Cryptography and Network Security Chapter 2 Fifth Edition
- Slides: 49
Cryptography and Network Security Chapter 2 Fifth Edition by William Stallings Lecture slides by Lawrie Brown
Contents u Symmetric Cipher Model u Substitution Techniques u Transposition Techniques u Rotor Machines u Steganography
Ciphers u Symmetric cipher: same key used for encryption and decryption – Block cipher: encrypts a block of plaintext at a time (typically 64 or 128 bits) – Stream cipher: encrypts data one bit or one byte at a time u Asymmetric cipher: different keys used for encryption and decryption 3
Symmetric Encryption u or conventional / private-key / single-key u sender and recipient share a common key u all classical encryption algorithms are private-key u was only type prior to invention of public-key in 1970’s u and by far most widely used
Some Basic Terminology u plaintext - original message u ciphertext - coded message u cipher - algorithm for transforming plaintext to ciphertext u key - info used in cipher known only to sender/receiver u encipher (encrypt) - converting plaintext to ciphertext u decipher (decrypt) - recovering ciphertext from plaintext u cryptography - study of encryption principles/methods u cryptanalysis (codebreaking) - study of principles/ methods of deciphering ciphertext without knowing key u cryptology - field of both cryptography and cryptanalysis
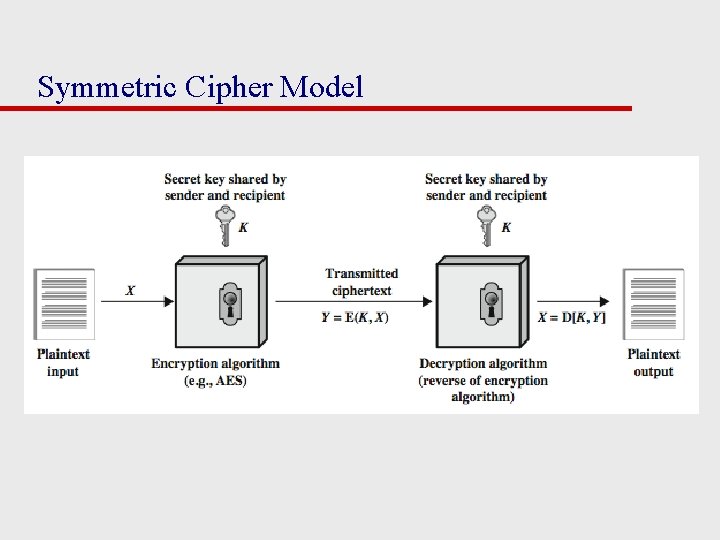
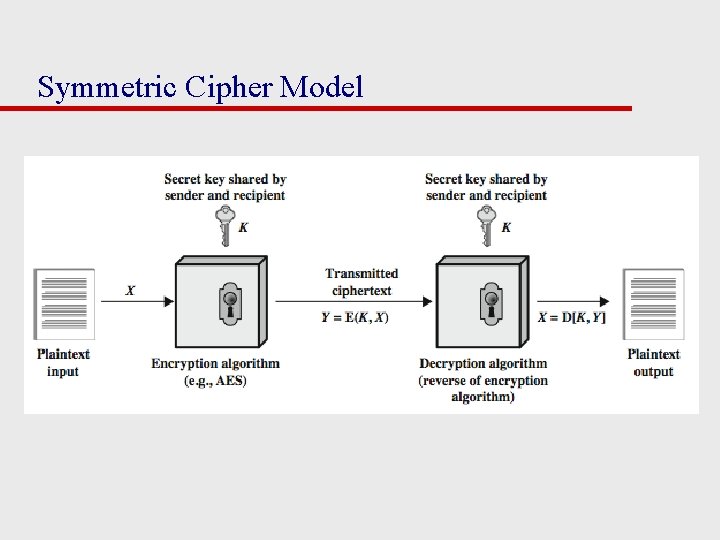
Symmetric Cipher Model
Requirements and Assumptions u Requirements for secure use of symmetric encryption: 1. Strong encryption algorithm: Given the algorithm and ciphertext, an attacker cannot obtain key or plaintext 2. Sender/receiver know secret key (and keep it secret) u Assumptions: 1. Cipher is known 2. Secure channel to distribute keys
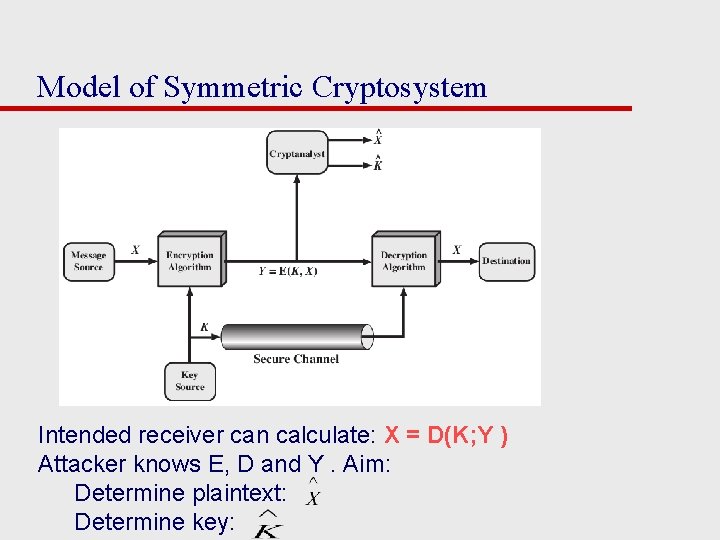
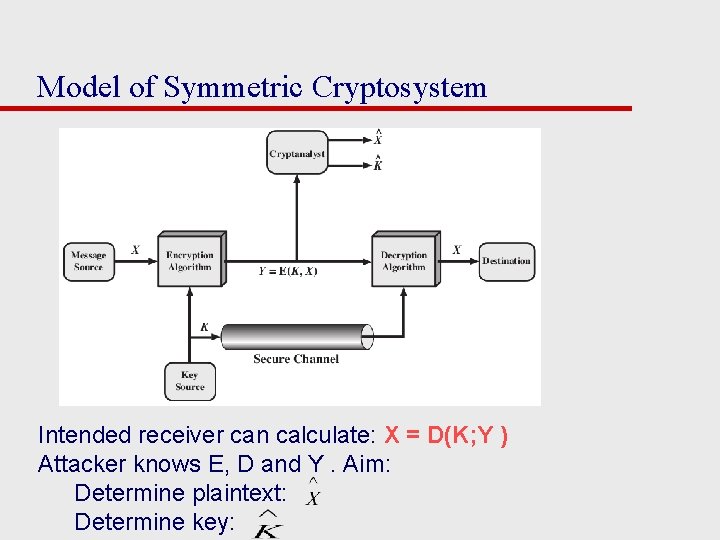
Model of Symmetric Cryptosystem Intended receiver can calculate: X = D(K; Y ) Attacker knows E, D and Y. Aim: Determine plaintext: Determine key:
Characterising Cryptographic Systems u Operations used for encryption: – Substitution replace one element in plaintext with another – Transposition re-arrange elements – Product systems multiple stages of substitutions and transpositions u Number of keys used: – Symmetric sender/receiver use same key (single-key, secret-key, shared -key, conventional) – Public-key sender/receiver use different keys (asymmetric) u Processing of plaintext: – Block cipher process one block of elements at a time – Stream cipher process input elements continuously
Cryptanalysis u Objective of attacker: recover key (not just message) u Approaches of attacker: – Cryptanalysis Exploit characteristics of algorithm to deduce plaintext or key – Brute-force attack Try every possible key on ciphertext until intelligible translation into plaintext obtained u If either attack finds key, all future/past messages are compromised
Cryptanalytic Attacks u ciphertext only – only know algorithm & ciphertext, is statistical, know or can identify plaintext u known plaintext – know/suspect plaintext & ciphertext u chosen plaintext – select plaintext and obtain ciphertext u chosen ciphertext – select ciphertext and obtain plaintext u chosen text – select plaintext or ciphertext to en/decrypt
Measures of Security u Unconditionally Secure – Ciphertext does not contained enough information to derive plaintext or key – One-time pad is only unconditionally secure cipher (but not very practical) u Computationally Secure – If either: » Cost of breaking cipher exceeds value of encrypted information » Time required to break cipher exceeds useful lifetime of encrypted information – Hard to estimate value/lifetime of some information – Hard to estimate how much effort needed to break cipher
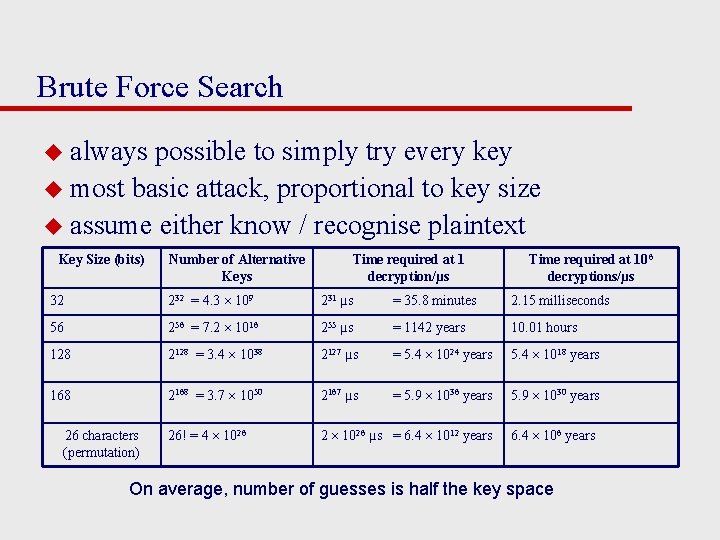
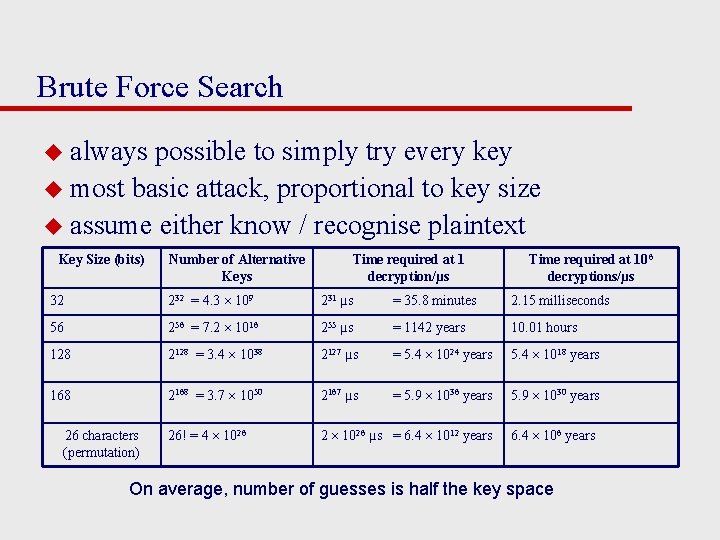
Brute Force Search u always possible to simply try every key u most basic attack, proportional to key size u assume either know / recognise plaintext Key Size (bits) Number of Alternative Keys Time required at 1 decryption/µs Time required at 106 decryptions/µs 32 232 = 4. 3 109 231 µs = 35. 8 minutes 2. 15 milliseconds 56 256 = 7. 2 1016 255 µs = 1142 years 10. 01 hours 128 2128 = 3. 4 1038 2127 µs = 5. 4 1024 years 5. 4 1018 years 168 2168 = 3. 7 1050 2167 µs = 5. 9 1036 years 5. 9 1030 years 26! = 4 1026 2 1026 µs = 6. 4 1012 years 26 characters (permutation) 6. 4 106 years On average, number of guesses is half the key space
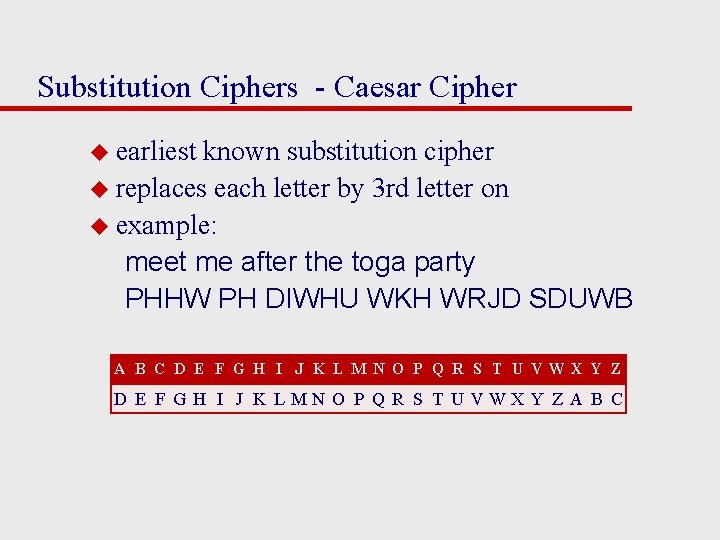
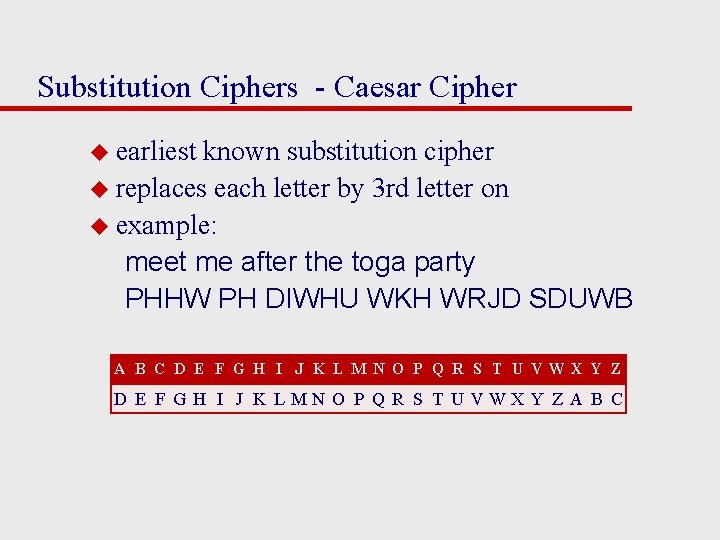
Substitution Ciphers - Caesar Cipher u earliest known substitution cipher u replaces each letter by 3 rd letter on u example: meet me after the toga party PHHW PH DIWHU WKH WRJD SDUWB A B C D E F G H I J K L M N O P Q R S T U VWX Y Z D E F G H I J K L MN O P Q R S T U VWX Y Z A B C
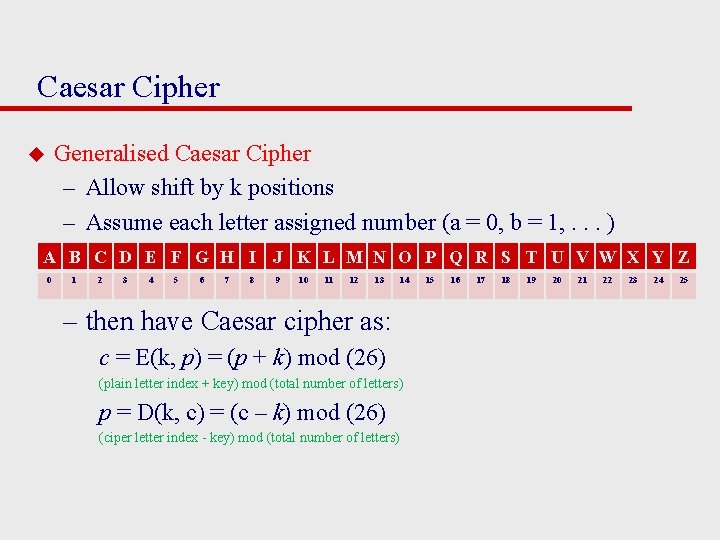
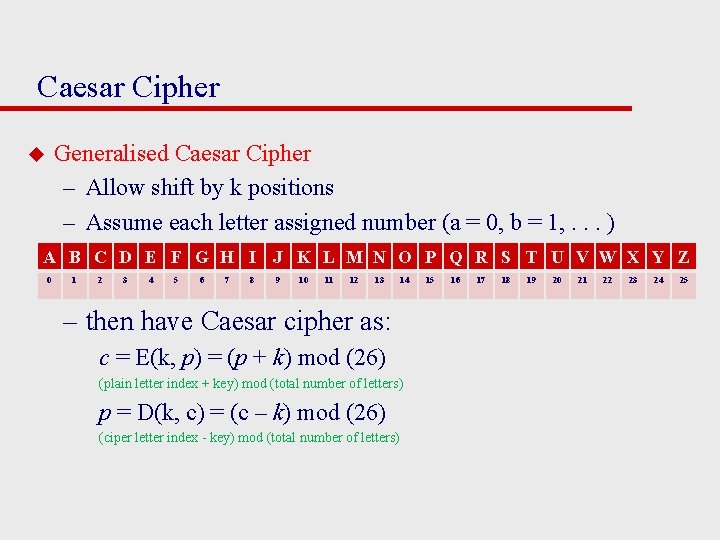
Caesar Cipher Generalised Caesar Cipher – Allow shift by k positions – Assume each letter assigned number (a = 0, b = 1, . . . ) u A B C D E F G H I J K L M N O P Q R S T U V W X Y Z 0 1 2 3 4 5 6 7 8 9 10 11 12 13 14 – then have Caesar cipher as: c = E(k, p) = (p + k) mod (26) (plain letter index + key) mod (total number of letters) p = D(k, c) = (c – k) mod (26) (ciper letter index - key) mod (total number of letters) 15 16 17 18 19 20 21 22 23 24 25
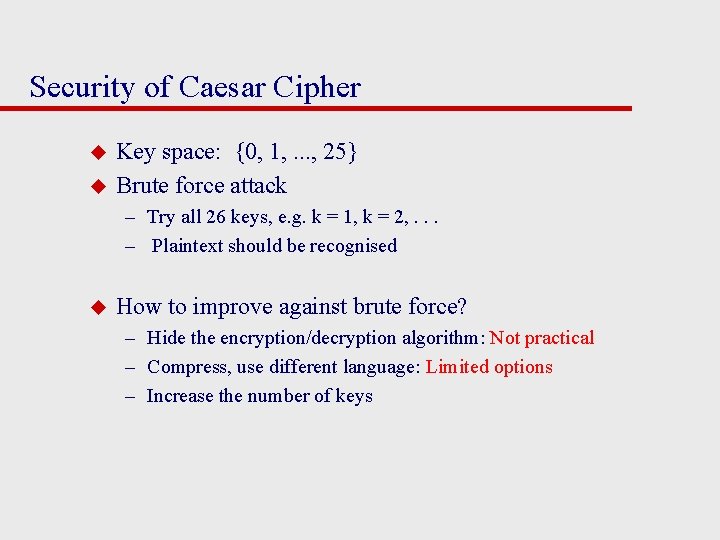
Security of Caesar Cipher u u Key space: {0, 1, . . . , 25} Brute force attack – Try all 26 keys, e. g. k = 1, k = 2, . . . – Plaintext should be recognised u How to improve against brute force? – Hide the encryption/decryption algorithm: Not practical – Compress, use different language: Limited options – Increase the number of keys
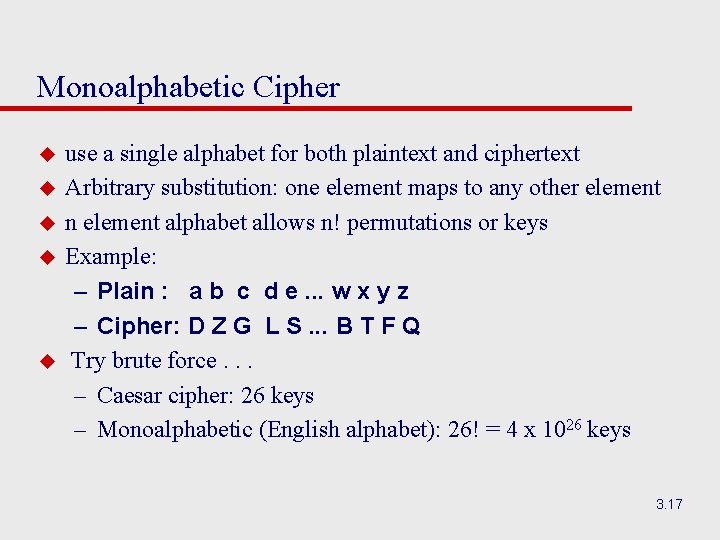
Monoalphabetic Cipher u u use a single alphabet for both plaintext and ciphertext Arbitrary substitution: one element maps to any other element n element alphabet allows n! permutations or keys Example: – Plain : a b c d e. . . w x y z – Cipher: D Z G L S. . . B T F Q Try brute force. . . – Caesar cipher: 26 keys – Monoalphabetic (English alphabet): 26! = 4 x 1026 keys 3. 17
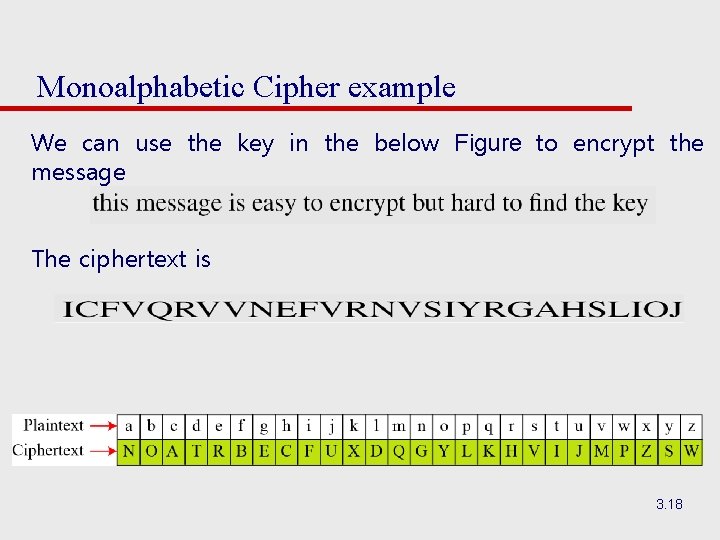
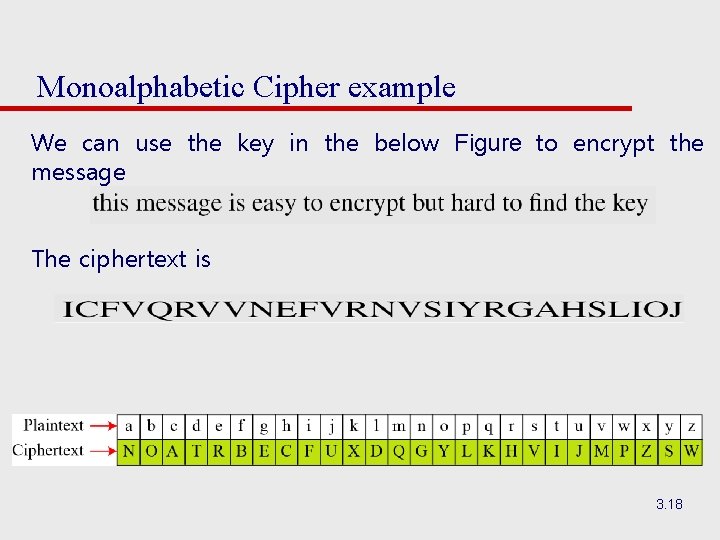
Monoalphabetic Cipher example We can use the key in the below Figure to encrypt the message The ciphertext is 3. 18
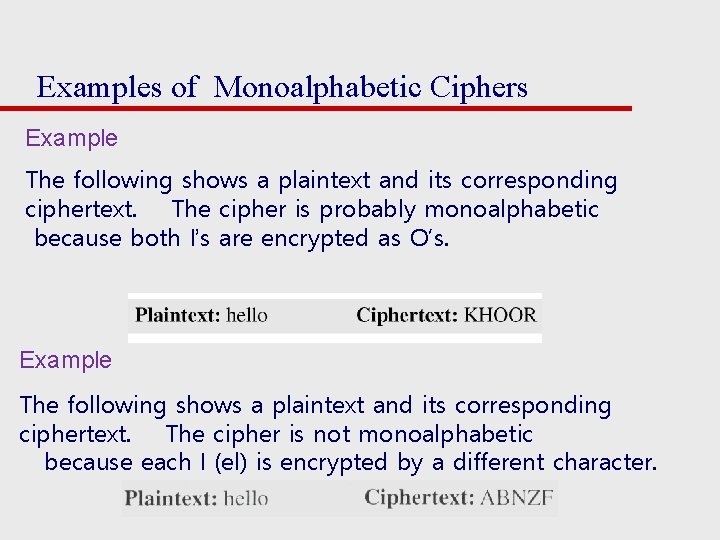
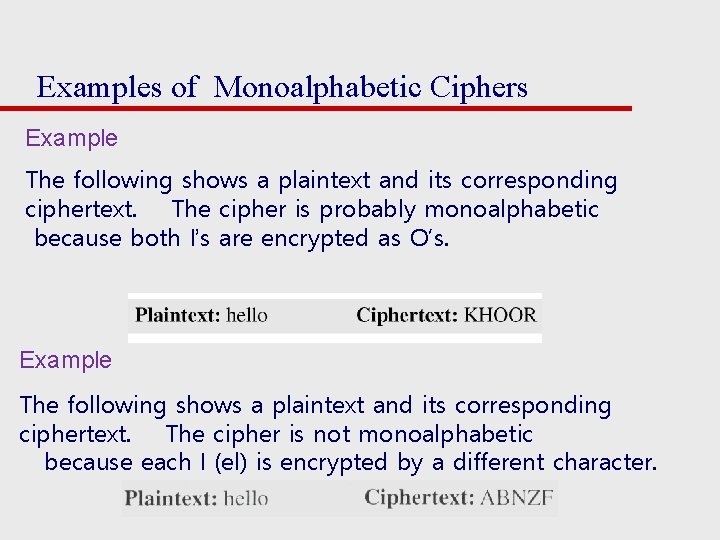
Examples of Monoalphabetic Ciphers Example The following shows a plaintext and its corresponding ciphertext. The cipher is probably monoalphabetic because both l’s are encrypted as O’s. Example The following shows a plaintext and its corresponding ciphertext. The cipher is not monoalphabetic because each l (el) is encrypted by a different character.
Monoalphabetic Cipher Security u now have a total of 26! = 4 x 1026 keys u With so many keys, it is secure against brute-force attacks. u But not secure against some cryptanalytic attacks. u Problem is language characteristics.
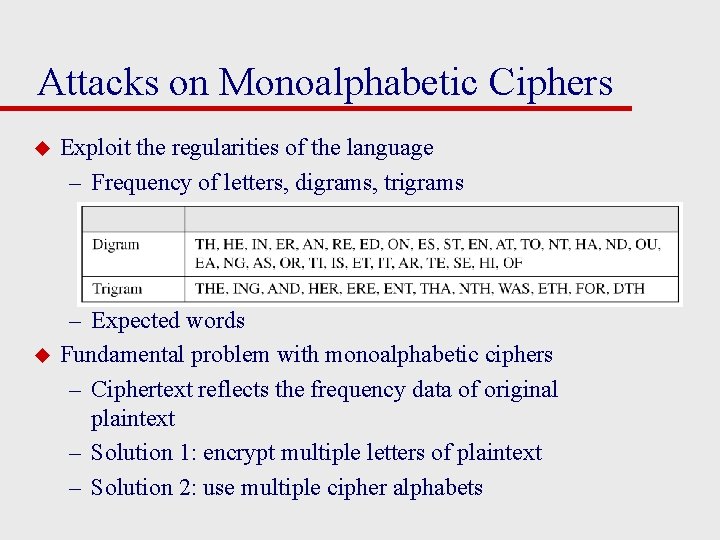
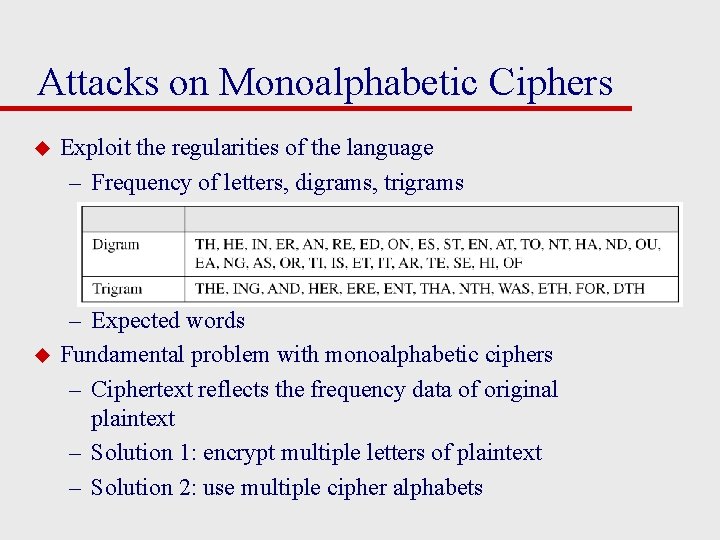
Attacks on Monoalphabetic Ciphers u u Exploit the regularities of the language – Frequency of letters, digrams, trigrams – Expected words Fundamental problem with monoalphabetic ciphers – Ciphertext reflects the frequency data of original plaintext – Solution 1: encrypt multiple letters of plaintext – Solution 2: use multiple cipher alphabets
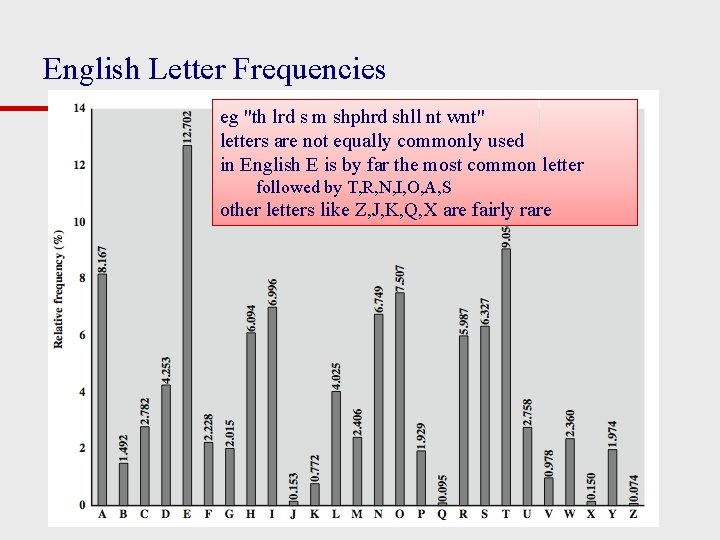
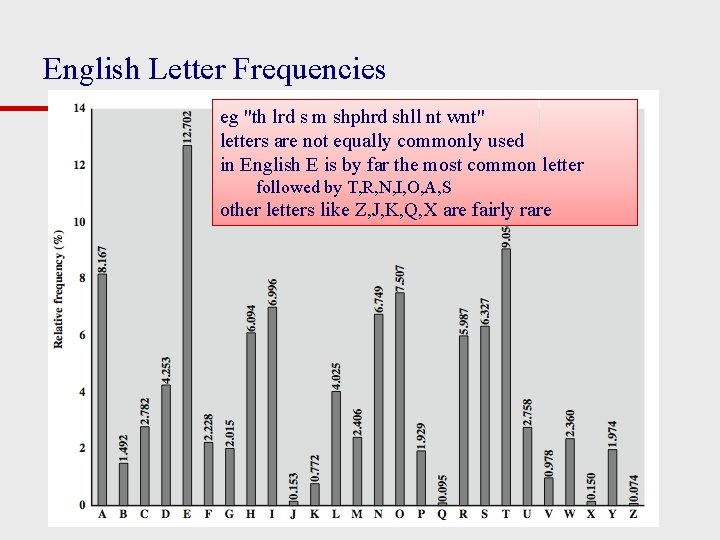
English Letter Frequencies eg "th lrd s m shphrd shll nt wnt" letters are not equally commonly used in English E is by far the most common letter followed by T, R, N, I, O, A, S other letters like Z, J, K, Q, X are fairly rare
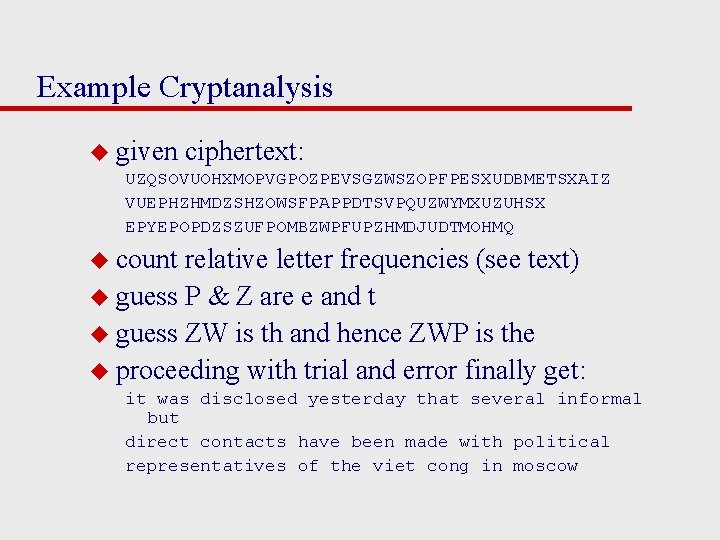
Example Cryptanalysis u given ciphertext: UZQSOVUOHXMOPVGPOZPEVSGZWSZOPFPESXUDBMETSXAIZ VUEPHZHMDZSHZOWSFPAPPDTSVPQUZWYMXUZUHSX EPYEPOPDZSZUFPOMBZWPFUPZHMDJUDTMOHMQ u count relative letter frequencies (see text) u guess P & Z are e and t u guess ZW is th and hence ZWP is the u proceeding with trial and error finally get: it was disclosed yesterday that several informal but direct contacts have been made with political representatives of the viet cong in moscow
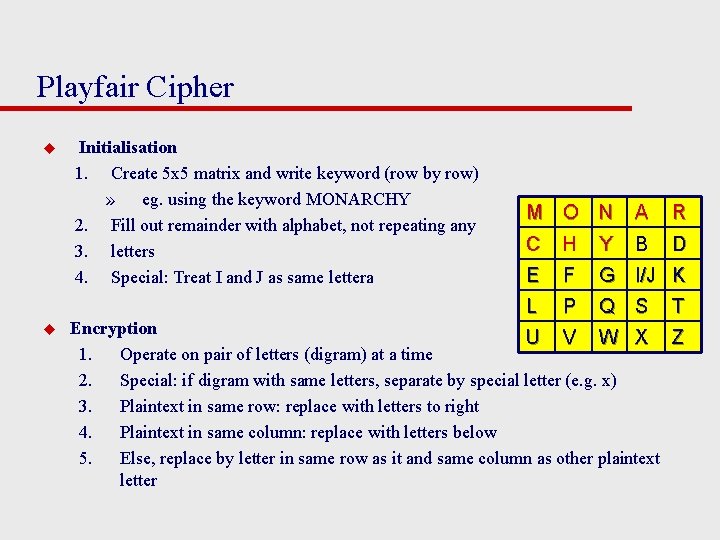
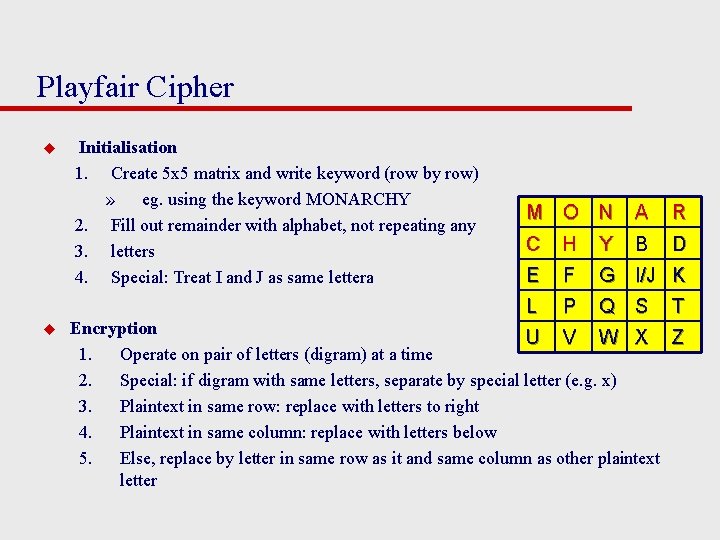
Playfair Cipher u u Initialisation 1. Create 5 x 5 matrix and write keyword (row by row) » eg. using the keyword MONARCHY 2. Fill out remainder with alphabet, not repeating any 3. letters 4. Special: Treat I and J as same lettera M O N A R C H Y B D E F G I/J K L P Q S T Encryption U V W X Z 1. Operate on pair of letters (digram) at a time 2. Special: if digram with same letters, separate by special letter (e. g. x) 3. Plaintext in same row: replace with letters to right 4. Plaintext in same column: replace with letters below 5. Else, replace by letter in same row as it and same column as other plaintext letter
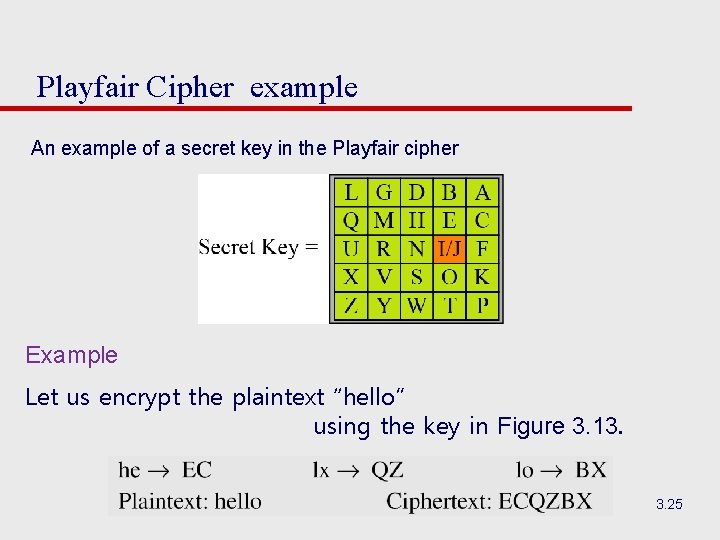
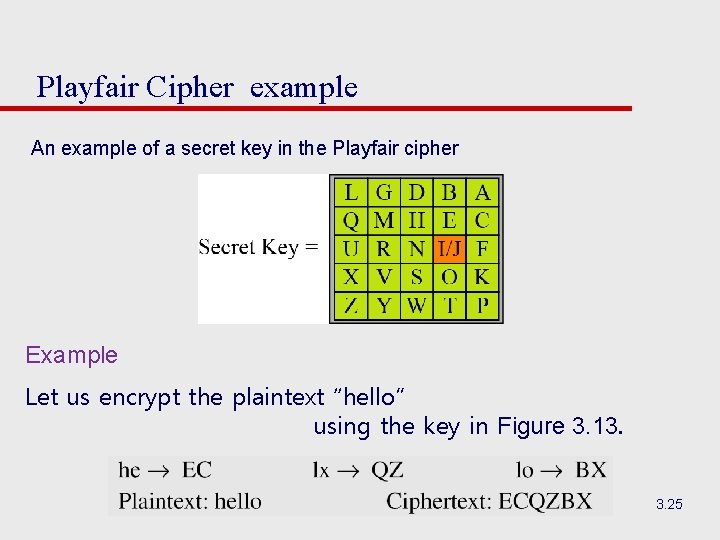
Playfair Cipher example An example of a secret key in the Playfair cipher Example Let us encrypt the plaintext “hello” using the key in Figure 3. 13. 3. 25
Security of Playfair Cipher Is it Breakable? u Better than monoalphabetic: – relative frequency of digrams – much less than of individual letters u But relatively easy (digrams, trigrams, expected words)
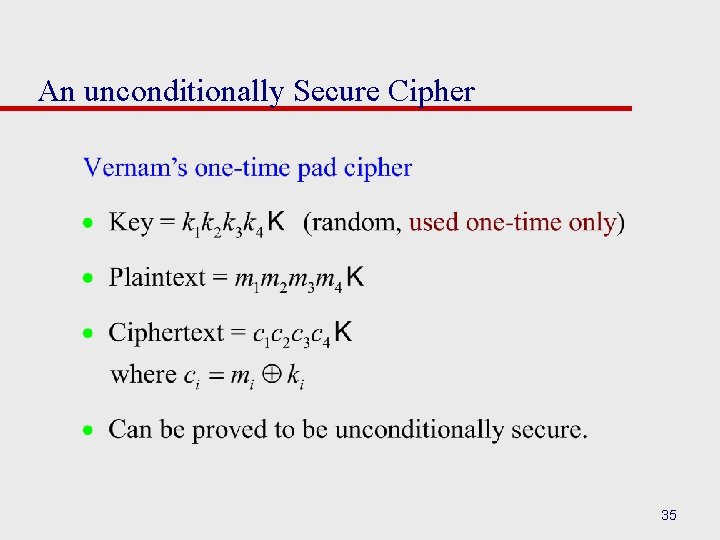
Polyalphabetic Ciphers u polyalphabetic substitution ciphers – A sequence of monoalphabetic ciphers (M 1, M 2, M 3, . . . , Mk) is used in turn to encrypt letters. – A key determines which sequence of ciphers to use. – Each plaintext letter has multiple corresponding ciphertext letters. – This makes cryptanalysis harder since the letter frequency distribution will be flatter. u Examples: – Vigenere cipher – Vernam cipher ( see the text book) – One time pad
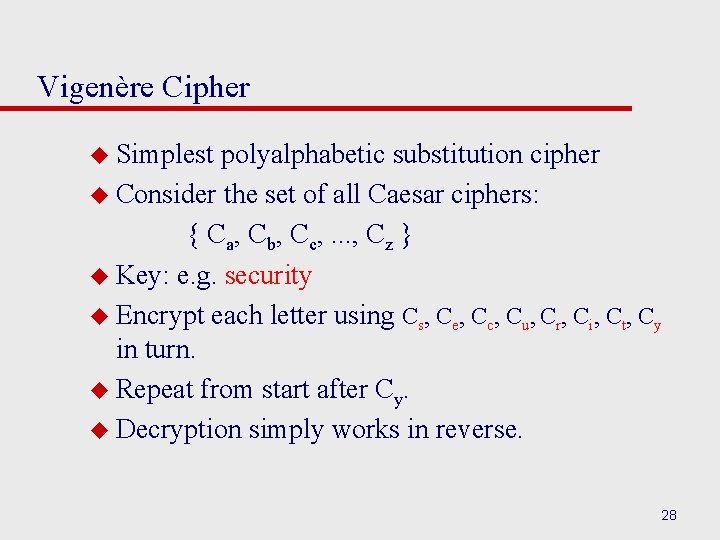
Vigenère Cipher u Simplest polyalphabetic substitution cipher u Consider the set of all Caesar ciphers: { Ca, Cb, Cc, . . . , Cz } u Key: e. g. security u Encrypt each letter using Cs, Ce, Cc, Cu, Cr, Ci, Ct, Cy in turn. u Repeat from start after Cy. u Decryption simply works in reverse. 28
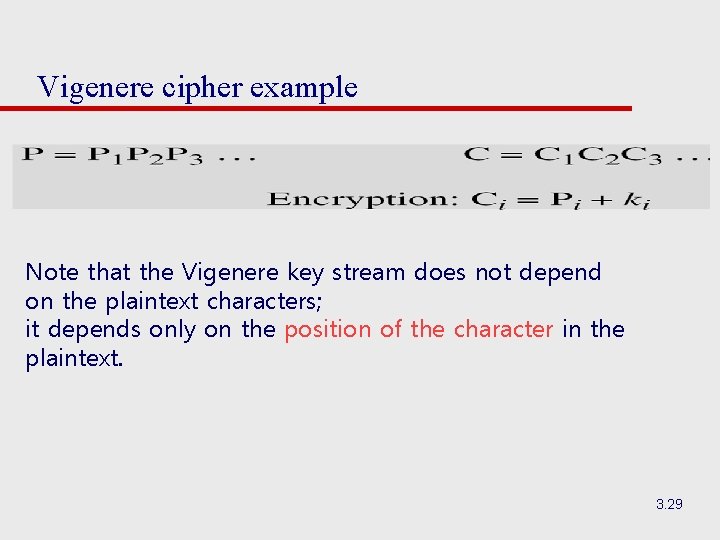
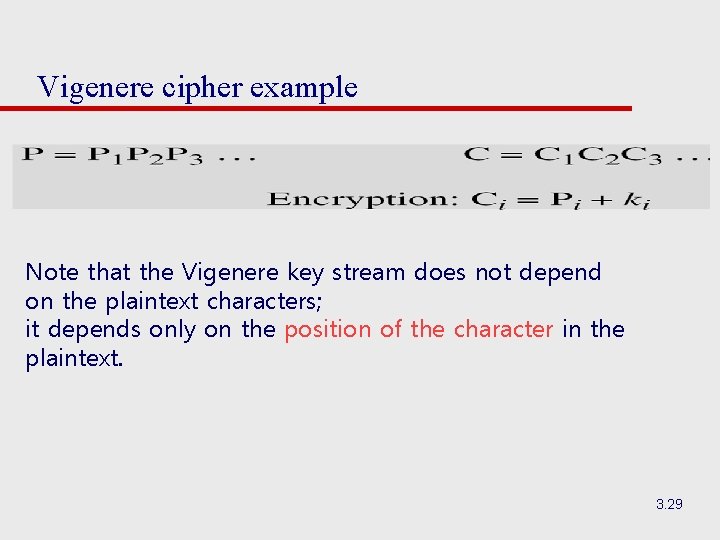
Vigenere cipher example Note that the Vigenere key stream does not depend on the plaintext characters; it depends only on the position of the character in the plaintext. 3. 29
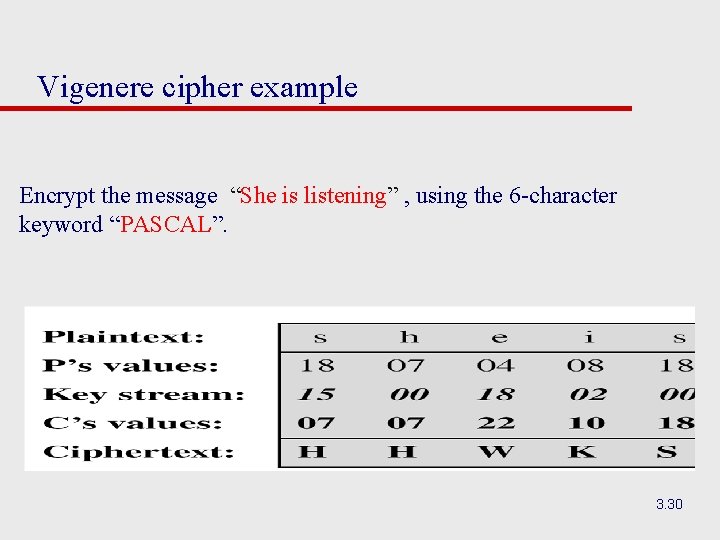
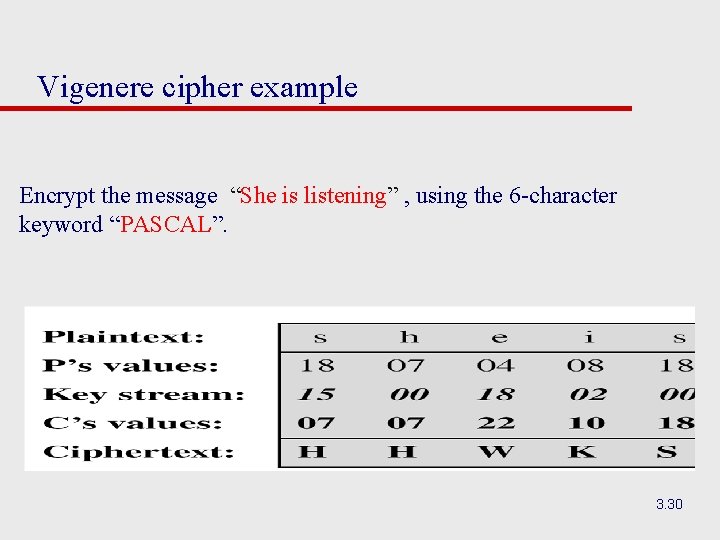
Vigenere cipher example Encrypt the message “She is listening” , using the 6 -character keyword “PASCAL”. 3. 30
Security of Vigenère Ciphers Is it Breakable? u Yes , Vigenere ciphers, like all polyalphabetic ciphers, do not preserve the frequency of the characters. Weakness is repeating, structured keyword
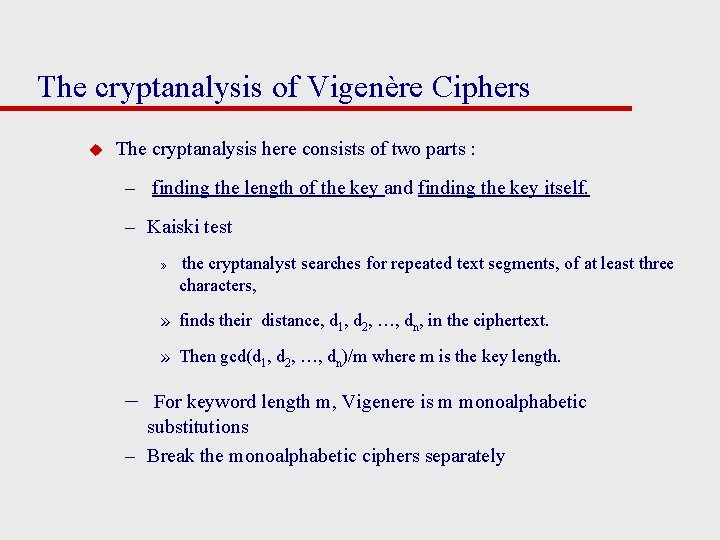
The cryptanalysis of Vigenère Ciphers u The cryptanalysis here consists of two parts : – finding the length of the key and finding the key itself. – Kaiski test » the cryptanalyst searches for repeated text segments, of at least three characters, » finds their distance, d 1, d 2, …, dn, in the ciphertext. » Then gcd(d 1, d 2, …, dn)/m where m is the key length. – For keyword length m, Vigenere is m monoalphabetic substitutions – Break the monoalphabetic ciphers separately
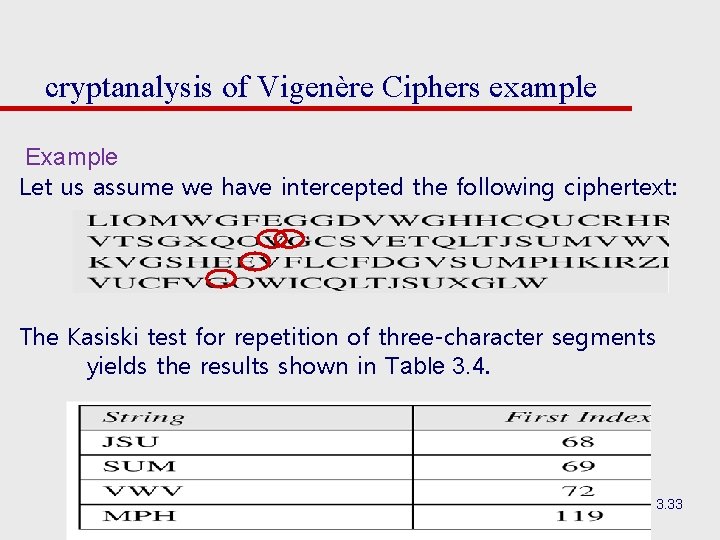
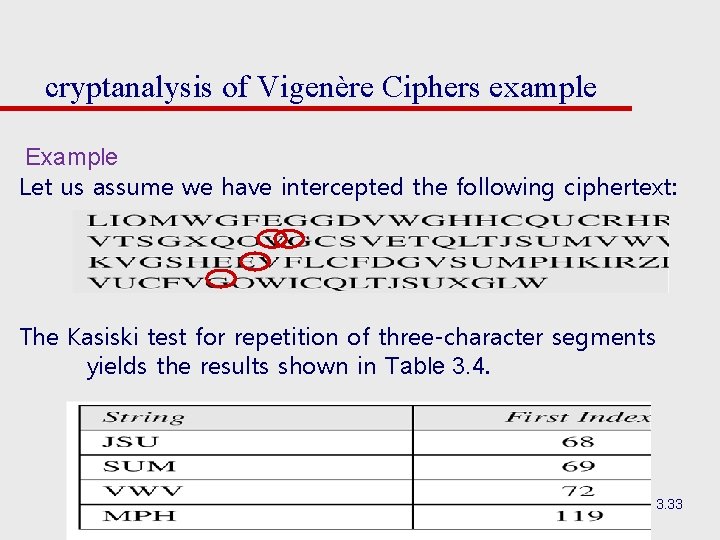
cryptanalysis of Vigenère Ciphers example Example Let us assume we have intercepted the following ciphertext: The Kasiski test for repetition of three-character segments yields the results shown in Table 3. 4. 3. 33
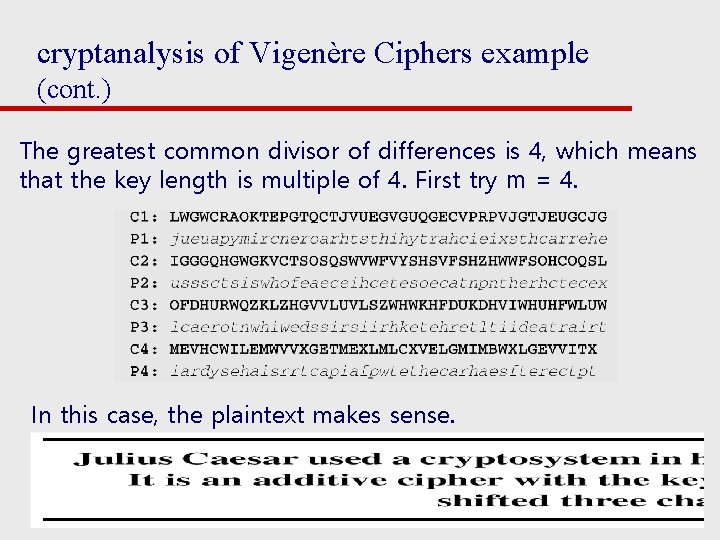
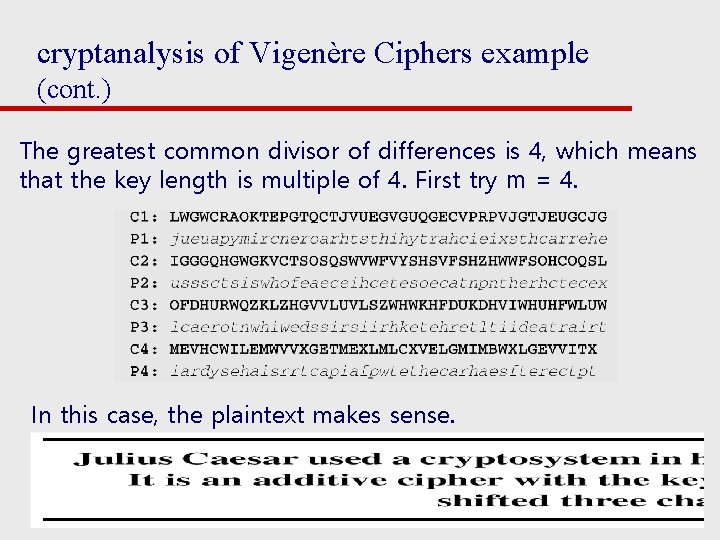
cryptanalysis of Vigenère Ciphers example (cont. ) The greatest common divisor of differences is 4, which means that the key length is multiple of 4. First try m = 4. In this case, the plaintext makes sense. 3. 34
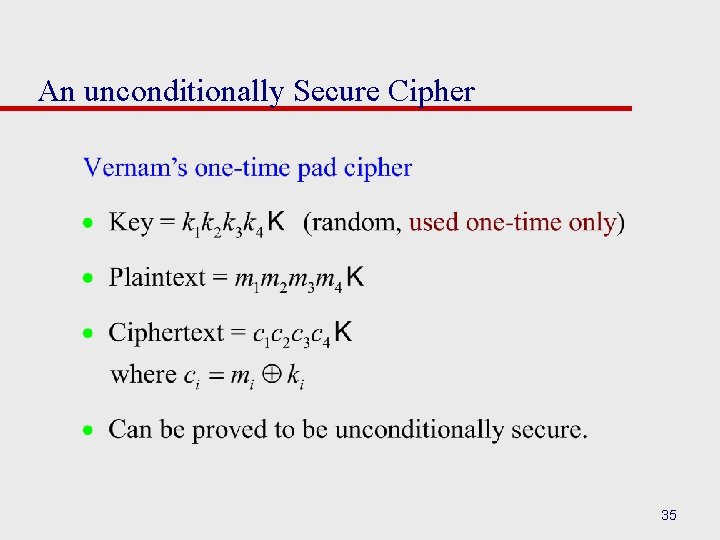
An unconditionally Secure Cipher 35
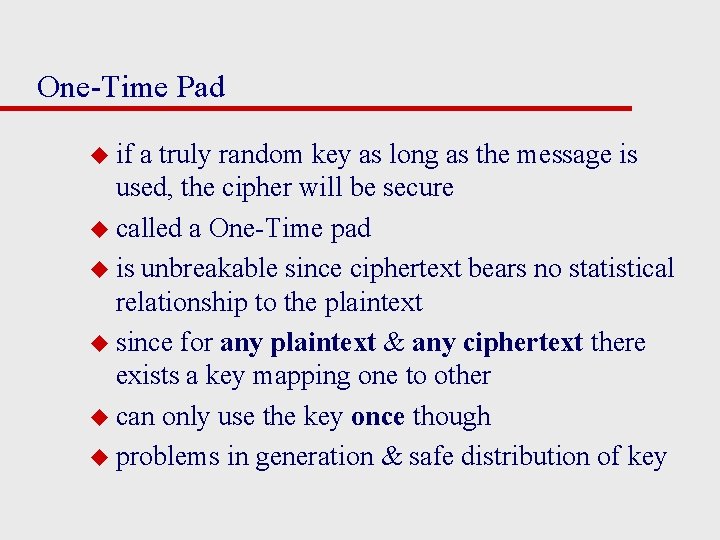
One-Time Pad u if a truly random key as long as the message is used, the cipher will be secure u called a One-Time pad u is unbreakable since ciphertext bears no statistical relationship to the plaintext u since for any plaintext & any ciphertext there exists a key mapping one to other u can only use the key once though u problems in generation & safe distribution of key
Transposition Ciphers u now consider classical transposition or permutation ciphers u these hide the message by rearranging the letter order u without altering the actual letters used u can recognise these since have the same frequency distribution as the original text
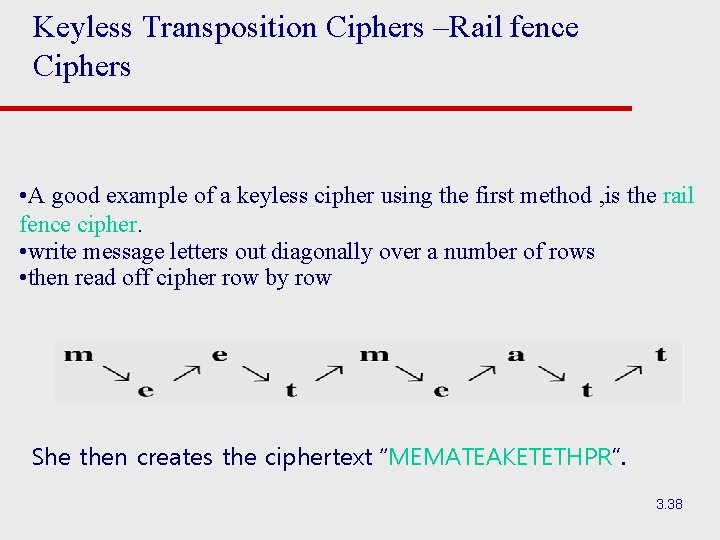
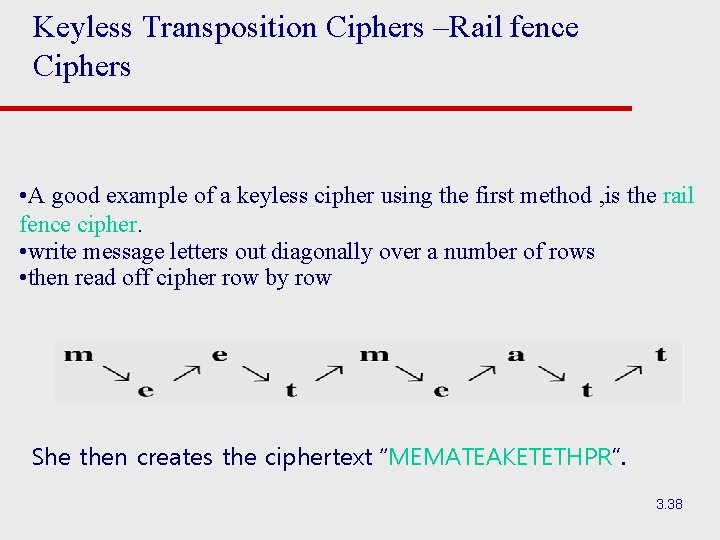
Keyless Transposition Ciphers –Rail fence Ciphers • A good example of a keyless cipher using the first method , is the rail fence cipher. • write message letters out diagonally over a number of rows • then read off cipher row by row She then creates the ciphertext “MEMATEAKETETHPR”. 3. 38
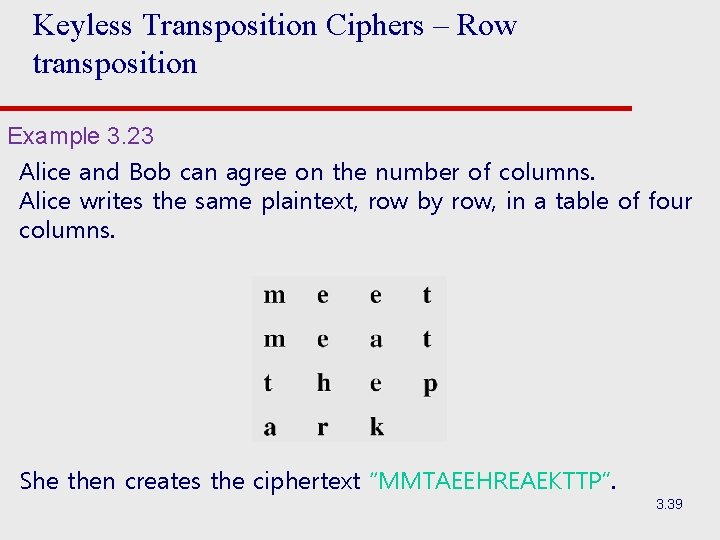
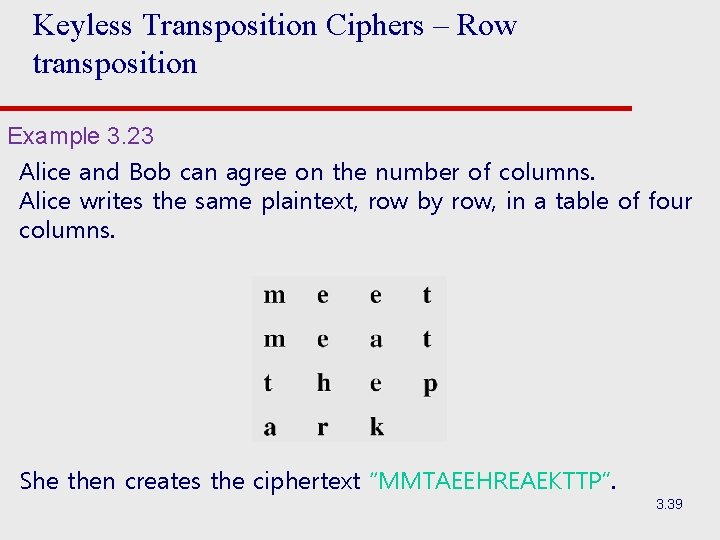
Keyless Transposition Ciphers – Row transposition Example 3. 23 Alice and Bob can agree on the number of columns. Alice writes the same plaintext, row by row, in a table of four columns. She then creates the ciphertext “MMTAEEHREAEKTTP”. 3. 39
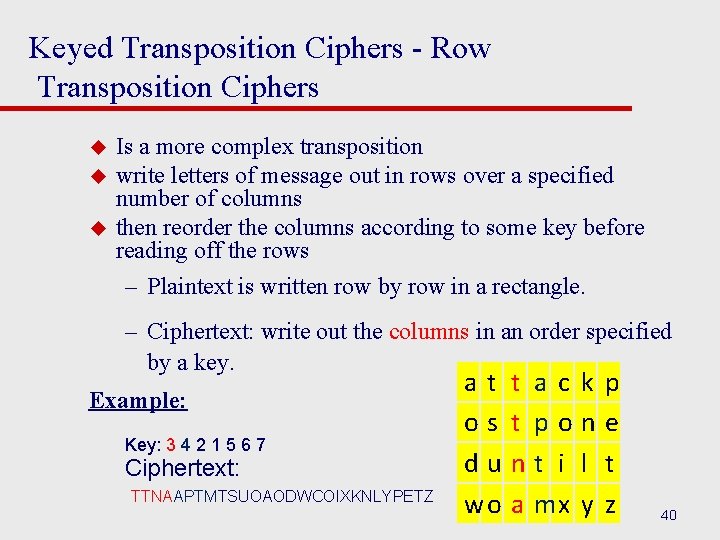
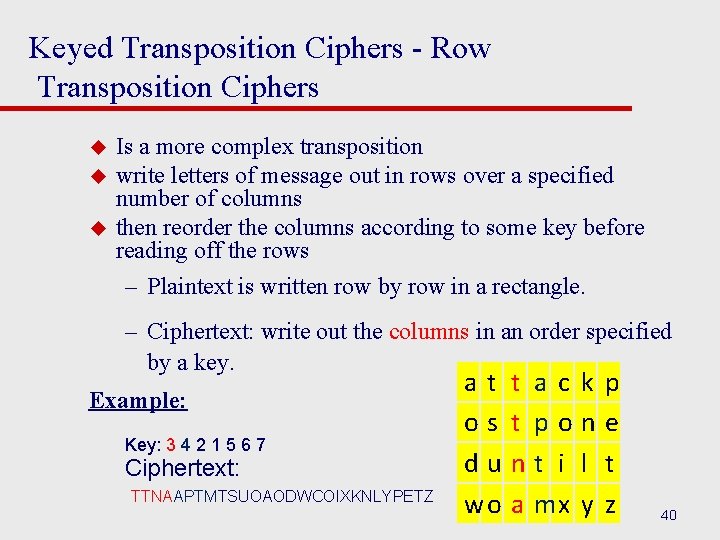
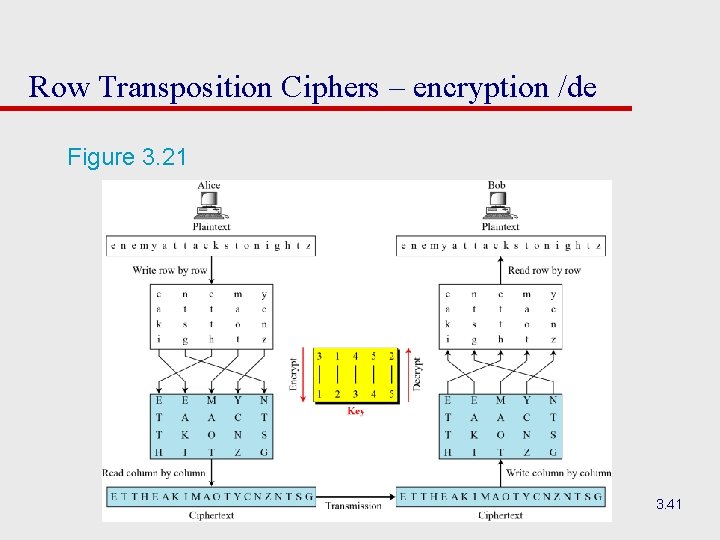
Keyed Transposition Ciphers - Row Transposition Ciphers u u u Is a more complex transposition write letters of message out in rows over a specified number of columns then reorder the columns according to some key before reading off the rows – Plaintext is written row by row in a rectangle. – Ciphertext: write out the columns in an order specified by a key. Example: Key: 3 4 2 1 5 6 7 Ciphertext: TTNAAPTMTSUOAODWCOIXKNLYPETZ at os du wo t t n a ac po t i mx k n l y p e t z 40
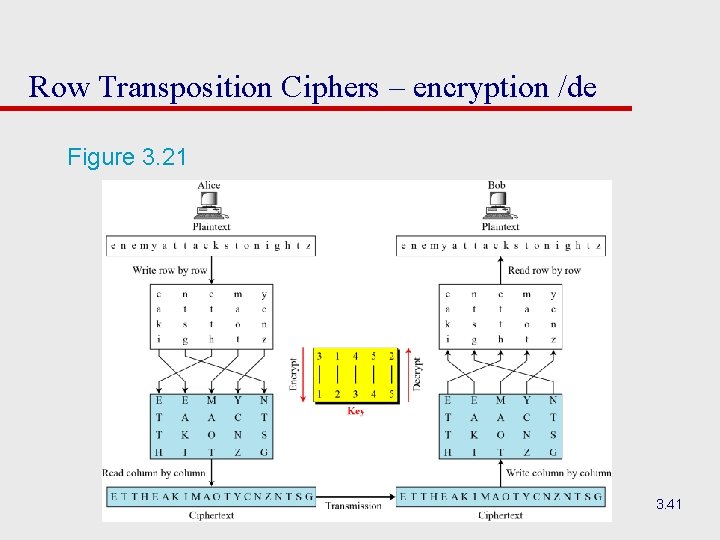
Row Transposition Ciphers – encryption /de Figure 3. 21 3. 41
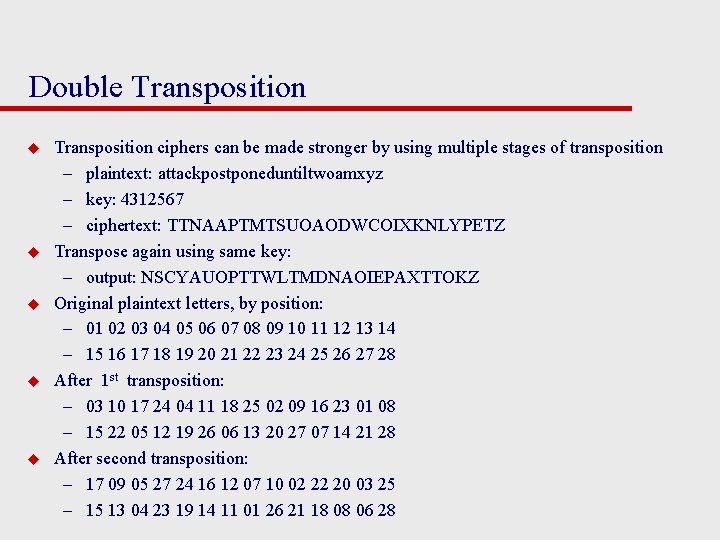
Double Transposition u u u Transposition ciphers can be made stronger by using multiple stages of transposition – plaintext: attackpostponeduntiltwoamxyz – key: 4312567 – ciphertext: TTNAAPTMTSUOAODWCOIXKNLYPETZ Transpose again using same key: – output: NSCYAUOPTTWLTMDNAOIEPAXTTOKZ Original plaintext letters, by position: – 01 02 03 04 05 06 07 08 09 10 11 12 13 14 – 15 16 17 18 19 20 21 22 23 24 25 26 27 28 After 1 st transposition: – 03 10 17 24 04 11 18 25 02 09 16 23 01 08 – 15 22 05 12 19 26 06 13 20 27 07 14 21 28 After second transposition: – 17 09 05 27 24 16 12 07 10 02 22 20 03 25 – 15 13 04 23 19 14 11 01 26 21 18 08 06 28
Cryptanalysis of Transposition Ciphers u The ciphers are vulnerable to several kinds of ciphertextonly attacks. u Statistical Attack: – A transposition cipher does not change the frequency of letters in ciphertext, but dose not preserve the frequency of digrams and trigrams. u Brute-Force Attack: – u The number of keys can be huge (1! + 2! + … + L!), where L is the length of the ciphertext. A better approach is to guess the number of columns. 3. 43
Product Ciphers u ciphers using substitutions or transpositions are not secure because of language characteristics u hence consider using several ciphers in succession to make harder, but: – two substitutions make a more complex substitution – two transpositions make more complex transposition – but a substitution followed by a transposition makes a new much harder cipher u this is bridge from classical to modern ciphers
Rotor Machines u u u u u Multiple stages of encryption can be used for substitution and transposition ciphers Rotor machines were early application of this – Principle was basis for Enigma cipher used by Germany in WW 2 Machine has multiple cylinders Monoalphabetic substitution cipher for each cylinder Output of one cylinder is input to next cylinder Plaintext is input to first cylinder; ciphertext is output of last cylinder Entering a plaintext letter causes last cylinder to rotate its cipher Complete rotation of one cylinder causes previous cylinder to rotate its cipher Principle is used in Data Encryption Standard (DES)
Hagelin Rotor Machine
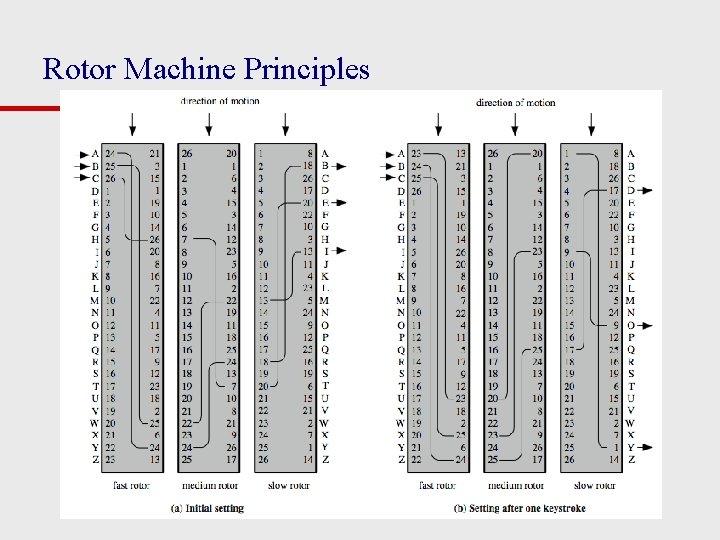
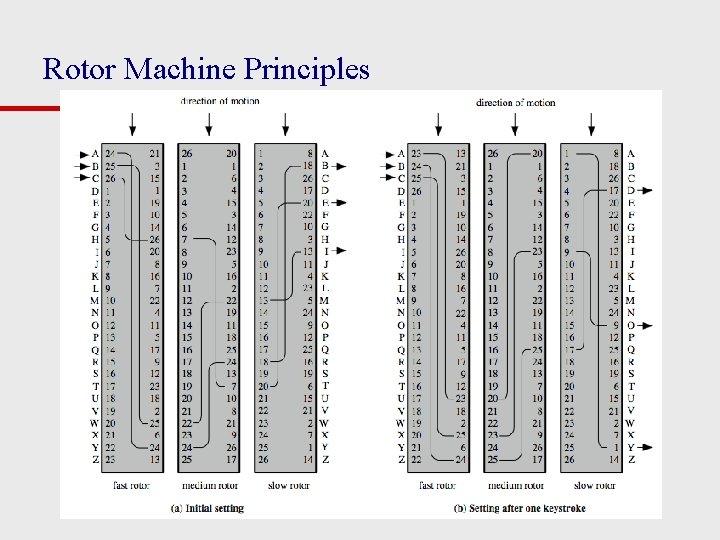
Rotor Machine Principles
Steganography u u u an alternative to encryption hides existence of message – using only a subset of letters/words in a longer message marked in some way – using invisible ink – hiding in LSB in graphic image or sound file has drawbacks – Once attacker knows your method, everything is lost – Can be inecient (need to send lot of information to – carry small message) u advantage is can obscure encryption use
Summary u have considered: – classical cipher techniques and terminology – monoalphabetic substitution ciphers – cryptanalysis using letter frequencies – Playfair cipher – polyalphabetic ciphers – transposition ciphers – product ciphers and rotor machines – stenography