SizeEfficient Digital Signatures with Appendix by Truncating Unnecessarily
Size-Efficient Digital Signatures with Appendix by Truncating Unnecessarily Long Hashcode Jinwoo LEE ┼ and Pil Joong LEE Information security lab. , POSTECH • • WAIS 2015 Session 5: Privacy 2014 -1 -10
� Introduction Digital Signature Mechanism with Appendix (DSw. A) ISO/IEC 14888 -3: DSw. A Based on Discrete Logarithm Contribution Information Security Lab. POSTECH Introduction: 2014 -1 -10
Digital Signature Mechanism with Appendix (DSw. A) The notion of digital signature is an alternative for handwritten signatures in digital world This concept was introduced by ‘Diffie, W. , Hellman, , M. E. : New directions in cryptography, IEEE Trans. Inform. Theory, 1976’ Each user can publish a public key, &keep a private key Private key is used for producing signatures Public key is used for verifying signatures Two types of digital signature mechanisms: Digital signature mechanism with appendix (DSw. A) Whole message has to be stored &/or transmitted along with the signature Digital signature mechanism giving message recovery Verification process reveals all or part of the message Information Security Lab. POSTECH Introduction: 2014 -1 -10
ISO/IEC 14888 -3: DSw. A Based on Discrete Logarithm There are many DSw. A which is constructed based on the Discrete Logarithm Problem (DLP) ISO/IEC(International Organization for Standardization / International Electrotechnical Commission) maintains a standard for DSw. A based on DLP ISO/IEC 14888 -3 “Information technology – Security techniques – Digital signatures with appendix – Part 3: Discrete logarithm based mechanisms” DSw. A based on DLP has a digital signature ∑ ( = (R, S) ), which is appended after the message The length of R and S could be different Information Security Lab. POSTECH Introduction: 2014 -1 -10
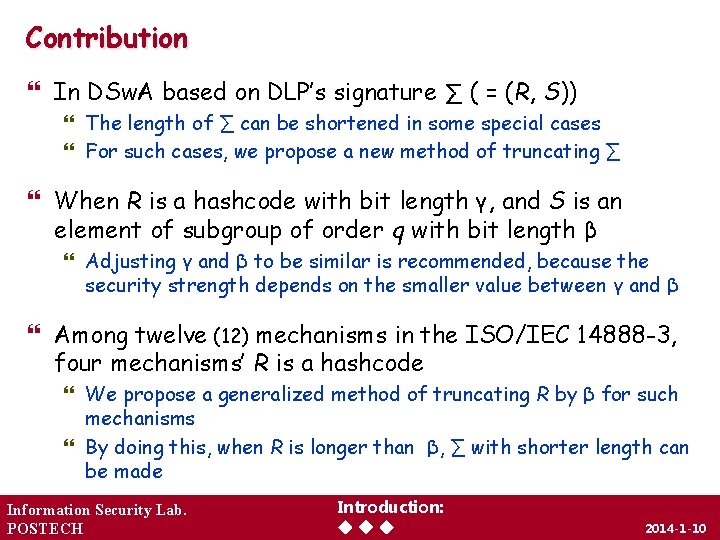
Contribution In DSw. A based on DLP’s signature ∑ ( = (R, S)) The length of ∑ can be shortened in some special cases For such cases, we propose a new method of truncating ∑ When R is a hashcode with bit length γ, and S is an element of subgroup of order q with bit length β Adjusting γ and β to be similar is recommended, because the security strength depends on the smaller value between γ and β Among twelve (12) mechanisms in the ISO/IEC 14888 -3, four mechanisms’ R is a hashcode We propose a generalized method of truncating R by β for such mechanisms By doing this, when R is longer than β, ∑ with shorter length can be made Information Security Lab. POSTECH Introduction: 2014 -1 -10
� Preliminaries ISO/IEC 10118 -3: Hash functions KCDSA and SDSA Information Security Lab. POSTECH Preliminaries: 2014 -1 -10
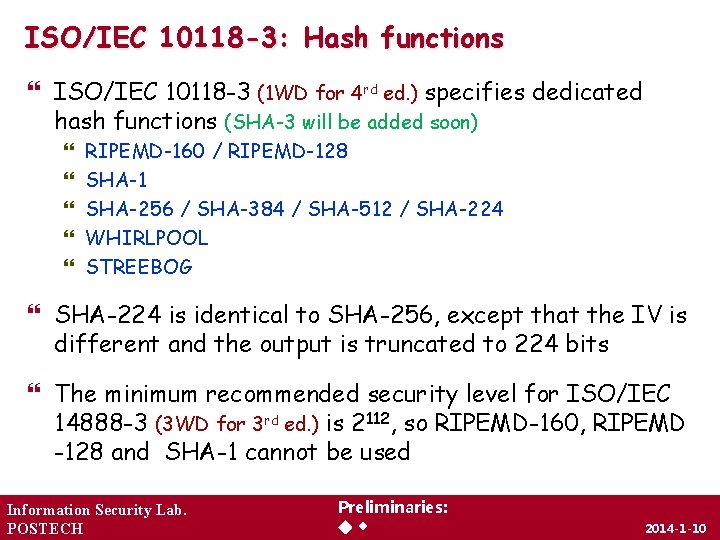
ISO/IEC 10118 -3: Hash functions ISO/IEC 10118 -3 (1 WD for 4 rd ed. ) specifies dedicated hash functions (SHA-3 will be added soon) RIPEMD-160 / RIPEMD-128 SHA-1 SHA-256 / SHA-384 / SHA-512 / SHA-224 WHIRLPOOL STREEBOG SHA-224 is identical to SHA-256, except that the IV is different and the output is truncated to 224 bits The minimum recommended security level for ISO/IEC 14888 -3 (3 WD for 3 rd ed. ) is 2112, so RIPEMD-160, RIPEMD -128 and SHA-1 cannot be used Information Security Lab. POSTECH Preliminaries: 2014 -1 -10
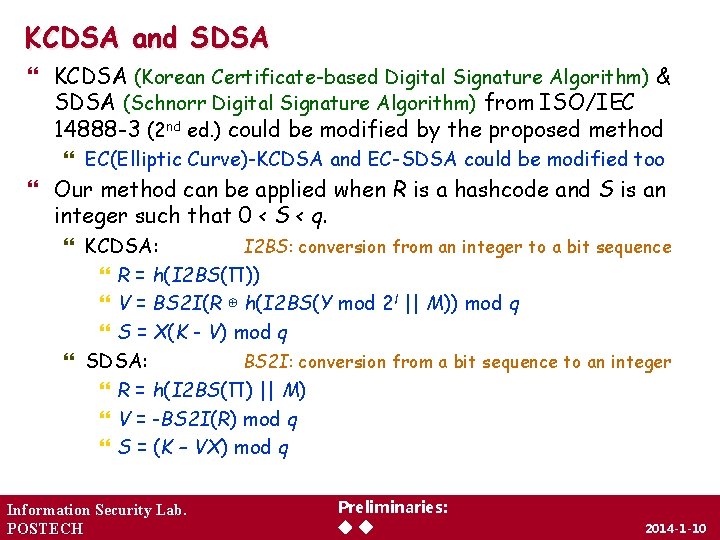
KCDSA and SDSA KCDSA (Korean Certificate-based Digital Signature Algorithm) & SDSA (Schnorr Digital Signature Algorithm) from ISO/IEC 14888 -3 (2 nd ed. ) could be modified by the proposed method EC(Elliptic Curve)-KCDSA and EC-SDSA could be modified too Our method can be applied when R is a hashcode and S is an integer such that 0 < S < q. KCDSA: I 2 BS: conversion from an integer to a bit sequence R = h(I 2 BS(Π)) V = BS 2 I(R ⊕ h(I 2 BS(Y mod 2 l || M)) mod q S = X(K - V) mod q SDSA: BS 2 I: conversion from a bit sequence to an integer R = h(I 2 BS(Π) || M) V = -BS 2 I(R) mod q S = (K – VX) mod q Information Security Lab. POSTECH Preliminaries: 2014 -1 -10
� Proposed scheme Construction Modified KCDSA Modified SDSA Information Security Lab. POSTECH Proposed scheme: 2014 -1 -10
Construction When R is a hashcode of length γ and S is an integer of length β: If γ is longer than β, R is truncated by β By doing this truncation, signature ∑ with shorter length can be made without loss of any security strength The security of the proposed method is fine if the hash function used does not lose its security when truncated If the proposed method is applied, length of ∑ is reduced from γ + β to 2β Applying the method to a mechanism in which R is a hashcode of SHA-256 and S is an integer of 224 -bit results in a visible reduction of the length of the Π from 480 -bit to 448 -bit Information Security Lab. POSTECH Proposed scheme: 2014 -1 -10
Modified KCDSA When computing R (= h(I 2 BS(Π))), If γ is longer than β, then the computation of R is replaced by R = I 2 BS(BS 2 I(h(I 2 BS(Π))) mod 2β). Here, mod 2β is used for truncating R by least significant β bits When computing V (= BS 2 I(R ⊕ H) mod q), where H = h(Y’ || M) is the hashcode of the concatenation of Y’ = I 2 BS(Y mod 2 l) and message M, if γ is longer than β, then the computation of H is replaced by H = I 2 BS(BS 2 I(h(Y’ || M)) mod 2β) In the verification process, R and H are computed by the same way Information Security Lab. POSTECH Proposed scheme: 2014 -1 -10
Modified SDSA When computing R (= h(I 2 BS(Π) || M)), If γ is longer than β, then the computation of R is replaced by R = I 2 BS(BS 2 I(h(I 2 BS(Π) || M)) mod 2β). Here, mod 2β is used for truncating R by least significant β bits (For the SDSA, R is not used to generate other variables such as V of KCDSA) In the verification process, R is computed by the same way Information Security Lab. POSTECH Proposed scheme: 2014 -1 -10
� Security Analysis General Case ISO/IEC 10118 -3: Hash functions Information Security Lab. POSTECH Security Analysis: 2014 -1 -10
General Case For the modified DSw. A scheme to which our proposed method is applied to be safe Truncation of the hashcode should not have any side effects rather than reducing its length To the best of our knowledge, there is no proof for now Not every hash function is free from the side effects of truncation SHA-0 is easily broken through near-collisions when truncated. (Biham, E. , Chen, R. : Near-collisions of SHA-0. Advances in Cryptography – CRYPTO 2004, 2004) On the other hand, the hash functions we considered are all safe from near-collisions Information Security Lab. POSTECH Security Analysis: 2014 -1 -10
ISO/IEC 10118 -3: Hash functions In ISO/IEC 10118 -3, the output for the hash functions is the hashcode which is derived by taking the leftmost LH (length of a hashcode) bits of the final output string from the last round function This means that a truncated hash function is allowed in the ISO/IEC specification Therefore, as far as the hash functions from ISO/IEC 10118 -3 is used, there is no security problem occurred by truncating the hashcode Information Security Lab. POSTECH Security Analysis: 2014 -1 -10
� Conclusion We proposed a general method for reducing the size of ∑ (= (R, S)) By truncating R when R is a hashcode of length γ And S is an integer of length β such that 0 < S < q For such cases it is preferred to adjust γ and β to be similar Because the security strength depends on the smaller value between γ and β If γ becomes longer than β, it makes longer ∑ without increasing any security strength However, in practice, only the hash function with longer output could be available In such cases our method can be useful to reduce the size of ∑ Information Security Lab. POSTECH Conclusion: 2014 -1 -10
�Thanks for your attention!! �Questions or Comments ? Information Security Lab. POSTECH 2014 -1 -10
- Slides: 17