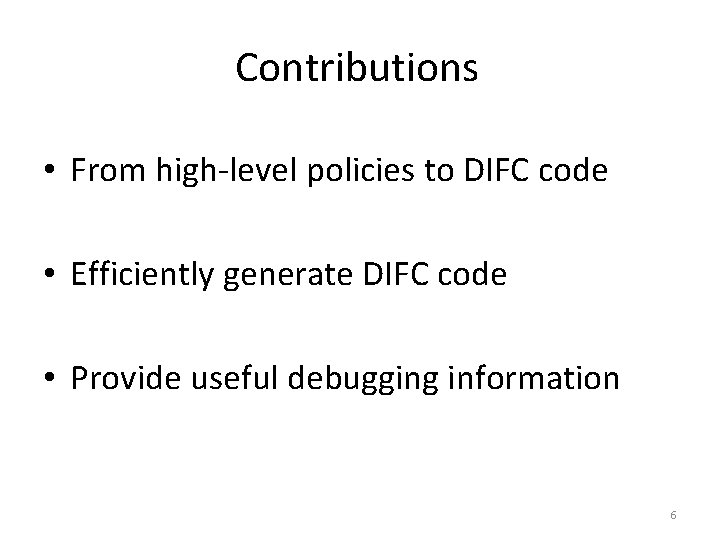
Contributions • From high-level policies to DIFC code • Efficiently generate DIFC code • Provide useful debugging information 6
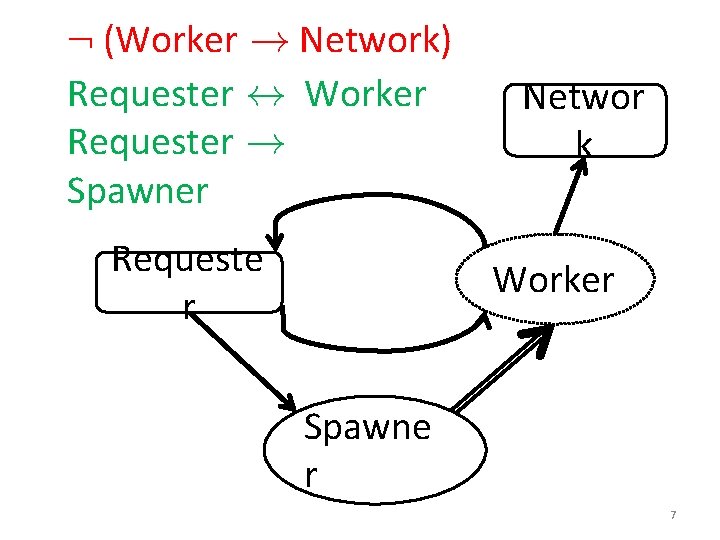
: (Worker ! Network) Requester $ Worker Requester ! Spawner Requeste r Networ k Worker Spawne r 7
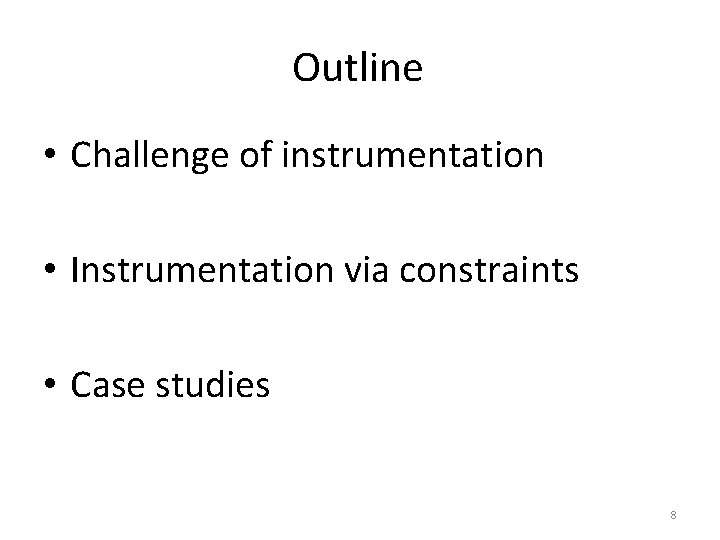
Outline • Challenge of instrumentation • Instrumentation via constraints • Case studies 8
The Challenge of Instrumentation • DIFC mechanics • Instrumenting a server 9
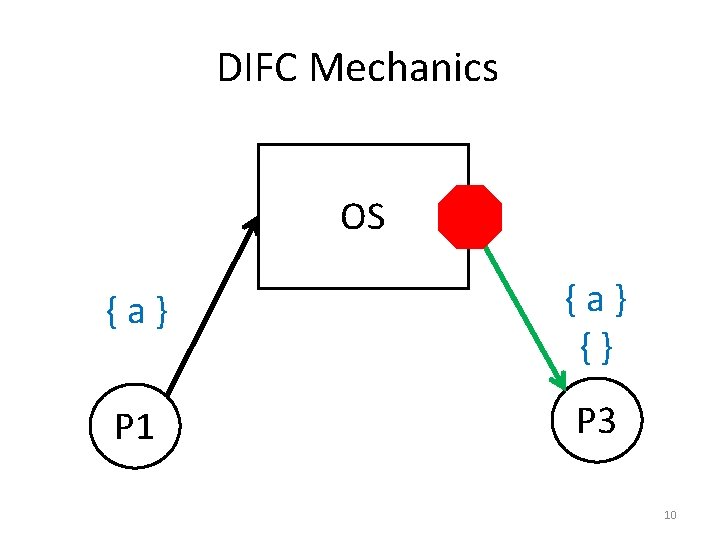
DIFC Mechanics OS {a} {} P 1 P 3 P 2 10
raise a label = read more 11
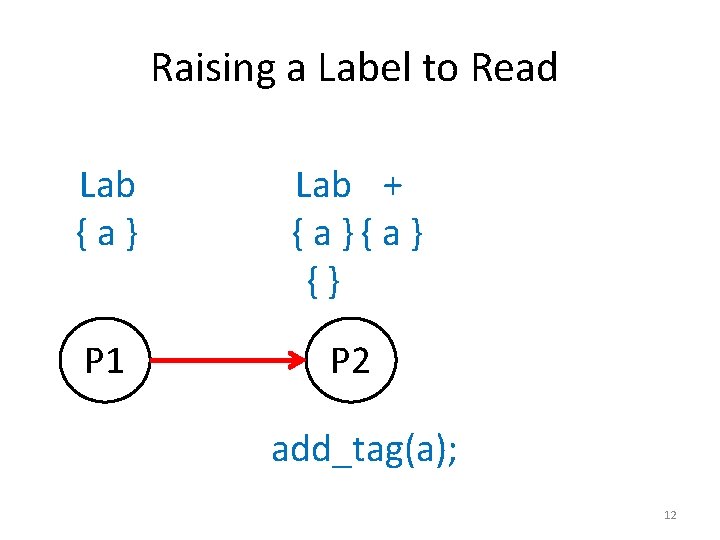
Raising a Label to Read Lab {a} Lab + { a } {} P 1 P 2 add_tag(a); 12
lower label = declassify 13
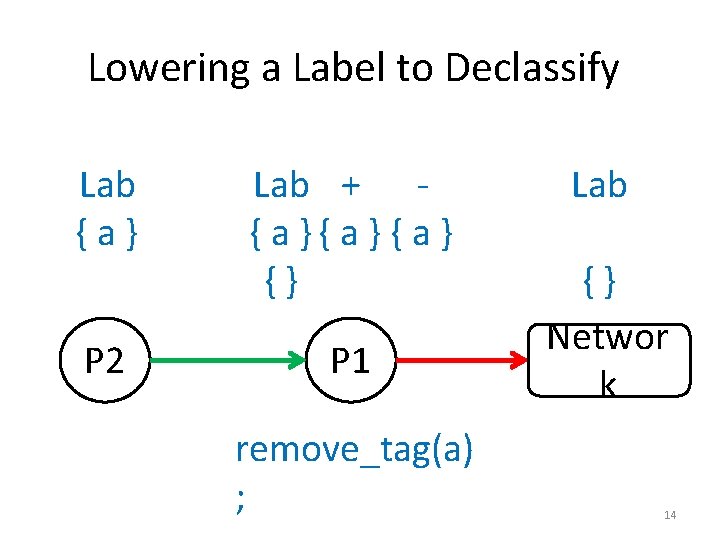
Lowering a Label to Declassify Lab {a} Lab + { a } {} P 2 P 1 remove_tag(a) ; Lab {} Networ k 14
The Challenge of Instrumentation • DIFC mechanics • Instrumenting a server 15
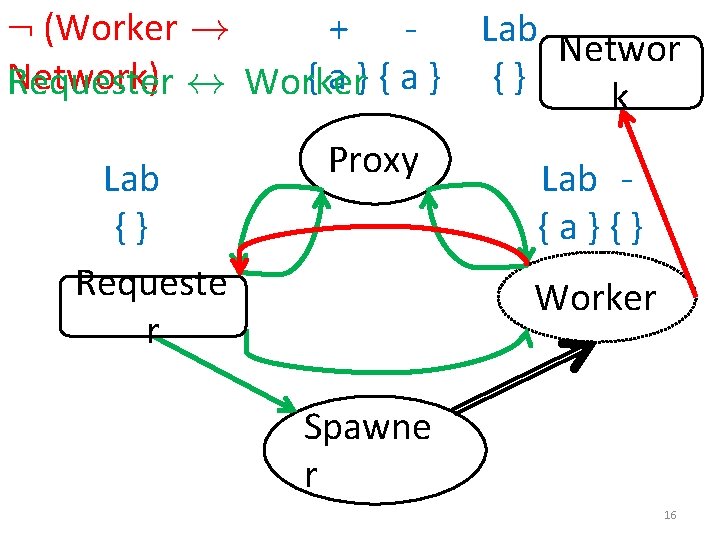
: (Worker ! + Network) {a}{a} Requester $ Worker Lab {} Requeste r Proxy Lab Networ {} k Lab {a}{} Worker Spawne r 16
Challenge of Instrumentation Instrument DIFC code that is: 1. Legal 2. Secure 3. Functional
Outline • Challenge of instrumentation • Instrumentation via constraints • Case studies 18
Key Insight From DIFC code, a DIFC system dynamically compares labels to decide flows. 19
Key Insight From a program and policy, an instrumenter statically constrains labels to instrument DIFC code. 20
Key Payoffs of Constraints • Naturally express semantics, policies • Efficiently generate DIFC code • Provide useful debugging information 21
Instrumentation via Constraints • Generating constraints • Solving constraints 22
Generating Constraints 1. Legal 2. Secure 3. Functional 23
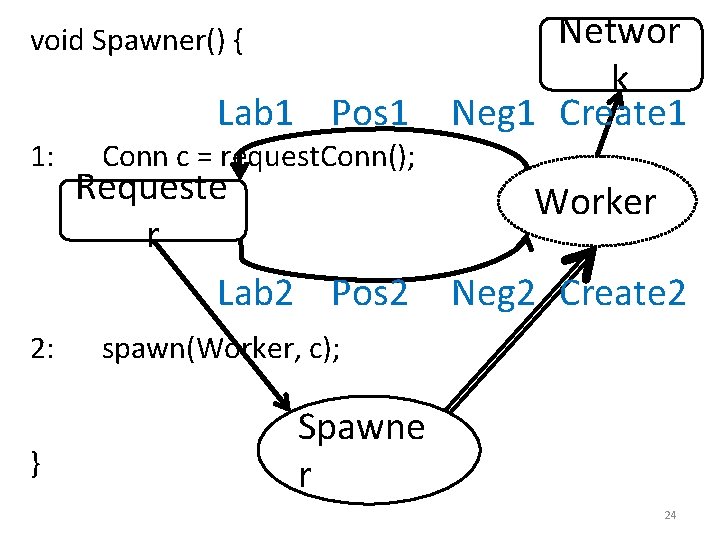
void Spawner() { 1: 2: } Lab 1 Pos 1 Conn c = request. Conn(); Requeste r Lab 2 Pos 2 Networ k Neg 1 Create 1 Worker Neg 2 Create 2 spawn(Worker, c); Spawne r 24
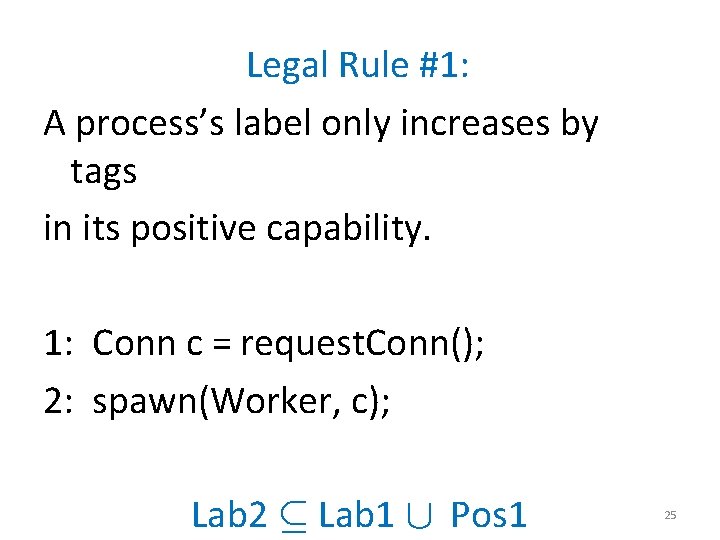
Legal Rule #1: A process’s label only increases by tags in its positive capability. 1: Conn c = request. Conn(); 2: spawn(Worker, c); Lab 2 µ Lab 1 [ Pos 1 25
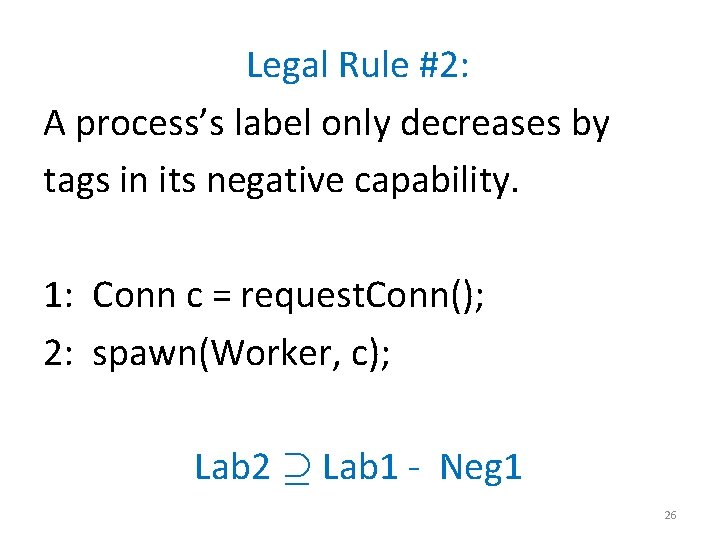
Legal Rule #2: A process’s label only decreases by tags in its negative capability. 1: Conn c = request. Conn(); 2: spawn(Worker, c); Lab 2 ¶ Lab 1 - Neg 1 26
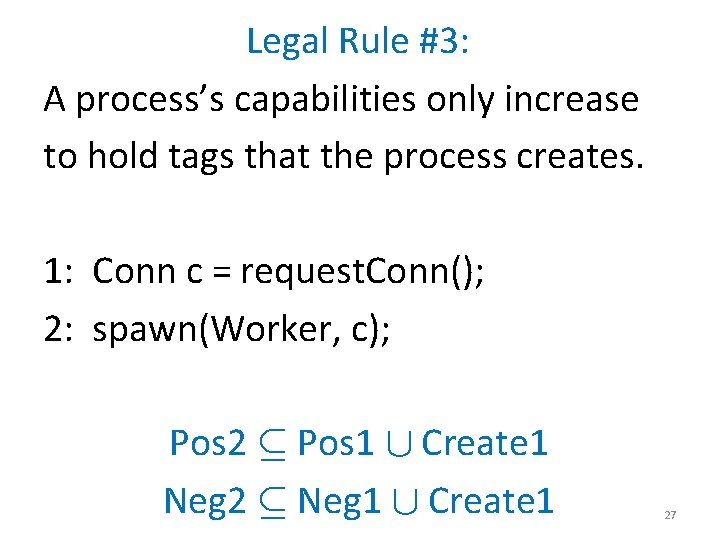
Legal Rule #3: A process’s capabilities only increase to hold tags that the process creates. 1: Conn c = request. Conn(); 2: spawn(Worker, c); Pos 2 µ Pos 1 [ Create 1 Neg 2 µ Neg 1 [ Create 1 27
Generating Constraints 1. Legal 2. Secure 3. Functional 28
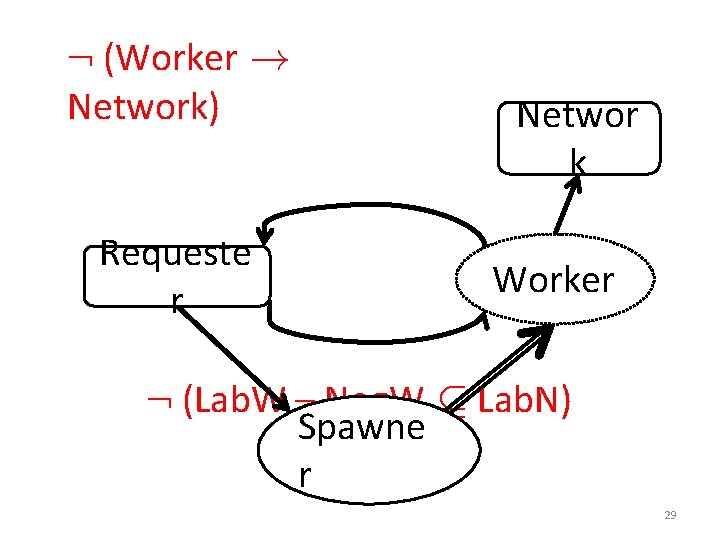
: (Worker ! Network) Requeste r Networ k Worker : (Lab. W – Neg. W µ Lab. N) Spawne r 29
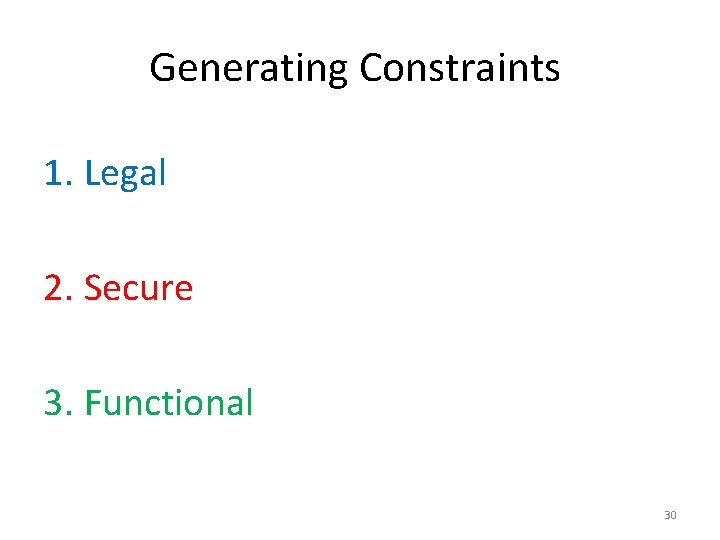
Generating Constraints 1. Legal 2. Secure 3. Functional 30
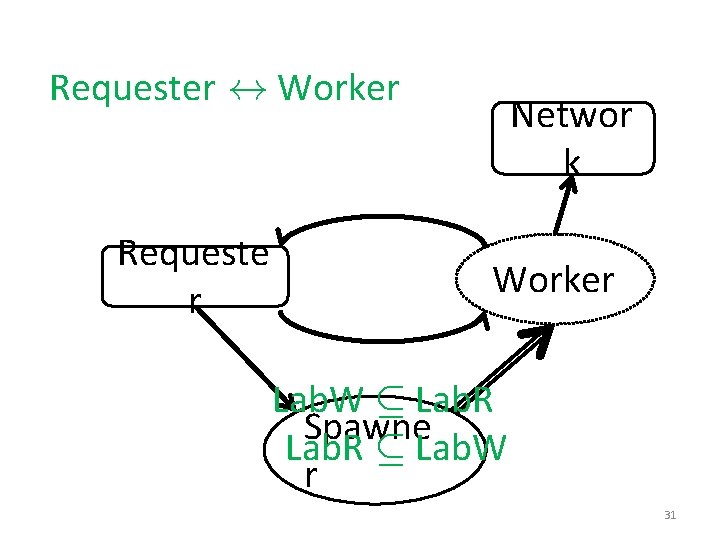
Requester $ Worker Requeste r Networ k Worker Lab. W µ Lab. R Spawne Lab. R µ Lab. W r 31
Instrumentation via Constraints • Generating constraints • Solving constraints 32
Solving Constraints • NP-complete in general • Amenable to SMT solvers in practice 33
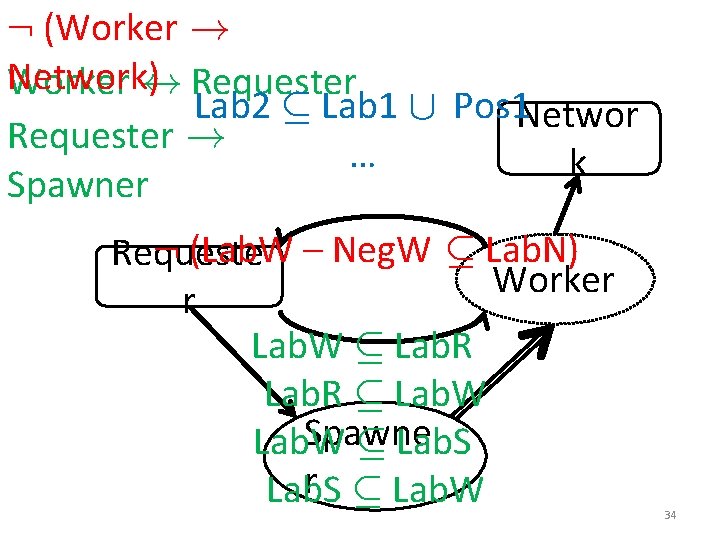
: (Worker ! Network) Worker $ Requester Lab 2 µ Lab 1 [ Pos 1 Networ Requester ! … k Spawner : (Lab. W – Neg. W µ Lab. N) Requeste Worker r Lab. W µ Lab. R µ Lab. W Spawne Lab. W µ Lab. S r µ Lab. W Lab. S 34
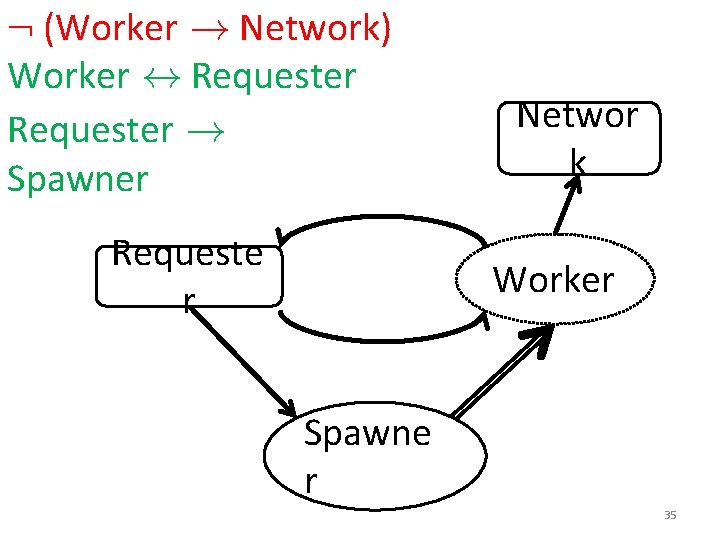
: (Worker ! Network) Worker $ Requester ! Spawner Requeste r Networ k Worker Spawne r 35
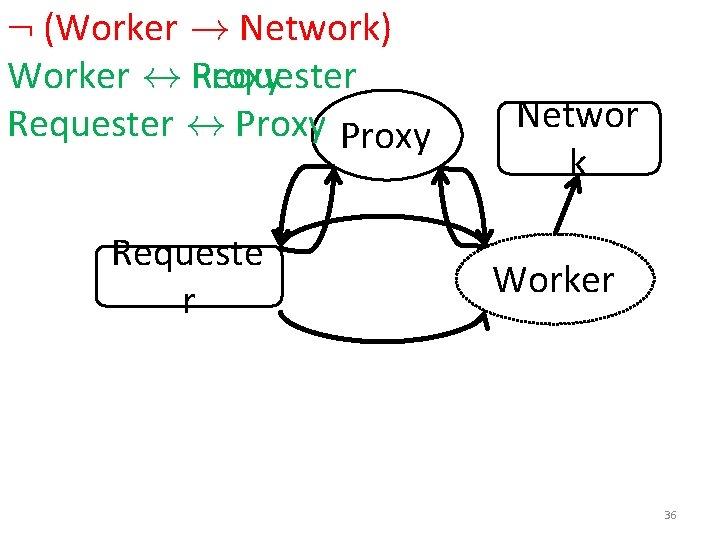
: (Worker ! Network) Worker $ Proxy Requester $ Proxy Requeste r Networ k Worker 36
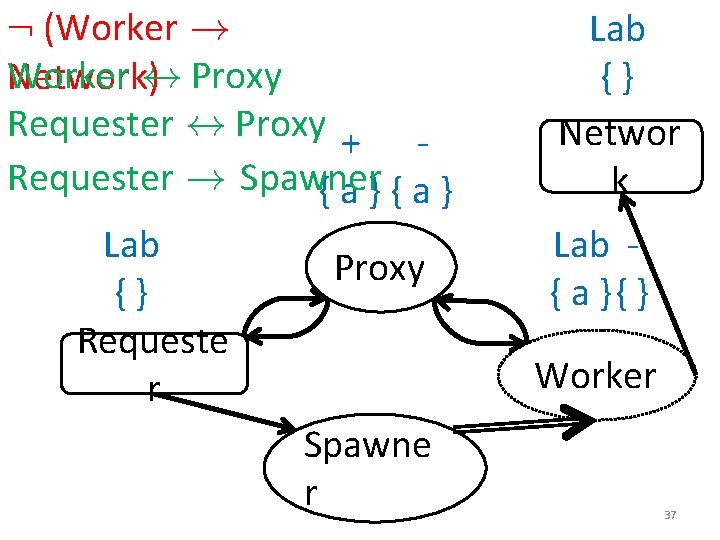
: (Worker ! Worker Network)$ Proxy Requester $ Proxy + Requester ! Spawner {a}{a} Lab {} Requeste r Proxy Lab {} Networ k Lab { a }{ } Worker Spawne r 37
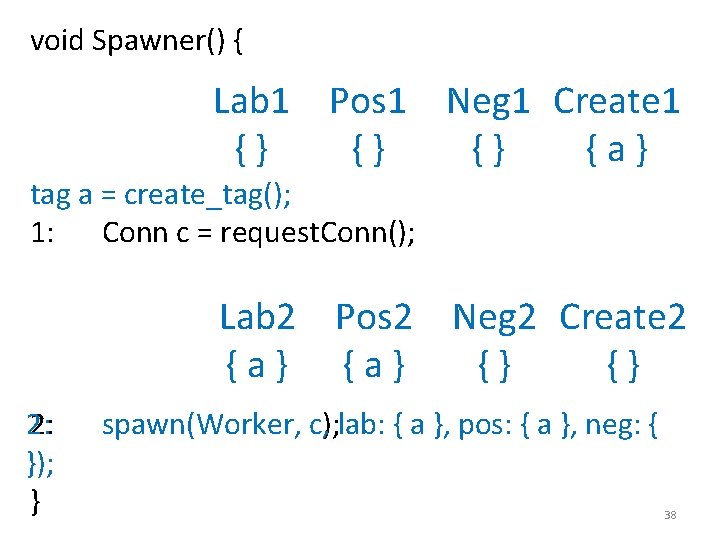
void Spawner() { Lab 1 Pos 1 Neg 1 Create 1 {} {} {} {a} tag a = create_tag(); 1: Conn c = request. Conn(); Lab 2 Pos 2 Neg 2 Create 2 {a} {} {} 2: 2: }); } c); lab: { a }, pos: { a }, neg: { spawn(Worker, c, 38
Outline • Challenge of instrumentation • Instrumentation via constraints • Case studies 39
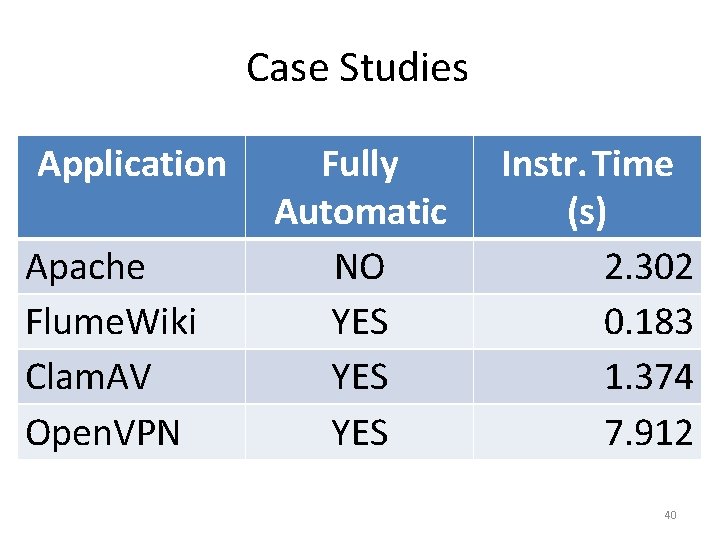
Case Studies Application Apache Flume. Wiki Clam. AV Open. VPN Fully Automatic NO YES YES Instr. Time (s) 2. 302 0. 183 1. 374 7. 912 40
Conclusion Program Security Policy Instrumenter Secure Program 41
Thanks for listening! 42
Conclusion Program Security Policy Instrumenter Secure Program 43
Extra Slides 44
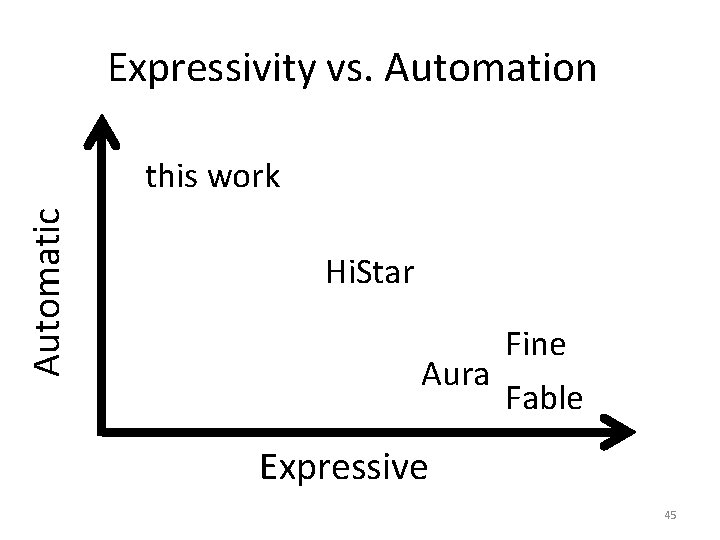
Expressivity vs. Automation Automatic this work Hi. Star Fine Aura Fable Expressive 45

46
Challenge for DIFC Programmers • Semantic gap from policy to DIFC code • Instrumenting legacy code 47
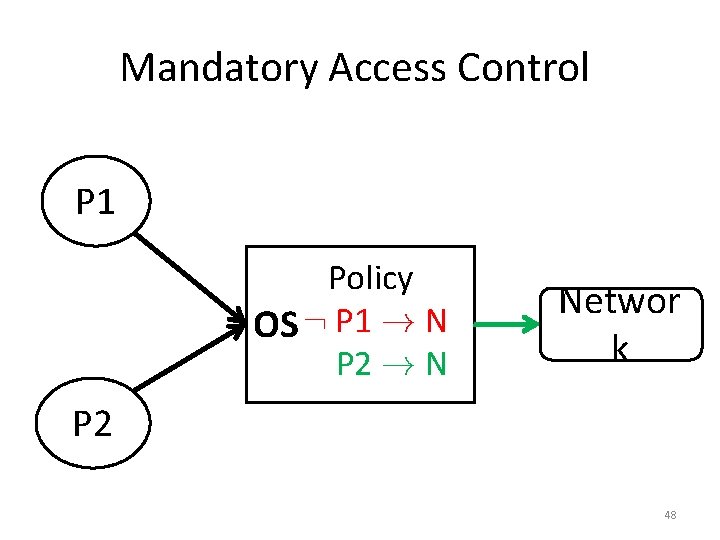
Mandatory Access Control P 1 Policy OS : P 1 ! N P 2 ! N Networ k P 2 48
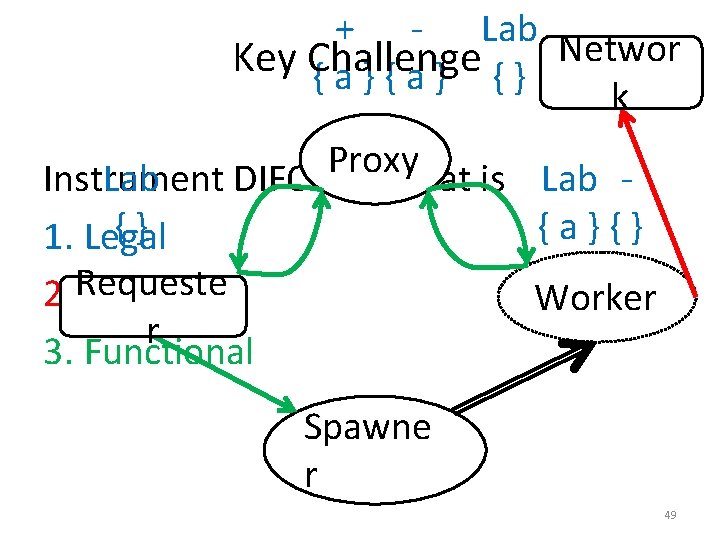
+ - Lab Networ Key Challenge {a}{a} {} k Proxy Instrument Lab DIFC code that is Lab {} {a}{} 1. Legal 2. Requeste Secure Worker r 3. Functional Spawne r 49
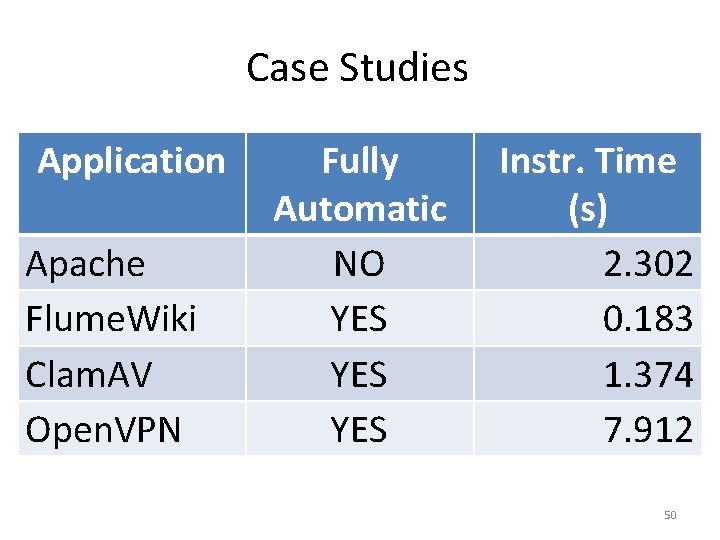
Case Studies Application Apache Flume. Wiki Clam. AV Open. VPN Fully Automatic NO YES YES Instr. Time (s) 2. 302 0. 183 1. 374 7. 912 50
- Slides: 50