A Security Based Model for Mobile Agent Software
A Security Based Model for Mobile Agent Software Systems Haiping Xu, Ph. D. Computer and Information Science Department University of Massachusetts Dartmouth http: //www. cis. umassd. edu/~hxu 04/9/200404/15/02 CIS Dept. , UMass Dartmouth
Outline Part 1: Background and Motivations Part 2: Agent-Oriented G-Net Model Part 3: Design of Intelligent Mobile Agents Part 4: Design of Facilitator Agents Part 5: A Case Study: Agent Migration Part 6: Conclusions and Future Work. 04/9/2004 CIS Dept. , UMass Dartmouth 2
Part 1: Background and Motivations The development of software systems starts with two main activities: Software requirements analysis Software design Software requirements analysis: to reduce potential errors caused by incomplete and ambiguous requirements Software design: to depict the overall structure of a system by decomposing the system into its logical components. 04/9/2004 CIS Dept. , UMass Dartmouth 3
Formal Methods in Software Engineering The purpose of software requirements analysis can be achieved in two ways: Write a specification in natural languages Choose a formal language, e. g. , Petri nets Ideally, formal methods can be applied in each phase of the software development life cycle, e. g. , the design phase However, to create a formal model in the design phase and to verify its correctness is rare. 04/9/2004 CIS Dept. , UMass Dartmouth 4
![Introduction to Petri Net “Three-in-one” capability of Petri net models [Murata 1989] Graphical representation Introduction to Petri Net “Three-in-one” capability of Petri net models [Murata 1989] Graphical representation](http://slidetodoc.com/presentation_image_h2/924c3650d4abc081da6cf6f076a98ea5/image-5.jpg)
Introduction to Petri Net “Three-in-one” capability of Petri net models [Murata 1989] Graphical representation Mathematical description Simulation tool Definition: A Petri net is a 4 -tuple, PN = (P, T, F, M 0) where P = {P 1, P 2, …, Pm} is a finite set of places; T = {t 1, t 2, …, tn} is a finite set of transitions; F (P x T) (T x P) is a set of arcs (flow relation); M 0: P --> {0, 1, 2, 3, …} is the initial marking. 04/9/2004 CIS Dept. , UMass Dartmouth 5
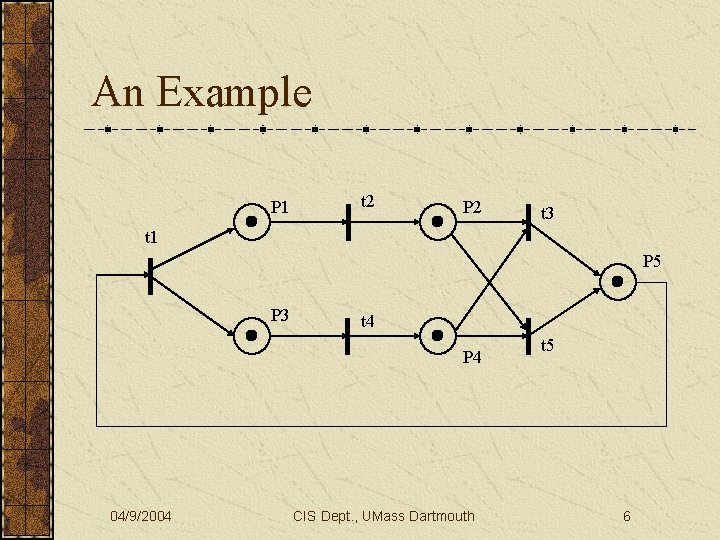
An Example P 1 t 2 P 2 t 3 t 1 P 5 P 3 t 4 P 4 04/9/2004 CIS Dept. , UMass Dartmouth t 5 6
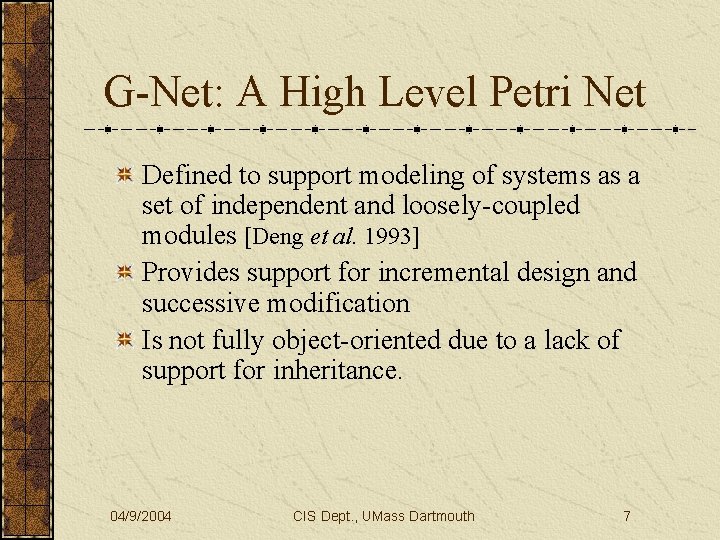
G-Net: A High Level Petri Net Defined to support modeling of systems as a set of independent and loosely-coupled modules [Deng et al. 1993] Provides support for incremental design and successive modification Is not fully object-oriented due to a lack of support for inheritance. 04/9/2004 CIS Dept. , UMass Dartmouth 7
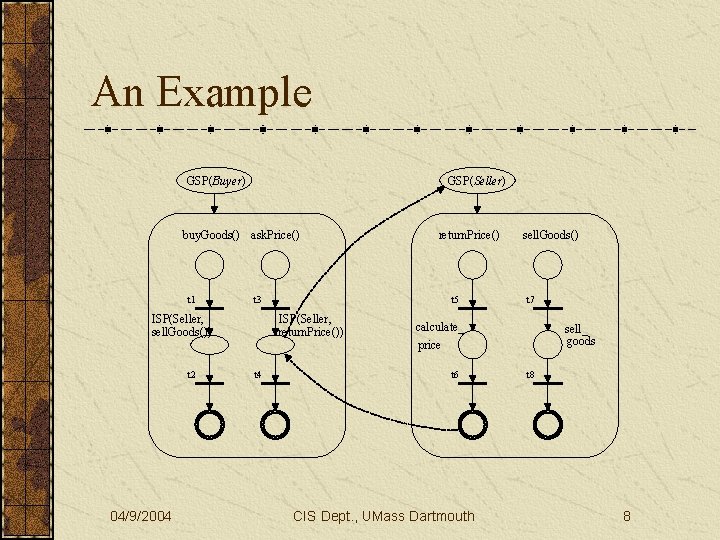
An Example GSP(Buyer) GSP(Seller) buy. Goods() ask. Price() t 1 t 3 ISP(Seller, sell. Goods()) t 2 04/9/2004 t 5 ISP(Seller, return. Price()) t 4 return. Price() sell. Goods() t 7 calculate_ price t 6 CIS Dept. , UMass Dartmouth sell_ goods t 8 8
Introduction to Agents The term “agent” comes from the Greek word “agein”, which means to drive or to lead A software agent is a program that acts on behalf of a (human) user A software agent is typically situated in some environment, and that is capable of autonomous action. 04/9/2004 CIS Dept. , UMass Dartmouth 9
Research Directions Multi-agent systems (MAS) Agents act as “active” objects (intelligence) Collaborative or competitive Generally use distributed but static (non-mobile) agents Mobile agents (MA) Model agent mobility and agent coordination Generally assume very limited or even no intelligence. 04/9/2004 CIS Dept. , UMass Dartmouth 10
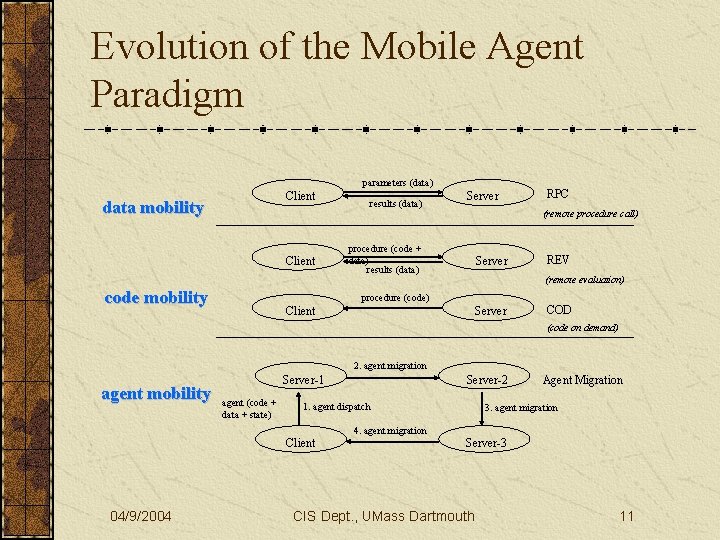
Evolution of the Mobile Agent Paradigm parameters (data) Client data mobility Client code mobility results (data) Server RPC (remote procedure call) procedure (code + data) results (data) Server REV (remote evaluation) procedure (code) Server Client COD (code on demand) 2. agent migration agent mobility Server-1 agent (code + data + state) 1. agent dispatch Client 04/9/2004 Server-2 4. agent migration Agent Migration 3. agent migration Server-3 CIS Dept. , UMass Dartmouth 11
Why Mobile Agent ? Asynchronous Tasks Asynchronous processing of requests Mobile device can be disconnected and reconnected Reduction of Communication Costs The number of interactions The amount of data communicated over the network. 04/9/2004 CIS Dept. , UMass Dartmouth 12
Academic Research Work Formal models for agent mobility Distributed join-calculus: an extension of -calculus that introduce the explicit notions of named localities and distributed failure [Fournet et al. , 1996] Mobile UNITY: a programming notation that captures the notion of mobility and transient interaction among mobile nodes [Roman et al. , 1997] Mobi. S: an extended version of Poli. S, which is a specification language based multiple tuple spaces [Mascolo, 1999] LIME: a middleware based on tuple spaces [Murphy et al. , 2001] Very few attempts to formally model agent security for mobile agents The use of encrypted functions for mobile agent security, which protects mobile agents from malicious hosts [Lee and Harrison, 2004] Mobile agent security through multi-agent cryptographic protocols [Tate and Xu, 2003]. 04/9/2004 CIS Dept. , UMass Dartmouth 13
Challenges Security issues for mobile agent systems Inter-agent security Agent-host security Inter-host security Most of the existing work concentrates on solving one of the above problems In contrast, our approach provides a uniform framework to deal with all the above security issues. 04/9/2004 CIS Dept. , UMass Dartmouth 14
Part 2: Agent-Oriented G-Net Model Software agent systems: one of the most important topics in distributed and autonomous decentralized systems Key features: autonomous, reactive, proactive and internally-motivated agents However, the G-net model is not sufficient for agent modeling because: Does not support a common communication language and common protocols among agents Does not directly support asynchronous message passing Does not support modeling agent’s mental state, such as goals, plans and knowledge. 04/9/2004 CIS Dept. , UMass Dartmouth 15
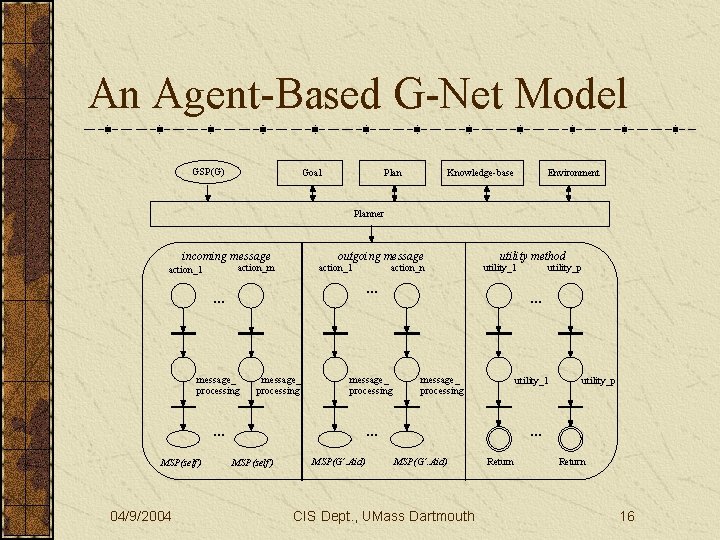
An Agent-Based G-Net Model GSP(G) Goal Plan Knowledge-base Environment Planner incoming message outgoing message action_m action_1 message_ processing … 04/9/2004 utility method utility_1 … … MSP(self) action_n … message_ processing utility_1 … MSP(self) MSP(G’. Aid) utility_p … MSP(G’. Aid) CIS Dept. , UMass Dartmouth Return 16
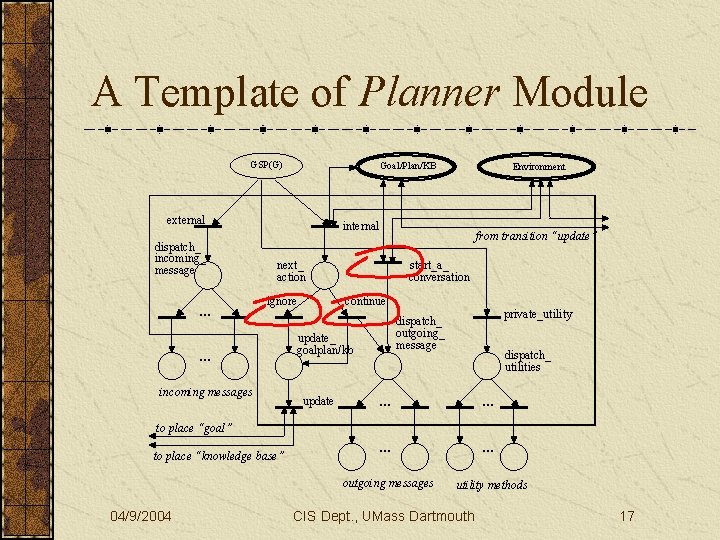
A Template of Planner Module GSP(G) Goal/Plan/KB external dispatch_ incoming_ message … Environment internal next_ action ignore … incoming messages from transition “update” start_a_ conversation continue update_ goalplan/kb update private_utility dispatch_ outgoing_ message dispatch_ utilities … … outgoing messages utility methods to place “goal” to place “knowledge base” 04/9/2004 CIS Dept. , UMass Dartmouth 17
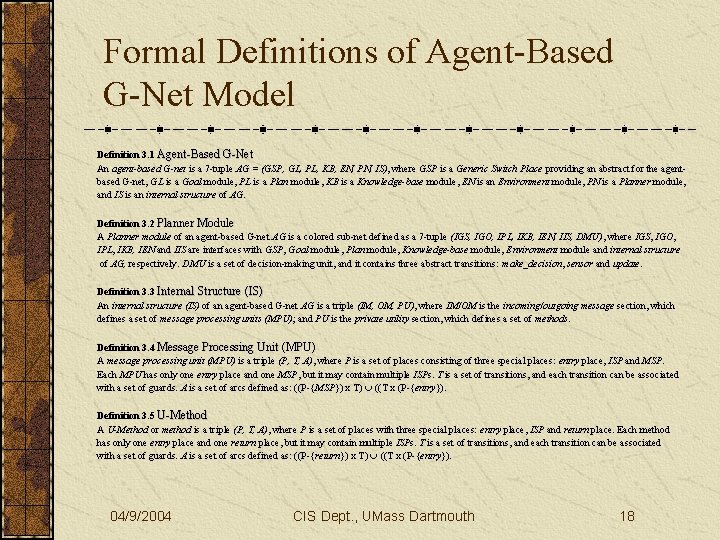
Formal Definitions of Agent-Based G-Net Model Definition 3. 1 Agent-Based G-Net An agent-based G-net is a 7 -tuple AG = (GSP, GL, PL, KB, EN, PN, IS), where GSP is a Generic Switch Place providing an abstract for the agentbased G-net, GL is a Goal module, PL is a Plan module, KB is a Knowledge-base module, EN is an Environment module, PN is a Planner module, and IS is an internal structure of AG. Definition 3. 2 Planner Module A Planner module of an agent-based G-net AG is a colored sub-net defined as a 7 -tuple (IGS, IGO, IPL, IKB, IEN, IIS, DMU), where IGS, IGO, IPL, IKB, IEN and IIS are interfaces with GSP, Goal module, Plan module, Knowledge-base module, Environment module and internal structure of AG, respectively. DMU is a set of decision-making unit, and it contains three abstract transitions: make_decision, sensor and update. Definition 3. 3 Internal Structure (IS) An internal structure (IS) of an agent-based G-net AG is a triple (IM, OM, PU), where IM/OM is the incoming/outgoing message section, which defines a set of message processing units (MPU); and PU is the private utility section, which defines a set of methods. Definition 3. 4 Message Processing Unit (MPU) A message processing unit (MPU) is a triple (P, T, A), where P is a set of places consisting of three special places: entry place, ISP and MSP. Each MPU has only one entry place and one MSP, but it may contain multiple ISPs. T is a set of transitions, and each transition can be associated with a set of guards. A is a set of arcs defined as: ((P-{MSP}) x T) ((T x (P-{entry}). Definition 3. 5 U-Method A U-Method or method is a triple (P, T, A), where P is a set of places with three special places: entry place, ISP and return place. Each method has only one entry place and one return place, but it may contain multiple ISPs. T is a set of transitions, and each transition can be associated with a set of guards. A is a set of arcs defined as: ((P-{return}) x T) ((T x (P-{entry}). 04/9/2004 CIS Dept. , UMass Dartmouth 18
A Framework for Modeling Agent. Oriented Software To support inheritance, we revise the planner module: Abstract transition: represents abstract units of decision-making or mental-state-updating (with synchronization) Autonomous unit: makes an agent autonomous and internallymotivated Asynchronous Superclass switch Place (ASP): used to forward a MPU or a method call (token) to a “superclass” model in the case of inherited communication mechanisms. Show the useful role of inheritance in agent-oriented software design. 04/9/2004 CIS Dept. , UMass Dartmouth 19
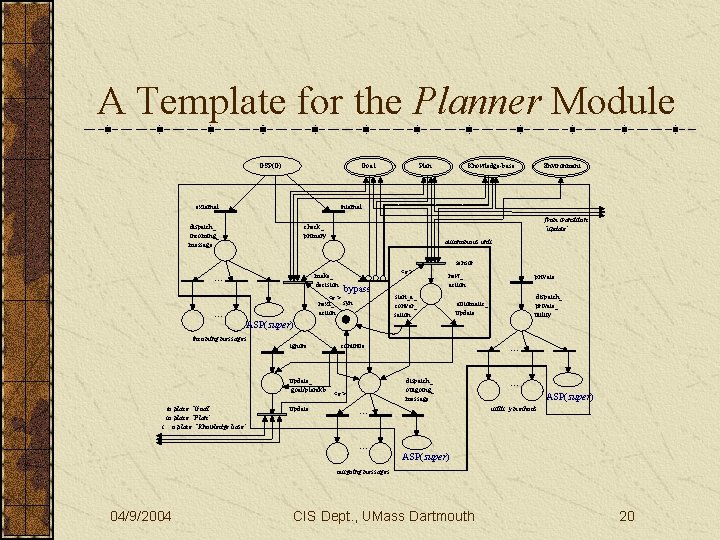
A Template for the Planner Module Goal GSP(G) external Plan Knowledge-base Environment internal dispatch_ incoming_ message from transition “update” check_ primary autonomous unit sensor make_ decision … <e> bypass <e> next_ syn action … ASP(super) incoming messages ignore update_ goal/plan/kb to place “Goal” to place “Plan” t o place “Knowledge base” update new_ action start_a_ conver_ sation … dispatch_ outgoing_ message … ASP(super) utilit y methods … … dispatch_ private_ utility automatic_ update continue <e> private ASP(super) outgoing messages 04/9/2004 CIS Dept. , UMass Dartmouth 20
Part 3: Design of Intelligent Mobile Agents – A Generic Model Two schemes for agent development: Weak agent approach Strong agent approach Most of the existing work on mobile agents use weak agent approach (not flexible, security issues …) In contrast, we propose a generic model for intelligent mobile agent. 04/9/2004 CIS Dept. , UMass Dartmouth 21
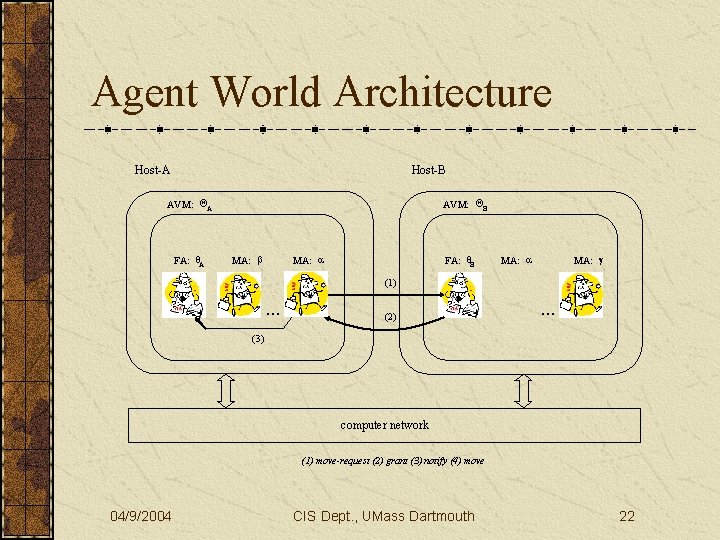
Agent World Architecture Host-A Host-B AVM: QA FA: q. A AVM: QB MA: b MA: a FA: q. B MA: a MA: g (1) … (2) … (3) computer network (1) move-request (2) grant (3) notify (4) move 04/9/2004 CIS Dept. , UMass Dartmouth 22
Formal Definitions of Agent World Architecture Definition 3. 1 Agent World (AW) An agent world (AW) is a 3 -tuple (WKHOST, SHOST, HCOM), where WKHOST is a well-known static host, which is responsible for recording the most recent address and public key of all other hosts and for issuing certificates to the FAs in SHOST is a set of hosts that can provide the services of an agent virtual machine. HCOM is the communication protocol among hosts in SHOST; an example of such protocols is TCP/IP. Definition 3. 2 Agent Virtual Machine (AVM) An agent virtual machine (AVM) is a 5 -tuple (IFA, SIMA, HOSTIP, ID), where IFA is a facilitator for AVM, which is responsible for recording information of mobile agents running on that AVM, and also for providing services for mobile agents running on the AVM. SMA is a set of mobile agents. HOSTIP is the current IP address of the host that is supporting this AVM, and ID is a unique identifier for that AVM. Definition 3. 3 Static Host (SH) and Mobile Host (MH) A host is a 4 -tuple (SAVM, ACOM, HOMEIP, CURIP), where SAVM is a set of agent virtual machines (AVM). ACOM is the communication protocol among AVMs in SAVM, and examples of such protocols are IPC and TCP/IP. HOMEIP is the original IP address of the host, and CURIP is the current IP address of the host. If at any time, CURIP = HOMEIP, we call the host a static host (SH); otherwise, we call it a mobile host (MH). Definition 3. 4 Static Agent (SA) and Mobile Agent (MA) An agent A is a 3 -tuple (HOMEIP, CURIP, AO), where HOMEIP is the IP address of the host on which agent A is created. CURIP is the IP address of the host supporting agent A. AO is the agent object with the general structure as we described in Section 2. If at any time, CURIP = HOMEIP, we refer to agent A as a static agent (SA); otherwise, we refer to agent A as a mobile agent (MA). 04/9/2004 CIS Dept. , UMass Dartmouth 23
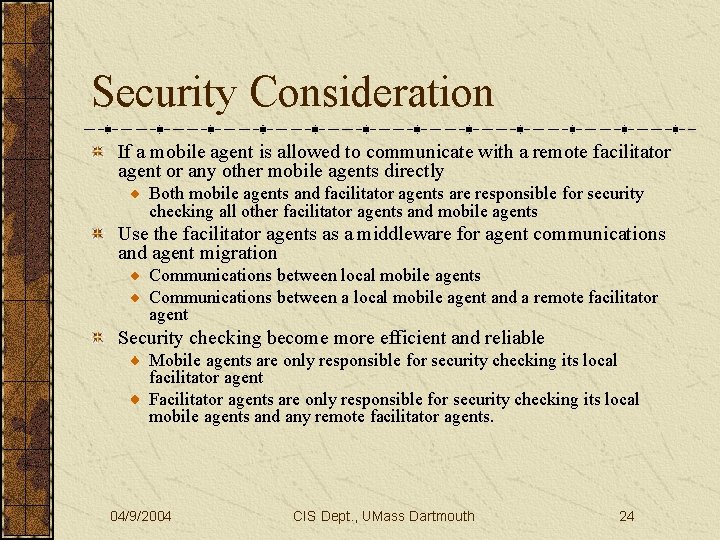
Security Consideration If a mobile agent is allowed to communicate with a remote facilitator agent or any other mobile agents directly Both mobile agents and facilitator agents are responsible for security checking all other facilitator agents and mobile agents Use the facilitator agents as a middleware for agent communications and agent migration Communications between local mobile agents Communications between a local mobile agent and a remote facilitator agent Security checking become more efficient and reliable Mobile agents are only responsible for security checking its local facilitator agent Facilitator agents are only responsible for security checking its local mobile agents and any remote facilitator agents. 04/9/2004 CIS Dept. , UMass Dartmouth 24
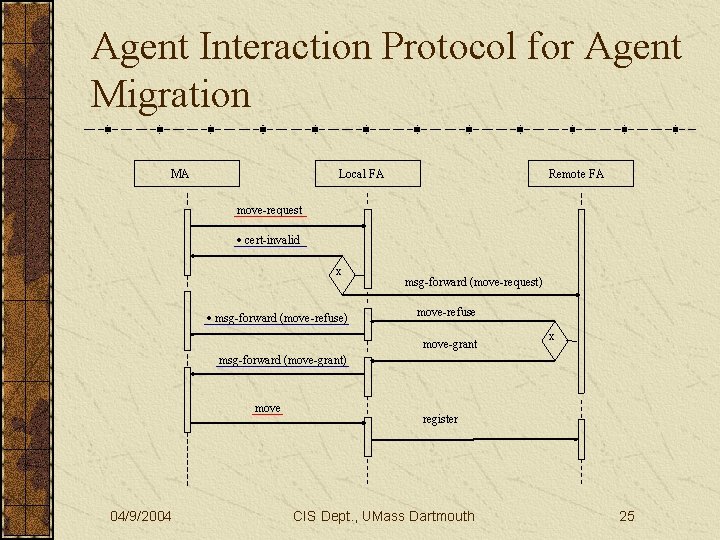
Agent Interaction Protocol for Agent Migration MA Local FA Remote FA move-request cert-invalid x msg-forward (move-refuse) msg-forward (move-request) move-refuse move-grant x msg-forward (move-grant) move 04/9/2004 register CIS Dept. , UMass Dartmouth 25
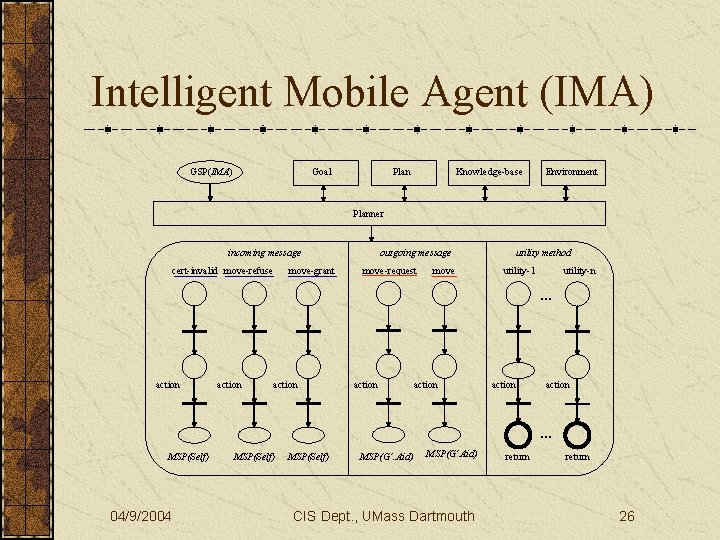
Intelligent Mobile Agent (IMA) GSP(IMA) Goal Plan Knowledge-base Environment Planner incoming message cert-invalid move-refuse move-grant outgoing message move-request move utility method utility-1 utility-n … action action … MSP(Self) 04/9/2004 MSP(Self) MSP(G’. Aid) MSP(G’Aid) CIS Dept. , UMass Dartmouth return 26
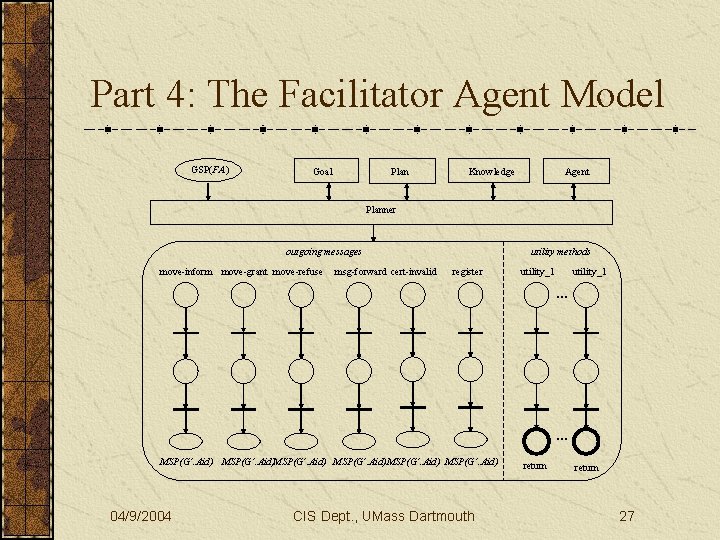
Part 4: The Facilitator Agent Model GSP(FA) Goal Plan Knowledge Agent Planner outgoing messages move-inform move-grant move-refuse msg-forward cert-invalid utility methods register utility_1 … … MSP(G’. Aid)MSP(G’. Aid) 04/9/2004 CIS Dept. , UMass Dartmouth return 27
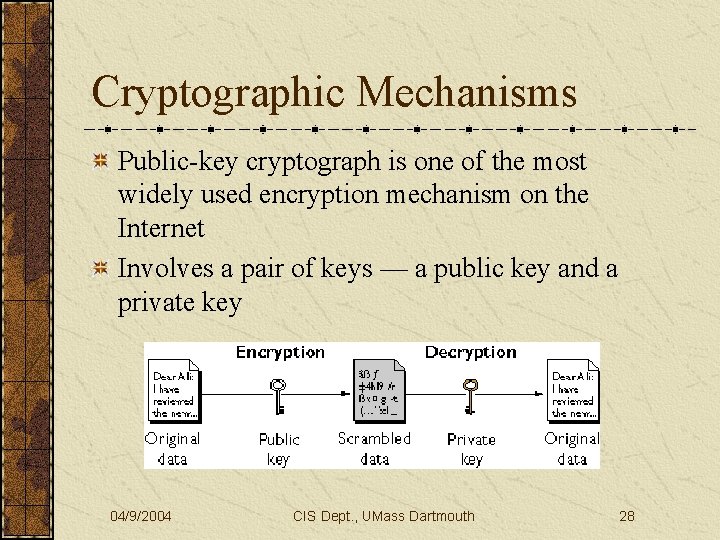
Cryptographic Mechanisms Public-key cryptograph is one of the most widely used encryption mechanism on the Internet Involves a pair of keys — a public key and a private key 04/9/2004 CIS Dept. , UMass Dartmouth 28
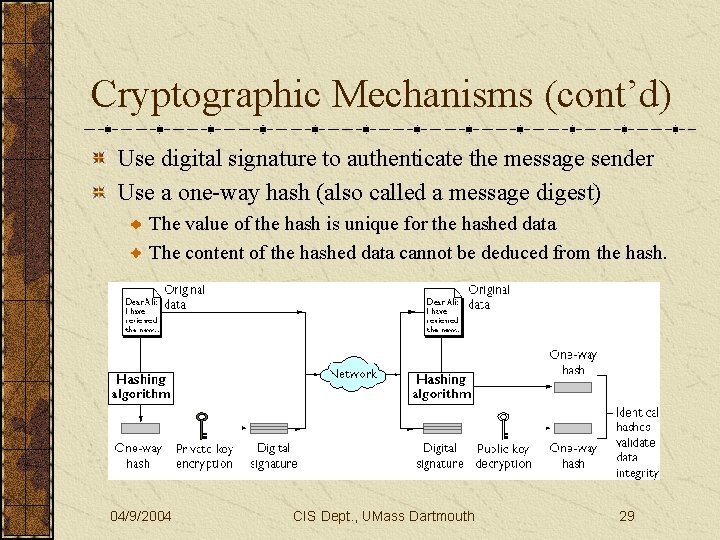
Cryptographic Mechanisms (cont’d) Use digital signature to authenticate the message sender Use a one-way hash (also called a message digest) The value of the hash is unique for the hashed data The content of the hashed data cannot be deduced from the hash. 04/9/2004 CIS Dept. , UMass Dartmouth 29
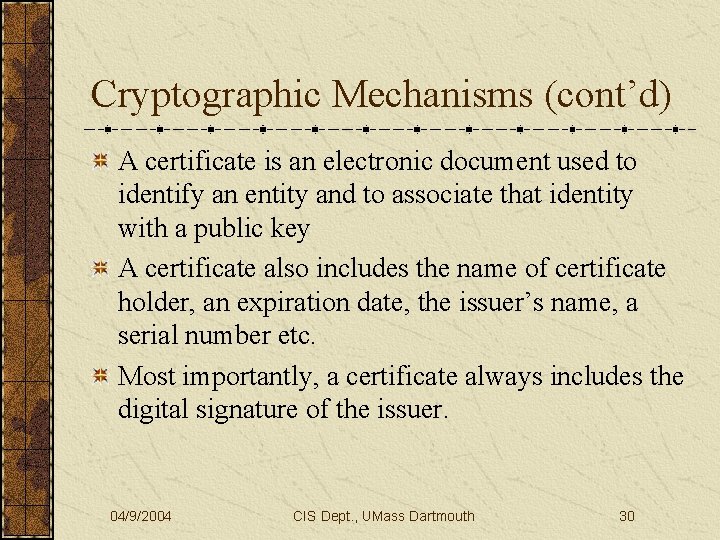
Cryptographic Mechanisms (cont’d) A certificate is an electronic document used to identify an entity and to associate that identity with a public key A certificate also includes the name of certificate holder, an expiration date, the issuer’s name, a serial number etc. Most importantly, a certificate always includes the digital signature of the issuer. 04/9/2004 CIS Dept. , UMass Dartmouth 30

Certificate/Passport/Visa Approach User assigns a certificate to a mobile agent when it is created Contains info such as issuer’s name, public key etc. Is recognizable by the local facilitator agent Is not recognizable by a remote facilitator agent Local facilitator agent assigns a passport to the mobile agent to replace the initial certificate A mobile agent can use the passport to apply for a visa from a foreign facilitator agent. 04/9/2004 CIS Dept. , UMass Dartmouth 31
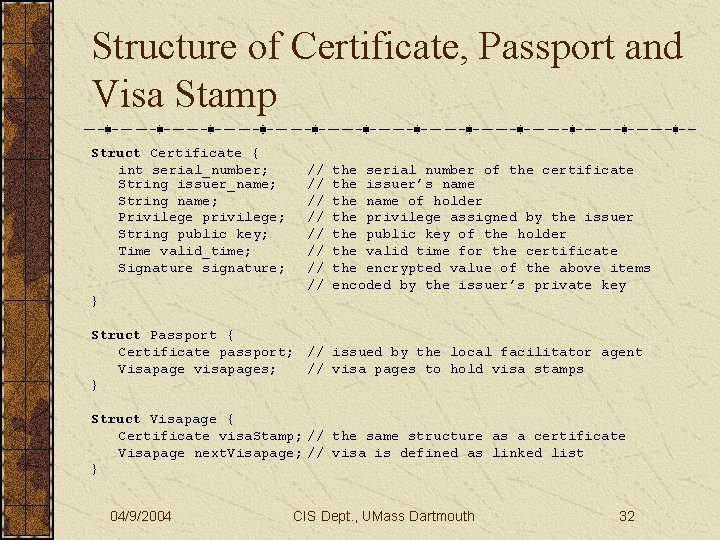
Structure of Certificate, Passport and Visa Stamp Struct Certificate { int serial_number; String issuer_name; String name; Privilege privilege; String public key; Time valid_time; Signature signature; // // the serial number of the certificate the issuer’s name the name of holder the privilege assigned by the issuer the public key of the holder the valid time for the certificate the encrypted value of the above items encoded by the issuer’s private key } Struct Passport { Certificate passport; // issued by the local facilitator agent Visapage visapages; // visa pages to hold visa stamps } Struct Visapage { Certificate visa. Stamp; // the same structure as a certificate Visapage next. Visapage; // visa is defined as linked list } 04/9/2004 CIS Dept. , UMass Dartmouth 32
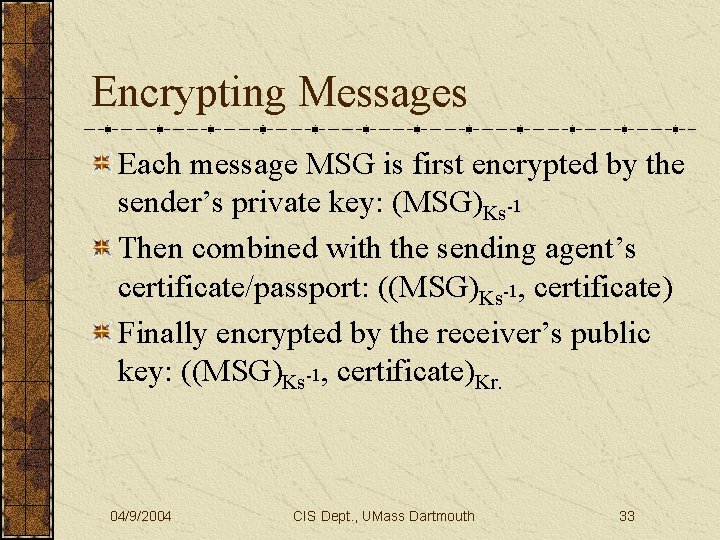
Encrypting Messages Each message MSG is first encrypted by the sender’s private key: (MSG)Ks-1 Then combined with the sending agent’s certificate/passport: ((MSG)Ks-1, certificate) Finally encrypted by the receiver’s public key: ((MSG)Ks-1, certificate)Kr. 04/9/2004 CIS Dept. , UMass Dartmouth 33
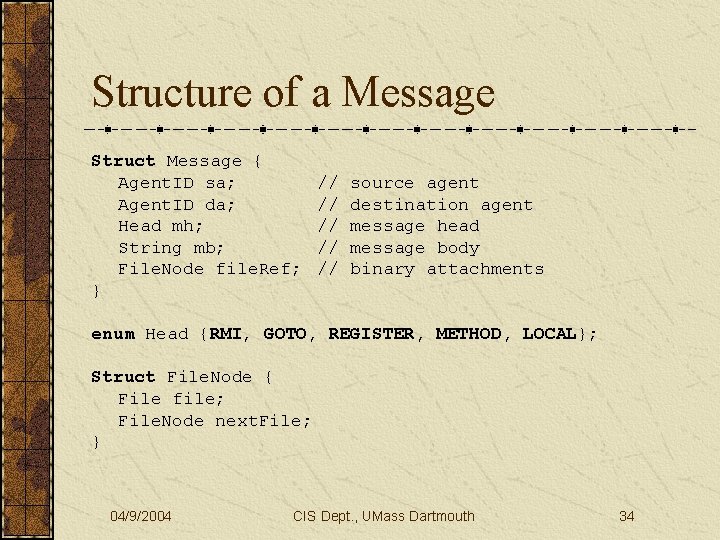
Structure of a Message Struct Message { Agent. ID sa; Agent. ID da; Head mh; String mb; File. Node file. Ref; } // // // source agent destination agent message head message body binary attachments enum Head {RMI, GOTO, REGISTER, METHOD, LOCAL}; Struct File. Node { File file; File. Node next. File; } 04/9/2004 CIS Dept. , UMass Dartmouth 34
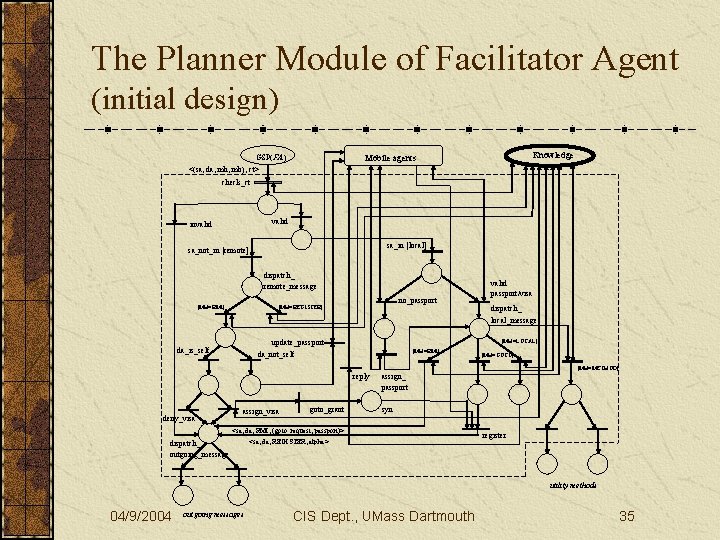
The Planner Module of Facilitator Agent (initial design) GSP(FA) Knowledge Mobile agents <(sa, da, mh, mb), ct> check_ct valid invalid sa_in [local] sa_not_in [remote] dispatch_ remote_message [MH=RMI] no_passport [MH=REGISTER] dispatch_ local_message [MH=LOCAL] update_passport da_is_self valid passport/visa [MH=RMI] da_not_self [MH=GOTO] [MH=METHOD] reply deny_visa assign_visa goto_grant assign_ passport syn <sa, da, RMI, (goto_request, passport)> dispatch_ outgoing_message <sa, da, REGISTER, alpha> register utility methods 04/9/2004 outgoing messages CIS Dept. , UMass Dartmouth 35
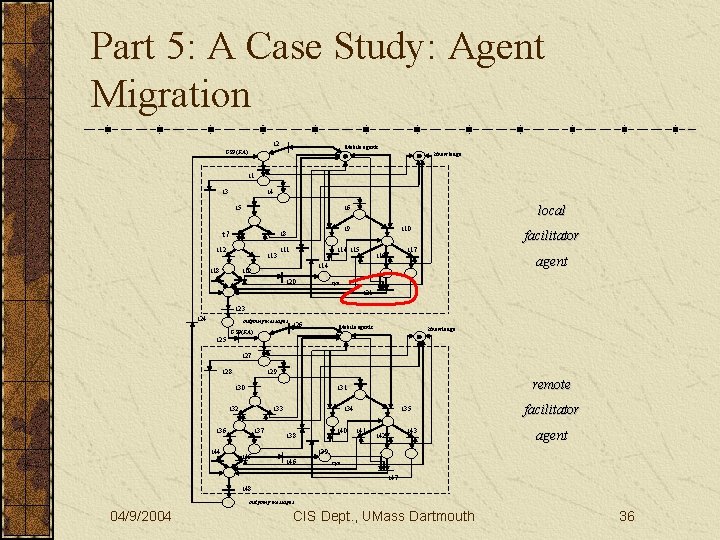
Part 5: A Case Study: Agent Migration t 2 Mobile agents GSP(FA) Knowledge t 1 t 3 t 4 t 5 t 9 t 8 t 7 t 12 t 13 t 18 local t 6 t 11 t 10 t 14 t 15 facilitator t 17 t 16 agent t 14 t 19 t 20 syn t 21 t 23 t 24 outgoing messages t 26 Mobile agents GSP(FA) Knowledge t 25 t 27 t 28 t 29 t 30 t 32 t 33 t 36 t 44 remote t 31 t 37 t 45 t 34 t 40 t 38 t 35 t 41 t 43 t 42 facilitator agent t 39 t 46 syn t 47 t 48 outgoing messages 04/9/2004 CIS Dept. , UMass Dartmouth 36
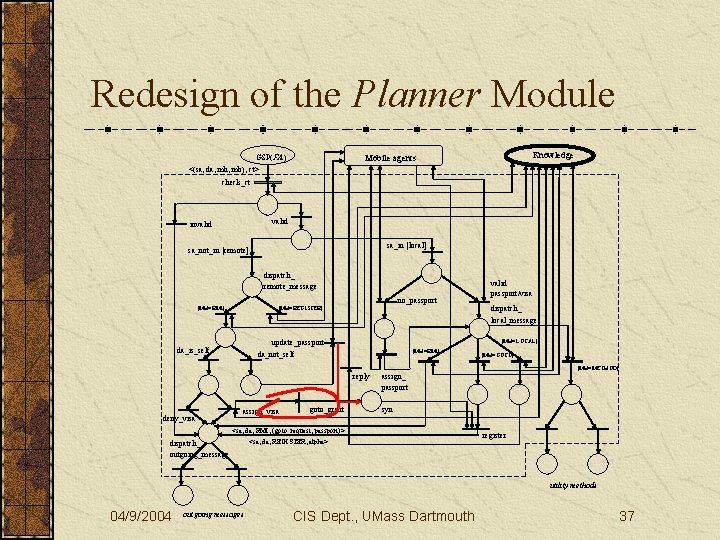
Redesign of the Planner Module Knowledge Mobile agents GSP(FA) <(sa, da, mh, mb), ct> check_ct valid invalid sa_in [local] sa_not_in [remote] dispatch_ remote_message [MH=RMI] no_passport [MH=REGISTER] dispatch_ local_message [MH=LOCAL] update_passport da_is_self valid passport/visa [MH=RMI] da_not_self [MH=GOTO] [MH=METHOD] reply deny_visa assign_visa goto_grant assign_ passport syn <sa, da, RMI, (goto_request, passport)> dispatch_ outgoing_message <sa, da, REGISTER, alpha> register utility methods 04/9/2004 outgoing messages CIS Dept. , UMass Dartmouth 37
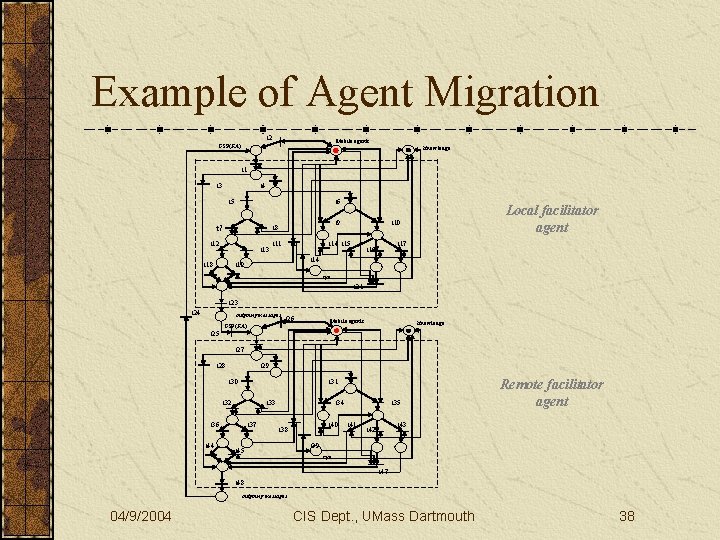
Example of Agent Migration t 2 Mobile agents GSP(FA) Knowledge t 1 t 3 t 4 t 5 t 6 t 9 t 8 t 7 t 12 t 13 t 18 t 11 Local facilitator agent t 10 t 14 t 15 t 17 t 16 t 14 t 19 syn t 21 t 23 t 24 outgoing messages t 26 Mobile agents GSP(FA) Knowledge t 25 t 27 t 28 t 29 t 30 t 31 t 32 t 33 t 36 t 44 t 37 t 34 t 40 t 38 t 45 t 35 t 41 Remote facilitator agent t 43 t 42 t 39 syn t 47 t 48 outgoing messages 04/9/2004 CIS Dept. , UMass Dartmouth 38
Advantages of Our Approach Application-specific mobile agent class can be defined as a subclass of IMA Security checking for mobile agents is efficient and reliable due to localization The resulting Petri net model can be used as a foundation formal Petri net analysis and simulation techniques. 04/9/2004 CIS Dept. , UMass Dartmouth 39
Part 6: Concluding Comments There is an increasing need to ensure that complex software systems are robust, reliable and fit for purpose (Agent-Oriented SE) Petri nets provide a formal and visual model with natural expression for concurrency and coordination Adapt Petri net models to define a security-based model for mobile agent software system. 04/9/2004 CIS Dept. , UMass Dartmouth 40
Future Work Study various security issues in mobile agent design, especially the efficiency and reliability of different security protocols Design and develop a compilation process to automatically build security protocols into our existing agent models Develop a model-based mobile agent development environment (M-MADE) for rapid agent design and implementation (i. e. , synthesis of the work). 04/9/2004 CIS Dept. , UMass Dartmouth 41
Thanks for your attention! The slides for this talk may be downloaded from http: //www. cis. umassd. edu/~hxu 04/9/200404/15/02 CIS Dept. , UMass Dartmouth
- Slides: 42