Computer Architecture Building a Modern Computer From First
Computer Architecture Building a Modern Computer From First Principles www. nand 2 tetris. org Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 1 slide
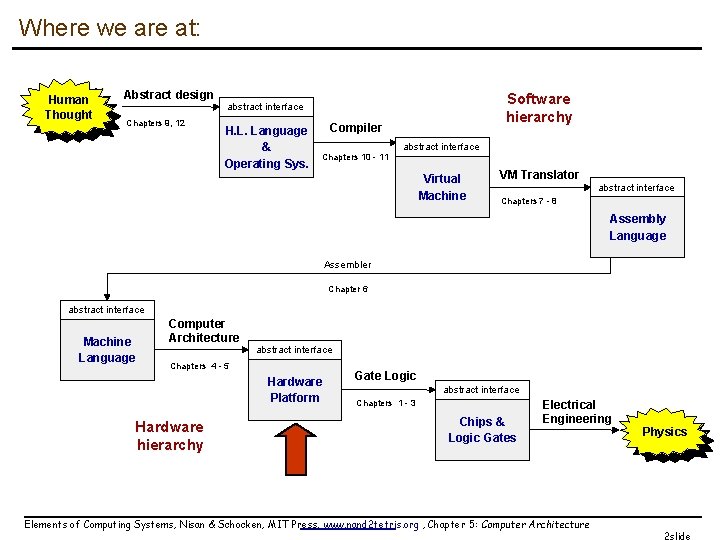
Where we are at: Human Thought Abstract design Chapters 9, 12 Software hierarchy abstract interface H. L. Language & Operating Sys. Compiler Chapters 10 - 11 abstract interface Virtual Machine VM Translator abstract interface Chapters 7 - 8 Assembly Language Assembler Chapter 6 abstract interface Machine Language Computer Architecture abstract interface Chapters 4 - 5 Hardware Platform Hardware hierarchy Gate Logic abstract interface Chapters 1 - 3 Chips & Logic Gates Electrical Engineering Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture Physics 2 slide
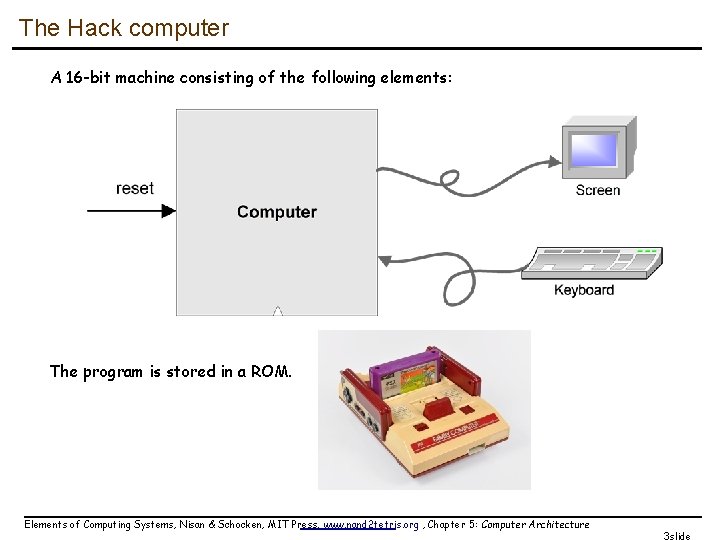
The Hack computer A 16 -bit machine consisting of the following elements: The program is stored in a ROM. Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 3 slide
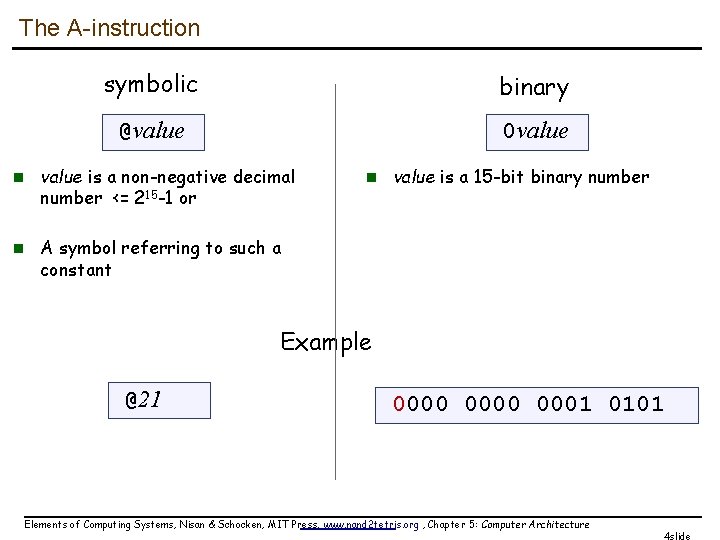
The A-instruction symbolic binary @value 0 value n value is a non-negative decimal number <= 215 -1 or n value is a 15 -bit binary number n A symbol referring to such a constant Example @21 0000 0001 0101 Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 4 slide
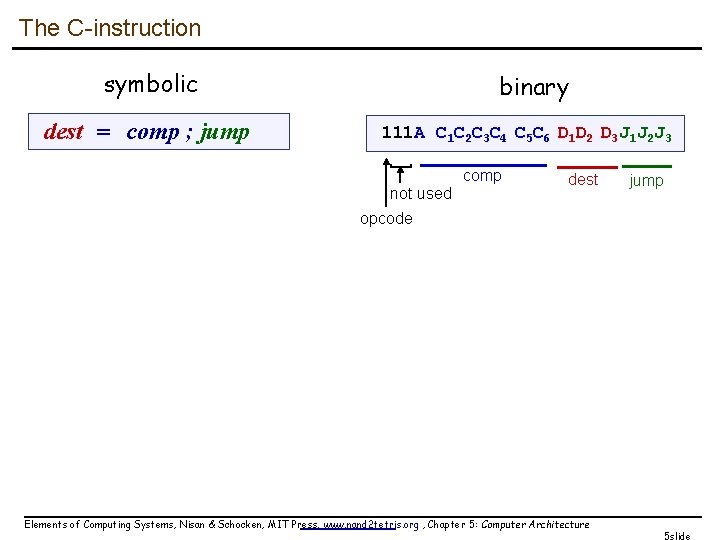
The C-instruction symbolic dest = comp ; jump binary 111 A C 1 C 2 C 3 C 4 C 5 C 6 D 1 D 2 D 3 J 1 J 2 J 3 ] not used comp dest jump opcode Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 5 slide
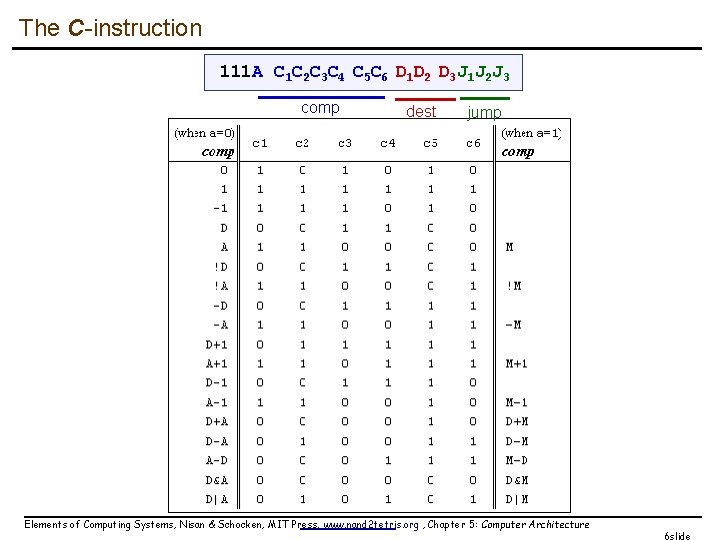
The C-instruction 111 A C 1 C 2 C 3 C 4 C 5 C 6 D 1 D 2 D 3 J 1 J 2 J 3 comp dest jump Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 6 slide
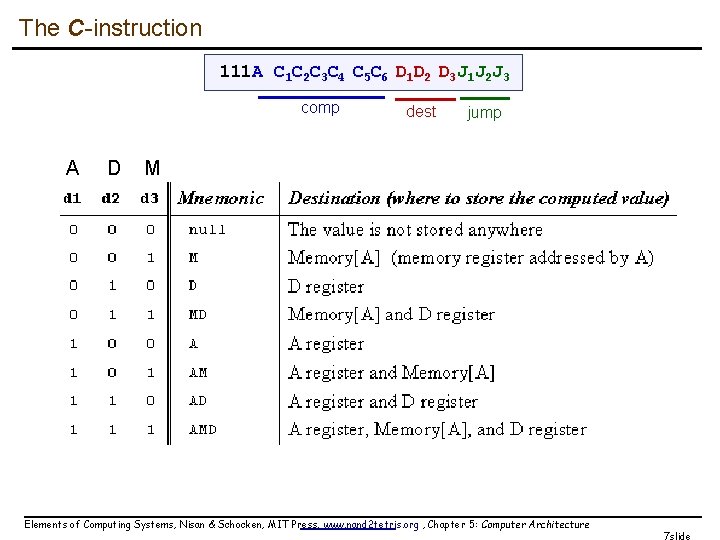
The C-instruction 111 A C 1 C 2 C 3 C 4 C 5 C 6 D 1 D 2 D 3 J 1 J 2 J 3 comp A D dest jump M Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 7 slide
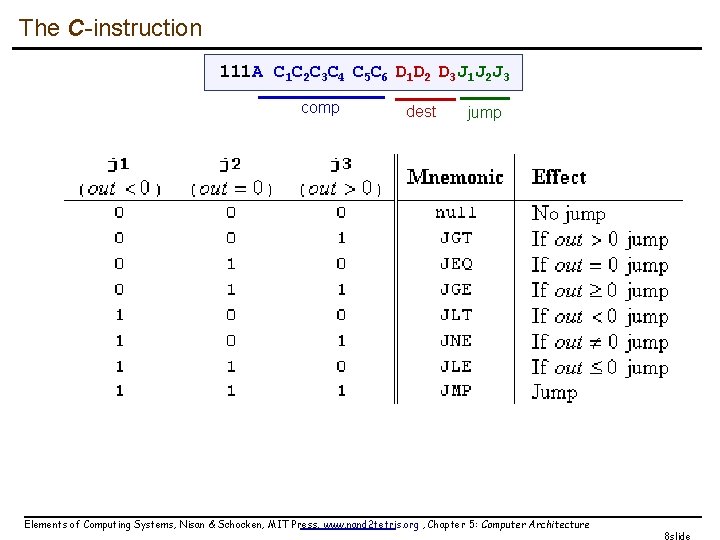
The C-instruction 111 A C 1 C 2 C 3 C 4 C 5 C 6 D 1 D 2 D 3 J 1 J 2 J 3 comp dest jump Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 8 slide
![Hack assembly/machine language Source code (example) // Computes 1+. . . +RAM[0] // And Hack assembly/machine language Source code (example) // Computes 1+. . . +RAM[0] // And](http://slidetodoc.com/presentation_image_h/73d46a41fc3f758baba3b9747934ea19/image-9.jpg)
Hack assembly/machine language Source code (example) // Computes 1+. . . +RAM[0] // And stored the sum in RAM[1] @i M=1 // i = 1 @sum M=0 // sum = 0 (LOOP) @i // if i>RAM[0] goto WRITE D=M @R 0 D=D-M @WRITE D; JGT @i // sum += i D=M @sum M=D+M @i // i++ M=M+1 @LOOP // goto LOOP 0; JMP (WRITE) @sum D=M @R 1 M=D // RAM[1] = the sum (END) @END 0; JMP Target code assemble Hack assembler or CPU emulator 00000010000 1110111111001000 00000010001 111010001000 00000010000 11111100000100000000 11110100000010010 111000000010000 11111100000100000010001 111100001000 00000010000 111111001000 0000000100 111010000111 00000010001 111111000001000000001 11100001000 00000010110 111010000111 assembly code v. s. machine code Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 9 slide
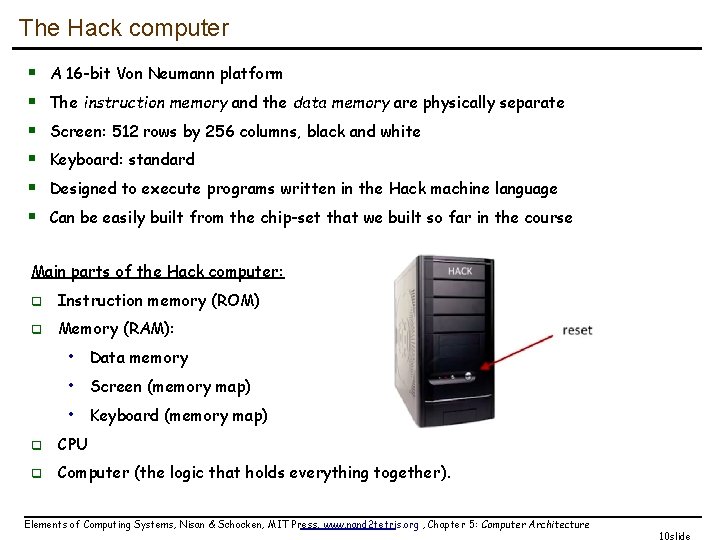
The Hack computer § § § A 16 -bit Von Neumann platform The instruction memory and the data memory are physically separate Screen: 512 rows by 256 columns, black and white Keyboard: standard Designed to execute programs written in the Hack machine language Can be easily built from the chip-set that we built so far in the course Main parts of the Hack computer: q Instruction memory (ROM) q Memory (RAM): • Data memory • Screen (memory map) • Keyboard (memory map) q CPU q Computer (the logic that holds everything together). Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 10 slide
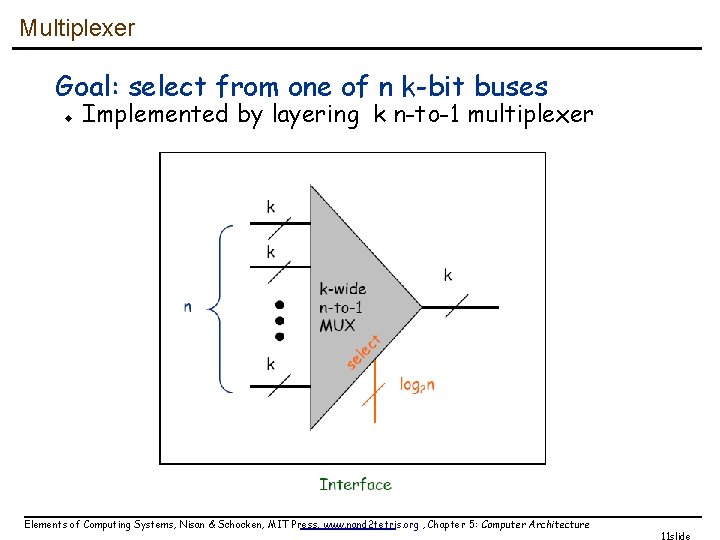
Multiplexer Goal: select from one of n k-bit buses u Implemented by layering k n-to-1 multiplexer Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 11 slide
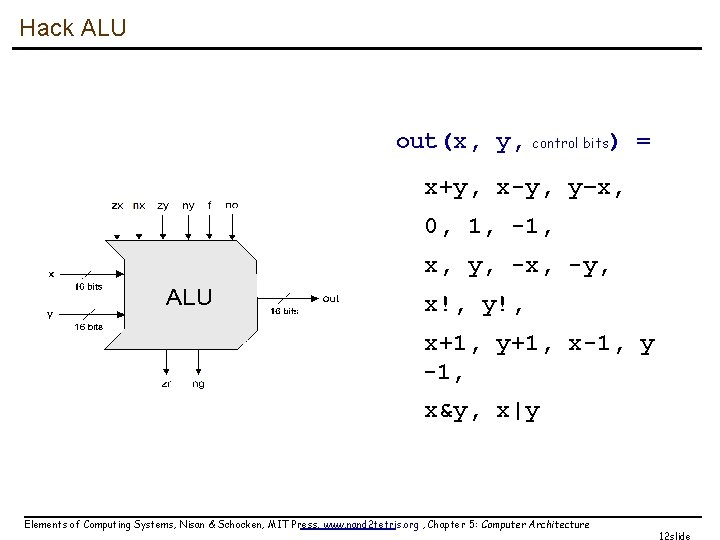
Hack ALU out(x, y, control bits) = x+y, x-y, y–x, 0, 1, -1, x, y, -x, -y, x!, y!, x+1, y+1, x-1, y -1, x&y, x|y Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 12 slide
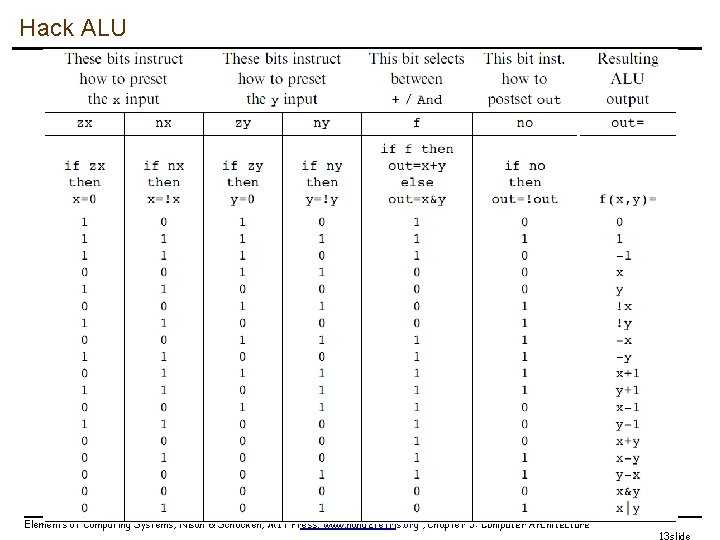
Hack ALU Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 13 slide
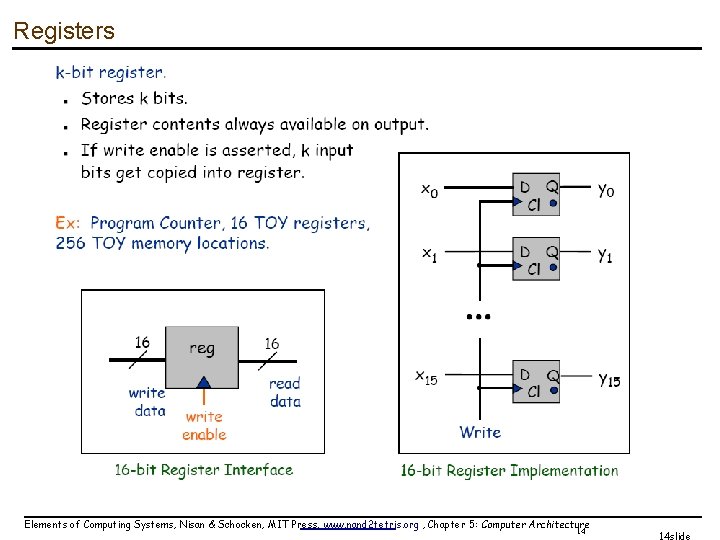
Registers Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 14 14 slide
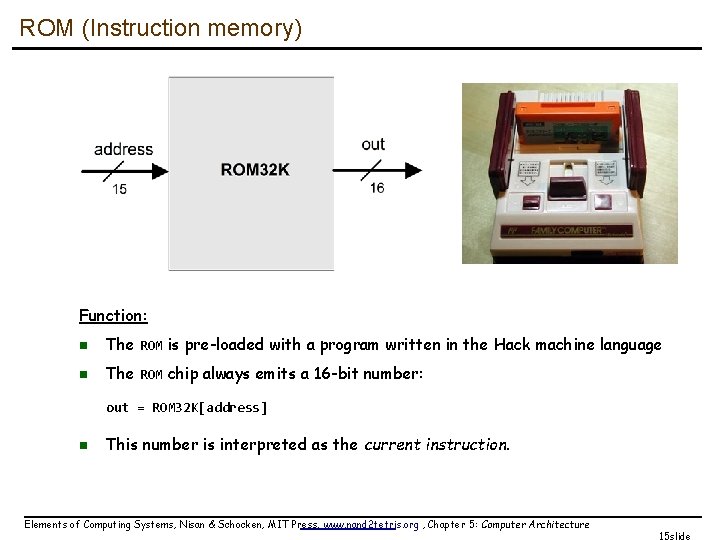
ROM (Instruction memory) Function: n The ROM is pre-loaded with a program written in the Hack machine language n The ROM chip always emits a 16 -bit number: out = ROM 32 K[address] n This number is interpreted as the current instruction. Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 15 slide
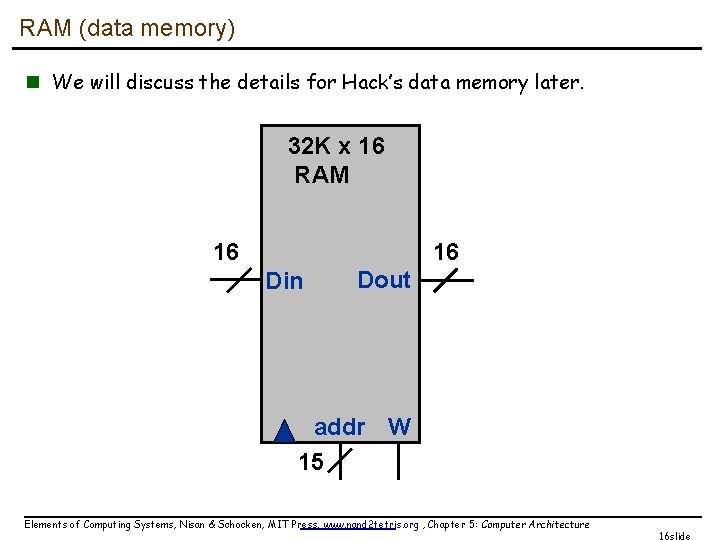
RAM (data memory) n We will discuss the details for Hack’s data memory later. 32 K x 16 RAM 16 16 Din Dout addr W 15 Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 16 slide
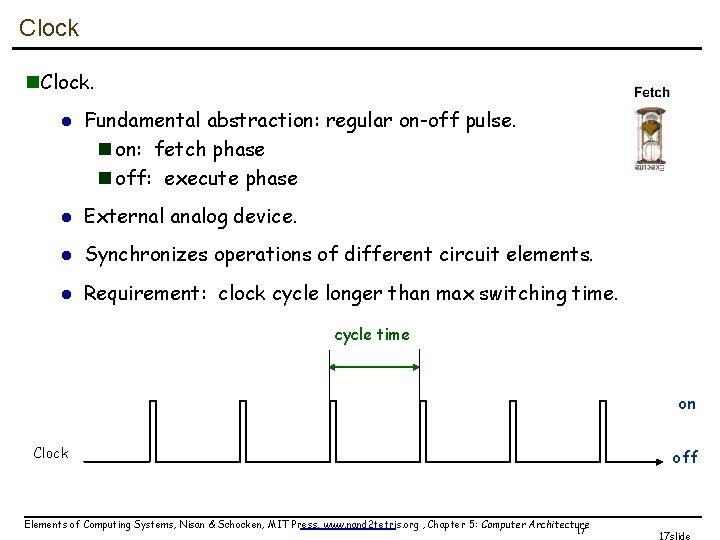
Clock n. Clock. l Fundamental abstraction: regular on-off pulse. n on: fetch phase n off: execute phase l External analog device. l Synchronizes operations of different circuit elements. l Requirement: clock cycle longer than max switching time. cycle time on Clock off Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 17 17 slide
Design a processor n. How to build a processor (Hack, this time) l l Develop instruction set architecture (ISA) n 16 -bit words, two types of machine instructions Determine major components n ALU, registers, program counter, memory Determine datapath requirements n Flow of bits Analyze how to implement each instruction n Determine settings of control signals Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 18 18 slide
![Hack programming reference card Hack commands: A-command: @value // A<-value; M=RAM[A] C-command: dest = Hack programming reference card Hack commands: A-command: @value // A<-value; M=RAM[A] C-command: dest =](http://slidetodoc.com/presentation_image_h/73d46a41fc3f758baba3b9747934ea19/image-19.jpg)
Hack programming reference card Hack commands: A-command: @value // A<-value; M=RAM[A] C-command: dest = comp ; jump // dest = and ; jump // are optional Where: comp = 0 , 1 , -1 , D , A , !D , !A , -D , -A , D+1 , A+1 , D-1, A-1 , D+A , D-A , A-D , D&A , D|A, M , !M , -M , M+1, M-1 , D+M, D-M, M-D, D&M, D|M dest = M, D, A, MD, AM, AD, AMD, or null jump = JGT , JEQ , JGE , JLT , JNE , JLE , JMP, or null In the command dest = comp; jump, the jump materialzes (PC<-A) if (comp jump 0) is true. For example, in D=D+1, JLT, we jump if D+1 < 0. Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 19 slide
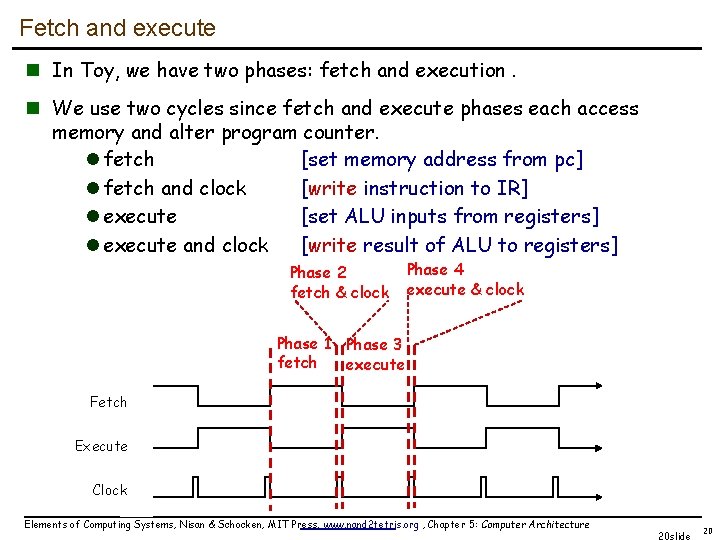
Fetch and execute n In Toy, we have two phases: fetch and execution. n We use two cycles since fetch and execute phases each access memory and alter program counter. l fetch [set memory address from pc] l fetch and clock [write instruction to IR] l execute [set ALU inputs from registers] l execute and clock [write result of ALU to registers] Phase 2 fetch & clock Phase 1 Phase 3 fetch execute Phase 4 execute & clock Fetch Execute Clock Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 20 slide 20
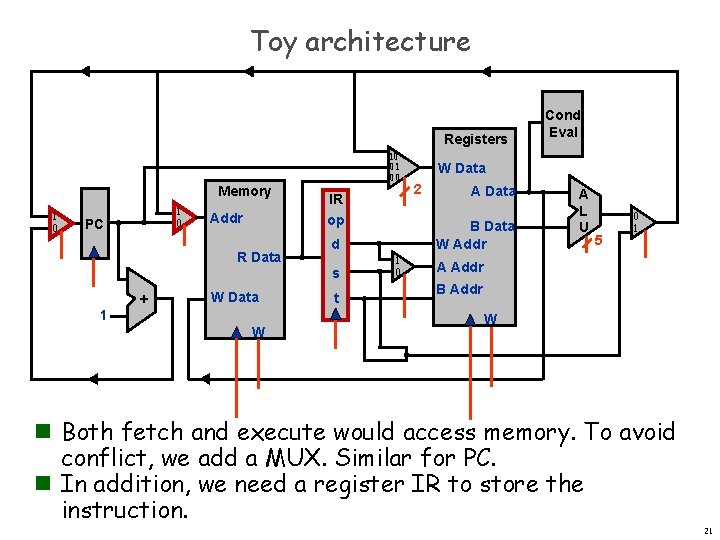
Toy architecture Registers Memory 1 0 PC Addr 10 01 00 IR op R Data s + W Data 1 W t W Data 2 A Data B Data W Addr d 1 0 Cond Eval A L U 5 0 1 A Addr B Addr W n Both fetch and execute would access memory. To avoid conflict, we add a MUX. Similar for PC. n In addition, we need a register IR to store the instruction. 21
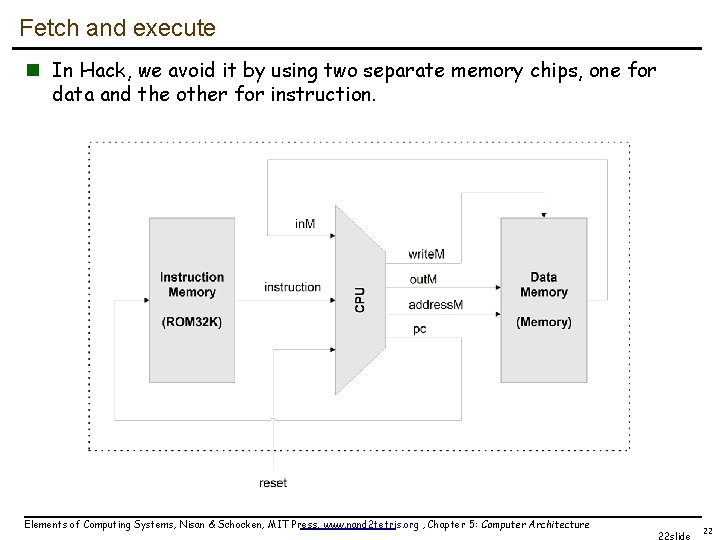
Fetch and execute n In Hack, we avoid it by using two separate memory chips, one for data and the other for instruction. Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 22 slide 22
Design a processor n. How to build a processor (Hack, this time) l l Develop instruction set architecture (ISA) n 16 -bit words, two types of machine instructions Determine major components n ALU, registers, program counter, memory Determine datapath requirements n Flow of bits Analyze how to implement each instruction n Determine settings of control signals Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 23 23 slide
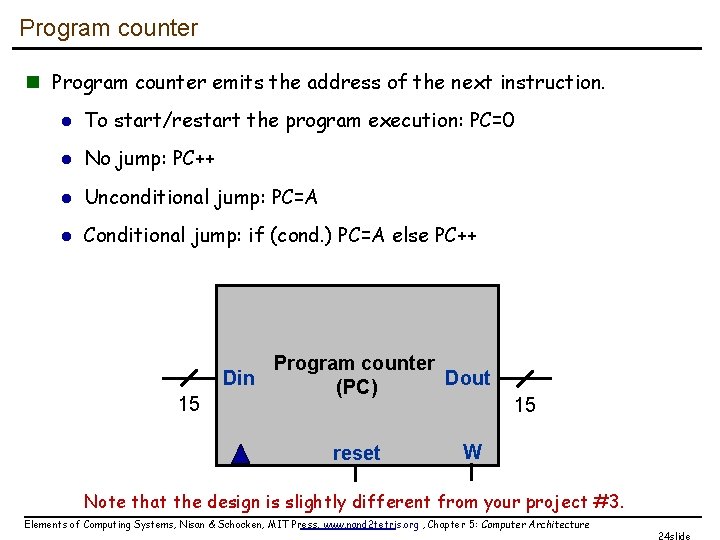
Program counter n Program counter emits the address of the next instruction. l To start/restart the program execution: PC=0 l No jump: PC++ l Unconditional jump: PC=A l Conditional jump: if (cond. ) PC=A else PC++ 15 Program counter Din Dout (PC) reset 15 W Note that the design is slightly different from your project #3. Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 24 slide
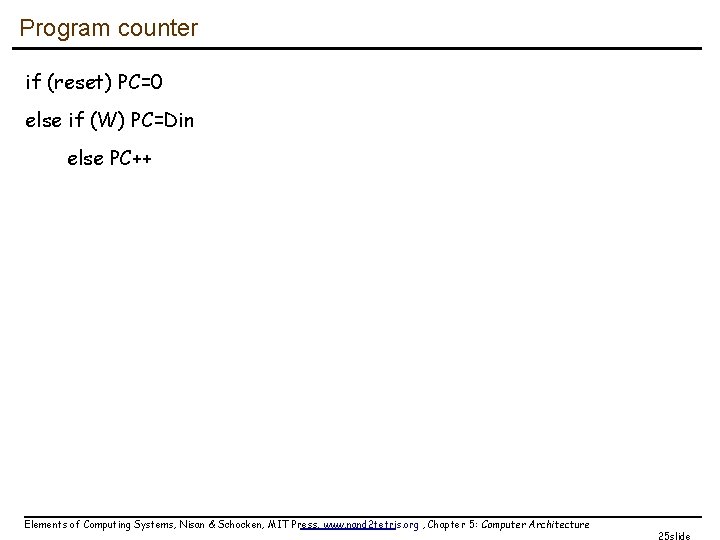
Program counter if (reset) PC=0 else if (W) PC=Din else PC++ Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 25 slide
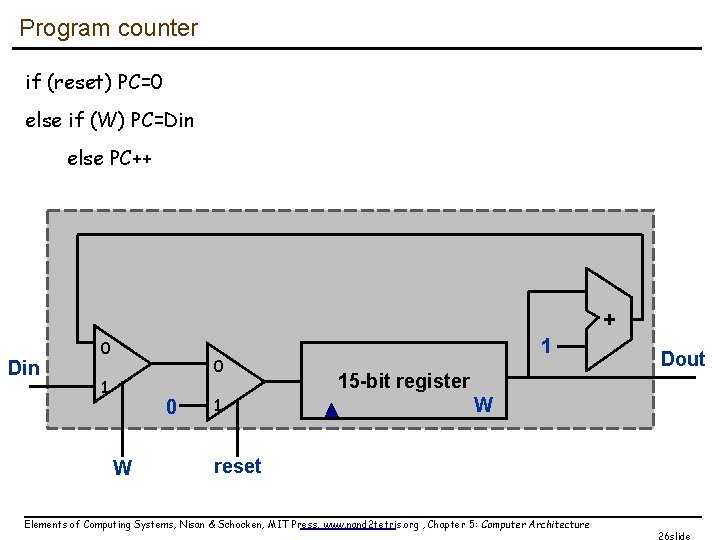
Program counter if (reset) PC=0 else if (W) PC=Din else PC++ + Din 0 0 1 0 W 1 1 15 -bit register Dout W reset Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 26 slide
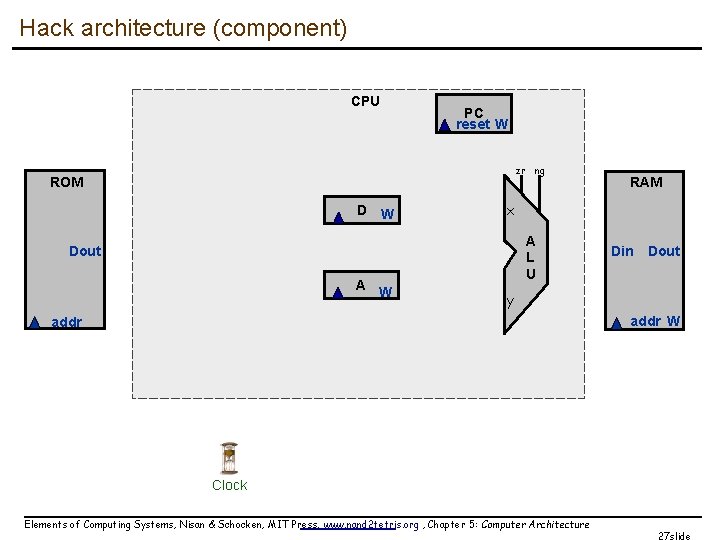
Hack architecture (component) CPU PC reset W zr ng ROM D W x A L U Dout A W RAM Din Dout y addr W addr Clock Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 27 slide
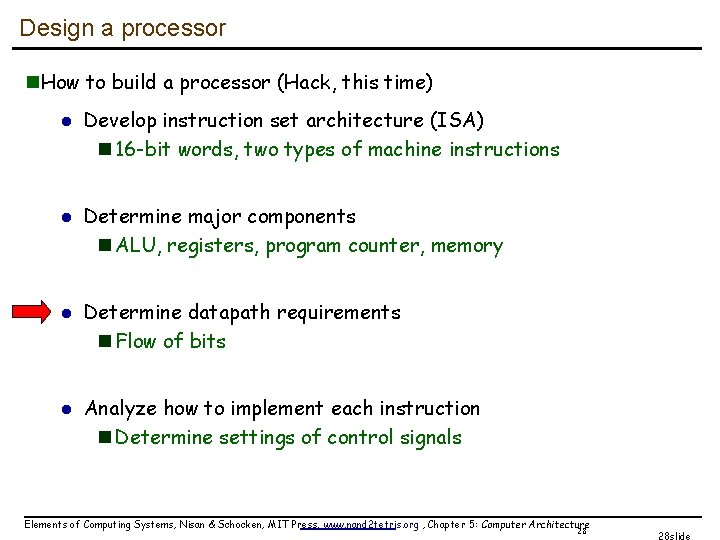
Design a processor n. How to build a processor (Hack, this time) l l Develop instruction set architecture (ISA) n 16 -bit words, two types of machine instructions Determine major components n ALU, registers, program counter, memory Determine datapath requirements n Flow of bits Analyze how to implement each instruction n Determine settings of control signals Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 28 28 slide
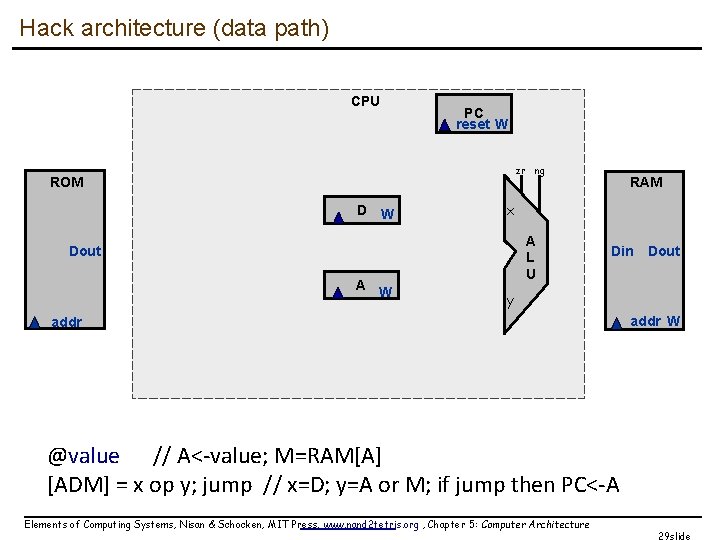
Hack architecture (data path) CPU PC reset W zr ng ROM D W x A L U Dout A W RAM Din Dout y addr W @value // A<-value; M=RAM[A] [ADM] = x op y; jump // x=D; y=A or M; if jump then PC<-A Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 29 slide
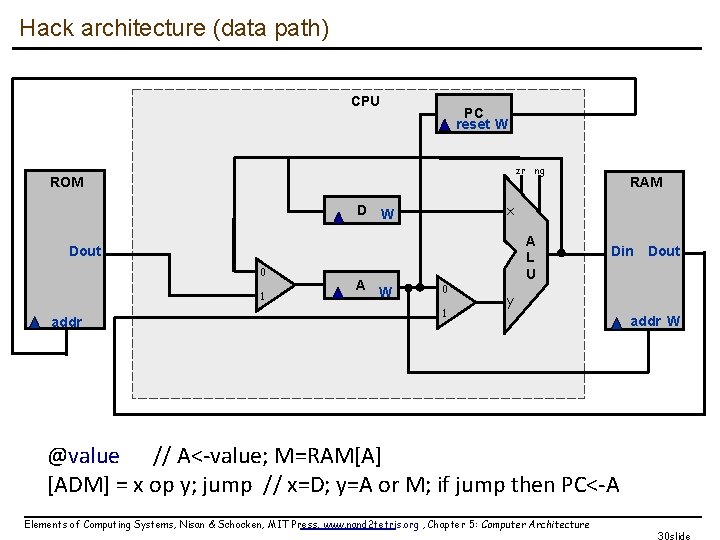
Hack architecture (data path) CPU PC reset W zr ng ROM x D W A L U Dout 0 1 addr A W RAM 0 1 Din Dout y addr W @value // A<-value; M=RAM[A] [ADM] = x op y; jump // x=D; y=A or M; if jump then PC<-A Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 30 slide
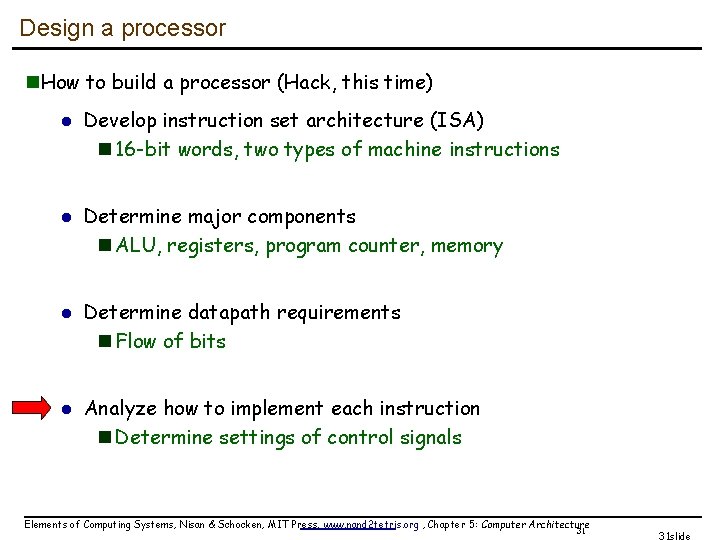
Design a processor n. How to build a processor (Hack, this time) l l Develop instruction set architecture (ISA) n 16 -bit words, two types of machine instructions Determine major components n ALU, registers, program counter, memory Determine datapath requirements n Flow of bits Analyze how to implement each instruction n Determine settings of control signals Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 31 31 slide
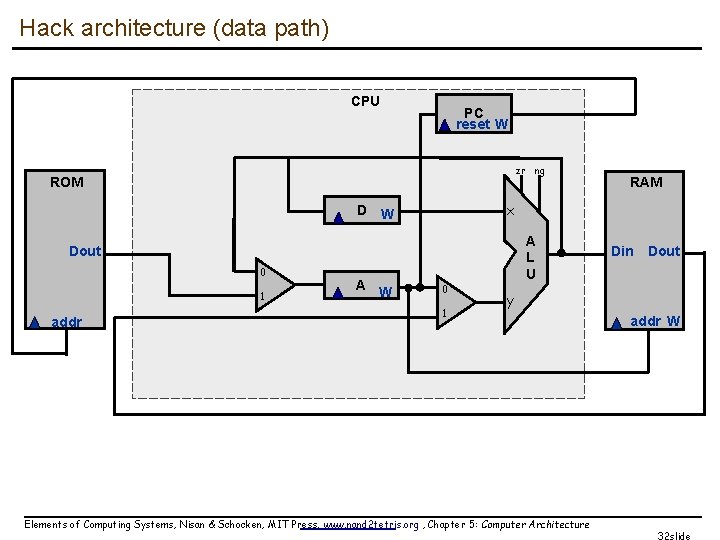
Hack architecture (data path) CPU PC reset W zr ng ROM x D W A L U Dout 0 1 addr A W RAM 0 1 Din Dout y Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture addr W 32 slide
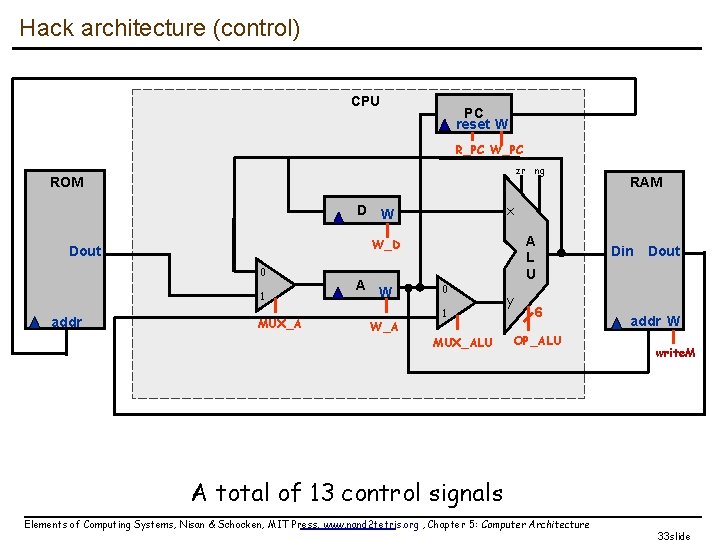
Hack architecture (control) CPU PC reset W R_PC W_PC zr ng ROM x D W 0 1 addr A L U W_D Dout MUX_A A W W_A RAM 0 1 MUX_ALU y 6 OP_ALU Din Dout addr W write. M A total of 13 control signals Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 33 slide
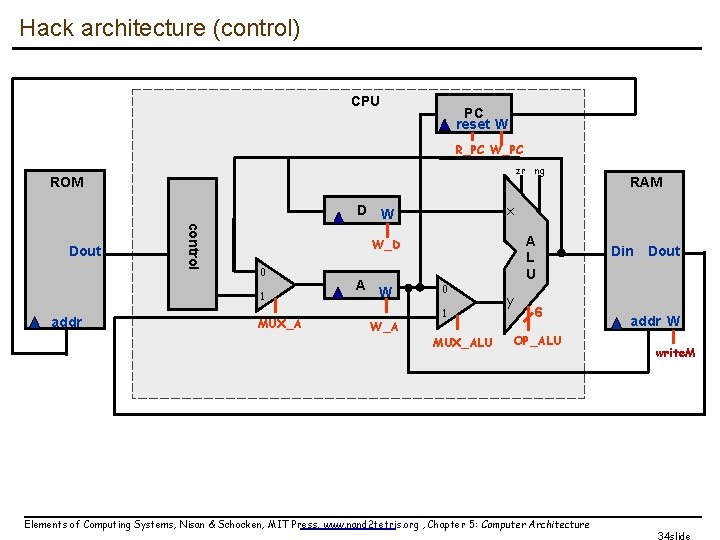
Hack architecture (control) CPU PC reset W R_PC W_PC zr ng ROM x D W control Dout 1 addr A L U W_D 0 MUX_A A W W_A RAM 0 1 MUX_ALU y 6 OP_ALU Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture Din Dout addr W write. M 34 slide
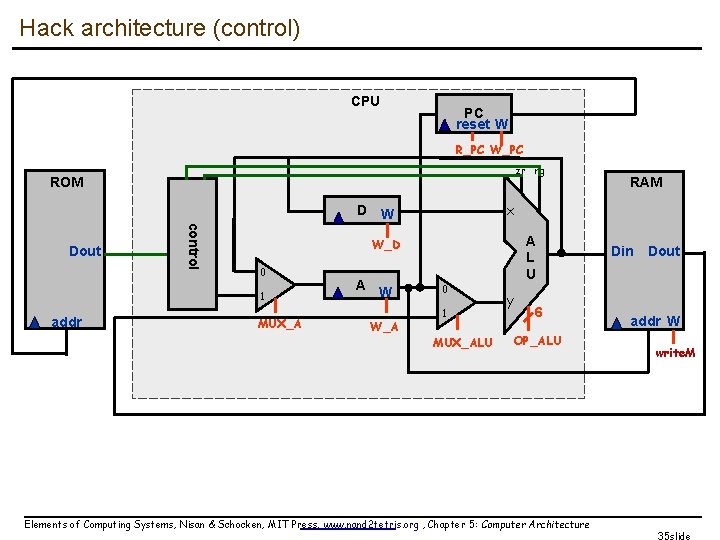
Hack architecture (control) CPU PC reset W R_PC W_PC zr ng ROM x D W control Dout 1 addr A L U W_D 0 MUX_A A W W_A RAM 0 1 MUX_ALU y 6 OP_ALU Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture Din Dout addr W write. M 35 slide
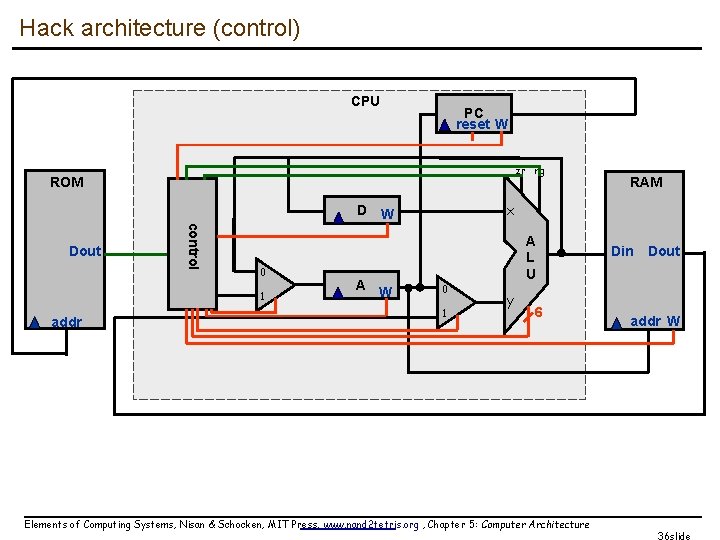
Hack architecture (control) CPU PC reset W zr ng ROM x D W control Dout 0 1 addr A W RAM 0 1 A L U y 6 Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture Din Dout addr W 36 slide
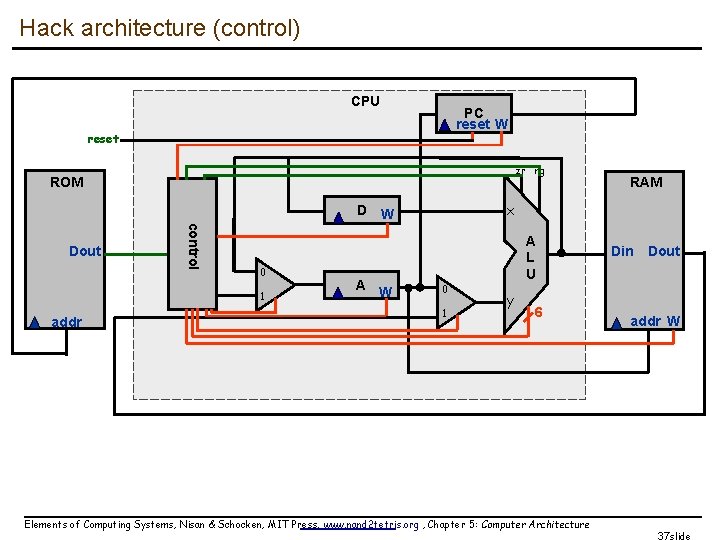
Hack architecture (control) CPU PC reset W reset zr ng ROM x D W control Dout 0 1 addr A W RAM 0 1 A L U y 6 Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture Din Dout addr W 37 slide
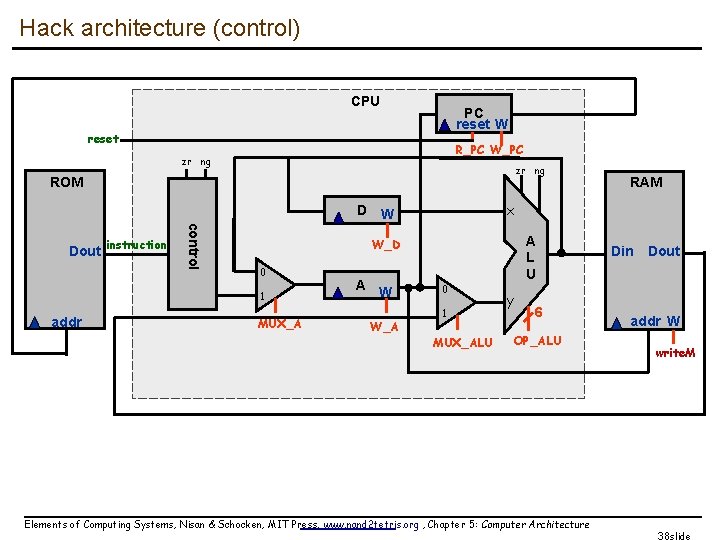
Hack architecture (control) CPU PC reset W reset R_PC W_PC zr ng ROM x D W control Dout instruction 1 addr A L U W_D 0 MUX_A A W W_A RAM 0 1 MUX_ALU y 6 OP_ALU Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture Din Dout addr W write. M 38 slide
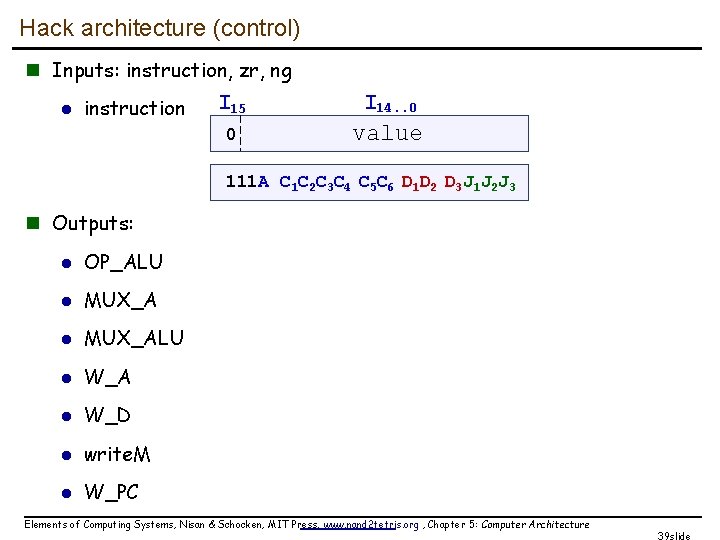
Hack architecture (control) n Inputs: instruction, zr, ng l instruction I 15 0 I 14. . 0 value 111 A C 1 C 2 C 3 C 4 C 5 C 6 D 1 D 2 D 3 J 1 J 2 J 3 n Outputs: l OP_ALU l MUX_ALU l W_A l W_D l write. M l W_PC Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 39 slide
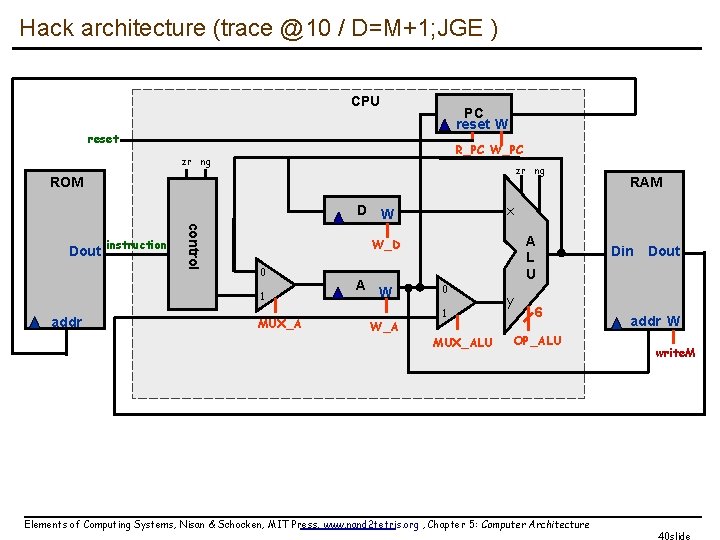
Hack architecture (trace @10 / D=M+1; JGE ) CPU PC reset W reset R_PC W_PC zr ng ROM x D W control Dout instruction 1 addr A L U W_D 0 MUX_A A W W_A RAM 0 1 MUX_ALU y 6 OP_ALU Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture Din Dout addr W write. M 40 slide
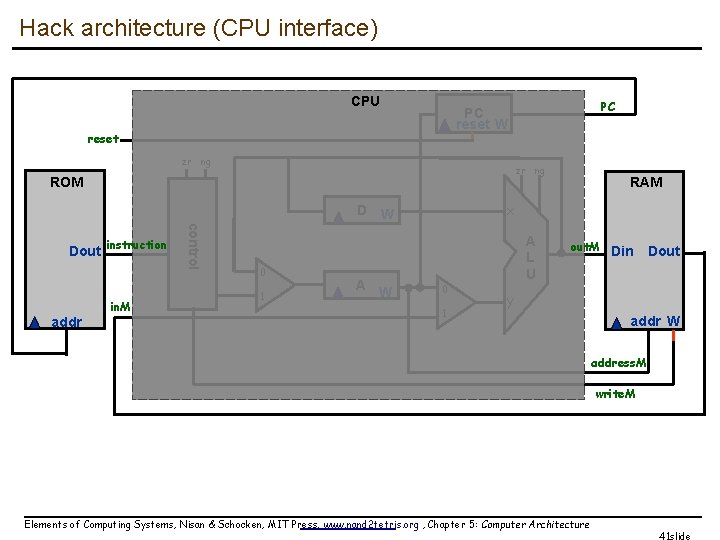
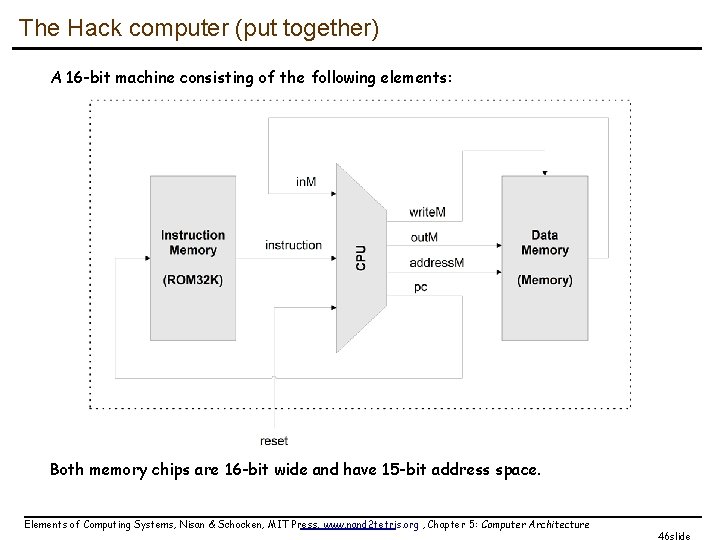
Hack architecture (CPU interface) CPU reset zr ng ROM control addr in. M 0 1 A W RAM x D W Dout instruction PC PC reset W 0 1 A L U out. M Din Dout y addr W address. M write. M Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 41 slide
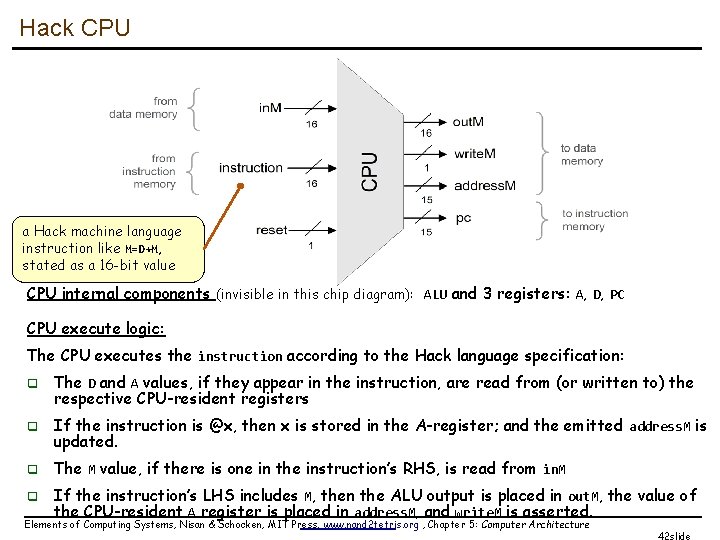
Hack CPU a Hack machine language instruction like M=D+M, stated as a 16 -bit value CPU internal components (invisible in this chip diagram): ALU and 3 registers: A, D, PC CPU execute logic: The CPU executes the instruction according to the Hack language specification: q The D and A values, if they appear in the instruction, are read from (or written to) the respective CPU-resident registers q If the instruction is @x, then x is stored in the A-register; and the emitted address. M is updated. q The M value, if there is one in the instruction’s RHS, is read from in. M q If the instruction’s LHS includes M, then the ALU output is placed in out. M, the value of the CPU-resident A register is placed in address. M, and write. M is asserted. Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 42 slide
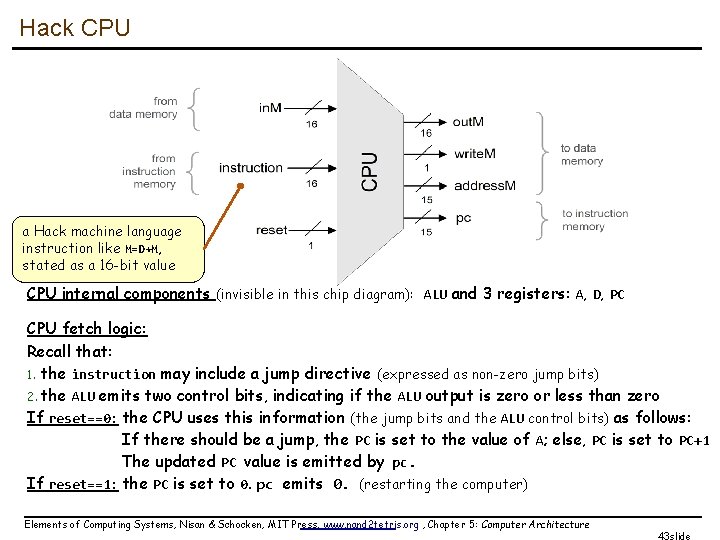
Hack CPU a Hack machine language instruction like M=D+M, stated as a 16 -bit value CPU internal components (invisible in this chip diagram): ALU and 3 registers: A, D, PC CPU fetch logic: Recall that: 1. the instruction may include a jump directive (expressed as non-zero jump bits) 2. the ALU emits two control bits, indicating if the ALU output is zero or less than zero If reset==0: the CPU uses this information (the jump bits and the ALU control bits) as follows: If there should be a jump, the PC is set to the value of A; else, PC is set to PC+1 The updated PC value is emitted by pc. If reset==1: the PC is set to 0. pc emits 0. (restarting the computer) Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 43 slide
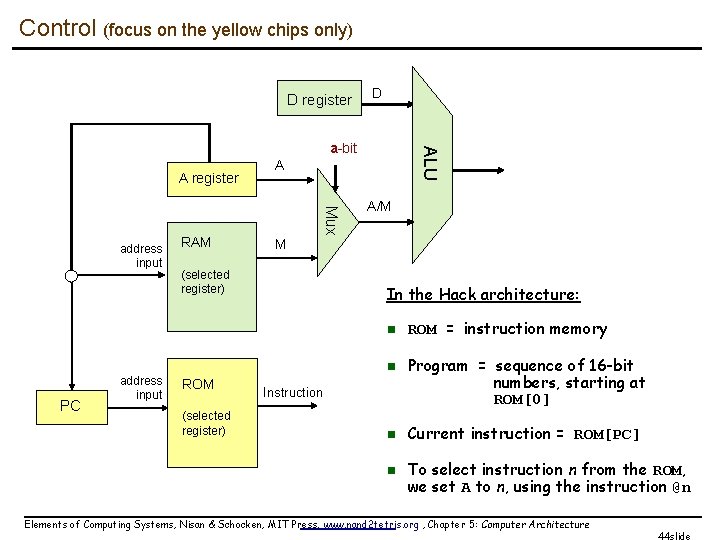
Control (focus on the yellow chips only) D register D A register RAM A Mux address input ALU a-bit A/M M (selected register) In the Hack architecture: n n PC address input ROM (selected register) Instruction n n ROM = instruction memory Program = sequence of 16 -bit numbers, starting at ROM[0] Current instruction = ROM[PC] To select instruction n from the ROM, we set A to n, using the instruction @n Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 44 slide
Side note (focus on the yellow chip parts only) D register D A register PC address input RAM A M (selected register) ROM (selected register) A/M Mux address input ALU a-bit Instruction In the Hack architecture, the A register addresses both the RAM and the ROM, simultaneously. Therefore: n Command pairs like @addr followed by D=M; some. Jump. Directive make no sense n n Best practice: in well-written Hack programs, a C-instruction should contain q either a reference to M, or q a jump directive, but not both. Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 45 slide
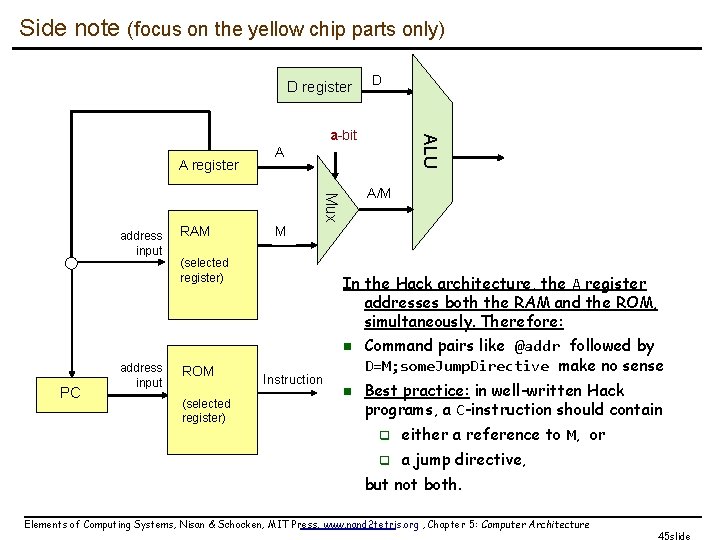
The Hack computer (put together) A 16 -bit machine consisting of the following elements: Both memory chips are 16 -bit wide and have 15 -bit address space. Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 46 slide
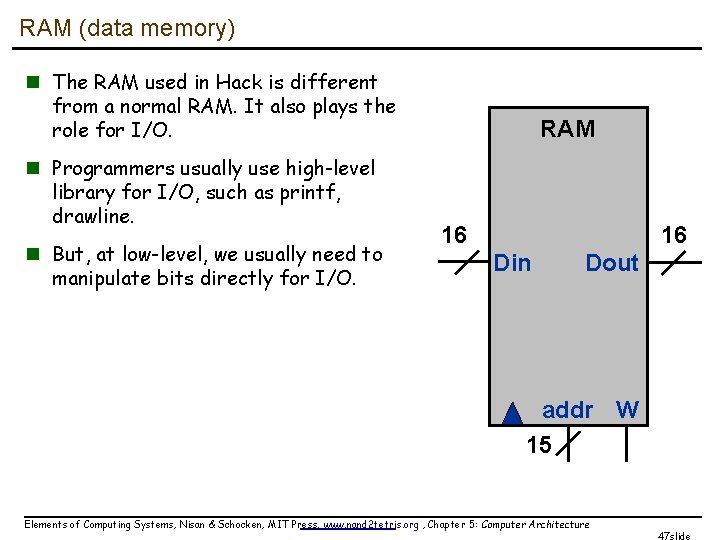
RAM (data memory) n The RAM used in Hack is different from a normal RAM. It also plays the role for I/O. n Programmers usually use high-level library for I/O, such as printf, drawline. n But, at low-level, we usually need to manipulate bits directly for I/O. RAM 16 16 Din Dout addr W 15 Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 47 slide
Displays n CRT displays l resolution l refresh rate Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 48 slide
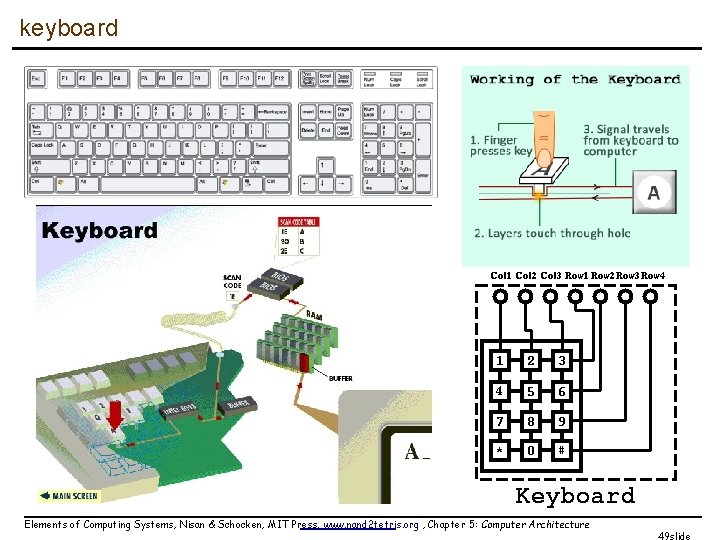
keyboard Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 49 slide
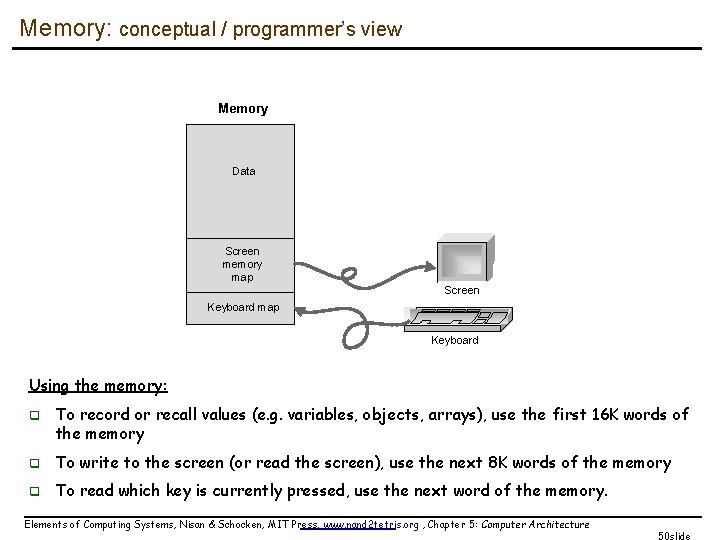
Memory: conceptual / programmer’s view Memory Data Screen memory map Screen Keyboard map Keyboard Using the memory: q To record or recall values (e. g. variables, objects, arrays), use the first 16 K words of the memory q To write to the screen (or read the screen), use the next 8 K words of the memory q To read which key is currently pressed, use the next word of the memory. Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 50 slide
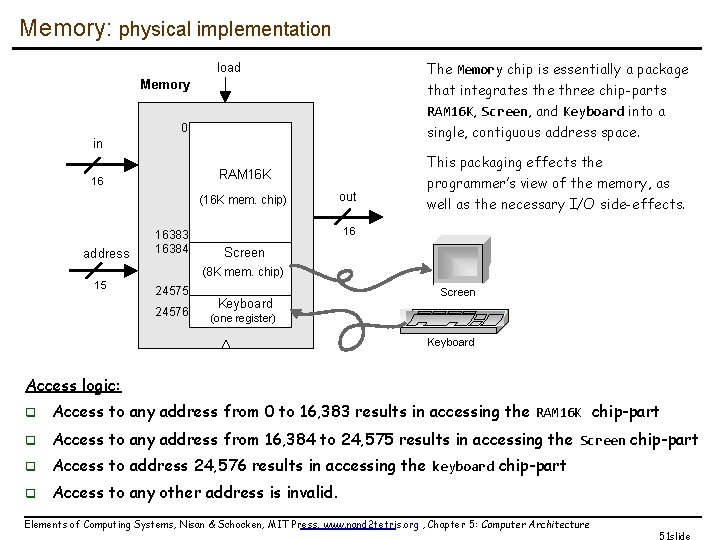
Memory: physical implementation The Memory chip is essentially a package load Memory that integrates the three chip-parts RAM 16 K, Screen, and Keyboard into a 0 single, contiguous address space. in 16 (16 K mem. chip) address This packaging effects the RAM 16 K 16383 16384 out programmer’s view of the memory, as well as the necessary I/O side-effects. 16 Screen (8 K mem. chip) 15 24576 Keyboard Screen (one register) Keyboard Access logic: q Access to any address from 0 to 16, 383 results in accessing the RAM 16 K chip-part q Access to any address from 16, 384 to 24, 575 results in accessing the Screen chip-part q Access to address 24, 576 results in accessing the keyboard chip-part q Access to any other address is invalid. Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 51 slide
![Data memory Low-level (hardware) read/write logic: load To read RAM[k]: set address to k, Data memory Low-level (hardware) read/write logic: load To read RAM[k]: set address to k,](http://slidetodoc.com/presentation_image_h/73d46a41fc3f758baba3b9747934ea19/image-52.jpg)
Data memory Low-level (hardware) read/write logic: load To read RAM[k]: set address to k, probe out To write RAM[k]=x: set address to k, set in to x, set load to 1, run the clock High-level (OS) read/write logic: To read RAM[k]: use the OS command out = peek(k) To write RAM[k]=x: use the OS command poke(k, x) peek and poke are OS commands whose implementation should effect the same behavior as the low-level commands More about peek and poke this later in the course, when we’ll write the OS. Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 52 slide
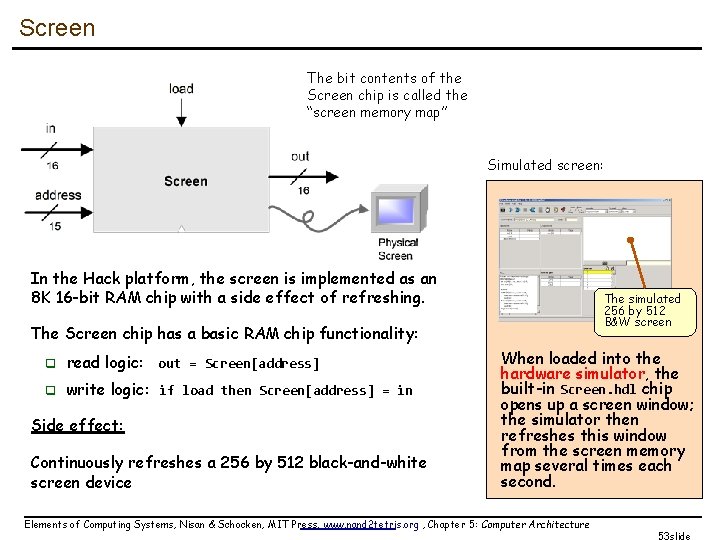
Screen The bit contents of the Screen chip is called the “screen memory map” Simulated screen: In the Hack platform, the screen is implemented as an 8 K 16 -bit RAM chip with a side effect of refreshing. The simulated 256 by 512 B&W screen The Screen chip has a basic RAM chip functionality: q read logic: out = Screen[address] q write logic: if load then Screen[address] = in Side effect: Continuously refreshes a 256 by 512 black-and-white screen device When loaded into the hardware simulator, the built-in Screen. hdl chip opens up a screen window; the simulator then refreshes this window from the screen memory map several times each second. Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 53 slide
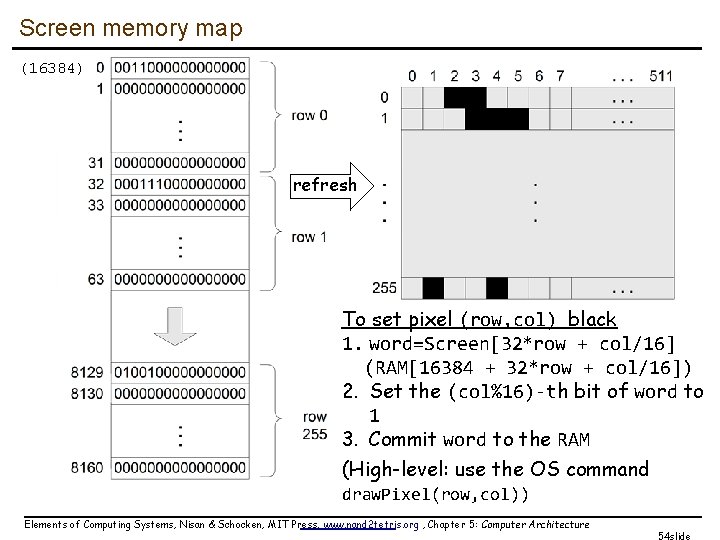
Screen memory map (16384) refresh To set pixel (row, col) black 1. word=Screen[32*row + col/16] (RAM[16384 + 32*row + col/16]) 2. Set the (col%16)-th bit of word to 1 3. Commit word to the RAM (High-level: use the OS command draw. Pixel(row, col)) Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 54 slide
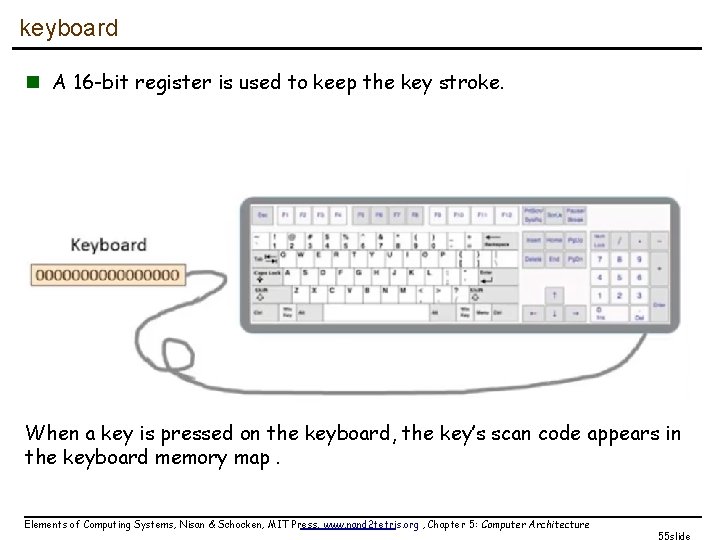
keyboard n A 16 -bit register is used to keep the key stroke. When a key is pressed on the keyboard, the key’s scan code appears in the keyboard memory map. Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 55 slide
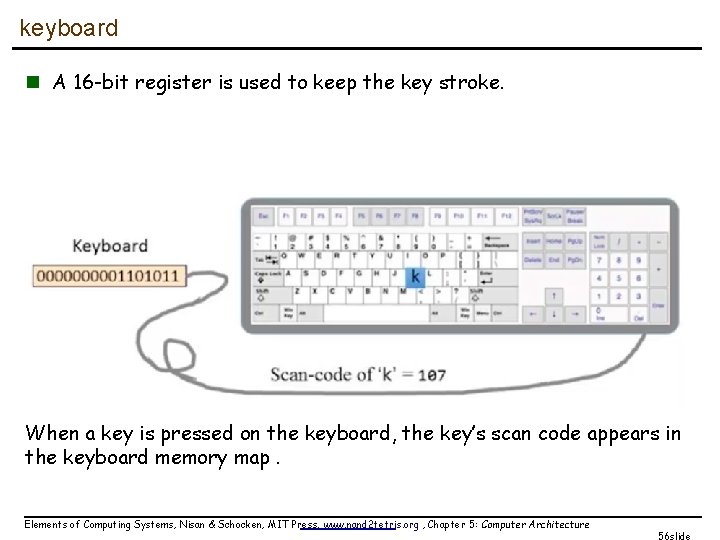
keyboard n A 16 -bit register is used to keep the key stroke. When a key is pressed on the keyboard, the key’s scan code appears in the keyboard memory map. Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 56 slide
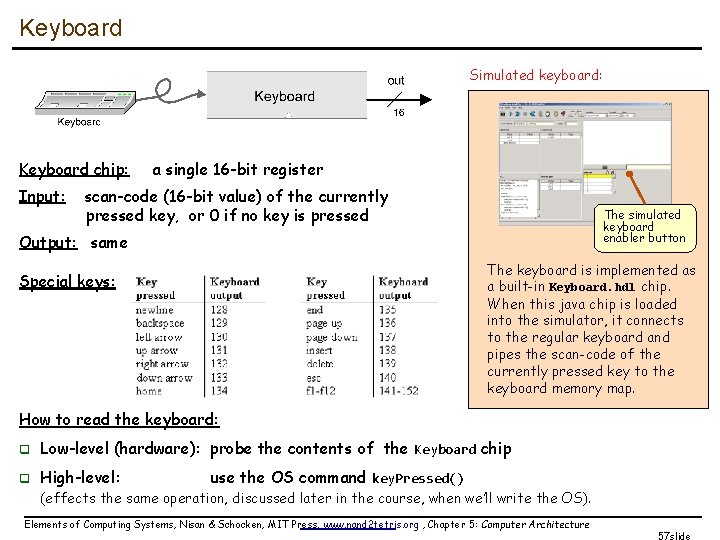
Keyboard Simulated keyboard: Keyboard chip: Input: a single 16 -bit register scan-code (16 -bit value) of the currently pressed key, or 0 if no key is pressed The simulated keyboard enabler button Output: same The keyboard is implemented as a built-in Keyboard. hdl chip. When this java chip is loaded into the simulator, it connects to the regular keyboard and pipes the scan-code of the currently pressed key to the keyboard memory map. Special keys: How to read the keyboard: q Low-level (hardware): probe the contents of the Keyboard chip q High-level: q (effects the same operation, discussed later in the course, when we’ll write the OS). use the OS command key. Pressed() Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 57 slide
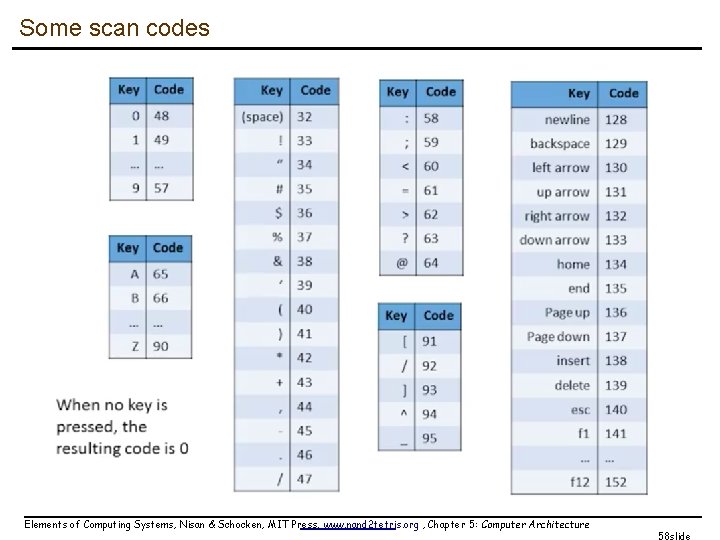
Some scan codes Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 58 slide
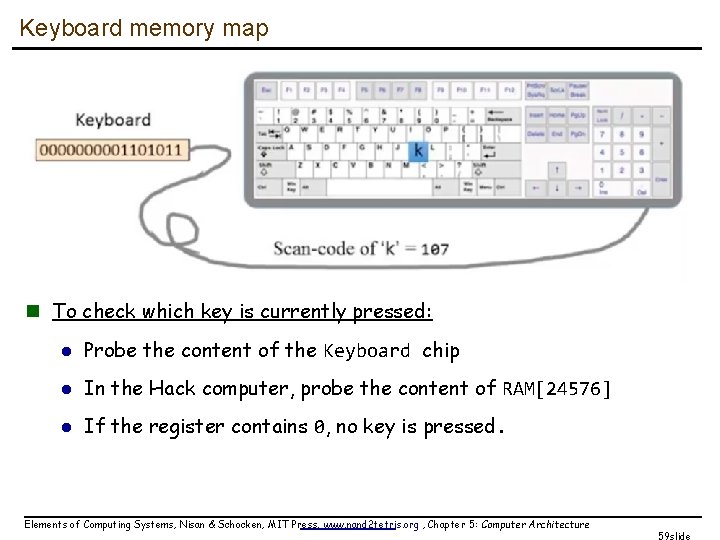
Keyboard memory map n To check which key is currently pressed: l Probe the content of the Keyboard chip l In the Hack computer, probe the content of RAM[24576] l If the register contains 0, no key is pressed. Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 59 slide
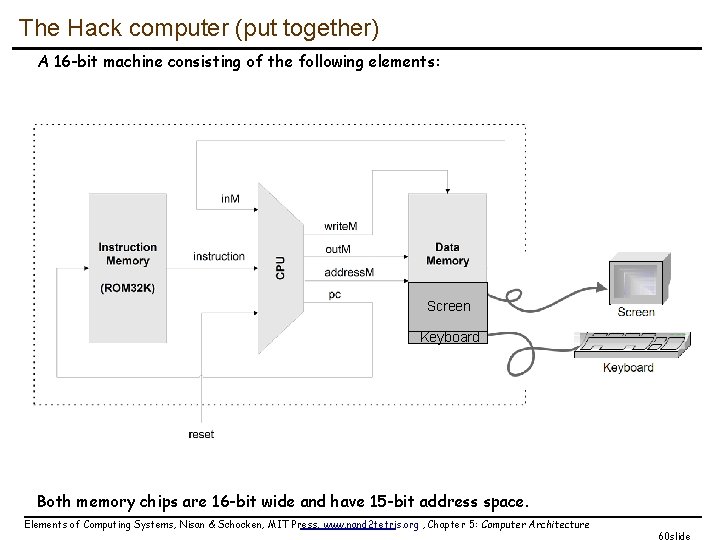
The Hack computer (put together) A 16 -bit machine consisting of the following elements: Screen Keyboard Both memory chips are 16 -bit wide and have 15 -bit address space. Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 60 slide
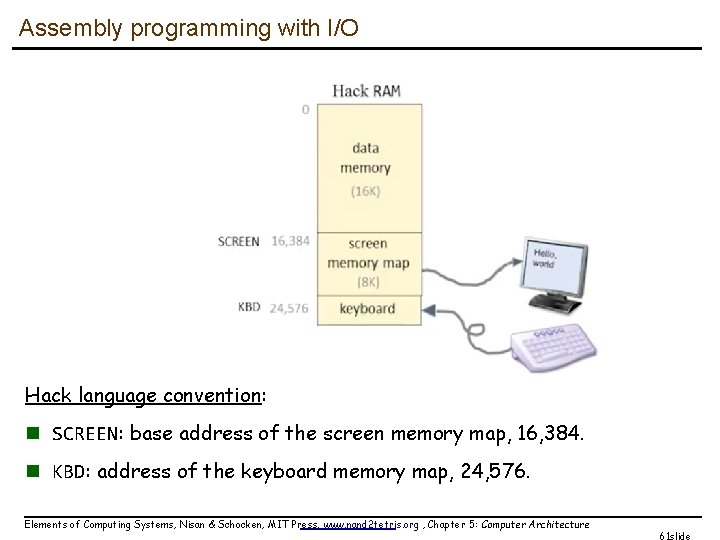
Assembly programming with I/O Hack language convention: n SCREEN: base address of the screen memory map, 16, 384. n KBD: address of the keyboard memory map, 24, 576. Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 61 slide
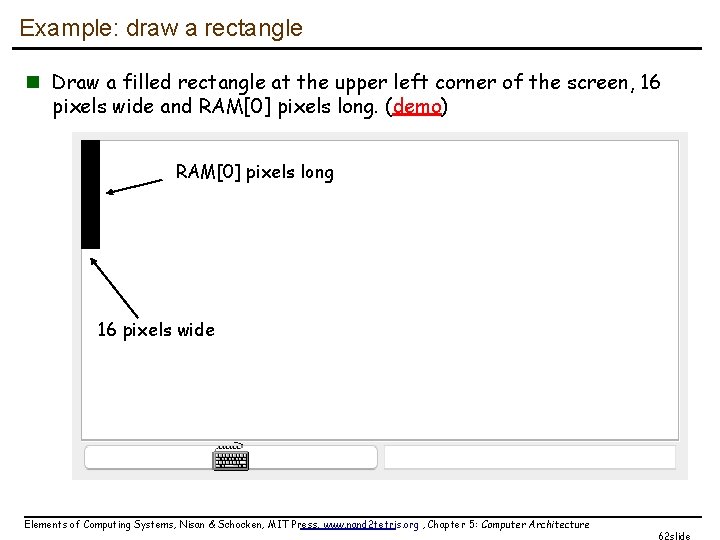
Example: draw a rectangle n Draw a filled rectangle at the upper left corner of the screen, 16 pixels wide and RAM[0] pixels long. (demo) RAM[0] pixels long 16 pixels wide Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 62 slide
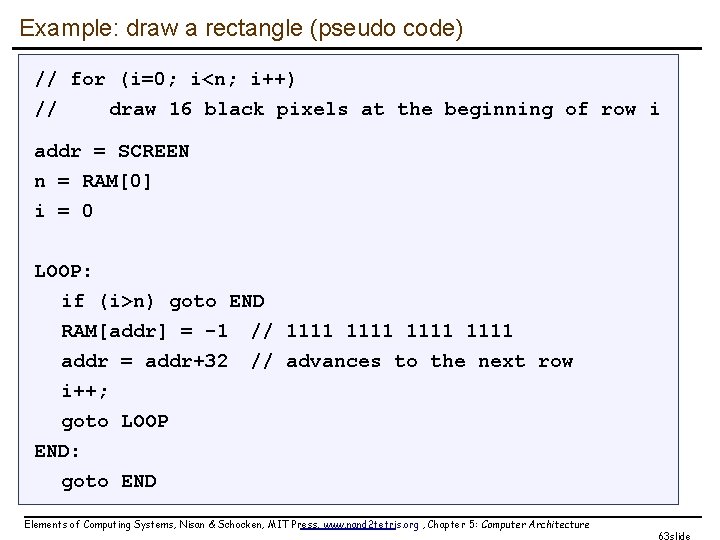
Example: draw a rectangle (pseudo code) // for (i=0; i<n; i++) // draw 16 black pixels at the beginning of row i addr = SCREEN n = RAM[0] i = 0 LOOP: if (i>n) goto END RAM[addr] = -1 // 1111 addr = addr+32 // advances to the next row i++; goto LOOP END: goto END Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 63 slide
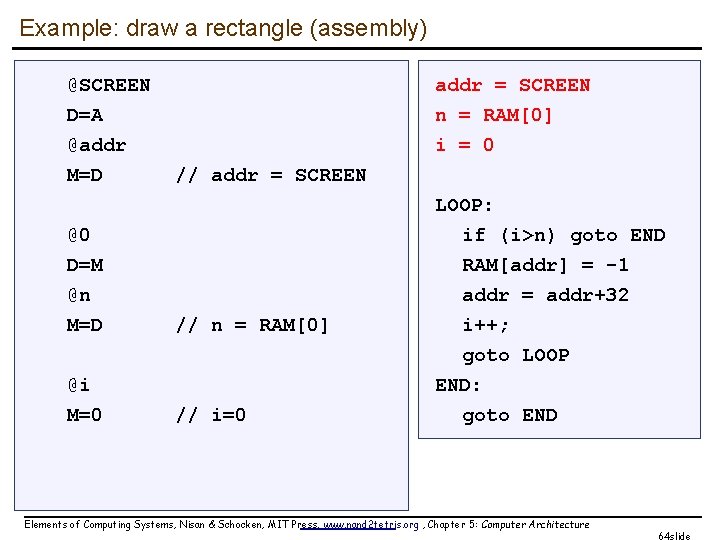
Example: draw a rectangle (assembly) @SCREEN D=A @addr M=D addr = SCREEN n = RAM[0] i = 0 // addr = SCREEN @0 D=M @n M=D // n = RAM[0] @i M=0 // i=0 LOOP: if (i>n) goto END RAM[addr] = -1 addr = addr+32 i++; goto LOOP END: goto END Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 64 slide
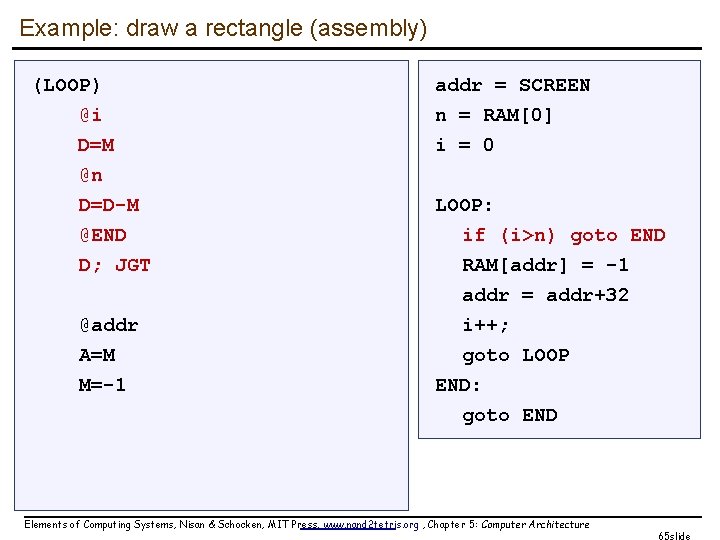
Example: draw a rectangle (assembly) (LOOP) @i D=M @n D=D-M @END D; JGT @addr A=M M=-1 addr = SCREEN n = RAM[0] i = 0 LOOP: if (i>n) goto END RAM[addr] = -1 addr = addr+32 i++; goto LOOP END: goto END Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 65 slide
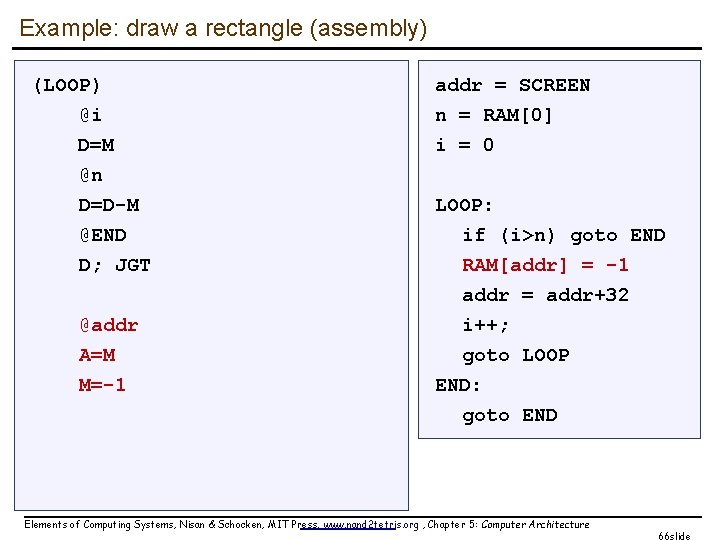
Example: draw a rectangle (assembly) (LOOP) @i D=M @n D=D-M @END D; JGT @addr A=M M=-1 addr = SCREEN n = RAM[0] i = 0 LOOP: if (i>n) goto END RAM[addr] = -1 addr = addr+32 i++; goto LOOP END: goto END Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 66 slide
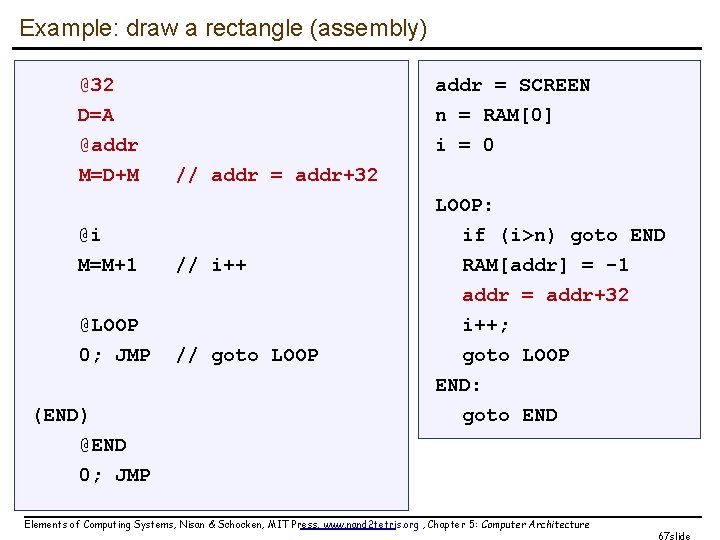
Example: draw a rectangle (assembly) @32 D=A @addr M=D+M addr = SCREEN n = RAM[0] i = 0 // addr = addr+32 @i M=M+1 // i++ @LOOP 0; JMP // goto LOOP (END) @END 0; JMP LOOP: if (i>n) goto END RAM[addr] = -1 addr = addr+32 i++; goto LOOP END: goto END Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 67 slide
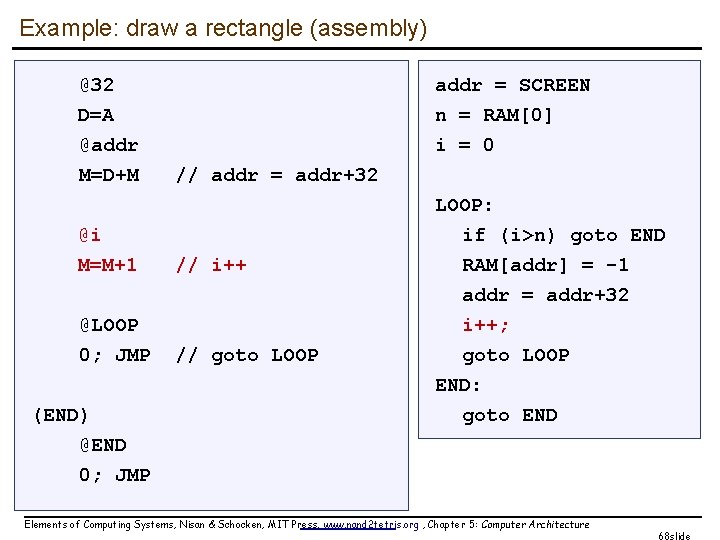
Example: draw a rectangle (assembly) @32 D=A @addr M=D+M addr = SCREEN n = RAM[0] i = 0 // addr = addr+32 @i M=M+1 // i++ @LOOP 0; JMP // goto LOOP (END) @END 0; JMP LOOP: if (i>n) goto END RAM[addr] = -1 addr = addr+32 i++; goto LOOP END: goto END Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 68 slide
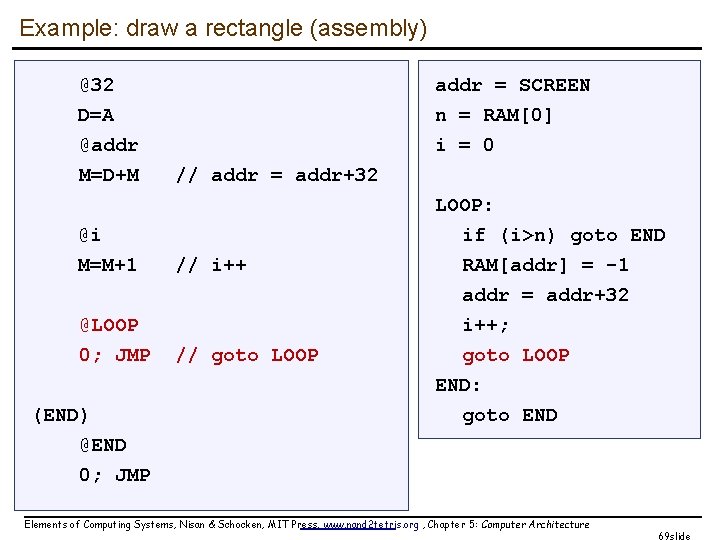
Example: draw a rectangle (assembly) @32 D=A @addr M=D+M addr = SCREEN n = RAM[0] i = 0 // addr = addr+32 @i M=M+1 // i++ @LOOP 0; JMP // goto LOOP (END) @END 0; JMP LOOP: if (i>n) goto END RAM[addr] = -1 addr = addr+32 i++; goto LOOP END: goto END Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 69 slide
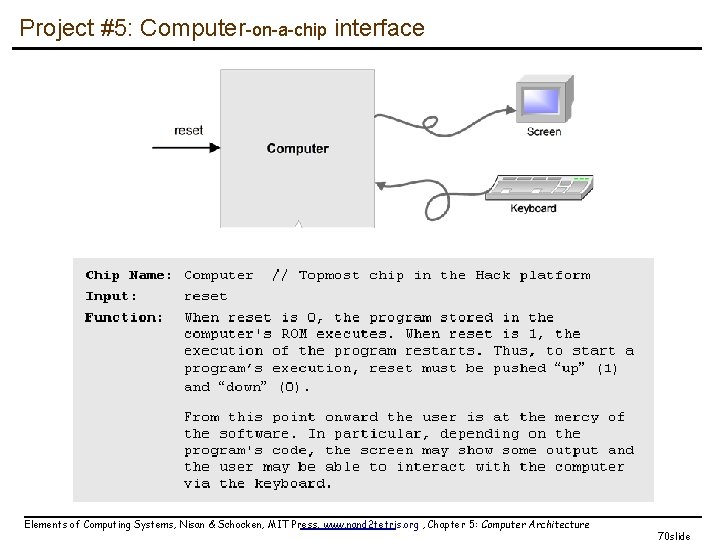
Project #5: Computer-on-a-chip interface Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 70 slide
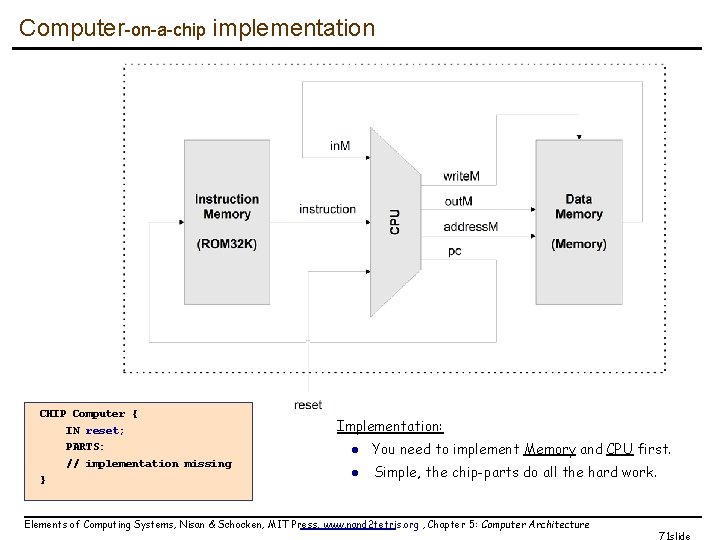
Computer-on-a-chip implementation CHIP Computer { IN reset; PARTS: // implementation missing } Implementation: l You need to implement Memory and CPU first. l Simple, the chip-parts do all the hard work. Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 71 slide
Perspective: from here to a “real” computer n Caching n More I/O units n Special-purpose processors (I/O, graphics, communications, …) n Multi-core / parallelism n Efficiency n Energy consumption considerations n And more. . . Elements of Computing Systems, Nisan & Schocken, MIT Press, www. nand 2 tetris. org , Chapter 5: Computer Architecture 72 slide
- Slides: 72