COMP 3357 Managing Cyber Risk Richard Henson University
COMP 3357 Managing Cyber Risk Richard Henson University of Worcester January 2017
By the end of this module you should be able to: n Identify strategic, financial and operational benefits and issues of Cyber Risk Management n Review current and future trends of the technical and nontechnical risks and aspects of Information Risk Management and security, including laws, regulations, and human factors n Analyse how firms can mitigate cyber risk and differentiate from competition to increase market share n Devise a risk assessment plan for an organisation, and use this to create a business continuity/disaster recovery plan
Week 1 – Management of Information & Cyber Risk n Objectives: Ø Explain risk – qualitatively, in basic (human survival) terms Ø Explain risk to organisations – re. survival… Ø Explain the areas of organisational risk historically (pre digital processing) Ø Explain why security of information was often left off the organisation risk list, and consequences in the digital age…
Risk and Survival n Human race survived millions of years Ø“survival of the fittest” Øwhat does that mean? n Threats… to survival! Øpredators Ølack of food & drink Ølack of shelter
Human Response to Threat? n Genetically based on… Øtrigger of chemicals (e. g. adrenalin) Ø“Fight or Flight” n Also based on organised behaviour: Øfind food & water sources Øbuild a home
Appropriateness of Adrenalin st in 21 century UK? n Survival much less about flight and fight, food and shelter Ø unless living on the street… Ø BUT human imagination (e. g. clever adverts) can make it seem that way! n In practice… survival about keeping off the streets… Ø parents with enough money/assets Ø a reasonably well paid job
Organisational Risk Lose customers n Lose suppliers n Faulty equipment n Unreliable/departing employees n n What about its data?
Valuing a Business n Based on… Øequipment? » how assessed, , , ØProfit? » how assessed… ØPeople? » how assessed… ØSystems? » how assessed…
Analysing Organisational Risk n Not all are businesses… Ønot always about profit n Many Nf. P (Not-for-Profit) Øcharities » based on fund-raising? » threats to “giving” ØPublic sector » based on service e. g. swimming, education n threats to providing a safe swimming pool or school offering good education & pupil safety
That’s another fine mess… (!) n Until recently, value of a business based on Øassets Øno/quality of customers/partners ØProfit (and projections…) n Assets? Øvalue = the market value of physical assets Ødata not a physical asset… ignored!
Loss of Data? No value, no risk? n As data not perceived as of value… Ønot even on the asset register (!) n Business always dependent on data… Øsomehow overlooked as an asset n Digital data treated the same way (!!!)
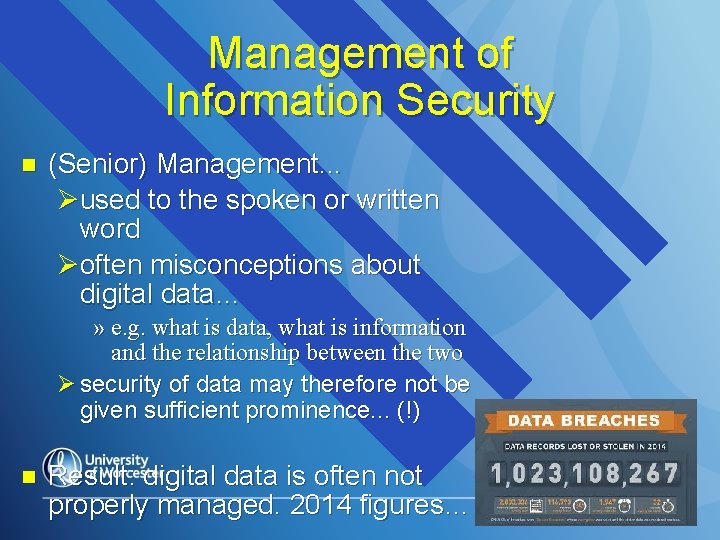
Management of Information Security n (Senior) Management. . . Øused to the spoken or written word Øoften misconceptions about digital data… » e. g. what is data, what is information and the relationship between the two Ø security of data may therefore not be given sufficient prominence. . . (!) n Result: digital data is often not properly managed. 2014 figures…
The Threats to organisations… n Divides neatly into: Ø“internal”… employees Ø“external”… hackers
Types of Business Data (1) n Administration Ø internal use Ø information to government bodies n Customer & Supplier information Ø customer information PERSONAL Ø some customer information SENSITIVE Ø both protected through Data Protection Act
Types of Business Data (2) n Transaction Information Ø regarded as financial data Ø protected by the Financial Service Authority n Management decision-making information Ø internal use only n System Data Ø internal use only
Reasons to look after Data: 1. The Law n All UK organisations that hold data on people must register with the Information Commissioner's Office (ICO) Ø criminal offence not to do so. . . n Personal and sensitive data must be kept in accordance with eight principles of the Data Protection Act (1984, updated 1998) Ø not to do so can result in hefty fines Ø or even imprisonment
Reasons to look after Data: 1. The Law - continued n Financial data also covered under the law, through the Financial Services Authority (FSA)… rebadged to become. FCA in 2013 Ø much more severe penalties than the ICO… » e. g. Nationwide fined in 2007 n approx £ 1 million » e. g. HSBC fined in 2009 n £ several MILLION » e. g. Zurich Insurance fined 2010 n £ >1 million
2. Data losses do not look good for the business! § Depending on which data a business loses… Øit may not be able to trade efficiently, or even at all! ØWorst case scenario: 10 days maximum to recover, or out of business! n If business data is stolen, they may ALSO lose trade secrets, customer image, supplier information, market share…
1. The Law - continued n 2003: EU Privacy & Electronic Communications Regulation (PECR) ØMisuse of customer information for marketing purposes n 1990: Computer Misuse Act Øunauthorised access to “computer material” is a criminal offence! Ømost convictions under DPA civil
Data Losses & not-for-profit organisations n Personal data may not be regarded as so important, other than in legal terms Ø hence the catastrophic sequence of errors that led to 25 million records being lost by HMRC n HOWEVER… customers do expect their personal data to be safeguarded Ø increasing concern about privacy in recent years Ø source of great embarrassment if data lost
Internal Data Losses n Well-meaning employees not following procedures and misusing data or allowing it to get into the wrong hands…. n Employees or temps with bad intent…
External (hacking…) » Inside people or business partners accessing data from outside, and either accidentally or on purpose, misusing it » People hacking in from outside, usually via the Internet
Do “we” have a problem? n Perceptions “from the inside” quite different from “outside looking in”
Fixing Data Security… n Where to start? ØIdentify risks, threats vulnerabilities… ØPut together a top-level information security policy
Risk, Threat, Vulnerability…? n Group Exercise… Øwhat are the risks (to data)? Øwhat are vulnerabilities (of system)? Øwhat are threats (internal/external influences)?
Start at the top…an Information Security Policy n Information is so important to organisations, security of information should be central to organisation’s strategic plan… Øtherefore part of organisational policy… n Problem: organisations (especially small ones) are very reluctant to do this…
How can organisations be encouraged to have a policy? n Over to you again…
An Information Security Policy n Fortunately, now becoming a commercial imperative for do any on-line business with a credit card Ø thanks to recent PCI DSS guidelines… Ø other information assurance schemes require this ISO 27001, COBIT, IASME) Ø more rigorously enforced by ICO n (e. g. ONCE the organisation has finally accepted that they need a policy, they should base it on existing organisational strategy Ø can then implemented tactically and operationally through the organisational structure
Stakeholders n A number of jobs involve security of data in one way or another e. g. : Ø Data Controller (Data Protection Act) Ø Head of Personnel/HR Ø Department Heads (especially Finance) n Who should bear the responsibility/carry the can? ? Ø ISO 27001 requirement… Ø http: //www. iso. org/iso/home/standards/certification/home/standards/certifica tion/iso-survey. htm
Who are “stakeholders” in organisational Information Security? n Who should be responsible for what? Ø (no responsibility… no accountability) n Exercise again in groups…

Differences between Public & Private Sectors? n Is there a difference regarding data? Ø if strategic business data is lost, with no back up » cannot do new business » cannot fulfil existing business » the business will fold Ø If public organisation data similarly lost » service level drops or becomes zero » people get angry, write to media » public sector body gets lots of bad publicity » system gets patched up and limps on » enquiry suggests deficiencies & changes to be made…
Economics of Information Security n Academic research area Ø seeks to produce economic models for organisations to attribute value to data n Back to basics of Information Security: Ø Confidentiality – relationship between confidentiality & intrinsic value? Ø Integrity – very difficult to quantify Ø Availability – if loss of particular data: » » » causes system failure puts the business temporarily out of business must have intrinsic value
Value of Business Data n More success to date with organisational data that affects business availability than with personal data. . . Ø can put a monetary value on loss to the organisation of e. g. » a day’s lost production » a 10% fall in share price Ø If 10000 customer details are leaked, who cares? ? ? » Members of the public? » The Information Commissioner… » would this affect: n n the business’s availability in the market place the business’s share price?

Moving forward… n Or catching up (!) n EU legislation comes into effect 2018. Ørequires organisations to take a risk-based approach to privacy Øa
Further Research n Business-oriented recent white papers: Ø http: //www. findwhitepapers. com/security n What SHOULD have happened as the 1998 DPA was implemented…: Ø http: //management. silicon. com/government/0, 3902 4677, 11015799, 00. htm n Information Commissioner’s current website – huge collection of documents: Ø http: //www. ico. gov. uk
- Slides: 35