SSH Keys Security Asset or Liability Securing SSH

// SSH Keys: Security Asset or Liability? Securing SSH Keys in Today’s Enterprise Marty Milbert Global Principal Architect Venafi 1 // © 2019 Venafi. All Rights Reserved.

// Agenda 1 What Is SSH And Where Is It Used? 2 How We Misunderstand Its Importance 3 The Four Big SSH Risks You Should Address First 4 How To Get Started 2 // © 2019 Venafi. All Rights Reserved.
// Two Actors on a Network: Identity and Access People Machines Usernames and Passwords Machine Identities Interactive Automated Secure and Protect Identities – People and Machines 3 // © 2019 Venafi. All Rights Reserved.
// $8 B Annually on IAM We spend billions protecting usernames and passwords. Source: Marketsand. Markets. com. Identity & Access Management Market by Component, Organization Size, Deployment Type, Vertical, and Region - Global Forecast to 2021 February 2017. Report Code: TC 3138. But almost nothing protecting machine identities which secure our critical systems and data. 4 // © 2019 Venafi. All Rights Reserved.
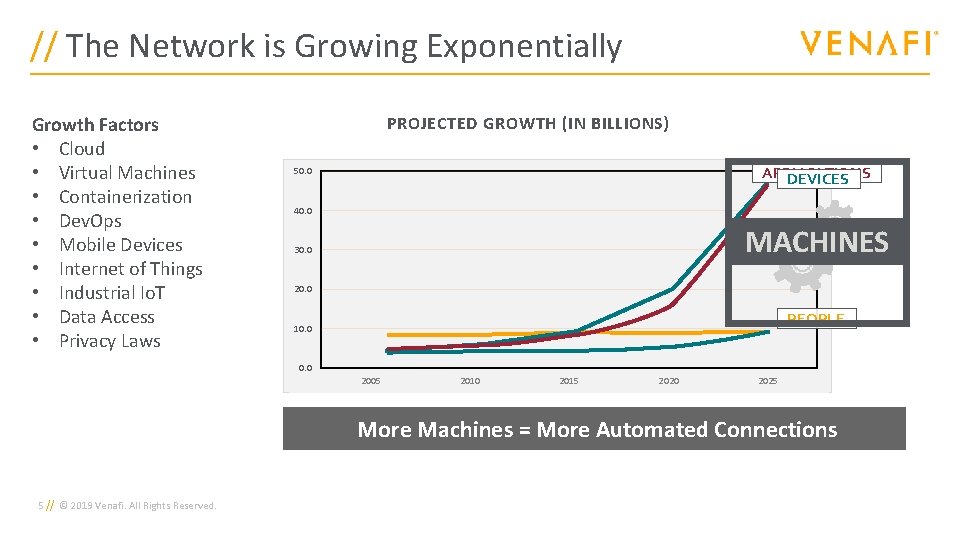
// The Network is Growing Exponentially Growth Factors • Cloud • Virtual Machines • Containerization • Dev. Ops • Mobile Devices • Internet of Things • Industrial Io. T • Data Access • Privacy Laws PROJECTED GROWTH (IN BILLIONS) APPLICATIONS DEVICES 300. 0 50. 0 250. 0 40. 0 MACHINES 200. 0 30. 0 150. 0 20. 0 100. 0 PEOPLE 10. 0 50. 0 2005 2010 2015 2020 2025 More Machines = More Automated Connections 5 // © 2019 Venafi. All Rights Reserved.
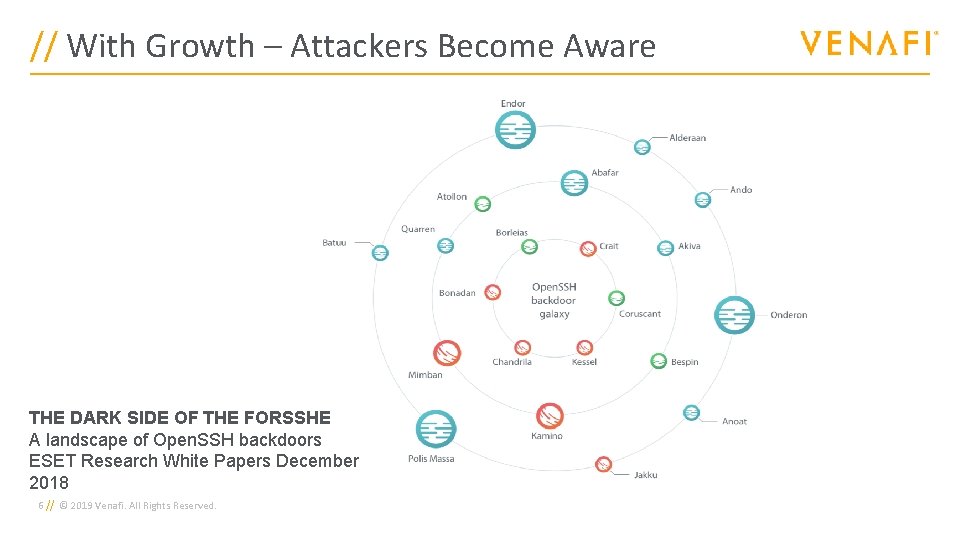
// With Growth – Attackers Become Aware THE DARK SIDE OF THE FORSSHE A landscape of Open. SSH backdoors ESET Research White Papers December 2018 6 // © 2019 Venafi. All Rights Reserved.
// Stories From the Trenches Plethora of Known Malware – All Based on Recompiled Open. SSH • • Endor 2010 = Logging & exfiltration of SSH activity, code obfuscation, and many variants. Bespin 2017 = Same as Endor plus encryption using hardcoded key Kamino 2012 = Remotely controlled via C&C, anti-logging feature, and data obfuscation Total of 21 different families (ESET THE DARK SIDE OF THE FORSSHE – December 2018) Operation Windigo (2014 – 2017) • • • 25, 000 unique servers compromised - multiple OS’s impacted Combination of rootkit Trojan (Ebury) with modified Open. SSH files Transported SSH data connecting through compromised system gets exfiltrated through DNS Go Malware (July 2019) • • • When discovering SSH ports, the malware will try default access keys After logon, malware leverages known hosts and moves laterally “https: //www. securityweek. com/cryptomining-campaign-targets-linux-servers-go-malware” 7 // © 2019 Venafi. All Rights Reserved.
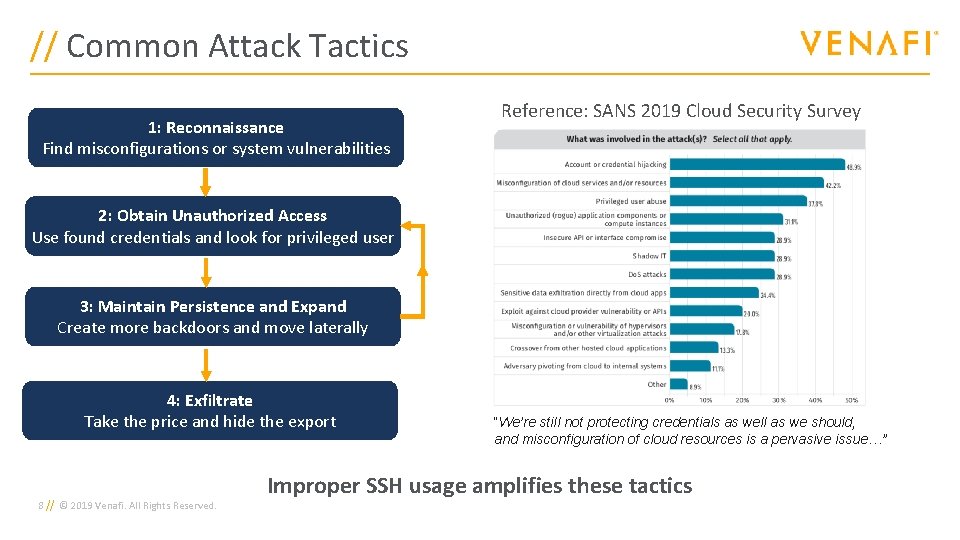
// Common Attack Tactics 1: Reconnaissance Find misconfigurations or system vulnerabilities Reference: SANS 2019 Cloud Security Survey 2: Obtain Unauthorized Access Use found credentials and look for privileged user 3: Maintain Persistence and Expand Create more backdoors and move laterally 4: Exfiltrate Take the price and hide the export 8 // © 2019 Venafi. All Rights Reserved. “We’re still not protecting credentials as well as we should, and misconfiguration of cloud resources is a pervasive issue…” Improper SSH usage amplifies these tactics
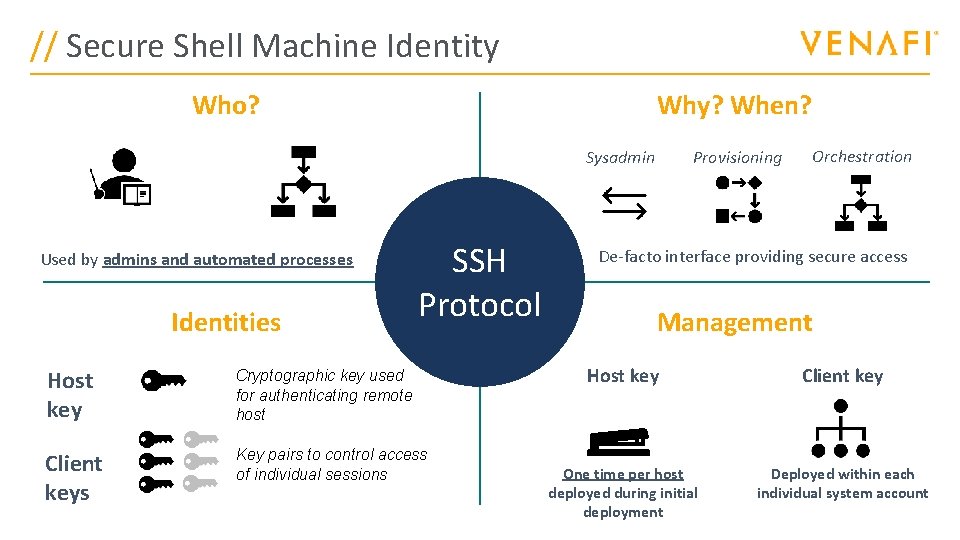
// Secure Shell Machine Identity Who? Why? When? Provisioning Sysadmin Used by admins and automated processes Identities SSH Protocol Host key Cryptographic key used for authenticating remote host Client keys // Key pairs to control access of individual sessions Orchestration De-facto interface providing secure access Management Host key Client key One time per host deployed during initial deployment Deployed within each individual system account

// Free ≠ Not Valuable Nobody owns it and it’s free | Easy to overlook its importance 10 // © 2019 Venafi. All Rights Reserved.

// SSH Study • Study by Dimensional Research • Surveyed over 400 • IT and security professionals with in-depth knowledge of SSH • From the U. S. , U. K. and Germany • Goal: Measure how well organizations implement security controls for SSH keys 11 // © 2019 Venafi. All Rights Reserved. The Result? Most organizations are underprepared to protect against SSH-based attacks
// Distributed Management For over half (59%), Most or all admins manage SSH for the systems they control Study by Dimensional Research n = 411 IT and security professionals with in-depth knowledge of SSH 12 // © 2019 Venafi. All Rights Reserved.
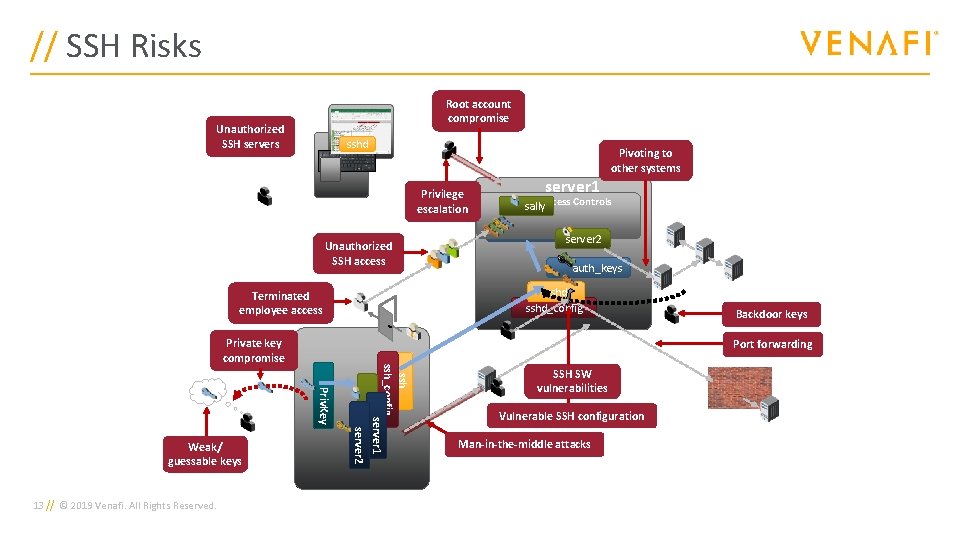
// SSH Risks Root account compromise Unauthorized SSH servers sshd Privilege escalation Unauthorized SSH access ssh_config server 1 sally server 2 13 // © 2019 Venafi. All Rights Reserved. auth_keys server 2 auth_keys Backdoor keys Port forwarding Priv. Key Weak/ guessable keys PAMsally & Access Controls sshd_config Terminated employee access Private key compromise server 1 Pivoting to other systems SSH SW vulnerabilities Vulnerable SSH configuration Man-in-the-middle attacks
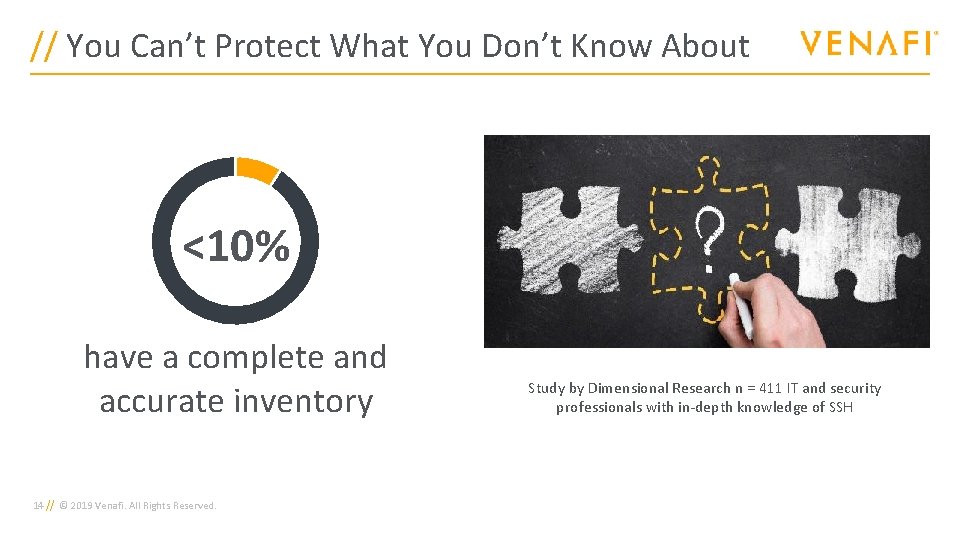
// You Can’t Protect What You Don’t Know About <10% have a complete and accurate inventory 14 // © 2019 Venafi. All Rights Reserved. Study by Dimensional Research n = 411 IT and security professionals with in-depth knowledge of SSH
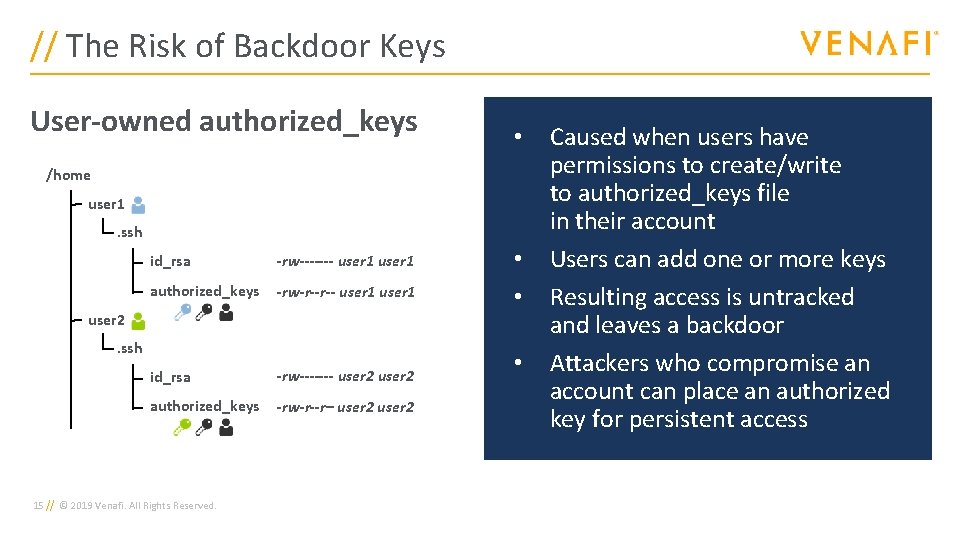
// The Risk of Backdoor Keys User-owned authorized_keys • /home user 1. ssh id_rsa -rw------- user 1 authorized_keys -rw-r--r-- user 1 id_rsa -rw------- user 2 authorized_keys -rw-r--r– user 2. ssh 15 // © 2019 Venafi. All Rights Reserved. • • • Caused when users have permissions to create/write to authorized_keys file in their account Users can add one or more keys Resulting access is untracked and leaves a backdoor Attackers who compromise an account can place an authorized key for persistent access
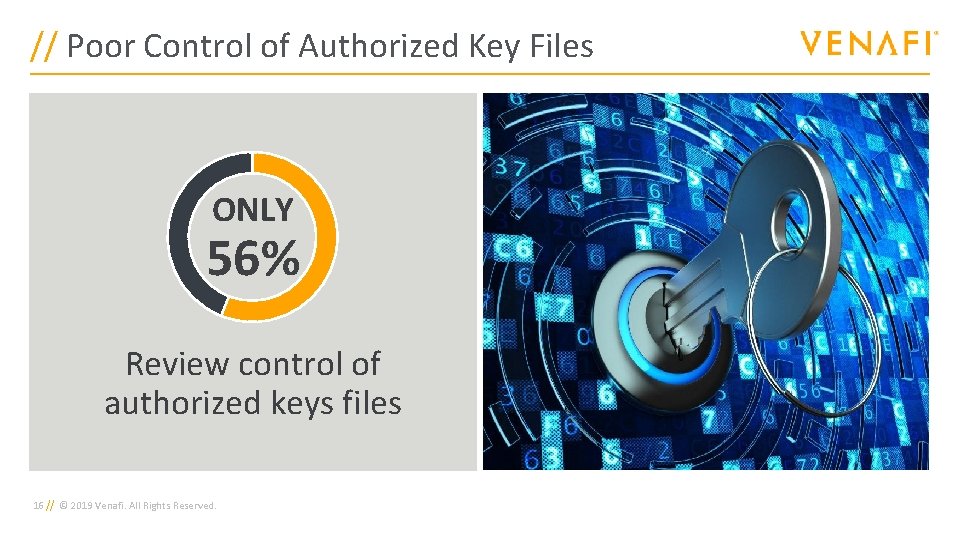
// Poor Control of Authorized Key Files ONLY 56% Review control of authorized keys files 16 // © 2019 Venafi. All Rights Reserved.
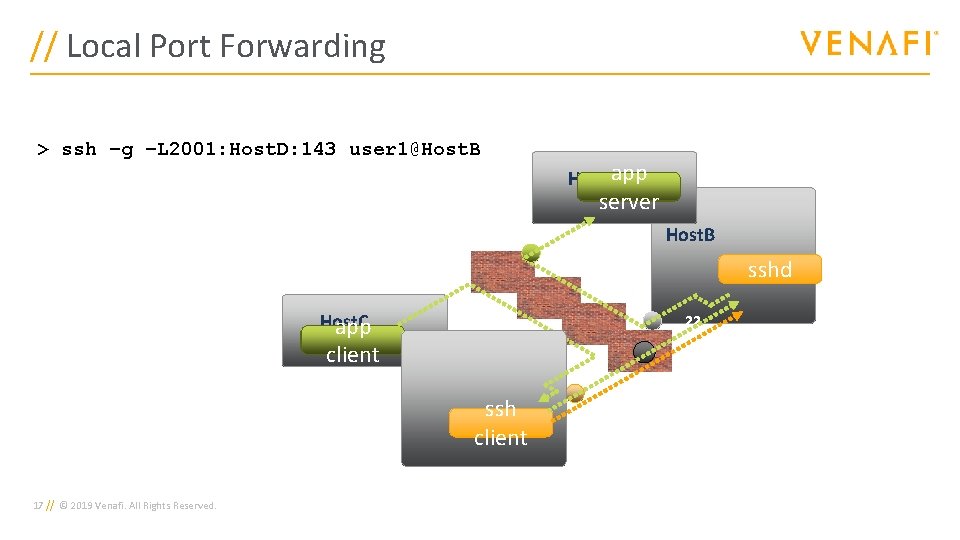
// Local Port Forwarding > ssh –g user 1@Host. B –L 2001: Host. D: 143 user 1@Host. B Host. Dapp server 143 Host. B sshd Host. C app client 22 2001 Host. A ssh client 17 // © 2019 Venafi. All Rights Reserved.
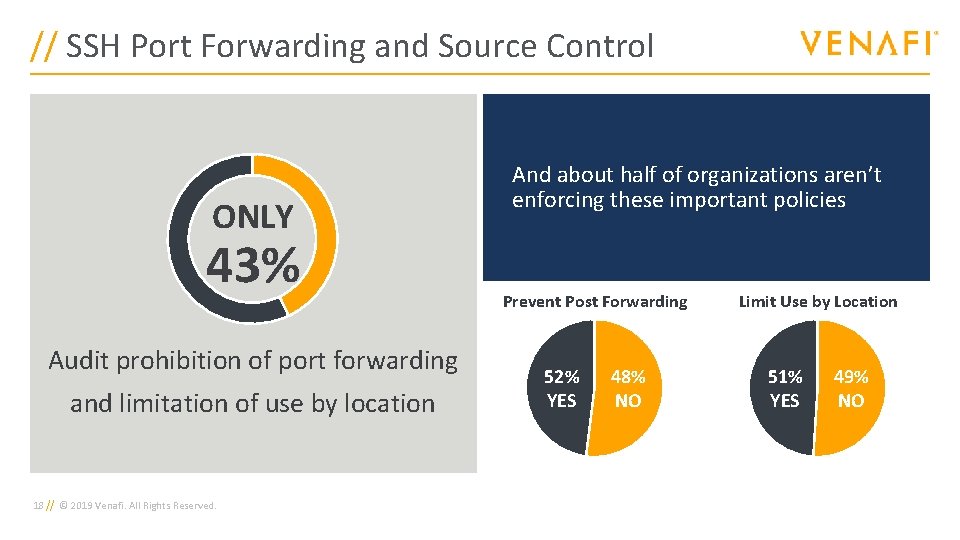
// SSH Port Forwarding and Source Control ONLY 43% Audit prohibition of port forwarding and limitation of use by location 18 // © 2019 Venafi. All Rights Reserved. And about half of organizations aren’t enforcing these important policies Prevent Post Forwarding 52% YES 48% NO Limit Use by Location 51% YES 49% NO
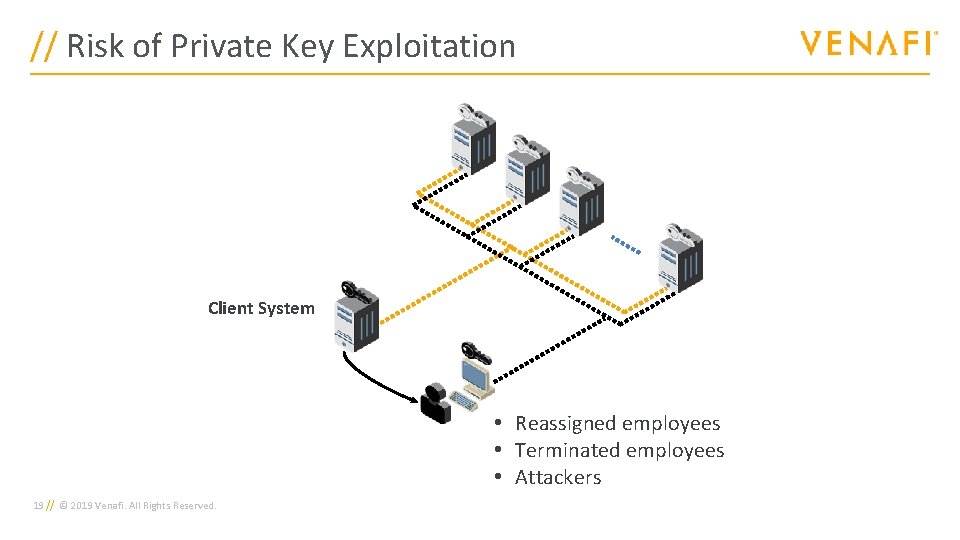
// Risk of Private Key Exploitation Client System • Reassigned employees • Terminated employees • Attackers 19 // © 2019 Venafi. All Rights Reserved.
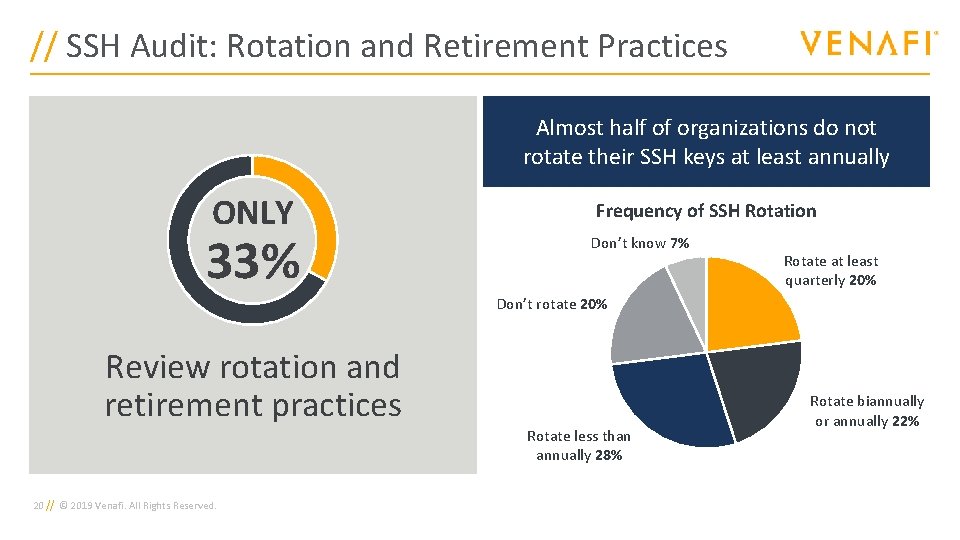
// SSH Audit: Rotation and Retirement Practices Almost half of organizations do not rotate their SSH keys at least annually ONLY 33% Frequency of SSH Rotation Don’t know 7% Rotate at least quarterly 20% Don’t rotate 20% Review rotation and retirement practices 20 // © 2019 Venafi. All Rights Reserved. Rotate less than annually 28% Rotate biannually or annually 22%
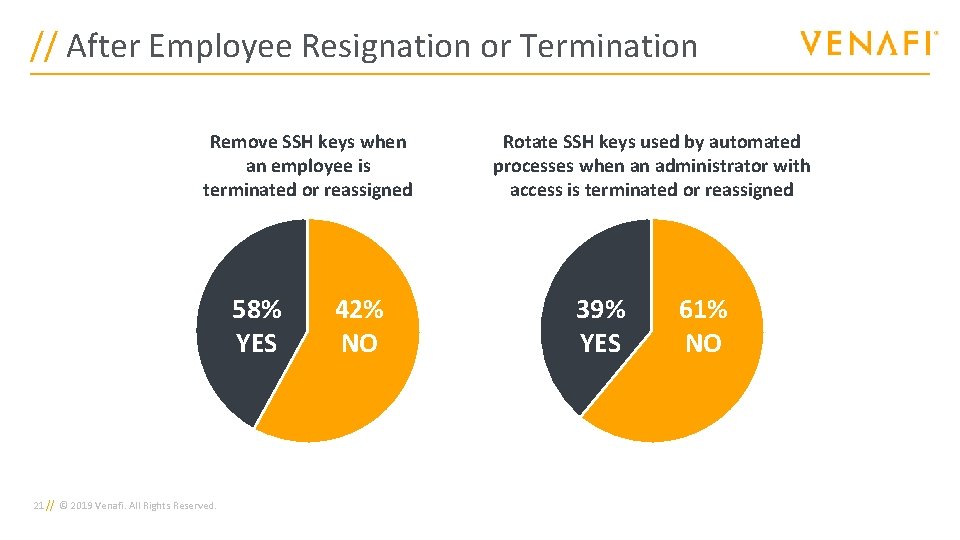
// After Employee Resignation or Termination Remove SSH keys when an employee is terminated or reassigned 58% YES 21 // © 2019 Venafi. All Rights Reserved. 42% NO Rotate SSH keys used by automated processes when an administrator with access is terminated or reassigned 39% YES 61% NO
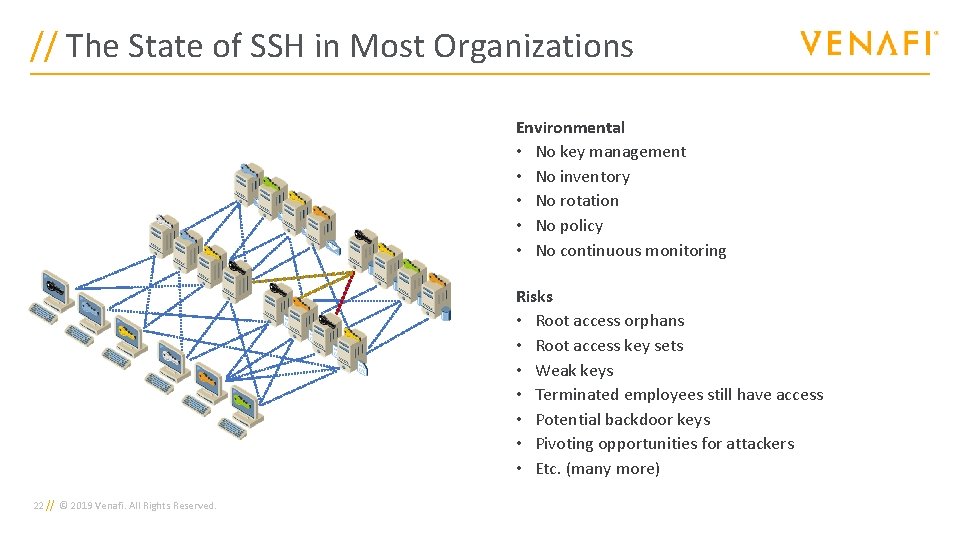
// The State of SSH in Most Organizations Environmental • No key management • No inventory • No rotation • No policy • No continuous monitoring Risks • Root access orphans • Root access key sets • Weak keys • Terminated employees still have access • Potential backdoor keys • Pivoting opportunities for attackers • Etc. (many more) 22 // © 2019 Venafi. All Rights Reserved.
// Privileged Access Management Isn’t Enough PAM covers the interactive access of people but doesn’t focus on machine access 23 // © 2019 Venafi. All Rights Reserved.
// Summary • SSH environment provides privileged access to most systems • It should be centrally controlled • Hygiene policies should be analogous to user identities Without centralized SSH key management • Risk of breach • Risk of non-compliance with PCI-DSS, HIPAA, etc. • Pivoting risk exacerbated 24 // © 2019 Venafi. All Rights Reserved.
// 5 Things You Should Begin Immediately 1. Get and maintain an accurate inventory 2. Control permission of authorized key files 3. Prevent port forwarding and require source control 4. Rotate keys and review entitlements regularly 5. Audit for compliance 25 // © 2019 Venafi. All Rights Reserved.

// Thank You Marty Milbert Global Principal Architect Venafi 26 // © 2019 Venafi. All Rights Reserved.
- Slides: 26