TRAINING GUIDE Adding New VLSM Subnets Network Security
TRAINING GUIDE Adding New VLSM Subnets, Network Security and Management, and IPv 6 Concepts CIT/249
INTRODUCTION In this presentation we will be able to observe some of the aspects that we have studied and practiced throughout the course. Among them the importance of IPv 4 and IPv 6, as well as the importance of the implementation of these, and identify them We would be able to see the correct description of ACLs, NAT and PAT, and their importance related to network security. In addition we can see the various ways to improve it. We can also study aspects such as: • A complete step-by-step illustration of how to configure the security features on a router • An accurate depiction of how to calculate a subnet ID and subnet broadcast address • A clear explanation of how to test for overlap in a VLSM scheme and troubleshoot issues that may arise from the overlap
WHY WAS IT NECESSARY TO IMPLEMENT IPV 6 The implement of PV 6 is necessary for the next three reasons: 1. SECURITY 1. SCALABILITY 1. CONNECTABILITY https: //www. link-labs. com/blog/why-ipv 6 -is-important-for-internet-of-things
HOW DO YOU PROPERLY ABBREVIATE AN IPV 6 ADDRESS? • Most IPv 6 addresses do not occupy all of their possible 128 bits. This condition results in fields that are padded with zeros or contain only zeros. • The IPv 6 addressing architecture allows you use the two-colon (: : ) notation to represent contiguous 16 -bit fields of zeros. For example, you might abbreviate the IPv 6 address in Figure 3– 2 by replacing the two contiguous fields of zeros in the interface ID with two colons. The resulting address is 2001: 0 db 8: 3 c 4 d: 0015: : 1 a 2 f: 1 a 2 b. Other fields of zeros can be represented as a single 0. You can also omit any leading zeros in a field, such as changing 0 db 8 to db 8. • So the address 2001: 0 db 8: 3 c 4 d: 0015: 0000: 1 a 2 f: 1 a 2 b can be abbreviated as 2001: db 8: 3 c 4 d: 15: : 1 a 2 f: 1 a 2 b. • You can use the two colon notation to replace any contiguous fields of all zeros in the IPv 6 address. For example, the IPv 6 address 2001: 0 db 8: 3 c 4 d: 0015: 0000: d 234: : 3 eee: 0000 can be collapsed into 2001: db 8: 3 c 4 d: 15: 0: d 234: 3 eee: : . https: //docs. oracle. com/cd/E 19253 -01/816 -4554/ipv 6 -overview-24/index. html
WHAT TWO 64 -BIT PARTS ARE CONTAINED IN AN IPV 6 ADDRESS, AND WHAT DOES EACH The IPv 6 address can split into two 64 -bit pieces. The first 64 -bit segment represents the Global Routing Prefix (also PART REPRESENT? known as the Network Prefix). The Global Routing Prefix is the portion of the address that determines the destination network to which the packet will be routed. Logically it will be subdivided by various components which allow IPv 6 addresses to be more effectively aggregated, thus reducing the size of routing tables. The typical components of the Network Prefix include: • Registry Prefix • ISP Prefix • Site Prefix • Subnet Prefix The second half of the IPv 6 address is the Interface Identifier. Per RFC 4291 -IP Version 6 Addressing Architecture, the Interface Identifier is built by dividing the 48 -bit MAC address for the interface into two pieces and inserting “FFFE” in between these pieces (24 -bits MAC + FFFE + 24 -bits MAC). This is known as an EUI-64 prefix address. The universal/local flag can also be toggled (7 th bit in first octet of MAC address) to produce a “modified” EUI-64 address. Let’s look at an example to clarify this. Suppose that the Network Prefix for your network is 2001: DB 8: 1: 2: : /64 and your MAC address for the interface is 02: 03: e 8: 00: 65: 10, then the modified EUI-64 IPv 6 address would be: 2001: 0 DB 8: 0001: 0002: 0003: E 8 FF: FE 00: 6510 https: //blogs. cisco. com/security/ipv 6 -addressing
WHAT IS THE DIFFERENCE BETWEEN AN ANYCAST ADDRESS AND A UNICAST ADDRESS • Unicast is generally, any address in networking that represents a single device or interfacce, instead of a group of addresses (as would be represented by a multicast or broadcast address). • When you need to have more than two nodes see the traffic, you have options. • If all of the nodes are on the same subnet, then broadcast becomes a viable solution. All nodes on the subnet will see all traffic. There is no TCP-like connection state maintained. Broadcast is a layer 2 feature in the Ethernet protocol, and also a layer 3 feature in IPv 4. • Multicast is a class D IPv 4 address. When used as a destination address in a packet, the routers collectively work to deliver copies of the one original packet to all hosts who have previously registred to receive packets sent to that particular multicast address. • To use anycast you advertise the same network in multiple spots of the Internet, and rely on shortest-path calculations to funnel clients to your multiple locations. As far the network nodes themselves are concerned, they're using a unicast connection to talk to your anycasted nodes. For more on Anycast, try: What is "anycast" and how is it helpful? . Anycast is also a layer 3 feature, but is a function of how route-coalescing happens. https: //serverfault. com/questions/279482/what-is-the-difference-between-unicast-anycastbroadcast-and-multicast-traffic Odom, W. (2016)
HOW CAN YOU EASILY MULTICAST ADDRESSES? IDENTIFY IPV 6 Multicast addresses in IPv 6 are similar to multicast addresses in IPv 4. They are used to communicate with dynamic groupings of hosts, for example all routers on the link (“one-tomany distribution”). IPv 6 multicast addresses start with FF 00: : /8. After the first 8 bits there are 4 bits which represent the flag fields. Next 4 bits indicate the scope of the IPv 6 network for which the multicast traffic is intended. Routers use the scope field to determine whether multicast traffic can be forwarded. The remaining 112 bits of the address make up the multicast Group ID. Some of the possible scope values are: 1 – interface-local 2 – link-local 4 – admin-local 5 – site-local 8 – organization-local E – global For example, the addresses that begin with FF 02: : /16 are multicast addresses intended to stay on the local link. http//stu-ccna. com/ipv 6 -multicast-addresses/
WHAT COMMANDS ARE USED TO APPLY INITIAL ROUTER CONFIGURATIONS? 1. Configure Cerminal 2. Hostname Name 3. Enable Secret Password 4. No IP Domain-Lookup http: //www. pearsonitcertification. com/articles /article. aspx? p=1829346
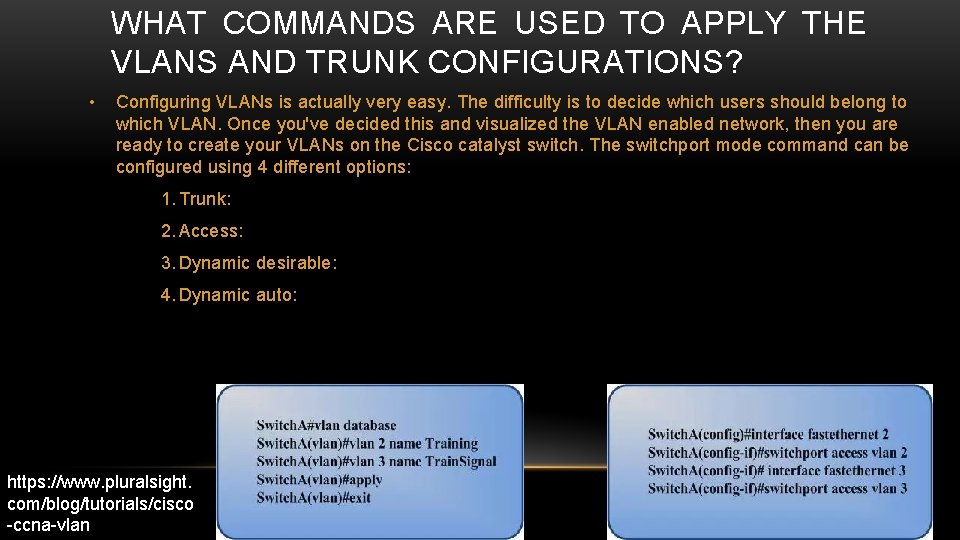
WHAT COMMANDS ARE USED TO APPLY THE VLANS AND TRUNK CONFIGURATIONS? • Configuring VLANs is actually very easy. The difficulty is to decide which users should belong to which VLAN. Once you've decided this and visualized the VLAN enabled network, then you are ready to create your VLANs on the Cisco catalyst switch. The switchport mode command can be configured using 4 different options: 1. Trunk: 2. Access: 3. Dynamic desirable: 4. Dynamic auto: https: //www. pluralsight. com/blog/tutorials/cisco -ccna-vlan
A OVERALL DESCRIPTION OF AN IPV 4 BASED WAN • IPv 4 is the 4 th version of a Internet Protocol. • IPv 4 uses 32 -bit addresses for network communication in five classes A-E.
A OVERALL DESCRIPTION OF AN IPV 4 BASED WAN CONT • The IP address identifies a system location on the Network. • Each IP address includes a network ID and a host ID. • The network ID identifies the system that are located on the physical network IP routers. • The Host ID identifies a workstation, servers, routers or other TCP/IP host within the network
HOW TO CALCULATE A SUBNET ID AND SUBNET BROADCAST ADDRESS • Classful network total bits is 8. Sub-net mask can be 0, 128, 192, 224, 240, 248, 252, 254 and 255. • Subnet mask 255 is default, so it'll not consider for subnet masking. • Number of bits left for host = m = Tb - n = 8 - 3 = 5
HOW TO CALCULATE A SUBNET ID AND SUBNET BROADCAST ADDRESS CONT • Now you have to calculate "Number of subnets" = 2 n and "Value of last bit used for subnet masking"(Δ) = 2 m. • Now you can find previously calculated number of subnets by separating subnets each having "Value of last bit used for subnet masking" or Δ addresses. The 8 subnets (Each of them has 32 addresses.
A CLEAR EXPLANATION OF HOW TO TEST FOR OVERLAP IN A VLSM SCHEME AND TROUBLESHOOT ISSUES THAT MAY ARISE FROM THE OVERLAP • VLSM Overlapping • Calculate the subnet ID • Scan the list from top to bottom • Analyze each subnet.
STEP-BY-STEP ILLUSTRATION OF HOW TO ADD A NEW SUBNET • Pick the subnet mask (prefix length). • Calculate all possible subnet numbers. • Make a list of existing subnet IDs. • Compare the existing subnets. • Choose the new subnet ID

STEP BY STEP • Describe ACLs NAT and PATS • Secure networks • Securing your cisco router • Troubleshooting tools
DESCRIBE ACL’S (ACCESS CONTROL LIST ) • ACL’S Access control list is a list of permission attached to a system object
NETWORK ADDRESS TRANSLATION (NAT) • NAT have three main purposes : 1. Provides a firewall to hide internal IP addresses 2. Give the company the ability to use more internal ip addresses 3. Enables a company to combine and use multiple ip addresses connections into a single internet connection.
PORT ADDRESS TRANSLATION (PAT) • PAT is a extension of NAT that’s allows multiple devices that are connected to a single LAN that is connected to a public IP address.
SECURING THE NETWORK • Network Intrusion detection • Two-Factor Authentication • Network access control
SECURING YOUR ROUTER 1. 2. 3. Control access to your router : apply rules to restrict external access 4. 5. Access-list 110 deny ip 192. 168. 16. 10 255. 0 any 6. 7. 8. 9. Access-list 110 deny udp any eq snmp Access-list 110 deny tcp any host $yourswitchip> Restrict telnet access: telnet is not the best but if you have to use it always use SSH it has to restricted from any access Restrict snmp: should always be restricted , to avoid malicious spyware from getting information on your network. Encrypt all passwords Enable secret $yournewpassword > Disable all unused services

TROUBLESHOOTING TOOLS • Cisco view • Internetwork performance monitor • Trafficdirector rmon application • Vlandirector switch management application • Network monitors • Network analyzers • Router diagnostic commands • Third party troubleshooting tools • Cisco network management tools
CONCLUSION This training guideline help me to understand importance of how IPv 4 has done a great job in the 1990 s and continuing through the 2000 s but with the addresses coming to near deletion its time for change and how IPv 6 is going to change the future of protocols with over 10, 000, 000, 000 times more addresses available. The importance of ACL’s NAT and PAT for network security and also doing step by step configuration on switches or routers, creating subnets id and subnet broadcast addresses.
REFERENCES • Odom, W. (2016) “CCENT/CCNA ICND! 100 -105 Official Cert Guide”. Indianapolis. Cisco Press. • https: //www. link-labs. com/blog/why-ipv 6 -is-important-for-internet-of-things • https: //docs. oracle. com/cd/E 19253 -01/816 -4554/ipv 6 -overview-24/index. html • https: //serverfault. com/questions/279482/what-is-the-difference-between-unicast-anycastbroadcast-and-multicast-traffic • http: //study-ccna. com/ipv 6 -multicast-addresses/ • http: //www. pearsonitcertification. com/articles/article. aspx? p=1829346 • https: //www. pluralsight. com/blog/tutorials/cisco-ccna-vlan • https: //www. techopedia. com/definition/5367/internet- protocol-version-4 -ipv 4
- Slides: 24