1 SUBMITTED TO ER BHARAT NARESH BANSAL SUBMITTED
1 SUBMITTED TO: ER. BHARAT NARESH BANSAL SUBMITTED BY: ANU BALA(100500416662) PARAMJEET KAUR(100500416691) SHEENAM BALA(100500416700) SHEFALI SINGLA(100500416701) SATINDER SINGH(1185081) 10/3/2020 6 MONTH INDUSTRIAL TRAINIG ON EMBEDDED LINUX WITH ARM PROCESSOR
2 10/3/2020 Multiple Data Compression & Decompression also Encryption Using Iterative Techniques
3 NEED OF MDC Basic purpose of this project compress the data which have in text format. But we can compress any type of data if we know code format of that type data. Exp : image , audio , video etc. Iterative Technique is used for compression which is Latest and use for bit shifting. By this project we can compress the data more than 50%. We can reduce the bandwidth at desired level by this method. The data transmission is very smooth & fast after compression. The main advantage of this project Encryption. Nobody can read your data without Encryption key. The price of Encryption key in Lakhs at industry level. 10/3/2020
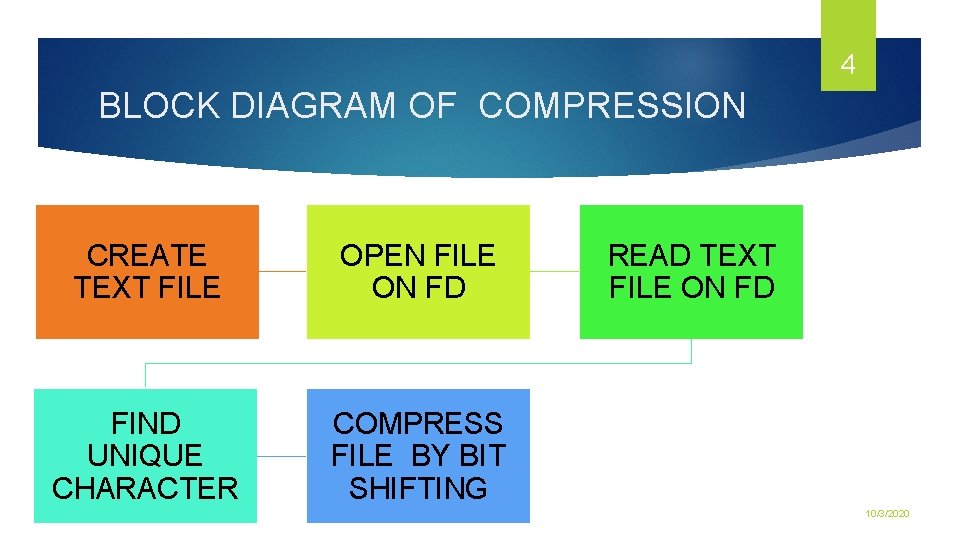
4 BLOCK DIAGRAM OF COMPRESSION CREATE TEXT FILE OPEN FILE ON FD FIND UNIQUE CHARACTER COMPRESS FILE BY BIT SHIFTING READ TEXT FILE ON FD 10/3/2020
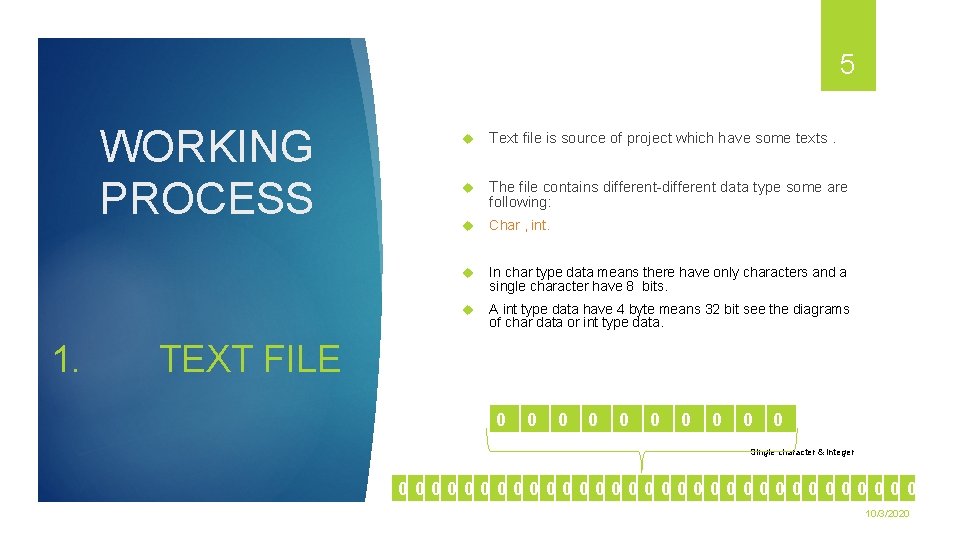
5 WORKING PROCESS 1. Text file is source of project which have some texts. The file contains different-different data type some are following: Char , int. In char type data means there have only characters and a single character have 8 bits. A int type data have 4 byte means 32 bit see the diagrams of char data or int type data. TEXT FILE 0 0 0 0 0 Single character & integer 0000000000000000 10/3/2020
6 2. OPEN FILE After making a text file then open this file in project. Project is based on Embedded c or linux so there have use some system calls or c programming. First of all we use some header files which includes small additional operations for exp: #include<stdio. h>; includes printf of scanf operation. Every header file start from # which is predefined micro. Predefined micro symbol is used for handshake with compiler. Then make a open function & for open file use open system call. Open(“file name ”, mode of file); 10/3/2020
7 3. READ TEXT FILE After open the file then we read the file character by character with index of characters. Command is used for read operation: read(fd , &buffer/pointer , no. of byte); Some parameters which are using in this read function are following: Fd ---file descriptor Buffer---Array(int/char) Pointer ----point & hold the address of any type of data. 10/3/2020
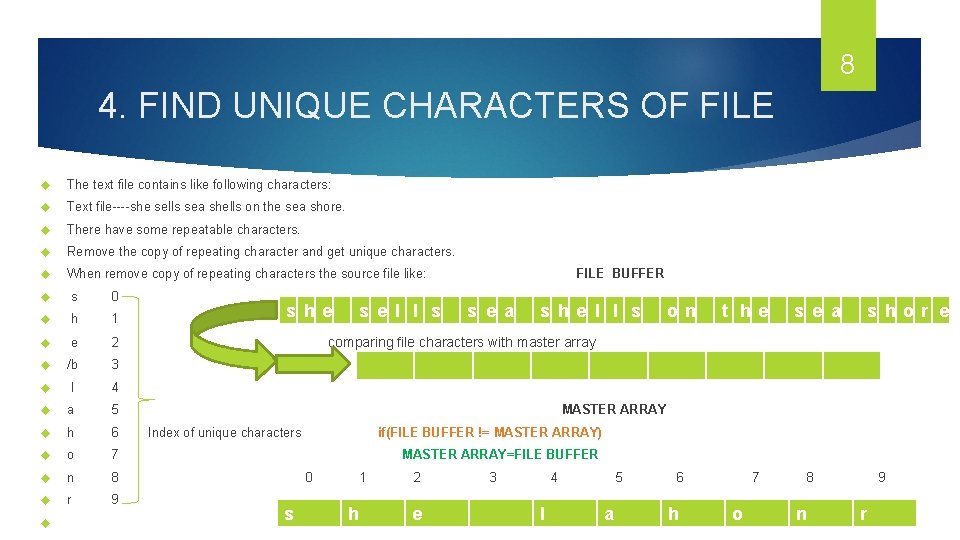
8 4. FIND UNIQUE CHARACTERS OF FILE The text file contains like following characters: Text file----she sells sea shells on the sea shore. There have some repeatable characters. Remove the copy of repeating character and get unique characters. When remove copy of repeating characters the source file like: s 0 h 1 e 2 /b 3 l 4 a 5 h 6 o 7 n 8 r 9 s he s e l l s FILE BUFFER s e a s he l l s on t he s e a s hor e comparing file characters with master array MASTER ARRAY Index of unique characters if(FILE BUFFER != MASTER ARRAY) MASTER ARRAY=FILE BUFFER 0 s 1 h 2 e 3 4 l 5 a 6 h 7 o 8 n 9 r 10/3/2020
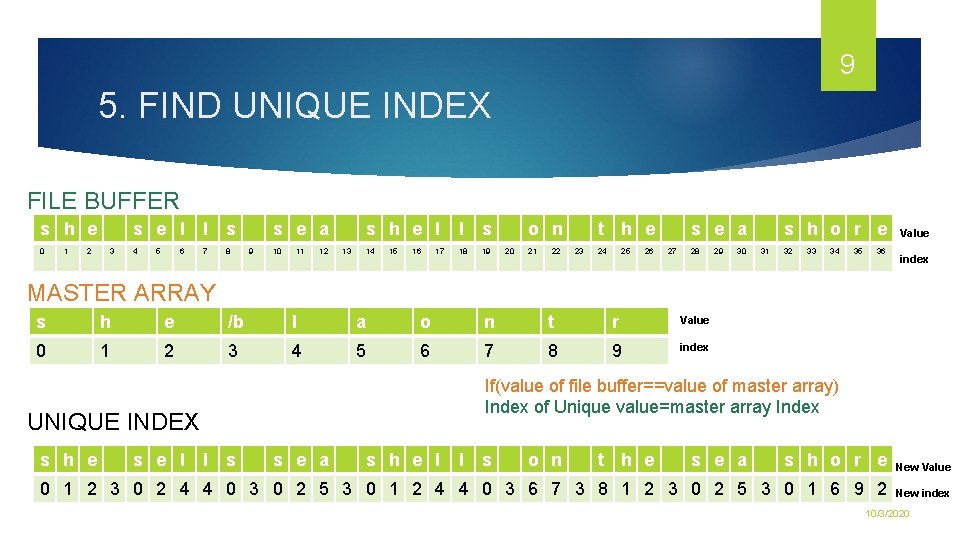
9 5. FIND UNIQUE INDEX FILE BUFFER s h e 0 1 2 3 s e l l s 4 7 8 5 6 s e a 9 10 11 12 13 s h e l l s 14 18 19 15 16 17 o n 20 21 22 t h e 23 24 25 26 s e a 27 28 29 30 s h o r e 31 32 33 34 35 36 Value index MASTER ARRAY s h e /b l a o n t r Value 0 1 2 3 4 5 6 7 8 9 index If(value of file buffer==value of master array) Index of Unique value=master array Index UNIQUE INDEX s h e s e l l s s e a s h e l l s o n t h e s e a s h o r e New Value 0 1 2 3 0 2 4 4 0 3 0 2 5 3 0 1 2 4 4 0 3 6 7 3 8 1 2 3 0 2 5 3 0 1 6 9 2 New index 10/3/2020
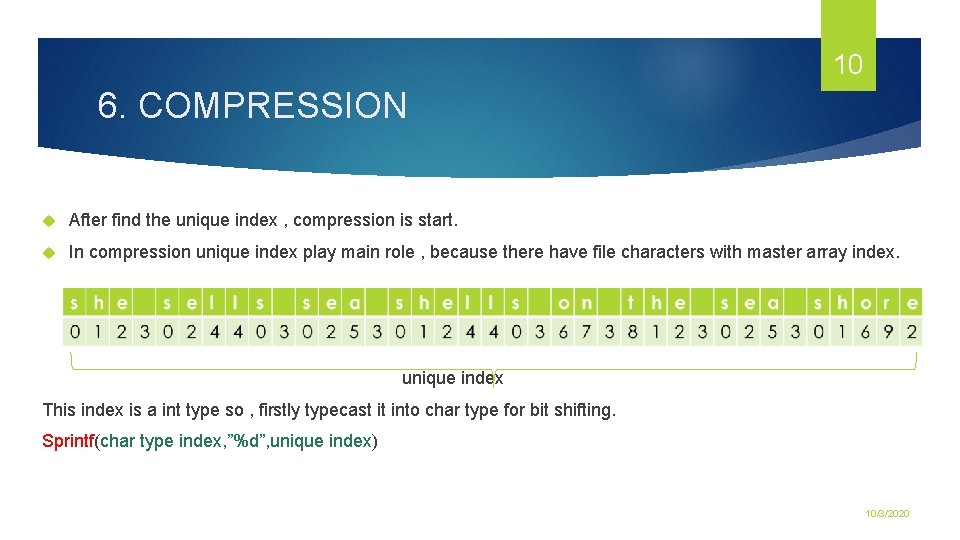
10 6. COMPRESSION After find the unique index , compression is start. In compression unique index play main role , because there have file characters with master array index. unique index This index is a int type so , firstly typecast it into char type for bit shifting. Sprintf(char type index, ”%d”, unique index) 10/3/2020
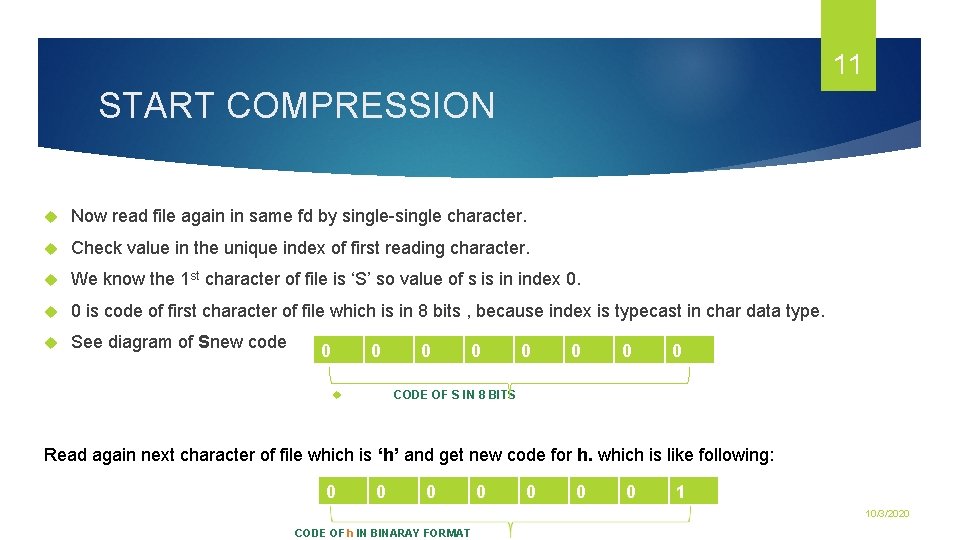
11 START COMPRESSION Now read file again in same fd by single-single character. Check value in the unique index of first reading character. We know the 1 st character of file is ‘S’ so value of s is in index 0. 0 is code of first character of file which is in 8 bits , because index is typecast in char data type. See diagram of Snew code 0 0 0 0 CODE OF S IN 8 BITS Read again next character of file which is ‘h’ and get new code for h. which is like following: 0 0 0 0 1 10/3/2020 CODE OF h IN BINARAY FORMAT
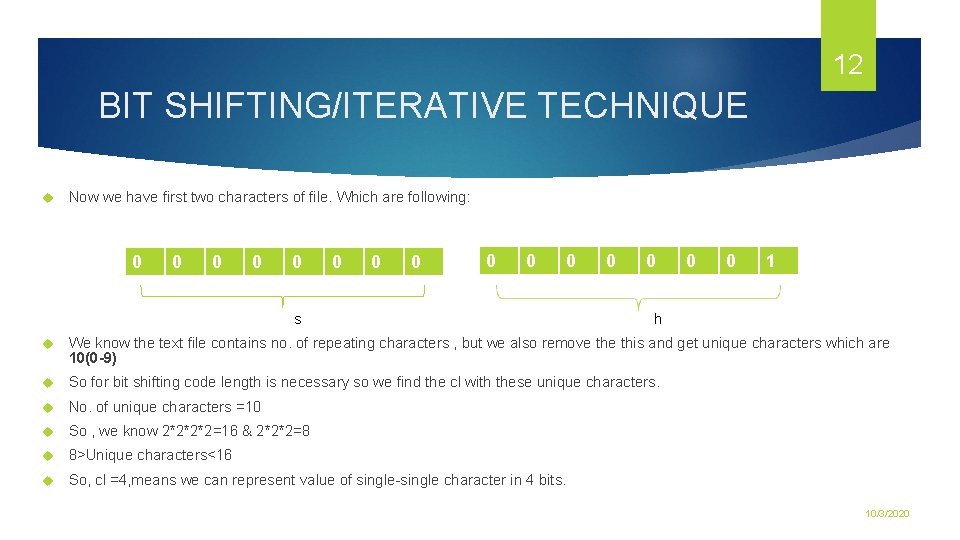
12 BIT SHIFTING/ITERATIVE TECHNIQUE Now we have first two characters of file. Which are following: 0 0 0 s 0 0 1 h We know the text file contains no. of repeating characters , but we also remove this and get unique characters which are 10(0 -9) So for bit shifting code length is necessary so we find the cl with these unique characters. No. of unique characters =10 So , we know 2*2*2*2=16 & 2*2*2=8 8>Unique characters<16 So, cl =4, means we can represent value of single-single character in 4 bits. 10/3/2020
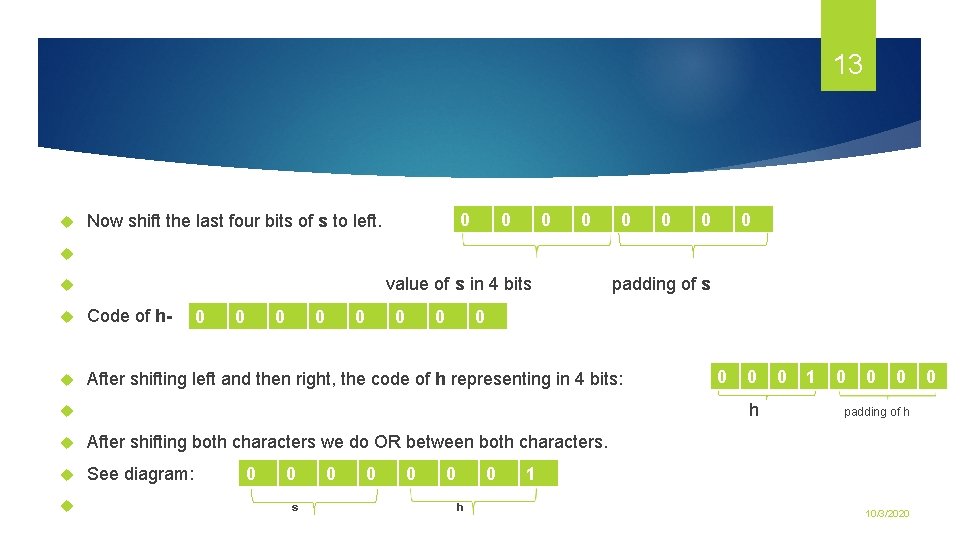
13 0 Now shift the last four bits of s to left. 0 0 0 0 value of s in 4 bits padding of s Code of h- After shifting left and then right, the code of h representing in 4 bits: 0 0 0 0 0 h After shifting both characters we do OR between both characters. See diagram: 0 0 0 s 0 0 0 h 0 1 0 0 0 padding of h 1 10/3/2020 0
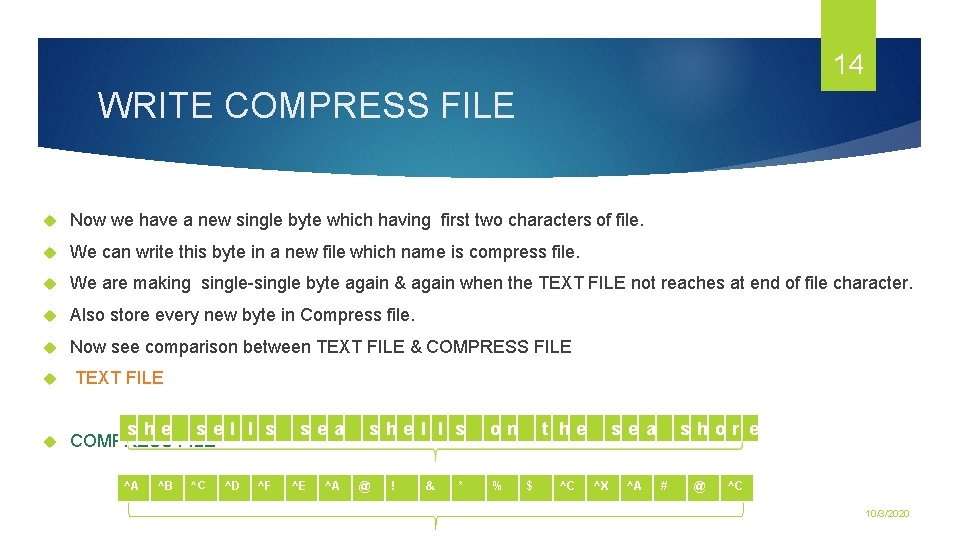
14 WRITE COMPRESS FILE Now we have a new single byte which having first two characters of file. We can write this byte in a new file which name is compress file. We are making single-single byte again & again when the TEXT FILE not reaches at end of file character. Also store every new byte in Compress file. Now see comparison between TEXT FILE & COMPRESS FILE TEXT FILE s he s e l l s COMPRESS FILE ^A ^B ^C ^D ^F s e a ^E ^A s he l l s @ ! & * on % t he $ ^C s e a ^X ^A s hor e # @ ^C 10/3/2020
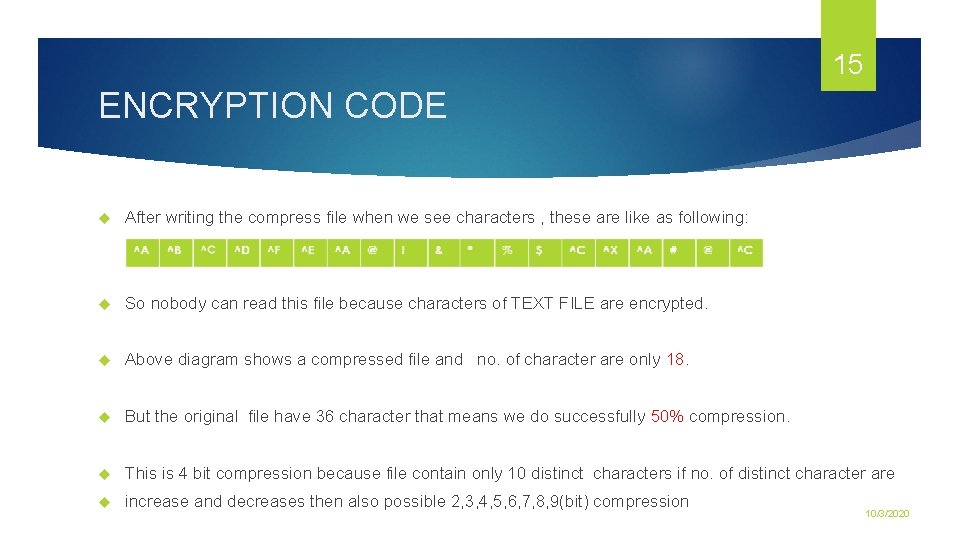
15 ENCRYPTION CODE After writing the compress file when we see characters , these are like as following: So nobody can read this file because characters of TEXT FILE are encrypted. Above diagram shows a compressed file and no. of character are only 18. But the original file have 36 character that means we do successfully 50% compression. This is 4 bit compression because file contain only 10 distinct characters if no. of distinct character are increase and decreases then also possible 2, 3, 4, 5, 6, 7, 8, 9(bit) compression 10/3/2020
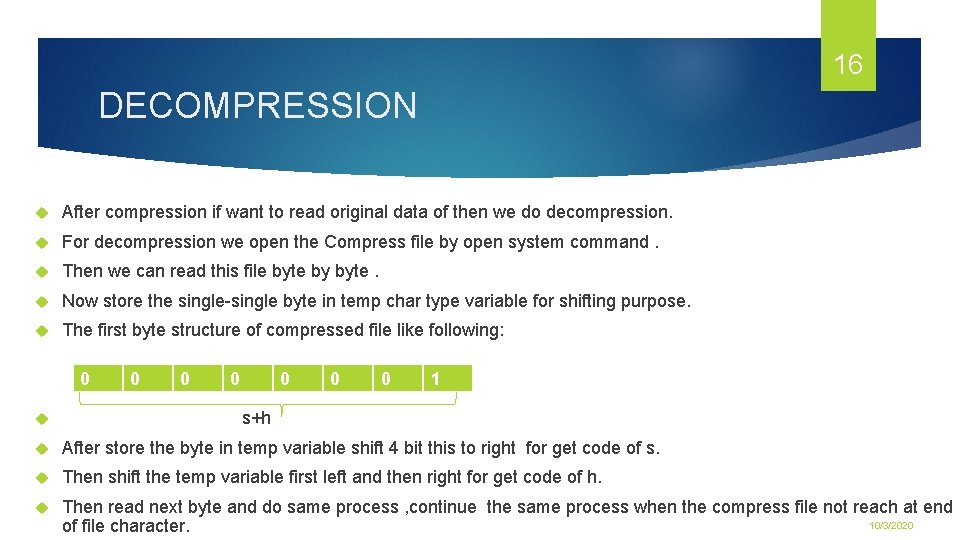
16 DECOMPRESSION After compression if want to read original data of then we do decompression. For decompression we open the Compress file by open system command. Then we can read this file byte by byte. Now store the single-single byte in temp char type variable for shifting purpose. The first byte structure of compressed file like following: 0 0 0 0 1 s+h After store the byte in temp variable shift 4 bit this to right for get code of s. Then shift the temp variable first left and then right for get code of h. Then read next byte and do same process , continue the same process when the compress file not reach at end 10/3/2020 of file character.
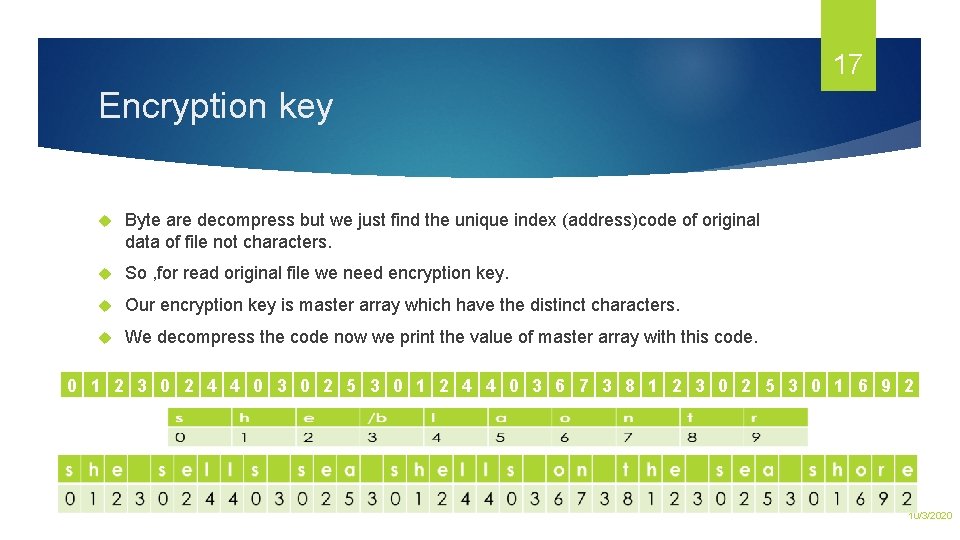
17 Encryption key Byte are decompress but we just find the unique index (address)code of original data of file not characters. So , for read original file we need encryption key. Our encryption key is master array which have the distinct characters. We decompress the code now we print the value of master array with this code. 0 1 2 3 0 2 4 4 0 3 0 2 5 3 0 1 2 4 4 0 3 6 7 3 8 1 2 3 0 2 5 3 0 1 6 9 2 10/3/2020
PROJECT 03: 10/3/2020 INTER PROCESS COMMUNICATION BETWEEN REQ. CLIENT SERVER & PROCESSOR 18
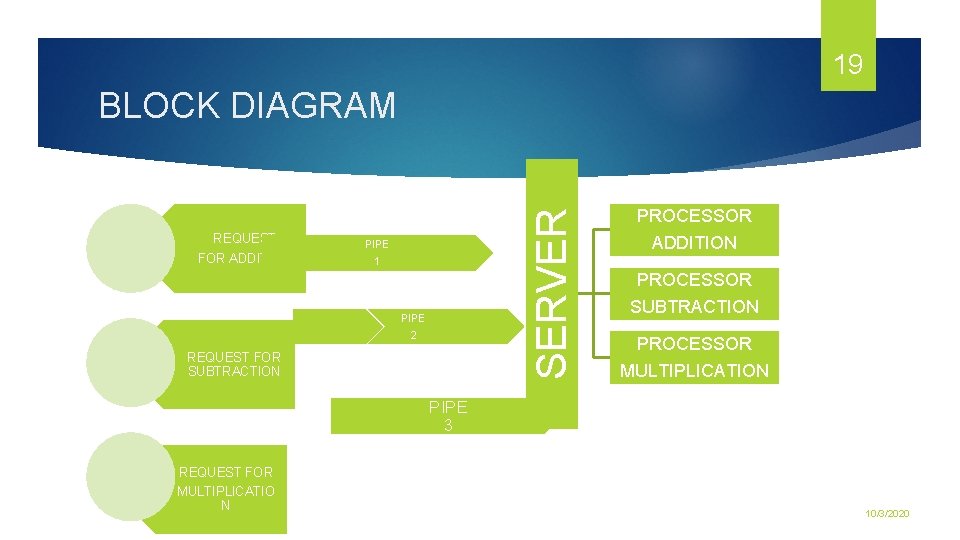
19 REQUEST FOR ADDITION SERVER BLOCK DIAGRAM PIPE 1 PIPE 2 REQUEST FOR SUBTRACTION PROCESSOR ADDITION PROCESSOR SUBTRACTION PROCESSOR MULTIPLICATION PIPE 3 REQUEST FOR MULTIPLICATIO N 10/3/2020
20 SERVER Server like main part of ipc project because that maintain both services requesting from sender & processing from processor. In this project we use 3 processor but count of clients and processors are unlimited depends upon the application. Server connected with the clients and processors via single-single pipe. The pipe is created by server using pipe system call. For making connection between clients and processor we pass the FD, s from server using excel command. two types of FD – read FD and write FD. READ FD use for read the data & WRITE FD is used for write the data. 10/3/2020
21 For doing execl we create a process and make child and parent process by fork( ); system call. Fork create two process: Parent Child(zombie , orphan) Excel is use in child process. The data RD WR operation doing in parent process. If child is executing first than parent process then it is called zombie child. If child is executing after the parent process then that is called orphan child 10/3/2020
22 REQUESTING CLIENTS Requesting clients means users which are sending the request to server for process the data. There have three clients- Addition Subtraction Multiplication Every client send 2 variable and a single operator (+) to server for process the data. Variables having some value which are processed by processors to client through server. 10/3/2020
23 PROCESSORS According to the project there have three processors which process the data which send from client to server. Sever send the client requested data according to operator value to the processor. Means there have following type processors: Addition purpose processor(+) Subtraction purpose processor(-) Multiplication purpose processor(*) 10/3/2020
24 10/3/2020 THANK YOU
- Slides: 24