RSA Conference 2004 SAML Interoperability Lab Agenda SAML
RSA Conference 2004 SAML Interoperability Lab
Agenda SAML and the OASIS SSTC SAML Timeline Brief SAML History SAML Interop Lab Q&A Demo
SAML and the OASIS SSTC SAML: Security Assertion Markup Language — A framework for the exchange of security-related information Developed within OASIS, a non-profit with a standards creation mission — http: //www. oasis-open. org The OASIS Security Services Technical Committee (SSTC) manages the development of SAML Any OASIS member can participate in the SSTC — ~35 active SSTC voting members (up from V 1. 1) — 20+ companies and organizations
Brief SAML History SAML is a success because its development was and continues to be driven by real business use cases — Web SSO — Authorization Services — Distributed Transactions Very strong “coopetition” Focus, focus! — Very careful prioritization of work items SAML solutions: — Save $$$ — Create new business opportunities
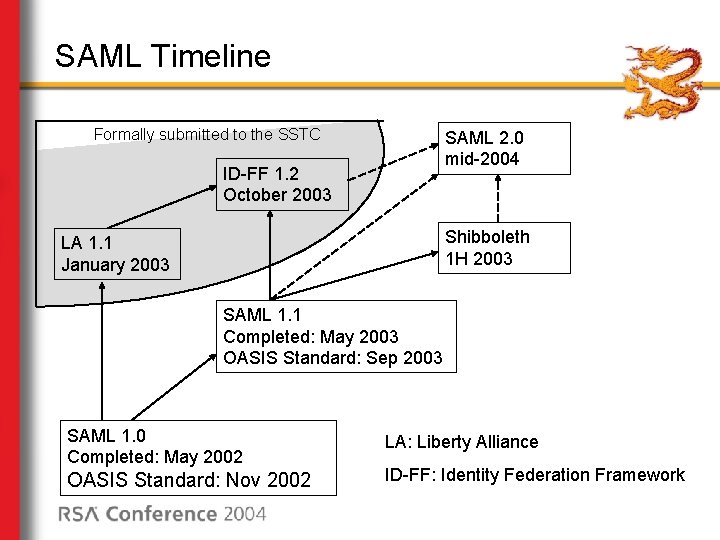
SAML Timeline Formally submitted to the SSTC SAML 2. 0 mid-2004 ID-FF 1. 2 October 2003 Shibboleth 1 H 2003 LA 1. 1 January 2003 SAML 1. 1 Completed: May 2003 OASIS Standard: Sep 2003 SAML 1. 0 Completed: May 2002 OASIS Standard: Nov 2002 LA: Liberty Alliance ID-FF: Identity Federation Framework
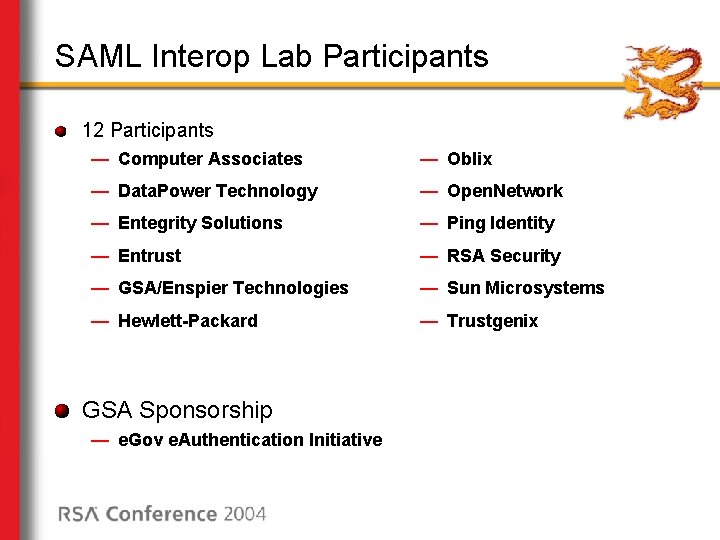
SAML Interop Lab Participants 12 Participants — Computer Associates — Oblix — Data. Power Technology — Open. Network — Entegrity Solutions — Ping Identity — Entrust — RSA Security — GSA/Enspier Technologies — Sun Microsystems — Hewlett-Packard — Trustgenix GSA Sponsorship — e. Gov e. Authentication Initiative
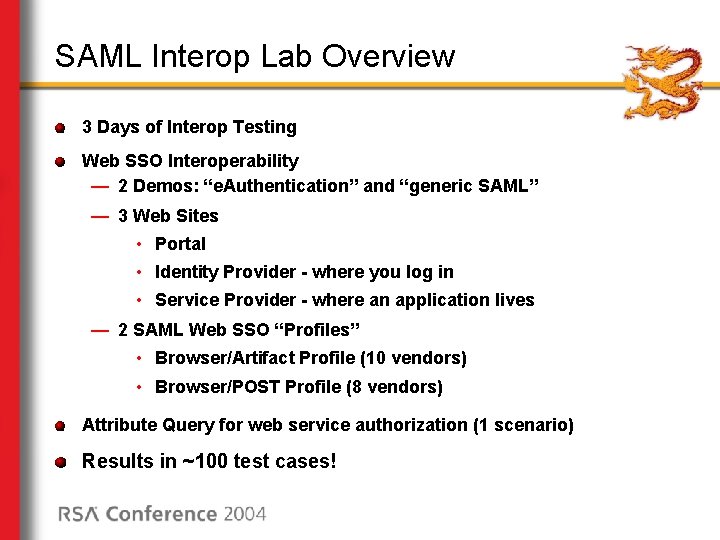
SAML Interop Lab Overview 3 Days of Interop Testing Web SSO Interoperability — 2 Demos: “e. Authentication” and “generic SAML” — 3 Web Sites • Portal • Identity Provider - where you log in • Service Provider - where an application lives — 2 SAML Web SSO “Profiles” • Browser/Artifact Profile (10 vendors) • Browser/POST Profile (8 vendors) Attribute Query for web service authorization (1 scenario) Results in ~100 test cases!
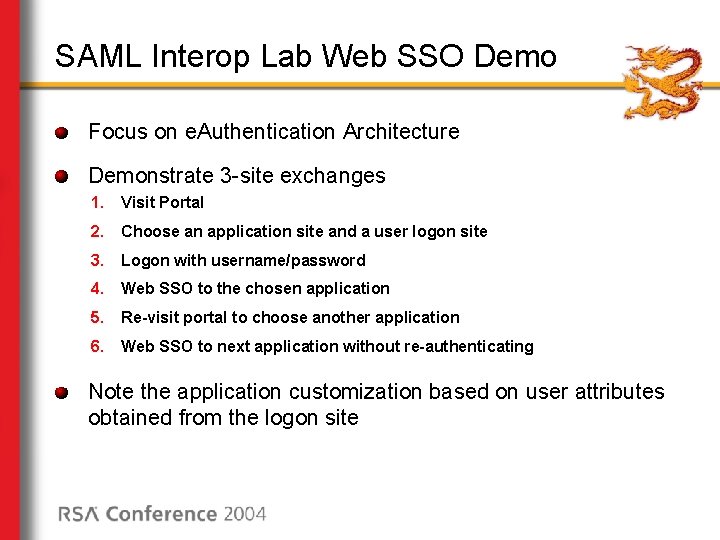
SAML Interop Lab Web SSO Demo Focus on e. Authentication Architecture Demonstrate 3 -site exchanges 1. Visit Portal 2. Choose an application site and a user logon site 3. Logon with username/password 4. Web SSO to the chosen application 5. Re-visit portal to choose another application 6. Web SSO to next application without re-authenticating Note the application customization based on user attributes obtained from the logon site
Wrapup Questions? On to the demo!
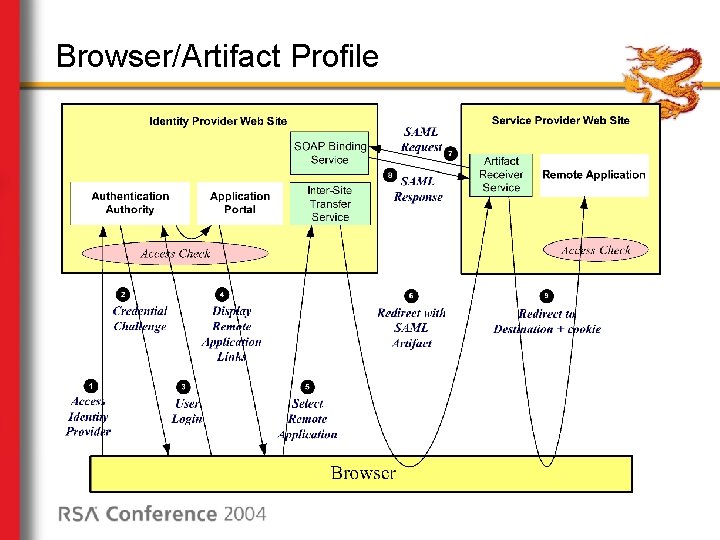
Browser/Artifact Profile
Browser/POST Profile
- Slides: 11