SAML Integration Doug Bayer Director Windows Security Microsoft
SAML Integration Doug Bayer Director, Windows Security Microsoft Corporation dbayer@microsoft. com
Agenda u Overview of Microsoft authentication & authorization plans u Problem space v Our understanding of the scenarios u Our current approach u How could we use SAML? v Migration? v Integration? SAML August 27, 2001 S 2
Windows. NET Authentication Architecture u Windows. NET Authorization: Extending the Windows Model v v u Resource-Based Authorization: ACLs & Groups Application-Based Authorization: RBAC Making It All Secure SAML August 27, 2001 S 3
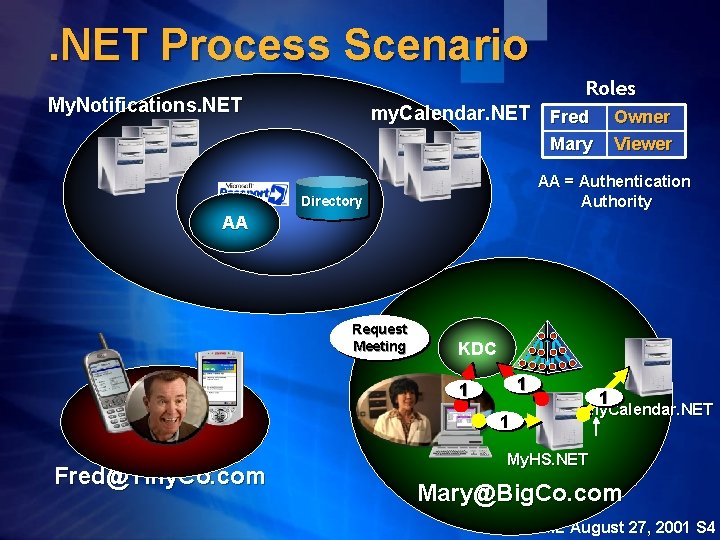
. NET Process Scenario Roles My. Notifications. NET my. Calendar. NET Fred Owner Viewer Mary AA = Authentication Authority Directory AA Request Meeting KDC 1 1 1 Fred@Tiny. Co. com 1 my. Calendar. NET My. HS. NET Mary@Big. Co. com SAML August 27, 2001 S 4
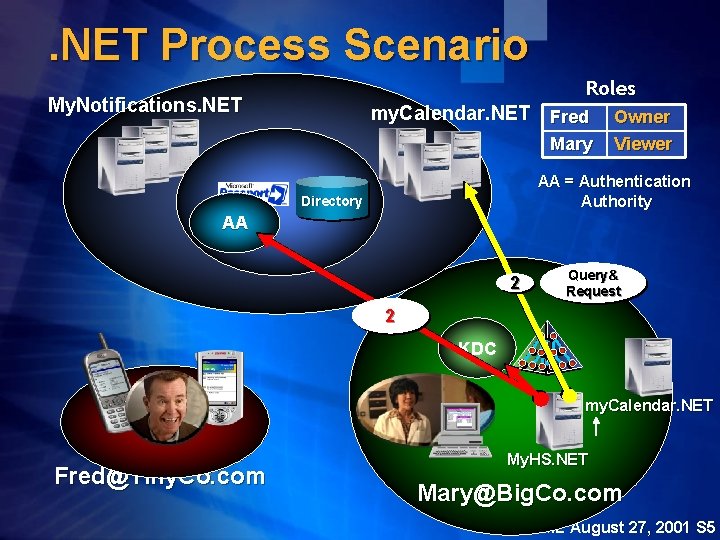
. NET Process Scenario Roles My. Notifications. NET my. Calendar. NET Fred Mary Owner Viewer AA = Authentication Authority Directory AA 2 Query& Request 2 KDC my. Calendar. NET Fred@Tiny. Co. com My. HS. NET Mary@Big. Co. com SAML August 27, 2001 S 5
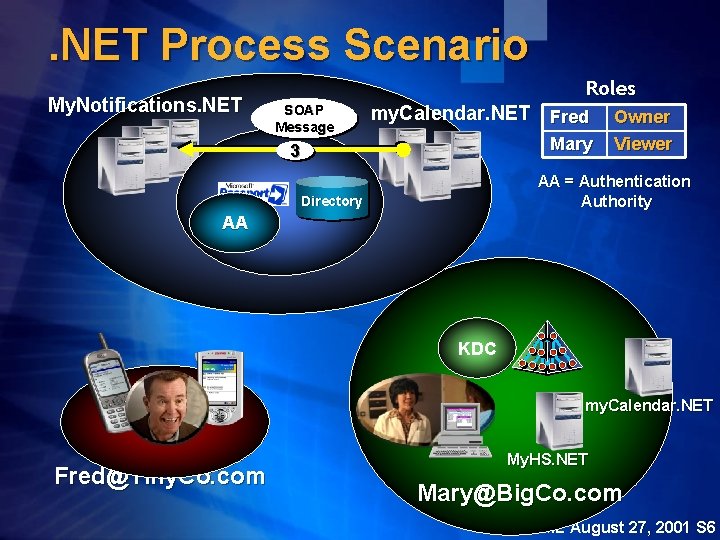
. NET Process Scenario My. Notifications. NET Roles SOAP Message my. Calendar. NET Fred Mary 3 Owner Viewer AA = Authentication Authority Directory AA KDC my. Calendar. NET Fred@Tiny. Co. com My. HS. NET Mary@Big. Co. com SAML August 27, 2001 S 6
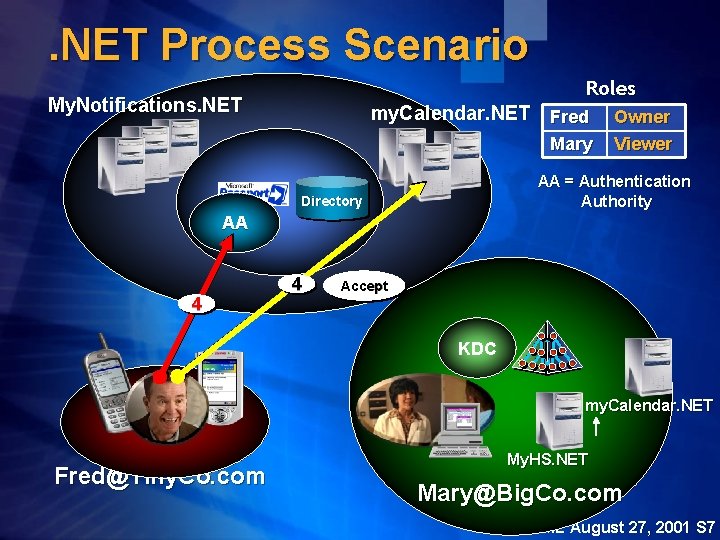
. NET Process Scenario Roles My. Notifications. NET my. Calendar. NET Fred Mary Owner Viewer AA = Authentication Authority Directory AA 4 4 Accept KDC my. Calendar. NET Fred@Tiny. Co. com My. HS. NET Mary@Big. Co. com SAML August 27, 2001 S 7
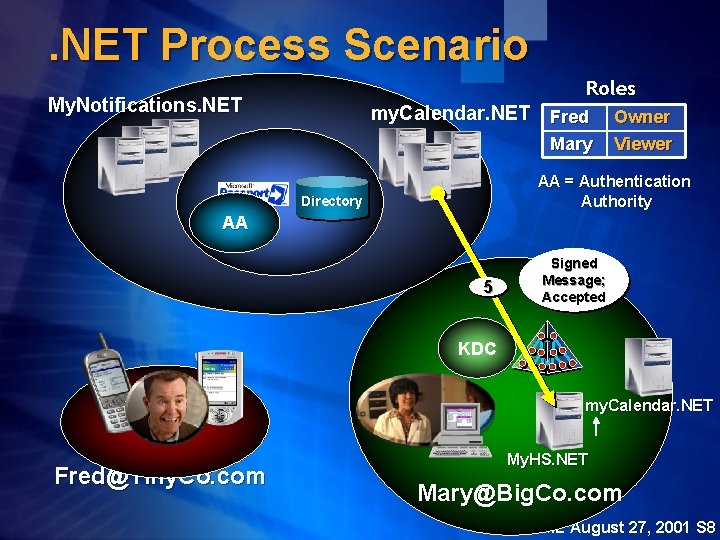
. NET Process Scenario Roles My. Notifications. NET my. Calendar. NET Fred Mary Owner Viewer AA = Authentication Authority Directory AA 5 Signed Message; Accepted KDC my. Calendar. NET Fred@Tiny. Co. com My. HS. NET Mary@Big. Co. com SAML August 27, 2001 S 8
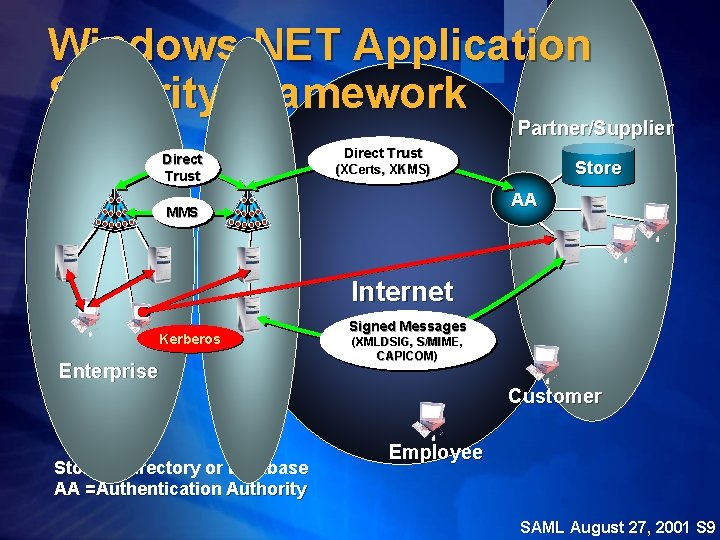
Windows. NET Application Security Framework Partner/Supplier Direct Trust Store (XCerts, XKMS) AA MMS Internet Signed Messages Kerberos Enterprise DMZ (XMLDSIG, S/MIME, CAPICOM) Customer Store = Directory or Database AA =Authentication Authority Employee SAML August 27, 2001 S 9
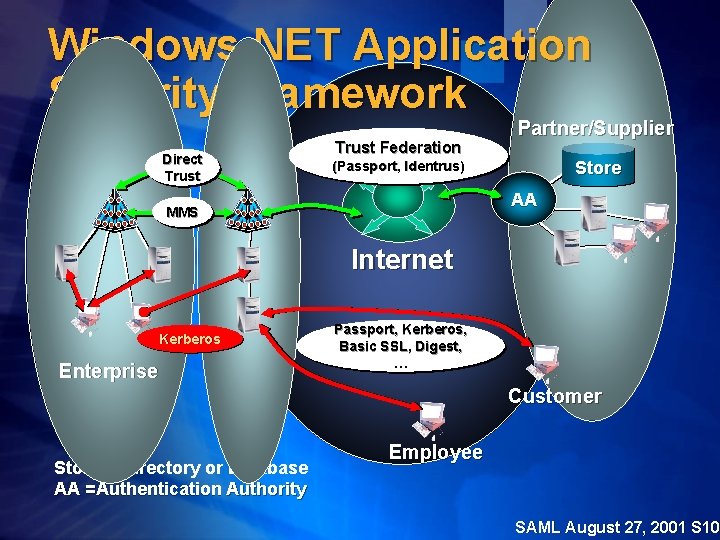
Windows. NET Application Security Framework Trust Federation Direct Trust Partner/Supplier Store (Passport, Identrus) AA MMS Internet Kerberos Enterprise DMZ Passport, Kerberos, Basic SSL, Digest, … Customer Store = Directory or Database AA =Authentication Authority Employee SAML August 27, 2001 S 10
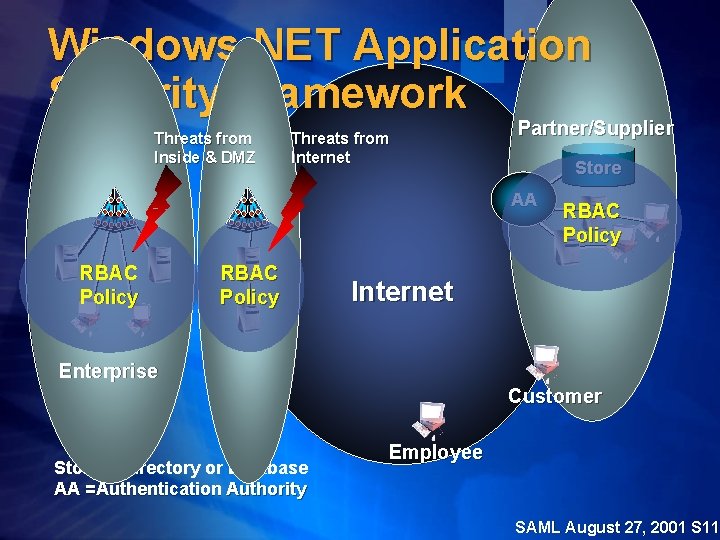
Windows. NET Application Security Framework Threats from Inside & DMZ Threats from Internet Partner/Supplier Store AA RBAC Policy Enterprise DMZ RBAC Policy Internet Customer Store = Directory or Database AA =Authentication Authority Employee SAML August 27, 2001 S 11
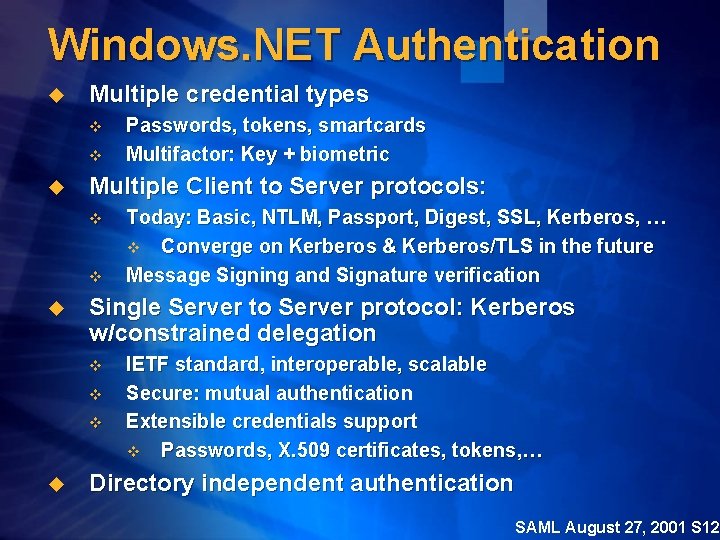
Windows. NET Authentication u Multiple credential types v v u Multiple Client to Server protocols: v v u Today: Basic, NTLM, Passport, Digest, SSL, Kerberos, … v Converge on Kerberos & Kerberos/TLS in the future Message Signing and Signature verification Single Server to Server protocol: Kerberos w/constrained delegation v v v u Passwords, tokens, smartcards Multifactor: Key + biometric IETF standard, interoperable, scalable Secure: mutual authentication Extensible credentials support v Passwords, X. 509 certificates, tokens, … Directory independent authentication SAML August 27, 2001 S 12
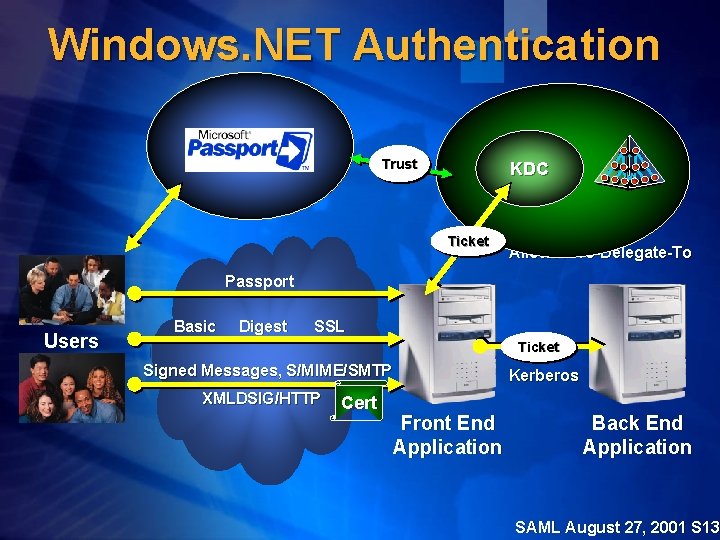
Windows. NET Authentication Trust KDC Ticket Verify Policy: Allowed-To-Delegate-To Passport Users Basic Digest SSL Ticket Signed Messages, S/MIME/SMTP XMLDSIG/HTTP Cert Kerberos Front End Application Back End Application SAML August 27, 2001 S 13
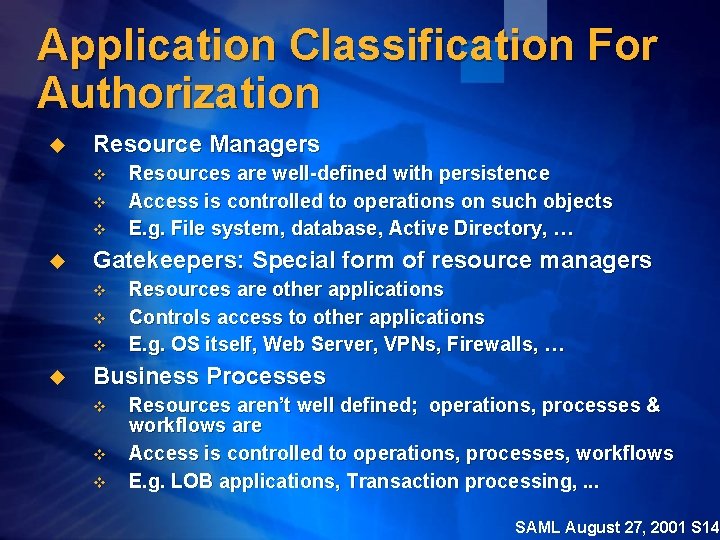
Application Classification For Authorization u Resource Managers v v v u Gatekeepers: Special form of resource managers v v v u Resources are well-defined with persistence Access is controlled to operations on such objects E. g. File system, database, Active Directory, … Resources are other applications Controls access to other applications E. g. OS itself, Web Server, VPNs, Firewalls, … Business Processes v v v Resources aren’t well defined; operations, processes & workflows are Access is controlled to operations, processes, workflows E. g. LOB applications, Transaction processing, . . . SAML August 27, 2001 S 14
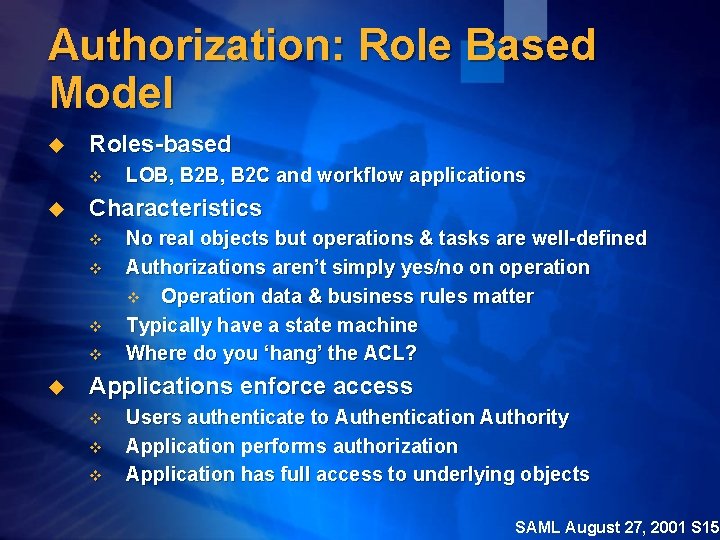
Authorization: Role Based Model u Roles-based v u Characteristics v v u LOB, B 2 C and workflow applications No real objects but operations & tasks are well-defined Authorizations aren’t simply yes/no on operation v Operation data & business rules matter Typically have a state machine Where do you ‘hang’ the ACL? Applications enforce access v v v Users authenticate to Authentication Authority Application performs authorization Application has full access to underlying objects SAML August 27, 2001 S 15
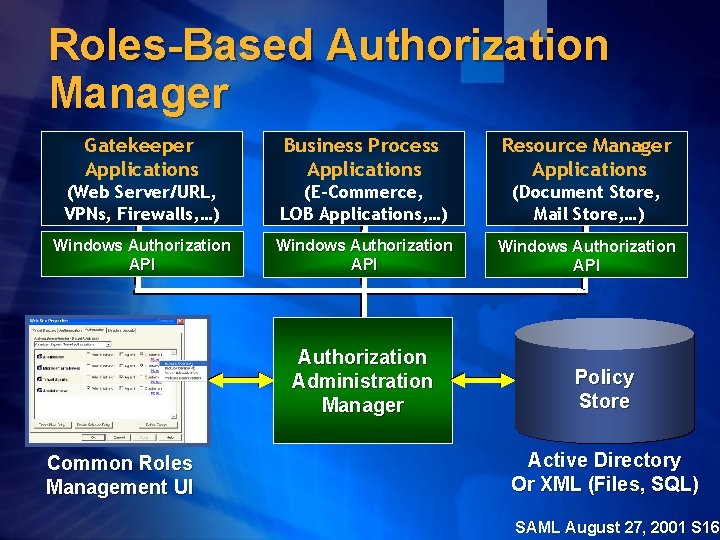
Roles-Based Authorization Manager Gatekeeper Applications Business Process Applications Resource Manager Applications (Web Server/URL, VPNs, Firewalls, …) (E-Commerce, LOB Applications, …) (Document Store, Mail Store, …) Windows Authorization API Authorization Administration Manager Common Roles Management UI Policy Store Active Directory Or XML (Files, SQL) SAML August 27, 2001 S 16
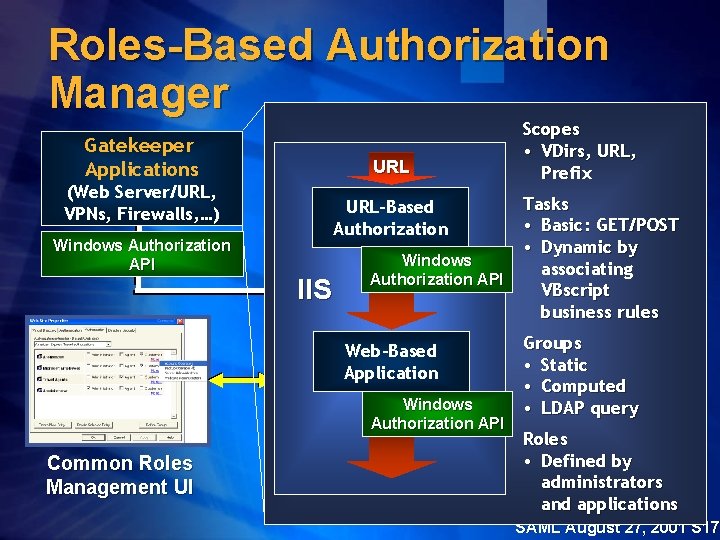
Roles-Based Authorization Manager Gatekeeper Applications URL (Web Server/URL, VPNs, Firewalls, …) URL-Based Authorization Windows Authorization API IIS Windows Authorization API Web-Based Application Windows Authorization API Common Roles Management UI Scopes • VDirs, URL, Prefix Tasks • Basic: GET/POST • Dynamic by associating VBscript business rules Groups • Static • Computed • LDAP query Roles • Defined by administrators and applications SAML August 27, 2001 S 17
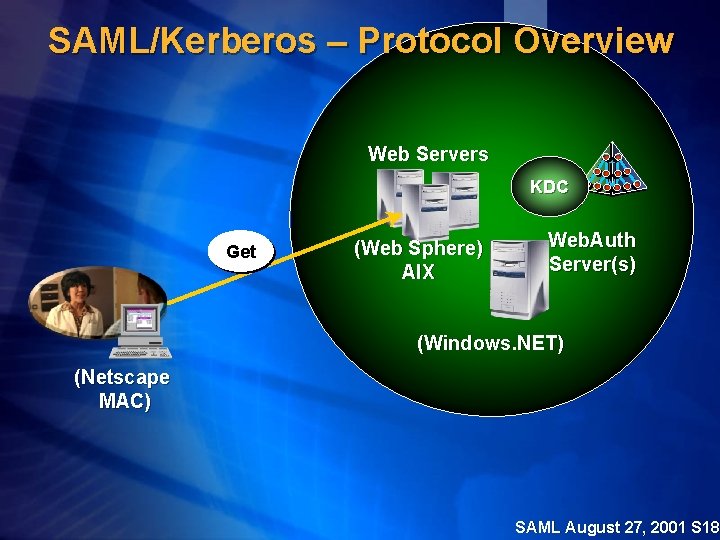
SAML/Kerberos – Protocol Overview Web Servers KDC Get (Web Sphere) AIX Web. Auth Server(s) (Windows. NET) (Netscape MAC) SAML August 27, 2001 S 18
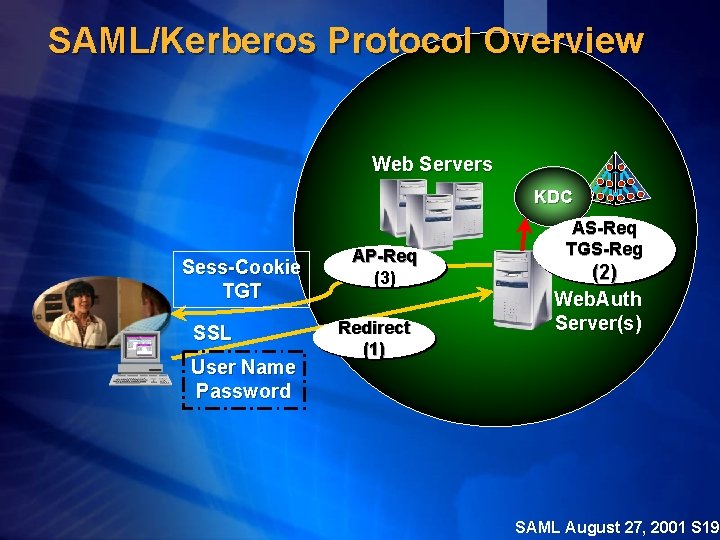
SAML/Kerberos Protocol Overview Web Servers KDC Sess-Cookie TGT SSL User Name Password AP-Req (3) Redirect (1) AS-Req TGS-Reg (2) Web. Auth Server(s) SAML August 27, 2001 S 19
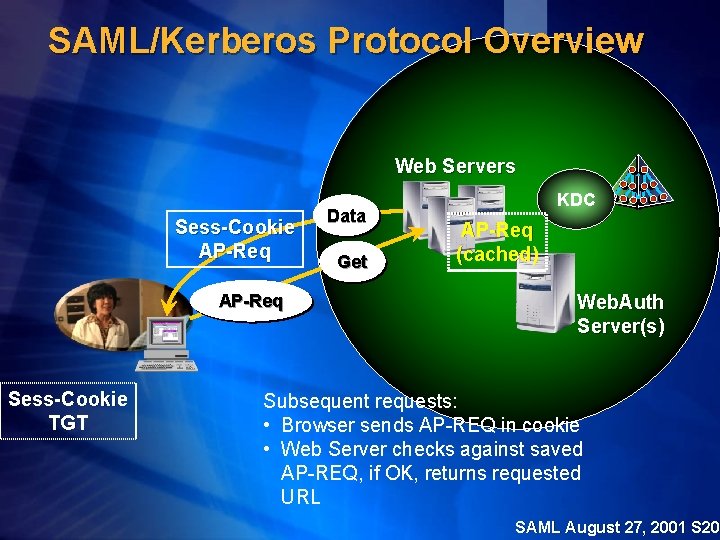
SAML/Kerberos Protocol Overview Web Servers Sess-Cookie AP-Req Sess-Cookie TGT Data Get KDC AP-Req (cached) Web. Auth Server(s) Subsequent requests: • Browser sends AP-REQ in cookie • Web Server checks against saved AP-REQ, if OK, returns requested URL SAML August 27, 2001 S 20
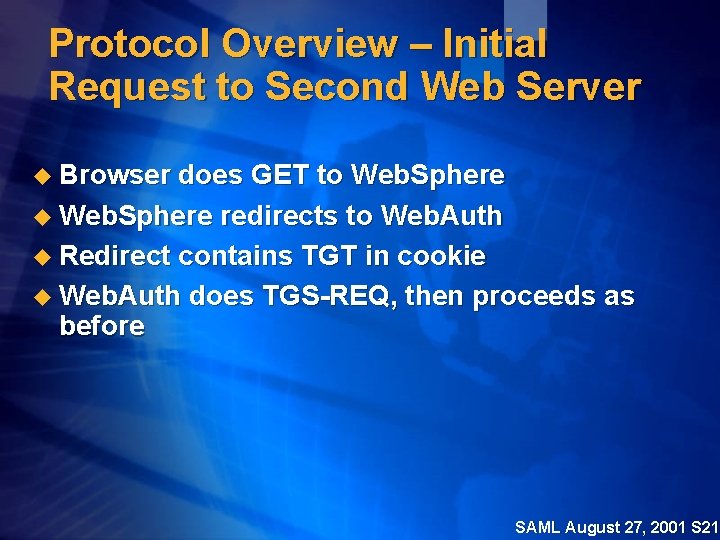
Protocol Overview – Initial Request to Second Web Server u Browser does GET to Web. Sphere u Web. Sphere redirects to Web. Auth u Redirect contains TGT in cookie u Web. Auth does TGS-REQ, then proceeds as before SAML August 27, 2001 S 21
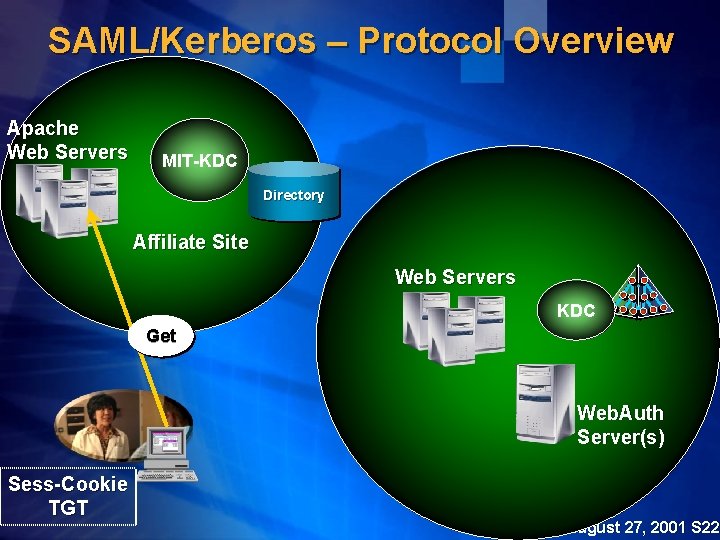
SAML/Kerberos – Protocol Overview Apache Web Servers MIT-KDC Directory Affiliate Site Web Servers KDC Get Web. Auth Server(s) Sess-Cookie TGT SAML August 27, 2001 S 22
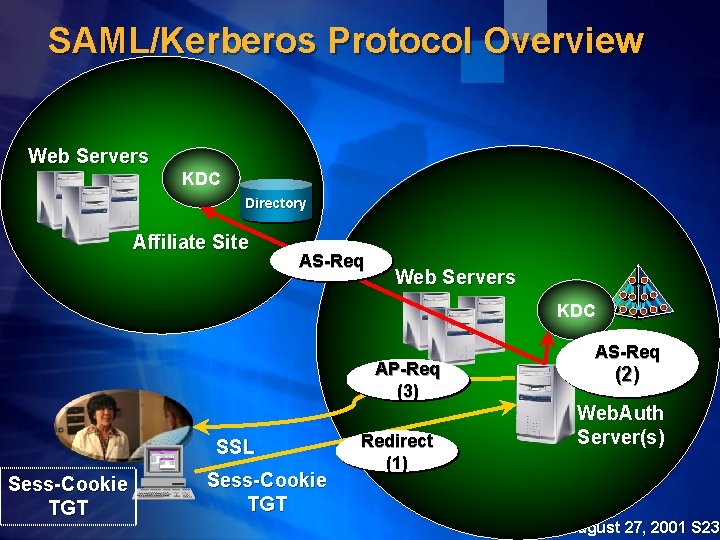
SAML/Kerberos Protocol Overview Web Servers KDC Directory Affiliate Site AS-Req Web Servers KDC AP-Req (3) SSL Sess-Cookie TGT Redirect (1) AS-Req (2) Web. Auth Server(s) SAML August 27, 2001 S 23
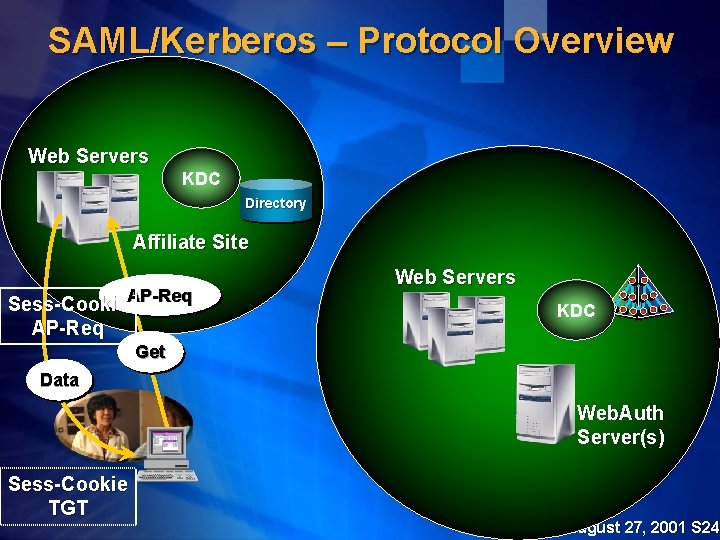
SAML/Kerberos – Protocol Overview Web Servers KDC Directory Affiliate Site Sess-Cookie. AP-Req Web Servers KDC Get Data Web. Auth Server(s) Sess-Cookie TGT SAML August 27, 2001 S 24
Questions? SAML August 27, 2001 S 25
- Slides: 25