Demo Research Progress and Plans Bharat Bhargava With
Demo, Research Progress and Plans Bharat Bhargava With students P. Angin, R. Ranchal, R. Sivakumar, N. Idika, M. Azarmi, L. Othmane bbshail@purdue. edu 765 -413 -7312 CERIAS and Department of Computer Science Purdue University West Lafayette, Indiana http: //www. cs. purdue. edu/homes/rranchal/NGC_Sep_2010. ppt Purdue University, Sep 9, 2010
Outline 1. 2. 3. 4. 5. 6. 7. Privacy in Cloud Active Bundle Scheme for Privacy in Cloud Demo 1. Active Bundle Policy Enforcement Demo 2. Publisher-Subscriber Model based on Active Bundles Demo 3. Mobile Agent based Active Bundles Future Directions: Collaborative Whitepaper Scope Privacy and Identity Management in Cloud Computing 2
Privacy in Cloud Computing 3
Privacy and issues in Cloud • Cloud SP is a third party that maintains information about, or on behalf of, another entity. • Whenever an entity shares information in the cloud, privacy or confidentiality questions may arise Issues 1. Loss of control: Data, applications, and resources are located with SP. 2. Lack of trust: Trusting a third party requires taking risks. 3. Multi-tenancy: Tenants share resources and may have opposing goals which could be conflicting. Cloud Computing spawns huge risks such as: • Expected losses from a single breach can be significantly large; and • The heterogeneity of “users” represents an opportunity of multiple collaborative threats. 4
Active Bundle Scheme for Privacy • Proposed solution for protecting data privacy Keep data encapsulated in a data protection mechanism • Active bundle (AB) AB – An encapsulating mechanism that protects data and computation carried within it – Includes metadata to be used for managing privacy • Both privacy of carried data and privacy of the whole AB – Able to perform a set of operations protecting its privacy – Uses its own disseminated protocol • ABs can be used to provide privacy protection for the full data lifecycle 5
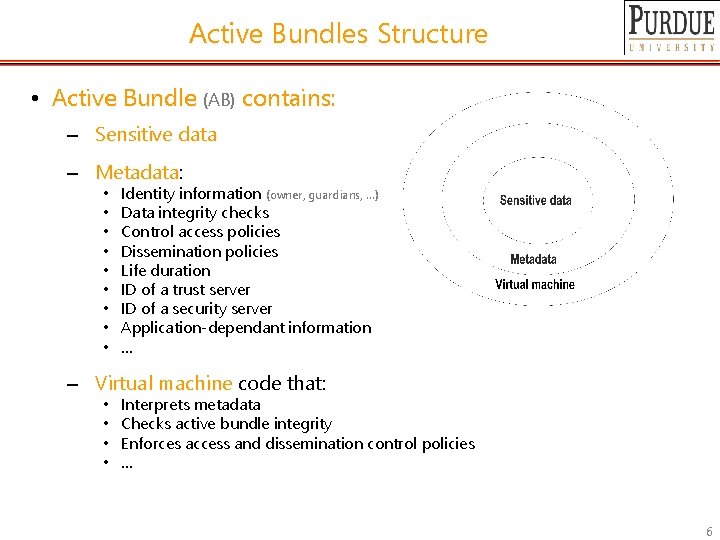
Active Bundles Structure • Active Bundle (AB) contains: – Sensitive data – Metadata: Metadata • • • Identity information (owner, guardians, …) Data integrity checks Control access policies Dissemination policies Life duration ID of a trust server ID of a security server Application-dependant information … – Virtual machine code that: • • Interprets metadata Checks active bundle integrity Enforces access and dissemination control policies … 6
Active Bundles Operations • Active Bundles—Operations – Self-Integrity check E. g. , Uses a hash function – Decoy Spreads decoy data to deflect attention away from the AB – Evaporation Self-destroys (a part of) AB’s sensitive data when threatened with a disclosure – Apoptosis Self-destructs AB’s sensitive data and metadata 7
DEMO- Active Bundle Policy Enforcement 8
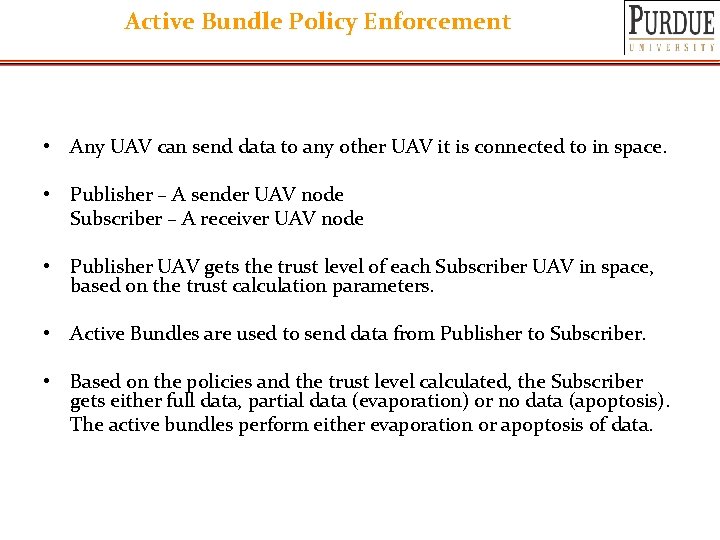
Active Bundle Policy Enforcement • Any UAV can send data to any other UAV it is connected to in space. • Publisher – A sender UAV node Subscriber – A receiver UAV node • Publisher UAV gets the trust level of each Subscriber UAV in space, based on the trust calculation parameters. • Active Bundles are used to send data from Publisher to Subscriber. • Based on the policies and the trust level calculated, the Subscriber gets either full data, partial data (evaporation) or no data (apoptosis). The active bundles perform either evaporation or apoptosis of data.
Parameters for Trust Calculation • Location Example: USA, Middle East, Iraq etc. • Security Clearance Example: Top-secret, Secret, Confidential, Unclassified • Bandwidth Example: High Bandwidth, Low Bandwidth • Obligation Example: Met, Not met • Distance Example: Very near, Near, Far, Very Far
Parameters for Trust Calculation (contd. ) • Color Example: Friend, Enemy, Unknown • Authentication Level Example: Fully authenticated, Partially authenticated, Not authenticated. • Context Example: Emergency, Disaster, Normal etc. • Subscriber’s History Example: Good transactions vs. Bad transactions
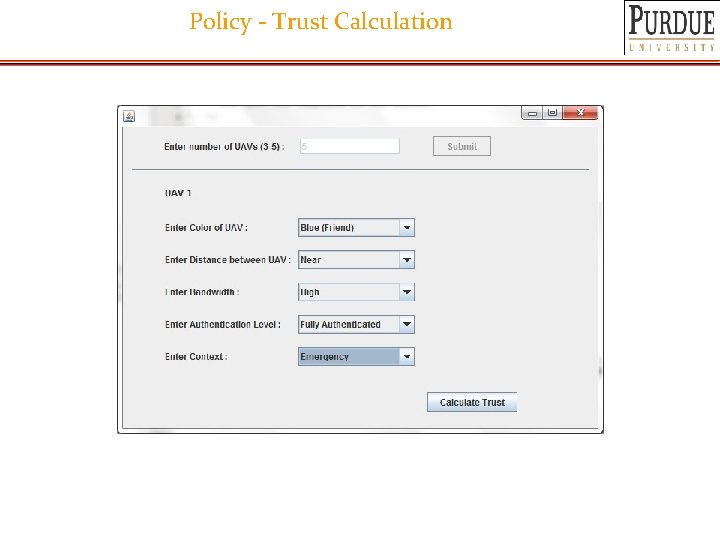
Policy - Trust Calculation
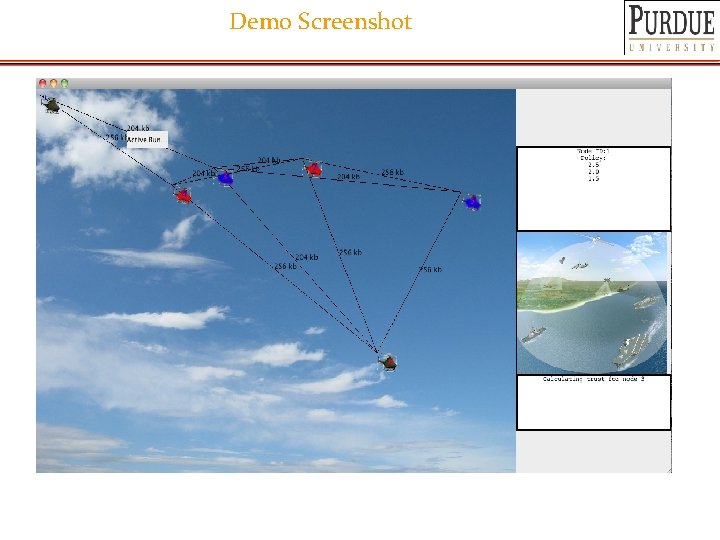
Demo Screenshot
Examples of Policy Enforcement 14
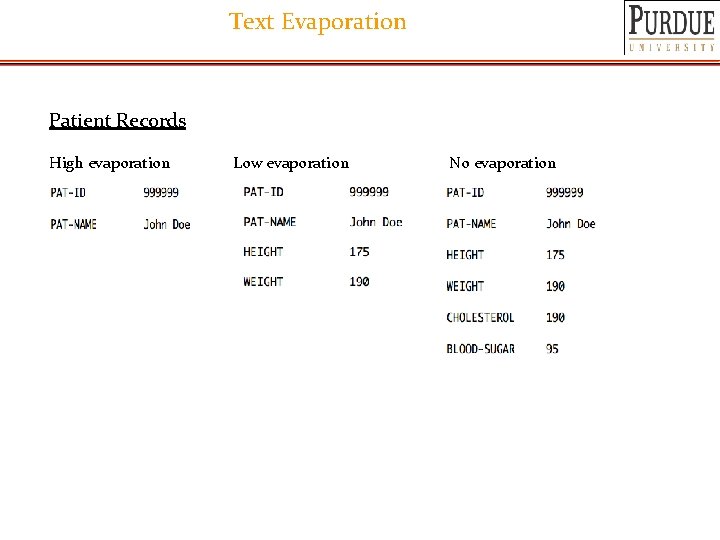
Text Evaporation Patient Records High evaporation Low evaporation No evaporation
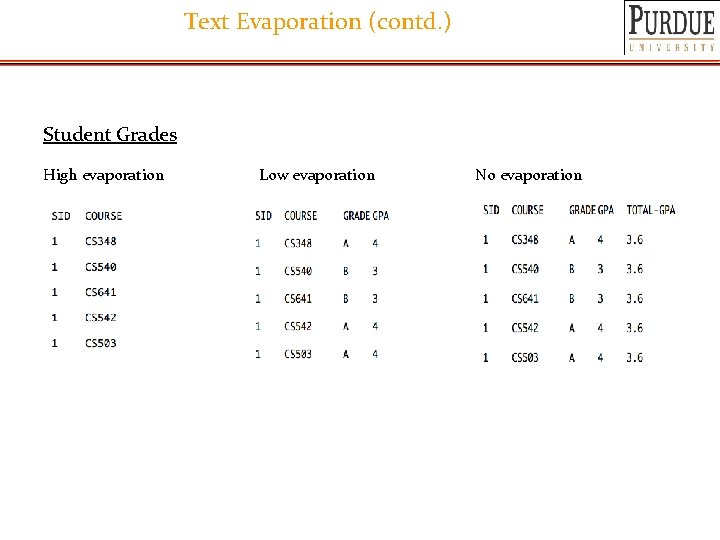
Text Evaporation (contd. ) Student Grades High evaporation Low evaporation No evaporation
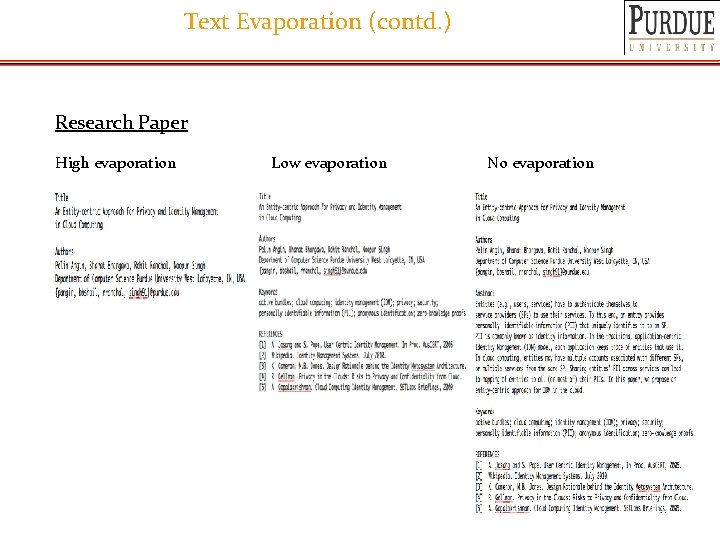
Text Evaporation (contd. ) Research Paper High evaporation Low evaporation No evaporation
Publisher-Subscriber Model Demo 18
Demo Architecture • Publish-Subscriber model • Information broker will mediate all interactions among publishers and subscribers • Policy model: – Publisher policy – Subscriber policy • Policy assessment and comparison in ABs
Mobile Agent based Active Bundle Demo 20
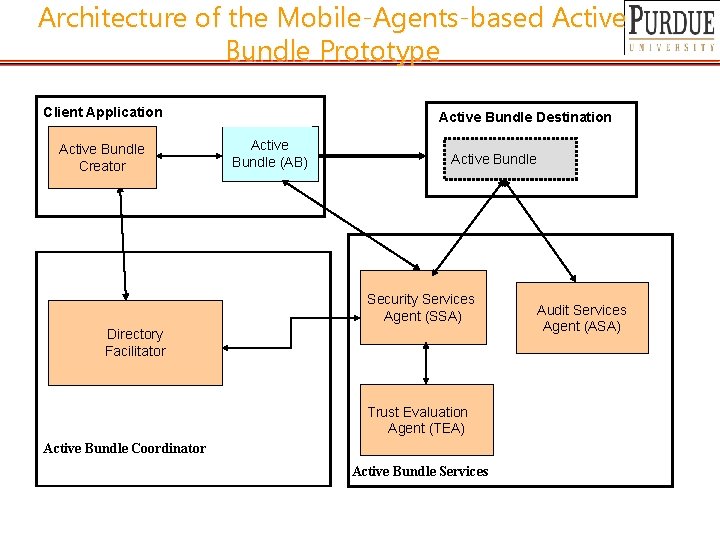
Architecture of the Mobile-Agents-based Active Bundle Prototype Client Application Active Bundle Creator Bundle. Destination Active Bundle (AB) Active Bundle Security Services Agent (SSA) Directory Facilitator Trust Evaluation Agent (TEA) Active Bundle Coordinator Active Bundle Services Audit Services Agent (ASA)
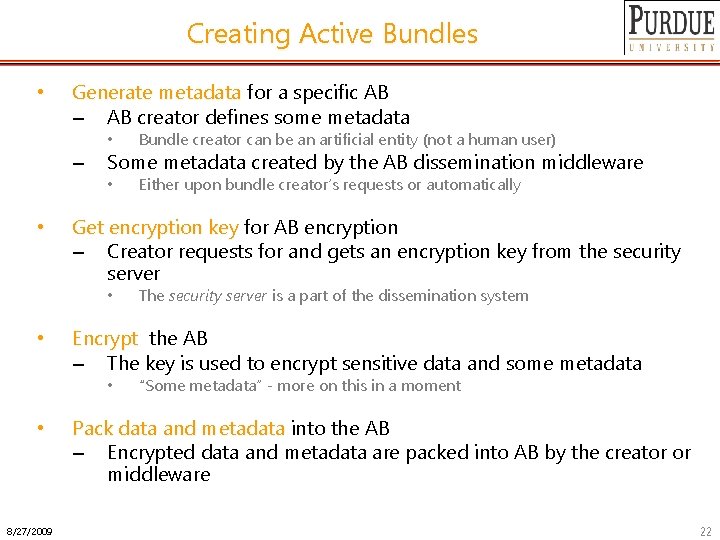
Creating Active Bundles • Generate metadata for a specific AB – AB creator defines some metadata – • • Bundle creator can be an artificial entity (not a human user) • Either upon bundle creator’s requests or automatically Some metadata created by the AB dissemination middleware Get encryption key for AB encryption – Creator requests for and gets an encryption key from the security server • • Encrypt the AB – The key is used to encrypt sensitive data and some metadata • • 8/27/2009 The security server is a part of the dissemination system “Some metadata” - more on this in a moment Pack data and metadata into the AB – Encrypted data and metadata are packed into AB by the creator or middleware 22
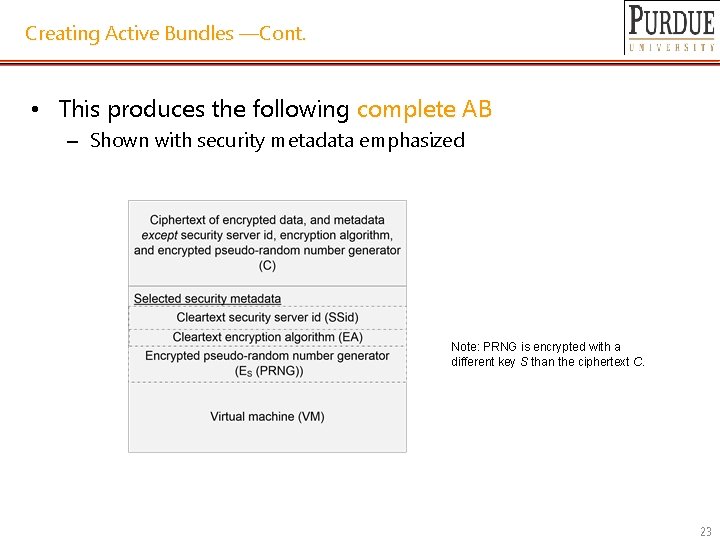
Creating Active Bundles —Cont. • This produces the following complete AB – Shown with security metadata emphasized Note: PRNG is encrypted with a different key S than the ciphertext C. 23
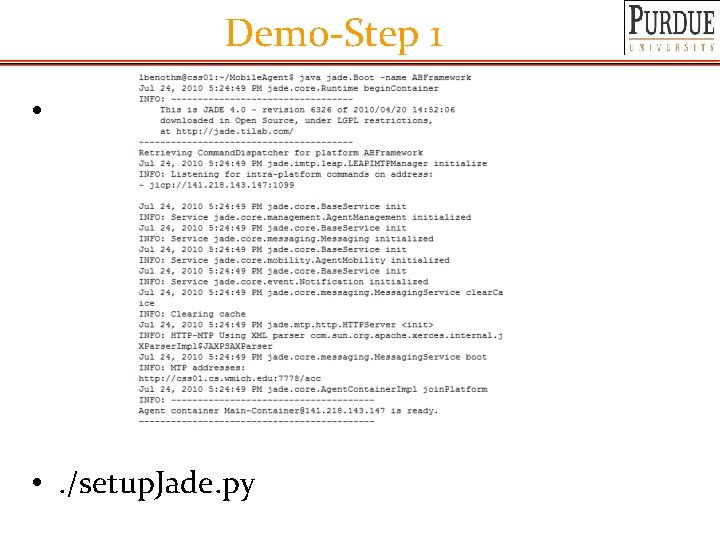
Demo-Step 1 • • . /setup. Jade. py
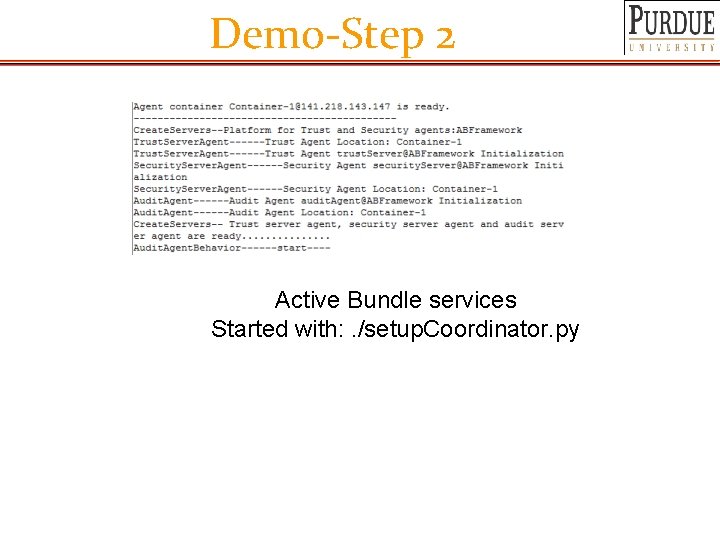
Demo-Step 2 Active Bundle services Started with: . /setup. Coordinator. py
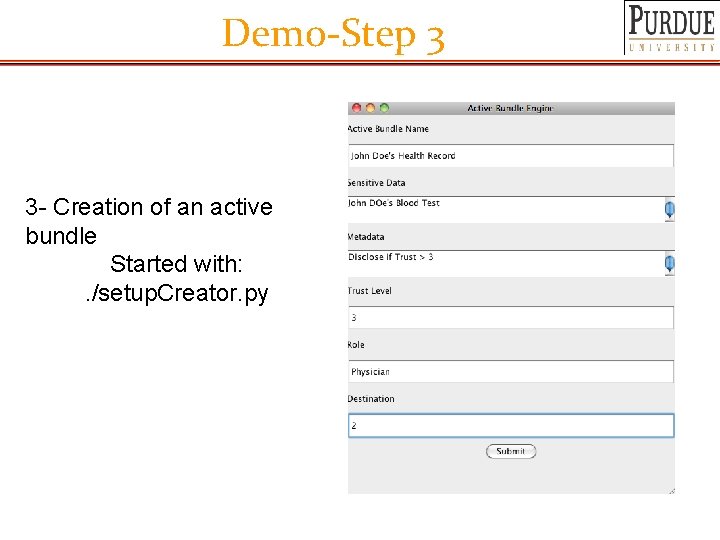
Demo-Step 3 3 - Creation of an active bundle Started with: . /setup. Creator. py
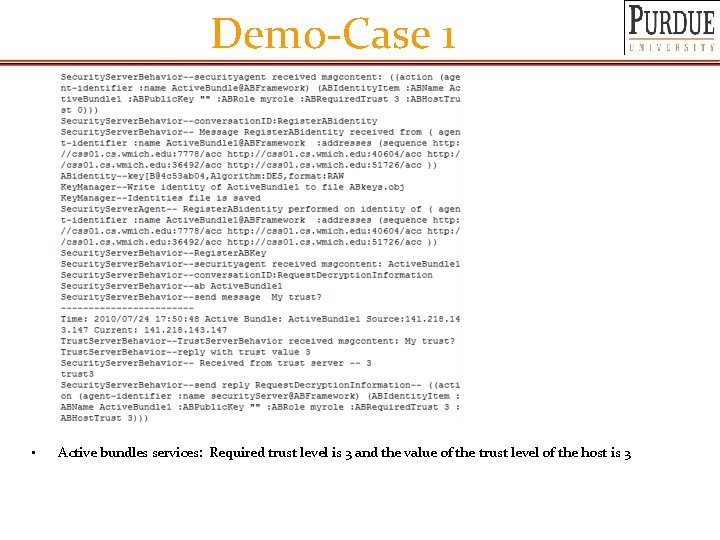
Demo-Case 1 • Active bundles services: Required trust level is 3 and the value of the trust level of the host is 3
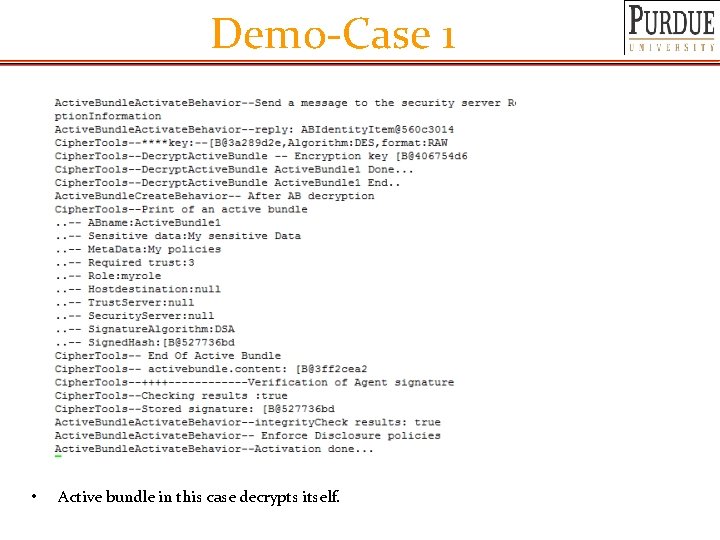
Demo-Case 1 • Active bundle in this case decrypts itself.
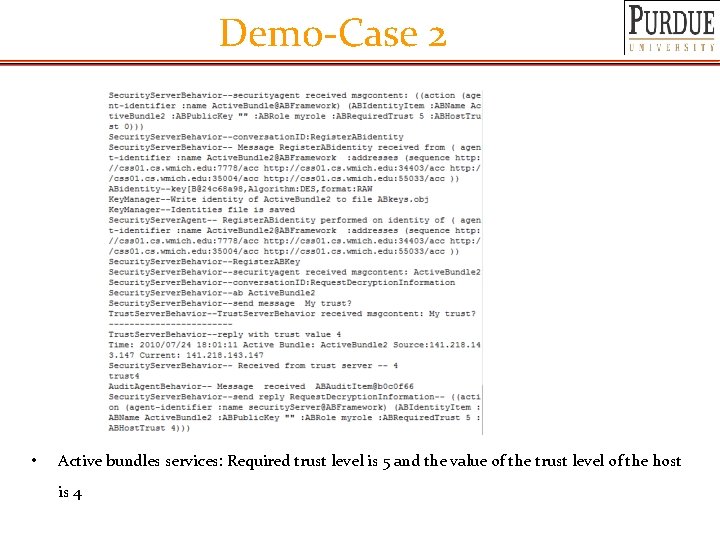
Demo-Case 2 • Active bundles services: Required trust level is 5 and the value of the trust level of the host is 4
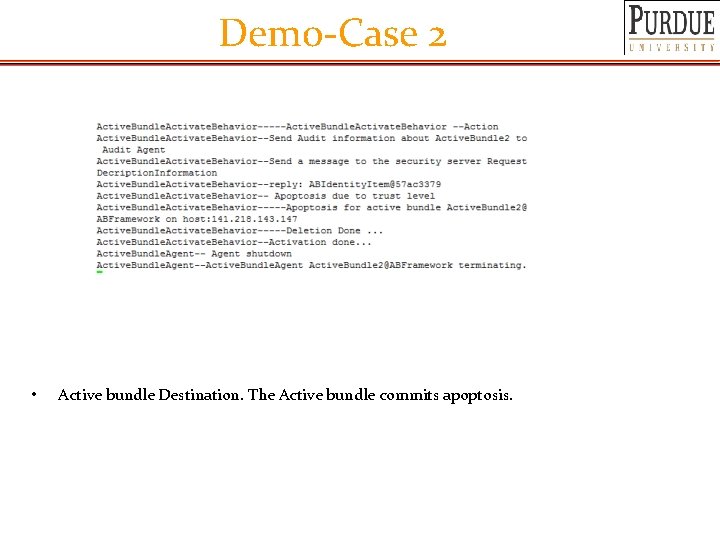
Demo-Case 2 • Active bundle Destination. The Active bundle commits apoptosis.
Future Directions 31
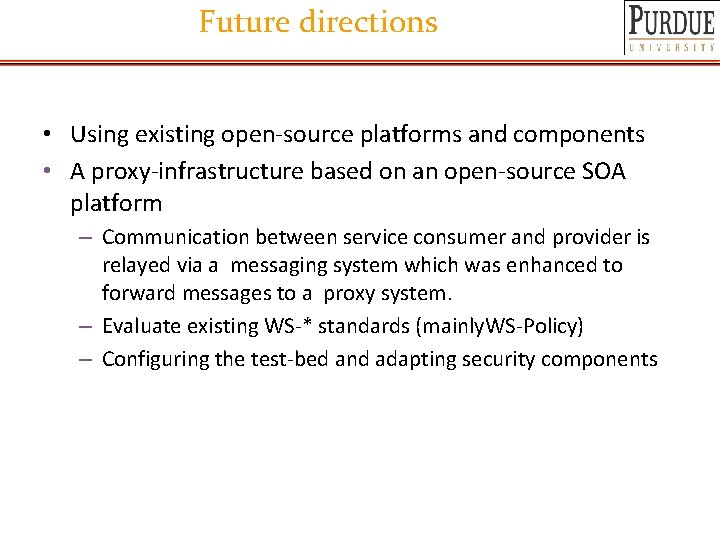
Future directions • Using existing open-source platforms and components • A proxy-infrastructure based on an open-source SOA platform – Communication between service consumer and provider is relayed via a messaging system which was enhanced to forward messages to a proxy system. – Evaluate existing WS-* standards (mainly. WS-Policy) – Configuring the test-bed and adapting security components
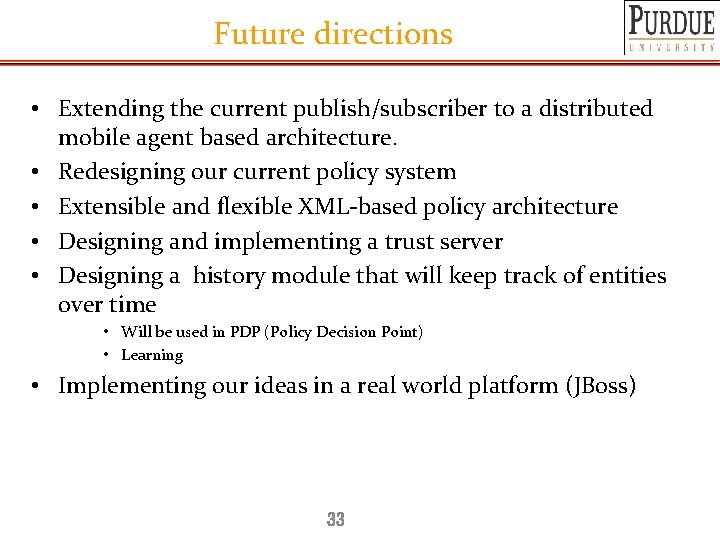
Future directions • Extending the current publish/subscriber to a distributed mobile agent based architecture. • Redesigning our current policy system • Extensible and flexible XML-based policy architecture • Designing and implementing a trust server • Designing a history module that will keep track of entities over time • Will be used in PDP (Policy Decision Point) • Learning • Implementing our ideas in a real world platform (JBoss) 33
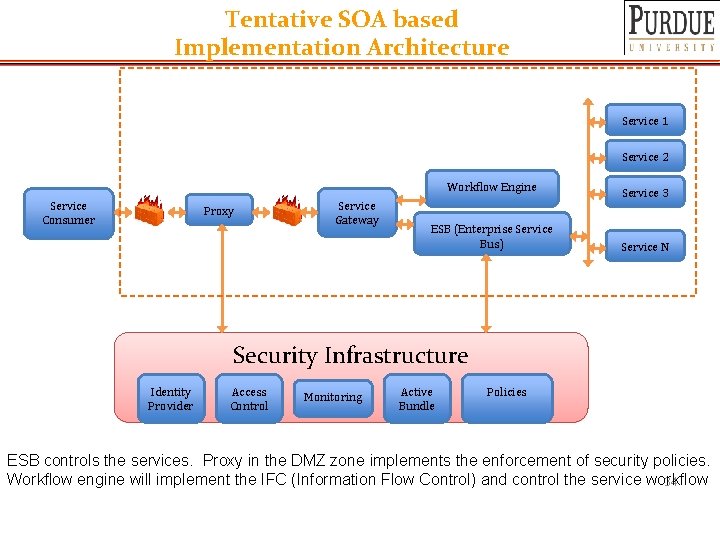
Tentative SOA based Implementation Architecture Service 1 Service 2 Service Consumer Proxy Service Gateway Workflow Engine Service 3 ESB (Enterprise Service Bus) Service N Security Infrastructure Identity Provider Access Control Monitoring Active Bundle Policies ESB controls the services. Proxy in the DMZ zone implements the enforcement of security policies. Workflow engine will implement the IFC (Information Flow Control) and control the service workflow 34
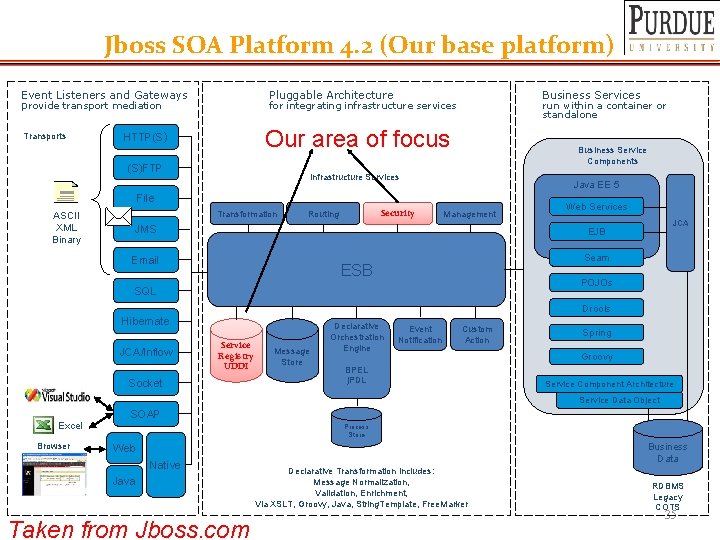
Jboss SOA Platform 4. 2 (Our base platform) Event Listeners and Gateways provide transport mediation Transports Pluggable Architecture Business Services for integrating infrastructure services run within a container or standalone Our area of focus HTTP(S) (S)FTP Business Service Components Infrastructure Services Java EE 5 File ASCII XML Binary Transformation Security Routing Management JMS Web Services JCA EJB Email Seam ESB POJOs SQL Drools Hibernate JCA/Inflow Service Registry UDDI Socket Message Store Declarative Orchestration Engine Event Notification Custom Action BPEL j. PDL Spring Groovy Service Component Architecture Service Data Object SOAP Excel Browser Process Store Business Data Web Native Java Taken from Jboss. com Declarative Transformation includes: Message Normalization, Validation, Enrichment, Via XSLT, Groovy, Java, String. Template, Free. Marker RDBMS Legacy COTS 35
Privacy and Identity Management in Cloud 36
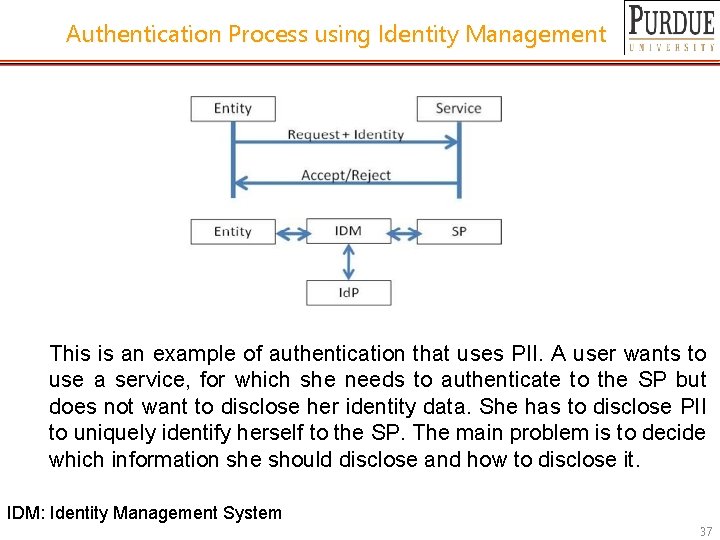
Authentication Process using Identity Management This is an example of authentication that uses PII. A user wants to use a service, for which she needs to authenticate to the SP but does not want to disclose her identity data. She has to disclose PII to uniquely identify herself to the SP. The main problem is to decide which information she should disclose and how to disclose it. IDM: Identity Management System 37
IDM in Cloud In the traditional application-centric IDM model -Each application keeps trace of identities of the entities that use it. In cloud computing-Entities have multiple accounts associated with a single or multiple service providers (SPs). -Sharing sensitive identity information along with associated attributes of the same entity across services can lead to mapping of the identities to the entity 38
Related Work: Overview Identity Information for Negotiation can be sent as: • Token/Pseudonym • Identity Information in clear plain text • Active Bundle Related Work: • Open. ID • Microsoft Windows Card. Space • PRIME All these systems require a trusted third party and do not work on untrusted host 39
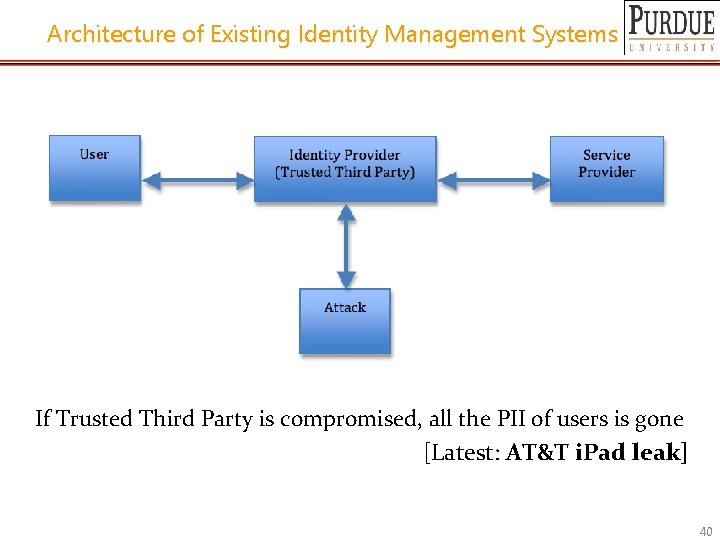
Architecture of Existing Identity Management Systems If Trusted Third Party is compromised, all the PII of users is gone [Latest: AT&T i. Pad leak] 40
Problems of Identity Management Problems in Focus: 1. Authenticate without disclosing data (unencrypted data) 2. Use service on untrusted hosts by getting authenticated based on identity data (hosts not owned by user) 3. Minimize risk of disclosure during communication between user and service provider (protect from Side Channel and Correlation Attacks) 4. Independence of Trusted Third Party 41
Selected Research Problems • • Authenticate without disclosing data (unencrypted data) As soon as the data is decrypted it become prone to attacks. This is particularly of a concern if the provider decides to store this data. Use service on untrusted hosts (hosts not owned by user) Minimal disclosure and minimize risk of disclosure during communication between user and service provider (protect from Side Channel and Correlation Attacks) Independence of TTPs 42
Characteristics of the Proposed IDM Characteristics of proposed solution: 1. Authenticate without disclosing unencrypted data (such as Passwords/Keys) (use predicate over encrypted data) 2. Ability to use Identity data on untrusted hosts • • • Self Integrity Check Integrity compromised- apoptosis or evaporation Data should not be on this host 3. Prevention from Correlation Attacks since the exchange of data from Active Bundle to host is local to the host. 43
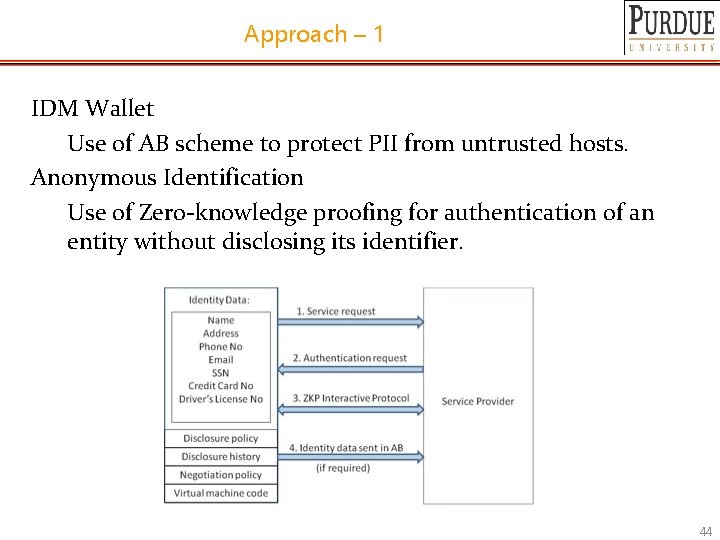
Approach – 1 IDM Wallet Use of AB scheme to protect PII from untrusted hosts. Anonymous Identification Use of Zero-knowledge proofing for authentication of an entity without disclosing its identifier. 44
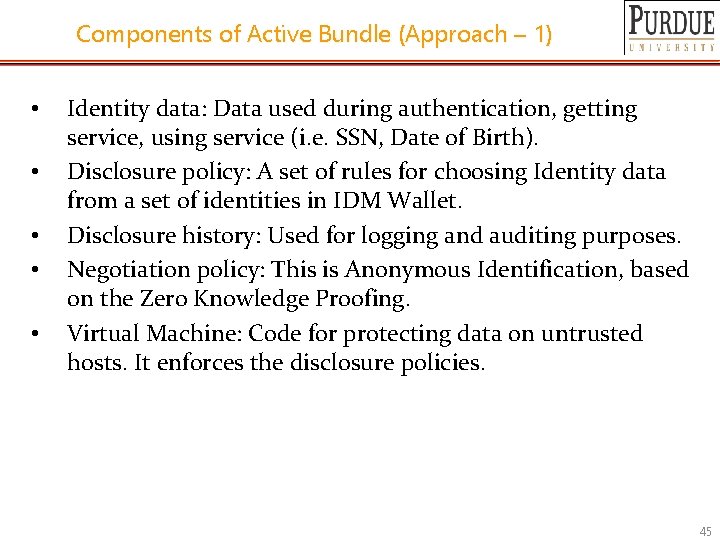
Components of Active Bundle (Approach – 1) • • • Identity data: Data used during authentication, getting service, using service (i. e. SSN, Date of Birth). Disclosure policy: A set of rules for choosing Identity data from a set of identities in IDM Wallet. Disclosure history: Used for logging and auditing purposes. Negotiation policy: This is Anonymous Identification, based on the Zero Knowledge Proofing. Virtual Machine: Code for protecting data on untrusted hosts. It enforces the disclosure policies. 45
Anonymous Identification (Approach – 1) Anonymous Identification (Shamir's approach for Credit Cards) • • Id. P provides Encrypted Identity Information to the user and SP. SP and User interact Both run Id. P's public function on the certain bits of the Encrypted data. Both exchange results and agree if it matches. 46
Working (Approach – 1) 1. An entity requests a service from an SP (e. g. , a website). 2. SP informs the entity, user must authenticate and provide its identity information (if required). 3. IDM Wallet uses its policy and determines what claims it should issue given the proof supplied by the claimant and the policy requirements of the SP. 4. IDM Wallet runs an interactive protocol based on Anonymous Identification with the SP for authentication. 5. If further required by SP, IDM Wallet creates an AB token and forwards it to the SP. SP then uses its technical policy to decide whether to recognize (authenticate) the user and provide the service. 47
Approach – 2 • Use of AB scheme to protect PII from untrusted hosts • Use of Predicates over encrypted data to authenticate without disclosing unencrypted identity data. 48
Working (Approach – 2) • • • Owner O encrypts Identity Data(PII) using algorithm Encrypt and O’s public key PK. Encrypt outputs CT—the encrypted PII. SP transforms his request for PII to a predicate represented by function p. SP sends shares of p to the n parties who hold the shares of MSK. n parties execute together Key. Gen using PK, MSK, and p, and return TKp to SP. SP calls the algorithm Query that takes as input PK, CT, TKp and produces p(PII) which is the evaluation of the predicate. The owner O is allowed to use the service only when the predicate evaluates to “true”. 49
Characteristics and Advantages • • • Ability to use Identity data on untrusted hosts. It has a selfintegrity check to find if the data is tampered. If the integrity is compromised, it will destroy the data itself by doing apoptosis or evaporation to protect it from falling into wrong hands. Independent of third party. This prevents correlation attacks, man in the middle attacks, side-channel attacks and protects from the problem of third party being compromised, since the exchange of data from AB to host is local to the host. It increases the trust by putting the user in control of who has his data and how it is being used in the process of authentication, negotiation, and data exchange. Gives minimum information to the SP. SP receives only necessary information. 50
![References [Sample et al. 2009] C. Sample, D. Kelley. Cloud Computing Security: Routing and References [Sample et al. 2009] C. Sample, D. Kelley. Cloud Computing Security: Routing and](http://slidetodoc.com/presentation_image_h2/3ebfdcc7c08a8ed80e96cc1c3be47a07/image-51.jpg)
References [Sample et al. 2009] C. Sample, D. Kelley. Cloud Computing Security: Routing and DNS Threats, http: //www. securitycurve. com/wordpress/, June 23, 2009 [Alrodhan et al. 2009] W. A. Alrodhan, C. J. Mitchell, Improving the Security of Card. Space, EURASIP Journal on Information Security Vol. 2009, doi: 10. 1155/2009/167216, 2009. [Simone et al. 2008] S. F. Hubner, HCI work in PRIME, https: //www. primeproject. eu/, 2008. [Gopala et al. 2009] A. Gopalakrishnan. Cloud Computing Identity Management. SETLabs. Briefings, Vol 7, http: //www. infosys. com/research/, 2009. [Laurie et al. 2007] B. Laurie. Selective Disclosure, http: //research. google. com/pubs/author 9639. html/, May 11, 2007. [Barth et al. 2006] A. Barth, A. Datta, J. Mitchell and H. Nissenbaum, “Privacy and Contextual Integrity: Framework and Applications”, Proc. of the 2006 IEEE Symposium on Security and Privacy, 184 -198 [Barth et al. 2007] Adam Barth, Anupam Datta, John C. Mitchell, sharada sundaram. "Privacy and Utility in Business Processes". Proceedings of 20 th IEEE Computer Security Foundations Symposium, July, 2007 51
- Slides: 51