COMP 2221 Networks in Organisations Richard Henson February
COMP 2221 Networks in Organisations Richard Henson February 2016
Week 4: Some Important Network Operating Systems • Objectives: Ø Explain a (network) operating system architecture in terms of a multi-layered model Ø Briefly explain features of a typical network operating system (server end & client end) Ø Explain why user and system settings need to be controlled on networked machines Ø Explain the role of the registry in Windows desktop and network configuration, user settings, and security
What are Operating Systems? • Bundle of Software! Ømany programs working together • Make the computer function… Øcontrol of hardware Øplatform to support applications • including user interface Øutilities to control the platform • e. g. disk/file management
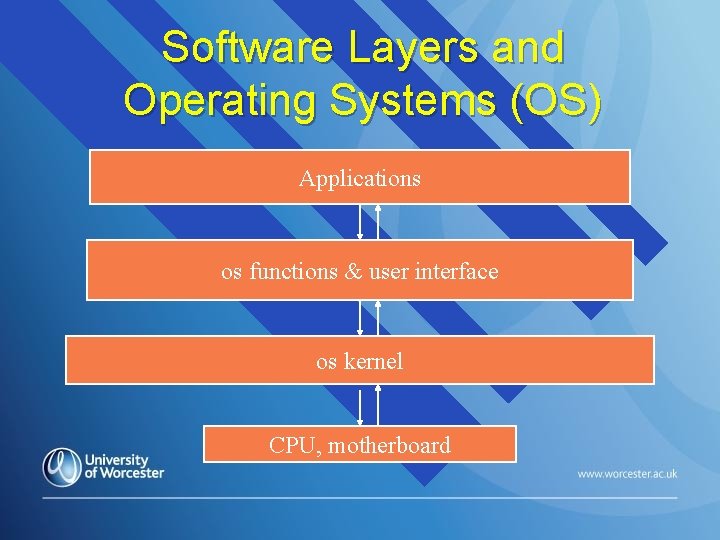
Software Layers and Operating Systems (OS) Applications os functions & user interface os kernel CPU, motherboard
What if the Operating System has software faults? • The platform becomes “unstable”!! ØCould be errors in… • • • hardware control? user interface? utilities?
On a client-server network? • Client platform unstable? • What would happen to: Øapplications running on a poorly designed platform? Øthe rest of the local network? Øbusinesses depending on such apps?
Software Faults & CWE • Lot of recent interest in why software (even • some operating systems…) is so unreliable Mitre Corporation (US) with govt backing… Ø classified software fault types into a Common Weakness Enumeration (CWE) • community developed, formal list of software weakness types • Intended use of CWE: Øto better describe software weaknesses in architecture, design, or code 7 [TSI/2012/183] © Copyright 2003 -2012
More about CWE • CWE provides: Østandard measuring stick for software tools targeting software weaknesses Øcommon baseline standard for efforts to identify, mitigate, and prevent software weaknesses • Currently 998 distinct CWE entries identified by Mitre!! (version 2. 9) Øhttp: //cwe. mitre. org/data Ømore commonly encountered weaknesses usually “repeat offenders”
Example of an operating system flaw • Apple: Ødangerous flaw revealed in i. OS 7 and X (21/2/14) Øhttp: //gizmodo. com/why-apples-hugesecurity-flaw-is-so-scary 1529041062? utm_campaign=socialflow_gi zmodo_facebook&utm_source=gizmodo_fa cebook&utm_medium=socialflow
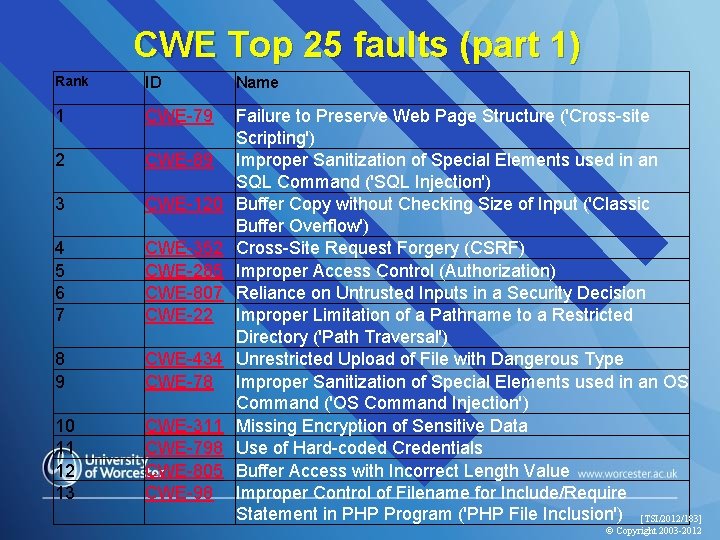
CWE Top 25 faults (part 1) Rank ID Name 1 CWE-79 2 CWE-89 3 CWE-120 4 5 6 7 CWE-352 CWE-285 CWE-807 CWE-22 8 9 CWE-434 CWE-78 10 11 12 13 CWE-311 CWE-798 CWE-805 CWE-98 Failure to Preserve Web Page Structure ('Cross-site Scripting') Improper Sanitization of Special Elements used in an SQL Command ('SQL Injection') Buffer Copy without Checking Size of Input ('Classic Buffer Overflow') Cross-Site Request Forgery (CSRF) Improper Access Control (Authorization) Reliance on Untrusted Inputs in a Security Decision Improper Limitation of a Pathname to a Restricted Directory ('Path Traversal') Unrestricted Upload of File with Dangerous Type Improper Sanitization of Special Elements used in an OS Command ('OS Command Injection') Missing Encryption of Sensitive Data Use of Hard-coded Credentials Buffer Access with Incorrect Length Value Improper Control of Filename for Include/Require Statement in PHP Program ('PHP File Inclusion') [TSI/2012/183] © Copyright 2003 -2012
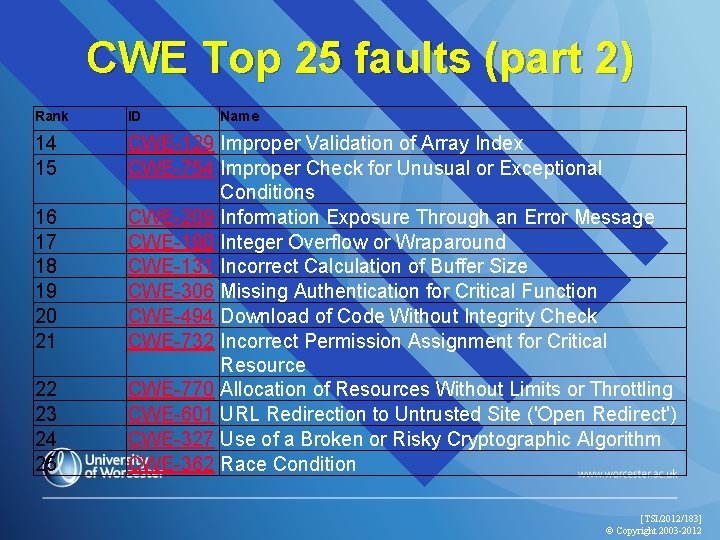
CWE Top 25 faults (part 2) Rank ID 14 15 CWE-129 Improper Validation of Array Index CWE-754 Improper Check for Unusual or Exceptional Conditions CWE-209 Information Exposure Through an Error Message CWE-190 Integer Overflow or Wraparound CWE-131 Incorrect Calculation of Buffer Size CWE-306 Missing Authentication for Critical Function CWE-494 Download of Code Without Integrity Check CWE-732 Incorrect Permission Assignment for Critical Resource CWE-770 Allocation of Resources Without Limits or Throttling CWE-601 URL Redirection to Untrusted Site ('Open Redirect') CWE-327 Use of a Broken or Risky Cryptographic Algorithm CWE-362 Race Condition 16 17 18 19 20 21 22 23 24 25 Name [TSI/2012/183] © Copyright 2003 -2012
TSI Logo Susceptibilities • The confirmed presence of one or more • vulnerabilities within an implemented system, such as the presence of an operating system with a buffer overflow defect Susceptibilities in systems stem from: Ø a. initial implementation Ø b. changes to software, such as from adding new facilities or the correction of detected errors (‘patching’) Ø c. use of utility programs, which may be capable of circumventing security measures in the controlling or application software [TSI/2013/306 | Draft 0. B | 2014 -02 -10]
TSI Logo Vulnerabilities • Vulnerabilities can be: Ø The existence of a generic weakness in a particular platform, such as a buffer overflow occurring in a specific operating system or application Ø Interactions between multiple software elements that bypass intended controls Ø Accidental actions of software developers that result in defects and deviations Ø Deliberate actions of software developers that bypass intended controls, such as trap doors that permit unauthorised access to the system [TSI/2013/306 | Draft 0. B | 2014 -02 -10]
![Vulnerabilities from Major Vendors (2011 figures) [TSI/2012/183] © Copyright 2003 -2012 Vulnerabilities from Major Vendors (2011 figures) [TSI/2012/183] © Copyright 2003 -2012](http://slidetodoc.com/presentation_image_h2/83d3c1770ff06798c63823d8defa142f/image-14.jpg)
Vulnerabilities from Major Vendors (2011 figures) [TSI/2012/183] © Copyright 2003 -2012
Software Weakness Mitigation • What to do about all these faults…. ? • Many concepts and practices needed for Trustworthy development of software have existed for many years… Ø“Due Diligence” ØPareto 80: 20 15 [TSI/2012/183] © Copyright 2003 -2012
Due Diligence ØImplies software should be reasonably trustworthy…. • what does “reasonably” mean? ØImplementations vary with Audiences and Assurance Requirements
Pareto 80: 20 (favoured by TSI) ØPractice improved iteratively using existing experience ØExample: • switching on and acting on Compiler Warning Flags… n would obviates many common “repeat offender” weaknesses • If only this was normal practice!!! It could be….
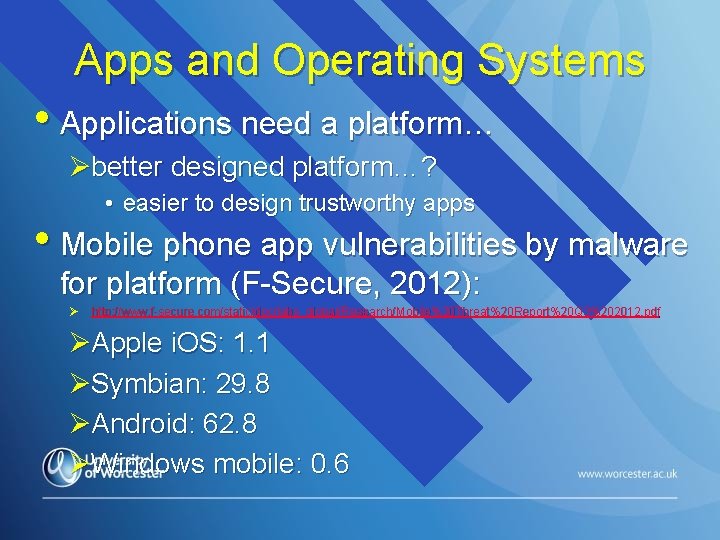
Apps and Operating Systems • Applications need a platform… Øbetter designed platform…? • easier to design trustworthy apps • Mobile phone app vulnerabilities by malware for platform (F-Secure, 2012): Ø http: //www. f-secure. com/static/doc/labs_global/Research/Mobile%20 Threat%20 Report%20 Q 3%202012. pdf ØApple i. OS: 1. 1 ØSymbian: 29. 8 ØAndroid: 62. 8 ØWindows mobile: 0. 6
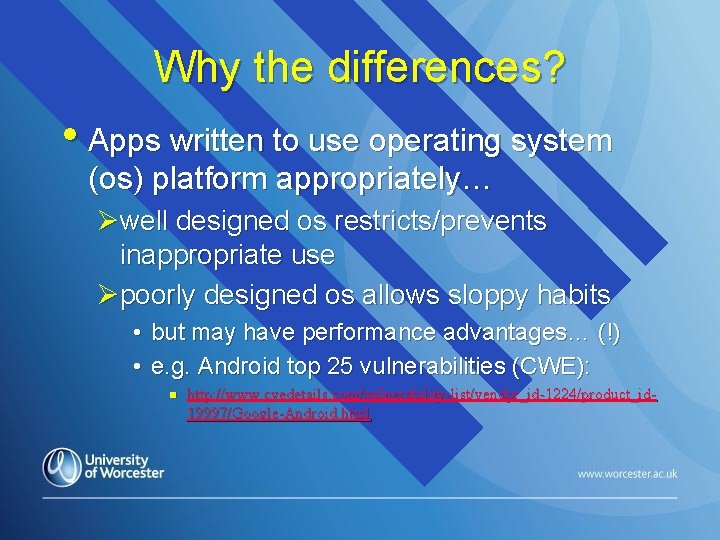
Why the differences? • Apps written to use operating system (os) platform appropriately… Øwell designed os restricts/prevents inappropriate use Øpoorly designed os allows sloppy habits • but may have performance advantages… (!) • e. g. Android top 25 vulnerabilities (CWE): n http: //www. cvedetails. com/vulnerability-list/vendor_id-1224/product_id 19997/Google-Android. html
Operating Systems for PC Ethernet Networks • Original Topology (1980 s, early 90 s): Øbus, coaxial cable & BNC connectors (!) • DOS? ØNo way! not designed for: • server end stuff • distributed communications • security…
Client-side Developments… • Microsoft Domination… Ø XP: finished off the evolution from Windows 95/98 Ø Vista: mainly a desktop change • not universally appreciated! • mobile devices started to have: n n CPUs & operating systems (!) user interfaces & use apps… • Reaction to Vista… Ø Apple became popular Ø other “mobile” desktops became popular • Windows 7 stopped the rot… • Windows Mobile: good platform for apps Ø but Windows client-end dominance lost for good…
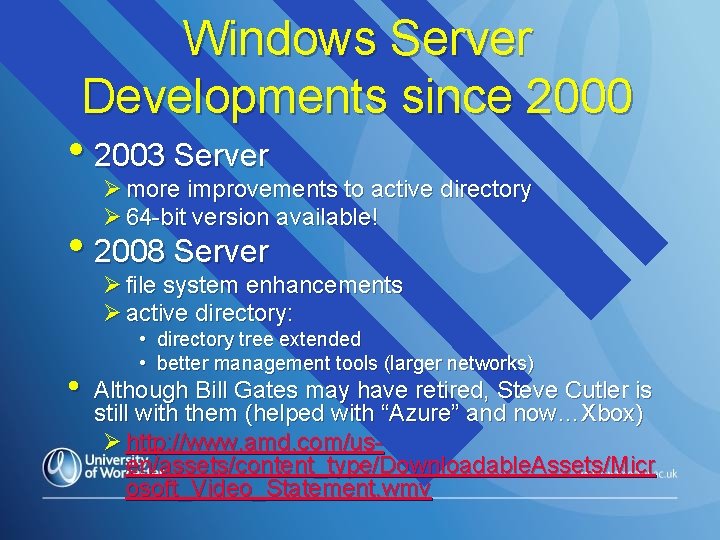
Windows Server Developments since 2000 • 2003 Server Ø more improvements to active directory Ø 64 -bit version available! • 2008 Server Ø file system enhancements Ø active directory: • • directory tree extended • better management tools (larger networks) Although Bill Gates may have retired, Steve Cutler is still with them (helped with “Azure” and now…Xbox) Ø http: //www. amd. com/usen/assets/content_type/Downloadable. Assets/Micr osoft_Video_Statement. wmv
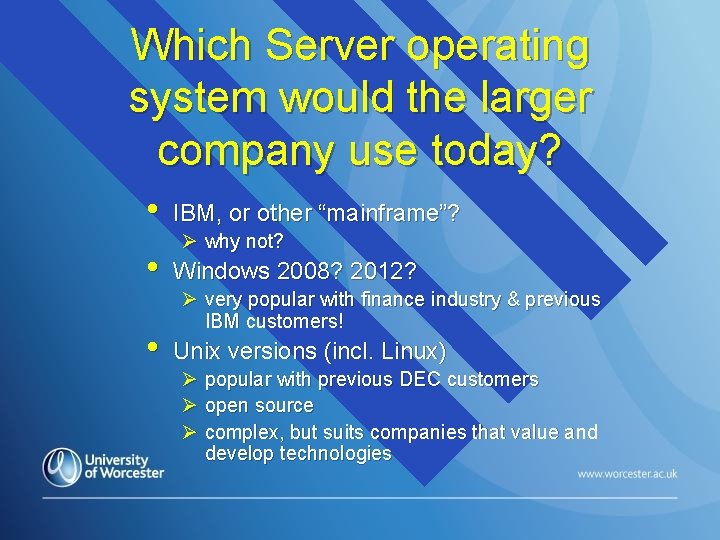
Which Server operating system would the larger company use today? • IBM, or other “mainframe”? • Windows 2008? 2012? • Unix versions (incl. Linux) Ø why not? Ø very popular with finance industry & previous IBM customers! Ø popular with previous DEC customers Ø open source Ø complex, but suits companies that value and develop technologies
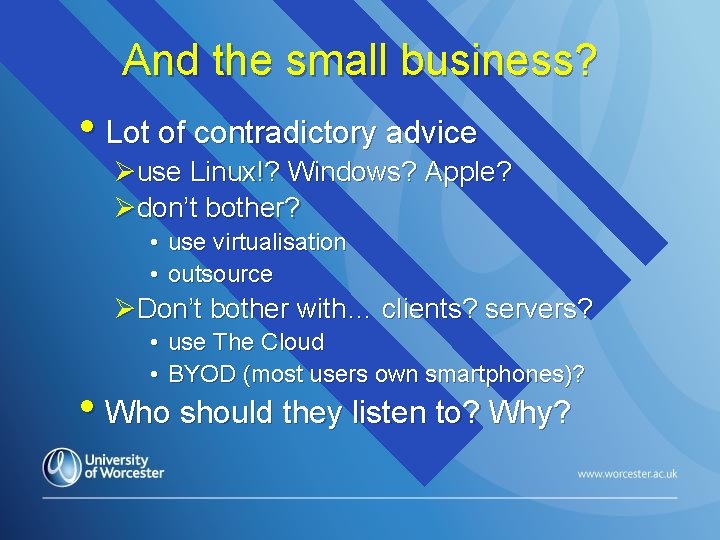
And the small business? • Lot of contradictory advice Øuse Linux!? Windows? Apple? Ødon’t bother? • use virtualisation • outsource ØDon’t bother with… clients? servers? • use The Cloud • BYOD (most users own smartphones)? • Who should they listen to? Why?
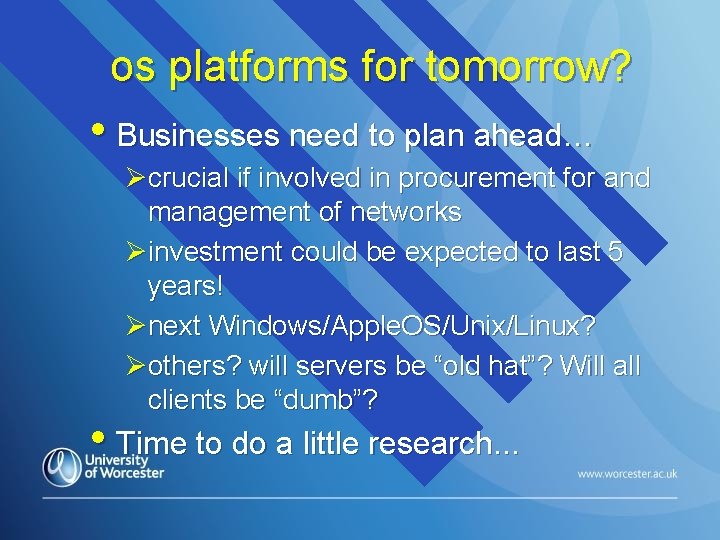
os platforms for tomorrow? • Businesses need to plan ahead… Øcrucial if involved in procurement for and management of networks Øinvestment could be expected to last 5 years! Ønext Windows/Apple. OS/Unix/Linux? Øothers? will servers be “old hat”? Will all clients be “dumb”? • Time to do a little research. . .

What is a “platform”? • Hardware that will support a CPU Ø motherboard (or eq 1 uiv) Ø ROM and RAM Ø hard disk and controller • Software that executes through the CPU to provide a stable user environment Ø low-level operating system functions Ø utilities Ø user interface
Connectivity between platforms • OSI: Seven Layer model • As far as the user is concerned… Ølayer 7 is all that matters • But there should be access control… Øuser needs to log on (via level 5) Øachieved through level 7 pop up and input coupled to interrogation of local or LAN database
BIOS Developments • Earlier motherboards had a single chip containing the BIOS on ROM and a writeable CMOS area Ø the command line interface invoked was 16 -bit • More recent motherboards use EFI (Extensible Firmware Interface) Ø uses a 32 -bit command line Ø only really exploited with Windows 7, and 2008 Server…
Access control and networks • Organisations have responsibilities, and confidentiality Ønowadays, these are delivered through the network • Confidentiality. Integrity: Øe. g. Personal data held under the Data Protection Act • Availability: Øthose who need access to files & services must have it…
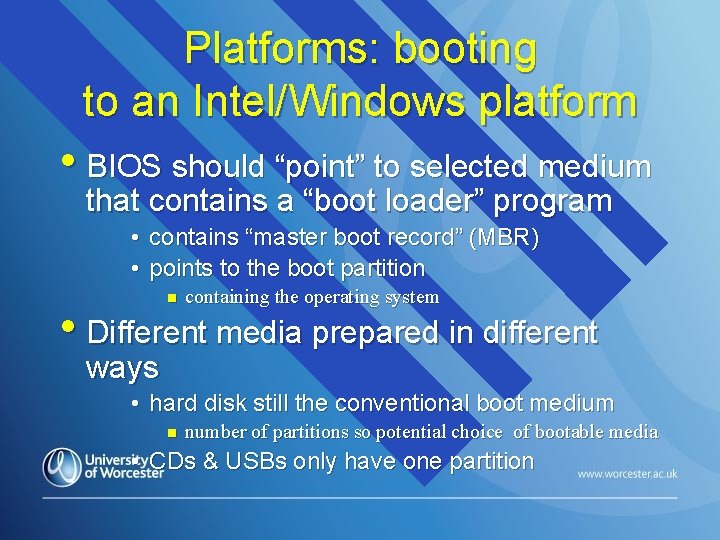
Platforms: booting to an Intel/Windows platform • BIOS should “point” to selected medium that contains a “boot loader” program • contains “master boot record” (MBR) • points to the boot partition n containing the operating system • Different media prepared in different ways • hard disk still the conventional boot medium n number of partitions so potential choice of bootable media • CDs & USBs only have one partition
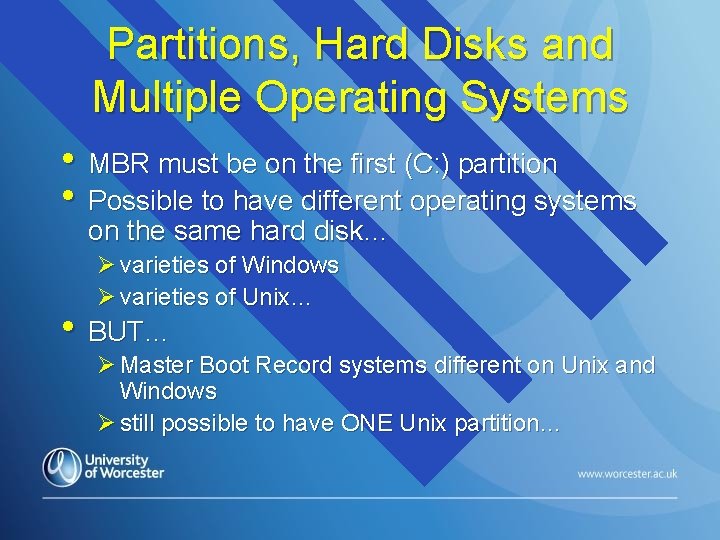
Partitions, Hard Disks and Multiple Operating Systems • MBR must be on the first (C: ) partition • Possible to have different operating systems on the same hard disk… Ø varieties of Windows Ø varieties of Unix… • BUT… Ø Master Boot Record systems different on Unix and Windows Ø still possible to have ONE Unix partition…
Logon • Once the operating system has been loaded… Øuser logon screen presented • Rapid local boot is fine… Øbut most organisational computers are on networks… • why? Øwhy does network logon take so long?
“Policies”: Controlling User and System Settings • The Windows user’s desktop is controlled with policies Ø user policies Ø system policies • Configuring and using policies - essential part of any network administrator’s job! Ø could be 100 s or 1000 s of systems, & users
Storage of User/System Settings: Windows Registry • Early Windows extended DOS text files of system & user settings: Ø SYSTEM. INI enhanced CONFIG. SYS Ø WIN. INI enhanced AUTOEXEC. BAT • Windows 95 created a two dimensional structure… known as The Registry Ø principles later extended in Windows NT v 4 to allow system and user settings to be downloaded to local registry across the network
Viewing/Editing the Registry • REGEDT 32 from command prompt… Ølook but don’t touch! Ø contents should not be changed manually unless you really know what you are doing!!! • Registry data that is loaded into memory can also be overwritten by data: Øfrom local profiles Ødownloaded across the network…
System Settings • For configuration of hardware and software Ødifferent types of system need different settings Øsystem settings for a given computer may need to be changed for particular users e. g. to change screen refresh rate for epileptics
User Settings • More a matter of convenience for the user Ø mandatory profiles • users all get the same desktop settings! • anything added is lost during logoff! Ø roaming profiles - desktop settings preserved between user sessions • saved across the network…
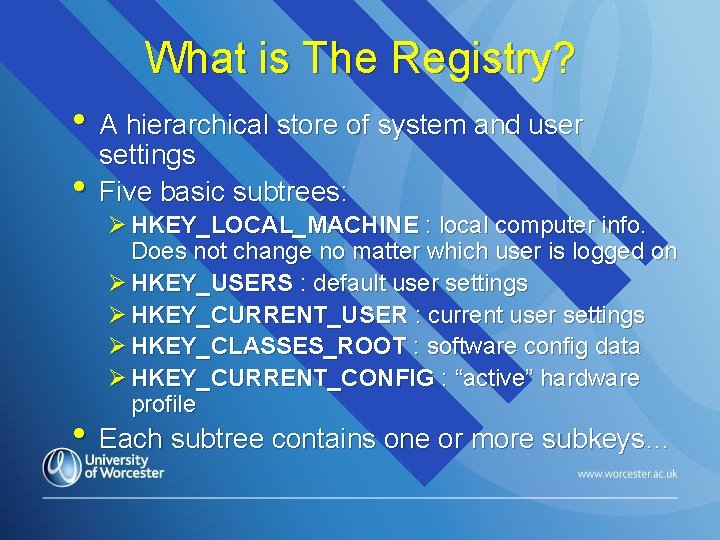
What is The Registry? • A hierarchical store of system and user • settings Five basic subtrees: Ø HKEY_LOCAL_MACHINE : local computer info. Does not change no matter which user is logged on Ø HKEY_USERS : default user settings Ø HKEY_CURRENT_USER : current user settings Ø HKEY_CLASSES_ROOT : software config data Ø HKEY_CURRENT_CONFIG : “active” hardware profile • Each subtree contains one or more subkeys…
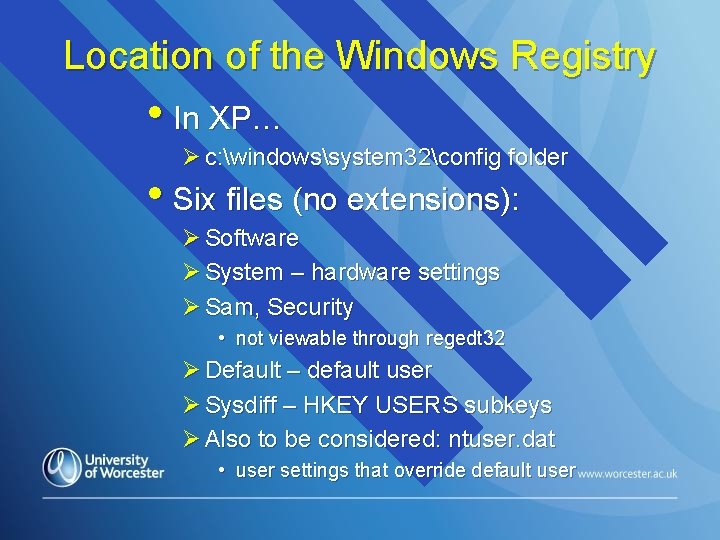
Location of the Windows Registry • In XP… Ø c: windowssystem 32config folder • Six files (no extensions): Ø Software Ø System – hardware settings Ø Sam, Security • not viewable through regedt 32 Ø Default – default user Ø Sysdiff – HKEY USERS subkeys Ø Also to be considered: ntuser. dat • user settings that override default user
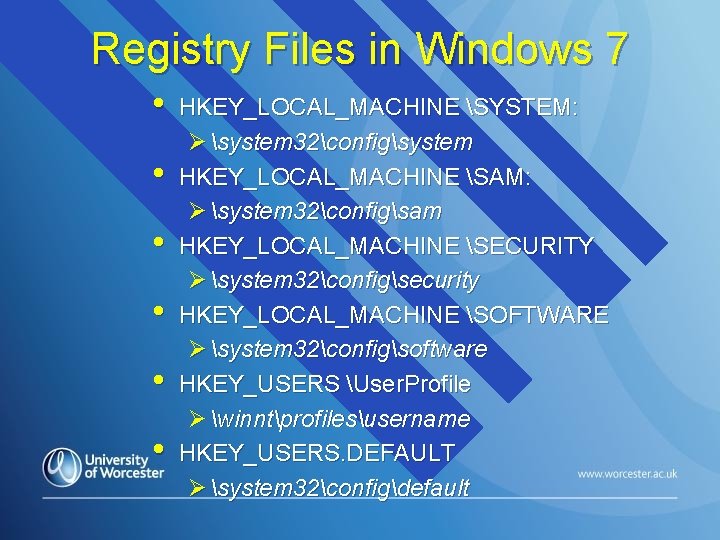
Registry Files in Windows 7 • • • HKEY_LOCAL_MACHINE SYSTEM: Ø system 32configsystem HKEY_LOCAL_MACHINE SAM: Ø system 32configsam HKEY_LOCAL_MACHINE SECURITY Ø system 32configsecurity HKEY_LOCAL_MACHINE SOFTWARE Ø system 32configsoftware HKEY_USERS User. Profile Ø winntprofilesusername HKEY_USERS. DEFAULT Ø system 32configdefault
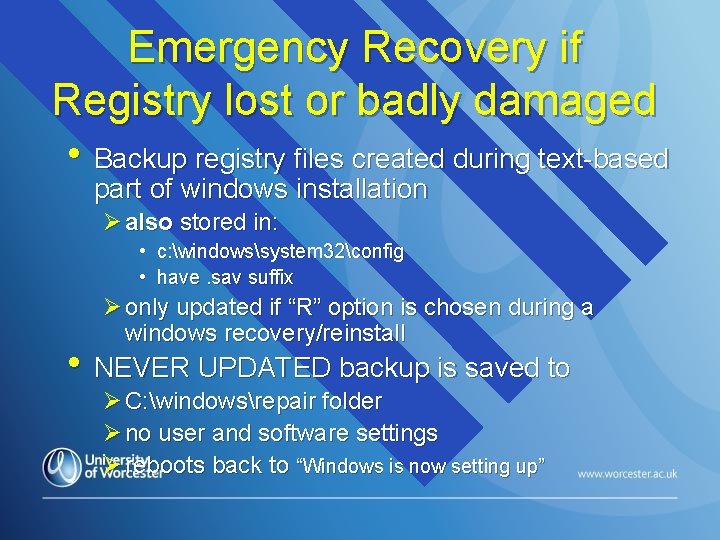
Emergency Recovery if Registry lost or badly damaged • Backup registry files created during text-based part of windows installation Ø also stored in: • c: windowssystem 32config • have. sav suffix Ø only updated if “R” option is chosen during a windows recovery/reinstall • NEVER UPDATED backup is saved to Ø C: windowsrepair folder Ø no user and software settings Ø reboots back to “Windows is now setting up”
Backing up the Registry • Much forgotten… an oversight that may later be much regretted!!! Ø can copy to tape, USB stick CD/DVD, or disk Ø rarely more than 100 Mb • Two options; Ø Use third-party backup tool • e. g http: //www. acronis. co. uk Ø Use windows “backup” • not recommended by experts! • but already there & does work! • to copy the registry if this tool is chosen, a “system state” backup option should be selected
- Slides: 43