Collaborative Portal Security CSE 5810 Prof Steven A
Collaborative Portal Security CSE 5810 Prof. Steven A. Demurjian, Sr. Computer Science & Engineering Department The University of Connecticut 371 Fairfield Road, Box U-1155 Storrs, CT 06269 -1155 steve@engr. uconn. edu http: //www. engr. uconn. edu/~steve (860) 486 - 4818 Portal. Security-1
Security for Collaborative Web Portals m CSE 5810 m Collaborative Portals Rapidly Emerging as Means for Communication, Interaction, and Problem Solving over Distances q Source. Forge Media. Wiki q Microsoft Sharepoint q php. BB Security Model and Enforcement Often Lacking q Consider WIKIs Ø Anonymous Users (Read Only) Ø Registered Users (Full Write Access) Ø Result: No Guarantee of Data Correctness m Need to Transcend Simplistic Approach for Application Level, Document Level (Author/View), and Look-and-Feel of Portal Itself Portal. Security-2
What is a WIKI? CSE 5810 m m m m Repository for Information that Accessible to All Collaborative Platform Content Contribution/Creation/Modification Document Authoring Historical Tracking of Actions Shared Platform to Facilitate Information Exchange, Joint Efforts, etc. Runs in Web Environment (Browser) – No Software to Install Limited Security: User Accounts/Passwords Portal. Security-3
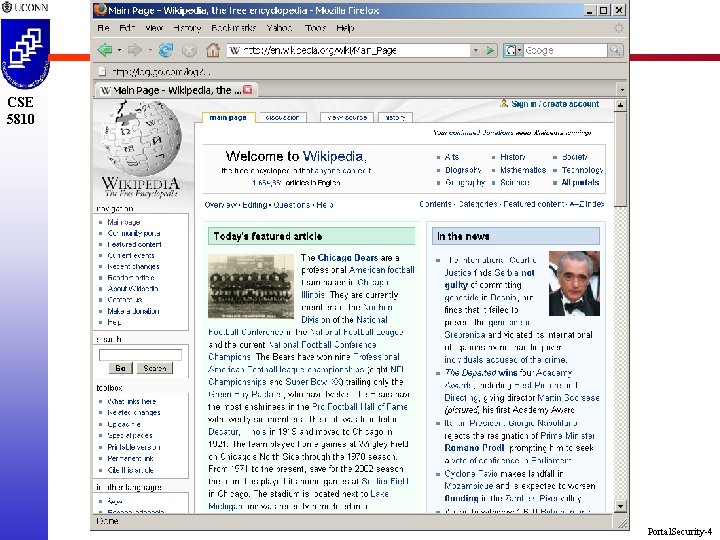
CSE 5810 Portal. Security-4
CSE 5810 Portal. Security-5
CSE 5810 Portal. Security-6
CSE 5810 Portal. Security-7
Media. Wiki underlies Wiki. Pedia CSE 5810 http: //www. mediawiki. org/wiki/Media. Wiki Portal. Security-8
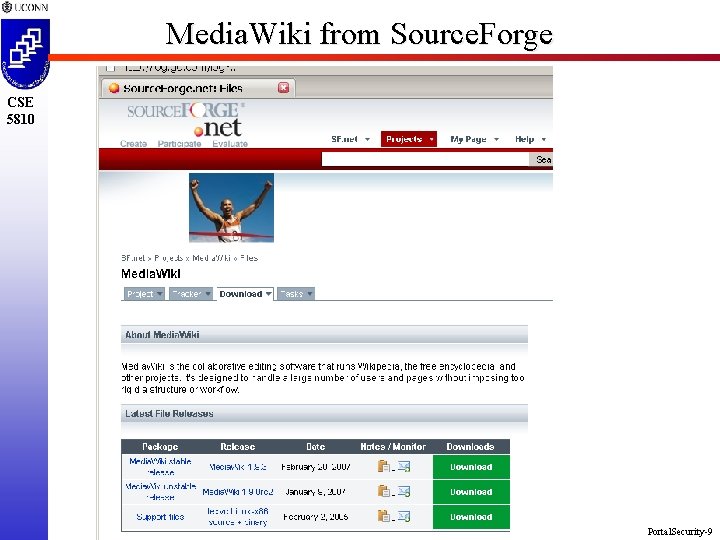
Media. Wiki from Source. Forge CSE 5810 Portal. Security-9
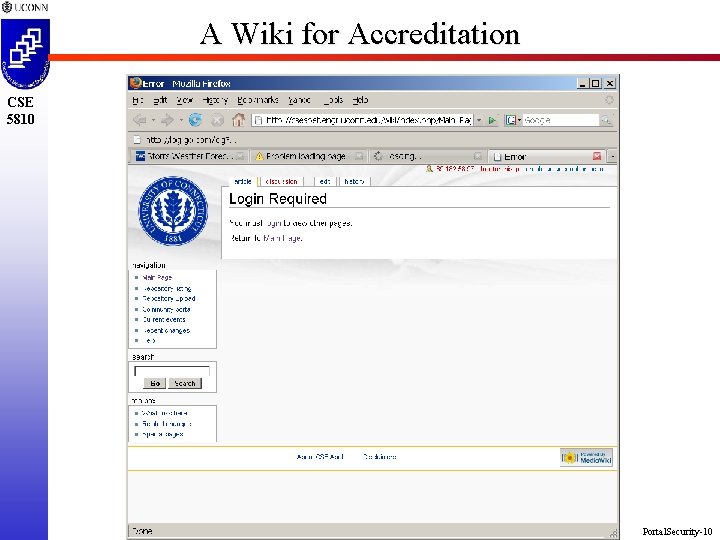
A Wiki for Accreditation CSE 5810 Portal. Security-10
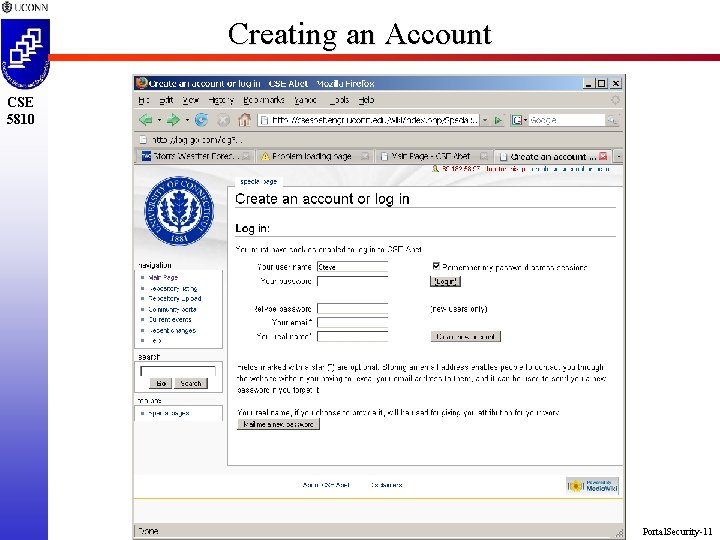
Creating an Account CSE 5810 Portal. Security-11
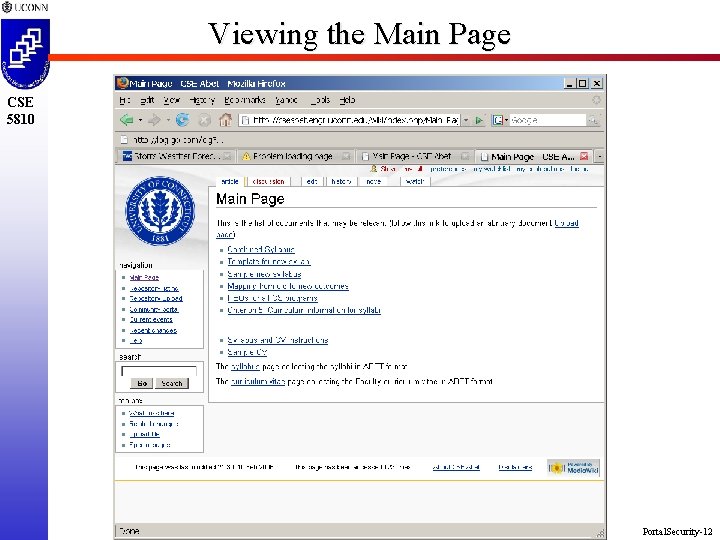
Viewing the Main Page CSE 5810 Portal. Security-12
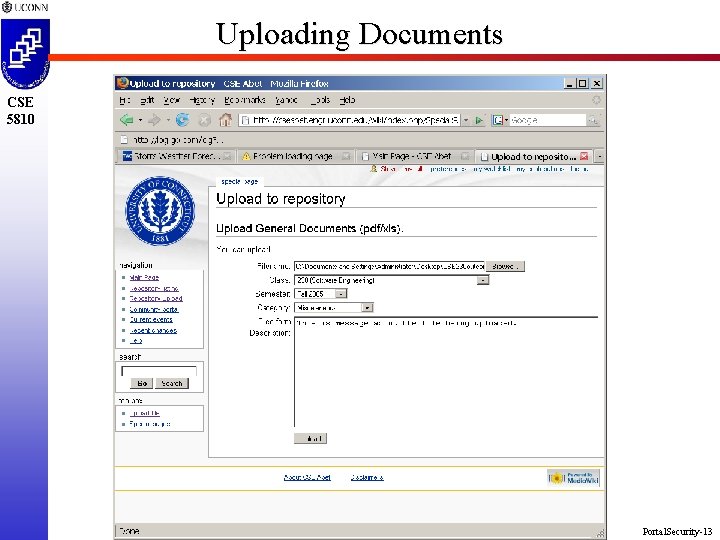
Uploading Documents CSE 5810 Portal. Security-13
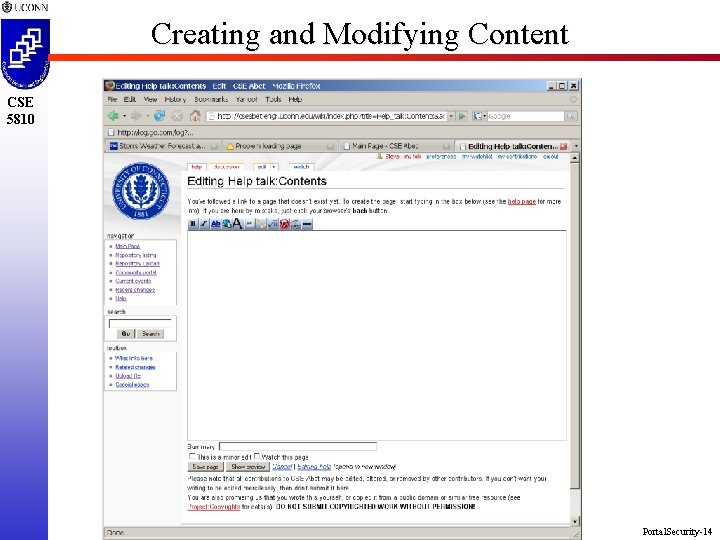
Creating and Modifying Content CSE 5810 Portal. Security-14
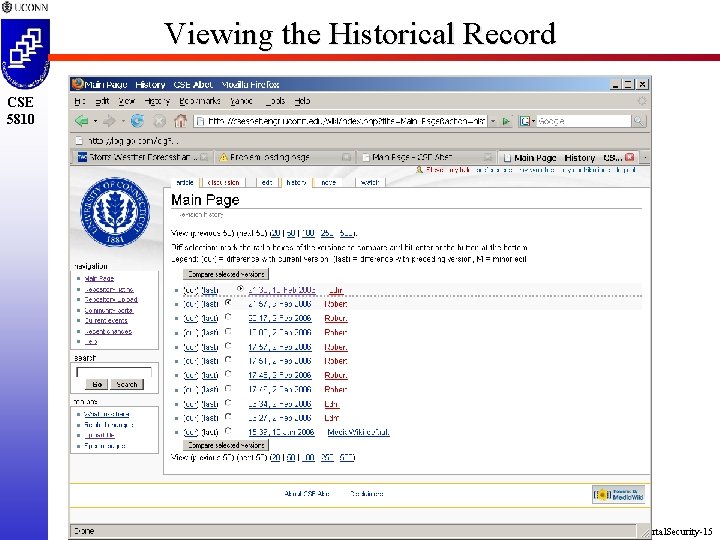
Viewing the Historical Record CSE 5810 Portal. Security-15
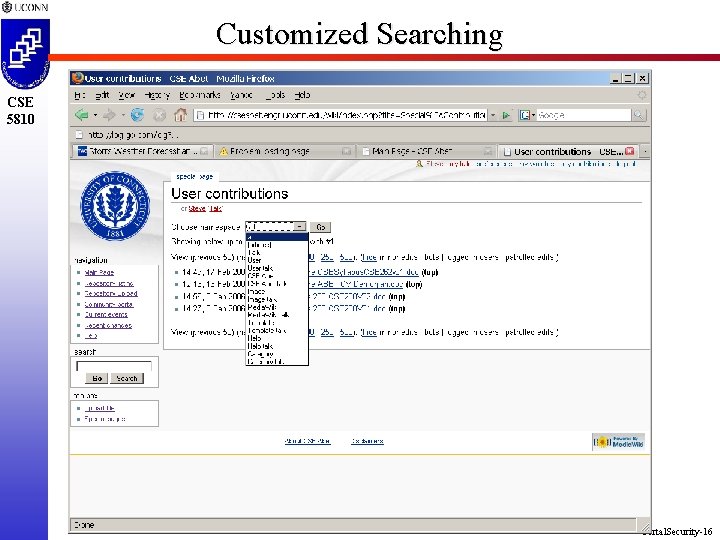
Customized Searching CSE 5810 Portal. Security-16
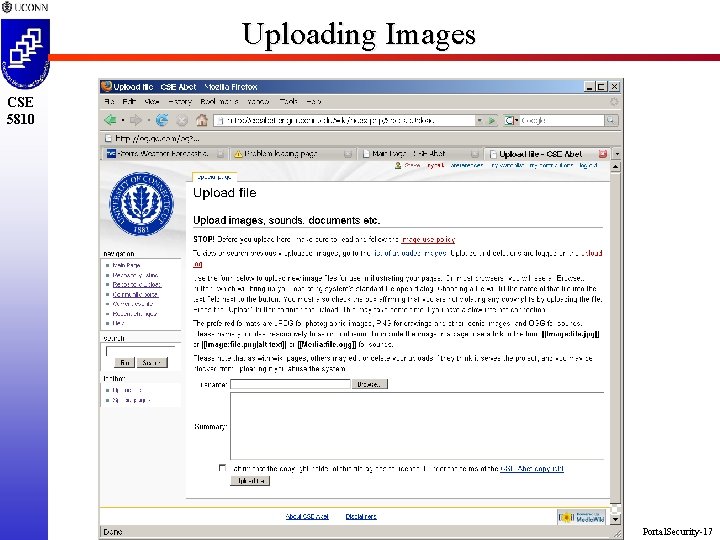
Uploading Images CSE 5810 Portal. Security-17
Problems with Media. Wiki and Others m CSE 5810 m m m Not Very User Friendly, Particularly for Non. Computer Savvy Population Difficult to Customize with Specialized Features and Capabilities beyond Basic Look and Feel Changes Security Limited to User/Password Combinations q Everyone can do Anything q Set up as Shared and Collaborative for All q No Control on Incorrect Content Being Uploaded Addition of Security Violates General WIKI Concept of Open and Available to All Portal. Security-18
Current R&D on WIKIs m CSE 5810 m Led by Serebrum (www. serebrum. com) Developing AXON WIKI with Capabilities that include: q Content Creating Editing (WYSISYG) q Document Publishing (Web, PDF, RTF) q Document Distribution (Email, Print, Fax) q Mobile Access (Limited with Black. Berry) q Security Ø Role-Based Access Control to Define Privileges Ø For Example, Physician, Provider, Patient, Clinical Researcher, etc. q Full Collaborative Environment Portal. Security-19
Usage of Axon in Safety. Net m CSE 5810 m m m Used by Project Team (PIs, Co-PIs, Providers, etc. ) Repository for Planning Effort Upload, Create, Review, Modify Documents Allows Safety. Net Team to Familiarize Themselves with WIKI Technology/Web Portals No Software to Install Problems with Off-the-Shelf Product (Media. Wiki) q Customization Time Consuming (and Limited) q Security Minimal – but Acceptable for this Use (Can’t store any Patient Related Information) q Limited User Friendliness May Result in Poor Opinion of Web Technology Portal. Security-20
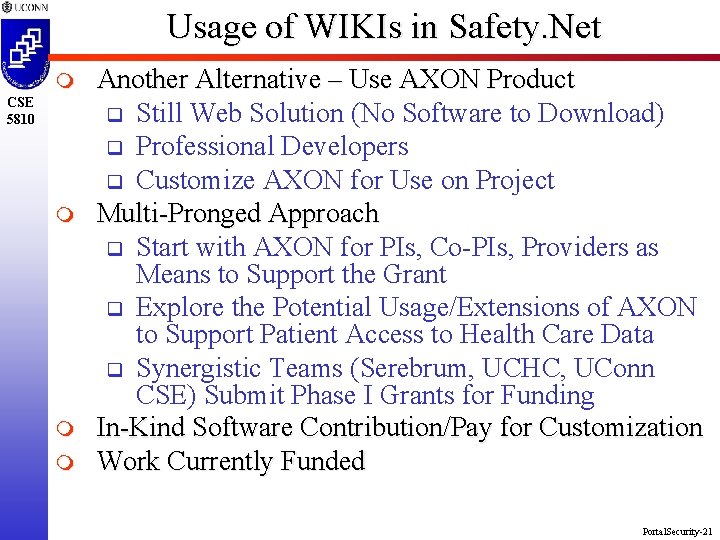
Usage of WIKIs in Safety. Net m CSE 5810 m m m Another Alternative – Use AXON Product q Still Web Solution (No Software to Download) q Professional Developers q Customize AXON for Use on Project Multi-Pronged Approach q Start with AXON for PIs, Co-PIs, Providers as Means to Support the Grant q Explore the Potential Usage/Extensions of AXON to Support Patient Access to Health Care Data q Synergistic Teams (Serebrum, UCHC, UConn CSE) Submit Phase I Grants for Funding In-Kind Software Contribution/Pay for Customization Work Currently Funded Portal. Security-21
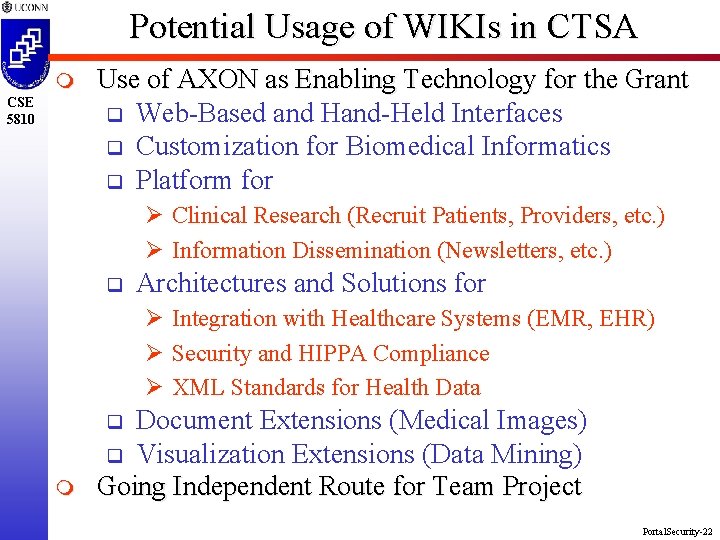
Potential Usage of WIKIs in CTSA m CSE 5810 Use of AXON as Enabling Technology for the Grant q Web-Based and Hand-Held Interfaces q Customization for Biomedical Informatics q Platform for Ø Clinical Research (Recruit Patients, Providers, etc. ) Ø Information Dissemination (Newsletters, etc. ) q Architectures and Solutions for Ø Integration with Healthcare Systems (EMR, EHR) Ø Security and HIPPA Compliance Ø XML Standards for Health Data Document Extensions (Medical Images) q Visualization Extensions (Data Mining) Going Independent Route for Team Project q m Portal. Security-22
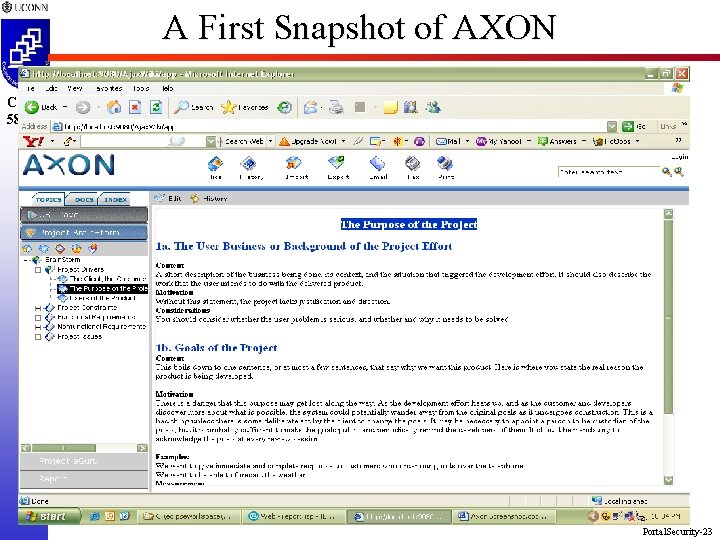
A First Snapshot of AXON CSE 5810 Portal. Security-23
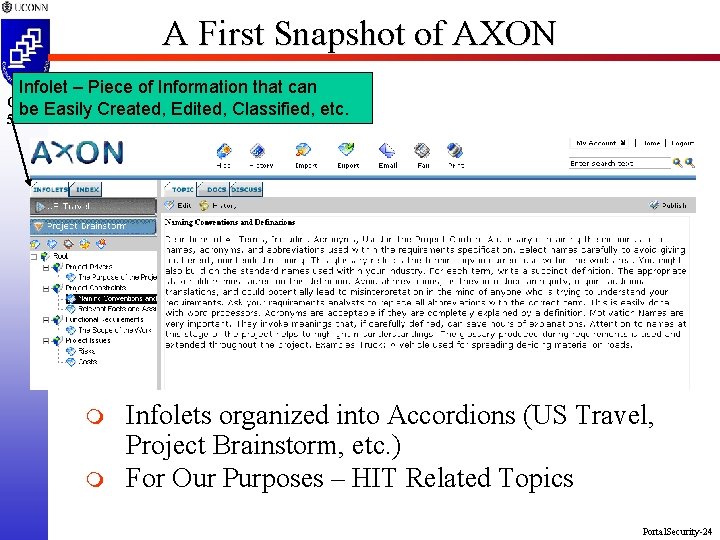
A First Snapshot of AXON Infolet – Piece of Information that can Easily Created, Edited, Classified, etc. CSE be 5810 m m Infolets organized into Accordions (US Travel, Project Brainstorm, etc. ) For Our Purposes – HIT Related Topics Portal. Security-24
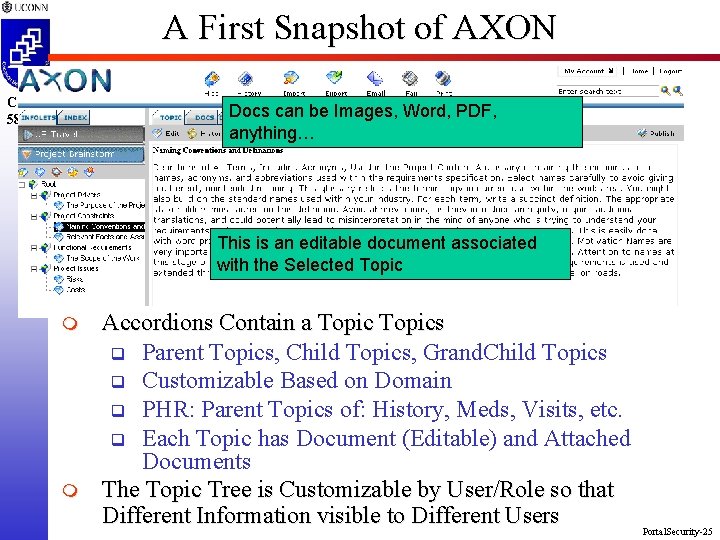
A First Snapshot of AXON CSE 5810 Docs can be Images, Word, PDF, anything… This is an editable document associated with the Selected Topic m m Accordions Contain a Topics q Parent Topics, Child Topics, Grand. Child Topics q Customizable Based on Domain q PHR: Parent Topics of: History, Meds, Visits, etc. q Each Topic has Document (Editable) and Attached Documents The Topic Tree is Customizable by User/Role so that Different Information visible to Different Users Portal. Security-25
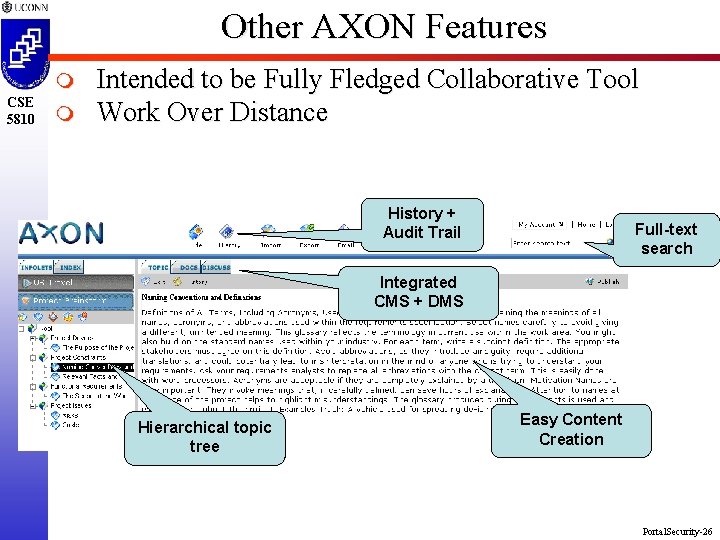
Other AXON Features m CSE 5810 m Intended to be Fully Fledged Collaborative Tool Work Over Distance History + Audit Trail Full-text search Integrated CMS + DMS Hierarchical topic tree Easy Content Creation Portal. Security-26
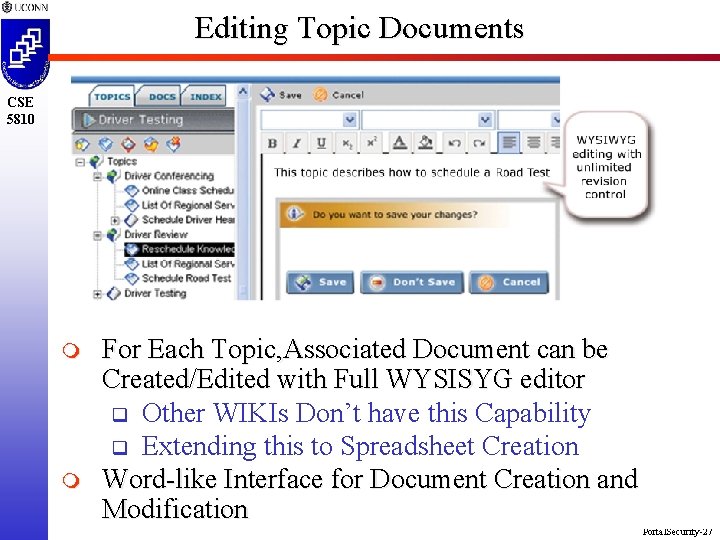
Editing Topic Documents CSE 5810 m m For Each Topic, Associated Document can be Created/Edited with Full WYSISYG editor q Other WIKIs Don’t have this Capability q Extending this to Spreadsheet Creation Word-like Interface for Document Creation and Modification Portal. Security-27
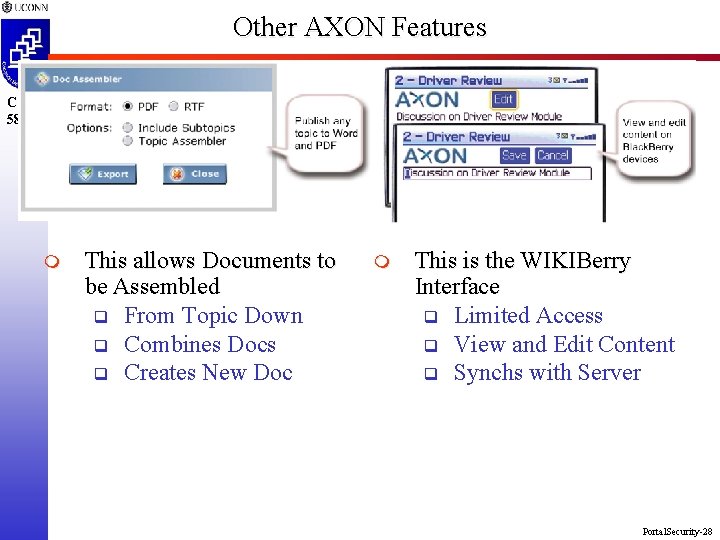
Other AXON Features CSE 5810 m This allows Documents to be Assembled q From Topic Down q Combines Docs q Creates New Doc m This is the WIKIBerry Interface q Limited Access q View and Edit Content q Synchs with Server Portal. Security-28
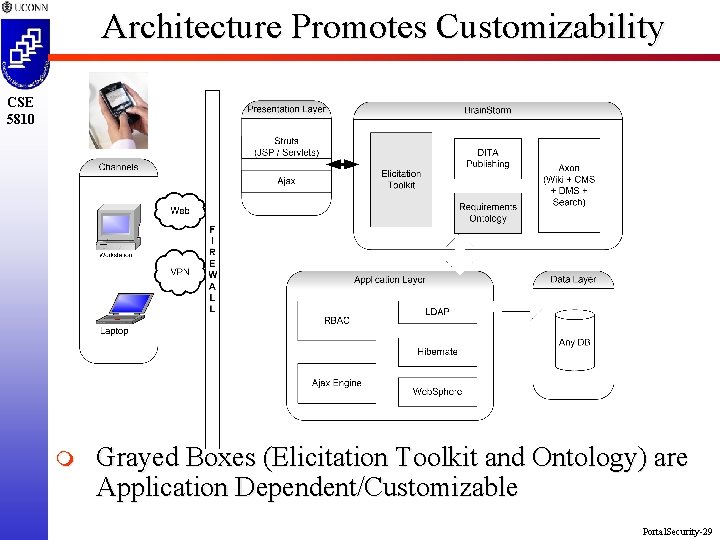
Architecture Promotes Customizability CSE 5810 m Grayed Boxes (Elicitation Toolkit and Ontology) are Application Dependent/Customizable Portal. Security-29
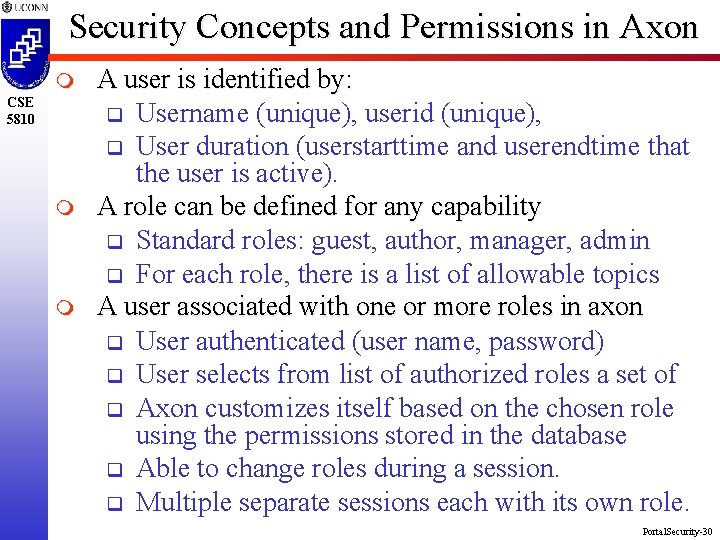
Security Concepts and Permissions in Axon m CSE 5810 m m A user is identified by: q Username (unique), userid (unique), q User duration (userstarttime and userendtime that the user is active). A role can be defined for any capability q Standard roles: guest, author, manager, admin q For each role, there is a list of allowable topics A user associated with one or more roles in axon q User authenticated (user name, password) q User selects from list of authorized roles a set of q Axon customizes itself based on the chosen role using the permissions stored in the database q Able to change roles during a session. q Multiple separate sessions each with its own role. Portal. Security-30
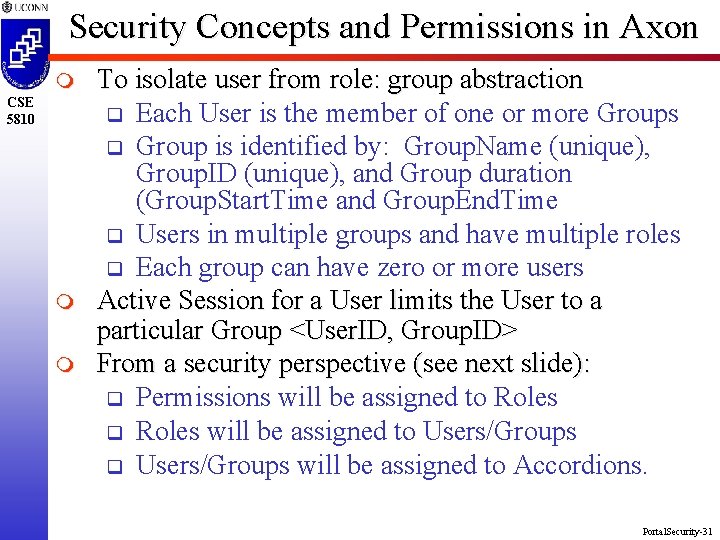
Security Concepts and Permissions in Axon m CSE 5810 m m To isolate user from role: group abstraction q Each User is the member of one or more Groups q Group is identified by: Group. Name (unique), Group. ID (unique), and Group duration (Group. Start. Time and Group. End. Time q Users in multiple groups and have multiple roles q Each group can have zero or more users Active Session for a User limits the User to a particular Group <User. ID, Group. ID> From a security perspective (see next slide): q Permissions will be assigned to Roles q Roles will be assigned to Users/Groups q Users/Groups will be assigned to Accordions. Portal. Security-31
CSE 5810 Portal. Security-32

Current AXON Main Scren CSE 5810 Portal. Security-33
Other Important Concepts m CSE 5810 m m A Project contains multiple Accordions q E. g. US Travel, Brainstorm, EGuru, and Report q For Each Accordions, a Topic Tree, a Document List, and an Index is maintained q Each Accordion can have one or more Users, q Each Accordion can have zero or more Groups University Accordions: Just like Peoplesoft q Faculty, Student, Grad Program Director q Faculty Accordion (corresponding to the Faculty Role) would have Record Grade, Permission Numbers, Advisee List, and other Child Topics PHR Accordions: q Patient History, Education Materials, Appointments, etc. Portal. Security-34
Other Important Concepts m CSE 5810 The Topic Tree contains three levels of parent, child, and grandchild topics: q Each topic in this tree is associated with exactly one xhtml page. q Each topic in this tree is associated with zero or more documents of all types (Word, PPT, PDF, GIF, etc. ). q The DOCS tab contains a list of documents. specifically, for the selected topic - all documents for the topic and its descendants are shown. Portal. Security-35
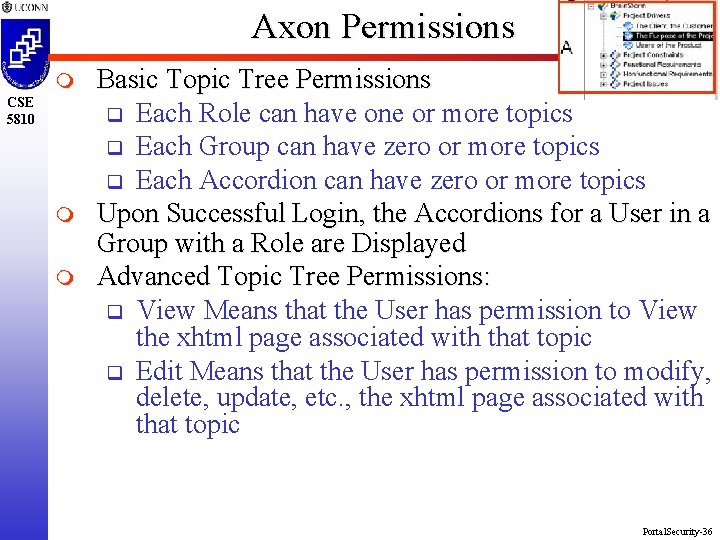
Axon Permissions m CSE 5810 m m Basic Topic Tree Permissions q Each Role can have one or more topics q Each Group can have zero or more topics q Each Accordion can have zero or more topics Upon Successful Login, the Accordions for a User in a Group with a Role are Displayed Advanced Topic Tree Permissions: q View Means that the User has permission to View the xhtml page associated with that topic q Edit Means that the User has permission to modify, delete, update, etc. , the xhtml page associated with that topic Portal. Security-36
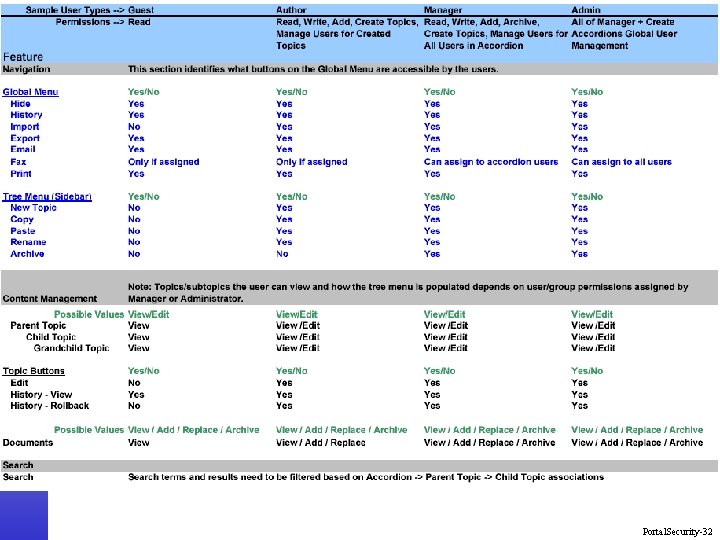
Axon Permissions m CSE 5810 Edit/History Permissions q Edit having a value of Yes means the Edit button is enabled Ø If the Topic Tree has a Permission of Edit for a Topic, then the permission for the Topic Button Edit should be set to Yes. History View and History Rollback are assigned on a Yes/No basis to each Role. Button Permissions: q Buttons: Global Menu for Hide, History, Import, Export, Email, Fax, and Print. q Permissions are Yes/No on a role-by-role basis. No means that the associated ICON doesn’t appear q m Portal. Security-37
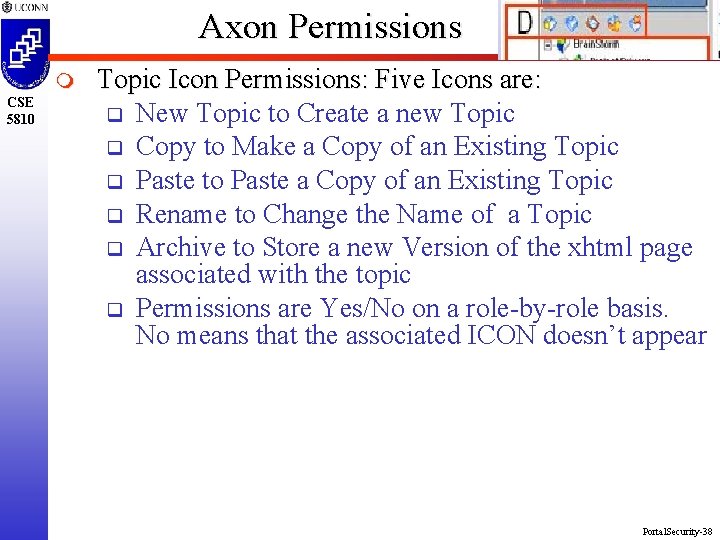
Axon Permissions m CSE 5810 Topic Icon Permissions: Five Icons are: q New Topic to Create a new Topic q Copy to Make a Copy of an Existing Topic q Paste to Paste a Copy of an Existing Topic q Rename to Change the Name of a Topic q Archive to Store a new Version of the xhtml page associated with the topic q Permissions are Yes/No on a role-by-role basis. No means that the associated ICON doesn’t appear Portal. Security-38
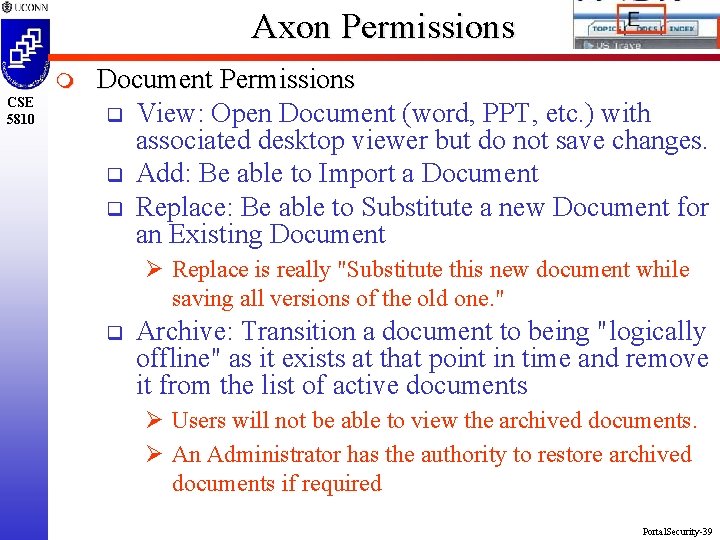
Axon Permissions m CSE 5810 Document Permissions q View: Open Document (word, PPT, etc. ) with associated desktop viewer but do not save changes. q Add: Be able to Import a Document q Replace: Be able to Substitute a new Document for an Existing Document Ø Replace is really "Substitute this new document while saving all versions of the old one. " q Archive: Transition a document to being "logically offline" as it exists at that point in time and remove it from the list of active documents Ø Users will not be able to view the archived documents. Ø An Administrator has the authority to restore archived documents if required Portal. Security-39
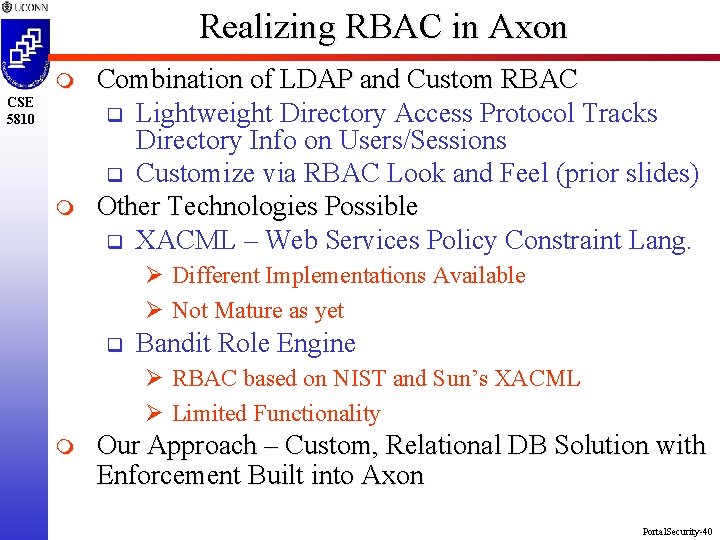
Realizing RBAC in Axon m CSE 5810 m Combination of LDAP and Custom RBAC q Lightweight Directory Access Protocol Tracks Directory Info on Users/Sessions q Customize via RBAC Look and Feel (prior slides) Other Technologies Possible q XACML – Web Services Policy Constraint Lang. Ø Different Implementations Available Ø Not Mature as yet q Bandit Role Engine Ø RBAC based on NIST and Sun’s XACML Ø Limited Functionality m Our Approach – Custom, Relational DB Solution with Enforcement Built into Axon Portal. Security-40
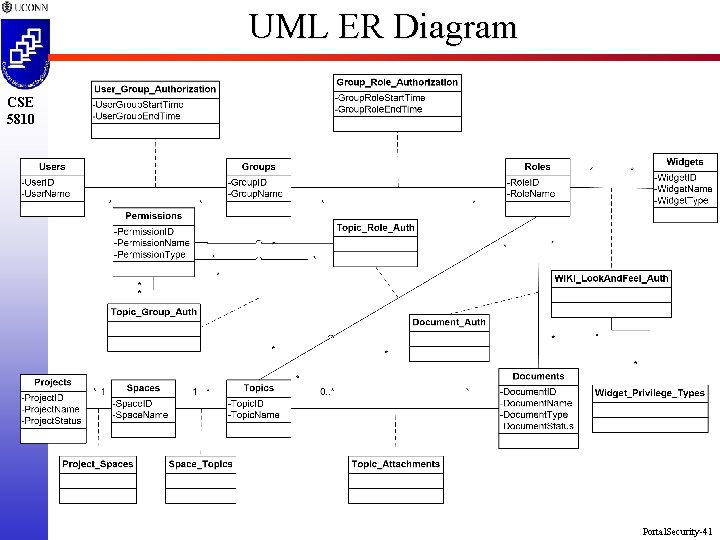
UML ER Diagram CSE 5810 Portal. Security-41
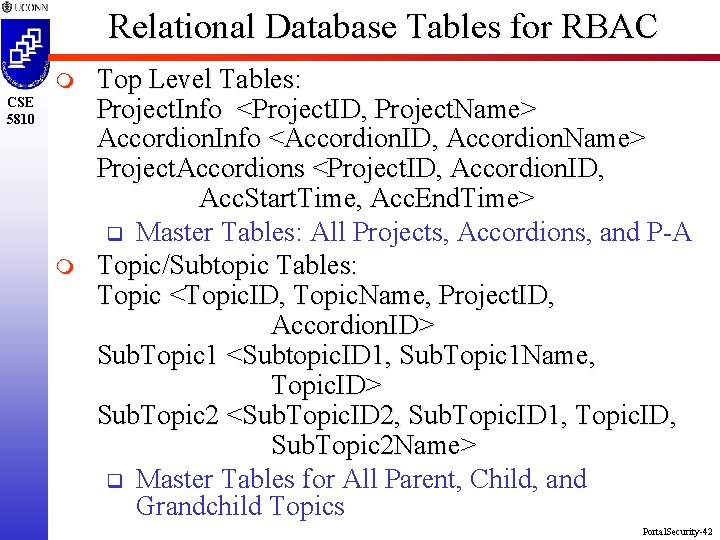
Relational Database Tables for RBAC m CSE 5810 m Top Level Tables: Project. Info <Project. ID, Project. Name> Accordion. Info <Accordion. ID, Accordion. Name> Project. Accordions <Project. ID, Accordion. ID, Acc. Start. Time, Acc. End. Time> q Master Tables: All Projects, Accordions, and P-A Topic/Subtopic Tables: Topic <Topic. ID, Topic. Name, Project. ID, Accordion. ID> Sub. Topic 1 <Subtopic. ID 1, Sub. Topic 1 Name, Topic. ID> Sub. Topic 2 <Sub. Topic. ID 2, Sub. Topic. ID 1, Topic. ID, Sub. Topic 2 Name> q Master Tables for All Parent, Child, and Grandchild Topics Portal. Security-42
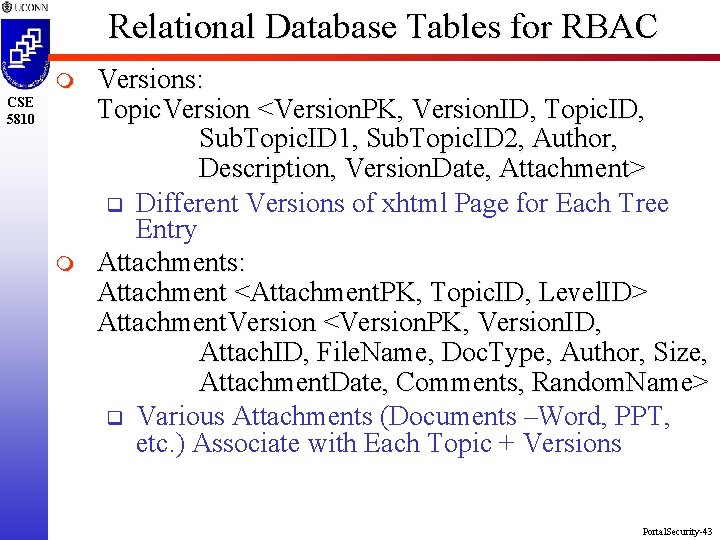
Relational Database Tables for RBAC m CSE 5810 m Versions: Topic. Version <Version. PK, Version. ID, Topic. ID, Sub. Topic. ID 1, Sub. Topic. ID 2, Author, Description, Version. Date, Attachment> q Different Versions of xhtml Page for Each Tree Entry Attachments: Attachment <Attachment. PK, Topic. ID, Level. ID> Attachment. Version <Version. PK, Version. ID, Attach. ID, File. Name, Doc. Type, Author, Size, Attachment. Date, Comments, Random. Name> q Various Attachments (Documents –Word, PPT, etc. ) Associate with Each Topic + Versions Portal. Security-43
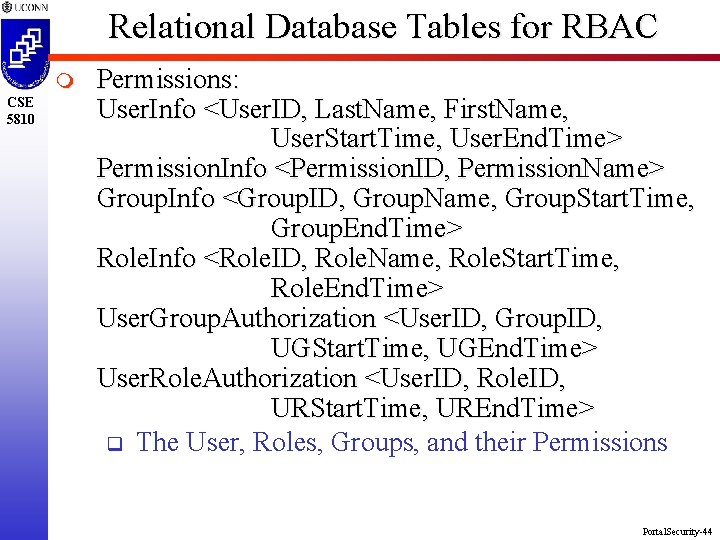
Relational Database Tables for RBAC m CSE 5810 Permissions: User. Info <User. ID, Last. Name, First. Name, User. Start. Time, User. End. Time> Permission. Info <Permission. ID, Permission. Name> Group. Info <Group. ID, Group. Name, Group. Start. Time, Group. End. Time> Role. Info <Role. ID, Role. Name, Role. Start. Time, Role. End. Time> User. Group. Authorization <User. ID, Group. ID, UGStart. Time, UGEnd. Time> User. Role. Authorization <User. ID, Role. ID, URStart. Time, UREnd. Time> q The User, Roles, Groups, and their Permissions Portal. Security-44
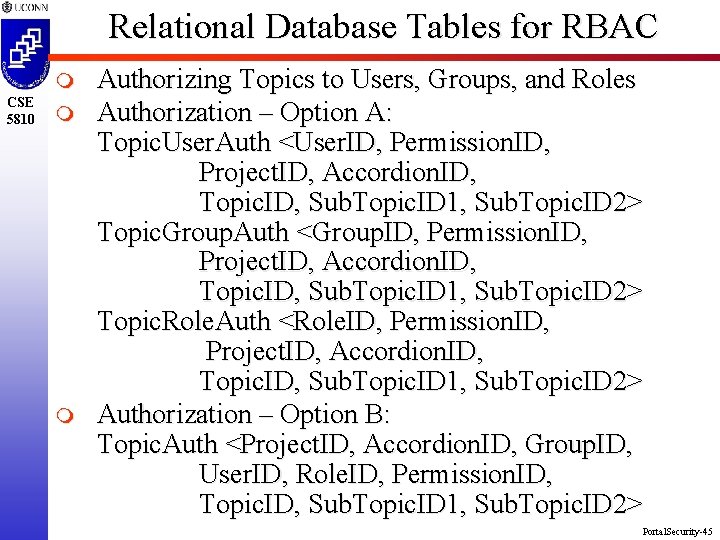
Relational Database Tables for RBAC m CSE 5810 m m Authorizing Topics to Users, Groups, and Roles Authorization – Option A: Topic. User. Auth <User. ID, Permission. ID, Project. ID, Accordion. ID, Topic. ID, Sub. Topic. ID 1, Sub. Topic. ID 2> Topic. Group. Auth <Group. ID, Permission. ID, Project. ID, Accordion. ID, Topic. ID, Sub. Topic. ID 1, Sub. Topic. ID 2> Topic. Role. Auth <Role. ID, Permission. ID, Project. ID, Accordion. ID, Topic. ID, Sub. Topic. ID 1, Sub. Topic. ID 2> Authorization – Option B: Topic. Auth <Project. ID, Accordion. ID, Group. ID, User. ID, Role. ID, Permission. ID, Topic. ID, Sub. Topic. ID 1, Sub. Topic. ID 2> Portal. Security-45
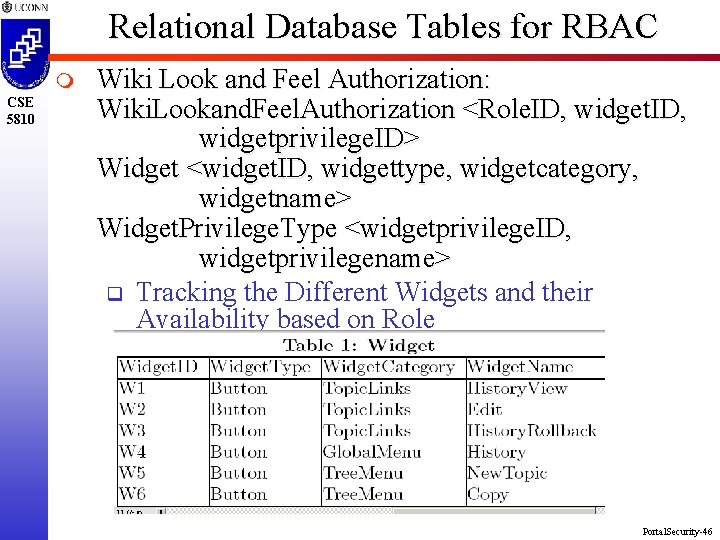
Relational Database Tables for RBAC m CSE 5810 Wiki Look and Feel Authorization: Wiki. Lookand. Feel. Authorization <Role. ID, widgetprivilege. ID> Widget <widget. ID, widgettype, widgetcategory, widgetname> Widget. Privilege. Type <widgetprivilege. ID, widgetprivilegename> q Tracking the Different Widgets and their Availability based on Role Portal. Security-46
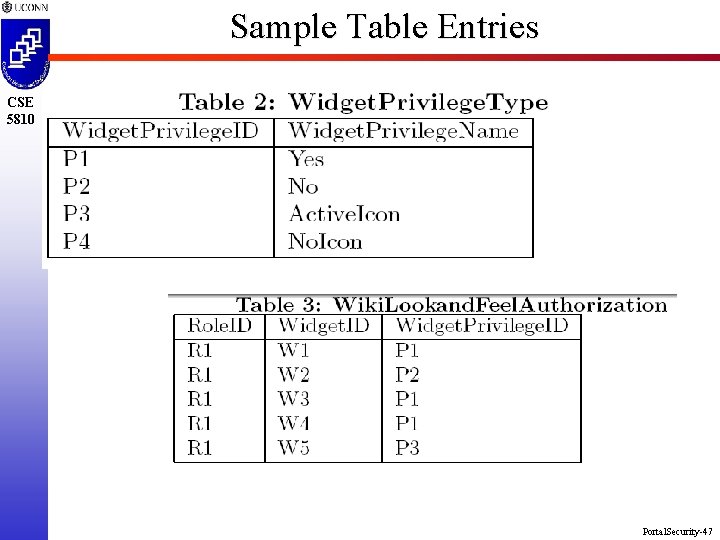
Sample Table Entries CSE 5810 Portal. Security-47
Concluding Remarks: Portal Security m CSE 5810 m m m Expand WIKI Security Beyond Coarse Grained Transition and Generalize to Web Portals Security for: q Application Level q Document Level q Portal Look-and-Feel Truly Collaborative and Secure Other Work q Extending Axon with MAC (Navy SBIR) q Dealing with Delegation, Separation of Duty, etc. Leveraging the Concepts for Team Project Portal. Security-48
- Slides: 48